Autonomous AI agents duped into leaking sensitive data in phishing test
AI agents given access to corporate email and business applications could become a new phishing target for attackers, according to cybersecurity researchers, after a test agent built on OpenClaw was tricked into sharing cloud credentials and customer data with an external attacker. Varonis Threat Labs said it built an OpenClaw AI agent called Pinchy to […]
AI red teaming comes of age
When Ram Shankar Siva Kumar launched Microsoft’s AI red team in 2019, the discipline barely existed. “The running joke used to be that people who used to work in AI red teaming, you can round them up in a 14-foot catamaran,” he tells CSO. At the time, Microsoft’s approach looked familiar to anyone in cybersecurity: […]
UK move to filter photos and messages triggers encryption worries for CISOs
UK Prime Minister Keir Starmer’s speech on Monday insisting that tech companies create device controls to somehow block children from viewing or creating sexually explicit imagery has raised alarms among CISOs, who worry that the same technology could undermine enterprise security. Starmer gave tech firms three months to create and implement such restrictions voluntarily, at […]
Enterprises know AI-generated code is vulnerable; they’re shipping it anyway
AI-generated code is riddled with security flaws, yet enterprises are shipping more of it than ever before. Why? Perhaps they’re over-confident, lack true visibility into security risks, or are simply choosing to ignore the problem and hope it goes away. It’s a dangerous game to play at the dawn of the agentic AI era, as […]
Anthropic releases Mythos-class Fable 5 model with safeguards for cyber risks
Anthropic unveiled two new powerful AI models built on its previously restricted Mythos architecture: Claude Fable 5, which is being made broadly available, and Claude Mythos 5, which remains limited to a small group of cybersecurity and infrastructure partners. Anthropic describes Fable 5 as the most capable model it has ever released to the public, […]
Check Point warns of ransomware-linked attacks exploiting outdated VPN protocol
Check Point has issued emergency hotfixes for a pair of vulnerabilities affecting VPN deployments that still use the deprecated Internet Key Exchange version 1 (IKEv1) protocol, warning that one of the flaws is already being exploited in the wild. The more serious issue allows attackers to establish VPN sessions without a valid password, potentially giving […]
Security shifts to the human layer as AI scams surge
Cybercriminals are increasingly reshaping familiar social-engineering campaigns around the way employees use AI, with separate advisories from Microsoft and Google documenting how attackers are adapting scams to AI-powered tools, trusted digital services, and changing workplace behavior. Microsoft Threat Intelligence, in its advisory, said threat actors are “leveraging the wider global interest around AI itself as […]
AI worm prototype shows attackers don’t need Mythos to take over your network
Researchers from the University of Toronto developed a computer worm prototype powered by an AI agent that successfully self-replicated to different systems within a simulated computer network. The worm used a free large language model (LLM) running on local hardware and exploited a combination of older and new vulnerabilities, as well as misconfigurations that remain […]
Meet Hades: The malware that lies to AI security agents
Threat actors are continuing their onslaught against software supply chains, now with malware named after death itself. The newly-discovered Hades Campaign is a “highly sophisticated” supply chain compromise that targets Python developer environments and runs as soon as infected packages are imported. It uses the popular Bun toolkit to silently execute multi-layer payloads that can […]
OpenAI’s Lockdown Mode is trying to solve the problem that it created
OpenAI’s move to implement a Lockdown Mode that tries to limit data exfiltration by shutting down external capabilities is being seen as making the best out of a bad situation. But Lockdown Mode doesn’t block exfiltration as much as it slightly reduces it, and the reality of enterprises using multiple AI vendors for their agentic […]
Attackers exploiting unpatched Cisco SD-WAN flaw
Cisco warns customers of an actively exploited high-severity vulnerability in Catalyst SD-WAN Manager, an enterprise network management system that has been targeted by hackers multiple times in the past. Located in the command-line interface, the flaw allows authenticated attackers to escalate privileges to root and take over the entire system. The vulnerability, tracked as CVE-2026-20245, […]
Protocol Buffers schemas expose remote code execution risk
A widely used JavaScript implementation of Google’s Protocol Buffers format is placing too much trust in untrusted data, exposing affected applications to remote code execution and other attacks. Researchers at Cyera have disclosed six vulnerabilities affecting “protobuf.js,” all stemming from the library’s handling of schema and metadata. Attackers could exploit an input validation oversight to […]
Why most enterprise security teams would fail a military readiness test
Have you ever watched a military cyber ops team go to work responding to a cyberattack simulation? It’s like that scene from Die Hard 4.0 when all the screens start flashing red and systems start shutting down; however, unlike the movies, where bumbling government IT workers are caught out and panicking, our military actually moves […]
15 tough cybersecurity questions every CISO must answer
As CISOs know, an effective security program cannot be static. Rather, it must adapt to the evolving threat landscape and an ever-changing business environment. To adapt and improve, CISOs must continuously evaluate their existing program. That starts with asking tough questions about their performance, investments, and strategies. Here, security leaders share 15 questions every CISO […]
HTTP/2’s speed abused to slow webserver performance in DoS attack
Security researchers are warning of an issue with the default HTTP/2 configuration used by major web servers which reportedly survived more than a decade of human review before showing up in Codex-assisted analysis. A flaw in the handling of the HTTP/2 protocol made a denial-of-service (DoS) attack possible on web servers including nginx, Apache HTTP […]
Ukraine’s foreign minister offer recipe for improved resilience
Cybersecurity professionals were offered lessons of resilience in the most extreme circumstances from Ukraine’s former minister of foreign affairs. Dmytro Kuleba, who served as Ukraine’s Minister of Foreign Affairs between 2020 and 2024, told Infosecurity Europe delegates that the key to Ukraine’s survival after the full-scale Russian invasion of 2022 was pre-planning, a lesson learned […]
Microsoft identifies seven new ways AI agents can be hacked
Microsoft has identified seven new failure modes in agentic AI systems, in addition to those it identified last year in its first Taxonomy of Failure Modes in Agentic AI Systems. Four things contributed to the growing list of ways agentic AI can go wrong: the speed at which the technology went mainstream, the growing maturity […]
Patching fast and slow: Ruby devs delay to defend against supply chain attack
The team behind RubyGems, a package hosting site for Ruby developers, has added a new feature to bundler, a tool for managing Ruby packages (or ‘gems’) to protect developers against the recent wave of software supply chain attacks: A cooling-off period before recently updated packages are installed on their systems. Recent attacks on software repositories […]
Malware could drain your fuel tank as well as your bank account
Ongoing cyber-attacks on automated tank gauges (ATGs) could result in fuel tanks being drained without businesses noticing, the US Cybersecurity & Infrastructure Security Agency has warned. Connected ATGs are widely deployed in gas stations, as well as on military bases, in hospitals, and in manufacturing plants. And it’s not just fuel stores at risk: ATGs […]
Claude Code has an MCP security problem — and your developers are already using it
Claude Code is Anthropic’s AI coding assistant — a command-line tool that developers are adopting fast. It connects to external services through Model Context Protocol, the standard that lets AI tools interact with Jira, Confluence, GitHub, databases and internal APIs. When a developer connects one of those services, Claude Code runs an OAuth flow, the […]
AI tools becoming hot commodities on ransomware marketplaces
Sales of AI-based tools is accelerating within underground ransomware marketplaces, lowering the barrier to entry for new actors in the process. An analysis of Telegram channels, 20 dark web forums, and five underground markets by anti-ransomware platform vendor Halcyon found that AI utility posts grew to 1,486 in February 2026, up from just 38 in […]
US government report slams NIST for NVD backlog
A report from the US Commerce department’s inspector general blames the National Institute of Standards and Technology (NIST) for the ever-growing backlog of vulnerabilities for inclusion in the National Vulnerability Database (NVD). But cybersecurity practitioners say that the backlog, although very real, has been building for years, and that the government is doing little to […]
OpenAI responds to White House executive order on AI governance
OpenAI has proposed mandatory federal evaluations of the most capable AI models before public release while arguing that regulators should stop short of deciding whether those systems can be deployed, staking out a middle ground in the debate over how frontier AI should be governed. The company’s proposal came a day after the White House […]
Hugging Face Transformers RCE flaw enables stealthy compromise via AI model configs
A high severity vulnerability in Hugging Face Transformers enables attackers to compromise systems that use the popular Python library to test and run AI models. The flaw impacts library versions that continue to be actively downloaded and comes at a time when attackers are increasingly targeting the AI supply chain, including through malicious models hosted […]
Beware the ‘son of Mythos,’ security experts warn
Enterprise security teams were urged by security experts at Infosecurity Europe to brace for impact as both Anthrophic and OpenAI expand access to their frontier AI models for vulnerability discovery. Anthropic, in particular, is significantly expanding Project Glasswing, its scheme to provide select organizations with access to Claude Mythos, an AI-powered vulnerability discovery tool that many […]
Hole in GitHub’s browser-based VSCode editor could lead to stolen token
A vulnerability in GitHub’s browser-based VSCode editor could lead to the theft of a developer’s token under certain circumstances, says a researcher. The issue, revealed this week in a blog by Ammar Askar, has apparently been already addressed by GitHub owner Microsoft. But it raises a questions about both DevOps security, and about the researcher’s […]
Enterprise Spotlight: Rethinking cloud strategy in the age of AI
Cloud computing has reached a crossroads. The high cost and data sensitivity of AI workloads are raising the appeal of private clouds, even as neoclouds and sovereign clouds shake up the cloud provider landscape. New cyberthreats, shifting compute requirements, and management complexity are adding to cloud complications. Download the June 2026 issue of the Enterprise […]
Microsoft wants to put AI agents on a short leash
As enterprises race to adopt AI agents across software development workflows, Microsoft is rolling out new controls aimed at keeping the transformation from becoming a security headache. At its annual developer conference, Microsoft Build, the company unveiled a set of initiatives, including a brand new runtime containment offering, Microsoft Execution Container (MXC), for agentic AI […]
AI may finally unlock the cyber budgets CISOs have wanted for years
For nearly two decades, cybersecurity leaders have faced the same reality: No matter how catastrophic the latest breach, ransomware attack, or nation-state intrusion, security spending often struggled against competition with every other business priority. AI may finally be changing that equation. The rapid emergence of frontier AI systems capable of autonomous cyber operations — combined […]
Lessons from the Canvas cyberattack
Canvas cyberattack: Who, what, when, how? What and when? Over May 6 and 7, 2026, Canvas learning management system (LMS) users were served up a defaced web page in place of the expected login page. The altered web page displayed a warning by the ShinyHunters criminal hacker and extortion group advising of the Instructure compromise. […]
Anthropic grants Project Glasswing access to 150 more companies, with a focus on critical infrastructure
Anthropic on Tuesday announced that it was adding 150 more companies to its Project Glasswing AI-based vulnerability hunting initiative, with a particular focus on critical infrastructure companies including those involved in “power, water, healthcare, communications and hardware.” Analysts and security vendors agreed that the move is a positive step, noting that the more companies involved […]
Two-year old Oracle WebLogic Server vulnerability is being exploited
US federal government departments have been given until Thursday to patch a two-year old high severity vulnerability in Oracle WebLogic Server that could allow an unauthenticated attacker to access critical data. The vulnerability, CVE-2024-21182, was added Monday to the Cybersecurity and Infrastructure Security Agency’s (CISA) Known Exploited Vulnerabilities (KEV) catalog, giving federal Oracle admins a […]
HP Poly VoIP vulnerability sets the stage for executive voice deepfakes
HP has released patches for a critical buffer overflow vulnerability in multiple IP-enabled conference phones from its Poly Voice line. The flaw allows unauthenticated attackers to obtain root privileges on the underlying operating system, potentially enabling them to execute other attacks such as eavesdropping on conversations and recording voice data for AI-enabled impersonation attacks. The […]
Trump revives parts of canceled AI order with cybersecurity-focused directive
US President Donald Trump signed an executive order aimed at strengthening cybersecurity defenses and establishing a voluntary framework for cooperation between the federal government and developers of advanced artificial intelligence models, reviving portions of a broader AI initiative that he abruptly shelved less than two weeks ago. The order, “Promoting Advanced Artificial Intelligence Innovation and […]
Infected Red Hat npm packages expose developer credentials
Developers who pulled packages from Red Hat’s @redhat-cloud-services npm namespace over the weekend got a secret-stealing worm instead. Security researchers from several cybersecurity outlets are warning of a new supply chain attack compromising over 30 Red Hat Cloud Services-related npm packages to steal credentials, authentication tokens, and other secrets from developer environments. The campaign, which […]
Attackers exploit Palo Alto GlobalProtect flaw days after disclosure
A Palo Alto Networks vulnerability that allows attackers to establish unauthorized VPN access into corporate networks is being actively exploited in the wild, weeks after the company disclosed the flaw as a medium-severity issue and said it was unaware of any attacks. However, according to Rapid7, threat actors began exploiting the bug within days of […]
Attack targeting OpenAI Codex users exposes AI software supply chain risks
A malicious npm package posing as a remote user interface for OpenAI Codex exfiltrated developer authentication tokens, after attackers allegedly published code to npm that was not visible in the project’s public GitHub repository. Researchers at Aikido said the package, called codexui-android, appeared to offer legitimate functionality while collecting authentication tokens and sending them to […]
7 tabletop exercise mistakes that sabotage incident response
Discussion-based, low-stress simulations during which IT, legal, and other key leadership stakeholders walk through theoretical scenarios to test their preparedness for cyber incidents is a popular and highly useful tool. Yet unless tabletop training is properly handled, the results can be misleading and potentially destructive. When your organization’s incident response training consistently fails to meet […]
Oracle’s first monthly patch release fixes 35 flaws, including 11 rated ‘critical’
Oracle has released the first security fixes in its new monthly Critical Security Patch Update (CSPU) cycle, designed to address urgent vulnerabilities that can’t wait for the company’s quarterly patching. The initial batch addresses 35 flaws, including several for which exploit code is publicly available. In total, there are 11 flaws rated ‘critical’, 18 rated […]
Flowise’s MCP implementation can run ghost commands
Enterprises using the lightweight, open-source Flowise platform to power self-hosted AI workloads have a new near-max severity issue to worry about. Researchers at Obsidian Security have detailed a one-click remote code execution (RCE) vulnerability affecting self-hosted Flowise deployments through its implementation of Model Context Protocol (MCP) stdio servers. The problem is essentially a sandboxing failure […]
6 critical security gaps every CISO must address
CISOs acknowledge that no organization is completely safe, but many also admit their security measures aren’t where they’d like them to be. One-third of CISOs surveyed for Proofpoint’s 2025 Voice of the CISO Report said the data within their organization is not adequately protected, and 58% said their organizations were unprepared to respond to a […]
CSO30 ASEAN & Hong Kong Awards 2026 open for nominations
The CSO30 ASEAN & Hong Kong Awards return in 2026, as an important moment to recognise the cybersecurity leaders and teams who are making resilience measurable across the region. In a landscape shaped by rapid threat evolution, board-level scrutiny and rising expectations of business continuity, these awards spotlight the people and programmes that are turning […]
Russia-aligned crime group Greyvibe extensively uses AI in attacks
Researchers have uncovered a previously undocumented Russian group that makes extensive use of large language models (LLMs) in its attacks against private, government, and military organizations in Ukraine. It uses a variety of attack vectors along with custom malware, with the goal of intelligence gathering for the ongoing war. Dubbed Greyvibe by researchers from WithSecure, […]
Microsoft and security researcher’s dueling posts about cybersecurity disclosures get nasty
Microsoft and a prominent cybersecurity researcher have gotten into a very public and rather personal exchange of unpleasantries about what responsible cybersecurity disclosures should mean in 2026. A cybersecurity researcher going by the name Nightmare Eclipse, who has disclosed several cybersecurity holes before patches were available, posted that he had tried to contact Microsoft officials […]
DNS-AID will make AI agents easier to discover, says Linux Foundation
As AI agents become more numerous and more communicative, keeping track of where to find them is becoming increasingly important. Numerous proprietary agent registries are on the market, but the Linux Foundation suggests we simply extend the distributed, open Domain Name System (DNS) infrastructure we already have. The foundation is now inviting contributions to the […]
Certifiably random: Swiss researchers claim perfect random number source
Researchers in Switzerland claim to have built a perfect random number generator from two quantum superconducting chips, a 30-meter-long pipe, and some software. The resulting device could be used to generate cryptographic keys, or to offer a “public randomness service” for lotteries or blockchain applications, they say. They’re not the first to make the claim. […]
Notepad++ vulnerabilities could enable arbitrary code execution on Windows systems
Two arbitrary code execution vulnerabilities in Notepad++ let local attackers run commands of their choice on Windows machines by tampering with the editor’s XML configuration files, with both flaws rated High at CVSS 7.8. The flaws, tracked as CVE-2026-48778 and CVE-2026-48800, affect every version of the editor up to and including 8.9.6, Notepad++ said in […]
The Gentlemen are coming for your files, and then your network
Ransomware operators have spent years refining the art of locking files. Now, some are working harder to get those lockers to every reachable system first. Microsoft’s recent warning of the Gentlemen ransomware revealed its operators using a self-propagating Go-based encryptor capable of moving laterally through compromised environments and deploying itself across additional systems. “Modern ransomware […]
Cybersecurity trends in SEC filings
In 2023, the Securities and Exchange Commission (SEC) required public companies to include a new section in their 10-K annual filings that is devoted to cybersecurity. This section is meant to address “cybersecurity risk management, strategy, governance and incidents.” I got curious as to what senior cybersecurity executives are conveying about their companies in these […]
GDPR set the tone for regulatory action — and the AI fine pushback to come
Big tech firms continue to push back against fines levied for alleged violations of European data protection law, in what could be a harbinger for AI regulations to come. While lawyers and experts quizzed by CSO broadly argue that big tech firms contesting data protection rules isn’t a particular cause for concern, the more widespread […]
IBM and Red Hat want to become the ‘security clearinghouse’ for open source applications in the enterprise
Open source code is everywhere in the enterprise; it’s estimated that upwards of 90% of Fortune 500 companies have it in their software supply chains. But open source code is notoriously rife with vulnerabilities, and identifying and patching those bugs can be an endless battle for security teams. IBM and Red Hat are betting that […]
Lack of response to critical vulnerability in Gogs is a reminder of the limits of open source projects
A newly discovered and so far unpatched critical vulnerability in the open source Gogs Git service not only demands immediate action from developers to secure their code, it also puts a spotlight on the potential issues in using self-hosted code platforms from small maintainers. The hole is a critical argument injection vulnerability, discovered by a […]
Indian CERT urges firms to contain exploited internet-facing flaws within 12 hours
India’s cybersecurity agency, CERT-In, has urged organizations to patch, mitigate, or isolate known exploited vulnerabilities affecting internet-facing “crown jewel” systems within 12 hours where feasible, warning that AI-assisted attacks are dramatically compressing the time between vulnerability disclosure and exploitation. The recommendation, part of a sweeping new CERT-In blueprint on defending against AI-assisted cyber exploitation, signals […]
GlassWorm falls, but the repo problem is far from solved
Taking down a sprawling malware operation once signaled progress in securing the open-source ecosystem. Now, it barely registers. The GlassWorm campaign disruption comes at a moment when attackers can quickly reconstitute, and defenders are increasingly grappling with a new challenge: distinguishing real threats from automated noise. “I think coordinated actions, like GlassWorm, can sever control, […]
The AI governance imperative you can’t afford to ignore
CIOs rushing to roll out AI agents without real visibility into their decision-making processes are flirting with disaster. According to AI experts, deploying agents without observability processes and tools creates a ticking time bomb with the potential for huge negative consequences. Many companies are deploying AI agents and expecting them to increase productivity with little […]
What the industrialization of exploitation means for defenders
For decades, cybersecurity was a battle of skill. Elite attackers versus elite defenders. The rules of engagement were understood, even if the playing field wasn’t level. If you hired better analysts and bought better tools, hopefully you hardened your systems well enough and built detection capabilities that wore out the adversary’s patience. That era is […]
Employees are unknowingly inviting tech support impersonators into firms, says FBI
Online or telephone IT support scams have been tricking employees into downloading or clicking on malware for years. But according to the FBI, one group that targets US-based law firms has recently found success in person, by convincing firms to allow a supposed IT support person into the building, where they insert a storage device […]
Another IT governance headache: AI-enabled sanction evasion
Over the next three to five years, both governments and the private sector will need to rapidly adapt identification and mitigation protocols as adversaries move from AI-assisted to AI-enabled sanctions evasion and proliferation financing (PF), a new research paper warns. The report, Algorithms of Evasion: The Rise of AI-Enabled Proliferation Financing, from the Royal United […]
AI models more vulnerable than claimed when faced with iterative attacks
CISOs relying on LLM runtime guardrails and official safety scores when making security decisions about their organizations’ AI usage and model selection are due for a wakeup call. According to a new study from Cisco, frontier models from OpenAI, Anthropic, Google, xAI, and Amazon have significantly worse risk profiles when pressured in multi-turn attacks compared […]
FastAPI-based AI tools exposed to authentication bypass by flaw in Starlette framework
A single malformed character in a web request can let an unauthenticated attacker slip past the access controls that guard applications built on Starlette, the open-source Python framework that powers FastAPI, researchers said. The flaw, tracked as CVE-2026-48710 could allow attackers to bypass host-validation protections using malformed Host headers, according to an advisory from cybersecurity […]
The NSA, ‘Mythos’ and the quiet emergence of AI cyber doctrine
For most of my career running security operations, the shape of cyber conflict has been defined by who could move faster than the other side. Faster at identifying a vulnerability, faster at patching, faster at detecting, faster at responding. The last few months have made me reevaluate that framing. Speed still matters. It just no […]
DSPM buyer’s guide: Top 10 data security posture management tools
Data security posture management (DSPM) explained Data security posture management (DSPM) tools help security teams examine their entire data environment to find shadow data, reducing the risk of data loss. Tracking down sensitive data across both cloud and on-premises systems can be vexing. Each environment presents its own challenges. Given the dynamic and ephemeral nature […]
Microsoft previews automatic device isolation in Defender for Endpoint
Microsoft is previewing a new automatic device isolation capability in Defender for Endpoint’s auto attack disruption tool to help security pros contain cyber attacks in progress on their IT networks. The company announced the capability earlier this month in a column about new features in Defender. There’s no word on when automatic device isolation will […]
GitHub Actions abused by Megalodon attack to slip malicious commits into 5,500 repos
A large-scale automated GitHub backdooring campaign was caught pushing thousands of malicious commits into public repositories while posing as routine CI/CD upkeep. Researchers at SafeDep observed the campaign, Megalodon, touching more than five thousand repositories over a six-hour window on May 18. The attack was in the form of a malicious commit, “acac5a9,” targeting GitHub […]
TrapDoor malware campaign puts developer workstations in CISO spotlight
A malicious package campaign across npm, PyPI, and Crates.io has put developer workstations back under scrutiny, after researchers said it targeted developer workflows and AI coding assistant files. Researchers at Socket said the campaign, which they are tracking as TrapDoor, “spans more than 34 malicious packages and 384+ related versions and artifacts” across the three […]
Stop treating AI governance as a review layer. Make it release infrastructure
I’ve spent years building compliance into security products. FedRAMP and Department of War Impact Level authorizations, vulnerability management pipelines: They all follow the same pattern. Build the product, then prove it meets requirements. The compliance layer sits outside the engineering workflow. It reviews what already exists. That model worked when the product stayed static between […]
Vulnerabilities have become cyber attackers’ No. 1 door to the enterprise
Patching practices are coming under intense pressure of late, as time-to-exploit windows accelerate — a new reality likely to worsen as AI assistance in attack chains rises. Now cyber defenders have another cause for flaw alarm: Vulnerability exploitation has significantly pulled away from stolen credentials as the most common entry point in security breaches, according […]
Security experts caution MFA alone can no longer stop threat actors
Cybersecurity experts are warning enterprise admins about an increasing number of phishing campaigns aimed at stealing Microsoft 365 (M365) access tokens to bypass multifactor authentication login protection. Phishing kits aimed at capturing M365 tokens aren’t new; some reports say these kits have been around since 2021. One of the latest is EvilTokens, which researchers at […]
Project Glasswing has uncovered 10,000 vulnerabilities: Anthropic
Anthropic says it and upwards of 50 partners involved in Project Glasswing have uncovered an estimated 10,000 critical or high-severity vulnerabilities in their software offerings. The company launched the cybersecurity initiative, which is built around Claude Mythos Preview, in April, stating that its launch partners would use it as part of their defensive security work. […]
AI security needs a shift from models to systems, researchers argue
Enterprises cannot secure AI agents by making the underlying models more robust and must instead enforce security controls at the system level around them, researchers behind a paper published this month argued, warning that traditional AI-security approaches are increasingly misaligned with how autonomous agents actually operate inside enterprise environments. The paper argues that enterprises should […]
As AI speeds coding, CVE Lite CLI keeps security deliberately AI-free
As AI coding assistants accelerate software development, one OWASP-backed open-source project is arguing that dependency security tooling still arrives too late to be truly useful. CVE Lite CLI, a JavaScript and TypeScript dependency vulnerability scanner focused on local lockfile analysis, is positioning itself around a simple idea. Developers should see dependency risks while they are […]
To pay, or not to pay: 58% of CISOs say they would pay the ransom for their data
If you were hit by ransomware tomorrow, would you pay to get your data back? That’s what more than half of CISOs in a recent survey said their organization would do. It’s a situation more companies are going to face in future. “Attacks are increasing and continuing to increase,” said Christy Wyatt, CEO of security […]
Google leaks details for Chromium bug that can turn browsers into bots
Chromium — the open-source browser that underpins Google Chrome, Microsoft Edge, and Opera, among others — contains an unpatched vulnerability that attackers can exploit to execute JavaScript code persistently across browser restarts. As a result, the flaw can be used to hijack users’ browsers for distributed denial-of-service attacks, run crypto miners, and more. The vulnerability […]
FBI warns of Kali Oauth stealers
The FBI has warned of the danger from a new wave of phishing attacks generated by a tool called Kali365. It enables cyber criminals to obtain Microsoft 365 access tokens and bypass multi-factor authentication (MFA) protocols without intercepting the user’s credentials by capturing Oauth tokens linked to the victim’s Microsoft 365 account. The scam works […]
Police take down VPN service (this time with a good reason)
European authorities have cracked down on a VPN that has been used for various criminal activities. The operation, led by investigators in France and the Netherlands with help from Europol and Eurojust, has dismantled First VPN, a service that has been heavily promoted within Russia as a way of evading law enforcement. Criminals used it […]
Microsoft says it’s making AI ‘safe for work’ in your browser
Microsoft is testing the addition of agentic AI to its corporate browser, Edge for Business. A new version, currently available in a limited preview, will help perform routine tasks more efficiently, according to Microsoft’s partner product manager for Edge, Lindsay Kubasik. Agentic AI will help with completing multi-step tasks such as filling in forms, navigating […]
Why your AI strategy stops where the PLC starts: Hard lessons from the OT frontlines
I spent two days at a substation connecting a major offshore wind farm to the grid. The control room featured three new AI-ready dashboards and a board mandate to “leverage machine learning for resilience.” It also had a maintenance laptop running Windows 7, literally taped to the inside of a cabinet because the Velcro had […]
Identity as the primary attack surface: What modern breaches are really exploiting
The “retro” way “The thing about the old days is… they are the old days” – Slim Charles, The Wire Protecting a specified network perimeter was the main focus of enterprise security strategy for several decades. Businesses made significant investments in firewalls, intrusion detection systems, endpoint security and segmentation controls, all of which were built […]
Google folds CodeMender into agent ecosystem amid push for AI-led AppSec
Google is expanding the role of its CodeMender security agent from autonomous vulnerability remediation toward a larger agentic development ecosystem, signalling a broader push toward AI-driven AppSec. Months after introducing CodeMender, an AI-powered agent designed to autonomously identify and patch software vulnerabilities, Google is now integrating the technology into its expanding Agent Platform strategy unveiled […]
Critical vulnerability in Cisco Secure Workload rated at maximum severity
A critical vulnerability in the on-premises version of the Cisco Secure Workload security platform could allow a threat actor to obtain the privileges of a site admin, enabling them to compromise endpoints and read or modify configuration data. “CSOs need to drop what they are doing and patch this immediately,” warned consultant Robert Enderle, who […]
Microsoft patches two zero-day flaws in Defender
Microsoft released emergency fixes for two zero-day vulnerabilities in the malware protection components of Microsoft Defender. The flaws allow local attackers to gain system-level privileges or cause the anti-malware service to stop working correctly. Both conditions are valuable in a malware attack, first to prevent detection if the system relies only on Microsoft endpoint protection […]
Unpatched ChromaDB flaw leaves servers open to remote code execution
Researchers have published details about a critical vulnerability in ChromaDB that could allow unauthenticated attackers to execute arbitrary code and access sensitive data on machines running the open-source vector database. The issue, tracked as CVE-2026-45829, is located in ChromaDB’s API server and was published by researchers at HiddenLayer after reportedly failing to get in contact […]
Microsoft releases open-source tools to operationalize AI agent safety
Microsoft has open-sourced two new tools aimed at bringing AI safety checks much earlier into the agent development lifecycle. The tools, called Rampart and Clarity, were announced this week as part of Microsoft’s broader push to operationalize safety engineering for agentic AI. “We built these tools because we believe that AI safety has to become […]
AI becoming an SOC imperative for curtailing emerging cyber threats
The cybersecurity profession is on the verge of a sea change, and security pros must begin to master AI tools to combat emerging threats by building more autonomous, real-time protections. Expert panelists at a recent DTX conference session in Manchester, titled “Bot vs Bot: Surviving the Era of Autonomous Cyber Warfare,” highlighted how bringing AI […]
Microsoft is working on a patch for ‘YellowKey’ attack on Bitlocker, offers temporary fix
Microsoft says it is considering a patch for a zero-day vulnerability, dubbed YellowKey, that allows attackers with access to a Windows device to bypass Bitlocker encryption protection and read and write files. The flaw was disclosed last week, and there is already a public proof of concept available. The company issued an advisory Tuesday saying […]
Drupal admins rushing to patch maximum severity SQL injection vulnerability
Administrators of the Drupal open source content management platform are rushing to install an emergency patch issued today to fix a “highly critical” SQL injection vulnerability in the application’s core. While the vulnerability only affects websites that use the PostgreSQL database, there may be upstream issues with Symfony, a set of PHP packages and web […]
GitHub admits major source code leak after 3,800 internal repositories breached
Microsoft’s GitHub has suffered what appears to be its biggest ever security breach after confirming that attackers exfiltrated code from around 3,800 of the company’s internal repositories. News of the incident first emerged on May 19, when GitHub said it was investigating “unauthorized access.” Hours later, the company’s X account confirmed the worst: “Yesterday we […]
SHub Reaper impersonates Apple, Google, and Microsoft in one MacOS attack chain
A newly disclosed macOS infostealer campaign is exploiting user trust in some of the biggest names in tech to slip past defenses. Researchers at SentinelOne have detailed a new variant of the SHub malware family, dubbed “Reaper,” that impersonates Apple, Google, and Microsoft at different stages of a single attack chain targeting Mac users. The […]
Why some security fixes never reach your vulnerability dashboard
On April 22, for roughly 90 minutes, a malicious version of Bitwarden CLI appeared on npm. Version 2026.4.0 contained a credential-stealing payload that executed an obfuscated loader and harvested AWS, Azure, GCP, GitHub, and npm tokens from any developer machine that ran npm install. The attackers reached Bitwarden’s npm publishing path through a compromised GitHub […]
Microsoft disrupts malware code-signing service used by ransomware gangs
Microsoft has disrupted the infrastructure powering the largest malware code-signing service used to help ransomware groups and other cybercriminals make malicious programs harder to detect on Windows. The threat actors behind the service used stolen identities and impersonated legitimate organizations to obtain more than 1,000 code-signing certificates. Microsoft seized the group’s website, signspace[.]cloud, revoked the […]
Contractor’s public GitHub account exposed GovCloud and CISA credentials
Until a few days ago, a publicly-accessible GitHub repository exposed credentials for both US government AWS accounts and internal Cybersecurity and Infrastructure Security Agency (CISA) systems. That’s according to cybersecurity reporter Brian Krebs, who first broke the news over the weekend, acting on a tip from researcher Guillaume Valadon at GitGuardian. Valadon confirmed the information […]
AntV data visualization tool the latest to be hit by ongoing npm supply chain attacks
The world’s largest open-source registry, node package manager (npm), has been hit by another fast-moving malware attack, this time targeting the widely-used AntV enterprise data visualization tool. Unlike last week’s high-profile npm attack on TanStack, which exploited a complex GitHub Actions cache poisoning weakness, the latest incident early on May 19 took the more conventional […]
GitHub scales back bug bounties, reminds users security is their responsibility too
Faced with the growing volume of submission to its bug bounty program, GitHub is replacing cash bounties with swag rewards for reports with low security impact — and asking researchers to stop submitting reports that are low quality or about things that aren’t its fault. The cloud-based code repository platform has seen a sharp increase […]
Internet Explorer may be dead, but its ghost still runs malware
Microsoft’s aging “mshta.exe” utility, a leftover component from Internet Explorer, is still being actively abused in modern malware campaigns years after the browser itself was retired. According to new research from Bitdefender, attackers continue to abuse Microsoft HTML Application Host (MSHTA), a built-in Windows utility capable of executing VBScript and JavaScript from local or remote […]
7 tips for accelerating cyber incident recovery
Despite strong and redundant defenses, enterprises remain vulnerable to a wide range of cyberattacks. And because attacks — and cyber incidents — are inevitable, developing an incident response and recovery process that’s quick, comprehensive, and coordinated is essential. Expediting incident recovery time is critical because the longer an outage persists, the more costs, risk, and business […]
Schwachstellen managen: Die besten Vulnerability-Management-Tools
Schwachstellen zu managen, muss keine Schwerstarbeit sein. Wenn Sie die richtigen Tools einsetzen. Das sind die besten in Sachen Vulnerability Management. Foto: eamesBot – shutterstock.com Nicht nur das Vulnerability Management hat sich im Laufe der Jahre erheblich verändert, sondern auch die Systeme, auf denen Schwachstellen identifiziert und gepatcht werden müssen. Systeme für das Schwachstellen-Management fokussieren […]

SIEM-Kaufratgeber
Die kontextuellen Daten, die SIEM-Lösungen liefern, sind eine grundlegende Komponente moderner Security-Stacks. PeopleImages.com – Yuri A | shutterstock.com Protokoll-Daten zu auditieren, zu überprüfen und zu managen, ist alles andere als eine glamouröse Aufgabe – aber ein entscheidender Aspekt, um ein sicheres Unternehmensnetzwerk aufzubauen. Schließlich schaffen Event Logs oft eine sekundäre Angriffsfläche für Cyberkriminelle, die damit […]
Security-Infotainment: Die besten Hacker-Dokus
Sie fühlen sich leer ohne Security-Dashboard? Diese Dokumentationen überbrücken den Schmerz bis zum nächsten Arbeitstag. Foto: Gorodenkoff – shutterstock.com Wenn Sie in Ihrer Profession als Sicherheitsentscheider voll aufgehen, brauchen Sie möglicherweise auch zwischen den Arbeitstagen ihre tägliche Dosis Cybersecurity. Falls Ihnen die zahlreichen Annäherungen Hollywoods an das Thema viel zu weit von der Realität entfernt […]
Microsoft May security patch fails for some due to boot partition size glitch
“Something didn’t go as planned. Undoing changes.” That’s all the clue some Windows 11 users will get when Microsoft’s May Security Update fails to install because of insufficient free space on the EFI System Partition (ESP), leaving their systems unprotected by the dozens of patches it contained. This issue affects devices with limited free space […]
AI cyberattackers are getting better faster
The ability of AI models to perform end-to-end, multi-stage penetration tests that match the capabilities of humans undertaking the same tasks has improved dramatically in recent months, according to new benchmarks published by the UK government’s AI Security Institute (AISI). In November 2025, the difficulty of cyber tasks the best models could complete was doubling […]
New image-based prompt injection attack targets multimodal AI models
Security researchers have developed a new image-based prompt injection attack that can manipulate how multimodal AI systems interpret user instructions without modifying the original text prompt, potentially expanding security risks for AI agents and vision-language systems. In a research paper published this week, researchers from Xidian University described a technique called “CrossMPI,” which uses nearly […]
‘Patched’ Windows bug resurfaces 6 years later as working SYSTEM-level exploit
An old elevation-of-privilege (EoV) vulnerability affecting the Cloud Filter driver “cldflt.sys” in Windows has come back to haunt Microsoft, as researchers claim it is still exploitable six years after it was supposedly patched. The flaw, originally reported to Microsoft by Google Project Zero researcher James Forshaw in September 2020, was recently picked up by Nightmare […]
Why the best security investment a board can make in 2026 isn’t another tool
There is a conversation that happens in boardrooms every quarter that security leaders will recognize. The CISO presents the threat landscape. The board asks what the company needs. The answer, almost always, is another tool. Another platform, another module, another vendor to close the latest gap. The budget gets approved. The tool gets deployed. And […]
AI coding is fueling a secrets-sprawl crisis few CISOs are containing
When Matt Schlicht built Moltbook, the social network where AI agents talk to one another, he didn’t write the code himself. He “just had a vision,” and vibe-coded it. The social network launched on Jan. 28, 2026, and within days, security researchers started to see serious security flaws. Experts at cloud security company Wiz and, […]
Expired domain leads to supply chain attack on node-ipc npm package
A popular npm package called node-ipc has been compromised, with hackers publishing malicious versions that bundle credential stealing malware. The root cause of the compromise was an expired domain name that attackers managed to register in order to hijack a maintainer’s account. The node-ipc package has had malware added to its code in the past. […]
Exchange Server zero-day vulnerability can be triggered by opening a malicious email
A newly discovered zero-day vulnerability in Microsoft Exchange Server has experts declaring an emergency and urging CSOs to think about the need to abandon on-premises email solutions. “Because it’s already being exploited in the wild, this isn’t a ‘patch next week situation; it’s a ‘mitigate right now’ emergency,” warned Rob Enderle of the Enderle Group. […]
Cisco warns of an actively exploited SD-WAN flaw with max severity
Cisco has disclosed a max-severity authentication bypass vulnerability affecting its Catalyst SD-WAN Controller and Catalyst SD-WAN Manager platforms, warning that the flaw has already been found to be exploited in the wild. The disclosure follows an earlier authentication bypass vulnerability that Cisco patched in February. In the latest advisory, the company said the new flaw […]
Autonomous systems are finally working. Security is next
Waymo recently crossed a major milestone: Over 170 million autonomous miles driven without a single serious crash or injury. For years, autonomous driving was treated as a promise that was always just out of reach — too complex, too risky and not ready for the real world. That argument is no longer credible. Autonomous systems […]
EU’s Cyber Resiliency Act will put IT leaders to the test
Unlike most cyber security regulations, the EU’s Cyber Resilience Act is about product safety rather than processes or certification, extending the CE mark from the physical side of products to software, firmware, backend services, and anything with a network connection. It encodes existing best practices, enforces minimum product support lifecycles, and could mean developing stronger […]
The economics of ransomware 3.0
The moment every boardroom dreads There is a moment in almost every ransomware negotiation — usually around 36 hours, when legal, IT and the CFO are all in the same room — when someone says it out loud: “Let’s just see what the insurance covers.” That instinct, understandable as it is, has become one of […]
AI agent finds 18-year-old remote code execution flaw in Nginx
Researchers have found a critical vulnerability in the widely used Nginx web server that can potentially lead to remote code execution under certain conditions. The flaw is a heap buffer overflow that has gone undetected in the program’s code for the past 18 years. Tracked as CVE-2026-42945, the vulnerability is one of 4 bugs found […]
Meet Fragnesia, the third Linux kernel vulnerability in a month
Linux admins reeling from handling last month’s CopyFail and last week’s Dirty Frag kernel vulnerabilities have a new headache to deal with: Fragnesia. “This is a significant vulnerability,” Robert Beggs, head of incident response firm DigitalDefence, told CSO. “It is bypassing traditional filesystem permissions that are present and enforced (for example, ‘file is owned by […]
FlowerStorm phishing gang adopts virtual-machine obfuscation to evade email defenses
A widely active phishing-as-a-service (PhaaS) operation known as FlowerStorm has begun using a browser-based virtual machine to conceal credential theft code, marking what researchers say is an escalation in phishing-kit sophistication that could make attacks harder for traditional email and static-analysis tools to detect. Researchers at Sublime Security said in April that they identified the […]
PraisonAI vulnerability gets scanned within 4 hours of disclosure
A newly disclosed authentication bypass flaw in the open-source AI orchestration framework PraisonAI was probed by internet scanners less than four hours after its public disclosure. According to Sysdig observations, roughly three hours and 44 minutes after a GitHub advisory dropped, a scanner identifying itself as “CVE-Detector/1.0” was already looking through the exposed PraisonAI instances […]
What CISOs need to land a board role
Cybersecurity leaders often have complex relationships with their boards. Many boards lack cyber expertise, and CISOs can encounter roadblocks as a result when it comes to earning board approval. Other security leaders may not have a direct line to their board, or they may be viewed as too technical to win the support needed. One […]
Fired employee sought AI help to hide deletion of hosting firm’s customer data
The apparent revenge deletion of US federal databases after the dismissal of twin brothers from an online hosting company is another reminder to IT and HR leaders that tough off-boarding procedures have to be implemented to prevent insider attacks. Destructive attacks either from disgruntled current or former employees aren’t new. But the conviction by a […]
Fortinet fixes two critical RCE flaws in FortiAuthenticator and FortiSandbox
Fortinet released a batch of patches across its products on Patch Tuesday, including two critical vulnerabilities that can lead to remote code execution. Fortinet flaws, both zero-day and n-day, have been exploited in the wild many times in the past, so companies should deploy patches as soon as possible. “Fortinet vulnerabilities are often attractive to […]
What happens when China’s AI catches up to Mythos?
The Trump-Xi summit opening in Beijing this week carries an agenda item unlike any in the history of US-China diplomacy: what to do about artificial intelligence that can autonomously find and exploit vulnerabilities in the world’s most critical software — and what happens when both superpowers have it. Anthropic’s Mythos Preview, released last month to […]
Microsoft’s new AI system finds 16 Windows flaws, including four critical RCEs
Microsoft has unveiled a new AI-driven vulnerability discovery system that identified 16 previously unknown Windows vulnerabilities, including four critical remote code execution flaws, in what security analysts say could mark a major shift in how software vulnerabilities are discovered and remediated. The system, codenamed MDASH, was developed by Microsoft’s Autonomous Code Security team alongside the […]
Palo Alto Networks bets on identity security for autonomous AI with Idira launch
Palo Alto Networks has launched Idira, a new identity security platform aimed at securing human users, machine identities, and AI agents amid the rising adoption of autonomous AI systems amongst enterprises. The company is positioning Idira as a next-generation identity security platform that goes beyond traditional privileged access management (PAM) systems by applying dynamic privilege […]
ClickFix finds a backup plan in PySoxy proxy chains
ClickFix, a one-shot social engineering technique that tricks victims into executing malicious workflows disguised as fixes to technical issues in their systems, has got a persistence upgrade. In a one-off instance, ReliaQuest researchers have spotted an intrusion chain using scheduled tasks, PowerShell-based command-and-control (C2), and a unique abuse of the decade-old open-source proxy tool PySoxy. […]
CISA’s AI SBOM guidance pushes software supply-chain oversight into new territory
The US Cybersecurity and Infrastructure Security Agency (CISA) and its G7 cyber agency partners have released a list of minimum elements for an AI software bill of materials, a move that could help CISOs assess the security and provenance of AI systems entering enterprise environments. The guidance extends traditional SBOM concepts into AI by calling […]
2026 CSO Award winners showcase business-enabling cyber innovation
The annual CSO Awards annually recognize security projects that demonstrate outstanding security leadership and business value. For this year’s program, CSO honors 64 security organizations whose hard work and innovative approaches have had a significant impact on how their enterprises navigate risks in an increasingly challenging cyber environment. These projects showcase the variety of strategies […]
Google entdeckt erstmals KI-basierten Zero-Day-Exploit
Willkommen im neuen, KI-geschwängerten Bedrohungszeitalter. Gorodenkoff / Shutterstock Die Google Threat Intelligence Group (GTIG) warnt davor, dass kriminelle Hacker mittlerweile KI einsetzen – sowohl, um Schwachstellen aufzuspüren, als auch um anschließend Malware zu entwickeln, die diese aktiv ausnutzt. Der Anlass: Im Rahmen der eingehenden Analyse einer Angriffskampagne prorussischer Hacker haben die Sicherheitsexperten nach eigenen Angaben […]
Der Kaufratgeber für Breach & Attack Simulation Tools
Breach & Attack Simulation Tools geben Aufschluss darüber, wie gut (oder schlecht) Ihre Sicherheitskontrollen funktionieren. Roman Samborskyi | shutterstock.com Lösungen im Bereich Breach & Attack Simulation (BAS) unterstützen Unternehmen dabei, ihr Sicherheitsniveau zu verstehen. Dazu automatisieren die Tools die Tests spezifischer Bedrohungsvektoren. Als Grundlage dienen dabei in der Regel das MITRE-ATT&CK– oder Cyber-Killchain-Framework. BAS-Produkte simulieren […]
May Patch Tuesday roundup: Critical holes in Windows Netlogon, DNS, and SAP S/4HANA
Critical vulnerabilities in Windows Server’s networking and identity infrastructure, as well as a serious hole in Microsoft Dynamics 365 on-premises version, highlight Microsoft’s May Patch Tuesday fixes. They are among the 118 vulnerabilities identified this month by the company. Some in cloud-based services like Azure and Microsoft Teams have already been fixed, so no admin […]
Mistral AI SDK, TanStack Router hit in npm software supply chain attack
The TeamPCP threat group has pulled off another big supply chain attack which within a few hours this week was able to successfully compromise 170 Node Package Manager (npm) and PyPI packages. The attack affected the entire TanStack Router ecosystem (@tanstack) of 42 packages, a routing library hugely popular among React web application developers. Multiple […]
OpenAI introduces Daybreak cyber platform, takes on Anthropic Mythos
OpenAI has unveiled Daybreak, its answer to Anthropic’s Claude Mythos, amid a growing market for frontier AI-powered cyber defense platforms. The initiative combines OpenAI’s large language models, Codex’s agentic capabilities, and integrations with the broader enterprise security ecosystem. The company said Daybreak is focused on accelerating cyber defense operations and enabling organizations to secure software […]
Fake Claude Code takes the IElevator to your browser secrets
Developers looking for Anthropic’s increasingly popular Claude Code tool are now being lured into downloading malware. According to researchers at Ontinue, attackers are abusing a fake Claude Code installer to deliver a previously undocumented PowerShell payload. The malware is designed to evade detection, recover browser encryption material, and steal sensitive data from developer systems. “Developers […]
cPanel flaw exposes enterprises to hosting supply-chain risks
A newly disclosed cPanel vulnerability is being exploited at scale, giving attackers a route into web hosting environments that many enterprises may not monitor closely. Analysts say the risk highlights weak visibility into hosting supply chains. The flaw, tracked as CVE-2026-41940, has been used to deploy backdoors, plant SSH keys, steal credentials, and compromise hosting […]
Developer workstations are the new beachhead
I spent the first week of April reading three separate threat intelligence reports that, on the surface, had nothing in common. One covered a North Korean campaign that had published over 1,700 malicious packages across five open-source ecosystems. Another detailed a malware operation using a Zig-compiled binary to silently infect every IDE on a developer’s […]
CISOs step into the AI spotlight
Serving in the military requires a precise, tactical mindset, and that’s exactly what Barry Hensley espoused during his 24 years in the US Army, where he rose to the rank of colonel. The military “is where you earn your stripes, showing your soldiers your willingness to jump into a foxhole and pick up a weapon,” […]
Why patching SLAs should be the floor, not the strategy
I’ve been a CISO for two separate companies, know several CISOs personally, and interact with many others through various cybersecurity forums. We all have one thing in common. We can tell you our patching SLA numbers off the top of our heads. Ninety-five percent of criticals closed in 14 days. Eighty-something on highs. The board […]
Cybersicherheitsvorschriften: So erfüllen Sie Ihre Compliance-Anforderungen
Mit der Zunahme von Cyberbedrohungen steigt auch die Zahl der Compliance-Rahmenwerke. So können CISOs diese Herausforderung bewältigen. Foto: Dapitart – shutterstock.com Die Anforderungen von Cybersicherheitsvorschriften können je nach Unternehmensgröße, Region, Branche, Datensensibilität und Programmreifegrad sehr unterschiedlich sein. Ein börsennotiertes Unternehmen hat beispielsweise keine andere Wahl, als mehrere Vorschriften einzuhalten sowie Risikobewertungen und Pläne für Abhilfemaßnahmen […]
Customer Identity & Access Management: Die besten CIAM-Tools
Wir haben die besten Lösungen in Sachen Customer Identity & Access Management für Sie zusammengestellt. Jackie Niam | shutterstock.com Customer Identity & Access Management (CIAM) bildet eine Unterkategorie von Identity & Access Management (IAM). CIAM wird dazu eingesetzt, die Authentifizierungs- und Autorisierungsprozesse von Applikationen zu managen, die öffentlich zugänglich sind, beziehungsweise von Kunden bedient werden. […]
Linux kernel maintainers suggest a ‘kill switch’ to protect systems until a zero-day vulnerability is patched
Linux server admins may get the ability to turn off a vulnerable function in the OS kernel until a patch for a zero-day vulnerability is ready, if a proposal from a kernel developer and maintainer is accepted by the open source community. The idea of a kill switch for privileged operators has been suggested by […]
Entries now open for the 2026 CSO30 Australia Awards
Nominations are now open for the 2026 CSO30 Australia Awards, celebrating the country’s most effective and influential cybersecurity leaders. The CSO30 Awards will once again be held alongside the CIO50 Awards, bringing together Australia’s leading technology and security executives for a flagship industry event on 22 September in Sydney. Part of Foundry’s prestigious global awards […]
Lyrie.ai Joins First Batch of Anthropic’s Cyber Verification Program
Dubai-founded OTT Cybersecurity LLC also unveils the Agent Trust Protocol (ATP), the first open cryptographic standard for AI agent identity, scope, and action verification — slated for IETF submission. OTT Cybersecurity LLC, the company behind Lyrie.ai, today announced two milestones that together position the company as foundational infrastructure for the agentic AI era: acceptance into […]
Google discovers weaponized zero-day exploits created with AI
The Google Threat Intelligence Group (GTIG) today released evidence of a zero-day exploit developed by a cybercriminal group with the help of AI. It marks the first time the security research group has identified what it believes to be an AI-crafted zero-day exploit in the wild. While evidence of threat actors using AI models for […]
AI security is repeating endpoint security’s biggest mistake
The security industry is experiencing déjà vu, and most teams haven’t recognized it yet. If you were in the trenches during the early 2000s, you remember the antivirus arms race. IT teams buried under signature updates. Configuration baselines checked obsessively. Patch cycles treated as the primary defense. Meanwhile, attackers pivoted. They wrote malware that matched […]
8 guiding principles for reskilling the SOC for agentic AI
At DXC Technology, global CISO Mike Baker has established one of the largest agentic security operation centers (SOCs) in the world. To upskill the workforce as part of this journey, he embedded experts from agentic SOC vendor 7AI within his security teams. When Damon McDougald, global cybersecurity services lead at Accenture, wanted to retrain his […]
1,800+ MCP servers exposed without authentication: How zero trust can secure the AI agent revolution
We find ourselves teetering upon a precipice of our own unwitting construction, and the vertiginous depth of our collective negligence ought to give every security practitioner profound pause. In our headlong rush to deploy AI agents across enterprise environments, we have erected an infrastructure so thoroughly unfortified that it beggars belief. The Model Context Protocol, […]
Five new holes, one exploited, found in Ivanti Endpoint Manager Mobile
The five new vulnerabilities discovered in Ivanti’s on-premises mobile endpoint management solution are a “classic example of the legacy trap” that CSOs must avoid, says an expert. “Patch today to survive the weekend,” said Robert Enderle of the Enderle Group, “but start planning your exit from legacy MDM as soon as possible.” He was commenting […]
Claude in Chrome is taking orders from the wrong extensions
Anthropic Claude’s Chrome browser extension, known as Claude in Chrome, has a bug that can allow other malicious extensions to hijack it, compromising trusted AI workflows. Researchers at LayerX Security have warned that Claude’s overly trusted browser communication flows can be abused to inject scripts that can potentially hijack the assistant’s capabilities and manipulate browsing […]
Your CTEM program is probably ignoring MCP. Here’s how to fix it
Model Context Protocol (MCP) is the connective tissue of modern AI tooling and has quietly become one of the most significant blind spots in modern security programs. Like shadow IT before it, shadow AI — especially as it relates to MCP risk — introduces a new class of exposures that security teams lack adequate tooling […]
Pen tests show AI security flaws far more severe than legacy software bugs
Penetration tests of AI-based systems are revealing a greater percentage of high-risk flaws than those discovered in legacy systems. Security consultancy Cobalt’s annual State of Pentesting Report reveals that 32% of all AI and large language model (LLM) findings are rated as high risk — nearly 2.5 times the rate (13%) of severe flaws found […]
Your refresh plan has a CVE blind spot
The conversation is straightforward, but the problem behind it is not. The customer bought servers in 2017 and typically refresh every five to six years. Generally, around the 2022 to 2023 timeframe, they would have looked to buy new. Historically, that is what would have happened. But COVID hit, and there were supply chain constraints […]
Become a millionaire by bug hunting on Android
Over the past decade, Google has introduced a wide range of bug bounty programs for its software and services. The company has now announced that the reward for individuals who discover vulnerabilities in Android or the Chrome browser is being increased, bringing the maximum reward to $1.5 million. However, reports indicate that you must find […]
13 new critical holes in JavaScript sandbox allow execution of arbitrary code
Thirteen critical vulnerabilities have been found in the vm2 JavaScript sandbox package that could allow an attacker’s code to escape the container and do nasty things to IT environments. As a result, developers using this library in their applications are urged to update the software to the latest version, which is currently 3.11.2. The warnings […]
Ollama vulnerability highlights danger of AI frameworks with unrestricted access
A critical vulnerability in Ollama poses a direct risk of sensitive information leaks to more than 300,000 internet-exposed servers, researchers have found. The flaw, tracked as CVE-2026-7482, stems from an out-of-bounds heap read in Ollama’s model quantization pipeline. Ollama is one of the most popular frameworks for running AI models on local hardware. The flaw […]
LinkedIn illegally blocking free accounts from seeing ‘who’s viewed your profile’ data, group alleges
A LinkedIn feature that allows paid subscribers to view a list of visitors to their profile should be made available to all EU users free of charge to comply with the region’s General Data Protection Regulation (GDPR), a legal complaint launched by the None of Your Business (NOYB) digital rights group has claimed. Filed this […]
Bots in translation: Can AI really fix SIEM rule sprawl across vendors?
Enterprises migrating between SIEM platforms often have to manually rewrite detection rules because vendors such as Splunk, Microsoft Sentinel, IBM QRadar, and Google Chronicle use different query languages and data models. Researchers now say AI may be able to automate much of that work, though security experts remain divided over whether the problem really requires […]
Critical Palo Alto Networks software bug hits exposed firewalls
Palo Alto Networks is warning customers about a critical buffer overflow vulnerability affecting its PAN-OS user-ID authentication portal that is already being exploited in the wild. The flaw allows attackers to execute arbitrary code with root privileges on exposed firewalls, the company said in a security advisory. PAN-OS is the software that runs all Palo […]
CISOs: Align cyber risk communication with boardroom psychology
By now, executive boards across industries understand that cyberattacks can be costly. What they often lack, however, is a clear view of which risks pose the biggest threat to their business and why certain investments need to rise to the top. Many security leaders lose traction at that point. The challenge is less about sounding […]
Ten years later, has the GDPR fulfilled its purpose?
This year marks the 10th anniversary of the EU’s adoption of the General Data Protection Regulation, which became mandatory for all companies beginning on May 25, 2018. The aim of the GDPR was simple, but important: to improve individuals’ control over their personal data. This regulation replaced Directive 95/46/EC with the clear purpose of unifying data […]
US government agency to safety test frontier AI models before release
The Center for AI Standards and Innovation (CAISI), a division of the US Department of Commerce, has signed agreements with Google DeepMind, Microsoft, and xAI that would give the agency the ability to vet AI models from these organizations and others prior to their being made publicly available. According to a release from CAISI, which […]
Iranian state-backed spies pose as ransomware slingers in false flag attacks
An Iranian state-sponsored espionage group is pretending to be a regular ransomware gang in a new wave of ransomware attacks targeting enterprises. APT group MuddyWater (aka Seedworm) is masquerading as the Chaos ransomware-as-a-service group to confuse incident response and mask its spying and cyber-sabotage, according to research by security vendor Rapid7. The attacks — geared […]
New malware turns Linux systems into P2P attack networks
Attackers have found a new way to turn Linux systems into stealthy supply chain distribution hubs that are resistant to takedowns. Researchers from Trend Micro have disclosed a new malware framework, dubbed Quasar Linux or QLNX, describing it as a modular Linux remote access trojan (RAT). But what sets the campaign apart is the malware […]
Poisoned truth: The quiet security threat inside enterprise AI
As enterprises rush to deploy internal LLMs, AI copilots, and autonomous agents, most security conversations focus on familiar threats: prompt injection, jailbreaks, model abuse, and data exfiltration. But some security leaders argue a quieter risk deserves far more attention: what happens when the model’s understanding of reality itself becomes corrupted. This problem is broadly described […]
Train like you fight: Why cyber operations teams need no-notice drills
St. Michael’s Hospital in Toronto recently executed a full Code Orange simulation: A mass casualty emergency protocol requiring the activation of every clinical and operational team across the hospital. As a Level 1 trauma centre, it conducts large-scale exercises involving teams across the entire hospital: Emergency, surgery, communications, administration. The exercise is not a compliance […]
Die besten DAST- & SAST-Tools
Tools für Dynamic und Static Application Security Testing helfen Entwicklern, ihren Quellcode zu härten. Wir zeigen Ihnen die besten Tools zu diesem Zweck. Chim | shutterstock.com Die Softwarelieferkette – respektive ihre Schwachstellen – haben in den vergangenen Jahren für viel Wirbel gesorgt. Ein besonders schlagzeilenträchtiges Beispiel ist der Angriff auf den IT-Dienstleister SolarWinds, bei dem […]
Supply-chain attacks take aim at your AI coding agents
Attackers too are looking to cash in on the AI coding craze, adapting their supply-chain techniques to target coding agents themselves. Many AI agents autonomously scan package registries such as NPM and PyPI for components to integrate into their coding projects, and attackers are beginning to take advantage of this. Bait packages with persuasive descriptions […]
Edge browser leaves passwords exposed in plain text, says researcher
A Norwegian researcher has identified an issue with Microsoft Edge’s Password Manager that could be a serious concern for businesses. Tom Jøran Sønstebyseter Rønning found that passwords are being saved within the browser in plain text, with the effect that any PC, particularly a shared machine, within an organization is a potential risk. In a […]
CISA mulls new three-day remediation deadline for critical flaws
Experts have mixed reactions to a report that the US Cybersecurity and Infrastructure Security Agency (CISA) is considering reducing the timeline in which government agencies must address critical vulnerabilities from two weeks to only three days. The current 14-day window applies to high-severity flaws dating from 2021 onwards, listed as known to be under exploit […]
CISA pushes critical infrastructure operators to prepare to work in isolation
The US Cybersecurity and Infrastructure Security Agency (CISA) has unveiled a new national initiative aimed at helping critical infrastructure operators withstand and recover from major cyberattacks by preparing to operate in isolation from the internet and third-party dependencies. The program, CI Fortify, is designed to ensure that organizations can continue delivering essential services even when […]
Oracle will patch more often to counter AI cybersecurity threat
Oracle plans to issue security patches for its ERP, database, and other software on a monthly cycle, rather than quarterly, to respond to the increased pace of AI-enabled software vulnerability discovery. Other software vendors, notably Microsoft, SAP, and Adobe, already release patches on a monthly beat, always on the second Tuesday of each month. Oracle, […]
AI finds 20-year-old bugs in PostgreSQL and MariaDB
Open-source databases are facing a bit of a memory problem as AI helps surface decades-old buffer overflow issues in widely used components. Security researchers have disclosed a set of high and critical-severity vulnerabilities affecting PostgreSQL and MariaDB, with two bugs reportedly tracing their roots back more than 20 years. At Wiz’s zeroday.cloud hacking event, researchers […]
Stealthy malware abuses Microsoft Phone Link to siphon SMS OTPs from enterprise PCs
A newly identified malware campaign is abusing Microsoft’s Phone Link feature to intercept SMS-based one-time passwords and other sensitive mobile data directly from Windows systems. The activity, first observed by Cisco Talos in January 2026, involves a remote access trojan dubbed CloudZ and a custom plugin named Pheno that together allow attackers to harvest credentials […]

CISOs step up to the security workforce challenge
A robust cybersecurity program needs a range of skilled people, yet many CISOs continue to face an ongoing skills shortage — and the squeeze may only get worse as AI gains traction. Some 95% of cybersecurity practitioners and decision-makers noted at least one security skills gap at their organization, with almost 60% citing critical or significant […]

Why most zero-trust architectures fail at the traffic layer
Zero trust has become one of the most widely adopted security models in enterprise environments. Organizations invest heavily in identity systems, access policies and modern security tooling. On paper, these environments look well-protected. Yet during incidents, a different reality often emerges. I have worked with organizations where zero-trust initiatives were fully implemented from an identity […]

10 Anzeichen für einen schlechten CSO
Sind IT-Mitarbeiter unzufrieden, kann das an schlechten Führungskräften oder an einer unzureichenden IT-Strategie liegen. Foto: fizkes – shutterstock.com Unternehmen können die für sie allgemein schlechte Lage am Arbeitsmarkt kaum beeinflussen. Doch sie können einige Faktoren vermeiden, die zu Kündigungen durch Mitarbeitende führen. Dazu gehört insbesondere eine schlechte Führung, die fähige Fachkräfte vergrault. Hier sind die […]

Anthropic Mythos spurs White House to weigh pre-release reviews for high-risk AI models
The Trump administration is in early discussions about whether advanced AI models should be vetted before public release, according to reporting from the New York Times, the Wall Street Journal, and Axios. The conversations center on systems capable of facilitating cyberattacks, particularly models that could help users identify and exploit software vulnerabilities. Officials are considering […]
Security agencies draw red lines around agentic AI deployments
With prompt injection and other attack pathways consistently surfacing across agentic AI deployments, security watchdogs have stepped in, collectively, to draw some hard boundaries. A joint advisory from the US Cybersecurity and Infrastructure Security Agency (CISA) and international partners has called for tighter control over permissions, stronger monitoring, and a more deliberate rollout strategy, urging […]

The fake IT worker problem CISOs can’t ignore
Hiring fake IT workers has been a growing problem in recent years — but it’s often a problem very few want to admit to. From Fortune 500 companies down to smaller organizations, remote hiring practices have been exploited to grant trusted access to individuals who are not who they claim to be creating an insider […]

How CISOs should utilize data security posture management to inform risk
Every CISO eventually faces the same tension: You know your security program needs to mature, but the budget and headcount to do it all aren’t there. That tension is especially sharp when it comes to data security posture management (DSPM). Not every organization can afford, or even needs, the gold standard of DSPM deployment. Full-featured […]

Was ist ein Botnet?
Ein Botnetz besteht aus vielen “Zombie”-Rechnern und lässt sich beispielsweise einsetzen, um DDoS-Attacken zu fahren. Das sollten Sie zum Thema wissen. FOTOKINA | shutterstock.com Kriminelle Hacker suchen stets nach Möglichkeiten, Malware in großem Umfang zu verbreiten oder Distributed-Denial-of-Service (DDoS)-Angriffe zu fahren. Ein Botnet eignet sich dazu besonders gut. Botnet – Definition Ein Botnet ist eine […]

AI agents can bypass guardrails and put credentials at risk, Okta study finds
An AI agent that revealed sensitive data without being asked. An agent that overruled its own guardrails. Another that sent credentials to an attacker via Telegram, because it forgot it wasn’t supposed to do so after a reset. It’s no secret that AI agents have huge potential, balanced by equally big risks. What’s becoming apparent, […]

Windows shell spoofing vulnerability puts sensitive data at risk
Microsoft and the US Cybersecurity and Infrastructure Security Agency (CISA) have sounded the alarm about a Windows shell spoofing vulnerability that is already being exploited by attackers. It is not clear by whom as yet, but the main suspects are hackers in Russia. CISA has mandated that all federal agencies patch this vulnerability, designated CVE-2026-32202, by […]

Human-centric failures: Why BEC continues to work despite MFA
Business email compromise (BEC) is still thriving even in organizations that have implemented multi-factor authentication (MFA). As security professionals, we often assume that MFA is the silver bullet for email security, but real-world incidents suggest otherwise. Attackers exploit human behaviors, process gaps and operational blind spots that MFA alone cannot address. In many modern BEC […]

Just 34% of cyber pros plan to stick with their current employer
Declining job satisfaction means that only one in three (34%) cybersecurity professionals plan to stay with their current employer, increasing the pressure on CISOs’ talent retention strategies. And according to a survey of 500 cybersecurity professionals by IANS and Artico Search, while salary remains important it is not the primary driver of retention. Flexible work […]
Managing OT risk at scale: Why OT cyber decisions are leadership decisions
The first time I approached an OT environment, I assumed that the strategies effective in IT cybersecurity would be equally applicable. I was wrong. The experience revealed a fundamental difference, highlighting the need for a distinct approach to OT cyber risk management. The mistake was not technical. It was conceptual. I was treating OT as […]

Enterprise Spotlight: Transforming software development with AI
Artificial intelligence has had an immediate and profound impact on software development. Coding practices, coding tools, developer roles, and the software development process itself are all being reimagined as AI agents advance on every stage of the software development life cycle, from planning and design to testing, deployment, and maintenance. Download the May 2026 issue of the Enterprise Spotlight from the editors […]

4 ways to prepare your SOC for agentic AI
According to IDC, agentic AI is on track to become mainstream infrastructure. The analyst firm expects 45% of organizations to have autonomous agents operating at scale across critical business functions by 2030. In enterprise SOCs, AI is already reshaping functions like alert triage, enrichment, data correlation, IOC validation and initial containment. It could soon move […]

‘Trivial’ exploit can give attackers root access to Linux kernel
CSOs must ensure their Linux-based systems block unauthorized privilege escalation until distros release patches to plug a serious kernel vulnerability affecting all Linux distributions shipped since 2017. Until fixes are available for what’s been dubbed the Copy Fail logic bug (CVE-2026-31431), which lets users easily obtain root access, there isn’t much CSOs can do, says […]
Bank regulator sounds warning over cybersecurity threat posed by AI models
Frontier AI models inspired by Anthropic’s Claude Mythos could arm attackers with advanced capabilities that the banking sector is ill equipped to cope with, Australia’s financial regulator, the Australian Prudential Regulation Authority (APRA), has warned. In a letter addressed to the country’s financial sector this week, the body lays out how the arrival of Claude […]

Dismantle implicit trust in OT networks, CISA tells critical infrastructure operators
The US Cybersecurity and Infrastructure Security Agency (CISA) has asked owners and operators of operational technology to stop assuming their networks are safe, and has released joint guidance to adapt zero trust principles for industrial systems that support US power, water, transportation, building automation, and weapons-support infrastructure. OT owners should design controls on the assumption […]
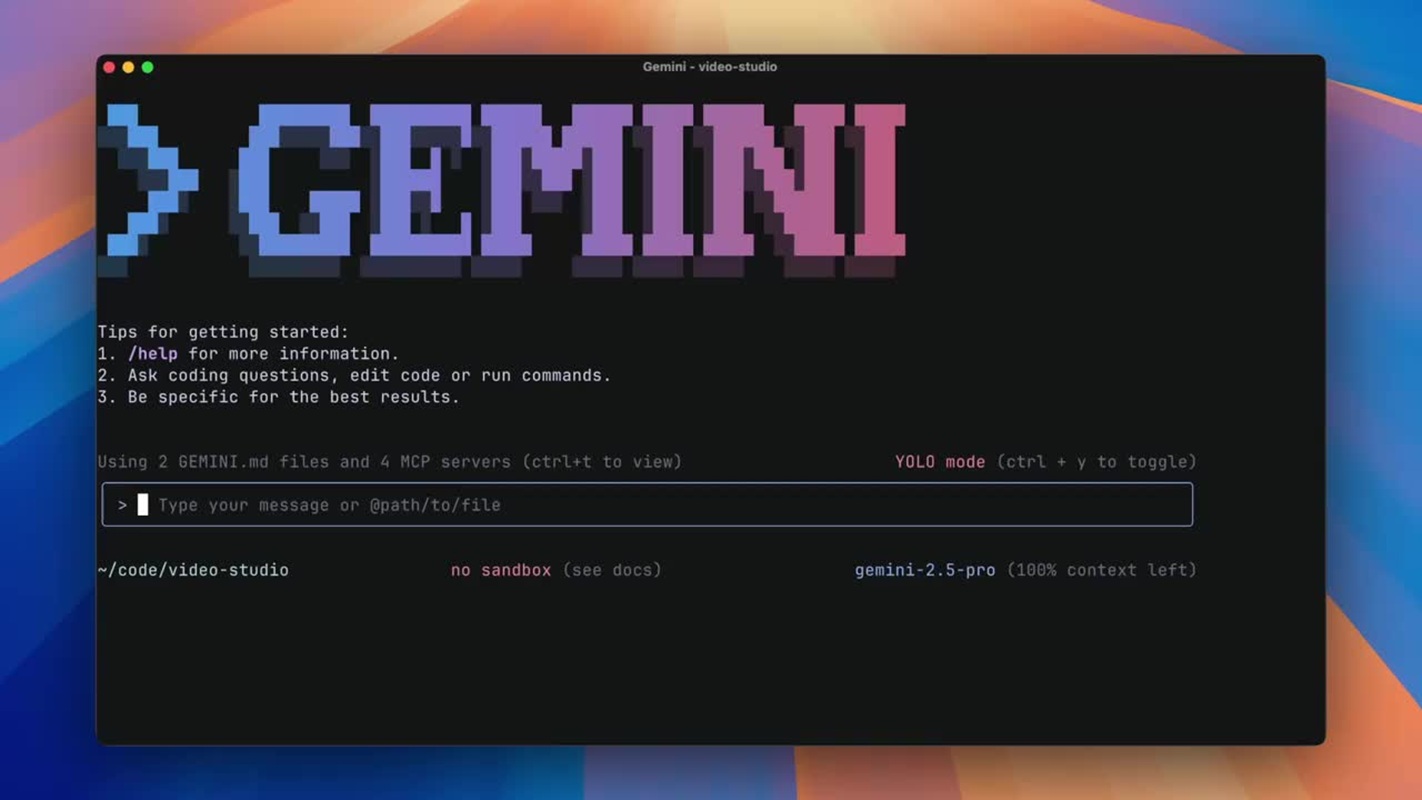
Max-severity RCE flaw found in Google Gemini CLI
Security researchers are warning about a max severity vulnerability in Google Gemini CLI that could allow remote code execution (RCE) in environments where the tool processes untrusted inputs. The issue was disclosed by Novee Security researchers and affects the @google/gemini-cli package and its associated GitHub Action, widely used in CI/CD workflows. “Gemini CLI (@google/gemini-cli) and […]

SAP npm package attack highlights risks in developer tools and CI/CD pipelines
A supply chain attack on SAP-related npm packages has put fresh scrutiny on the developer tools and build workflows that enterprises rely on to produce software. The campaign, referred to as “mini Shai-Hulud,” affected packages used in SAP’s JavaScript and cloud application development ecosystem. The malicious versions added installation-time code that could steal developer credentials, […]

Stopping the quiet drift toward excessive agency with re-permissioning
In their infancy, LLM models were not difficult to contain. You gave a prompt; they responded, and if something was wrong it was usually “just text.” This could take the form of a summary that missed the best bits, a tone-deaf line or a wordy sentence. But then, agents were co-opted as the core reasoning […]

ODNI to CISOs on threat assessments: You’re on your own
Every year, CISOs, CSOs, and chief risk officers pore over the Office of the Director of National Intelligence (ODNI)’s Annual Threat Assessment (ATA) for insights on emerging threats they may soon face. This year, however, structural changes to the report itself underscore a foundational shift that CISOs, CSOs, and CROs must pay attention to. In […]

10 wichtige Security-Eigenschaften: So setzen Sie die Kraft Ihres IT-Sicherheitstechnik-Teams frei
Lesen Sie, worauf es bei der Zusammenarbeit zwischen Ihrem IT-Security- und Engineering-Team ankommt. Foto: Lipik Stock Media – shutterstock.com Security-Teams bestehen in erster Linie aus Mitarbeitern, die für den Betrieb und die Einhaltung von Vorschriften und Richtlinien zuständig sind. IT-Sicherheitstechnik-Teams, neudeutsch Security-Engineering-Teams, hingegen sind Konstrukteure. Sie entwickeln Dienste, automatisieren Prozesse und optimieren Bereitstellungen, um das […]

Researchers unearth industrial sabotage malware that predated Stuxnet by 5 years
Designed to cripple Iran’s nuclear enrichment program, the 2010 Stuxnet worm set a cybersecurity precedent as the first time a nation escalated its activities from strategic espionage to sabotage in cyberspace. Now, a new discovery suggests such operations were in full swing years before Stuxnet came to light. Researchers from SentinelOne have tracked down samples […]

Critical GitHub RCE bug exposed millions of repositories
A critical remote code execution (RCE) vulnerability in GitHub could potentially allow attackers to execute arbitrary code on GitHub.com and GitHub Enterprise Server. Uncovered by Wiz researchers, the now-patched bug exploited how GitHub handles server-side “git push” operations. By crafting malicious input within a standard Git push, an authenticated user could execute arbitrary commands via […]

AWS leans on prior ingenuity to face future AI and quantum threats
As Amazon celebrates the 20th anniversary of its AWS cloud this year, the world’s biggest cloud computing provider now faces two giant cybersecurity threats — AI and quantum. How the company will navigate these emerging issues to ensure the security and resilience of systems used by its millions of corporate customers remains an evolving question. […]

What it takes to win that CSO role
CSO and CISO roles are among the hardest to fill in IT. Which should be good news for cybersecurity professionals that aspire to leadership positions as the organization’s top security exec. For those that do, the authority, clout, pay, and benefits are increasing significantly. But so too are the responsibility and accountability placed on cybersecurity […]

Third Party Risk Management: So vermeiden Sie Compliance-Unheil
Third Party Risk Management hilft Unternehmen, das Risiko von Compliance-Verstößen zu vermeiden. Foto: Diyajyoti – shutterstock.com In Zeiten der Digitalisierung ist es für Unternehmen unerlässlich, auf die Unterstützung von Drittanbietern zurückzugreifen. Sei es im Bereich der IT-Infrastruktur oder bei der Datenverarbeitung – externe Dienstleister helfen dabei, Geschäftsprozesse effektiver und effizienter zu gestalten. Doch mit der […]

More fake extensions linked to GlassWorm found in Open VSX code marketplace
The threat actor seeding the Open VSX code marketplace with fraudulent extensions that download the GlassWorm malware has uploaded 73 more impersonated links, as its attempt to infect software supply chains continues. Philipp Burckhardt, head of threat intelligence at Socket, which revealed the latest activity, called it a “significant escalation” in the gang’s activity, after […]

Critical Cursor bug could turn routine Git into RCE
Security researchers have disclosed a high-severity vulnerability affecting the Cursor IDE, allowing arbitrary code execution on a developer’s machine through a seemingly routine repository interaction. According to findings by AI pentesting platform Novee Security, once a developer cloned and interacted with a malicious repository, the IDE’s AI agent could trigger embedded Git logic, resulting in […]

Securing RAG pipelines in enterprise SaaS
In the enterprise SaaS space, AI agents are becoming an integral part of the SaaS product. To make these intelligent agents truly useful, they need contextual, customer-specific knowledge, something standard Large Language Models (LLMs), open source or otherwise, inherently lack since they are not trained on customer proprietary data. Retrieval-Augmented Generation (RAG) is the bridge […]

What CISOs need to get right as identity enters the agentic era
Identity has always been central to security, but the proliferation of AI agents is rapidly changing the challenge of managing and securing identity, spurring CISOs to rethink their identity strategies — even how it is defined. “Identity is now both a control surface and an attack surface. We’ve had non-human identities as API keys, tokens, […]

Stopping AiTM attacks: The defenses that actually work after authentication succeeds
The security industry has spent years building better authentication. Longer passwords, second factors, hardware tokens. And attackers responded by moving past authentication entirely. Adversary-in-the-middle (AiTM) phishing does not steal credentials and replay them. It sits between the user and the legitimate service, watches a real authentication succeed in real time, and walks away with the […]

EDR-Software – ein Kaufratgeber
EDR-Software verhindert Endpunkt-Sicherheitsdebakel. Die richtige Lösung vorausgesetzt. SvetaZi | shutterstock.com Software im Bereich Endpoint Detection and Response (EDR) erfreut sich weiterhin steigender Beliebtheit – und wird mit zunehmender Reife immer effektiver. EDR-Lösungen bieten Realtime-Einblicke in die Endpunkt-Aktivitäten und ermöglichen es, Mobiltelefone, Workstations, Laptops, Server und andere Devices vor Cyberangriffen zu schützen. In diesem Kaufratgeber erfahren […]

Infected Cisco firewalls need cold start to clear persistent Firestarter backdoor
Security researchers have discovered a chilling backdoor aimed at Cisco System firewalls that exploits unpatched vulnerabilities to maintain persistence, even after patching. This means that attackers can continue to access compromised devices without re-exploiting the holes. At risk are devices running Cisco ASA or Firepower software, including certain Firepower and Secure Firewall devices. So far, however, […]

Microsoft patched an ‘agent-only’ role that was not
An administrative role meant for AI agents within Microsoft’s Entra ID ecosystem could allow privilege escalation and tenant takeover attacks, as it had privileges over more than agent-related objects. Researchers at Silverfort found that users assigned to Microsoft’s “Agent ID Administrator” role, scoped to agent-related objects like blueprints and agent identities, could take ownership of […]
AI is reshaping DevSecOps to bring security closer to the code
Artificial intelligence tools are revamping DevSecOps processes, enabling security and development teams to more effectively build safeguards into software products from the get-go. But AI’s impact on DevSecOps goes well beyond tooling and processes, altering the scope, skills, and strategies foundational to the discipline as well. “AI is fundamentally shifting DevSecOps from reactive validation to […]

AI is reshaping DevSecOps to bring security closer to the code
Artificial intelligence tools are revamping DevSecOps processes, enabling security and development teams to more effectively build safeguards into software products from the get-go. But AI’s impact on DevSecOps goes well beyond tooling and processes, altering the scope, skills, and strategies foundational to the discipline as well. “AI is fundamentally shifting DevSecOps from reactive validation to […]

The ‘manager of agents’: How AI evolves the SOC analyst role
Every SOC analyst has heard it by now: “AI is coming for your job”. I hear it in conversations with SOC teams. I see it in the hesitation during evaluations. And increasingly, I feel it as a source of resistance — especially from the very people AI is supposed to help. But the reality is […]

4 Wege aus der Security-Akronymhölle
Gefangen im Buchstabensud? mikeledray | shutterstock.com Vor seinen MAGA- und DOGE-Eskapaden wurde Elon Musk in erster Linie als visionärer Entrepreneur wahrgenommen. Damals, im Jahr 2010, ließ er den Mitarbeitern seines Raumfahrtunternehmens SpaceX ein Memo zukommen. Darin kritisierte er den übermäßigen, internen Gebrauch von Abkürzungen in gewohnt ausdrucksstarkem Stil: “Bei SpaceX gibt es eine schleichende Tendenz, […]

New US House privacy bills raise hard questions about enterprise data collection
US House Republicans have introduced two major privacy proposals that would reshape how US companies collect, process, and retain consumer data: the SECURE Data Act for general consumer privacy and the GUARD Financial Data Act for financial institutions. The bills would create national standards for privacy and security practices while broadly preempting many state privacy […]
Scattered Spider co-conspirator pleads guilty
Another member of the notorious Scattered Spider gang of cyber criminals has pleaded guilty in a US court, and will be sentenced later this year. Tyler Buchanan pleaded guilty in a Florida court to conspiring with others to hack into companies’ computer systems with the intent of stealing at least $8 million in virtual currency. […]

CISA last in line for access to Anthropic Mythos
The US Cybersecurity and Infrastructure Security Agency (CISA) does not yet have access to Anthropic’s bug-hunting AI model, Claude Mythos, even though other government agencies do, Axios reported earlier this week. As if that weren’t a big enough slap in the face for the national cyber-defense agency, the list of those who do have access […]

Security-KPIs und -KRIs: So messen Sie Cybersicherheit
Cybersicherheit zu messen, ist kein Kinderspiel. Foto: Ultraskrip – shutterstock.com Eine wichtige Säule jedes ausgereiften Cyberrisk-Programms ist die Fähigkeit, die Performance der IT-Security und registrierte Bedrohungen zu messen, zu analysieren und zu melden. Die Cybersecurity zu messen, ist allerdings kein leichtes Unterfangen: Einerseits, weil sich viele Führungskräfte ohne entsprechenden Background schwer tun, IT-Risiken zu verstehen. […]

Bitwarden CLI password manager trojanized in supply chain attack
Researchers warn of a new software supply chain attack that resulted in a malicious version of Bitwarden CLI, the terminal version of the extremely popular open-source password manager. The attack is believed to be related to the string of recent supply chain compromises attributed to a group called TeamPCP. “The attack appears to have leveraged […]

3 practical ways AI threat detection improves enterprise cyber resilience
Why “more alerts” isn’t the same as better security If you run security in an enterprise environment, you already know the problem. Generic detection tools generate thousands of alerts, most of them low value. Analysts spend hours chasing noise while attackers quietly move laterally using valid credentials and trusted tools. AI‑driven threat detection promises to […]

The curious case of Sean Plankey’s derailed CISA nomination
Donald Trump’s nominee to lead the Cybersecurity and Infrastructure Security Agency (CISA), Sean Plankey, informed Homeland Security Secretary Markwayne Mullin and the White House that he is withdrawing his nomination after a 13-month stall, during which the well-regarded cybersecurity veteran faced mounting resistance. “After thirteen months since my initial nomination, it has become clear the […]
Offer customers passkeys by default, UK’s NCSC tells enterprises
The UK’s National Cyber Security Centre (NCSC) is recommending passkeys as the default authentication method for businesses to offer consumers, citing industry progress that now makes them a more secure and user-friendly alternative to passwords. In a blog post published this week, the agency said passkeys can now be recommended to both the public and […]

Offer customers passkeys by default, UK’s NCSC tells enterprises
The UK’s National Cyber Security Centre (NCSC) is recommending passkeys as the default authentication method for businesses to offer consumers, citing industry progress that now makes them a more secure and user-friendly alternative to passwords. In a blog post published this week, the agency said passkeys can now be recommended to both the public and […]

Google drafts AI agents to secure systems against AI hackers
Google unveiled a broad push toward agentic, AI-driven defense at Google Cloud Next ‘26 to help SOC analysts as they scramble to keep up with the influx of CVEs Mythos threatens. As Mythos promises to uncover more software vulnerabilities, Google is betting that only agents, not analysts, can keep pace with what is coming. Google […]

Microsoft taps Anthropic’s Mythos to strengthen secure software development
Microsoft plans to integrate Anthropic’s Mythos AI model into its Security Development Lifecycle, a move that suggests advanced generative AI is beginning to play a direct role in how major software vendors identify vulnerabilities and harden code against attack. The company said it will use Mythos Preview, along with other advanced models, as part of […]

CNAPP – ein Kaufratgeber
Gorodenkoff | shutterstock.com Cloud Security bleibt ein diffiziles Thema und die Tools, mit denen sie sich gewährleisten lässt, werden zunehmend komplexer und schwieriger zu durchschauen – auch dank der ungebrochenen Liebe der Branche zu Akronymen. Mit CNAPP kommt nun ein weiteres hinzu. CNAPP – Definition Die Abkürzung steht für Cloud-Native Application Protection Platform – und […]

Riddled with flaws, serial-to-Ethernet converters endanger critical infrastructure
Serial-to-Ethernet adapters used in industrial, retail, and healthcare environments to link serial devices to TCP/IP networks are riddled with vulnerabilities and outdated open-source components, researchers warn. The flaws enable various attacks scenarios, including taking full control of mission-critical equipment such as remote terminal units, programmable logic controllers, point-of-sale systems, and bedside patient monitors. In a […]

Claude Mythos signals a new era in AI-driven security, finding 271 flaws in Firefox
The Claude Mythos Preview appears to be living up to the hype, at least from a cybersecurity standpoint. The model, which Anthropic rolled out to a small group of users, including Firefox developer Mozilla, earlier this month, has discovered 271 vulnerabilities in version 148 of the browser. All have been fixed in this week’s release […]

Malicious pgserve, automagik developer tools found in npm registry
Application developers are being warned that malicious versions of pgserve, an embedded PostgreSQL server for application development, and automagik, an AI coding tool, have been dropped into the npm JavaScript registry, where they could poison developers’ computers. Downloading and using these versions will lead to the theft of data, tokens, SSH keys, credentials, including those […]

Microsoft issues out-of-band patch for critical security flaw in update to ASP.NET Core
Developers are advised to check their applications after Microsoft revealed that last week’s ASP.NET Core update inadvertently introduced a serious security flaw into the web framework’s Data Protection Library. Microsoft describes the issue as a “regression,” coding jargon for an update that breaks something that was previously working correctly. In this case, what was introduced […]

NFC tap-to-pay gets tapped by hackers
Cyber crooks are abusing a trojanized Android payment application to steal near field communication (NFC) data and PINs, enabling cloning of payment cards and draining victim accounts. According to ESET researchers, a new variant of the NGate malware has been infused into the HandyPay NFC-relay application to transfer NFC data to the attacker’s device and […]

Anthropic bets on EPSS for the coming bug surge
Anthropic’s Mythos has intensified a problem that vulnerability management programs were already struggling to contain: too many vulnerabilities and not enough clarity about which ones matter. What changes with Mythos — and the AI-based class of vulnerability discovery systems it represents — is the speed at which software flaws can be found and exploited. That […]

SBOM erklärt: Was ist eine Software Bill of Materials?
Softwareentwicklung und Autoproduktion haben mehr gemein, als man denkt. Lesen Sie, was Sie zum Thema Software Bill of Materials (SBOM) wissen sollten. Foto: Ju1978 – shutterstock.com Eine Software Bill of Materials ist ein detaillierter Leitfaden, der unter anderem Aufschluss über die Komponenten Ihrer Software gibt. Als eine Art Stückliste hilft eine SBOM Anbietern und Käufern […]

Thousands of Apache ActiveMQ instances still unpatched, weeks after an actively exploited hole discovered
Two weeks after researchers using an AI tool discovered a major hole in Apache’s ActiveMQ messaging middleware, there are still thousands of unpatched instances open to the internet, more evidence that many application developers and IT leaders aren’t paying close attention to warnings about vulnerabilities. While the remote code injection vulnerability [CVE-2026-34197] was revealed on […]

Azure SRE Agent flaw lets outsiders silently eavesdrop on enterprise cloud operations
A high-severity authentication flaw in Microsoft’s Azure SRE Agent exposed sensitive agent data to unauthorized network access, according to a confirmed vulnerability disclosure. The issue was identified by Enclave AI researcher Yanir Tsarimi, who detailed the findings in a blog post describing how agent interactions could be accessed without proper authentication controls. The vulnerability has […]

Prompt injection turned Google’s Antigravity file search into RCE
Security researchers have revealed a prompt injection flaw in Google’s Antigravity IDE that could be weaponized to bypass its sandbox protections and achieve remote code execution (RCE). The issue came from Antigravity’s ability to allow AI agents to invoke native functions, like searching files, on behalf of the user. Designed to kill complexity, the feature […]

Why identity is the driving force behind digital transformation
Identity centric technologies have undergone a significant transformation in recent times. Gone are the days when it was all about logging in and out of any given system. Today, identity has become the backbone of all digital enterprises. It’s the ‘invisible engine’ that powers everything. From security to how modern-day products are sold. Today’s Identity […]

Top techniques attackers use to infiltrate your systems today
Much of the talk around cybersecurity these days revolves around AI and the threat it poses to corporate systems when used by nefarious actors. But the reality on the ground remains a little more mundane than polymorphic AI malware and criminal masterminds putting machine learning and generative AI to work at scale. Still, keeping on […]

The thin gray line: Handala, CyberAv3ngers and Iran’s proxy ops
On April 7, six US government agencies issued a critical advisory warning domestic private sector organizations of potential infrastructural cyberattacks conducted by Iranian-affiliated Advanced Persistent Threat (APT) actors. The advisory stops short of attributing these threats to a single group but makes reference to 2023 attacks on US water and wastewater facilities linked to the […]

Attackers abuse Microsoft Teams to impersonate the IT helpdesk in a new enterprise intrusion playbook
Attackers are increasingly exploiting enterprise collaboration platforms such as Microsoft Teams to gain initial access, impersonating IT helpdesk staff and persuading employees to grant remote control, according to new research from Microsoft. In a blog post, Microsoft described a “cross-tenant helpdesk impersonation” technique in which threat actors initiate conversations with employees via Teams’ external access […]

Hackers exploit Vercel’s trust in AI integration
Frontend cloud platform Vercel, the creator of Next.js and Turbo.js, has warned about a data breach after a compromised third-party AI application abused OAuth to access its internal systems. A Vercel employee used the third party app, identified as Context.ai , which allowed the attackers to take over their Google Workspace account and access some […]

CISOs reshape their roles as business risk strategists
Nitin Raina’s career history resembles that of many CISOs: He worked in IT infrastructure, operations, and services before moving into security and advancing through the ranks. He’s now global chief information security officer at technology consultancy Thoughtworks. But in a less common professional move Raina also picked up the role of global head of enterprise […]

Copilot & Agentforce offen für Prompt-Injection-Tricks
KI-Agenten sind populär – und anfällig dafür, missbraucht zu werden. DC Studio / Shutterstock KI-Agenten fürs Enterprise können bekanntlich Arbeitsabläufe optimieren. Aber auch die Datenexfiltration – wie Sicherheitsforscher von Capsule Security herausgefunden haben. Sie haben sowohl in Microsoft Copilot Studio als auch Salesforce Agentforce Prompt-Injection-Schwachstellen entdeckt. Diese ermöglichen Angreifern in beiden Fällen schadhafte Befehle über […]
Claude Mythos – ist der Hype gerechtfertigt?
Claude Mythos wird derzeit von ausgesuchten Organisationen getestet – in erster Linie großen Tech-Konzernen aus den USA. Anthropic | Screenshot Der Hype um Anthropics Security-Modell Mythos bekommt erste Risse: Während KI-Konkurrent OpenAI plant, mit einem eigenen Cybersecurity-fokussierten KI-Modell „entgegenzuwirken“, stellen die Sicherheitsexperten von VulnCheck in einer aktuellen Untersuchung die praktischen Auswirkungen von Claude Mythos, respektive […]

Für Cyberattacken gewappnet – Krisenkommunikation nach Plan
loading=”lazy” width=”400px”>Lesen Sie, welche Aspekte für einen Krisenkommunikationsplan entscheidend sind. Gorodenkoff – shutterstock.com Cyberangriffe fordern nicht nur CISOs in punkto Prävention und Krisenbewältigung heraus. Auch die Unternehmenskommunikation ist mit im Boot. Sie ist verantwortlich für den Krisenkommunikationsplan, den sie mit dem CISO entwickelt und bei Cybersicherheitsvorfällen umsetzt. Eine gute Krisenprävention hat aus der Perspektive der […]

Critical sandbox bypass fixed in popular Thymeleaf Java template engine
Maintainers of Thymeleaf, a widely used template engine for Java web applications, fixed a rare critical vulnerability that allows unauthenticated attackers to execute malicious code on servers. The vulnerability, tracked as CVE-2026-40478, is rated 9.1 on the CVSS severity scale and is described as a Server-Side Template Injection (SSTI) issue. Thymeleaf has a sandbox-like protection […]

Flawed Cisco update threatens to stop APs from getting further patches
Cisco admins are scrambling to patch a critical flash memory overflow vulnerability in over 200 Cisco Systems IOS XE-based models of wireless access points (APs), caused by a recent flawed software update. If the issue is not corrected quickly, the AP’s memory will become so flooded that new software updates will be blocked and the […]

White House moves to give federal agencies access to Anthropic’s Claude Mythos
The US government is preparing to authorize a version of Anthropic’s Claude Mythos model for use by major US federal agencies, amid concerns that the AI model could rapidly spot cybersecurity vulnerabilities and offer the ability to exploit them. Federal Chief Information Officer Gregory Barbaccia at the White House Office of Management and Budget (OMB) […]

Another Microsoft Defender privilege escalation bug emerges days after patch
Days after Microsoft patched a high-severity issue affecting its Windows Defender antivirus tool through April’s Patch Tuesday, researchers warn of another vulnerability that could enable SYSTEM privileges through local escalation. In a newly disclosed proof-of-concept (PoC) exploit, dubbed “RedSun,” GitHub user going by the name “Nightmare Eclipse” demonstrated how Microsoft Defender’s handling of certain cloud-tagged […]

Palo Alto’s Helmut Reisinger sees a cyber sea change ahead as AI advances
In two decades, Palo Alto Networks has evolved from a next-generation niche player to one of the largest global cybersecurity giants today. Under its mantra of “platformization,” the company has catapulted its revenues over its closest competitors and boosted its stock valuation to over $130 billion. No stranger to AI use in cybersecurity, Palo Alto recently announced […]

Positiv denken für Sicherheitsentscheider: 6 Mindsets, die Sie sofort ablegen sollten
In einem falschen Security-Mindset gefangen? Foto: Paul Craft – shutterstock.com Dass Jobs im Bereich Cybersecurity ein hohes Burnout-Potenzial aufweisen, ist längst kein Geheimnis mehr: Das Umfeld von Sicherheitsprofis ist vor allem geprägt von dem (gefühlten) Druck, täglich steigenden Anforderungen gerecht werden zu müssen. Dafür sind diverse Gründe ursächlich – in erster Linie aber die Art […]

Cisco Webex SSO flaw needs manual certificate update to fix
Admins who use Cisco Webex Services configured to use trust anchors within the SSO integration with Control Hub must install a new identity provider certificate to close a critical vulnerability, or risk losing access control. Cisco said in an advisory this week that admins must upload a new identity provider (IdP) SAML certificate to Webex […]

RCE by design: MCP architectural choice haunts AI agent ecosystem
AI agent building tools enable users to configure Model Context Protocol (MCP) servers may be exposing systems to remote code execution due to an architectural decision in Anthropic’s reference implementation. At issue are unsafe defaults in how MCP configuration works over the STDIO interface, with broad implications for the agent ecosystem, according to a new […]

NIST cuts down CVE analysis amid vulnerability overload
Overwhelmed by an escalating volume of security flaws, the National Institute of Standards and Technology (NIST) has announced significant changes to how it handles cybersecurity vulnerabilities and exposures (CVEs). Rather than commit to providing enrichment for all entries in its National Vulnerability Database (NVD), the agency will focus on just the most critical CVEs, which […]

Microsoft’s Windows Recall still allows silent data extraction
Microsoft’s Windows Recall feature remains vulnerable to complete data extraction despite a major security overhaul, according to a cybersecurity researcher who says malware running in a user’s context can quietly siphon off everything Recall has captured, without administrator privileges, kernel exploits, or breaking encryption. Alexander Hagenah, executive director at Zürich-based financial infrastructure operator SIX Group, […]

Behind the Mythos hype, Glasswing has just one confirmed CVE
Efforts to cut through the buzz surrounding Anthropic’s Mythos are emerging. As OpenAI moves to counter the hype around it with its own cybersecurity model, VulnCheck is reporting that the model’s publicly attributable output amounts to just one confirmed CVE. While Project Glasswing, the controlled access program for Mythos, promises a powerful offensive capability, gated […]

Insurance carriers quietly back away from covering AI outputs
Several major insurance carriers have begun to back away from providing cybersecurity and other insurance to companies using AI to run internal processes, insiders say. While there’s no standard response to customer use of AI in the insurance market, many carriers are now quietly declining to write policies for claims related to AI-generated outputs in […]

The endless CISO reporting line debate — and what it says about cybersecurity leadership
It is difficult to understand why, in 2026, we are still debating the reporting line of the chief information security officer (CISO). It is one of the first topics I wrote about in 2015, and after more than two decades of high-profile cyber incidents, sustained regulatory pressure, massive technology investments and the steady elevation of […]

Was bei der Cloud-Konfiguration schiefläuft – und wie es besser geht
Fehlerhaft konfigurierte Cloud-Dienste sorgen regelmäßig für Datenlecks – und schlimmeres. DC Studio | shutterstock.com Konfigurationsfehler in der Cloud, die Unternehmensdaten gefährden, sind nicht unbedingt etwas Neues – eher im Gegenteil. Umso schlimmer, dass Unternehmen ihre Cloud-Ressourcen immer noch nicht durchgängig absichern. Zumindest legt das ein aktueller Report nahe. Dafür hat der Cloud-Sicherheitsanbieter Qualys 101 Cybersecurity- […]

Critical nginx UI tool vulnerability opens web servers to full compromise
Security vendor Pluto Security has published details of a critical vulnerability in the open-source nginx UI web server configuration tool that has been under active exploitation by cybercriminals since March. News of the flaw, identified as CVE-2026-33032, first appeared on the National Vulnerability Database (NVD) on March 30, the same day that threat intelligence companies […]

Copilot and Agentforce fall to form-based prompt injection tricks
Enterprise AI agents are supposed to streamline workflows. Instead, two fresh findings show they can just as easily streamline data exfiltration. Security researchers have uncovered prompt-injection vulnerabilities in both Microsoft Copilot Studio and Salesforce Agentforce that allow attackers to execute malicious instructions via seemingly harmless prompts. According to Capsule Security findings, SharePoint forms and public-facing […]

The deepfake dilemma: From financial fraud to reputational crisis
Deepfake technology has crossed a critical threshold. What was impossible 10 years ago and required specific expertise only a few years ago is now cheap and accessible. Worse, it’s now good enough to fool a wide range of employees and executives. In fact, a 2025 Gartner survey found that 43% of cybersecurity leaders experienced at […]

7 biggest healthcare security threats
Cyberattacks targeting the healthcare sector have surged since the COVID-19 pandemic and the resulting rush to enable remote delivery of healthcare services. Security vendors and researchers tracking the industry have reported a major increase in phishing attacks, ransomware, web application attacks, and other threats targeting healthcare providers. Recent rising of ransomware attacks on healthcare, in […]

The need for a board-level definition of cyber resilience
Cyber resilience has become a critical governance concern as organizations face increasingly complex and costly cyber threats. However, recent research reveals that the concept of cyber resilience remains inconsistently defined across regulatory frameworks and in some cases presents contradictory guidance to cross-sector and multinational organizations. This conceptual fragmentation poses a systemic risk for top management […]

Mallory Launches AI-Native Threat Intelligence Platform, Turning Global Threat Data Into Prioritized Action
Built by a veteran security team and led by a former Google and Mandiant executive, Mallory delivers intelligence that drives action for enterprise security teams. Mallory is launching a AI-native threat intelligence platform, purpose-built to answer the questions CISOs and their teams are asking every day: What are the real threat vectors for our organization? […]

13 Fragen gegen Drittanbieterrisiken
Drum prüfe… Miljan Zivkovic | shutterstock.com Die zunehmende Abhängigkeit von IT-Dienstleistern und Software von Drittanbietern vergrößert die Angriffsfläche von Unternehmen erheblich. Das wird auch durch zahlreiche Cyberattacken immer wieder unterstrichen. Zwar lassen sich die Risiken in Zusammenhang mit Third-Party-Anbietern nicht gänzlich beseitigen, aber durchaus reduzieren. Dabei sollten Sicherheitsentscheider eine zentrale Rolle spielen, wie Randy Gross, […]

Curity looks to reinvent IAM with runtime authorization for AI agents
In 2026, enterprise developers are building and deploying the first generation of powerful, increasingly autonomous AI agents at incredible speed. Now comes the hard part: working out how to secure them. Vendors in the space are facing multiple challenges. To begin with, traditional identity and access management (IAM) tools were never designed to secure anything […]

April Patch Tuesday roundup: Zero day vulnerabilities and critical bugs
A critical hole in Windows Internet Key Exchange for secure communications, an actively exploited zero day in Microsoft SharePoint and a critical SQL injection vulnerability in a SAP product are the focus of the April Patch Tuesday releases requiring immediate attention from IT security teams. “April’s threat landscape is defined by immediate, real-world exploitation rather […]
4 questions to ask before outsourcing MDR
Security teams are stretched thin. Alerts never stop, attackers move faster, and expectations for uptime and resilience keep rising. For many IT and security leaders, Managed Detection and Response (MDR) has become less of a “nice to have” and more of a practical way to stay ahead. But outsourcing MDR is not just about handing […]

5 trends defining the future of AI-powered cybersecurity
The new N-able and Futurum Report reveals how AI is reshaping cyber resilience as it accelerates both business innovation and adversarial tradecraft. Attackers are scaling their operations with unprecedented speed, leveraging automation to bypass traditional defenses. For IT security leaders and MSP owners, the days of relying on static, perimeter-based security are over. To stay […]

EU regulators largely denied access to Anthropic Mythos
European regulators have largely been frozen out of early access to Anthropic’s new Mythos model, Politico reports. The AI technology, aimed at cybersecurity use cases, is said to be able to identify and exploit technical vulnerabilities at a level that surpasses most humans — signaling a structural shift for CISOs and the cybersecurity industry. For security […]

How AI is transforming threat detection
Artificial intelligence is rapidly reshaping how security teams detect and hunt cyber threats by helping analyze vast volumes of security data, uncovering subtle signs of malicious activity, and identifying potential attacks faster than traditional tools or human analysts alone. Analyst firm Gartner expects that by 2028, 50% of threat detection, investigation, and response (TDIR) platforms […]

The AI inflection point: What security leaders must do now
AI is no longer a speculative topic for security leaders. It has moved from experimentation to implementation, and increasingly, to measurable production impact. Over the past year, my conversations with CISOs have shifted. The question is no longer whether AI belongs in cybersecurity; it’s about deploying it responsibly, strategically and at scale. For security leaders, […]

Cyber-Inspekteur: Hybride Attacken nehmen weiter zu
Deutschland ist im Visier staatlicher Hacker. Mdisk – shutterstock.com Hybride Attacken auf kritische Infrastruktur in Deutschland und Bundeswehr-Truppen im Ausland nehmen weiter zu. Spätestens seit 2022 sei ein spürbarer Zuwachs zu verzeichnen, sagte der Bundeswehr-Inspekteur Cyber- und Informationsraum, Vizeadmiral Thomas Daum, bei einem Pressetermin bei der Nato-Cyberabwehrübung «Locked Shields» im niederrheinischen Kalkar. Cyber-Angriffe gegen die Bundeswehr […]

Anthropic’s Mythos signals a structural cybersecurity shift
Over the past week, reaction to Anthropic’s Glasswing disclosure has split along familiar lines. At one end: alarm over an AI system capable of autonomously identifying and exploiting vulnerabilities. At the other: dismissive hot takes, arguing there is nothing new here. A more grounded view comes from a new briefing by the Cloud Security Alliance […]

Critical flaw in Marimo Python notebook exploited within 10 hours of disclosure
A critical pre-authentication remote code execution vulnerability in Marimo, an open-source Python notebook platform owned by AI cloud company CoreWeave, was exploited in the wild less than 10 hours after its public disclosure, according to the Sysdig Threat Research Team. The vulnerability, tracked as CVE-2026-39987 with a severity score of 9.3 out of 10, affects […]
Seven IBM WebSphere Liberty flaws can be chained into full takeover
Security researchers are warning of a set of flaws affecting IBM WebSphere Liberty, a lightweight, modular Java application server, that can be chained into a full server compromise. The flaws, a total of seven, that led to the ultimate compromise of the server were initiated by a newly discovered pre-authentication issue in the platform’s SAML […]

CISOs tackle the AI visibility gap
Dale Hoak found himself asking a question that has become familiar to CISOs through the decades: What am I missing? More specifically, Hoak, CISO at software firm RegScale, was wondering what he might be missing around his company’s AI deployments. “The business was moving so fast in using AI, so initially we had some visibility […]

Was ist Federated Identity Management?
Federated Identity optimiert Komfort und Sicherheit auf Kosten der Komplexität. PeachShutterStock | shutterstock.com Im Kern der Enterprise Security steht die Zerreißprobe zwischen Benutzerkomfort und Security-Anforderungen. Dabei handelt es sich um einen Balanceakt, der regelmäßig auf Authentifizierungsebene ausgetragen wird und sich direkt auf das Onboarding- und Anmeldeerlebnis auswirkt. Geht es darum diesen Konflikt aufzulösen, steht Federated […]

Google adds end-to-end Gmail encryption to Android, iOS devices for enterprises
Google has made a big step forward by extending end-to-end encryption to Android and iOS devices for Gmail client-side encryption (CSE) users, says an expert. “All in all, this is a welcome update, especially in light of recent concerns surrounding WhatsApp’s encryption methods,” said Gartner analyst Avivah Litan. “Google’s approach offers verifiable customer-managed keys and […]

Old Docker authorization bypass pops up despite previous patch
Researchers warn about a new vulnerability that allows attackers to bypass authorization plug-ins in Docker Engine and gain root-level access to host systems. The flaw has the same root cause as another authorization bypass vulnerability patched in 2024, but the underlying problem has been known since 2016. Tracked as CVE-2026-34040, the new vulnerability is rated […]

Hacker Unknown now known, named on Europol’s most-wanted list
German police have pinned a name to one of the world’s most notorious hackers. Danii Shchukin operated under the names of UNKN or Unknown and GandCrab and was, according to German police, the leader of one of the largest globally active ransomware groups, known as GandCrab/Revi. Shchukin is known to have been operating since 2019. […]

Hungarian government email passwords exposed ahead of election
When voters in the forthcoming Hungarian election assess the current government, its record on internet security will not be one of its proudest achievements. An analysis by open source investigation organization Bellingcat has revealed that the passwords for almost 800 Hungarian government email accounts are circulating online, many of them associated with national security. These […]

Claude uncovers a 13‑year‑old ActiveMQ RCE bug within minutes
Anthropic’s Claude dug up a critical remote code execution (RCE) bug that sat quietly inside Apache ActiveMQ Classic for over a decade. Researchers at Horizon3.ai say that it only took minutes for their team to work out an exploit chain for the bug with the help of AI. The researcher behind the work, Naveen Sunkavally, […]

Why most zero-trust architectures fail at the traffic layer
Zero trust has become one of the most widely adopted security models in enterprise environments. Organizations invest heavily in identity systems, access policies, and modern security tooling. On paper, these environments look well-protected. Yet during incidents, a different reality often emerges. I have worked with organizations where zero-trust initiatives were fully implemented from an identity […]

The cyber winners and losers in Trump’s 2027 budget
Federal cybersecurity spending will decline in 2027 under Donald Trump’s proposed budget, with uneven shifts across agencies, as some see sizable increases while others face sharp reductions. According to the Office of Management and Budget (OMB) crosscut tables released with Trump’s budget, civilian federal cybersecurity spending is expected to fall from $12.455 billion in 2026 […]

CMMC compliance in the age of AI
Cybersecurity Maturity Model Certification 2.0 (CMMC 2.0) is pushing federal contractors to demonstrate, not just assert, that they can protect sensitive government data. Eligibility for contracts now depends on the ability to show how controlled unclassified information (CUI) is handled, why specific safeguards were selected and whether those safeguards operate consistently under scrutiny from assessors, […]

Was CISOs von Moschusochsen lernen können
Von Moschusochsen können sich CISOs eine Scheibe abschneiden – wenn es nach unserem Autor geht. Wirestock Creators – shutterstock.com Drittanbieter-Risikomanagement ist für CISOs und Sicherheitsentscheider eine signifikante Herausforderung. Wird sie nicht (richtig) gestemmt, drohen weitreichende geschäftliche Konsequenzen – bis hin zum Stillstand der Produktion. Das wurde in den vergangenen Monaten von diversen Cyberattacken auf Drittanbieter unterstrichen. […]

Hackers have been exploiting an unpatched Adobe Reader vulnerability for months
Adobe Reader vulnerabilities have been exploited for decades by threat actors taking advantage of the universal use of the utility to fool employees into downloading infected PDF documents through phishing lures. Now a security researcher says a Reader hole has been quietly exploited by malware for as long as four months, fingerprinting computers to gather […]

Cloudflare ‘actively adjusting’ quantum priorities in wake of Google warning
Google’s accelerated post-quantum encryption deadline has spurred other leaders in the industry, including Cloudflare, to consider pushing forward their own plans. The US National Institute of Standards and Technology (NIST) has set a 2030 deadline for depreciating legacy encryption algorithms ahead of their planned retirement in 2035. Late last month Google brought forward its own […]

Weak at the seams
Before I ever held a security title, I was a software engineer implementing vertically integrated automation systems for industrial manufacturing, warehouse-scale conveyor networks, robotic material handling, physical infrastructure controlled by software on increasingly connected networks. I learned early that tightly coupled systems produce tightly coupled failures. When a single software fault could halt a distribution […]

New ClickFix variant bypasses Apple safeguards with one‑click script execution
ClickFix malware campaigns are evolving again, with threat actors removing one of their most obvious and user‑dependent steps: convincing victims to paste malicious commands into Terminal. Instead, the latest variant uses a single browser click to trigger script execution, streamlining the infection chain and reducing user hesitation. Researchers at Jamf Threat Labs have identified a […]
Patch windows collapse as time-to-exploit accelerates
The gap between vulnerability disclosure and exploitation is drastically decreasing, putting security teams’ patching practices on notice. According to Rapid7’s latest Cyber Threat Landscape Report, confirmed exploitation of newly disclosed high- and critical-severity vulnerabilities (CVSS 7-10) increased 105% year to 146 in 2025, up from 71 in 2024. Moreover, the median time from vulnerability publication […]
Weak at the seams
Before I ever held a security title, I was a software engineer implementing vertically integrated automation systems for industrial manufacturing, warehouse-scale conveyor networks, robotic material handling, physical infrastructure controlled by software on increasingly connected networks. I learned early that tightly coupled systems produce tightly coupled failures. When a single software fault could halt a distribution […]

So geht Post-Incident Review
Post-Incident Reviews können dazu beitragen, die richtigen Lehren aus Sicherheitsvorfällen zu ziehen – wenn sie richtig aufgesetzt sind. dotshock | shutterstock.com Angenommen, Ihr Unternehmen wird von Cyberkriminellen angegriffen, kommt dabei aber mit einem blauen Auge davon, weil die Attacke zwar spät, aber noch rechtzeitig entdeckt und abgewehrt werden konnte – ohne größeren Business Impact. Jetzt […]

Questions raised about how LinkedIn uses the petabytes of data it collects
Through LinkedIn’s more than one billion business users, the Microsoft unit has access to a vast array of personally-identifiable information, including data that could identify religious and political positions. What is less clear is what LinkedIn does with all of that data. A small European company that sells a browser extension to leverage different aspects […]
Arelion employs NETSCOUT Arbor DDoS protection products
Arelion operates the world’s best-connected IP fiber backbone, providing high-capacity transit services to a variety of the globe’s leading ISPs as well as many large enterprises. They provide an award-winning customer experience to clients in 129 countries worldwide, and their global Internet services connect more than 700 cloud, security, and content providers with low-latency transit. […]

6 Winter 2026 G2 Leader Badges prove this DDoS protection stands out
NETSCOUT’s Arbor Threat Mitigation System (TMS) was honored with five badges, while Arbor Sightline earned one badge on G2 for the winter 2026 quarter. These badges span multiple categories. Arbor TMS was awarded badges in the following categories for winter 2026: Leader – Enterprise DDoS Protection Momentum Leader – DDoS Protection Regional Leader (Asia) – DDoS Protection Leader – […]
How botnet-driven DDoS attacks evolved in 2H 2025
The second half of 2025 marked a pivotal shift in the world of distributed denial-of-service (DDoS) attacks. Organizations across the globe faced a perfect storm: Artificial intelligence (AI) matured as an offensive weapon, botnet infrastructure reached new heights with multiterabit attack capacity, and DDoS-for-hire services became more accessible—even to nontechnical adversaries. NETSCOUT’s ATLAS global threat intelligence […]

Yael Nardi joins Minimus as Chief Business Officer to drive hyper-growth
New York, NY: Minimus, a provider of hardened container images and secure container images designed to reduce CVE risk, today announced the appointment of Yael Nardi as Chief Business Officer (CBO). In this newly created role, Nardi will lead the company’s next phase of operations, overseeing top-of-funnel growth strategy, strategic operations, and future corporate development. As the market landscape […]

Hackers exploit a critical Flowise flaw affecting thousands of AI workflows
Threat actors have found a way to inject arbitrary JavaScript into the Flowise low-code platform for building custom LLM and agentic systems. The code injection was possible due to a design oversight, rated at max-severity, in the platform’s custom MCP node, which acts as a plug-in connector for an application’s AI agent to talk to […]

Iran‑linked PLC attacks cause real‑world disruption at critical US infra sites
As the US and Iran agreed to a ceasefire on Tuesday, six US federal agencies have warned that Iran-affiliated threat actors have compromised internet-exposed programmable logic controllers at critical infrastructure facilities in the US. The attacks, which the agencies linked to escalating hostilities between Iran and the US and Israel, targeted Rockwell Automation and Allen-Bradley […]

LLM-generated passwords are indefensible. Your codebase may already prove it
Two independent research programs, one from AI security firm Irregular, one from Kaspersky, have now converged on the same conclusion: Every frontier LLM generates structurally predictable passwords that standard entropy meters catastrophically overrate. AI coding agents are autonomously embedding those credentials in production infrastructure, and conventional secret scanners have no mechanism to detect them. As […]

Forest Blizzard leverages router compromises to launch AiTM attacks, target Outlook sessions
Russian threat actor Forest Blizzard has been exploiting unsecured home and small-office internet equipment, such as routers, to redirect traffic through attacker-controlled DNS servers. The group has leveraged this DNS hijacking activity to support post-compromise adversary-in-the-middle (AiTM) attacks on Transport Layer Security (TLS) connections, targeting Microsoft Outlook on the web domains, according to a Microsoft […]
The zero-day timeline just collapsed. Here’s what security leaders do next
A zero-day is not frightening because it is sophisticated. It is frightening because it is unknown. There is no patch in the moment it matters most. That single condition undermines the comfort most security programs rely on: time. In the past, attackers didn’t need zero-days because they relied on predictable failures in patching and credential […]
Microsoft’s new Agent Governance Toolkit targets top OWASP risks for AI agents
Microsoft has quietly introduced the Agent Governance Toolkit, an open-source project designed to monitor and control AI agents during execution as enterprises try to move them into production workflows. The toolkit, which is a response to the Open Worldwide Application Security Project’s (OWASP) emerging focus on AI and LLM security risks, adds a runtime security […]

The tabletop exercise grows up
In the early 1800s, Prussian officers began rehearsing battles around sand tables. They called it Kriegsspiel, and it worked because it forced them to make high-stakes decisions under pressure. Fast forward to today, and that same concept has become cybersecurity’s go-to tool for crisis preparedness: the tabletop exercise. For good reason: it still works. Full […]

Tipps für CISOs, die die Branche wechseln wollen
Tipps für CISOs mit “Vertical-Switch-Ambitionen”. FotoDax | shutterstock.com In der Außenperspektive sollte es für Menschen, die es zum Chief Information Security Officer gebracht haben, eigentlich kein Problem sein, die Branche zu wechseln. In der Realität stellen viele Sicherheitsentscheider allerdings regelmäßig fest, dass das Gegenteil der Fall ist: Wenn man einmal in einer bestimmten Branche tätig […]

What Anthropic Glasswing reveals about the future of vulnerability discovery
AI giant Anthropic has unveiled Project Glasswing, a cybersecurity initiative built around Claude Mythos Preview, a model it describes as “cybersecurity in the age of AI” that can autonomously identify software vulnerabilities at scale. Rather than release the model publicly, Anthropic is restricting access to a closed consortium of more than 40 companies that includes […]

Fortinet releases emergency hotfix for FortiClient EMS zero-day flaw
Hackers have been exploiting a critical vulnerability in FortiClient Endpoint Management Server (FortiClient EMS) since at least the end of March. Fortinet has published an advisory and released an emergency hotfix that can be applied to affected deployments until a patched version can be released. The vulnerability, now tracked as CVE-2026-35616, allows unauthenticated attackers to […]

5 practical steps to strengthen attack resilience with attack surface management
Every asset you manage expands your attack surface. Internet‑facing applications, cloud workloads, credentials, endpoints, and third‑party integrations all represent potential entry points for attackers. As environments grow more distributed, that exposure expands faster than most security teams can track manually. Attack surface management (ASM) helps answer a critical question for IT security teams: What can […]

5 steps to strengthen supply chain security and improve cyber resilience
Supply chain attacks have rapidly become one of the most damaging and difficult threats facing IT and security teams. When an adversary compromises a trusted vendor, software component, cloud service, or MSP tool, they bypass traditional defenses and enter through the front door. For organizations managing distributed environments, and for MSPs supporting dozens or hundreds […]

Microsoft says Medusa-linked Storm-1175 is speeding ransomware attacks
Microsoft has warned that Storm-1175, a cybercrime group linked to Medusa ransomware, is exploiting vulnerable web-facing systems in fast-moving attacks, at times moving from initial access to data theft and ransomware deployment within 24 hours. The company said the group has heavily targeted organizations in healthcare, education, professional services, and finance across Australia, the UK, […]

Supply chain security is now a board-level issue: Here’s what CSOs need to know
For many years, supply chain security was viewed purely as a technical concern. However, with high-profile vulnerabilities and regulations, it is now a board-level issue that requires organizations to rethink how to build resiliency and insulate their operations. The changing regulatory landscape has been a key driver of the C-suite’s focus, as legislation such as […]

The rise of proactive cyber: Why defense is no longer enough
For more than two decades, cybersecurity has been built on a reactive model: detect intrusions, patch vulnerabilities, respond to incidents, and repeat. That model is now under sustained pressure from a threat environment that is faster, more coordinated, and increasingly automated. Two recent developments illustrate how quickly that model is breaking down. Earlier this month, […]

The noisy tenants: Engineering fairness in multi-tenant SIEM solutions
I recently had the opportunity to review five popular SIEM solutions as part of a judging panel for a Security award. While each platform had its own unique flair, their core promises were remarkably consistent: 24/7/365 SOC monitoring: Round-the-clock coverage backed by global experts to validate and prioritize alerts. Proactive threat hunting: Active searches for […]

North Korean hackers abuse LNKs and GitHub repos in ongoing campaign
DPRK-linked threat actors are preferring stealth over sophistication in targeting South Korean organizations, as researchers report the use of weaponized Windows shortcut (.LNK) files and GitHub-based command-and-control (C2) channels in a new campaign. According to new Fortinet findings, a series of attacks that began in 2024 were found using a multi-stage scripting process and GitHub […]

Authentication is broken: Here’s how security leaders can actually fix it
Authentication keeps breaking where it matters most: On regulated front lines such as healthcare, government, aerospace and travel. The core issue is not a lack of innovation. Instead, it is a brittle and fragmented ecosystem of cards, readers, middleware and software that rarely work together under real-world pressure. Even today’s “passwordless” solutions can be undermined […]

6 ways attackers abuse AI services to hack your business
Attackers are starting to exploit AI systems to mount attacks in the same way they once relied on built-in enterprise tools such as PowerShell. Instead of relying on malware, cybercriminals are increasingly abusing AI tools enterprises depend on — a trend some experts describe as living off the AI land. “We’re seeing it in things […]

Escaping the COTS trap
Over the years, enterprise cybersecurity environments have accumulated staggering numbers of commercial tools. Industry research converges on a consistent picture of tool proliferation that drives complexity, cost, and risk. The global cybersecurity market is valued at approximately $243 billion in 2024 and projected to surpass $520 billion annually by 2026. Commercial off-the-shelf (COTS) software promises […]
Security lapse lets researchers view React2Shell hackers’ dashboard
An apparent security lapse has allowed researchers to peer into the work of a threat group currently exploiting unpatched servers open to the four-month-old React2Shell vulnerability to steal login credentials, keys, and tokens at scale. Researchers from Cisco Systems’ Talos threat intelligence team who made the discovery said Thursday that the data harvested by an […]

A core infrastructure engineer pleads guilty to federal charges in insider attack
When Daniel Rhyne pleaded guilty on April 1 to having launched an insider extortion attack against his then-employer, authorities enumerated the techniques he used, including unauthorized remote desktop sessions, deletion of network administrator accounts, changing of passwords, and scheduling unauthorized tasks on the domain controller. After he shut down key systems and accounts, he sent […]

Google patches fourth Chrome zero-day so far this year
Google has patched another zero-day vulnerability in Chrome, its fourth this year. In patching the vulnerability, tracked as CVE-2026-5281, the company acknowledged that an exploit for it already exists in the wild. According to the report in NIST’s National Vulnerability Database, the vulnerability in Dawn, the implementation of WebGPU used by Chrome, allowed a remote […]

Internet Bug Bounty program hits pause on payouts
Researchers who identify and report bugs in open-source software will no longer be rewarded by the Internet Bug Bounty team. HackerOne, which administers the program, has said that it is “pausing submissions” while it contemplates ways in which open source security can be handled more effectively. The Internet Bug Bounty program, funded by a number […]

Claude Code is still vulnerable to an attack Anthropic has already fixed
The leak of Claude Code’s source is already having consequences for the tool’s security. Researchers have spotted a vulnerability documented in the code. The vulnerability, revealed by AI security company Adversa, is that if Claude Code is presented with a command composed of more than 50 subcommands, then for subcommands after the 50th it will […]

CERT-EU blames Trivy supply chain attack for Europa.eu data breach
The European Union’s Computer Emergency Response Team, CERT-EU, has traced last week’s theft of data from the Europa.eu platform to the recent supply chain attack on Aqua Security’s Trivy open-source vulnerability scanner. The attack on the AWS cloud infrastructure hosting the Europa.eu web hub on March 24 resulted in the theft of 350 GB of […]

12 cyber industry trends revealed at RSAC 2026
The 2026 RSA circus is over. The tents are packed and the elephants have been loaded onto the train. Nevertheless, it was an eventful week. There were fleets of vehicles — Escalades, Rivians, trucks but curiously, no Teslas — strewn with vendor names and tag lines, and you couldn’t walk anywhere near Howard Street in […]

Die besten XDR-Tools
srcset=”https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?quality=50&strip=all 6500w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=300%2C168&quality=50&strip=all 300w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=768%2C432&quality=50&strip=all 768w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=1024%2C576&quality=50&strip=all 1024w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=1536%2C864&quality=50&strip=all 1536w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=2048%2C1152&quality=50&strip=all 2048w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=1240%2C697&quality=50&strip=all 1240w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=150%2C84&quality=50&strip=all 150w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=854%2C480&quality=50&strip=all 854w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=640%2C360&quality=50&strip=all 640w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=444%2C250&quality=50&strip=all 444w” width=”1024″ height=”576″ sizes=”auto, (max-width: 1024px) 100vw, 1024px”>Lesen Sie, worauf Sie in Sachen XDR achten sollten – und welche Lösungen sich in diesem Bereich empfehlen. ArtemisDiana | shutterstock.com Manuelles, siloartiges Management ist in der […]

Cloudflare’s new CMS is not a WordPress killer, it’s a WordPress alternative
Cloudflare on Wednesday rolled out EmDash, which it described as “the spiritual successor to WordPress.” The security vendor positioned EmDash as a far more secure site building tool that avoids the extensive cybersecurity problems with WordPress plugins. But the Cloudflare claims go far beyond cybersecurity issues. The vendor is arguing that the very nature of […]

Cisco fixes critical IMC auth bypass present in many products
Cisco has released patches for a critical vulnerability in its out-of-band management solution, present in many of its servers and appliances. The flaw allows unauthenticated remote attackers to gain admin access to the Cisco Integrated Management Controller (IMC), which gives administrators remote control over servers even when the main OS is shut down. The vulnerability, […]

EvilTokens abuses Microsoft device code flow for account takeovers
A new phishing-as-a-service (PhaaS) campaign is abusing Microsoft’s device code authentication flow to gain unauthorized access to user accounts. Sekoia researchers first spotted the toolkit “EvilTokens” that lets attackers capture authentication tokens by tricking users into completing a legitimate login process in Microsoft’s own environment. The activity, observed since at least mid-February, relies on social […]
Cybersecurity in the age of instant software
AI is rapidly changing how software is written, deployed, and used. Trends point to a future where AIs can write custom software quickly and easily: “instant software.” Taken to an extreme, it might become easier for a user to have an AI write an application on demand — a spreadsheet, for example — and delete […]

Tools, um MCP-Server abzusichern
srcset=”https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?quality=50&strip=all 7200w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=300%2C168&quality=50&strip=all 300w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=768%2C432&quality=50&strip=all 768w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=1024%2C576&quality=50&strip=all 1024w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=1536%2C864&quality=50&strip=all 1536w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=2048%2C1152&quality=50&strip=all 2048w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=1240%2C697&quality=50&strip=all 1240w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=150%2C84&quality=50&strip=all 150w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=854%2C480&quality=50&strip=all 854w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=640%2C360&quality=50&strip=all 640w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=444%2C250&quality=50&strip=all 444w” width=”1024″ height=”576″ sizes=”auto, (max-width: 1024px) 100vw, 1024px”>Unabhängig davon, welche MCP-Server Unternehmen wofür einsetzen – “Unsicherheiten” sollten dabei außenvorbleiben. Gorodenkoff | shutterstock.com Model Context Protocol (MCP) verbindet KI-Agenten mit Datenquellen und erfreut sich im […]

Vim and GNU Emacs: Claude Code helpfully found zero-day exploits for both
Developers can spend days using fuzzing tools to find security weaknesses in code. Alternatively, they can simply ask an LLM to do the job for them in seconds. The catch: LLMs are evolving so rapidly that this convenience might come with hidden dangers. The latest example is from researcher Hung Nguyen from AI red teaming […]

WhatsApp malware campaign uses malicious VBS files to gain persistent access
Microsoft is warning WhatsApp users of a new malware campaign that tricks them into executing malicious Visual Basic Script (VBS) files, ultimately enabling persistence and remote access. In a March 31 report, Microsoft Defender Experts said attackers have been distributing malicious Visual Basic Script (VBS) files through WhatsApp since at least late February, relying on […]

Hacker zielen auf Exilportal Iranwire
Unbekannte sollen das Exilportal Iranwire gehackt haben. PX Media – shutterstock.com Hacker haben nach Angaben der iranischen Justiz mutmaßlich Zugriff auf Daten eines bekannten Exilportals erlangt. Dabei seien große Menge an Daten erbeutet worden, darunter Schriftwechsel, Listen von Angestellten, Informanten sowie streng vertrauliche Daten, berichtete das Sprachrohr der iranischen Justiz, die Nachrichtenagentur Misan. Bei dem Portal handelte […]
9 ways CISOs can combat AI hallucinations
AI hallucinations are a well-known problem and, when it comes to compliance assessments, these convincing but inaccurate assessments can cause real damage with poor risk assessments, incorrect policy guidance, or even inaccurate incident reports. Cybersecurity leaders say the real trouble starts when AI moves past writing summaries and begins making judgment calls. That’s when it’s […]

Security awareness is not a control: Rethinking human risk in enterprise security
Organizations have been responding to phishing, business email compromise, and credential theft in essentially the same manner for over ten years. They essentially follow a playbook that involves investing in awareness training, running phishing simulations, and requiring employees to complete annual security modules. The reason behind this is simple and the reasoning behind these efforts […]

Im Fokus: IT-Leadership

Enterprise Spotlight: Setting the 2026 IT agenda
IT leaders are setting their operations strategies for 2026 with an eye toward agility, flexibility, and tangible business results. Download the January 2026 issue of the Enterprise Spotlight from the editors of CIO, Computerworld, CSO, InfoWorld, and Network World and learn about the trends and technologies that will drive the IT agenda in the year […]

Attack Surface Management – ein Kaufratgeber
Mit diesen Attack Surface Management Tools sorgen Sie im Idealfall dafür, dass sich Angreifer gar nicht erst verbeißen. Sergey Zaykov | shutterstock.com Regelmäßige Netzwerk-Scans reichen für eine gehärtete Angriffsfläche nicht mehr aus. Um die Sicherheit von Unternehmensressourcen und Kundendaten zu gewährleisten, ist eine kontinuierliche Überwachung auf neue Ressourcen und Konfigurationsabweichungen erforderlich. Werkzeuge im Bereich Cyber […]

Anthropic employee error exposes Claude Code source
An Anthropic employee accidentally exposed the entire proprietary source code for its AI programming tool, Claude Code, by including a source map file in a version of the tool posted on Anthropic’s open npm registry account, a risky mistake, says an AI expert. “A compromised source map is a security risk,” said US-based cybersecurity and […]

Attackers trojanize Axios HTTP library in highest-impact npm supply chain attack
Attackers compromised the npm account of the lead maintainer of Axios, a widely used JavaScript HTTP client library, and used it to publish malicious versions of the package that deployed a cross-platform remote access trojan on developer machines. The incident represents the highest-impact npm supply chain attack on record given Axios’ approximately 100 million weekly […]

5-month-old F5 BIG-IP DoS bug becomes critical RCE exploited in the wild
A vulnerability misclassified five months ago as a denial-of-service issue in F5 BIG-IP Access Policy Manager (APM) turned out to be a critical pre-authentication remote code execution flaw that is now under active exploitation. Hackers are using it to deploy a persistent malware program that runs with root privileges. The CVE-2025-53521 vulnerability was first disclosed […]

OpenAI patches twin leaks as Codex slips and ChatGPT spills
OpenAI has fixed two flaws in its AI stack that could allow AI agents to move sensitive data in unintended ways. The issues, disclosed by researchers at BeyondTrust and Check Point Research, affect the OpenAI Codex coding agent and ChatGPT’s code execution environment, respectively. One enabled GitHub token theft through command injection, while the other […]

8 ways to bolster your security posture on the cheap
As every CISO knows, maintaining a strong cybersecurity posture is costly. What’s not so well known is that there are many ways cybersecurity can be enhanced with the help of relatively trivial investments. Simply by thinking creatively, a security leader can substantially boost enterprise protection at a minimal cost. Could your organization benefit from some […]

The external pressures redefining cybersecurity risk
Over the last four years, I’ve watched organizations get blindsided by threats that originated in a third-party network. More than 35% of data breaches are caused by a compromised vendor or partner, not by any failure in the organization’s controls. While many organizations know that the biggest threats to their security come from forces entirely […]

6 key takeaways from RSA Conference 2026
Writing a conference preview is an act of professional speculation. You read the agenda, map the schedule session density, and make your personal best call about where the intellectual energy will concentrate. From my perspective going in, RSA Conference 2026 outlined a defining tension for CISOs today: how to enable AI adoption fast enough to […]

Fahndung nach Cyberkriminellen – 130 Firmen attackiert
130 Unternehmen und Institutionen gerieten ins Visier der Hacker. Tayler Derden | shutterstock.com Nach jahrelangen Cybercrime-Angriffen auf mehr als Hundert Unternehmen und Einrichtungen in Deutschland haben Ermittler zwei zentrale Verdächtige identifiziert. Der eine sei der mutmaßliche Kopf von zwei Hackergruppen, der andere der mutmaßliche Programmierer der von diesen Gruppen genutzten Schadsoftware. Dies teilten das bei […]

Fortinet hit by another exploited cybersecurity flaw
Yet another critical flaw in a Fortinet product has come to light as attackers continue to target the company, this time by actively exploiting a critical SQL injection vulnerability in the cybersecurity company’s management server. The vulnerability, (CVE-2026-21643), allows unauthenticated threat actors to execute arbitrary code on unpatched systems via specifically-crafted HTTP requests. These low-complexity […]

LangChain path traversal bug adds to input validation woes in AI pipelines
Security researchers are warning that applications using AI frameworks without proper safeguards can expose sensitive information in basic, yet critical, non-AI ways. According to a recent Cyera analysis, widely used AI orchestration tools, LangChain and LangGraph, are vulnerable to critical input validation flaws that could allow attackers to access sensitive enterprise data. In a recent […]

Leak reveals Anthropic’s ‘Mythos,’ a powerful AI model aimed at cybersecurity use cases
Anthropic didn’t intend to introduce Mythos this way. Details of what it calls its most capable AI model yet surfaced through a data leak in its content management system (CMS), revealing a LLM with sharply improved reasoning and coding skills. The data leak, which was the result of the company’s staffers inadvertently exposing material about […]

APIs are the new perimeter: Here’s how CISOs are securing them
Recent breaches suggest attackers are shifting beyond traditional endpoints to target application programming interfaces (APIs). But typical perimeter protections can completely miss this vector. “We used to talk about defense-in-depth and endpoint protection,” says Sean Murphy, CISO at BECU, a nationwide credit union. “That morphed into identity, and now the API is the new perimeter.” […]

Why Kubernetes controllers are the perfect backdoor
In my years securing cloud-native environments, I’ve noticed a recurring blind spot. We obsess over the “front doors” such as exposed dashboards, misconfigured RBAC, or unpatched container vulnerabilities. We harden the perimeter, but we often ignore the machinery humming inside. Sophisticated adversaries have moved beyond simple smash-and-grab tactics. They don’t just want to run a […]

Data Security Posture Management: Die besten DSPM-Tools
Data Security Posture Management erfordert nicht nur die richtigen Tools, sondern auch eine entsprechende Vorbereitung. Foto: Rawpixel.com | shutterstock.com Cloud Computing ist von Natur aus dynamisch und flüchtig: Daten können schnell und einfach erstellt, gelöscht oder verschoben werden. Das sorgt dafür, dass auch die Cloud-Angriffsfläche sehr dynamisch ist – was Schutzmaßnahmen erschwert. Ein lästiges Problem […]

European Commission data stolen in a cyberattack on the infrastructure hosting its web sites
The European Commission is continuing to investigate the theft of data from its cloud infrastructure earlier this week. On Thursday, the Commission revealed there had been an attack on its Europa.eu platform, offering few details, then, on Friday, security news site Bleeping Computer reported that the attack had involved the compromise of an account or […]

Lloyds Bank reveals how IT bug exposed transaction data
Lloyds Banking Group has identified the glitch that led to some of its customers being able to see details of other customers’ transactions on March 12. It revealed the information in a letter to the UK Parliament’s Treasury Committee, setting out the details of the incident and how it has been handled. The issue arose […]

Attackers exploit critical Langflow RCE within hours as CISA sounds alarm
Attackers have exploited a critical Langflow RCE within hours of disclosure, prompting the US Cybersecurity and Infrastructure Security Agency (CISA) to formally flag it for urgent remediation. The flaw, which allows running arbitrary code on vulnerable Langflow instances without >credentials, was weaponized within 20 hours of the open-source AI-pipeline tool disclosing it. According to a Sysdig report, […]

Cyberangriff auf die Linke
Die Hackergruppe “Qilin” steht möglicherweise hinter dem Angriff. Studio-M – shutterstock.com Die Linke ist nach eigenen Angaben Opfer einer schweren Cyberattacke geworden und vermutet dahinter russischsprachige Hacker. Man habe am Donnerstag sofort reagiert und Teile der IT-Infrastruktur vom Netz genommen, teilte Bundesgeschäftsführer Janis Ehling mit. «Nach derzeitigen Erkenntnissen zielen die Täter darauf ab, sensible Daten […]

8 steps CISOs can take to empower their teams
Many leaders know empowered teams deliver better results, but not all leaders understand how to get there. It all starts with knowing what empowerment truly means. Put simply: Empowerment is the absence of micromanagement. Empowerment provides the foundation for people to develop autonomy; to take action, responsibility, and accountability; and to have the room necessary […]

Was ist Social Engineering?
Mit Social-Engineering-Techniken manipulieren Cyberkriminelle die menschliche Psyche. Lesen Sie, wie das funktioniert und wie Sie sich schützen können. sp3n | shutterstock.com Selbst wenn Sie bei der Absicherung Ihres Rechenzentrums, Ihrer Cloud-Implementierungen und der physischen Sicherheit Ihres Firmengebäudes alle Register ziehen – mit Hilfe von Social Engineering finden gewiefte Cyberkriminelle meistens einen Weg, diese Maßnahmen zu […]

Google: The quantum apocalypse is coming sooner than we thought
Google isn’t just responsible for the encryption of a big chunk of the communications on the internet. It is also building its own quantum computers, so it’s well placed to evaluate how close the technology is to fruition. Until now, the company has been aligned with the NIST timeline, which specifies 2030 for deprecating quantum-unsafe […]

The CISO’s guide to responding to shadow AI
Move over shadow IT; shadow AI is the new risk on the scene. The explosion of available AI tools, leadership’s enthusiasm for the new technology, the push for employees to do more with less, nascent governance and the sheer speed at which AI is evolving has created the perfect environment for shadow AI to flourish. […]

Databricks pitches Lakewatch as a cheaper SIEM — but is it really?
Databricks has previewed a new open agentic Security Information and Event Management software (SIEM) named Lakewatch that signals its first deliberate step beyond data warehousing into security analytics. The data warehouse-provider is pitching Lakewatch as a lower-cost alternative to traditional security tools, arguing that consolidating security analytics into its data platform can reduce overall spend. […]

GitHub phishers use fake OpenClaw tokens to drain crypto wallets
Threat actors are actively exploiting OpenClaw’s viral popularity to run a phishing campaign that targets developers on GitHub with lures of free crypto tokens. According to a disclosure by OX Security, the campaign involves fake “CLAW” token airdrops that promise thousands of dollars in rewards. Developers are being tricked into malicious GitHub repositories and discussions, […]

10 essenzielle Maßnahmen für physische Sicherheit
Wenn physische Security nur immer so simpel umzusetzen wäre… Foto: Leremy | shutterstock.com Obwohl CISOs im Allgemeinen eher selten mit dem gesamten Spektrum der Gesundheits- und Arbeitssicherheitsbelange betraut sind, spielen sie diesbezüglich doch eine wichtige, strategische Rolle – insbesondere, wenn es um physische Sicherheitssysteme mit IT-Anbindung und den direkten Zugang zu IT-Assets geht. Die wesentlichen […]

New critical Citrix NetScaler hole of similar severity to CitrixBleed2, says expert
A new critical vulnerability that is similar to the widely-exploited CitrixBleed and CitrixBleed2 holes should be patched in NetScaler devices immediately, say experts. The hole, CVE-2026-3055, is an out-of-bounds read vulnerability in customer-managed NetScaler ADC and NetScaler Gateway devices configured as SAML IDP for approving identity and authentication. It’s rated at 9.3 in severity on […]

Chained vulnerabilities in Cisco Catalyst switches could induce denial-of-service
Cisco’s widely deployed Catalyst 9300 Series enterprise switches have four security vulnerabilities, two of which could be chained to cause a denial-of-service outage, infrastructure security company Opswat has revealed. The two most operationally significant are CVE-2026-20114 and CVE-2026-20110, which the researchers found could be chained to make possible a dangerous privilege escalation. Opswat’s Unit 515 […]

Trivy supply chain breach compromises over 1,000 SaaS environments, Lapsus$ joins the extortion wave
What started as a supply chain attack on Trivy, a widely used security scanner, has become a Lapsus$-linked extortion campaign, with more than 1,000 enterprise SaaS environments already compromised. Charles Carmakal, CTO of Mandiant Consulting, made the assessment at a Google-hosted threat briefing held alongside the RSA Conference 2026 in San Francisco on Tuesday. “We […]

PyPI warns developers after LiteLLM malware found stealing cloud and CI/CD credentials
PyPI is warning of possible credential theft from AI applications and developer pipelines after two malicious versions of the widely used Python middleware for large language models, LiteLLM, were briefly published. “Anyone who has installed and run the project should assume any credentials available to the LiteLLM environment may have been exposed, and revoke/rotate them […]

6 key trends reshaping the IAM market
The identity and access management (IAM) market has shifted its focus from traditional “login and MFA” mechanisms toward treating identity as a security control plane. Buyers are prioritizing phishing-resistant authentication, including passkeys, and the management of non-human identities, according to an array of experts quizzed on developments in the market by CSO. “Workforce access is […]

AI is breaking traditional security models — Here’s where they fail first
Traditionally, enterprise security operating models operated a fixed and regular cycle: Findings surfaced through periodic scans, security teams triaged results and remediation followed through ticket-based workflows. It was almost an SOP of sorts; the accountability existed, but it was often implicit and fragmented. The remediation would travel across tools, teams and handoffs rather than designed […]

Empathie trifft IT-Sicherheit: Der Weg zu gelebter Compliance
CISOs sollten Sicherheitsrichtlinien mit Blick auf die Belegschaft gestalten. earthphotostock – shutterstock.com In vielen Unternehmen stoßen IT-Sicherheitsrichtlinien auf Widerstand, da Mitarbeitende sie als hinderlich oder praxisfern empfinden. Dies erschwert die Umsetzung, untergräbt die Wirksamkeit und belastet die Zusammenarbeit zwischen der Sicherheitsabteilung und den Fachbereichen. Statt als Partner wird Cybersecurity oft als Bremser wahrgenommen – ein […]

DDoS-Angriffe haben sich verdoppelt
srcset=”https://b2b-contenthub.com/wp-content/uploads/2026/03/DDoS-Attack-COunt_16-9.png?quality=50&strip=all 2200w, https://b2b-contenthub.com/wp-content/uploads/2026/03/DDoS-Attack-COunt_16-9.png?resize=300%2C168&quality=50&strip=all 300w, https://b2b-contenthub.com/wp-content/uploads/2026/03/DDoS-Attack-COunt_16-9.png?resize=768%2C432&quality=50&strip=all 768w, https://b2b-contenthub.com/wp-content/uploads/2026/03/DDoS-Attack-COunt_16-9.png?resize=1024%2C576&quality=50&strip=all 1024w, https://b2b-contenthub.com/wp-content/uploads/2026/03/DDoS-Attack-COunt_16-9.png?resize=1536%2C864&quality=50&strip=all 1536w, https://b2b-contenthub.com/wp-content/uploads/2026/03/DDoS-Attack-COunt_16-9.png?resize=2048%2C1152&quality=50&strip=all 2048w, https://b2b-contenthub.com/wp-content/uploads/2026/03/DDoS-Attack-COunt_16-9.png?resize=1240%2C697&quality=50&strip=all 1240w, https://b2b-contenthub.com/wp-content/uploads/2026/03/DDoS-Attack-COunt_16-9.png?resize=150%2C84&quality=50&strip=all 150w, https://b2b-contenthub.com/wp-content/uploads/2026/03/DDoS-Attack-COunt_16-9.png?resize=854%2C480&quality=50&strip=all 854w, https://b2b-contenthub.com/wp-content/uploads/2026/03/DDoS-Attack-COunt_16-9.png?resize=640%2C360&quality=50&strip=all 640w, https://b2b-contenthub.com/wp-content/uploads/2026/03/DDoS-Attack-COunt_16-9.png?resize=444%2C250&quality=50&strip=all 444w” width=”1024″ height=”576″ sizes=”auto, (max-width: 1024px) 100vw, 1024px”>Die Menge der DDoS-Attacken hat sich laut Gcore 2025 in der zweiten Jahreshälfte verdoppelt. Gcore Radar Laut dem halbjährlich erscheinenden Radar-Report des luxemburgischen Softwareanbieters Gcore haben sich […]

HP launches TPM Guard to help defeat physical TPM attacks
The Trusted Platform Module (TPM), developed by the Trusted Computing Group (TCG), is a mandatory security component in any computer running Windows 11. It stores sensitive information such as encryption keys in a separate, secure chip, passing it to the CPU as required. However, there’s a problem. If an attacker can get physical access to […]

New ‘StoatWaffle’ malware auto‑executes attacks on developers
A newly disclosed malware strain dubbed “StoatWaffle” is giving fresh teeth to the notorious, developer-targeting “Contagious Interview” threat campaign. According to NTT Security findings, the malware marks an evolution from the long-running campaign’s user-triggered execution to a near-frictionless compromise embedded directly in developer workflows. Attackers are using blockchain-themed project repositories as decoys, embedding a malicious […]

Autonomous AI adoption is on the rise, but it’s risky
Two AI releases early this year are prompting users to give up control and let autonomous agentic tools complete tasks on their behalf. IT leaders should be ready to deal with the consequences. Anthropic rolled out its agentic platform Claude Cowork in January for macOs and February for Windows, and use of agentic tool OpenClaw […]

Streamline physical security to enable data center growth in the era of AI
AI is the new space race for data centers, and consistency at speed is the rocket fuel that colocation and hyperscale providers need to reach orbit. Everything you already know about physical security still applies but it won’t matter unless you have the right plan and partnerships in place to scale without sacrificing quality. Growth […]

Why CISOs should embrace AI honeypots
The nightmare begins with our protagonist trying to find a way inside to get to the firm’s files, but every door is bolted shut. Then they spot a back entrance and they’re in, first walking, then running down one corridor, then another, and another, feeling that they’re getting ever closer to that file and a […]

ISO und ISMS: Darum gehen Security-Zertifizierungen schief
Mit einer ISO 27001-Zertifizierung weisen Unternehmen nach, dass sie ein wirksames Informationssicherheits-Managementsystems (ISMS) betreiben. Lesen Sie, weshalb der Zertifizierungsprozess häufig schief geht. Foto: mentalmind – shutterstock.com ISO-Zertifizierungen, aber auch die Einführung eines Informationssicherheits-Managementsystems (ISMS) nach IT-Grundschutz, werden von vielen Unternehmen als Beweis für ihre Qualität und ihren professionellen Ansatz bei der Durchführung ihrer Geschäftstätigkeit angesehen. […]

Palo Alto updates security platform to discover AI agents
As CISOs worry about AI agent sprawl, Palo Alto Networks has announced an update to its Prisma AIRS security platform and enterprise browser to include the ability to discover AI agents, models, and connections across the entire IT environment, to scan agents for vulnerabilities, and to allow admins to simulate red team tests for agents. […]

Faster attacks and ‘recovery denial’ ransomware reshape threat landscape
Mandiant’s M-Trends 2026 report, released today at the RSA Conference, shows that attackers are moving faster, operating more collaboratively, and increasingly focusing on the systems organizations rely on to recover from breaches. The report, based on more than 500,000 hours of incident response engagements in 2025, finds that attackers are compressing key phases of the […]

Chrome ABE bypass discovered: New VoidStealer malware steals passwords and cookies
A new infostealer is bypassing Chrome’s Application-Bound Encryption (ABE), using a debugger-based technique researchers say hasn’t been seen in the wild before. Called “VoidStealer,” the stealer seems to have found a way around ABE, introduced in Chrome 127 in 2024, a security control aimed at locking sensitive browser data like passwords and cookies behind tighter […]

Behavioral XDR and threat intel nab North Korean fake IT worker within 10 days of hire
The North Korea fake IT worker scheme has become a pernicious threat across several industries. While best practices emphasize precautions throughout the hiring phase, once onboarded such operatives can be challenging to detect. Combinations of behavioral analytics, threat intelligence, and other points of information are taking shape as essential defenses, as a recent case attests. […]

Why US companies must be ready for quantum by 2030: A practical roadmap
Last year, I asked a room of infrastructure, identity and application leaders a simple question: “Where in our environment do we rely on RSA or elliptic curve cryptography?” The first answers were the usual suspects: TLS on the edge, our VPN and the certificates on laptops. Then we pulled up a dependency map and the […]

The insider threat rises again
Insider threats are coming back in a consequential way. According to the State of Human Risk Report from Mimecast, 42% of organizations have experienced an increase in malicious insider incidents over the past year, with 42% also reporting a rise in negligent incidents for the first time. The report further found that organizations experienced an […]

Trivy vulnerability scanner backdoored with credential stealer in supply chain attack
Attackers have compromised the widely used open-source Trivy vulnerability scanner, injecting credential-stealing malware into official releases and GitHub Actions used by thousands of CI/CD workflows. The breach could trigger a cascade of additional supply-chain compromises if impacted projects and organizations don’t rotate their secrets immediately. The attack, disclosed by Trivy maintainers today, results from an […]

Are nations ready to be the cybersecurity insurers of last resort?
A senior member of the Cyber Monitoring Center (CMC), an organization formed last year to monitor, define and classify cyber events impacting UK organizations, this week questioned whether a £1.5 billion (about $2 billion) government loan guarantee provided to Jaguar Land Rover (JLR) should have happened in the first place. Speaking at an event hosted […]

Water utilities strengthen cybersecurity through cooperation
Water utilities are finding that letting information flow can flush out cybersecurity problems. The water industry has a security issue: Many utilities operate with ageing systems and minimal IT or cybersecurity personnel. But by coordinating responses to cyber-attacks, participants in a pilot program run by the Cyber Readiness Institute (CRI) and the Center on Cyber […]

Stop using AI to submit bug reports, says Google
Google will no longer accept AI-generated submissions to a program it funded to find bugs in open-source software. However, it is contributing to a separate program that uses AI to strengthen security in open-source code. The Google Open Source Software Vulnerability Reward Program team is increasingly concerned about the low quality of some AI-generated bug […]

DDoS-Attacken: Schlag gegen internationale Cyberkriminelle
DDos bleibt ein Evergreen unter den Security-Bedrohungen. Karsten Kunert mit ChatGPT In einem großangelegten Schlag gegen ein internationales Hacker-Netzwerk haben Sicherheitsbehörden in Nordamerika und Deutschland die beiden weltgrößten Botnetze zerschlagen. Die Infrastruktur der Kriminellen war vor allem für sogenannte Denial-of-Services-Attacken (DDoS), verwendet worden, teilte das Bundeskriminalamt mit. Dabei versuchen die Cyberkriminellen, die Webseiten und Apps […]

The espionage reality: Your infrastructure is already in the collection path
Threat actors have always sought advantage over their targets. Recently we’ve seen two efforts designed for long-term intelligence gain. This activity surfaced right where you would expect inside the enterprise. Enterprises now sit directly in the adversary’s collection path. They don’t have to be the target; they are on the board and in play because […]

Die besten IAM-Tools
Identity & Access Management ist für sicherheitsbewusste Unternehmen im Zero-Trust-Zeitalter Pflicht. Das sind die besten IAM-Anbieter und -Tools. Foto: ne2pi – shutterstock.com Identität wird zum neuen Perimeter: Unternehmen verlassen sich immer seltener auf die traditionelle Perimeter-Verteidigung und forcieren den Umstieg auf Zero-Trust-Umgebungen. Sicherer Zugriff und Identity Management bilden die Grundlage jeder Cybersicherheitsstrategie. Gleichzeitig sorgt die […]

CISA urges IT to harden endpoint management systems after cyberattack by pro-Iranian group
The US is urging infosec leaders to harden their endpoint management system configurations after last week’s hack of American medical supplies provider Stryker by pro-Iranian threat actor Handala. The warning from the US Cybersecurity and Infrastructure Security Agency (CISA) is principally for organizations using Microsoft Intune, a cloud-based unified endpoint management (UEM) service that Handala, […]

That cheap KVM device could expose your network to remote compromise
Researchers have found nine vulnerabilities in four popular low-cost KVM-over-IP devices, ranging from unauthenticated command injection to weak authentication defenses and insecure firmware updates. The flaws are particularly concerning given the growing presence of such devices in business environments, whether deployed intentionally by IT administrators and managed service providers or introduced as shadow IT. KVM-over-IP […]

Ransomware group exploited Cisco firewall vulnerability as a zero day, weeks before a patch appeared
One of the world’s most active ransomware groups, Interlock, started exploiting a critical-rated Cisco firewall vulnerability as a zero day weeks before it was patched in early March, Amazon has revealed. The vulnerability in question is CVE-2026-20131, a remotely exploitable deserialization flaw in Cisco Secure Firewall Management Center (FMC) Software which was given a maximum […]

Beijing wants its own quantum-resistant encryption standards rather than adopt NIST’s
China is reportedly planning to develop its own national post-quantum cryptography standards within the next three years, even as most of the world has already begun migrating to those finalized by the US in 2024. Post-quantum cryptography deals with algorithms that can protect data from the threat proposed by future quantum computers, which are expected […]

Telnet vulnerability opens door to remote code execution as root
A critical Telnet vulnerability with a CVSS rating of 9.8 enables attackers to take full control of affected systems before authentication even kicks in, security researchers at Dream Security have warned. Tracked as CVE-2026-32746, the vulnerability is in GNU inetutils telnetd, is a widely deployed implementation of the Telnet remote access protocol found across legacy […]

SpyCloud’s 2026 Identity Exposure Report Reveals Explosion of Non-Human Identity Theft
New Report Highlights Surge in Exposed API Keys, Session Tokens, and Machine Identities, and more. SpyCloud, the leader in identity threat protection, today released its annual 2026 Identity Exposure Report, one of the most comprehensive analyses of stolen credentials and identity exposure data circulating in the criminal underground and highlighting a sharp expansion in non-human […]

5 key priorities for your RSAC 2026 agenda
RSA Conference 2026 arrives at a significant inflection point for the cybersecurity industry — one that will see its more than 43,000 attendees and 600-plus exhibitors navigating an agenda that has fundamentally shifted in character. For the first time, “AI” is not a track at RSAC. It is the event. Of the 450-plus sessions across […]

The multi-billion dollar mistake: Why cloud misconfigurations are your biggest security threat
Last year, most businesses faced a cloud security incident. Here’s what stands out — it wasn’t sophisticated cybercriminals behind these events. Instead, basic errors opened the door. According to the Cloud Security Alliance’s 2024 report on risks in cloud computing, misconfigured settings caused nearly every single breach. Just one wrong switch — that’s all it […]

Your MFA isn’t broken — it’s being bypassed, and your employees can’t tell the difference
Multi-factor authentication was supposed to be the solution. For years, security teams have told employees that MFA would keep them safe. Password stolen? No problem — attackers still need that second factor. But adversary-in-the-middle (AiTM) phishing has changed everything. These attacks do not try to steal passwords and MFA codes separately. They capture the entire […]

Anthropic ban heralds new era of supply chain risk — with no clear playbook
The Trump administration’s decision to ban AI company Anthropic from Pentagon assets and other government systems as a “supply chain risk” could force CISOs into a position few have faced before: preparing to identify, isolate, and potentially remove a specific AI technology from across their organizations without a clear understanding of where it resides or […]

Cloud Access Security Broker – ein Kaufratgeber
Lesen Sie, worauf es bei der Wahl eines Cloud Access Security Broker ankommt – und welche Anbieter was genau zu bieten haben. Jack the sparow | shutterstock.com Ein Cloud Access Security Broker (CASB) sitzt zwischen Enterprise-Endpunkten und Cloud-Ressourcen und fungiert dabei als eine Art Monitoring-Gateway. Eine CASB-Lösung: gewährt Einblicke in Benutzeraktivitäten in der Cloud, setzt […]

Reco targets AI agent blind spots with new security capability
SaaS security platform Reco has decided to address the “agent sprawl” challenge from the increased adoption of AI-driven tools by enterprises. It argues that enterprises are faced with a security situation as numerous autonomous agents now traverse multiple systems, accessing sensitive data, and executing actions without direct human oversight. To help contain this risk, the […]

BSI moniert Software-Sicherheit im Gesundheitswesen
Schwachstellen bei Praxisverwaltungssystemen hätten zu Cyberangriffen führen können. Khakimullin Aleksandr – shutterstock.com Das Bundesamt für Sicherheit in der Informationstechnik (BSI) mahnt einen besseren Schutz sensibler Gesundheitsdaten in Computer-Anwendungen von Arztpraxen, Kliniken und in der Pflege an. Die IT-Sicherheit von Softwareprodukten im Gesundheitswesen sei “ausbaufähig”, teilte das Amt nach Tests von Standardkonfigurationen verschiedener Anwendungen mit. In einem Projekt untersucht wurden […]

Can you prove the person on the other side is real?
In my role, I spend a lot of time thinking about what “trust” means when money, grief and identity collide. By 2026, the real competition in our space won’t be who automates fastest or offers the most AI features. It will be who can still tell a legitimate executor, beneficiary or family representative from a […]

ClickFix treibt neue Infostealer-Kampagnen an
ClickFix-Kampagnen werden immer raffinierter und zielen verstärkt auf WordPress-Webseiten. Gorodenkoff | shutterstock.com Cyberkriminelle kombinieren kompromittierte Websites mit immer raffinierteren Social-Engineering-Köder-Methoden, um neue Infostealer-Malware zu verbreiten. Bekannt ist das Ganze unter dem Namen ClickFix – und zudem effektiv: In einer einzigen Kampagne wurden über 250 WordPress-Websites in zwölf Ländern infiziert. Während diese Kampagne zu unauffälligen, im […]

Cybersecurity and privacy priorities for 2026: The legal risk map
Escalating cybersecurity threats and growing privacy concerns lurk around every corner these days. Evolving technology and mounting regulations continue to present both the perils and solutions. All players — public and private, organizations and individuals alike — are to conquer the next quest in this realm. In the most recent Annual Litigation Trends Survey by […]

CISOs rethink their data protection strategies
Scott Kopcha witnessed what CISOs everywhere are seeing: employees eager to use artificial intelligence, whether through public models or custom AI tools, accessing company data at a breathtaking rate and volume. Kopcha already had a mature data protection strategy in place; as a law firm, his organization had a long history of safeguarding sensitive data. […]

Die besten Hacker-Filme
Vorsicht, dieses Film-Listicle kann zu Prokrastination verführen! Nomad Soul | shutterstock.com Security-Profis und -Entscheider mit Hang zur Filmkunst müssen auch nach Feierabend nicht auf ihr Leib-und-Magen-Thema verzichten – einer Fülle cineastischer Ergüsse sei Dank. Das Film-Pflichtprogramm für Security-Profis Wir haben die unserer Meinung nach besten (Achtung: Nerd-Brille erforderlich) Hacker-Filme nachfolgend für Sie zusammengestellt – in […]

Nvidia NemoClaw promises to run OpenClaw agents securely
In the few short weeks since OpenClaw became the biggest story in agentic AI, it has been dogged by concerns that it is not secure enough to be safely let loose in enterprises. This week at the Nvidia GPU Technology Conference (GTC) conference, CEO Jensen Huang announced what he believes is the answer: NemoClaw. Built […]

Cyber-Attacken fluten Eon-Netz: Angriffe verzehnfacht
Eon trägt eine große Verantwortung für die Energieversorgung in Deutschland. nitpicker – shutterstock.com Der Energiekonzern Eon sieht eine zunehmende Zahl von Cyberangriffen auf seine Energienetze. Mittlerweile seien täglich mehrere hundert Angriffe auf die Netzinfrastuktur zu verzeichnen, berichtete Vorstandsmitglied Thomas König am Montag im Austausch mit Journalisten. Im Vergleich zu von vor fünf Jahren habe sich die Zahl damit verzehnfacht. […]

AWS Bedrock’s ‘isolated’ sandbox comes with a DNS escape hatch
AWS’ promise of “complete isolation” for agentic AI workflows on Bedrock is facing scrutiny after researchers found its sandbox mode isn’t as sealed as advertised. In a recent disclosure, BeyondTrust detailed how the “Sandbox” mode in AWS Bedrock AgentCore’s Code Interpreter can be abused to break isolation boundaries using DNS queries. While the sandbox blocks […]

Runtime: The new frontier of AI agent security
AI agents are already operating inside enterprise networks, quietly doing some of the work employees once handled themselves — writing code, drafting emails, retrieving files, and connecting to internal systems. Sometimes they also make costly mistakes. At Meta, an employee asked an AI assistant to help manage her inbox. It deleted it instead. At Amazon, […]

6 Risk-Assessment-Frameworks im Vergleich
Mit dem richtigen Framework lassen sich Risiken besser ergründen. FOTOGRIN – shutterstock.com Für viele Geschäftsprozesse ist Technologie inzwischen unverzichtbar. Deshalb zählt diese auch zu den wertvollsten Assets eines Unternehmens. Leider stellt sie gleichzeitig jedoch auch eines der größten Risiken dar – was Risk-Assessment-Frameworks auf den Plan ruft. IT-Risiken formal zu bewerten, ermöglicht es Organisationen, besser einzuschätzen, […]

Was ist ein Keylogger?
Keylogger sind Malware der alten Schule. Lesen Sie, wie die Tools zur Tastaturüberwachung funktionieren und warum sie nicht nur etwas für Cyberkriminelle sind. IM_photo | shutterstock.com Auch wenn Keylogger schon etliche Jahre auf dem Buckel haben: Sie sind immer noch beliebt und werden häufig im Rahmen großangelegter Cyberangriffe eingesetzt. Keylogger – Definition Der Begriff Keylogger […]

Open VSX extensions hijacked: GlassWorm malware spreads via dependency abuse
Threat actors are abusing extension dependency relationships in the Open VSX registry to indirectly deliver malware in a new phase of the GlassWorm supply-chain campaign. Researchers at Socket said they have identified at least 72 additional malicious Open VSX extensions linked to the campaign since January 31, 2026. The extensions appear to target developers by […]

Nine critical vulnerabilities in Linux AppArmor put over 12M enterprise systems at risk
Security researchers at Qualys have disclosed nine vulnerabilities in AppArmor, the Linux Security Module that ships enabled by default across Ubuntu, Debian, and SUSE distributions. An unprivileged local attacker can exploit the flaws to gain full root access, break out of container isolation, and crash systems, all without requiring administrative credentials, the researchers said in […]

ClickFix techniques evolve in new infostealer campaigns
Cybercriminals are combining compromised websites with increasingly sophisticated ClickFix social engineering lures to deliver new infostealer malware, with one campaign alone weaponizing more than 250 WordPress sites across 12 countries. The campaign leads to stealthy in-memory payloads, while a separate attack detected by Microsoft targets Windows Terminal for payload execution instead of the traditional Run […]

GenAI-Security als Checkliste
Das Open Web Application Security Project (OWASP) gibt Unternehmen eine Checkliste für (mehr) GenAI-Sicherheit an die Hand. Foto: Gannvector | shutterstock.com Während Unternehmen wie OpenAI, Anthropic, Google oder Microsoft aber auch Open-Source-Alternativen bei ihren Generative-AI– und Large-Language-Model-Angeboten exponentielle User-Zuwächse verzeichnen, sind IT-Sicherheitsentscheider bemüht, mit der rasanten KI-Entwicklung in ihren Unternehmen Schritt zu halten. Die Non-Profit-Organisation […]

Google warns of two actively exploited Chrome zero days
Threat actors are exploiting two high severity zero day vulnerabilities in the Chrome browser that experts say IT teams must patch immediately. Google has issued emergency patches for the two holes, CVE-2026-3909 and CVE-2026-3910. This comes just days after the release of 29 fixes for holes as part of March Patch Tuesday, and a zero day […]

Cyber criminals too are working from home… your home
The FBI is so concerned about the threat of residential proxy attacks and the dangers posed by cyber criminals using the technique that it has posted guidance on its website. Residential proxies are used by cybercriminals to reroute traffic between individuals and the websites they visit to make it appear to originate elsewhere? By taking […]

Veeam warns admins to patch now as critical RCE flaws hit Backup & Replication
Backup vendor Veeam has released security updates to patch multiple vulnerabilities in its widely used Backup and Replication platform, including three critical flaws that could allow authenticated users to execute code on backup servers. Detailed in the company’s advisory KB4830, the vulnerabilities affect Veeam Backup & Replication 12.3.2.4165 and earlier version 12 builds, with fixes […]

Hybrid resilience: Designing incident response across on-prem, cloud and SaaS without losing your mind
I used to think hybrid incidents would get easier once we standardized on “one tool”: one monitoring platform, one ticketing system, one on-call process. After a few real outages, I changed my mind. Hybrid response fails at the seams between ownership models: on-prem teams, cloud teams, security, vendors. Each group can be correct inside its […]

Storm-2561 targets enterprise VPN users with SEO poisoning, fake clients
Microsoft has warned enterprises that cybercriminal group Storm-2561 is hijacking search engine results to serve trojanized VPN clients, stealing corporate credentials, and then covering its tracks before victims suspect anything is wrong. The group pushes spoofed websites to the top of results for queries such as “Pulse VPN download” or “Pulse Secure client,” redirecting users […]

The cyber perimeter was never dead. We just abandoned it.
Industry has comforted itself with the idea that the perimeter is dead. It is not. What happened is far worse. We ignored the edge, let unsupported hardware decay in place, and effectively donated our perimeter to adversaries who were more than willing to accept it. The FBI’s Winter SHIELD effort is the operational side of […]

10 Kennzahlen, die CISOs weiterbringen
Geht es um Security-Kennzahlen, sollten CISOs sich auf das Wesentliche fokussieren. Foto: Vadym Nechyporenko – shutterstock.com Die Security-Performance zu messen, gehört vielleicht nicht zu den aufregendsten Aufgaben eines CISOs – kann allerdings sehr nützlich sein, um eine ganze Reihe von Herausforderungen zu bewältigen. Neben der Erkenntnis darüber, wie effektiv ihre Security-Bemühungen sind, können Sicherheitsentscheider mit […]

Telus Digital hit with massive data breach
Telus Digital, which provides business process outsourcing (BPO) services to a range of organizations worldwide, has been hit with a massive cyberattack conducted by extortion group ShinyHunters The group, which has been in operation since 2020, specializes in stealing data from Salesforce and other SaaS vendors, and has also recently been conducting voice phishing (vishing) […]

Medical giant Stryker crippled after Iranian hackers remotely wipe computers
A major cyberattack on US medical supplies giant Stryker has resulted in thousands of devices being remotely wiped, after a pro-Iranian hacking group may have compromised the company’s Microsoft Intune management system. Details remain sketchy, but what appears to have happened on Wednesday at one of the world’s largest medical supplies companies could, if confirmed, […]

PhantomRaven returns to npm with 88 bad packages
Last year’s “PhantomRaven” supply-chain campaign is back, with security researchers uncovering 88 new malicious packages in what they describe as the second, third, and fourth waves of the operation. According to Endor Labs findings, the newly discovered packages were published between November 2025 and February 2026, with 81 of them still available on npm along […]

North Korean fake IT worker tradecraft exposed
Research from GitLab has exposed the latest tradecraft behind North Korean fake IT worker scams. GitLab banned 131 North Korean-attributed accounts last year, most of which involved JavaScript repositories that acted as resources in the so-called Contagious Interview campaign. In most cases, GitLab projects acted as obfuscated loaders for malware payloads — such as BeaverTail […]

AI use is changing how much companies pay for cyber insurance
In July 2025, McDonald’s had an unexpected problem on the menu, one involving McHire, its AI-powered platform used to recruit and screen job applicants. The system, developed by Paradox.ai, featured a rookie-level security flaw: the backend for restaurant operators accepted “123456” as both username and password, and lacked multi-factor authentication. As a result, the personal […]

“Zombie ZIP”: Neue Angriffstechnik täuscht Virenscanner
Mithilfe sogenannter Zombie-ZIPs lassen sich fast alle Virenscanner austricksen. Pressmaster | shutterstock.com Eine neue Technik mit dem Namen „Zombie ZIP“ ist in der Lage, Payloads in komprimierten Dateien zu verbergen. Sicherheitslösungen wie Antiviren- und EDR-Produkte (Endpoint Detection and Response) können sie nicht entdecken, denn die digitalen Untoten wurden speziell geschaffen, um die Security zu umgehen. […]

Wie CISOs schlechte Angebote enttarnen
Drum prüfe… Ground Picture | shutterstock.com Security-Anbietern stehen viele Wege offen, um CISOs und Sicherheitsentscheider mit Lobpreisungen und Angeboten zu ihren jeweils aktuellen Produkten und Lösungen zu penetrieren. Und die nutzen sie auch: Manche Sicherheitsverantwortliche erhalten mehr als 30 solcher Anfragen pro Woche – per Telefon, E-Mail oder auch über LinkedIn. Um erkennen zu können, […]

Resumés with malicious ISO attachments are circulating, says Aryaka
Threat actors are still having success tricking human resources staff into opening malware-infected phishing emails. The latest example is detailed by researchers at Aryaka, who this week described a campaign by an unnamed threat actor who is distributing resumés containing a malicious ISO file to HR departments. It’s delivered through recruitment channels, and hosted on […]

CISA warns of actively exploited Ivanti EPM and Cisco SD-WAN flaws
The US Cybersecurity and Infrastructure Security Agency (CISA) has warned that an authentication bypass vulnerability patched in Ivanti Endpoint Manager (EPM) last month is now being exploited in the wild. The agency has also updated its directive related to two Cisco Catalyst SD-WAN flaws that were also fixed last month after being used in zero-day […]

AWS expands Security Hub for multicloud security operations
Amazon Web Services is expanding AWS Security Hub to function as a centralized security operations platform capable of aggregating risk signals across multicloud environments. With the updated Security Hub, the company said it will introduce a unified operations layer that provides security teams with near real-time risk analytics, automated analysis, and prioritized insights. As enterprise […]

Overly permissive ‘guest’ settings put Salesforce customers at risk
Salesforce is urging its customers to review their Experience Cloud ‘guest’ configurations as cybercrime group ShinyHunters claims a new campaign involving data theft and extortion tied to exposed Salesforce environments. The group recently posted screenshots on its leak site claiming breaches of “several hundreds” of organizations, including around 400 websites and roughly 100 “high profile […]

Did cybersecurity recently have its Gatling gun moment?
On the James River, Petersburg, VA, June of 1864, during the American Civil War, General Benjamin Butler, of the US Army, deployed a new weapon into the field that effectively altered the nature of kinetic battles. The later named “Siege of Petersburg,” was the first recorded instance of the Gatling gun being used in battle. […]

Why zero trust breaks down in IoT and OT environments
Zero trust solves the wrong problem in OT Zero trust has become the dominant security narrative of the past decade, and rightly so. Its core principles, never trust, always verify; assume breach; enforce least privilege, have reshaped how organizations think about identity, access and lateral movement. In enterprise IT environments, these principles have produced measurable […]

Critical flaw in HPE Aruba CX switches lets attackers seize admin control without credentials
HPE Aruba Networking has released patches for five vulnerabilities in its AOS-CX switch software, the most severe of which could let a remote attacker take administrative control of enterprise network switches without any credentials. The critical flaw, CVE-2026-23813, scored 9.8 out of 10 on the CVSSv3.1 scale. According to a security advisory HPE published on […]

Announcing the 2026 CSO Hall of Fame honorees
Now entering its eighth year, the CSO Hall of Fame spotlights outstanding leaders who have significantly contributed to the practice of information risk management and security. This award honors trailblazers (security leaders with 10+ years in a CSO, CISO or other C-level security position) whose careers have shaped the future of cybersecurity and risk management. […]

CSO Awards 2026 celebrates world-class security strategies
For more than a decade, the CSO Awards have recognized security projects that demonstrate outstanding thought leadership and business value. The award is an acknowledged mark of cybersecurity excellence. “This year’s award winners show how security teams have repositioned themselves as strategic business enablers,” Beth Kormanik, Content Director of the CSO Cybersecurity Awards & Conference said in a statement. “They tackle […]

A 5-step approach to taming shadow AI
AI is being leveraged across organizations to boost productivity, accelerate innovation and optimize business processes. The problem is that adoption has outpaced discipline. Only a minority (23.8%) of organizations have formal AI risk frameworks in place, which is precisely how unauthorized, “shadow AI” takes root, leading to untracked data exposure, compliance friction and poor decisions […]

12 ways attackers abuse cloud services to hack your enterprise
Attackers are increasingly abusing trusted SaaS platforms, cloud infrastructure, and identity systems to blend malicious activity into legitimate enterprise traffic. Adversaries are pushing command and control (C2) through high-reputation services, including OpenAI and AWS, to blend in with normal business traffic and evade blocklists. The shift from “living off the land” to “living off the […]
6 Mittel gegen Security-Tool-Wildwuchs
loading=”lazy” width=”400px”>Viel hilft nicht immer viel. Roman Samborskyi | shutterstock.com Auf der Suche nach Möglichkeiten, sich vor ständig wachsenden Cyberbedrohungen zu schützen, erliegen nicht wenige Unternehmen einem regelrechten Security-Tool- und -Service-Kaufrausch. Kommen noch Abteilungssilos und regelmäßige Übernahmen hinzu, steigt die Chance, dass Sicherheitsentscheider mit Tool-Wildwuchs konfrontiert werden. Diesen zu reduzieren, liegt nicht nur aus Kostengründen […]

Devs looking for OpenClaw get served a GhostClaw RAT
A malicious npm package posing as an OpenClaw Installer has been caught deploying a remote access trojan (RAT) on victim machines, according to new JFrog research. The package, published under the name “@openclaw-ai/openclawai”, pretends to be an installer for the legitimate CLI tool but instead launches a multi-stage infection chain that steals system credentials, browser […]

The OT security time bomb: Why legacy industrial systems are the biggest cyber risk nobody wants to fix
When I first secured a production line, part of the control system was still running on an unpatched Windows XP machine tucked under a lab table — right next to the state-of-the-art GMP manufacturing setup that produced millions in value every day. Everyone knew that the system was a risk, but no one was willing […]

OpenAI to acquire Promptfoo to strengthen AI agent security testing
OpenAI said it plans to acquire AI testing startup Promptfoo, a move aimed at strengthening security checks for AI agents as enterprises move toward deploying autonomous systems in business workflows. Promptfoo’s tools allow developers to test LLM applications against adversarial prompts, including prompt injection and jailbreak attempts, and to evaluate whether models follow safety and […]

Why access decisions are becoming the weakest link in identity security
In my nearly two decades leading identity and risk programs, I’ve learned a sobering truth that every CISO eventually confronts: hackers don’t hack in — they log in. We often obsess over the perimeter and the sophistication of technical exploits, but many of the most damaging security failures I’ve witnessed didn’t involve a zero-day or […]
I replaced manual pen tests with automation. Here’s what I learned.
More accreditation and compliance requirements have been added in response to cyber incidents. While these frameworks play an important role in establishing security baselines, true security is more than just achieving a perfect compliance score. As I often say, “policies and procedures won’t stop an attacker, they’ll just have more documents to exfiltrate when they […]

NIS-2: Tausende reißen BSI-Frist und riskieren Strafen
Das deutsche Gesetz zur Umsetzung der NIS-2-Richtlinie ist am 6. Dezember 2025 in Kraft getreten. konstakorhonen – shutterstock.com Welche Auswirkungen IT-Sicherheitsvorfälle für die Bevölkerung haben können, hat sich etwa gezeigt, als im vergangenen Herbst ein Flughafen-Dienstleister Opfer eines Cyberangriffs wurde. Betroffen waren mehrere Flughäfen in Europa. Der Hackerangriff legte am Flughafen Berlin-Brandenburg (BER) elektronische Systeme […]

Rogues gallery: 15 worst ransomware groups active today
Ransomware-as-a-service (RaaS) models, double extortion tactics, and increasing adoption of AI characterize the evolving ransomware threat landscape. Law enforcement takedowns of groups such as LockBit have contributed to making the ransomware marketplace more fragmented, with emergent players attempting to muscle in on the action. Attackers range from nation-state actors to RaaS operations, lone operators, and […]

PQC roadmap remains hazy as vendors race for early advantage
Post-quantum cryptography (PQC) has long sat on the periphery of enterprise security, with experts calling it inevitable but not urgent. That posture is beginning to shift. Earlier this year, Palo Alto Networks published a blog announcing a new “quantum-safe security” initiative, framing it as a way for enterprises to assess where quantum-vulnerable cryptography exists across […]

Tarnung als Taktik: Warum Ransomware-Angriffe raffinierter werden
Statt eines kurzen, aber sehr schmerzhaften Stiches setzen Cyberkrimelle zunehmend darauf, sich in ihren Opfern festzubeißen und beständig auszusaugen. mycteria – shutterstock.com Ransomware-Angreifer ändern zunehmend ihre Taktik und setzen vermehrt auf unauffällige Infiltration. Dies liegt daran, dass die Drohung mit der Veröffentlichung sensibler Unternehmensdaten zum Hauptdruckmittel bei Erpressungen geworden ist. Der jährliche Red-Teaming-Bericht von Picus […]

Trump’s cyber strategy emphasizes offensive operations, deregulation, AI
The White House released President Donald Trump’s long-awaited cybersecurity strategy, a lean seven-page blueprint that breaks from past approaches by placing offensive cyber operations at the center of US policy. Developed by the Office of the National Cyber Director (ONCD), the strategy emphasizes disrupting adversaries, deregulating industry, and accelerating the adoption of artificial intelligence while […]

ClickFix attackers using new tactic to evade detection, says Microsoft
Threat actors are trying a different tactic to sucker employees into falling for ClickFix phishing attacks that install malware, says Microsoft. Rather than asking potential victims to copy and paste a (malicious) command into the Run dialog, launched by hitting the Windows button plus the letter R, they are being told to use the Windows […]

Only 30 minutes per quarter on cyber risk: Why CISO-board conversations are falling short
Cybersecurity is, as it should be in this era of AI-driven cyberattacks, a regular item on enterprise board agendas. However, the ways in which CISOs and boards interact, and the depth of those discussions, remain brief and superficial. According to a new report from IANS, Artico Search, and The CAP Group, CISO-board interactions remain short […]

FBI wiretap system tapped by hackers
The US Federal Bureau of Investigation (FBI) has identified a suspected incident on a network used to manage wiretaps and foreign intelligence surveillance warrants, CNN reported. The FBI acknowledged the incident in a statement to CNN, saying, “The FBI identified and addressed suspicious activities on FBI networks, and we have leveraged all technical capabilities to […]

OAuth vulnerability in n8n automation platform could lead to system compromise
A weakness in the configuration of OAuth credentials opens up a stored XSS vulnerability in the n8n automation platform, researchers at Imperva have discovered. Setting up OAuth allows n8n to connect to services such as Google Workspace, Microsoft 365, Slack, or GitHub without having to expose service passwords. This is core to automation platforms like […]

Targeted advertising is also targeting malware
Online ads are increasingly being used a means of introducing malware into organizations, according to The Media Trust. “Malvertising surpassed both email and direct hacks as the leading vector for malware delivery worldwide,” said Chris Olson, CEO of The Media Trust, an ad scanning and filtering company with, perhaps, a vested interest in playing up […]

Teenage hacker myth primed for a middle-age criminal makeover
The Hollywood image of criminal hackers being largely teenage ne’er do wells is due for an update. That’s because profit-seeking career criminals — often approaching middle age — make up the largest cohort of today’s cybercriminals, according to an analysis of criminal cases carried out by Orange Cyberdefence. The Orange Group’s cybersecurity unit analysed 418 […]

Challenges and projects for the CISO in 2026
Sophisticated attacks and the incorporation of AI tools, talent shortages, and tight budgets are some of the challenges commonly cited when it comes to managing cybersecurity in organizations. In a changing environment, the key is no longer to stay one step ahead, but to maintain a resilient infrastructure that ensures a rapid response when — […]

Zero-day exploits hit enterprises faster and harder
Google tracked 90 vulnerabilities exploited as zero-days last year, with Chinese cyberespionage groups doubling their count from 2024 and commercial surveillance vendors overtaking state-sponsored hackers for the first time. Nearly half of the recorded zero-days targeted enterprise technologies such as security appliances, VPNs, networking devices, and enterprise software platforms. “Increased exploitation of security and networking […]

7 Anzeichen für akuten MSSP-Bedarf
Managed Security Service Provider können das Sicherheitsniveau nachhaltig steigern. Godlikeart | shutterstock.com Ein Managed Security Service Provider (MSSP) bietet seinen Kunden ein umfassendes Spektrum an Sicherheits-Services. Als Drittanbieter kann ein MSSP die Arbeitsbelastung der internen IT-Teams deutlich reduzieren und Zeit freisetzen, um sich mit essenziellen Unternehmensprozessen und strategischen Überlegungen auseinanderzusetzen. Darüber hinaus kann ein MSSP […]

Europa im Visier von Cyber-Identitätsdieben
Deutsche Unternehmen müssen sich warm anziehen: Sowohl staatliche als auch „private“ Akteure haben es auf sie abgesehen. Shutterstock Wie die Experten von Darktrace in ihrem aktuellen Threat Report 2026 darstellen, bleiben Cloud- und E-Mail-Konten das Einfallstor Nummer Eins in Europa. Dem Bericht zufolge begannen im vergangenen Jahr in Europa 58 Prozent der Attacken mit kompromittierten […]

LeakBase marketplace unplugged by cops in 14 countries
The LeakBase cyberforum, considered one of the world’s largest online marketplaces for cybercriminals to buy and sell stolen data and cybercrime tools, has been seized by the US, and arrests have also been made in other countries. The US Department of Justice said Thursday that earlier this week, law enforcement agencies in 14 countries took […]

Cisco issues emergency patches for critical firewall vulnerabilities
Cisco has handed security teams one of the largest ever patching workloads affecting its firewall products, including fixes for two ‘perfect 10’ vulnerabilities in the company’s Secure Firewall Management Center (FMC) Software. Overall, the March 4 release, the first of its semiannual firewall updates for 2026, addresses 25 security advisories covering 48 individual CVEs. The […]

Coruna iOS exploit kit moved from spy tool to mass criminal campaign in under a year
Google’s threat intelligence researchers have identified a sophisticated exploit kit targeting iPhones that was first used by a commercial surveillance vendor’s customer before being repurposed by a suspected Russian espionage group and then by Chinese cybercriminals, highlighting what researchers describe as an active secondary market for high-end zero-day exploits. “How this proliferation occurred is unclear, […]

Europol: Großer Markt für gestohlene Daten geschlossen
Europol koordinierte den Schlag gegen Leakbase. PixelBiss – shutterstock.com Die Polizei von Amsterdam hat im Zuge einer internationalen Aktion laut Europol einen der weltweit größten Handelsplätze für gestohlene Daten geschlossen. Leakbase hatte weltweit 142.000 registrierte Nutzer, wie die europäische Polizeibehörde in Den Haag mitteilte. Die Server des Marktes waren in Amsterdam. Die Daten wurden sichergestellt. […]

State-affiliated hackers set up for critical OT attacks that operators may not detect
Several state-linked threat groups known for breaking into operational technology (OT) networks have shifted their focus over the past year from gaining and maintaining access to actively mapping out ways to disrupt physical industrial processes. The shift poses a significant threat because fewer than one in 10 OT networks have monitoring in place to detect […]

14 old software bugs that took way too long to squash
In 2021, a vulnerability was revealed in a system that lay at the foundation of modern computing. An attacker could force the system to execute arbitrary code. Shockingly, the vulnerable code was almost 54 years old — and there was no patch available, and no expectation that one would be forthcoming. Fortunately, that’s because the […]

Die besten Cyber-Recovery-Lösungen
Nicht greifende Recovery-Prozesse sind für Unternehmen ein Albtraumszenario, das dank ausgefeilter Angriffe immer öfter zur Realität wird. Arjuna Kodisinghe | shutterstock.com Im Rahmen traditioneller Incident-Response– und Recovery-Prozesse wird eine Kompromittierung identifiziert und ein “Desaster” deklariert – woraufhin die betroffenen Systeme aus dem Backup wiederhergestellt werden. Diese Abläufe erfolgen größtenteils manuell und erfordern an jedem Entscheidungspunkt […]

Microsoft leads takedown of Tycoon2FA phishing service infrastructure
The infrastructure hosting the Tycoon2FA service, which Europol said was among the largest phishing operations worldwide, has been taken down by a coalition of IT companies and law enforcement agencies. At least temporarily, this removes access to one more tool for evading multifactor authentication defenses from threat actors. Europol, which coordinated the operation, said Wednesday […]

Why AI, Zero Trust, and modern security require deep visibility
AI. Automation. Zero Trust. They dominate every security strategy document. But there’s a truth sitting underneath all three: none of them work without deep, trustworthy visibility. You can’t continuously verify identities without knowing how they behave. You can’t train AI on incomplete data and expect accurate detection. You can’t automate response if every decision is built […]

The 10-hour problem: How visibility gaps are burning out the SOC
Security teams aren’t drowning because the threats improved. They’re drowning because the visibility got worse. The October 2025 commissioned Forrester Consulting study conducted on behalf of NETSCOUT surfaces a problem that every analyst already knows: 61% of survey respondents say their analysts spend more than ten hours a week in the “analyze” phase alone. This isn’t […]

Iranian cyberattacks fail to materialize but threat remains acute
Five days into US and Israel’s war with Iran, the worst predictions for cyber-retaliation have yet to materialize. But Iran has built one of the world’s most active cyber operations, which means this is likely a temporary reprieve, experts warn. At the weekend, both the UK National Cyber Security Centre (NCSC) and the Canadian Centre […]

Anthropic AI ultimatums and IP theft: The unspoken risk
Two recent high-profile events concerning Anthropic’s Claude AI underscore a little-discussed risk at the heart of the enterprise’s rush to capitalize on leading AI capabilities. The first incident involved a China-based extraction campaign against Anthropic’s intellectual property. The second was the Trump administration’s banning of Claude for federal use after the company resisted US demands […]
How to know you’re a real-deal CSO — and whether that job opening truly seeks one
Recruiters of senior-level IT professionals often say that a truly skilled and experienced CSO is among the hardest of all IT roles to fill. The reason is due to the increased responsibility placed on these key employees, who are often part of the C-suite and may even report directly to the CEO. Unfortunately, this can […]

How to know you’re a real-deal CSO — and whether that job opening truly seeks one
Recruiters of senior-level IT professionals often say that a truly skilled and experienced CSO is among the hardest of all IT roles to fill. The reason is due to the increased responsibility placed on these key employees, who are often part of the C-suite and may even report directly to the CEO. Unfortunately, this can […]

AI-powered attack kits go open source, and CyberStrikeAI may be just the beginning
AI is making it ever easier for bad actors to launch attacks, and a newly-identified open source platform, CyberStrikeAI, seems to be lowering the bar even further. The platform packages end-to-end attack automation into a single AI-native orchestration engine, and is linked to the threat actor behind the recent campaign that breached hundreds of Fortinet […]

Studie: Hacker legen Betrieb bei vielen Unternehmen lahm
Hacker hatten auch 2025 deutsche Unternehmen im Visier. Studio-M – shutterstock.com Hacker haben im vergangenen Jahr bei vielen Unternehmen in Deutschland Schäden angerichtet. Das zeigt eine repräsentative Befragung des Zentrums für Europäische Wirtschaftsforschung (ZEW) aus Mannheim, die der Deutschen Presse-Agentur vorliegt. In der Informationswirtschaft, die unter anderem IT- und Mediendienstleister umfasst, gab ungefähr jedes siebte […]

Epic Fury introduces new layer of enterprise risk
Operation Epic Fury — the US administration’s sustained kinetic pressure on core Iranian regime assets — introduces a new layer of operational risk for every multinational with people, assets, or dependencies in the Middle East region and beyond. The immediate briefings from Washington — early damage assessments, stated intent, geopolitical framing, and situational updates and […]

7 factors impacting the cyber skills gap
Individuals with strong cybersecurity skills are in high demand. That’s no secret. What’s most important is the fact that the shortage is preventing many enterprises from building sustainable cybersecurity talent pipelines. According to World Economic Forum statistics, only 14% of organizations are confident they have the people and skills required to meet their cybersecurity objectives. […]

Das gehört in Ihr Security-Toolset
Lesen Sie, welche Werkzeuge essenziell sind, um Unternehmen gegen Cybergefahren abzusichern. Gorodenkoff | shutterstock.com Sicherheitsentscheider sind mit einer sich kontinuierlich verändernden Bedrohungslandschaft, einem zunehmend strengeren, regulatorischen Umfeld und immer komplexeren IT-Infrastrukturen konfrontiert. Auch deshalb wird die Qualität ihrer Sicherheits-Toolsets immer wichtiger. Das Problem ist nur, dass die Bandbreite der heute verfügbaren Cybersecurity-Lösungen überwältigend ist. Für […]

Vulnerability monitoring service secures public-sector websites faster
An automated scanning system has cut the time it takes to fix cybersecurity vulnerabilities across public sector IT systems, reducing median remediation time for general cyber vulnerabilities from 53 days to 32, and slashing DNS-specific average fix times from 50 days to eight. The results come from the UK government’s newly launched vulnerability monitoring service […]

Innovation without exposure: A CISO’s secure-by-design framework for business outcomes
The brief for security leaders has changed. It used to be enough to reduce risk and keep the lights on. Now you are expected to enable AI adoption, connect more “things” to the network, modernize cloud at pace and still demonstrably reduce exposure, often without the comfort of ever-expanding budgets. In that environment, innovation is […]

A scorecard for cyber and risk culture
Have you once watched a leadership team clap for their “security culture month” like they’d landed a rover? Posters everywhere. Quizzes. A prize draw. Someone baked cupcakes with padlocks iced on top. Cute. Two weeks later, a product manager asked an engineer to “just share the admin credentials for an hour” because the vendor demo […]

Hacker erpressen weniger Lösegeld
immer mehr betroffene Unternehmen und Organisationen folgen dem Rat, kein Lösegeld zu zahlen . fadfebrian – shutterstock.com Laut einem neuen Bericht des Analyseunternehmens Chainalysis konnten Hacker im Jahr 2025 im Zusammenhang mit Ransomware-Angriffen insgesamt 820 Millionen Dollar erbeuten. Auch wenn die Summe hoch ist, im Vergleich zum Vorjahr ist sie damit um 28 Prozent gesunken. […]

How CISOs can build a resilient workforce
With ongoing skills gaps, AI reshaping roles and workforce stress as standing concerns for many CISOs, ensuring the resilience of the workforce has become top of mind. But due to budget constraints, return to office mandates and teams struggling to keep up with the threat landscape, CISOs are faced with a real challenge. Stephen Ford, […]

Im Fokus: RZ-Modernisierung

Im Fokus: RZ-Modernisierung

Kubernetes Security: Wie Sie Ihre Cluster (besser) absichern
Anatoliy Eremin | shutterstock.com Kubernetes hat sich unter Enterprise-Softwareentwicklern zu einem durchschlagenden Erfolg entwickelt. Das veranlasst kriminelle Hacker zunehmend dazu, entsprechende Installationen mit speziell entwickelten Exploits anzugreifen. Dabei werden die Bedrohungsakteure immer besser darin, ihre Schadsoftware zu verstecken, (triviale) Sicherheitskontrollen zu umgehen und sich lateral durch Netzwerke zu bewegen, um weiteren Schaden anzurichten. Wie die […]

Security hole could let hackers take over Juniper Networks PTX core routers
Network admins with Juniper PTX series routers in their environments are being warned to patch immediately, because a newly-discovered critical vulnerability could lead to an unauthenticated threat actor running code with root privileges. The hole is “especially dangerous, because these devices often sit in the middle of the network, not on the fringes,” said Piyush […]

‘Silent’ Google API key change exposed Gemini AI data
Google Cloud API keys, normally used as simple billing identifiers for APIs such as Maps or YouTube, could be scraped from websites to give access to private Gemini AI project data, researchers from Truffle Security recently discovered. According to a Common Crawl scan of websites carried out by the company in November, there were 2,863 […]

One of the ‘most influential cybersecurity’ roles will pay under $175,000
A recent job ad is causing plenty of head-shaking, suggesting that some government high-ups appear to be out of touch with the current state of the cybersecurity job market. There is plenty of evidence that the world needs cybersecurity talent. According to a recent ISC2 survey, 33% of organizations cannot staff their security teams adequately […]
Your personal OpenClaw agent may also be taking orders from malicious websites
If you thought running an AI agent locally kept it safely inside your machine’s walls, you’re in for a surprise. Researchers at Oasis Security have disclosed a flaw chain that allowed a malicious website to quietly connect to a locally running OpenClaw agent and take full control. The issue stems from a fundamental assumption baked […]

US authorities punish sellers of malware and spyware
The US authorities have made it clear that they will have no truck with any individuals trying to by-pass regulations on trading cyberweapons with hostile powers. Selling sensitive cyber-exploit components to a Russian company landed Australian citizen Peter Williams with an 87-month prison sentence from the US District Court for the District of Columbia on […]

Why application security must start at the load balancer
For a long time, I thought of the load balancer as a performance device. Its job was to distribute traffic, improve uptime, and make applications feel fast. Security was something that happened elsewhere, on firewalls, inside WAFs or deep in the application code. That perspective changed early in my consulting career. I worked with a […]
Enterprise Spotlight: Data Center Modernization

How to make LLMs a defensive advantage without creating a new attack surface
Large language models (LLMs) have arrived in security in three different forms at once: as productivity tools that sit beside analysts, as components embedded inside products and workflows and as targets that attackers can probe, manipulate and steal. That convergence is why the conversation feels messy. The same capability that can summarize an incident in […]
Enterprise Spotlight: Data Center Modernization

The CSO guide to top security conferences
There is nothing like attending a face-to-face event for career networking and knowledge gathering, and we don’t have to tell you how helpful it can be to get a hands-on demo of a new tool or to have your questions answered by experts. Fortunately, plenty of great conferences are coming up in the months ahead. […]

Ransomware groups switch to stealthy attacks and long-term access
Ransomware attackers are switching tactics in favor of more stealthy infiltration, as the threat of public exposure of sensitive corporate data is becoming the main mechanism of extortion. Picus Security’s annual red-teaming report shows attackers shifting away from loud disruption toward quiet, long-term access — or from “predatory” smash-and-grab tactics to “parasitic” silent residency. Four […]

Hacker kompromittieren immer schneller
Der Einsatz von KI-Tools macht Cyberangriffe nicht nur schneller, sondern erhöht auch die Taktzahl. Color4260 / Shutterstock Crowdstrike hat die aktuelle Ausgabe seines Global Threat Report veröffentlicht – mit mehreren bemerkenswerten Erkenntnissen. So benötigte ein Angreifer im Jahr 2025 im Schnitt nur noch 29 Minuten, um sich vollständigen Zugriff auf ein Netzwerk zu verschaffen. Damit […]

China-linked hackers used Google Sheets to spy on telecoms and governments across 42 countries
Google has disrupted a China-linked espionage group that used Google’s spreadsheet application as a covert spy tool to compromise telecom providers and government agencies across 42 countries, sending commands and receiving stolen data through it, Google’s Threat Intelligence Group (GTIG) said on Thursday. Working with Mandiant, GTIG confirmed intrusions at 53 organizations across 42 countries, […]

The farmers and the mercenaries: Rethinking the ‘human layer’ in security
There’s a phrase that’s become gospel in cybersecurity: “Employees are the last line of defense.” We’ve built an entire industry around it. Billions of dollars in security awareness programs, mandatory simulations and user-reporting workflows across endpoints, applications and collaboration tools. All predicated on a premise that sounds reasonable until you examine what we’re actually asking. […]

5 trends that should top CISO’s RSA 2026 agendas
RSA 2026 is still weeks away and the hype machine is humming. This year’s theme, “The Power of Community,” is somewhat ironic as the overwhelming chatter at the Moscone Center in San Francisco from March 23 to March 26 will be about AI agents, not humans. Welcome to the cybersecurity community, agents, automatons, and robots! […]

9 unverzichtbare Open-Source-Security-Tools
Diese Open-Source-Tools adressieren spezifische Security-Probleme – mit minimalem Footprint. Foto: N Universe | shutterstock.com Cybersicherheitsexperten verlassen sich in diversen Bereichen auf Open-Source-Lösungen – nicht zuletzt weil diese im Regelfall von einer lebendigen und nutzwertigen Community gestützt werden. Aber auch weil es inzwischen Hunderte qualitativ hochwertiger, quelloffener Optionen gibt, um Breaches und Datenlecks auf allen Ebenen […]

So rechtfertigen Sie Ihre Security-Investitionen
Lesen Sie, welche Aspekte entscheidend sind, um die Investitionen in die Cybersicherheit im Unternehmen zu rechtfertigen. Miha Creative – shutterstock.com In modernen Unternehmensumgebungen werden Investitionen in Sicherheitstechnologien nicht mehr nur anhand ihres technischen Reifegrades beurteilt. Die Finanzierung hängt vermehrt davon ab, inwieweit sich damit Umsatz generieren lässt, Risiken gemindert und Mehrwerte für Aktionäre geschaffen werden. […]

Steaelite RAT combines data theft and ransomware management capability in one tool
It’s bad enough that threat actors are leveraging AI for their attacks, but now they can also access a new remote access trojan (RAT) that makes it easy to launch data theft and ransomware attacks on Windows computers from a single management pane. The tool is called Steaelite, and according to researchers at BlackFog, it’s […]

Five Eyes issue emergency directive on exploited Cisco SD-WAN zero-day
Cybersecurity agencies across the Five Eyes alliance have issued an emergency directive warning that a critical Cisco SD-WAN vulnerability is being actively exploited to gain unauthorized access to federal networks. Officials confirmed that threat actors are targeting core SD-WAN control systems —infrastructure that manages traffic across government and enterprise networks — and urged organizations to […]

Microsoft warns of job‑themed repo lures targeting developers with multi‑stage backdoors
Microsoft says it has uncovered a coordinated campaign targeting software developers through malicious repositories posing as legitimate Next.js projects and technical assessments. The campaign employs carefully crafted lures to blend into routine workflows, such as cloning repositories, opening projects, and running builds, thereby allowing the malicious code to execute undetected. Telemetry collected during an incident […]

Ukrainian convicted for helping fake North Korean IT workers
A Ukrainian man has been sentenced to five years in prison after helping North Korean IT workers infiltrate American companies using stolen identities, reports Bleepingcomputer. The 39-year-old man from Kiev pleaded guilty in November 2025 to charges including aggravated identity theft and conspiracy to commit fraud. He has also agreed to surrender assets worth over […]

Boards don’t need cyber metrics — they need risk signals
Security teams live in a world of numbers. Dashboards depict counts of blocked attacks, phishing clicks, vulnerabilities discovered, patches applied, alerts triaged, and incidents closed. Over the past decade, the cybersecurity industry has become adept at measuring activity with increasing precision. Experts say what remains far less consistent is whether those measurements help boards govern […]

So verändert KI Ihre GRC-Strategie
Rob Schultz / Shutterstock Da Unternehmen Cybersicherheit in ihre GRC (Governance, Risk & Compliance)-Prozesse integrieren, müssen bestehende Programme überarbeitet werden. Nur so lässt sich sicherstellen, dass der zunehmende Einsatz und die Risiken von Generative und Agentic AI Berücksichtigung finden – und Unternehmen compliant bleiben. Die Risiken, die mit KI einhergehen, sind schwierig zu quantifizieren. Aktuelle […]

Hacker knackt 600 Firewalls in einem Monat – mit KI
Bedrohungsakteure setzen zunehmend KI-Tools ein, um ihre Angriffe durchzuführen. Shutterstock/Gorodenkoff Sicherheitsforscher von Amazon Web Services (AWS) berichten, dass es einem russischsprachigen Hacker gelungen ist, zwischen dem 11. Januar und dem 18. Februar 2026 mehr als 600 Fortigate-Firewalls zu kompromittieren. Dem Bericht zufolge wurden keine FortiGate-Sicherheitslücken ausgenutzt – stattdessen griff der Hacker zunächst Firewalls mit schwachen […]

New Serv-U bugs extend SolarWinds’ run of high-severity disclosures
SolarWinds continues to be besieged by security issues, this time in its Serv-U managed file transfer server. The software company has released four patches for critical Serv-U remote code execution (RCE) vulnerabilities that could allow attackers to gain root (administrator) access to unpatched servers. These four common vulnerabilities and exposures (CVEs) are rated “critical,” the […]

Fake Zoom meeting silently installs surveillance software, says Malwarebytes
The latest fake Zoom meeting scam silently pushes surveillance software onto the Windows computers of unwitting employees. That’s according to researchers at Malwarebytes, who warn that staff falling for the scam land in a convincing imitation of a Zoom video call. Moments later, an automatic “Update Available” countdown downloads a malicious installer, without asking permission. […]

VMware fixes command injection flaw in Aria Operations
VMware has released patches for several high- and medium-risk vulnerabilities that impact its Aria Operations, Cloud Foundation, Telco Cloud Platform, and Telco Cloud Infrastructure products. The most serious of these flaws allows unauthenticated attackers to execute arbitrary commands on the underlying OS, while another gives authenticated users the ability to elevate to administrator privileges. The […]

What does business email compromise look like?
Business email compromise (BEC) is the digital con dressed to impress. It’s clean, calculated, and ready to fool even the sharpest eyes. These scammers don’t tell on themselves with sloppy hacks. They whisper in familiar voices, posing as your CEO, HR, or a trusted vendor. And, unlike phishing, they’re a precision strike built on inside […]

What are the types of ransomware attacks?
Ransomware isn’t an isolated, potential cyber threat—it’s like a living organism that can shapeshift with multiple strains, tactics, and targets. The cybercriminals behind ransomware attacks run these operations like a business and are motivated to keep up profits at any cost. Their tactics range from quickly locking down an entire network to slowly leaking sensitive […]

Take control: Locking down common endpoint vulnerabilities
Attackers are constantly on the prowl, scoping out vulnerabilities of network-connected devices in your systems. These devices—laptops, desktops, servers, IoT, and more—are like unlocked doors waiting for threat actors to stroll through. And here’s the kicker: many of these vulnerabilities are shockingly common and easily preventable. Let’s break down the weaknesses we most frequently track […]

Bitcoin-Milliarden von Raubkopie-Portal im Visier der Justiz
Urheberrechtsverstöße sind ein einträglisches Geschäft. PXLR Studio – shutterstock.com In Leipzig hat der Prozess um den illegalen Streamingdienst «movie2k.to» und einen Milliardengewinn mit Bitcoins begonnen. Vor dem Landgericht ist der 42 Jahre alte mutmaßliche Kopf des Portals unter anderem wegen gewerbsmäßiger Geldwäsche in 146 Fällen angeklagt. Mit ihm auf der Anklagebank sitzt ein 39-Jähriger, der […]

It’s time to rethink CISO reporting lines
Despite inroads in the C-suite and rising prominence across the business at large, security leaders are still more likely to operate at a remove from the organization’s executive leadership when it comes to reporting structures. According to IANS Research and Artico Search’s 2026 State of the CISO Benchmark Report, 64% of CISOs still report into […]

The rise of the evasive adversary
Since the earliest days of the internet, there has never been a let-up in adversarial activity. According to CrowdStrike’s just-released 12th annual Global Threat Report, malicious activity in cyberspace continues to not only accelerate but also expand its scale and increasingly abuse the trust of targeted organizations. The good news is that, despite discussion of […]

Anthropic’s Claude Code Security rollout is an industry wakeup call
When Anthropic launched a “limited research preview” of its Claude Code Security offering on Friday, Wall Street investors sent the stocks of the largest cybersecurity vendors plunging. But did the Anthropic rollout warrant such a reaction? After all, those companies, including CrowdStrike, Zscaler, Palo Alto Networks and Okta, are preparing their own agentic capabilities, and […]

OT-Security: Warum der Blick auf Open Source lohnt
Auch im OT-Security-Bereich stellen Open-Source-Lösungen eine kostengünstige Alternative zu kommerziellen Tools dar. MY STOCKERS – Shutterstock.com OT-Security als strategischer Erfolgsfaktor Die zunehmende Digitalisierung und Vernetzung in der industriellen Produktion haben OT-Security (Operational Technology-Sicherheit) zu einem Kernthema in Unternehmen gemacht. Produktionsdaten, SCADA-Systeme (Supervisory Control and Data Acquisition) und vernetzte Maschinen sind in vielen Branchen essenziell – […]

Russian group uses AI to exploit weakly-protected Fortinet firewalls, says Amazon
A Russian-speaking threat actor is using commercial generative AI services to compromise hundreds of Fortinet Fortigate firewalls, warns Amazon Threat Intelligence. Once on the network, the hackers successfully compromised Active Directory at hundreds of organizations, extracted complete credential databases, and targeted backup infrastructure — a potential precursor to ransomware deployment, the report adds. The report, […]

Hacker stiehlt Daten von Tausenden RTL-Mitarbeitern
Ein Hacker hat sich Zugriff auf Mitarbeiterdaten von RTL verschafft. nitpicker – shutterstock.com Die RTL Group wurde offenbar Opfer einer Cyberattacke. Wie Cybernews berichtet, brüstet sich ein Cyberkrimineller namens LuneBF mit gestohlenen Daten von mehr als 27.000 Mitarbeitern der Mediengruppe. In seinem Darknet-Post behauptet der Angreifer, sich Zugriff auf die Intranet-Website der RTL Group verschafft […]

New Arkanix stealer blends rapid Python harvesting with stealthier C++ payloads
A newly uncovered infostealer, suspected to be built with the help of a large language model, is targeting victims with Python and C++ variants, each tailored for a different stage of data theft. Kaspersky researchers discovered a stealer dubbed “Arkanix,” which is capable of harvesting credentials, browser data, cryptocurrency, and banking assets from infected machines. […]

Attackers exploit Ivanti EPMM zero-days to seize control of MDM servers
Attackers are actively exploiting two critical zero-day vulnerabilities in Ivanti’s Endpoint Manager Mobile (EPMM) to gain unauthenticated control of enterprise mobile device management infrastructure and install backdoors engineered to persist even after organizations apply available patches. “Two critical zero-day vulnerabilities (CVE-2026-1281 and CVE-2026-1340) affecting Ivanti Endpoint Manager Mobile (EPMM) are being actively exploited in the wild, affecting […]

13 ways attackers use generative AI to exploit your systems
Artificial intelligence is revolutionizing the technology industry and this is equally true for the cybercrime ecosystem, as cybercriminals are increasingly leveraging generative AI to improve their tactics, techniques, and procedures and deliver faster, stronger, and sneakier attacks. As with legitimate use of emerging AI tools, abuse of generative AI for nefarious ends thus far hasn’t […]

Compromised npm package silently installs OpenClaw on developer machines
A new security bypass has users installing AI agent OpenClaw — whether they intended to or not. Researchers have discovered that a compromised npm publish token pushed an update for the widely-used Cline command line interface (CLI) containing a malicious postinstall script. That script installs the wildly popular, but increasingly condemned, agentic application OpenClaw on […]

Don’t trust TrustConnect: This fake remote support tool only helps hackers
After breaking into a system, crooks often install legitimate remote admin tools to keep a foothold on the network — with the risk that the tool’s vendor spots them and locks them out. Now they have a new option: a fake remote monitoring and management (RMM) tool, complete with serious-looking online storefront, built just for […]

KI und Komplexität als Brandbeschleuniger für Cyberkriminelle
Cyberangriffe werden immer schneller, wodurch sich die Zeitspanne zwischen der ersten Kompromittierung und den negativen Folgen verkürzt. andrey_l – shutterstock.com Der Einzug von KI hat den benötigten Zeitaufwand für Cyberattacken massiv verkürzt, so dass menschliche Verteidiger nicht mehr mithalten können. So lautet das vielleicht wenig überraschende Ergebnis des 2026 Global Incident Response Report von Palo […]

Sonderkommission ermittelt zu Cyberangriff auf Kunstsammlungen Dresden
Die Staatlichen Kunstsammlungen Dresden waren Ziel einer Cyberattacke. Staatliche Kunstsammlungen Dresden Nach dem Cyberangriff auf die Staatlichen Kunstsammlungen Dresden in diesem Januar hat das Landeskriminalamt Sachsen (LKA) eine Sonderkommission gegründet. Diese führe auch die Ermittlungen unter Sachleitung der Generalstaatsanwaltschaft Dresden, wie die Ermittlungsbehörde mitteilte. Weitergehende Angaben machte die Generalstaatsanwaltschaft nicht. Am 21. Januar waren die […]

PayPal launches latest struggle to get rid of SMS for MFA
When PayPal started emailing customers this month that it was backing off unencrypted SMS for multifactor authentication (MFA) at login, it came with the typical approach-avoidance asterisk. The financial services giant signaled that it was turning the page on the much-maligned authentication method while simultaneously offering no timeline and assuring customers SMS wouldn’t entirely go […]

10 Passwordless-Optionen für Unternehmen
Um Passwörter hinter sich zu lassen, gibt es bessere Lösungen. Wir zeigen Ihnen zehn. Foto: Raffi Ilham Pratama – shutterstock.com Passwörter sind seit Jahrzehnten der Authentifizierungsstandard für Computersysteme, obwohl sie sich immer wieder aufs Neue als anfällig für diverse Cyberangriffsformen erwiesen haben und kompromittierte Benutzerkonten auf regelmäßiger Basis zum Einfallstor für kriminelle Hacker werden. Ein […]

New phishing campaign tricks employees into bypassing Microsoft 365 MFA
Another device code phishing campaign that abuses OAuth device registration to bypass multifactor authentication login protections has been discovered. Researchers at KnowBe4 say the campaign is largely targeting North American businesses and professionals by tricking unwitting employees into clicking a link in an email from a threat actor. The message purports to be about a […]

US dominance of agentic AI at the heart of new NIST initiative
This week, the US National Institute of Standards and Technology (NIST) announced a new listening exercise, the AI Agent Standards Initiative, which it hopes will provide a roadmap for addressing agentic AI hurdles and, it said, ensure that the technology “is widely adopted with confidence.” AI agents, which have now ascended to the status of […]

Six flaws found hiding in OpenClaw’s plumbing
Security researchers have uncovered six high-to-critical flaws affecting the open-source AI agent framework OpenClaw, popularly known as a “social media for AI agents.” The flaws were discovered by Endor Labs as its researchers ran the platform through an AI-driven static application security testing (SAST) engine designed to follow how data actually moves through the agentic […]
Hackers can turn Grok, Copilot into covert command-and-control channels, researchers warn
Enterprise security teams racing to enable generative AI tools may be overlooking a new risk: attackers can abuse web-based AI assistants such as Grok and Microsoft Copilot to quietly relay malware communications through domains that are often exempt from deeper inspection. The technique, outlined by Check Point Research (CPR), exploits the web-browsing and URL-fetch capabilities […]