What secure digital work looks like next: Omnissa CEO takes the stage at IGEL Now & Next Miami 2026
The future of work isn’t just digital; it’s intelligent, adaptive, and secure by design. That’s the message Omnissa is bringing to Now & Next Miami 2026, where its CEO, Shankar Iyer, will take the main stage to showcase how the company’s platform is redefining what’s possible for secure, frictionless digital work. As the leader behind the industry-leading […]
‘Silent’ Google API key change exposed Gemini AI data
Google Cloud API keys, normally used as simple billing identifiers for APIs such as Maps or YouTube, could be scraped from websites to give access to private Gemini AI project data, researchers from Truffle Security recently discovered. According to a Common Crawl scan of websites carried out by the company in November, there were 2,863 […]
Trump administration bans Anthropic, seemingly embraces OpenAI
The Trump administration on Friday moved to ban the use of products from artificial intelligence company Anthropic by federal businesses, escalating a high-stakes clash over whether private AI makers can limit how the US military uses their systems. Just hours later, Anthropic rival OpenAI’s CEO, Sam Altman, announced that his company had reached a deal […]
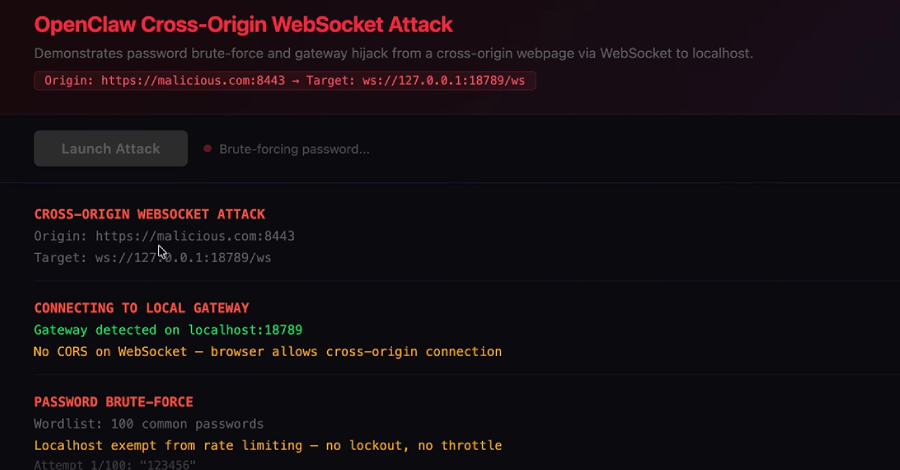
ClawJacked Flaw Lets Malicious Sites Hijack Local OpenClaw AI Agents via WebSocket
OpenClaw has fixed a high-severity security issue that, if successfully exploited, could have allowed a malicious website to connect to a locally running artificial intelligence (AI) agent and take over control. “Our vulnerability lives in the core system itself – no plugins, no marketplace, no user-installed extensions – just the bare OpenClaw gateway, running exactly […]
Connecticut Senate Bill Raises the Stakes on Data Breach Response
Hayley Steele and Gregory Szewczyk of Ballard Spahr write: A new bill introduced in Connecticut—Connecticut Senate Bill 117, An Act Concerning Breaches of Security Involving Electronic Personal Information—would create mandatory forensic examination requirements for entities that experience a “massive breach of security,” defined as a data breach affecting at least 100,000 Connecticut residents, and imposes… […]
Court Refuses to Slice Up CiCi’s Cyber Extortion Coverage
Andrea DeField and S. Alice Weeks of Hunton Andrews Kurth write: In the rarely litigated space of cyber insurance, the Northern District of Texas issued a win for cyber policyholders this week, offering a clear reminder to insurers that if they want to restrict coverage, they must draft the policy to clearly do so. In CiCi… […]
Israel plunges Iran into darkness with largest cyberattack in history during attack against Iran
The Jerusalem Post reports: As fighter jets and cruise missiles struck IRGC command centers, a parallel front reportedly paralyzed the Islamic Republic from within. Reports on Saturday, February 28, 2026, indicated that Iran entered an almost complete digital fog, in what appeared to be a large-scale cyberattack accompanying Operation “Roar of the Lion.” Critical infrastructure, official news sites,… […]
Leaked Odido data exposes sensitive information
In contrast to entities and courts that try to chill reporting, look at coverage of the Odido breach, where Dutch news outlets are not censored from informing the public about the scope of the breach. As seen on NL Times: A second batch of stolen customer data from Dutch telecom company Odido has revealed highly sensitive information… […]

Who is the Kimwolf Botmaster “Dort”?
In early January 2026, KrebsOnSecurity revealed how a security researcher disclosed a vulnerability that was used to build Kimwolf, the world’s largest and most disruptive botnet. Since then, the person in control of Kimwolf — who goes by the handle “Dort” — has coordinated a barrage of distributed denial-of-service (DDoS), doxing and email flooding attacks […]
Aeternum Botnet Loader Employs Polygon Blockchain C&C to Boost Resilience
Aeternum operates on smart contracts, making its command-and-control (C&C) infrastructure difficult to disrupt. The post Aeternum Botnet Loader Employs Polygon Blockchain C&C to Boost Resilience appeared first on SecurityWeek.
Anthropic Refuses to Bend to Pentagon on AI Safeguards as Dispute Nears Deadline
Anthropic said it sought narrow assurances from the Pentagon that Claude won’t be used for mass surveillance of Americans or in fully autonomous weapons. The post Anthropic Refuses to Bend to Pentagon on AI Safeguards as Dispute Nears Deadline appeared first on SecurityWeek.
Chilean Carding Shop Operator Extradited to US
The 24-year-old suspect has been accused of trafficking over 26,000 cards from a single brand. The post Chilean Carding Shop Operator Extradited to US appeared first on SecurityWeek.
900 Sangoma FreePBX Instances Infected With Web Shells
The attacks exploited a post-authentication command injection vulnerability in the endpoint manager’s interface. The post 900 Sangoma FreePBX Instances Infected With Web Shells appeared first on SecurityWeek.
38 Million Allegedly Impacted by ManoMano Data Breach
Hackers stole personal information such as names, email addresses, phone numbers, and other information. The post 38 Million Allegedly Impacted by ManoMano Data Breach appeared first on SecurityWeek.
In Other News: ATT&CK Advisory Council, Russian Cyberattacks Aid Missile Strikes, Predator Bypasses iOS Indicators
Other noteworthy stories that might have slipped under the radar: cyber valuations surge, OpenAI disrupts malicious AI use, ShinyHunters claims Odido breach. The post In Other News: ATT&CK Advisory Council, Russian Cyberattacks Aid Missile Strikes, Predator Bypasses iOS Indicators appeared first on SecurityWeek.
Trump Orders All Federal Agencies to Phase Out Use of Anthropic Technology
OpenAI and Google, along with Elon Musk’s xAI, also have contracts to supply their AI models to the military. The post Trump Orders All Federal Agencies to Phase Out Use of Anthropic Technology appeared first on SecurityWeek.

Thousands of Public Google Cloud API Keys Exposed with Gemini Access After API Enablement
New research has found that Google Cloud API keys, typically designated as project identifiers for billing purposes, could be abused to authenticate to sensitive Gemini endpoints and access private data. The findings come from Truffle Security, which discovered nearly 3,000 Google API keys (identified by the prefix “AIza”) embedded in client-side code to provide Google-related […]

Pentagon Designates Anthropic Supply Chain Risk Over AI Military Dispute
Anthropic on Friday hit back after U.S. Secretary of Defense Pete Hegseth directed the Pentagon to designate the artificial intelligence (AI) upstart as a “supply chain risk.” “This action follows months of negotiations that reached an impasse over two exceptions we requested to the lawful use of our AI model, Claude: the mass domestic surveillance […]
KT, LG Uplus face lingering fallout over hacking incidents
Lee Gyu-lee reports: Korea’s two major telecom companies, KT and LG Uplus, continue to grapple with the fallout over hacking incidents and data breaches that triggered customer departures and mounting pressure for tougher sanctions. KT has extended the deadline for customers to apply for early termination fee refunds after complaints that some users were unable… […]
25-01168.pdf
25-01168.pdf Anonymous (not verified) Fri, 02/27/2026 – 19:00 Case ID 25-01168 Forum FINRA Document Type Award Claimants Karl Jones Respondents Fidelity Brokerage Services LLC Neutrals Karen Roberts Washington Hearing Site Houston, TX Award Document 25-01168.pdf Documentum DocID 9f79ac08 Award Date Official Fri, 02/27/2026 – 12:00 Related Content Off Claimant Representatives Karl Lorenzo Jones Respondent Representatives […]
25-01450.pdf
25-01450.pdf Anonymous (not verified) Fri, 02/27/2026 – 19:00 Case ID 25-01450 Forum FINRA Document Type Award Claimants Kevin Bailey Respondents Charles Schwab & Co., Inc. Neutrals Patricia Ann Tracey Barry David Thorpe Susan L. Walker Hearing Site Phoenix, AZ Award Document 25-01450.pdf Documentum DocID 78509b13 Award Date Official Fri, 02/27/2026 – 12:00 Related Content Off […]
Hackers steal medical details of 15 million in France
Third-party vendors/business associates continue to be responsible for huge breaches involving patient data. Rébecca Frasquet and Chloé Rabs of AFP report: France’s health ministry said Friday that administrative details and medical notes on more than 15 million people had been hacked. The announcement came only days after officials warned that the details of 1.2 million… […]
Former Nuance employee admits breaching more than 1.2M Geisinger patient records
John Beauge reports the latest update in the case of Max Vance, also known as Andre J. Burk. Vance had been employed by Nuance Communications, a business associate of Geisinger Health. After his employment was terminated, he was still able to access Geisinger patient data. Geisinger detected the breach and notified Nuance. Now Beauge reports:… […]

Security hole could let hackers take over Juniper Networks PTX core routers
Network admins with Juniper PTX series routers in their environments are being warned to patch immediately, because a newly-discovered critical vulnerability could lead to an unauthenticated threat actor running code with root privileges. The hole is “especially dangerous, because these devices often sit in the middle of the network, not on the fringes,” said Piyush […]
25-02136.pdf
25-02136.pdf Anonymous (not verified) Fri, 02/27/2026 – 16:10 Case ID 25-02136 Forum FINRA Document Type Award Claimants Lawrence Davis Respondents E*Trade Securities LLC Neutrals William W. Haskell Hearing Site Honolulu, HI Award Document 25-02136.pdf Documentum DocID ffca5b9b Award Date Official Fri, 02/27/2026 – 12:00 Related Content Off Claimant Representatives Lawrence A. Davis Respondent Representatives Alan […]
24-02667.pdf
24-02667.pdf Anonymous (not verified) Fri, 02/27/2026 – 15:55 Case ID 24-02667 Forum FINRA Document Type Award Claimants Joseph Rallo Respondents D. Boral Capital Neutrals Kimberly C. Lawrence Harvey E. Benjamin Angela Jameson Hearing Site New York, NY Award Document 24-02667.pdf Documentum DocID ea13d48d Award Date Official Fri, 02/27/2026 – 12:00 Related Content Off Claimant Representatives […]
24-02598.pdf
24-02598.pdf Anonymous (not verified) Fri, 02/27/2026 – 15:55 Case ID 24-02598 Forum FINRA Document Type Award Claimants Alexa Marchisotto Jonathan Marchisotto Michael Marchisotto Respondents Fidelity Brokerage Services LLC Neutrals Jeffrey Alan Helewitz Howard Alan Grinsberg Kevin K Walsh Hearing Site Jersey City, NJ Award Document 24-02598.pdf Documentum DocID f89d61b2 Award Date Official Fri, 02/27/2026 – […]

‘Silent’ Google API key change exposed Gemini AI data
Google Cloud API keys, normally used as simple billing identifiers for APIs such as Maps or YouTube, could be scraped from websites to give access to private Gemini AI project data, researchers from Truffle Security recently discovered. According to a Common Crawl scan of websites carried out by the company in November, there were 2,863 […]
Enterprise Spotlight: Data Center Modernization
New IT roles emerge to tackle AI evaluation
New IT jobs are emerging to help organizations better evaluate AI outputs as they move from AI pilots to full-scale deployments. Many organizations are now considering assembling or hiring AI evaluation teams, with some experts calling these recently created roles an essential safety net for companies rolling out AI tools. The rapid rise of AI […]
Anthropic to US DoD: No compromise on AI ethics
Faced with demands from the US Department of Defense to allow its technology to be used for purposes the company considers unsafe or antidemocratic, Anthropic CEO Dario Amodei’s stance remains firm: “We cannot in good conscience accede to their request,” he wrote in a statement published on the company’s website late Thursday. Anthropic is a […]
Workday sees growth slowing, subscriber commitment shortening
Workday released its first quarterly results since the return of co-founder Aneel Bhusri and it’s fair to say that the markets were not too impressed, the share price falling by about 10%. Its overall results were solid enough: Subscription revenue for the quarter was $2.36 billion, up 16% year on year, and full year subscription […]
量子コンピューターとは何か いまさら聞けない基本と「できること/できないこと」
まず「計算」とは何をしているのか 量子コンピューターの話に入る前に、そもそもコンピューターの「計算」とは何かを押さえておくと理解が一気に楽になります。私たちが日常的に使うスマホやPC、そして企業のサーバーは、基本的には「情報を決まった手順で加工し、答えを出す装置」です。入力があり、処理があり、出力がある。この流れを支えているのが、0と1で情報を表すビットと、それを操作する論理回路です。例えば、地図アプリが最短ルートを探すのも、工場の生産計画を作るのも、暗号で通信を守るのも、結局は「大量の候補の中から、条件に合うものを探す」「正しさを検証する」「将来を予測する」といった計算に分解できます。ここで重要なのは、コンピューターが得意な計算と苦手な計算があるという点です。足し算や掛け算はとても速い一方で、候補が爆発的に増えるタイプの問題、つまり「組み合わせ」が増えすぎる問題では、どんなに高性能なコンピューターでも時間が足りなくなってしまいます。量子コンピューターが注目される背景には、この「組み合わせ爆発」や「複雑な相互作用」を含む計算が、産業のさまざまな場所でボトルネックになっている現実があります。ただし、量子コンピューターは万能ではなく、得意分野がはっきりしています。だからこそ、基本を正しく理解しておくことが大切になります。 ビットと量子ビットの違いを直感でつかむ 普通のコンピューターの最小単位はビットで、0か1のどちらかの値を取ります。一方、量子コンピューターの最小単位は量子ビットで、0と1の「どちらでもあるような状態」を作れます。この性質は「重ね合わせ」と呼ばれます。ただし、ここでよくある誤解が生まれます。重ね合わせを「0と1を同時に持つから、すべての答えを同時に計算できる」と説明してしまうと、なんとなくすごそうに見える反面、本質が見えなくなります。量子ビットは確かに0と1の成分を同時に持てますが、最後に読み出すときには、結果は0か1のどちらかとして観測されます。つまり、途中がどれだけ豊かでも、最終的な取り出し方には制約があります。量子計算が力を発揮する鍵は、「重ね合わせそのもの」よりも、重ね合わせた状態同士をうまく干渉させて、欲しい答えの確率を高め、いらない答えの確率を下げる点にあります。水面の波が重なって大きくなったり、打ち消し合って小さくなったりするのに似ています。量子コンピューターは、こうした干渉を計算に利用して、ある種の問題では古典的な方法より効率よく答えに近づけます。さらに、量子には「もつれ」と呼ばれる相関の強い結びつきがあります。複数の量子ビットが独立ではなく、全体として一つの状態を作るように振る舞うため、古典的には表現しづらい構造を扱えます。産業応用で話題になる「分子のふるまいをシミュレーションする」「複雑な最適化を解く」といったテーマでは、この表現力の違いが重要になります。 なぜ速くなるのかは「全部同時に試す」ではない 量子コンピューターが速いと言われるとき、よく「並列に全部試せる」イメージが語られます。しかし現実の量子計算は、単純な総当たりの置き換えではありません。むしろ、総当たりをそのまま量子にしても、最後に観測すると一つの答えしか得られないため、期待ほど速くなりません。量子が速くなるのは、問題の構造を利用して「欲しい情報だけを効率よく取り出せる」場合です。たとえば、巨大な数字を素因数分解する問題では、古典的には計算量が急激に増えていきますが、量子には特定の数学的構造を使って効率を上げられるアルゴリズムが知られています。また、未整列のデータから目的のものを探す検索問題でも、量子なら探索回数を減らせることが知られています。ここで大切なのは、量子コンピューターの価値が「速さ」だけではない点です。速いから偉いという話ではなく、「古典では扱いにくい状態空間を自然に表現できる」ことが価値になる領域があります。例えば、材料や化学の世界では、電子が複雑に相互作用するため、古典計算で正確に追うのが難しい場合があります。量子はその振る舞いを表現するのが得意で、もし実用規模の量子計算ができるようになれば、研究開発の手法そのものが変わる可能性があります。一方で、文章作成、画像編集、会計処理のような一般的な業務を量子で動かす必要は、少なくとも現時点ではほとんどありません。普通のコンピューターはすでに非常に高速で安価であり、量子の特性が意味を持つ問題に絞る方が合理的だからです。 「量子優位」「量子超越」「実用的優位」を区別する ニュースや解説で目にしやすい言葉に、「量子優位」や「量子超越」があります。これらは、量子コンピューターがあるタスクで古典コンピューターより優れた結果を示した、という意味で語られがちです。ただ、ここにも初心者が混乱しやすい落とし穴があります。まず、研究上の到達点として「特定の計算を、古典では現実的な時間でできない形で実行できた」という主張が出ることがあります。これは科学技術としては重要ですが、そのタスクが産業に直結するとは限りません。ベンチマーク的な計算で優位を示しても、実務で解きたい問題が同じとは限らないからです。産業への影響を考えるなら、より重要なのは「実用的優位」です。これは、企業が実際に困っている問題に対して、量子を使うことでコスト、時間、品質、リスクなどの面で意味のある改善が得られる状態を指します。研究の優位と、ビジネスの優位は別物であり、ここを混同すると「すごいニュースが出たのに、現場は何も変わらない」というズレが生まれます。量子コンピューターは今まさに発展途中で、研究のマイルストーンと産業化のマイルストーンが並行して積み上がっている段階です。初心者ほど、この二つを分けて理解すると、情報に振り回されにくくなります。 量子コンピューターが苦手なことと、得意なことの輪郭 量子コンピューターの難しさは、計算原理が不思議だからというより、実用に必要な条件がとても厳しい点にあります。量子ビットは外部の影響を受けやすく、わずかなノイズで状態が崩れます。崩れた状態で計算しても答えは信用できません。だから量子コンピューターでは、精密な制御や、エラーを抑える工夫が欠かせません。この制約があるため、現時点で利用できる量子コンピューターは、できる計算が限られます。できることを誤解なく言うなら、「量子の特性を活かせる可能性がある問題を、現実的な規模に近づけるための研究と検証ができる段階」です。企業が量子を試す場合も、いきなり本番業務を置き換えるというより、将来の価値が見込める領域を見つけ、データやモデルを整え、クラウドなどを通じて試行しながら知見を貯めるという動きが中心になります。それでも得意な方向性は見えてきています。ひとつは、分子や材料のように、自然界の量子現象をそのまま扱いたい領域です。もうひとつは、最適化や探索のように、組み合わせが膨大で、近似でもよいから良い解を早く得たい領域です。そしてもうひとつは、量子を含む新しい計算モデルを使った機械学習やデータ解析です。反対に、一般的なデータベース処理、文書作成、画像のレンダリング、Webサーバーのような用途は、古典計算が成熟しすぎていて、量子が入り込む余地が小さいと考えた方が自然です。量子は「全部を置き換える新型エンジン」ではなく、「一部の難所を突破するための特殊な工具」に近い存在だと捉えると、期待値がちょうどよくなります。 初心者が次に見るべき地図 量子コンピューターを理解するうえで最初に身につけたいのは、神秘性ではなく、得意不得意の切り分けです。量子ビットの重ね合わせやもつれは確かに独特ですが、重要なのは「それがどんな問題の構造に効くのか」「どんな制約があるのか」をセットで覚えることです。量子の話題は、どうしても夢のある言い方が先行します。しかし産業への影響を正しく見通すには、現実的な視点が必要です。量子は一夜にして既存の産業を塗り替えるのではなく、研究開発や意思決定の一部を徐々に変え、ある時点で効く領域がはっきりと立ち上がってくる可能性があります。そのとき備えがある企業とない企業では、差がつきます。次の記事では、量子コンピューターが「なぜ難しいのか」を、ハードウェア方式やエラーの観点からやさしく解説します。量子が今どこまで来ていて、何が壁になっているのかが分かると、ニュースの見方も、投資や学習の優先順位もクリアになります。
SAP users show pragmatism under pressure
SAP users in German-speaking countries will continue to invest in IT and SAP in 2026 — but more selectively and under greater economic pressure, according to a new study, from the German-speaking SAP User Group (DSAG). DSAG’s Investment Report 2026 found that 38% of the nearly 200 companies surveyed in Germany, Austria, and Switzerland will […]
One Identity Appoints Michael Henricks as Chief Financial and Operating Officer
One Identity, a trusted leader in identity security, today announced the appointment of Michael Henricks as Chief Financial and Operating Officer. This decision reflects the continued growth of the business and a focus on aligning financial leadership with operational objectives as One Identity scales. “As One Identity accelerates its growth, the addition of a Chief Financial […]
El Hospital Provincial de Castellón convierte la ciberseguridad en seguridad del paciente
La transformación digital del sector sanitario ha abierto una nueva frontera para la atención médica, pero también para los ciberdelincuentes. Hospitales, centros de salud y laboratorios se han convertido en uno de los objetivos prioritarios de los ataques informáticos por una razón evidente: manejan información extremadamente sensible y, además, no pueden permitirse parar. Un incidente […]
AWU by Salesforce: A shiny new metric that tells CIOs little of value
Every CIO would love a single metric that explains whether their spend on agentic software is paying off and gives them a clean story to tell the board when it’s time to move pilots to production or when renewal rolls around. Salesforce is pitching its new Agentic Work Unit (AWU) metric as a measure that […]
Las migraciones SAP suelen fracasar durante la fase de planificación
La mayoría de las migraciones SAP fracasan antes de que comience la implementación. Esta es la conclusión del informe ‘The State of SAP Migrations’ (El estado de las migraciones SAP) de ISG. La empresa de investigación y asesoramiento tecnológico, que encuestó a más de 200 responsables de la toma de decisiones empresariales y de TI […]

DoJ Seizes $61 Million in Tether Linked to Pig Butchering Crypto Scams
The U.S. Department of Justice (DoJ) this week announced the seizure of $61 million worth of Tether that were allegedly associated with bogus cryptocurrency schemes known as pig butchering. The confiscated funds were traced to cryptocurrency addresses used for the laundering of criminally derived proceeds stolen from victims of cryptocurrency investment scams, the department added. […]

900+ Sangoma FreePBX Instances Compromised in Ongoing Web Shell Attacks
The Shadowserver Foundation has revealed that over 900 Sangoma FreePBX instances still remain infected with web shells as part of attacks that exploited a command injection vulnerability starting in December 2025. Of these, 401 instances are located in the U.S., followed by 51 in Brazil, 43 in Canada, 40 in Germany, and 36 in France. […]
Malicious Go Crypto Module Steals Passwords, Deploys Rekoobe Backdoor
Cybersecurity researchers have disclosed details of a malicious Go module that’s designed to harvest passwords, create persistent access via SSH, and deliver a Linux backdoor named Rekoobe. The Go module, github[.]com/xinfeisoft/crypto, impersonates the legitimate “golang.org/x/crypto” codebase, but injects malicious code that’s responsible for exfiltrating secrets entered via terminal password
South Korean Authorities Accidentally Hand Hackers $4.8M in Crypto
Kenrodgers Fabian reports: A security blunder hit South Korea as the National Tax Service accidentally exposed a crypto wallet’s recovery key, leading to a $4.8 million theft. The incident happened when the tax authority published a press release photo showing the mnemonic phrase for a seized wallet. This phrase, essentially the master password for virtual… […]

One of the ‘most influential cybersecurity’ roles will pay under $175,000
A recent job ad is causing plenty of head-shaking, suggesting that some government high-ups appear to be out of touch with the current state of the cybersecurity job market. There is plenty of evidence that the world needs cybersecurity talent. According to a recent ISC2 survey, 33% of organizations cannot staff their security teams adequately […]

ScarCruft Uses Zoho WorkDrive and USB Malware to Breach Air-Gapped Networks
The North Korean threat actor known as ScarCruft has been attributed to a fresh set of tools, including a backdoor that uses Zoho WorkDrive for command-and-control (C2) communications to fetch more payloads and an implant that uses removable media to relay commands and breach air-gapped networks. The campaign, codenamed Ruby Jumper by Zscaler ThreatLabz, involves […]
Fake Fedex Email Delivers Donuts!, (Fri, Feb 27th)
It’s Friday, let’s have a look at another simple piece of malware to close a busy week! I received a Fedex notification about a delivery. Usually, such emails are simple phishing attacks that redirect you to a fake login page to collect your credentials. Here, it was a bit different:
Hacker Used Anthropic’s Claude to Steal Sensitive Mexican Data
Andrew Martin and Caroline Millan report: A hacker exploited Anthropic PBC’s artificial intelligence chatbot to carry out a series of attacks against Mexican government agencies, resulting in the theft of a huge trove of sensitive tax and voter information, according to cybersecurity researchers. The unknown Claude user wrote Spanish-language prompts for the chatbot to act as… […]
UK Court of Appeal Rules on the Concept of Personal Data in the Context of Data Security
Sam Jungyun Choi, Jadzia Pierce, and Paul Maynard of Covington and Burling write: On February 19, 2026, the UK Court of Appeal handed down its decision in DSG Retail Limited v The Information Commissioner [2026] EWCA Civ 140. The Court ruled that a controller’s data security duty applies to all personal data for which it acts as… […]
NL: Hackers had access to prison staff data for five months
Dutch News reports: Hackers had access to data from the Dutch prisons agency DJI for at least five months, according to an investigation by radio programme Argos. Cyber criminals could see e-mail addresses, phone numbers and security certificates of staff at the agency, Argos said, which may increase the risk of extortion or blackmail. The hackers… […]
Your personal OpenClaw agent may also be taking orders from malicious websites
If you thought running an AI agent locally kept it safely inside your machine’s walls, you’re in for a surprise. Researchers at Oasis Security have disclosed a flaw chain that allowed a malicious website to quietly connect to a locally running OpenClaw agent and take full control. The issue stems from a fundamental assumption baked […]

US authorities punish sellers of malware and spyware
The US authorities have made it clear that they will have no truck with any individuals trying to by-pass regulations on trading cyberweapons with hostile powers. Selling sensitive cyber-exploit components to a Russian company landed Australian citizen Peter Williams with an 87-month prison sentence from the US District Court for the District of Columbia on […]
Zyxel Patches Critical Vulnerability in Many Device Models
The issue impacts the UPnP function of multiple device models and could be exploited for remote code execution. The post Zyxel Patches Critical Vulnerability in Many Device Models appeared first on SecurityWeek.
Gambit Security Emerges From Stealth With $61 Million in Funding
The seed and Series A investment will enable the startup to accelerate product development and expand sales and customer success teams. The post Gambit Security Emerges From Stealth With $61 Million in Funding appeared first on SecurityWeek.
Claude Code Flaws Exposed Developer Devices to Silent Hacking
Anthropic has patched vulnerabilities whose impact was demonstrated by Check Point via malicious configuration files. The post Claude Code Flaws Exposed Developer Devices to Silent Hacking appeared first on SecurityWeek.
Four Risks Boards Cannot Treat as Background Noise
The goal isn’t about preventing every attack but about keeping the business running when attacks succeed. The post Four Risks Boards Cannot Treat as Background Noise appeared first on SecurityWeek.
Apple iPhone and iPad Cleared for Classified NATO Use
The devices have been added to the NATO Information Assurance Product Catalogue (NIAPC). The post Apple iPhone and iPad Cleared for Classified NATO Use appeared first on SecurityWeek.
Critical Flaws Exposed Gardyn Smart Gardens to Remote Hacking
CISA has released an advisory to warn about four vulnerabilities discovered by a researcher in Gardyn Home and Gardyn Studio. The post Critical Flaws Exposed Gardyn Smart Gardens to Remote Hacking appeared first on SecurityWeek.
Juniper Networks PTX Routers Affected by Critical Vulnerability
An out-of-band security update for Junos OS Evolved patches the remote code execution vulnerability CVE-2026-21902. The post Juniper Networks PTX Routers Affected by Critical Vulnerability appeared first on SecurityWeek.

Why application security must start at the load balancer
For a long time, I thought of the load balancer as a performance device. Its job was to distribute traffic, improve uptime, and make applications feel fast. Security was something that happened elsewhere, on firewalls, inside WAFs or deep in the application code. That perspective changed early in my consulting career. I worked with a […]

Trojanized Gaming Tools Spread Java-Based RAT via Browser and Chat Platforms
Threat actors are luring unsuspecting users into running trojanized gaming utilities that are distributed via browsers and chat platforms to distribute a remote access trojan (RAT). “A malicious downloader staged a portable Java runtime and executed a malicious Java archive (JAR) file named jd-gui.jar,” the Microsoft Threat Intelligence team said in a post on X. […]
Enterprise Spotlight: Data Center Modernization

How to make LLMs a defensive advantage without creating a new attack surface
Large language models (LLMs) have arrived in security in three different forms at once: as productivity tools that sit beside analysts, as components embedded inside products and workflows and as targets that attackers can probe, manipulate and steal. That convergence is why the conversation feels messy. The same capability that can summarize an incident in […]
Enterprise Spotlight: Data Center Modernization

Meta Files Lawsuits Against Brazil, China, Vietnam Advertisers Over Celeb-Bait Scams
Meta on Thursday said it’s taking legal action to tackle scams on its platforms by filing lawsuits against what it calls deceptive advertisers based in Brazil, China, and Vietnam. As part of the effort, the advertisers’ methods of payment have been suspended, related accounts have been disabled, and the website domain names used to pull […]

The CSO guide to top security conferences
There is nothing like attending a face-to-face event for career networking and knowledge gathering, and we don’t have to tell you how helpful it can be to get a hands-on demo of a new tool or to have your questions answered by experts. Fortunately, plenty of great conferences are coming up in the months ahead. […]

Ransomware groups switch to stealthy attacks and long-term access
Ransomware attackers are switching tactics in favor of more stealthy infiltration, as the threat of public exposure of sensitive corporate data is becoming the main mechanism of extortion. Picus Security’s annual red-teaming report shows attackers shifting away from loud disruption toward quiet, long-term access — or from “predatory” smash-and-grab tactics to “parasitic” silent residency. Four […]

Hacker kompromittieren immer schneller
Der Einsatz von KI-Tools macht Cyberangriffe nicht nur schneller, sondern erhöht auch die Taktzahl. Color4260 / Shutterstock Crowdstrike hat die aktuelle Ausgabe seines Global Threat Report veröffentlicht – mit mehreren bemerkenswerten Erkenntnissen. So benötigte ein Angreifer im Jahr 2025 im Schnitt nur noch 29 Minuten, um sich vollständigen Zugriff auf ein Netzwerk zu verschaffen. Damit […]
ISC Stormcast For Friday, February 27th, 2026 https://isc.sans.edu/podcastdetail/9828, (Fri, Feb 27th)
Post Content
Cisco says hackers have been exploiting a critical bug to break into big customer networks since 2023
Zack Whittaker reports: Cisco says hackers have been exploiting a bug in one of its popular networking products used by large enterprises for at least three years, prompting the U.S. government and its allies to urge organizations to take action. The bug, which has a maximum-rated vulnerability severity score of 10.0, allows hackers to remotely break… […]
25-01411(1).pdf
25-01411(1).pdf Anonymous (not verified) Thu, 02/26/2026 – 17:45 Case ID 25-01411 Forum FINRA Document Type Award Claimants Michael Norton Respondents David Lerner Associates, Inc. Neutrals Michael J. Meeusen John James McGovern Ronald Harris Kisner Hearing Site New York, NY Award Document 25-01411(1).pdf Documentum DocID d2b34e9c Award Date Official Mon, 01/05/2026 – 12:00 Related Content Off […]
“실패하는 것은 AI가 아니라 데이터” 데이터 준비도가 성패 가른다
AI가 기대만큼 성과를 내지 못한다면 문제는 모델이 아닐 가능성이 크다. 지저분한 데이터, 허술한 거버넌스, 그리고 조용히 성능을 갉아먹는 드리프트가 결과를 망치고 있다는 얘기다. 야구 선수 마리오 멘도사와 AI의 공통점은 ‘20% 성공률’이다. 멘도사의 타율은 ‘멘도사 라인(Mendoza Line)’이라는 말까지 낳았는데, 간신히 용인 가능한 수준의 성과를 뜻하는 단어로 굳어졌다. 산업 전반을 보면 AI 이니셔티브 5개 중 4개가 여전히 […]
칼럼 | DX를 넘어 지능형 전환으로···AI 에이전트 시대, 기업 가치 확장의 조건
지난 10년간 디지털 트랜스포메이션(DX)은 수작업 중심의 프로세스를 디지털 방식으로 전환하고, 인프라를 클라우드로 이전하며, 애플리케이션을 현대화하고, 고객과 직원 참여를 위한 새로운 채널을 구축하는 데 초점을 맞췄다. 그 결과 업무 처리 주기가 단축되고 운영 투명성이 높아졌으며 비용 절감 같은 가시적인 성과를 거뒀다. 그러나 동시에 한계도 드러냈다. 근본적으로 문제가 있는 프로세스를 단순히 디지털화하는 것만으로는 구조적 문제를 해결할 수 […]
CISO 650명에게 물었다…스플렁크가 진단한 AI 시대 보안 리더의 과제와 기회
시스코 자회사 스플렁크의 CISO 마이클 패닝은 보도자료를 통해 “CISO의 늘어나는 의무는 상당한 수준의 압박과 개인 차원의 책무를 동반한다”라며 “우리는 이제 단순한 기술관리를 넘어, 리스크와 인재, 그리고 핵심 비즈니스 성과를 좌우하는 디지털 회복탄력성까지 총괄 관리해야 하는 시점에 서 있다”라고 밝혔다. 보고서에 따르면 AI는 에이전틱 AI를 포함해 보안 조직에서 핵심 비즈니스 추진력이자 생산성 향상 수단으로 인식되고 있다. […]
How we engineered a scalable and performant enterprise AI platform
In the AI era, some long-standing engineering tradeoffs must be revisited. For years, multi-tenant architectures were the engineering defaults. They were a default for a reason as they were proven to be simpler, cheaper and easier to scale without much engineering efforts. This logic makes sense for applications that were built to be deterministic and […]
5 revealing stats about career challenges Black IT pros face
Despite data that shows diverse leadership teams make companies 36% more likely to outperform competitors, according to McKinsey, many have continued to ignore DEI in the wake of sweeping rollbacks in 2025. Amazon and Google, for instance, scaled back, or shuttered altogether, programs during the Trump administration’s first two weeks in office, dismantling a raft […]
IT leaders burnish their reps in big business moments
“There’s never been a better time to be a CIO.” IT leaders who’ve embraced this saying also understand that their role has never been more challenging. Technology has become so interwoven in businesses that CEOs expect more than an IT pro who keeps core applications refreshed and PCs updated. They need strategic partners who can […]
From lab to launch: Structuring ML operations for maximum velocity
Hiring data scientists has become the easy part of the AI equation. Every major enterprise now has a brilliant team of PhDs capable of building sophisticated recommendation engines, churn predictors and propensity models in their local environments. But deploying those models? That is where the ROI goes to die. In my experience leading engineering for […]
The hidden cost of AI adoption: Why most companies overestimate readiness
Walk into enough leadership meetings and you’ll hear the same story told with different accents: “We need AI.” It shows up in board decks, annual strategy documents and that one slide with a hockey-stick curve that magically turns pilot into profit. And look, I get it. AI is real. The upside is real. But here’s […]
Claves para dominar la disrupción: los CIO impulsan el negocio gracias a la IA generativa
Que la disrupción es constante y el cambio forma parte del día a día es una realidad cotidiana de muchos CIO, según expuso al arrancar el debate Fernando Muñoz, director de la comunidad de directivos de TI CIO Executive de Foundry España. Para los responsables de TI, esto significa que deben ir más allá de […]
ServiceNow plans automation of L1 Service Desk roles, promises more AI ‘specialists’ to come
ServiceNow plans to unleash the first member of its Autonomous Workforce, the Level 1 Service Desk AI specialist, next quarter. The agent will autonomously diagnose and resolve common IT support requests such as password resets, provisioning of software access, and network troubleshooting. It will base its actions on information from enterprise knowledge bases, historical incident […]
25-02263.pdf
25-02263.pdf Anonymous (not verified) Thu, 02/26/2026 – 13:35 Case ID 25-02263 Forum FINRA Document Type Award Claimants Robert Cohen Respondents Stifel, Nicolaus & Co., Inc. Neutrals Ted M. Rosen Richard E. Lauziere Marilee Roberg Hearing Site New York, NY Award Document 25-02263.pdf Documentum DocID 0dbbd8a6 Award Date Official Thu, 02/26/2026 – 12:00 Related Content Off […]
Aeternum C2 Botnet Stores Encrypted Commands on Polygon Blockchain to Evade Takedown
Cybersecurity researchers have disclosed details of a new botnet loader called Aeternum C2 that uses a blockchain-based command-and-control (C2) infrastructure to make it resilient to takedown efforts. “Instead of relying on traditional servers or domains for command-and-control, Aeternum stores its instructions on the public Polygon blockchain,” Qrator Labs said in a report shared with The
25-01674.pdf
25-01674.pdf Anonymous (not verified) Thu, 02/26/2026 – 12:00 Case ID 25-01674 Forum FINRA Document Type Award Claimants Jared Hoffman Respondents Ameriprise Financial Services, LLC Neutrals James W. Kerr Robert J. Buchner Geoffrey A. Drucker Hearing Site Columbus, OH Award Document 25-01674.pdf Documentum DocID 0467e2c9 Award Date Official Wed, 02/25/2026 – 12:00 Related Content Off Claimant […]
24-02390.pdf
24-02390.pdf Anonymous (not verified) Thu, 02/26/2026 – 12:00 Case ID 24-02390 Forum FINRA Document Type Award Claimants Mark Aizenberg Timothy Johnson Respondents Wells Fargo Clearing Services, LLC Neutrals Helen Marinak Blohm Carol Ann Jensen Ralph L. Jacobson Hearing Site San Francisco, CA Award Document 24-02390.pdf Documentum DocID 80b5cd9f Award Date Official Wed, 02/25/2026 – 12:00 […]
SR-FINRA-2026-005
SR-FINRA-2026-005 K32984 Thu, 02/26/2026 – 10:33 Rule Filing Status: Filed for Immediate Effectiveness Rule change to amend FINRA Rules 6380A and 6380B regarding the operation of the FINRA/Nasdaq Trade Reporting Facility Carteret, the FINRA/Nasdaq Trade Reporting Facility Chicago, and the FINRA/NYSE Trade Reporting Facility to provide a limited, temporary exception from reporting specified overnight transactions […]

UAT-10027 Targets U.S. Education and Healthcare with Dohdoor Backdoor
A previously undocumented threat activity cluster has been attributed to an ongoing malicious campaign targeting education and healthcare sectors in the U.S. since at least December 2025. The campaign is being tracked by Cisco Talos under the moniker UAT-10027. The end goal of the attacks is to deliver a never-before-seen backdoor codenamed Dohdoor. “Dohdoor utilizes […]
Extorting the Extorters? Moscow man accused of posing as FSB officer to extort Conti ransomware gang
Daryna Antoniuk reports: A Moscow resident has been accused of trying to extort money from the notorious Conti ransomware group by posing as an officer of Russia’s Federal Security Service (FSB), according to local media reports. Russian outlet RBC, citing sources familiar with the investigation, reported on Wednesday that the suspect, Ruslan Satuchin, allegedly presented himself as… […]

ThreatsDay Bulletin: Kali Linux + Claude, Chrome Crash Traps, WinRAR Flaws, LockBit & 15+ Stories
Nothing here looks dramatic at first glance. That’s the point. Many of this week’s threats begin with something ordinary, like an ad, a meeting invite, or a software update. Behind the scenes, the tactics are sharper. Access happens faster. Control is established sooner. Cleanup becomes harder. Here is a quick look at the signals worth […]

Expert Recommends: Prepare for PQC Right Now
Introduction: Steal It Today, Break It in a Decade Digital evolution is unstoppable, and though the pace may vary, things tend to fall into place sooner rather than later. That, of course, applies to adversaries as well. The rise of ransomware and cyber extortion generated funding for a complex and highly professional criminal ecosystem. The […]
Johnson Controls, Inc. Frick Controls Quantum HD
View CSAF Summary Successful exploitation of these vulnerabilities can lead to pre-authentication remote code execution, information leak or denial of service. The following versions of Johnson Controls, Inc. Frick Controls Quantum HD are affected: Frick Controls Quantum HD <=10.22 (CVE-2026-21654, CVE-2026-21656, CVE-2026-21657, CVE-2026-21658, CVE-2026-21659, CVE-2026-21660) CVSS Vendor Equipment Vulnerabilities v3 9.1 Johnson Controls, Inc. Johnson […]
SWITCH EV swtchenergy.com
View CSAF Summary Successful exploitation of these vulnerabilities could allow attackers to impersonate charging stations, hijack sessions, suppress or misroute legitimate traffic to cause large-scale denial of service, and manipulate data sent to the backend. The following versions of SWITCH EV swtchenergy.com are affected: swtchenergy.com vers:all/* (CVE-2026-27767, CVE-2026-25113, CVE-2026-25778, CVE-2026-27773) CVSS Vendor Equipment Vulnerabilities v3 […]
EV2GO ev2go.io
View CSAF Summary Successful exploitation of these vulnerabilities could allow attackers to impersonate charging stations, hijack sessions, suppress or misroute legitimate traffic to cause large-scale denial of service, and manipulate data sent to the backend. The following versions of EV2GO ev2go.io are affected: ev2go.io vers:all/* (CVE-2026-24731, CVE-2026-25945, CVE-2026-20895, CVE-2026-22890) CVSS Vendor Equipment Vulnerabilities v3 9.4 […]
CloudCharge cloudcharge.se
View CSAF Summary Successful exploitation of these vulnerabilities could allow attackers to impersonate charging stations, hijack sessions, suppress or misroute legitimate traffic to cause large-scale denial of service, and manipulate data sent to the backend. The following versions of CloudCharge cloudcharge.se are affected: cloudcharge.se vers:all/* (CVE-2026-20781, CVE-2026-25114, CVE-2026-27652, CVE-2026-20733) CVSS Vendor Equipment Vulnerabilities v3 9.4 […]
Mobility46 mobility46.se
View CSAF Summary Successful exploitation of these vulnerabilities could enable attackers to gain unauthorized administrative control over vulnerable charging stations or disrupt charging services through denial-of-service attacks. The following versions of Mobility46 mobility46.se are affected: mobility46.se vers:all/* (CVE-2026-27028, CVE-2026-26305, CVE-2026-27647, CVE-2026-22878) CVSS Vendor Equipment Vulnerabilities v3 9.4 Mobility46 Mobility46 mobility46.se Missing Authentication for Critical Function, […]
EV Energy ev.energy
View CSAF Summary Successful exploitation of these vulnerabilities could enable attackers to gain unauthorized administrative control over vulnerable charging stations or disrupt charging services through denial-of-service attacks. The following versions of EV Energy ev.energy are affected: ev.energy vers:all/* (CVE-2026-27772, CVE-2026-24445, CVE-2026-26290, CVE-2026-25774) CVSS Vendor Equipment Vulnerabilities v3 9.4 EV Energy EV Energy ev.energy Missing Authentication […]
Copeland XWEB and XWEB Pro
View CSAF Summary Successful exploitation of these vulnerabilities could allow an attacker to bypass authentication, cause a denial-of-service condition, cause memory corruption, and execute arbitrary code. The following versions of Copeland XWEB and XWEB Pro are affected: XWEB 300D PRO <=1.12.1 (CVE-2026-25085, CVE-2026-21718, CVE-2026-24663, CVE-2026-21389, CVE-2026-25111, CVE-2026-20742, CVE-2026-24517, CVE-2026-25195, CVE-2026-20910, CVE-2026-24689, CVE-2026-25109, CVE-2026-20902, CVE-2026-24695, CVE-2026-25105, […]
Pelco, Inc. Sarix Pro 3 Series IP Cameras
View CSAF Summary Successful exploitation of this vulnerability could allow attackers to gain unauthorized access to sensitive device data, bypass surveillance controls, and expose facilities to privacy breaches, operational risks, and regulatory compliance issues. The following versions of Pelco, Inc. Sarix Pro 3 Series IP Cameras are affected: Sarix Professional IMP 3 Series <=02.52 (CVE-2026-1241) […]
Yokogawa CENTUM VP R6, R7
View CSAF Summary Successful exploitation of these vulnerabilities could allow an attacker to terminate the software stack process, cause a denial-of-service condition, or execute arbitrary code. The following versions of Yokogawa CENTUM VP R6, R7 are affected: Vnet/IP Interface Package for CENTUM VP R6 (VP6C3300) <=R1.07.00 (CVE-2025-1924, CVE-2025-48019, CVE-2025-48020, CVE-2025-48021, CVE-2025-48022, CVE-2025-48023) Vnet/IP Interface Package […]
Chargemap chargemap.com
View CSAF Summary Successful exploitation of these vulnerabilities could enable attackers to gain unauthorized administrative control over vulnerable charging stations or disrupt charging services through denial-of-service attacks. The following versions of Chargemap chargemap.com are affected: chargemap.com vers:all/* (CVE-2026-25851, CVE-2026-20792, CVE-2026-25711, CVE-2026-20791) CVSS Vendor Equipment Vulnerabilities v3 9.4 Chargemap Chargemap chargemap.com Missing Authentication for Critical Function, […]

China-linked hackers used Google Sheets to spy on telecoms and governments across 42 countries
Google has disrupted a China-linked espionage group that used Google’s spreadsheet application as a covert spy tool to compromise telecom providers and government agencies across 42 countries, sending commands and receiving stolen data through it, Google’s Threat Intelligence Group (GTIG) said on Thursday. Working with Mandiant, GTIG confirmed intrusions at 53 organizations across 42 countries, […]
SecurityWeek Report: 426 Cybersecurity M&A Deals Announced in 2025
SecurityWeek’s M&A data indicates that today’s market is more disciplined, and it seems to favor GRC, data protection, and identity. The post SecurityWeek Report: 426 Cybersecurity M&A Deals Announced in 2025 appeared first on SecurityWeek.
CarGurus Data Breach Impacts Over 12 Million Users
Hackers claim to have stolen personally identifiable information and internal corporate data from the automotive firm. The post CarGurus Data Breach Impacts Over 12 Million Users appeared first on SecurityWeek.
Ex-US Defense Contractor Executive Jailed for Selling Exploits to Russia
Peter Williams was sentenced to 87 months in prison for selling cyber exploits to a Russian broker. The post Ex-US Defense Contractor Executive Jailed for Selling Exploits to Russia appeared first on SecurityWeek.
Medical Device Maker UFP Technologies Hit by Cyberattack
UFP Technologies appears to have been targeted in a ransomware attack that involved data theft and file-encrypting malware. The post Medical Device Maker UFP Technologies Hit by Cyberattack appeared first on SecurityWeek.
SolarWinds Patches Four Critical Serv-U Vulnerabilities
The four security defects could be exploited for remote code execution but require administrative privileges. The post SolarWinds Patches Four Critical Serv-U Vulnerabilities appeared first on SecurityWeek.
Google Disrupts Chinese Hackers Targeting Telecoms, Governments
The UNC2814 threat actor has been active since at least 2017, targeting organizations across 42 countries. The post Google Disrupts Chinese Hackers Targeting Telecoms, Governments appeared first on SecurityWeek.
The Blast Radius Problem: Stolen Credentials Are Weaponizing Agentic AI
More than half (56%) of the 400,000 vulnerabilities IBM X-Force tracked in 2025 required no authentication before exploitation. The post The Blast Radius Problem: Stolen Credentials Are Weaponizing Agentic AI appeared first on SecurityWeek.
Cisco Patches Catalyst SD-WAN Zero-Day Exploited by Highly Sophisticated Hackers
Already added to CISA’s KEV catalog, the flaw allows attackers to bypass authentication and gain administrative privileges. The post Cisco Patches Catalyst SD-WAN Zero-Day Exploited by Highly Sophisticated Hackers appeared first on SecurityWeek.
Trend Micro Patches Critical Apex One Vulnerabilities
TrendAI has fixed eight critical and high-severity issues in Windows and macOS endpoint security products. The post Trend Micro Patches Critical Apex One Vulnerabilities appeared first on SecurityWeek.
US Sanctions Russian Exploit Broker Operation Zero
The broker acquired eight zero-day exploits from a US defense contractor executive jailed for his actions. The post US Sanctions Russian Exploit Broker Operation Zero appeared first on SecurityWeek.
Microsoft Warns Developers of Fake Next.js Job Repos Delivering In-Memory Malware
A “coordinated developer-targeting campaign” is using malicious repositories disguised as legitimate Next.js projects and technical assessments to trick victims into executing them and establish persistent access to compromised machines. “The activity aligns with a broader cluster of threats that use job-themed lures to blend into routine developer workflows and increase the likelihood of code

Malicious StripeApi NuGet Package Mimicked Official Library and Stole API Tokens
Cybersecurity researchers have disclosed details of a new malicious package discovered on the NuGet Gallery, impersonating a library from financial services firm Stripe in an attempt to target the financial sector. The package, codenamed StripeApi.Net, attempts to masquerade as Stripe.net, a legitimate library from Stripe that has over 75 million downloads. It was uploaded by […]
Opinion 06/2026 on the draft decision of the Dutch Supervisory Authority regarding the Controller Binding Corporate Rules of the ABN AMRO Bank Group
Opinion 06/2026 on the draft decision of the Dutch Supervisory Authority regarding the Controller Binding Corporate Rules of the ABN AMRO Bank Group icolonnm Thu, 26/02/2026 – 11:06 10 February 2026 Opinion 06/2026 183.8KB English Download Members: Netherlands Topics: Binding Corporate Rules International Transfers of Data

The farmers and the mercenaries: Rethinking the ‘human layer’ in security
There’s a phrase that’s become gospel in cybersecurity: “Employees are the last line of defense.” We’ve built an entire industry around it. Billions of dollars in security awareness programs, mandatory simulations and user-reporting workflows across endpoints, applications and collaboration tools. All predicated on a premise that sounds reasonable until you examine what we’re actually asking. […]
Opinion 5/2026 on the draft decision of the Dutch Supervisory Authority regarding the Processor Binding Corporate Rules of the Arcadis Group
Opinion 5/2026 on the draft decision of the Dutch Supervisory Authority regarding the Processor Binding Corporate Rules of the Arcadis Group icolonnm Thu, 26/02/2026 – 10:58 10 February 2026 Opinion 5/2026 184.1KB English Download Members: Netherlands Topics: Binding Corporate Rules International Transfers of Data

5 trends that should top CISO’s RSA 2026 agendas
RSA 2026 is still weeks away and the hype machine is humming. This year’s theme, “The Power of Community,” is somewhat ironic as the overwhelming chatter at the Moscone Center in San Francisco from March 23 to March 26 will be about AI agents, not humans. Welcome to the cybersecurity community, agents, automatons, and robots! […]

Cisco SD-WAN Zero-Day CVE-2026-20127 Exploited Since 2023 for Admin Access
A newly disclosed maximum-severity security flaw in Cisco Catalyst SD-WAN Controller (formerly vSmart) and Catalyst SD-WAN Manager (formerly vManage) has come under active exploitation in the wild as part of malicious activity that dates back to 2023. The vulnerability, tracked as CVE-2026-20127 (CVSS score: 10.0), allows an unauthenticated remote attacker to bypass authentication and obtain

9 unverzichtbare Open-Source-Security-Tools
Diese Open-Source-Tools adressieren spezifische Security-Probleme – mit minimalem Footprint. Foto: N Universe | shutterstock.com Cybersicherheitsexperten verlassen sich in diversen Bereichen auf Open-Source-Lösungen – nicht zuletzt weil diese im Regelfall von einer lebendigen und nutzwertigen Community gestützt werden. Aber auch weil es inzwischen Hunderte qualitativ hochwertiger, quelloffener Optionen gibt, um Breaches und Datenlecks auf allen Ebenen […]

So rechtfertigen Sie Ihre Security-Investitionen
Lesen Sie, welche Aspekte entscheidend sind, um die Investitionen in die Cybersicherheit im Unternehmen zu rechtfertigen. Miha Creative – shutterstock.com In modernen Unternehmensumgebungen werden Investitionen in Sicherheitstechnologien nicht mehr nur anhand ihres technischen Reifegrades beurteilt. Die Finanzierung hängt vermehrt davon ab, inwieweit sich damit Umsatz generieren lässt, Risiken gemindert und Mehrwerte für Aktionäre geschaffen werden. […]
Finding Signal in the Noise: Lessons Learned Running a Honeypot with AI Assistance [Guest Diary], (Tue, Feb 24th)
[This is a Guest Diary by Austin Bodolay, an ISC intern as part of the SANS.edu BACS program]
ISC Stormcast For Thursday, February 26th, 2026 https://isc.sans.edu/podcastdetail/9826, (Thu, Feb 26th)
Post Content

Steaelite RAT combines data theft and ransomware management capability in one tool
It’s bad enough that threat actors are leveraging AI for their attacks, but now they can also access a new remote access trojan (RAT) that makes it easy to launch data theft and ransomware attacks on Windows computers from a single management pane. The tool is called Steaelite, and according to researchers at BlackFog, it’s […]
SR-FINRA-2026-005
SR-FINRA-2026-005 MwinamoC Wed, 02/25/2026 – 17:55 Financial Industry Regulatory Authority, Inc. (“FINRA”) is filing with the Securities and Exchange Commission (“SEC” or “Commission”) a proposed rule change to amend FINRA Rules 6380A and 6380B regarding the operation of the FINRA/Nasdaq Trade Reporting Facility Carteret, the FINRA/Nasdaq Trade Reporting Facility Chicago, and the FINRA/NYSE Trade Reporting […]

Five Eyes issue emergency directive on exploited Cisco SD-WAN zero-day
Cybersecurity agencies across the Five Eyes alliance have issued an emergency directive warning that a critical Cisco SD-WAN vulnerability is being actively exploited to gain unauthorized access to federal networks. Officials confirmed that threat actors are targeting core SD-WAN control systems —infrastructure that manages traffic across government and enterprise networks — and urged organizations to […]
25-00645.pdf
25-00645.pdf Anonymous (not verified) Wed, 02/25/2026 – 17:05 Case ID 25-00645 Forum FINRA Document Type Award Claimants Margaret Santiago Respondents Glenn Romer Center Street Securities, Inc. Neutrals Sidney J. Wartel Nofrey Matthew Fornaro Santarvis Brown Hearing Site Boca Raton, FL Award Document 25-00645.pdf Documentum DocID 2bdac0d6 Award Date Official Wed, 02/25/2026 – 12:00 Related Content […]
25-02104.pdf
25-02104.pdf Anonymous (not verified) Wed, 02/25/2026 – 17:05 Case ID 25-02104 Forum FINRA Document Type Award Claimants Mario Manniello Respondents Robinhood Financial, LLC. Neutrals Mark H. Schiff Hearing Site Boca Raton, FL Award Document 25-02104.pdf Documentum DocID 8221c4ee Award Date Official Tue, 02/24/2026 – 12:00 Related Content Off Claimant Representatives Mario Manniello Respondent Representatives Simeon […]
25-01146.pdf
25-01146.pdf Anonymous (not verified) Wed, 02/25/2026 – 17:05 Case ID 25-01146 Forum FINRA Document Type Award Claimants Edward Bacher Respondents Voya Financial Advisors, Inc. Neutrals F. Guthrie Castle Mary C. Davis Christopher M. McMurray Hearing Site Columbus, OH Award Document 25-01146.pdf Documentum DocID bc44fe12 Award Date Official Wed, 02/25/2026 – 12:00 Related Content Off Claimant […]
Clalit probes suspected cyberattack after Iranian-linked hackers leak patient files
Or Hadar reports: Clalit Health Services, the largest health maintenance organization in Israel, said it is investigating a suspected cyberattack after an Iranian-linked hacking group claimed it breached the insurer’s systems and published thousands of documents containing personal information of patients. The hacking group, calling itself “Handala,” has published thousands of documents online, including medical… […]
The CLAIR Model: A Synthesized Conceptual Framework for Mapping Critical Infrastructure Interdependencies [Guest Diary], (Wed, Feb 25th)
Accelerated Processing for Parties Who Qualify Based on Their Age or Health Condition
Accelerated Processing for Parties Who Qualify Based on Their Age or Health Condition K33357 Wed, 02/25/2026 – 14:32 For cases filed on or after March 30, 2026, a party may request accelerated processing of their arbitration proceeding pursuant to Rules 12808 for customer disputes or Rule 13808 for industry disputes. The party must be at least 70 […]
AI agents popular for programming — but not much else
AI agents are becoming more common in practice, but their use is still heavily focused on programming, according to new analysis by Anthropic of millions of interactions between humans and AI agents, where researchers studied how tools like Claude Code and public API solutions are used in real-world environments. According to the report, software development […]
Anthropic targets core business systems with new Claude plug-ins
Anthropic is expanding its push into the enterprise market with a new set of “coworker” plug-ins designed to embed its Claude AI directly into tools used by investment bankers, HR teams, and engineers, signaling a shift from standalone assistants toward AI agents that operate inside core business workflows. In a blog post, the company said […]
How weak talent strategy leaves IT with too much — and not enough — talent
In my work architecting AI transitions for global enterprises, I have identified a recurring systemic failure, a collision between hyper-accelerated output and stagnant governance. IT & Software Services (IT companies) are currently trapped in a talent paradox where they have an oversupply of AI-augmented ‘coding speed,’ yet a critical shortage of ‘architectural safety.’ They have […]
What AX can do to deliver cohesion and uniformity to AI agents
The point of agentic AI is for it to act by writing code, running scripts, executing commands, or calling APIs. All of that is more effective if those actions are discoverable, documented, consistent, and designed to be easy for agents to use in the first place. Agents need slightly different information from people. Both benefit […]
Using AI to unlock human potential at Liberty Mutual
Liberty Mutual’s approach to gen AI reflects a deeper understanding of enterprise transformation in that the hardest challenges aren’t technical but human. So global CIO Monica Caldas focuses on the central priorities of enterprise leaders: establishing effective AI governance, moving promising pilots into scalable solutions, and empowering employees to confidently adopt new ways of working. […]
Anthropic’s claim that AI can quickly refactor COBOL rattles IBM investors
Anthropic’s assertion that its agentic coding tool Claude Code can rapidly refactor legacy COBOL code has unsettled IBM investors, triggering a sell-off in shares, which resulted in the stock registering a 13% drop on Monday — its biggest single-day drop since October 2000. The assertion came in the form of a blog post from Anthropic […]
The agentic enterprise: Why value streams and capability maps are your new governance control plane
The economic pivot: From creation to execution The enterprise is currently undergoing a seismic pivot from generative AI, which focuses on content creation, to agentic AI, which focuses on goal execution. Unlike their predecessors, these agents possess “structured autonomy”: the ability to perceive contexts, plan actions and execute across systems without constant human intervention. For […]
From digital transformation to intelligent transformation
Over the past decade, digital transformation has focused on converting manual processes to digital ones, migrating infrastructure to the cloud, updating applications and creating new channels for customer and employee engagement. These efforts have resulted in tangible benefits such as accelerated cycle times, increased transparency and reduced costs. However, these initiatives have also revealed limitations: […]
It’s not your AI that’s failing. It’s your data
What do baseball’s Mario Mendoza and AI have in common? A 20% success rate. Mendoza’s batting average established the Mendoza Line: shorthand for barely acceptable performance. Across industries, four out of five AI initiatives still fall short of expectations. In all likelihood, it’s typically not the AI that’s failing, but the lack of data readiness. […]
Las plataformas de agentes de IA podrían reducir los costes de las licencias SaaS
La sugerencia de Anthropic de que su herramienta Claude Code podría utilizarse para automatizar la modernización de un lenguaje de programación veterano como COBOL —que seis décadas después de su primera implementación sigue siendo una actividad relevante para IBM— provocó el lunes una fuerte reacción en los mercados. La compañía registró una caída del 13,2% […]

Google Disrupts UNC2814 GRIDTIDE Campaign After 53 Breaches Across 42 Countries
Google on Wednesday disclosed that it worked with industry partners to disrupt the infrastructure of a suspected China-nexus cyber espionage group tracked as UNC2814 that breached at least 53 organizations across 42 countries. “This prolific, elusive actor has a long history of targeting international governments and global telecommunications organizations across Africa, Asia, and the Americas,”

Claude Code Flaws Allow Remote Code Execution and API Key Exfiltration
Cybersecurity researchers have disclosed multiple security vulnerabilities in Anthropic’s Claude Code, an artificial intelligence (AI)-powered coding assistant, that could result in remote code execution and theft of API credentials. “The vulnerabilities exploit various configuration mechanisms, including Hooks, Model Context Protocol (MCP) servers, and environment variables – executing

SLH Offers $500–$1,000 Per Call to Recruit Women for IT Help Desk Vishing Attacks
The notorious cybercrime collective known as Scattered LAPSUS$ Hunters (SLH) has been observed offering financial incentives to recruit women to pull off social engineering attacks. The idea is to hire them for voice phishing campaigns targeting IT help desks, Dataminr said in a new threat brief. The group is said to be offering anywhere between […]

Top 5 Ways Broken Triage Increases Business Risk Instead of Reducing It
Triage is supposed to make things simpler. In a lot of teams, it does the opposite. When you can’t reach a confident verdict early, alerts turn into repeat checks, back-and-forth, and “just escalate it” calls. That cost doesn’t stay inside the SOC; it shows up as missed SLAs, higher cost per case, and more room […]
South Korea considers updates to data and cyber laws
Charmian Aw, Paul Otto, and Ciara O’Leary of Hogan Lovells write: Recent large‑scale data breaches across major sectors in Korea, including across the telecommunications, retail, and finance sector, have prompted swift and coordinated response from lawmakers and regulators. The National Assembly and relevant government agencies are advancing legislative amendments and updating regulatory measures to strengthen… […]
UAE claims it stopped ‘terrorist’ ransomware attack
Jonathan Greig reports: The United Arab Emirates said it stopped a ransomware attack this weekend that allegedly targeted the country’s digital infrastructure. The country’s Cyber Security Council published a statement on Saturday that said they “successfully thwarted organized cyberattacks of a terrorist nature that targeted the country’s digital infrastructure and vital sectors in an attempt… […]
Wynn Resorts Confirms Data Breach After Hackers Remove It From Leak Site
Eduard Kovacs reports that the Wynn Resorts listing on the ShinyHunters leak site, previously noted on this site, has been removed, suggesting that the resort paid an extortion demand to get data deleted. “The unauthorized third party has stated that the stolen data has been deleted,” the company said in an emailed statement. “We are… […]
Malicious NuGet Packages Stole ASP.NET Data; npm Package Dropped Malware
Cybersecurity researchers have discovered four malicious NuGet packages that are designed to target ASP.NET web application developers to steal sensitive data. The campaign, discovered by Socket, exfiltrates ASP.NET Identity data, including user accounts, role assignments, and permission mappings, as well as manipulates authorization rules to create persistent backdoors in victim applications.
21st meeting of the CSC
21st meeting of the CSC icolonnm Wed, 25/02/2026 – 13:01 10 December 2025 21st meeting, in person 281.8KB English Download
CISA and Partners Release Guidance for Ongoing Global Exploitation of Cisco SD-WAN Systems
The purpose of this Alert is to provide resources for organizations with Cisco Software-Defined Wide-Area Networking (SD-WAN) systems, including Federal Civilian Executive Branch (FCEB) agencies, to address ongoing exploitation of multiple vulnerabilities. Notably, the Cybersecurity and Infrastructure Security Agency (CISA) has added CVE-2026-20127 and CVE-2022-20775 to its Known Exploited Vulnerabilities (KEV) Catalog on Feb. 25, 2026. As […]
CISA Adds Two Known Exploited Vulnerabilities to Catalog
CISA has added two new vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2022-20775 Cisco Catalyst SD-WAN Path Traversal Vulnerability CVE-2026-20127 Cisco Catalyst SD-WAN Controller and Manager Authentication Bypass Vulnerability These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities established the […]

Microsoft warns of job‑themed repo lures targeting developers with multi‑stage backdoors
Microsoft says it has uncovered a coordinated campaign targeting software developers through malicious repositories posing as legitimate Next.js projects and technical assessments. The campaign employs carefully crafted lures to blend into routine workflows, such as cloning repositories, opening projects, and running builds, thereby allowing the malicious code to execute undetected. Telemetry collected during an incident […]
Taiwan Security Firm Confirms Flaw Flagged by CISA Likely Exploited by Chinese APTs
The vulnerability in TeamT5 ThreatSonar Anti-Ransomware was recently added to CISA’s KEV catalog. The post Taiwan Security Firm Confirms Flaw Flagged by CISA Likely Exploited by Chinese APTs appeared first on SecurityWeek.
GitHub Issues Abused in Copilot Attack Leading to Repository Takeover
Attackers can inject malicious instructions in a GitHub Issue that are automatically processed by Copilot when launching a Codespace from that issue. The post GitHub Issues Abused in Copilot Attack Leading to Repository Takeover appeared first on SecurityWeek.
New ‘Sandworm_Mode’ Supply Chain Attack Hits NPM
The malicious code propagates like a worm, poisons AI assistants, exfiltrates secrets, and contains a destructive dead switch. The post New ‘Sandworm_Mode’ Supply Chain Attack Hits NPM appeared first on SecurityWeek.
CISO Conversations: Timothy Youngblood; 4x Fortune 500 CISO/CSO
Timothy Youngblood was CISO at Dell, CISO at Kimberley-Clark, VP & CISO at McDonald’s, and SVP, CSO & Product Security Officer at T-Mobile. The post CISO Conversations: Timothy Youngblood; 4x Fortune 500 CISO/CSO appeared first on SecurityWeek.
VMware Aria Operations Vulnerability Could Allow Remote Code Execution
Broadcom has patched several vulnerabilities in VMware Aria Operations, including high-severity flaws. The post VMware Aria Operations Vulnerability Could Allow Remote Code Execution appeared first on SecurityWeek.
‘Arkanix Stealer’ Malware Disappears Shortly After Debut
Written in C++ and Python, the malware exfiltrates system information, browser data, and steals files. The post ‘Arkanix Stealer’ Malware Disappears Shortly After Debut appeared first on SecurityWeek.
Ad Tech Company Optimizely Targeted in Cyberattack
The company says the attackers accessed internal business systems such as Zendesk and Salesforce. The post Ad Tech Company Optimizely Targeted in Cyberattack appeared first on SecurityWeek.
Claude’s New AI Vulnerability Scanner Sends Cybersecurity Shares Plunging
The stocks of major cybersecurity companies have fallen sharply over fears that AI is disrupting the industry. The post Claude’s New AI Vulnerability Scanner Sends Cybersecurity Shares Plunging appeared first on SecurityWeek.
Reddit Hit With $20 Million UK Data Privacy Fine Over Child Safety Failings
Britain’s data privacy watchdog slapped online forum Reddit on Tuesday with a fine worth nearly $20 million for failures involving children’s personal information. The post Reddit Hit With $20 Million UK Data Privacy Fine Over Child Safety Failings appeared first on SecurityWeek.
Astelia Raises $35 Million for Exposure Management
The company will expand its AI-based analysis capabilities, grow its employee base, and scale deployments. The post Astelia Raises $35 Million for Exposure Management appeared first on SecurityWeek.
Manual Processes Are Putting National Security at Risk
Why automating sensitive data transfers is now a mission-critical priority More than half of national security organizations still rely on manual processes to transfer sensitive data, according to The CYBER360: Defending the Digital Battlespace report. This should alarm every defense and government leader because manual handling of sensitive data is not just inefficient, it is […]
In The Loop February 2026
In the Loop, Tactical Tech’s monthly newsletter, includes new releases, open calls, job opportunities, information about our partners, events, recommended resources and more.

Ukrainian convicted for helping fake North Korean IT workers
A Ukrainian man has been sentenced to five years in prison after helping North Korean IT workers infiltrate American companies using stolen identities, reports Bleepingcomputer. The 39-year-old man from Kiev pleaded guilty in November 2025 to charges including aggravated identity theft and conspiracy to commit fraud. He has also agreed to surrender assets worth over […]
Defense Contractor Employee Jailed for Selling 8 Zero-Days to Russian Broker
A 39-year-old Australian national who was previously employed at U.S. defense contractor L3Harris has been sentenced to a little over seven years in prison for selling eight zero-day exploits to Russian exploit broker Operation Zero in exchange for millions of dollars. Peter Williams pleaded guilty to two counts of theft of trade secrets in October […]

SolarWinds Patches 4 Critical Serv-U 15.5 Flaws Allowing Root Code Execution
SolarWinds has released updates to address four critical security flaws in its Serv-U file transfer software that, if successfully exploited, could result in remote code execution. The vulnerabilities, all rated 9.1 on the CVSS scoring system, are listed below – CVE-2025-40538 – A broken access control vulnerability that allows an attacker to create a system […]

Boards don’t need cyber metrics — they need risk signals
Security teams live in a world of numbers. Dashboards depict counts of blocked attacks, phishing clicks, vulnerabilities discovered, patches applied, alerts triaged, and incidents closed. Over the past decade, the cybersecurity industry has become adept at measuring activity with increasing precision. Experts say what remains far less consistent is whether those measurements help boards govern […]

CISA Confirms Active Exploitation of FileZen CVE-2026-25108 Vulnerability
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday added a recently disclosed vulnerability in FileZen to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation. The vulnerability, tracked as CVE-2026-25108 (CVSS v4 score: 8.7), is a case of operating system (OS) command injection that could allow an authenticated user to execute

Hacker knackt 600 Firewalls in einem Monat – mit KI
Bedrohungsakteure setzen zunehmend KI-Tools ein, um ihre Angriffe durchzuführen. Shutterstock/Gorodenkoff Sicherheitsforscher von Amazon Web Services (AWS) berichten, dass es einem russischsprachigen Hacker gelungen ist, zwischen dem 11. Januar und dem 18. Februar 2026 mehr als 600 Fortigate-Firewalls zu kompromittieren. Dem Bericht zufolge wurden keine FortiGate-Sicherheitslücken ausgenutzt – stattdessen griff der Hacker zunächst Firewalls mit schwachen […]

So verändert KI Ihre GRC-Strategie
Rob Schultz / Shutterstock Da Unternehmen Cybersicherheit in ihre GRC (Governance, Risk & Compliance)-Prozesse integrieren, müssen bestehende Programme überarbeitet werden. Nur so lässt sich sicherstellen, dass der zunehmende Einsatz und die Risiken von Generative und Agentic AI Berücksichtigung finden – und Unternehmen compliant bleiben. Die Risiken, die mit KI einhergehen, sind schwierig zu quantifizieren. Aktuelle […]
Risky Business #826 -- A week of AI mishaps and skulduggery
On this week’s show, Patrick Gray, Adam Boileau and James WIlson discuss the week’s cybersecurity news. They cover: Low skill actors compromise 600 Fortinets with AI-generated playbooks Anthropic calls out Chinese AI firms over model distillation Meta’s director of AI safety tells her ClawdBot not to delete her mail… so of course it does Peter […]

New Serv-U bugs extend SolarWinds’ run of high-severity disclosures
SolarWinds continues to be besieged by security issues, this time in its Serv-U managed file transfer server. The software company has released four patches for critical Serv-U remote code execution (RCE) vulnerabilities that could allow attackers to gain root (administrator) access to unpatched servers. These four common vulnerabilities and exposures (CVEs) are rated “critical,” the […]

Fake Zoom meeting silently installs surveillance software, says Malwarebytes
The latest fake Zoom meeting scam silently pushes surveillance software onto the Windows computers of unwitting employees. That’s according to researchers at Malwarebytes, who warn that staff falling for the scam land in a convincing imitation of a Zoom video call. Moments later, an automatic “Update Available” countdown downloads a malicious installer, without asking permission. […]
ISC Stormcast For Wednesday, February 25th, 2026 https://isc.sans.edu/podcastdetail/9824, (Wed, Feb 25th)
Post Content

VMware fixes command injection flaw in Aria Operations
VMware has released patches for several high- and medium-risk vulnerabilities that impact its Aria Operations, Cloud Foundation, Telco Cloud Platform, and Telco Cloud Infrastructure products. The most serious of these flaws allows unauthenticated attackers to execute arbitrary commands on the underlying OS, while another gives authenticated users the ability to elevate to administrator privileges. The […]
Attackers Can Own Your Network in a Matter of Minutes
Jai Vijayan reports: In 2025, cybercriminals needed less time to move from break-in to lateral movement across a network than it takes to watch a typical sitcom. An analysis by CrowdStrike of threat activity last year found attackers took just 29 minutes on average to pivot to other systems after gaining an initial foothold in… […]

What does business email compromise look like?
Business email compromise (BEC) is the digital con dressed to impress. It’s clean, calculated, and ready to fool even the sharpest eyes. These scammers don’t tell on themselves with sloppy hacks. They whisper in familiar voices, posing as your CEO, HR, or a trusted vendor. And, unlike phishing, they’re a precision strike built on inside […]

What are the types of ransomware attacks?
Ransomware isn’t an isolated, potential cyber threat—it’s like a living organism that can shapeshift with multiple strains, tactics, and targets. The cybercriminals behind ransomware attacks run these operations like a business and are motivated to keep up profits at any cost. Their tactics range from quickly locking down an entire network to slowly leaking sensitive […]

Take control: Locking down common endpoint vulnerabilities
Attackers are constantly on the prowl, scoping out vulnerabilities of network-connected devices in your systems. These devices—laptops, desktops, servers, IoT, and more—are like unlocked doors waiting for threat actors to stroll through. And here’s the kicker: many of these vulnerabilities are shockingly common and easily preventable. Let’s break down the weaknesses we most frequently track […]
Key strategic decisions for your AI-ready data center
The infrastructure demands of modern data centers are undergoing a fundamental shift. As organizations deploy increasingly complex AI/ML models, high-performance computing clusters and real-time analytics platforms, traditional scale-up architectures have reached their limits. For CIOs, CTOs and data center managers, the question is no longer whether to adopt scale-out networking, but how to build it […]
The end of AI as an experiment: Designing for what comes next in 2026
After years of building AI-native companies and partnering with Fortune 500 teams through large-scale technology transformations, I’ve watched AI follow a familiar, deceptive path. It starts as a spark of an idea. Then a pilot. Then, almost without ceremony, it becomes part of the machinery that keeps the business running. This transition is no longer […]
Why training budgets are now strategic weapons
Remember when training meant scheduling a conference room, ordering catering, and hoping people would stay awake through PowerPoint slides? Those days are gone. The pandemic didn’t just force us online — it exposed something we suspected but couldn’t prove: our workforce’s skills were decaying faster than any annual training cycle could fix. What replaced that […]
Unlocking the ROI of AI: How enterprises can move from experimentation to execution
Despite the buzz surrounding AI, many organizations struggle to move beyond experimentation and pilot programs to fully scale AI across their enterprises. According to recent industry research conducted by EXL, while 96% of organizations believe scaling their AI initiatives over the next year is very important, companies have successfully integrated AI into less than half […]
A cloud-smart strategy for modernizing mission-critical workloads
Cloud adoption has fundamentally changed how enterprises build and deliver technology. For much of the past decade, cloud strategy was framed around a simple mandate: move fast and move to the cloud. That approach helped organizations modernize development practices and accelerate innovation. But in my experience working with mission-critical systems, I’ve seen that applying the […]
Why Model Context Protocol is suddenly on every executive agenda
Technology leaders are used to watching new standards emerge quietly and then disappear into the plumbing of enterprise IT. But Model Context Protocol (MCP) is following a different trajectory. Over the past year, it has moved from an obscure technical concept into the center of conversations about agentic AI, governance, and security risk, and it’s […]
Sendmarc Releases DMARCbis Fireside Chat Featuring Co-Editor Todd Herr
In a recent DMARCbis fireside chat, email authentication leaders discussed upcoming DMARC changes and how teams can plan for 2026. Sendmarc has released a new fireside chat featuring Todd Herr, Principal Solutions Architect at GreenArrow Email and co-editor of DMARCbis, on the upcoming update to DMARC (Domain-based Message Authentication, Reporting, and Conformance). Led by Dan […]
El CIO de dos empresas: la ideal y la real
El 28 de agosto de 2023, festivo en parte del Reino Unido y uno de los días más intensos del tráfico aéreo del verano, alrededor de 1.500 vuelos fueron cancelados. Aeropuertos colapsados, tripulaciones y aviones fuera de posición, pasajeros atrapados en conexiones imposibles por Europa, y un sector entero exigiendo respuestas. Aerolíneas como Ryanair elevaron […]

RoguePilot Flaw in GitHub Codespaces Enabled Copilot to Leak GITHUB_TOKEN
A vulnerability in GitHub Codespaces could have been exploited by bad actors to seize control of repositories by injecting malicious Copilot instructions in a GitHub issue. The artificial intelligence (AI)-driven vulnerability has been codenamed RoguePilot by Orca Security. It has since been patched by Microsoft following responsible disclosure. “Attackers can craft hidden instructions inside a
Open Redirects: A Forgotten Vulnerability?, (Tue, Feb 24th)
In 2010, OWASP added “Unvalidated Redirects and Forwards” to its Top 10 list and merged it into “Sensitive Data Exposure” in 2013 [owasp1] [owasp2]. Open redirects are often overlooked, and their impact is not always well understood. At first, it does not look like a big deal. The user is receiving a 3xx status code and […]
Greater Pittsburgh Orthopaedic Associates disclosed a 2025 breach, but was there also one in 2024?
Greater Pittsburgh Orthopaedic Associates (GPOA) recently began notifying patients of a breach that occurred on or about August 10, 2025. Although their notification letter to patients does not indicate that this was an incident involving encryption, on August 20, 2025, Ransomhouse had added GPOA to its dark web leak site. Their listing indicated that GPOA… […]
SR-FINRA-2025-005
SR-FINRA-2025-005 K32984 Tue, 02/24/2026 – 10:24 Rule Filing Status: Approved Rule change to amend the FINRA Capital Acquisition Broker (“CAB”) Rules. Event Category Rule Filings Add to Calendar Yes All Day 1 Event Date Wed, 03/25/2026 – 10:00 – Wed, 03/25/2026 – 16:00 America/New York

UAC-0050 Targets European Financial Institution With Spoofed Domain and RMS Malware
A Russia-aligned threat actor has been observed targeting a European financial institution as part of a social engineering attack to likely facilitate intelligence gathering or financial theft, signaling a possible expansion of the threat actor’s targeting beyond Ukraine and into entities supporting the war-torn nation. The activity, which targeted an unnamed entity involved in regional
Lazarus hackers adopt Medusa ransomware for extortion campaigns, targeting healthcare and nonprofits
Anna Ribeiro reports: A joint investigation by the Symantec and Carbon Black Threat Hunter teams details evidence that operators linked to the Lazarus hacker group are deploying Medusa ransomware in ongoing extortion campaigns targeting the U.S. healthcare sector and a Middle East entity, indicating the North Korean threat cluster continues ransomware-driven extortion campaigns despite prior U.S. indictments…. […]
Korean cops charge teens over bike hire breach that exposed data on 4.62M riders
Connor Jones reports: Two South Korean teenagers were this week charged with breaching Seoul’s public bike service, Ttareungyi. Identified only as Persons A and B, the pair, now of high school age, allegedly carried out the attack on Ttareungyi in June 2024 and stole data belonging to most of the service’s registered users. Officials said… […]
Hackers threaten to leak 8 million people’s stolen data if Dutch telecom Odido won’t pay ransom
Daniel Verlaan reports: The cybercriminal group Shinyhunters is responsible for hacking Odido. On the dark web, Odido is being pressured to pay the ransom—over a million euros. “This is your final warning,” the hackers write. “Otherwise, we will leak the data.” Shinyhunters confirmed to RTL Nieuws that it was behind the hack and has shown… […]
Some patients listed as “Charlie Kirk” or dead after major NZ health app MediMap hacked
1News reports: A digital medical records data company has been taken offline after some patient records were modified. Some users’ information had been changed, including to say they were deceased. MediMap is used by some health providers in aged care, disability, hospice and the community to accurately record medication doses. Read more at 1News. MediMap… […]
Gardyn Home Kit
View CSAF Summary Successful exploitation of these vulnerabilities could allow unauthenticated users to access and control edge devices, access cloud-based devices and user information without authentication, and pivot to other edge devices managed in the Gardyn cloud environment. The following versions of Gardyn Home Kit are affected: Home Kit Firmware Gardyn Home Kit Mobile Application […]
Schneider Electric EcoStruxure Building Operation Workstation
View CSAF Summary Schneider Electric is aware of a vulnerability in EcoStruxure Building Operation Workstation and EcoStruxure Building Operation WebStation. [EcoStruxure Building Operation (EBO)](https://www.se.com/ww/en/product-range/62111-ecostruxure-building-operation-software/#overview) is an open and scalable software platform providing insight, control and management of multiple building systems and devices in one mobile-enabled convenient view. It delivers valuable data for decision-making to improve […]
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2026-25108 Soliton Systems K.K. FileZen OS Command Injection Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing […]
InSAT MasterSCADA BUK-TS
View CSAF Summary Successful exploitation of these vulnerabilities may allow remote code execution. The following versions of InSAT MasterSCADA BUK-TS are affected: MasterSCADA BUK-TS vers:all/* (CVE-2026-21410, CVE-2026-22553) CVSS Vendor Equipment Vulnerabilities v3 9.8 InSAT InSAT MasterSCADA BUK-TS Improper Neutralization of Special Elements used in an SQL Command (‘SQL Injection’), Improper Neutralization of Special Elements used […]
Identity Prioritization isn't a Backlog Problem - It's a Risk Math Problem
Most identity programs still prioritize work the way they prioritize IT tickets: by volume, loudness, or “what failed a control check.” That approach breaks the moment your environment stops being mostly-human and mostly-onboarded. In modern enterprises, identity risk is created by a compound of factors: control posture, hygiene, business context, and intent. Any one of […]

Lazarus Group Uses Medusa Ransomware in Middle East and U.S. Healthcare Attacks
The North Korea-linked Lazarus Group (aka Diamond Sleet and Pompilus) has been observed using Medusa ransomware in an attack targeting an unnamed entity in the Middle East, according to a new report by the Symantec and Carbon Black Threat Hunter Team. Broadcom’s threat intelligence division said it also identified the same threat actors mounting an […]
Hundreds of FortiGate Firewalls Hacked in AI-Powered Attacks: AWS
Threat actors relying on AI have been exploiting exposed ports and weak credentials to take over FortiGate devices. The post Hundreds of FortiGate Firewalls Hacked in AI-Powered Attacks: AWS appeared first on SecurityWeek.
Romanian Hacker Pleads Guilty to Selling Access to US State Network
Catalin Dragomir admitted in a US court to selling access to an Oregon state government office’s network. The post Romanian Hacker Pleads Guilty to Selling Access to US State Network appeared first on SecurityWeek.
Autonomous AI Agents Provide New Class of Supply Chain Attack
While this campaign targets crypto wallets and steals money, the methodology has far wider potential that could be used by other attackers. The post Autonomous AI Agents Provide New Class of Supply Chain Attack appeared first on SecurityWeek.
Ukrainian Gets 5 Years in US Prison for Aiding North Korean IT Fraud
Oleksandr Didenko sold the stolen identities of US citizens, allowing North Koreans to get hired using freelance work platforms. The post Ukrainian Gets 5 Years in US Prison for Aiding North Korean IT Fraud appeared first on SecurityWeek.
US Healthcare Diagnostic Firm Says 140,000 Affected by Data Breach
The Everest ransomware group has taken credit for a hacker attack on Vikor Scientific, now called Vanta Diagnostics. The post US Healthcare Diagnostic Firm Says 140,000 Affected by Data Breach appeared first on SecurityWeek.
Anonymous Fénix Members Arrested in Spain
The group’s administrator and moderator were arrested last year, and two other members were arrested this month. The post Anonymous Fénix Members Arrested in Spain appeared first on SecurityWeek.
Reduce downtime, improve efficiency, and kick-start automation with the power of AI
Building systems downtime rarely starts where it is first detected—a minor failure can begin far upstream from where it’s revealed. For example, an HVAC power anomaly can degrade cooling, which then cascades into compute throttling and SLA risk. The good news is that facilities operators can be immediately notified of even the most minor of […]
SAP migrations often fail during planning phase
Most SAP migrations fail before implementation begins. This is the conclusion of the “The State of SAP Migrations” from ISG. The technology research and advisory firm, which surveyed more than 200 business and IT decision-makers from large, international companies with over 1,000 employees, found that less than one in five companies (18%) implement new SAP processes and […]
Stop managing projects. Start allocating capital
When was the last time you killed a “green” project? If the answer is “never,” you are likely still managing projects. If the answer is “last quarter, because we found a 3x better use for that capital,” then you are allocating capital. That distinction isn’t just semantic, it’s the gap between being a cost center […]
How to get AI democratization right
One primary IT objective is to reduce the complexity of using technology to empower business teams to continuously improve operations. In doing so, CIOs help departments become more customer-focused, efficient, and data-driven by leveraging their expertise to define their technical operations, often without IT’s direct involvement. This democratization of technology and data now extends to […]

UnsolicitedBooker Targets Central Asian Telecoms With LuciDoor and MarsSnake Backdoors
The threat activity cluster known as UnsolicitedBooker has been observed targeting telecommunications companies in Kyrgyzstan and Tajikistan, marking a shift from prior attacks aimed at Saudi Arabian entities. The attacks involve the deployment of two distinct backdoors codenamed LuciDoor and MarsSnake, according to a report published by Positive Technologies last week. “The group used several

Bitcoin-Milliarden von Raubkopie-Portal im Visier der Justiz
Urheberrechtsverstöße sind ein einträglisches Geschäft. PXLR Studio – shutterstock.com In Leipzig hat der Prozess um den illegalen Streamingdienst «movie2k.to» und einen Milliardengewinn mit Bitcoins begonnen. Vor dem Landgericht ist der 42 Jahre alte mutmaßliche Kopf des Portals unter anderem wegen gewerbsmäßiger Geldwäsche in 146 Fällen angeklagt. Mit ihm auf der Anklagebank sitzt ein 39-Jähriger, der […]

It’s time to rethink CISO reporting lines
Despite inroads in the C-suite and rising prominence across the business at large, security leaders are still more likely to operate at a remove from the organization’s executive leadership when it comes to reporting structures. According to IANS Research and Artico Search’s 2026 State of the CISO Benchmark Report, 64% of CISOs still report into […]

The rise of the evasive adversary
Since the earliest days of the internet, there has never been a let-up in adversarial activity. According to CrowdStrike’s just-released 12th annual Global Threat Report, malicious activity in cyberspace continues to not only accelerate but also expand its scale and increasingly abuse the trust of targeted organizations. The good news is that, despite discussion of […]

Anthropic’s Claude Code Security rollout is an industry wakeup call
When Anthropic launched a “limited research preview” of its Claude Code Security offering on Friday, Wall Street investors sent the stocks of the largest cybersecurity vendors plunging. But did the Anthropic rollout warrant such a reaction? After all, those companies, including CrowdStrike, Zscaler, Palo Alto Networks and Okta, are preparing their own agentic capabilities, and […]

Anthropic Says Chinese AI Firms Used 16 Million Claude Queries to Copy Model
Anthropic on Monday said it identified “industrial-scale campaigns” mounted by three artificial intelligence (AI) companies, DeepSeek, Moonshot AI, and MiniMax, to illegally extract Claude’s capabilities to improve their own models. The distillation attacks generated over 16 million exchanges with its large language model (LLM) through about 24,000 fraudulent accounts in violation of its terms

OT-Security: Warum der Blick auf Open Source lohnt
Auch im OT-Security-Bereich stellen Open-Source-Lösungen eine kostengünstige Alternative zu kommerziellen Tools dar. MY STOCKERS – Shutterstock.com OT-Security als strategischer Erfolgsfaktor Die zunehmende Digitalisierung und Vernetzung in der industriellen Produktion haben OT-Security (Operational Technology-Sicherheit) zu einem Kernthema in Unternehmen gemacht. Produktionsdaten, SCADA-Systeme (Supervisory Control and Data Acquisition) und vernetzte Maschinen sind in vielen Branchen essenziell – […]

Russian group uses AI to exploit weakly-protected Fortinet firewalls, says Amazon
A Russian-speaking threat actor is using commercial generative AI services to compromise hundreds of Fortinet Fortigate firewalls, warns Amazon Threat Intelligence. Once on the network, the hackers successfully compromised Active Directory at hundreds of organizations, extracted complete credential databases, and targeted backup infrastructure — a potential precursor to ransomware deployment, the report adds. The report, […]
ISC Stormcast For Tuesday, February 24th, 2026 https://isc.sans.edu/podcastdetail/9822, (Tue, Feb 24th)
Post Content
DFPG Investments, LLC Comment On Regulatory Notice 26-02
DFPG Investments, LLC Comment On Regulatory Notice 26-02 fnrw-backend Mon, 02/23/2026 – 17:47 Brad Anderson UT US banderson@diversify.com DFPG Investments, LLC Regulatory Notice 26-02 Core Official Date Mon, 02/23/2026 – 12:00 Comment File DFPG Investments, LLC FINRA Comment Re_ Regulatory Notice 26-02.pdf

APT28 Targeted European Entities Using Webhook-Based Macro Malware
The Russia-linked state-sponsored threat actor tracked as APT28 has been attributed to a new campaign targeting specific entities in Western and Central Europe. The activity, per S2 Grupo’s LAB52 threat intelligence team, was active between September 2025 and January 2026. It has been codenamed Operation MacroMaze. “The campaign relies on basic tooling and the exploitation […]

Wormable XMRig Campaign Uses BYOVD Exploit and Time-Based Logic Bomb
Cybersecurity researchers have disclosed details of a new cryptojacking campaign that uses pirated software bundles as lures to deploy a bespoke XMRig miner program on compromised hosts. “Analysis of the recovered dropper, persistence triggers, and mining payload reveals a sophisticated, multi-stage infection prioritizing maximum cryptocurrency mining hashrate, often destabilizing the victim
Another day, another malicious JPEG, (Mon, Feb 23rd)
In his last two diaries, Xavier discussed recent malware campaigns that download JPEG files with embedded malicious payload[1,2]. At that point in time, I’ve not come across the malicious “MSI image” myself, but while I was going over malware samples that were caught by one of my customer’s e-mail proxies during last week, I found […]

⚡ Weekly Recap: Double-Tap Skimmers, PromptSpy AI, 30Tbps DDoS, Docker Malware & More
Security news rarely moves in a straight line. This week, it feels more like a series of sharp turns, some happening quietly in the background, others playing out in public view. The details are different, but the pressure points are familiar. Across devices, cloud services, research labs, and even everyday apps, the line between normal […]

Hacker stiehlt Daten von Tausenden RTL-Mitarbeitern
Ein Hacker hat sich Zugriff auf Mitarbeiterdaten von RTL verschafft. nitpicker – shutterstock.com Die RTL Group wurde offenbar Opfer einer Cyberattacke. Wie Cybernews berichtet, brüstet sich ein Cyberkrimineller namens LuneBF mit gestohlenen Daten von mehr als 27.000 Mitarbeitern der Mediengruppe. In seinem Darknet-Post behauptet der Angreifer, sich Zugriff auf die Intranet-Website der RTL Group verschafft […]

How Exposed Endpoints Increase Risk Across LLM Infrastructure
As more organizations run their own Large Language Models (LLMs), they are also deploying more internal services and Application Programming Interfaces (APIs) to support those models. Modern security risks are being introduced less from the models themselves and more from the infrastructure that serves, connects and automates the model. Each new LLM endpoint expands the […]

New Arkanix stealer blends rapid Python harvesting with stealthier C++ payloads
A newly uncovered infostealer, suspected to be built with the help of a large language model, is targeting victims with Python and C++ variants, each tailored for a different stage of data theft. Kaspersky researchers discovered a stealer dubbed “Arkanix,” which is capable of harvesting credentials, browser data, cryptocurrency, and banking assets from infected machines. […]
PayPal Data Breach Led to Fraudulent Transactions
PayPal blamed an application error for the exposure of customer personal information for nearly 6 months. The post PayPal Data Breach Led to Fraudulent Transactions appeared first on SecurityWeek.
Mississippi Hospital System Closes All Clinics After Ransomware Attack
A ransomware attack forced the University of Mississippi Medical Center to close all of its roughly three dozen clinics around the state and cancel elective procedures. The post Mississippi Hospital System Closes All Clinics After Ransomware Attack appeared first on SecurityWeek.
Recent RoundCube Webmail Vulnerability Exploited in Attacks
Patched in December 2025, the exploited flaw leads to XSS attacks via the animate tags in SVG documents. The post Recent RoundCube Webmail Vulnerability Exploited in Attacks appeared first on SecurityWeek.
Inside Jack Henry’s bold-but-balanced AI revolution
Figuring out how AI fits into enterprises can feel like a full-time job in itself. No surprise then that 72% of CEOs are the main decision makers on AI–double from a year ago, according to recent Boston Consulting Group research. At Jack Henry, the honor of leading AI strategy falls to Chief Data Officer Keith […]
Does using AI in QA testing increase risk for software companies?
If you want a signal of just how widespread AI has become in software development, consider this: Vibe coding was named Collins Dictionary’s Word of the Year for 2025. The term describes developers quickly prototyping apps using AI tools with minimal planning or structure — a trend that captures the current mood of experimentation with […]
4 tips to help the new innovator’s struggle with AI and traditional code
What most people thought was going to be another year of agentic AI is quickly turning into a more practical focus on simultaneously dealing with probabilistic (AI/ML-driven) and deterministic (traditional rule-based) code. Not a portfolio of both, but a growing number of hybrid applications that need to carefully and skillfully integrate the best of both […]
6 strategies for accelerating IT modernization
Modernization remains a priority for CIOs, with IT executives saying that legacy systems and outdated infrastructure stymie AI adoption, innovation, and ultimately business growth. Indeed, CIOs cite modernization as a key component of their transformation work, which dominates the agenda of most IT leaders — some 77%, according to CIO.com’s 2025 State of the CIO […]

Attackers exploit Ivanti EPMM zero-days to seize control of MDM servers
Attackers are actively exploiting two critical zero-day vulnerabilities in Ivanti’s Endpoint Manager Mobile (EPMM) to gain unauthenticated control of enterprise mobile device management infrastructure and install backdoors engineered to persist even after organizations apply available patches. “Two critical zero-day vulnerabilities (CVE-2026-1281 and CVE-2026-1340) affecting Ivanti Endpoint Manager Mobile (EPMM) are being actively exploited in the wild, affecting […]

Malicious npm Packages Harvest Crypto Keys, CI Secrets, and API Tokens
Cybersecurity researchers have disclosed what they say is an active “Shai-Hulud-like” supply chain worm campaign that has leveraged a cluster of at least 19 malicious npm packages to enable credential harvesting and cryptocurrency key theft. The campaign has been codenamed SANDWORM_MODE by supply chain security company Socket. As with prior Shai-Hulud attack waves, the malicious […]
AI-generated imagery and protection of privacy: EDPB supports joint Global Privacy Assembly’s statement
AI-generated imagery and protection of privacy: EDPB supports joint Global Privacy Assembly’s statement icolonnm Mon, 23/02/2026 – 09:34 23 February 2026 EDPB Brussels, 23 February – EDPB Chair Anu Talus has signed a Joint Statement on AI-Generated Imagery and the Protection of Privacy on behalf of the EDPB. The statement, coordinated by the Global Privacy […]

MuddyWater Targets MENA Organizations with GhostFetch, CHAR, and HTTP_VIP
The Iranian hacking group known as MuddyWater (aka Earth Vetala, Mango Sandstorm, and MUDDYCOAST) has targeted several organizations and individuals mainly located across the Middle East and North Africa (MENA) region as part of a new campaign codenamed Operation Olalampo. The activity, first observed on January 26, 2026, has resulted in the deployment of new […]

13 ways attackers use generative AI to exploit your systems
Artificial intelligence is revolutionizing the technology industry and this is equally true for the cybercrime ecosystem, as cybercriminals are increasingly leveraging generative AI to improve their tactics, techniques, and procedures and deliver faster, stronger, and sneakier attacks. As with legitimate use of emerging AI tools, abuse of generative AI for nefarious ends thus far hasn’t […]
In The Loop May 2025
In the Loop, Tactical Tech’s monthly newsletter, includes new releases, open calls, job opportunities, information about our partners, events, recommended resources and more.
Call for Participants: To AI or not to AI - the uses of AI in digital investigations: hands on training in emerging tools and tactics
Not sure if, when, or how to use AI in your investigative work? Join us in Berlin, November 12–14, 2025, for To AI or Not to AI – The Uses of AI in Digital Investigations, an in-person training focused on practical skills and methods for navigating AI in digital investigations.
In The Loop July 2025
In the Loop, Tactical Tech’s monthly newsletter, includes new releases, open calls, job opportunities, information about our partners, events, recommended resources and more.
Open Call for a Volunteer to join our communications team - European Solidarity Corps Programme
Tactical Tech is opening a year-long paid volunteer opportunity for an individual who wants to learn more about creative interventions that champion a digitally resilient society and join our communications and partnerships team in the Berlin-based office.
Annual Report 2024
In 2024, Tactical Tech responded to a rapidly evolving digital landscape and its accelerating socio-political and environmental impacts, driven largely by the widespread adoption of AI technologies. With a forward-looking, creative, and collaborative approach, we empowered civil society, communities, and organizations to better understand and address the growing influence of digital technologies on democracy, society, […]
[Closed] Communications and Fundraising Coordinator (Marketing & PR Focus) Position
Tactical Tech is seeking an engaging storyteller with creativity and a passion for communications, marketing, and business development.
In The Loop September 2025
In the Loop, Tactical Tech’s monthly newsletter, includes new releases, open calls, job opportunities, information about our partners, events, recommended resources and more.
Call for Participants: “To AI or not to AI - the Role of GenAI in the Context of Digital Investigations” | Online training 11-13 February 2026 | Deadline to apply: 19 January 2026
Are you unsure if, when, and how to use AI in your work? Are you trying to identify what standards, challenges, and risks you need to consider? Join us on 11-13 February 2026, for three half-days of training on “To AI or not to AI – the Role of Generative AI in the Context of […]
In The Loop January 2026
In the Loop, Tactical Tech’s monthly newsletter, includes new releases, open calls, job opportunities, information about our partners, events, recommended resources and more.
Venice Security Emerges From Stealth With $33M Funding for Privileged Access Management
Formerly named Valkyrie, the company’s funding includes $25 million raised in a Series A round. The post Venice Security Emerges From Stealth With $33M Funding for Privileged Access Management appeared first on SecurityWeek.
Nearly 1 Million User Records Compromised in Figure Data Breach
The blockchain-based lender has confirmed a data breach after ShinyHunters leaked over 2GB of data allegedly stolen from the company. The post Nearly 1 Million User Records Compromised in Figure Data Breach appeared first on SecurityWeek.
French Government Says 1.2 Million Bank Accounts Exposed in Breach
The Ministry of Economy reported discovering unauthorized access to the national bank account registry FICOBA. The post French Government Says 1.2 Million Bank Accounts Exposed in Breach appeared first on SecurityWeek.
PromptSpy Android Malware Abuses Gemini AI at Runtime for Persistence
The malware leverages Gemini to analyze on-screen elements and ensure that it remains on the device even after a reboot. The post PromptSpy Android Malware Abuses Gemini AI at Runtime for Persistence appeared first on SecurityWeek.
Chip Testing Giant Advantest Hit by Ransomware
The company is investigating whether any customer or employee data was stolen by hackers. The post Chip Testing Giant Advantest Hit by Ransomware appeared first on SecurityWeek.
FBI: $20 Million Losses Caused by 700 ATM Jackpotting Attacks in 2025
The FBI has confirmed that the Ploutus malware, which has been around for over a decade, is still being used in the wild. The post FBI: $20 Million Losses Caused by 700 ATM Jackpotting Attacks in 2025 appeared first on SecurityWeek.
BeyondTrust Vulnerability Exploited in Ransomware Attacks
CISA has updated its KEV entry for CVE-2026-1731 to alert organizations of exploitation in ransomware attacks. The post BeyondTrust Vulnerability Exploited in Ransomware Attacks appeared first on SecurityWeek.
In Other News: Ransomware Shuts US Clinics, ICS Vulnerability Surge, European Parliament Bans AI
Other noteworthy stories that might have slipped under the radar: Axonius lays off employees, Abu Dhabi conference data leak, HackerOne addresses AI concerns. The post In Other News: Ransomware Shuts US Clinics, ICS Vulnerability Surge, European Parliament Bans AI appeared first on SecurityWeek.
NIST’s Quantum Breakthrough: Single Photons Produced on a Chip
NIST’s single photon chip will likely make QKD an option for a wider range of companies. The post NIST’s Quantum Breakthrough: Single Photons Produced on a Chip appeared first on SecurityWeek.
Critical Grandstream Phone Vulnerability Exposes Calls to Interception
The flaw tracked as CVE-2026-2329 can be exploited without authentication for remote code execution with root privileges. The post Critical Grandstream Phone Vulnerability Exposes Calls to Interception appeared first on SecurityWeek.
Why CIOs need analytics capability to scale AI
AI is accelerating analytics at unprecedented speed. But organizations that mistake AI adoption for analytics capability development are discovering that technology alone does not scale into value. For CIOs, the real differentiator is not AI sophistication, but the strength of the analytics capability that governs how AI is embedded into purposeful decision-making. AI as the […]
The modern desktop reset: why UK IT leaders are rethinking end-user computing
For years, end-user computing (EUC) strategy felt like a balancing act between two imperfect options: continue extending on-premises desktops and legacy VDI, or commit to a cloud initiative that promised long-term value but short-term complexity. In 2026, that middle ground is disappearing. The desktop is being reset—not because IT leaders are chasing the next trend, […]
Cloud DaaS vs on-premises VDI: why the TCO conversation has finally changed
For a long time, the total cost of ownership (TCO) debate between cloud desktops and on-premises VDI felt unresolved. On paper, on-premises environments looked cheaper once the infrastructure was “paid for.” Cloud DaaS promised flexibility, but sceptics questioned whether that flexibility justified ongoing consumption costs. That conversation has shifted decisively. Rising infrastructure costs, licensing complexity, […]
Future-proofing virtual desktops: what IT leaders need to plan for now
If the past few years have taught IT leaders anything, it’s that stability is no longer the default state. Work patterns shift quickly. Security threats evolve constantly. Business priorities change mid-year, not mid-decade. Against that backdrop, many organisations are re-examining a question that once felt settled: how future-ready is our desktop strategy, really? Future-proofing means […]
When cloud-only isn’t realistic: why hybrid desktop strategies are back
For many UK IT leaders, “cloud-only” desktop strategies sounded like the inevitable destination just a few years ago. Azure Virtual Desktop (AVD), Windows 365, and other DaaS platforms promised simplified management, lower CAPEX, and agile access for users everywhere. But in the real world, a pure cloud-only model isn’t always achievable… at least not overnight. […]
IT automation as a strategic advantage
Across UK organisations, the pressure on IT teams is no longer abstract. Skilled resources are limited, recruitment is slow, and experienced engineers are increasingly stretched across security, operations, and transformation initiatives at the same time. Yet expectations on IT have continued to increase. In this environment, time has become one of the most valuable assets […]
3 hidden risks of moving VDI to the cloud and how organisations avoid them
For many UK organisations, the move from on-premises VDI to the cloud feels inevitable. The drivers are well understood: cost pressure, ageing infrastructure, hybrid work, and the need for greater agility. Yet for all its promise, cloud migration still triggers hesitation, especially among risk-averse IT leaders responsible for security, performance, and continuity. That caution is […]
AWS adds Design-first and Bugfix workflows to Kiro
AWS is recognizing that most developers don’t work the way Kiro, its Visual Studio Code–based agentic IDE, forces them too — so it’s adding two new software development workflows to Kiro that meet developers where they are: working on existing projects, fixing bugs. Kiro started out with a vision of helping developers through a process […]
Workers, bosses, disagree on whether AI will create jobs
Senior executives see AI adoption leading to job cuts, while workers say it will increase employment, according to a new survey published by the US National Bureau of Economic Research. Amid so much speculation about the impact of the new technology, NBER’s study is tantalizingly titled “Firm data on AI” — but the data, which […]
SAP Emarsys is dead, long live SAP Engagement Cloud
SAP has changed the name of its SAP Emarsys customer experience offering to SAP Engagement Cloud, signalling — at last — its commitment to integrating it into the core of its enterprise infrastructure. The capabilities of SAP Emarsys will remain available as part of SAP Engagement Cloud, and SAP will add further enhancements. It’s also […]
ISC Stormcast For Monday, February 23rd, 2026 https://isc.sans.edu/podcastdetail/9820, (Mon, Feb 23rd)
Post Content
Top NATO allies believe cyberattacks on hospitals are an act of war. They’re still struggling to fight back.
Maggie Miller, Dana Nickel and Antoaneta Roussi report: NATO countries’ restrained response to hybrid attacks is at odds with public opinion, new polling shows: Broad swaths of the public in key allied countries say actions such as cyberattacks on hospitals should be considered acts of war. The POLITICO Poll, conducted in the United States, Canada,… […]
The hospitality sector continues to be lucrative targets
The hospitality sector has long been a target of hackers, and it’s a global problem. Here are three recent attacks in the news this week: In the U.S.: Choice Hotels International disclosed a breach affecting franchisees and applicants. Its notification letter states that a “skilled person used social engineering” to gain access on January 14,… […]

AI-Assisted Threat Actor Compromises 600+ FortiGate Devices in 55 Countries
A Russian-speaking, financially motivated threat actor has been observed taking advantage of commercial generative artificial intelligence (AI) services to compromise over 600 FortiGate devices located in 55 countries. That’s according to new findings from Amazon Threat Intelligence, which said it observed the activity between January 11 and February 18, 2026. “No exploitation of FortiGate
Ukrainian hackers uncover how Russian drone operators are using Belarus
As seen on InformNapalm: On February 18, 2026, Ukrainian President Volodymyr Zelenskyy imposed sanctions against Belarusian dictator Alyaksandr Lukashenka for his role in escalating and prolonging Russia’s aggressive war against Ukraine. One of the stated reasons is that in the second half of 2025, Russia deployed a system of repeaters for the control of attack… […]
This is how you do it: Dentist speaks out after practice hit by cyber attack
This could be the smallest breach DataBreaches has reported recently, and yet we are covering it instead of other, much bigger breaches that will undoubtedly generate lots of headlines. Why? Because it represents a refreshing example of quick response and transparency. Dr. Joe McEnhill, owner of Grange Dental Care, said the breach occurred on Thursday… […]
Discord’s age verification data has a frontend leak — now what?
Interesting Engineering reports: A newly uncovered flaw in Discord’s age verification rollout has added fresh pressure to the company’s 2026 compliance plans. Security researchers recently found that frontend components tied to identity vendor Persona were accessible on the open web, prompting debate over how securely the platform handles sensitive age checks. The discovery surfaced on… […]
Update Chrome now: Zero-day bug allows code execution via malicious webpages
Pieter Arntz reports: Google has issued a patch for a high‑severity Chrome zero‑day, tracked as CVE‑2026‑2441, a memory bug in how the browser handles certain font features that attackers are already exploiting. CVE-2026-2441 has the questionable honor of being the first Chrome zero-day of 2026. Google considered it serious enough to issue a separate update of the stable… […]

Anthropic Launches Claude Code Security for AI-Powered Vulnerability Scanning
Artificial intelligence (AI) company Anthropic has begun to roll out a new security feature for Claude Code that can scan a user’s software codebase for vulnerabilities and suggest patches. The capability, called Claude Code Security, is currently available in a limited research preview to Enterprise and Team customers. “It scans codebases for security vulnerabilities and […]

CISA Adds Two Actively Exploited Roundcube Flaws to KEV Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday added two security flaws impacting Roundcube webmail software to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation. The vulnerabilities in question are listed below – CVE-2025-49113 (CVSS score: 9.9) – A deserialization of untrusted data vulnerability that allows remote code
Japanese-Language Phishing Emails, (Sat, Feb 21st)
Introduction

EC-Council Expands AI Certification Portfolio to Strengthen U.S. AI Workforce Readiness and Security
With $5.5 trillion in global AI risk exposure and 700,000 U.S. workers needing reskilling, four new AI certifications and Certified CISO v4 help close the gap between AI adoption and workforce readiness. EC-Council, creator of the world-renowned Certified Ethical Hacker (CEH) credential and a global leader in applied cybersecurity education, today launched its Enterprise AI […]

Compromised npm package silently installs OpenClaw on developer machines
A new security bypass has users installing AI agent OpenClaw — whether they intended to or not. Researchers have discovered that a compromised npm publish token pushed an update for the widely-used Cline command line interface (CLI) containing a malicious postinstall script. That script installs the wildly popular, but increasingly condemned, agentic application OpenClaw on […]
Hospitals at Risk of BeyondTrust Ransomware Hacks
Marianne Kolbasuk McGee reports: U.S. federal authorities and industry officials are urging hospitals and clinics to address a critical flaw in BeyondTrust Remote Support and Privileged Remote Access software, which if exploited, could give an attacker a foothold inside a corporate network. The U.S. Department of Health and Human Services in an alert Thursday warned… […]
2023077467801 Avantax Investment Services, Inc. AWC lp.pdf
2023077467801 Avantax Investment Services, Inc. AWC lp.pdf Anonymous (not verified) Fri, 02/20/2026 – 18:05 Case ID 2023077467801 Document Number 3b3093ac Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Fri, 02/20/2026 – 12:00 Related Content Off Attachment 2023077467801 Avantax Investment Services, Inc. AWC lp.pdf
Resource: Privacy Law Directory — Codamail
Regular readers of my companion privacy-oriented site, PogoWasRight.org, may recall that the site recently noted The Data Broker Directory: Who has your data, where they got it, and who they sell it to by Codamail’s Stephen K. Gielda of Packetderm. Instead of taking a well-deserved break after all the work he did to compile that… […]
Romanian hacker faces up to 7 years for breaching Oregon emergency management department
Jonathan Greig reports: A 45-year-old Romanian national pleaded guilty this week to hacking into computers at Oregon’s Department of Emergency Management in June 2021 and selling the access he obtained for $3,000 worth of Bitcoin. Catalin Dragomir also hacked into 10 other U.S. companies, causing financial losses of at least $250,000. He was arrested in… […]

‘Starkiller’ Phishing Service Proxies Real Login Pages, MFA
Most phishing websites are little more than static copies of login pages for popular online destinations, and they are often quickly taken down by anti-abuse activists and security firms. But a stealthy new phishing-as-a-service offering lets customers sidestep both of these pitfalls: It uses cleverly disguised links to load the target brand’s real website, and […]
2024083942501 Kyle Lindner CRD 5421697 AWC vrp.pdf
2024083942501 Kyle Lindner CRD 5421697 AWC vrp.pdf Anonymous (not verified) Fri, 02/20/2026 – 13:15 Case ID 2024083942501 Document Number 88fd7acc Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals Kyle Lindner Action Date Fri, 02/20/2026 – 12:00 Related Content Off Attachment 2024083942501 Kyle Lindner CRD 5421697 AWC vrp.pdf Individual CRD 5421697

Don’t trust TrustConnect: This fake remote support tool only helps hackers
After breaking into a system, crooks often install legitimate remote admin tools to keep a foothold on the network — with the risk that the tool’s vendor spots them and locks them out. Now they have a new option: a fake remote monitoring and management (RMM) tool, complete with serious-looking online storefront, built just for […]

BeyondTrust Flaw Used for Web Shells, Backdoors, and Data Exfiltration
Threat actors have been observed exploiting a recently disclosed critical security flaw impacting BeyondTrust Remote Support (RS) and Privileged Remote Access (PRA) products to conduct a wide range of malicious actions, including deploying VShell and The vulnerability, tracked as CVE-2026-1731 (CVSS score: 9.9), allows attackers to execute operating system commands in the context of the
117th Plenary meeting
117th Plenary meeting icolonnm Fri, 20/02/2026 – 16:30 18 March 2026 Remote

Cline CLI 2.3.0 Supply Chain Attack Installed OpenClaw on Developer Systems
In yet another software supply chain attack, the open-source, artificial intelligence (AI)-powered coding assistant Cline CLI was updated to stealthily install OpenClaw, a self-hosted autonomous AI agent that has become exceedingly popular in the past few months. “On February 17, 2026, at 3:26 AM PT, an unauthorized party used a compromised npm publish token to […]
A single compromised account gave hackers access to 1.2 million French banking records
Emma Woollacott reports: Credentials stolen from a single government official enabled threat actors to access a French national database containing data on more than 1.2 million bank accounts. The attackers were able to access the Fichier des Comptes Bancaires et Assimilés (FICOBA) database, which contains files on all bank accounts opened in France. Stolen credentials… […]

KI und Komplexität als Brandbeschleuniger für Cyberkriminelle
Cyberangriffe werden immer schneller, wodurch sich die Zeitspanne zwischen der ersten Kompromittierung und den negativen Folgen verkürzt. andrey_l – shutterstock.com Der Einzug von KI hat den benötigten Zeitaufwand für Cyberattacken massiv verkürzt, so dass menschliche Verteidiger nicht mehr mithalten können. So lautet das vielleicht wenig überraschende Ergebnis des 2026 Global Incident Response Report von Palo […]
CISA Adds Two Known Exploited Vulnerabilities to Catalog
CISA has added two new vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2025-49113 RoundCube Webmail Deserialization of Untrusted Data Vulnerability CVE-2025-68461 RoundCube Webmail Cross-site Scripting Vulnerability These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise. Binding Operational […]
ClickFix Campaign Abuses Compromised Sites to Deploy MIMICRAT Malware
Cybersecurity researchers have disclosed details of a new ClickFix campaign that abuses compromised legitimate sites to deliver a previously undocumented remote access trojan (RAT) called MIMICRAT (aka AstarionRAT). “The campaign demonstrates a high level of operational sophistication: compromised sites spanning multiple industries and geographies serve as delivery infrastructure, a multi-stage

Identity Cyber Scores: The New Metric Shaping Cyber Insurance in 2026
With one in three cyber-attacks now involving compromised employee accounts, insurers and regulators are placing far greater emphasis on identity posture when assessing cyber risk. For many organizations, however, these assessments remain largely opaque. Elements such as password hygiene, privileged access management, and the extent of multi-factor authentication (MFA) coverage are

Ukrainian National Sentenced to 5 Years in North Korea IT Worker Fraud Case
A 29-year-old Ukrainian national has been sentenced to five years in prison in the U.S. for his role in facilitating North Korea’s fraudulent information technology (IT) worker scheme. In November 2025, Oleksandr “Alexander” Didenko pleaded guilty to wire fraud conspiracy and aggravated identity theft for stealing the identities of U.S. citizens and selling them to […]

Sonderkommission ermittelt zu Cyberangriff auf Kunstsammlungen Dresden
Die Staatlichen Kunstsammlungen Dresden waren Ziel einer Cyberattacke. Staatliche Kunstsammlungen Dresden Nach dem Cyberangriff auf die Staatlichen Kunstsammlungen Dresden in diesem Januar hat das Landeskriminalamt Sachsen (LKA) eine Sonderkommission gegründet. Diese führe auch die Ermittlungen unter Sachleitung der Generalstaatsanwaltschaft Dresden, wie die Ermittlungsbehörde mitteilte. Weitergehende Angaben machte die Generalstaatsanwaltschaft nicht. Am 21. Januar waren die […]

FBI Reports 1,900 ATM Jackpotting Incidents Since 2020, $20M Lost in 2025
The U.S. Federal Bureau of Investigation (FBI) has warned of an increase in ATM jackpotting incidents across the country, leading to losses of more than $20 million in 2025. The agency said 1,900 ATM jackpotting incidents have been reported since 2020, out of which 700 took place last year. In December 2025, the U.S. Department […]

PayPal launches latest struggle to get rid of SMS for MFA
When PayPal started emailing customers this month that it was backing off unencrypted SMS for multifactor authentication (MFA) at login, it came with the typical approach-avoidance asterisk. The financial services giant signaled that it was turning the page on the much-maligned authentication method while simultaneously offering no timeline and assuring customers SMS wouldn’t entirely go […]

10 Passwordless-Optionen für Unternehmen
Um Passwörter hinter sich zu lassen, gibt es bessere Lösungen. Wir zeigen Ihnen zehn. Foto: Raffi Ilham Pratama – shutterstock.com Passwörter sind seit Jahrzehnten der Authentifizierungsstandard für Computersysteme, obwohl sie sich immer wieder aufs Neue als anfällig für diverse Cyberangriffsformen erwiesen haben und kompromittierte Benutzerkonten auf regelmäßiger Basis zum Einfallstor für kriminelle Hacker werden. Ein […]
ISC Stormcast For Friday, February 20th, 2026 https://isc.sans.edu/podcastdetail/9818, (Fri, Feb 20th)
Post Content

New phishing campaign tricks employees into bypassing Microsoft 365 MFA
Another device code phishing campaign that abuses OAuth device registration to bypass multifactor authentication login protections has been discovered. Researchers at KnowBe4 say the campaign is largely targeting North American businesses and professionals by tricking unwitting employees into clicking a link in an email from a threat actor. The message purports to be about a […]
Risky Biz Soap Box: The lethal trifecta of AI risks
There’s a lethal trifecta of AI risks: access to private data, exposure to untrusted content, and external communication. In this conversation, Risky Business host Patrick Gray chats with Josh Devon, the co-founder of Sondera, about how to best address these risks. There is no magic solution to this problem. AI models mix code and data, […]

US dominance of agentic AI at the heart of new NIST initiative
This week, the US National Institute of Standards and Technology (NIST) announced a new listening exercise, the AI Agent Standards Initiative, which it hopes will provide a roadmap for addressing agentic AI hurdles and, it said, ensure that the technology “is widely adopted with confidence.” AI agents, which have now ascended to the status of […]
2022073427701 J.P. Morgan Securities LLC CRD 79 AWC ks.pdf
2022073427701 J.P. Morgan Securities LLC CRD 79 AWC ks.pdf Anonymous (not verified) Thu, 02/19/2026 – 15:50 Case ID 2022073427701 Document Number a2133230 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Thu, 02/19/2026 – 12:00 Related Content Off Attachment 2022073427701 J.P. Morgan Securities LLC CRD 79 AWC ks.pdf
2023079905502 Peter Thomas Lawrence CRD 2695687 AWC ks.pdf
2023079905502 Peter Thomas Lawrence CRD 2695687 AWC ks.pdf Anonymous (not verified) Thu, 02/19/2026 – 15:35 Case ID 2023079905502 Document Number 6ec774de Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals Peter Thomas Lawrence Action Date Thu, 02/19/2026 – 12:00 Related Content Off Attachment 2023079905502 Peter Thomas Lawrence CRD 2695687 AWC ks.pdf Individual CRD 2695687
Under the Hood of DynoWiper, (Thu, Feb 19th)
[This is a Guest Diary contributed by John Moutos]
22-02653.pdf
22-02653.pdf Anonymous (not verified) Thu, 02/19/2026 – 12:05 Case ID 22-02653 Forum FINRA Document Type Award Claimants Heidi Voeller Michael Voeller Respondents John Lowry Kim Monchik Spartan Capital Securities, LLC Neutrals Mark L Miller Julia Yael Ramos James Paul Young Hearing Site Bismarck, ND Award Document 22-02653.pdf Documentum DocID e6753296 Award Date Official Wed, 02/18/2026 […]

Six flaws found hiding in OpenClaw’s plumbing
Security researchers have uncovered six high-to-critical flaws affecting the open-source AI agent framework OpenClaw, popularly known as a “social media for AI agents.” The flaws were discovered by Endor Labs as its researchers ran the platform through an AI-driven static application security testing (SAST) engine designed to follow how data actually moves through the agentic […]
Welker OdorEyes EcoSystem Pulse Bypass System with XL4 Controller
View CSAF Summary Successful exploitation of this vulnerability could result in an over- or under-odorization event. The following versions of Welker OdorEyes EcoSystem Pulse Bypass System with XL4 Controller are affected: OdorEyes EcoSystem Pulse Bypass System with XL4 Controller vers:all/* (CVE-2026-24790) CVSS Vendor Equipment Vulnerabilities v3 8.2 Welker Welker OdorEyes EcoSystem Pulse Bypass System with […]
EnOcean SmartServer IoT
View CSAF Summary Successful exploitation of these vulnerabilities could allow an attacker to remotely execute arbitrary code and bypass ASLR. The following versions of EnOcean SmartServer IoT are affected: SmartServer IoT <=4.60.009 (CVE-2026-20761, CVE-2026-22885) CVSS Vendor Equipment Vulnerabilities v3 8.1 EnOcean Edge Inc EnOcean SmartServer IoT Improper Neutralization of Special Elements used in a Command […]
Jinan USR IOT Technology Limited (PUSR) USR-W610
View CSAF Summary Successful exploitation of these vulnerabilities could result in authentication being disabled, a denial-of-service condition, or an attacker stealing valid user credentials, including administrator credentials. The following versions of Jinan USR IOT Technology Limited (PUSR) USR-W610 are affected: USR-W610 <=3.1.1.0 (CVE-2026-25715, CVE-2026-24455, CVE-2026-26049, CVE-2026-26048) CVSS Vendor Equipment Vulnerabilities v3 9.8 Jinan USR IOT […]
Valmet DNA Engineering Web Tools
View CSAF Summary Successful exploitation of this vulnerability could allow an unauthenticated attacker to manipulate the web maintenance services URL to achieve arbitrary file read access. The following versions of Valmet DNA Engineering Web Tools are affected: Valmet DNA Engineering Web Tools <=C2022 (CVE-2025-15577) CVSS Vendor Equipment Vulnerabilities v3 8.6 Valmet Valmet DNA Engineering Web […]
Hackers can turn Grok, Copilot into covert command-and-control channels, researchers warn
Enterprise security teams racing to enable generative AI tools may be overlooking a new risk: attackers can abuse web-based AI assistants such as Grok and Microsoft Copilot to quietly relay malware communications through domains that are often exempt from deeper inspection. The technique, outlined by Check Point Research (CPR), exploits the web-browsing and URL-fetch capabilities […]
ISC Stormcast For Thursday, February 19th, 2026 https://isc.sans.edu/podcastdetail/9816, (Thu, Feb 19th)
Post Content
CISA Adds Two Known Exploited Vulnerabilities to Catalog
CISA has added two new vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2021-22175 GitLab Server-Side Request Forgery (SSRF) Vulnerability CVE-2026-22769 Dell RecoverPoint for Virtual Machines (RP4VMs) Use of Hard-coded Credentials Vulnerability These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to […]
EDPB identifies challenges hindering the full implementation of the right to erasure
EDPB identifies challenges hindering the full implementation of the right to erasure icolonnm Wed, 18/02/2026 – 11:18 18 February 2026 EDPB Brussels, 18 February – The European Data Protection Board (EDPB) has adopted a report on its Coordinated Enforcement Framework (CEF) action on the right to be forgotten (Art.17 GDPR). The Board selected this topic as it is one […]
Coordinated Enforcement Action, implementation of the right to erasure by controllers
Coordinated Enforcement Action, implementation of the right to erasure by controllers icolonnm Wed, 18/02/2026 – 11:15 18 February 2026 Implementation of the right to erasure by controllers report 431.6KB English Download file 1 Annex 1: National Reports on the CEF Right to erasure 2.2MB English Download file 2 Topics: Cooperation between authorities GDPR enforcement EDPB […]
Report on stakeholder event on anonymisation and pseudonymisation of 12 December 2025
Report on stakeholder event on anonymisation and pseudonymisation of 12 December 2025 icolonnm Wed, 18/02/2026 – 10:14 18 February 2026 Report on stakeholder event 210.1KB English Download Topics: Anonymization
Tracking Malware Campaigns With Reused Material, (Wed, Feb 18th)
A few days ago I wrote a diary called “Malicious Script Delivering More Maliciousness”[1]. In the malware infection chain, there was a JPEG picture that embedded the last payload delimited with “BaseStart-” and “-BaseEnd” tags.
Risky Business #825 -- Palo Alto Networks blames it on the boogie
On this week’s show, Patrick Gray, Adam Boileau and James WIlson discuss the week’s cybersecurity news. They cover: Palo Alto threat researchers want to attribute to China, but management says shush An increasing proportion of ransomware is data extortion. Is this good? Cambodia says it’s going to dismantle scam compounds CISA sufferers through yet another […]
ISC Stormcast For Wednesday, February 18th, 2026 https://isc.sans.edu/podcastdetail/9814, (Wed, Feb 18th)
Post Content
CISA Adds Four Known Exploited Vulnerabilities to Catalog
CISA has added four new vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2008-0015 Microsoft Windows Video ActiveX Control Remote Code Execution Vulnerability CVE-2020-7796 Synacor Zimbra Collaboration Suite (ZCS) Server-Side Request Forgery Vulnerability CVE-2024-7694 TeamT5 ThreatSonar Anti-Ransomware Unrestricted Upload of File with Dangerous Type Vulnerability CVE-2026-2441 Google Chromium CSS […]
Delta Electronics ASDA-Soft
View CSAF Summary Successful exploitation of this vulnerability may allow an attacker to write arbitrary data beyond the bounds of a stack-allocated buffer, leading to the corruption of a structured exception handler (SEH). The following versions of Delta Electronics ASDA-Soft are affected: ASDA-Soft <=7.2.0.0 (CVE-2026-1361) CVSS Vendor Equipment Vulnerabilities v3 7.8 Delta Electronics Delta Electronics […]
GE Vernova Enervista UR Setup
View CSAF Summary Successful exploitation of these vulnerabilities may allow code execution with elevated privileges. The following versions of GE Vernova Enervista UR Setup are affected: Enervista UR Setup <8.70 (CVE-2026-1762, CVE-2026-1763) CVSS Vendor Equipment Vulnerabilities v3 7.8 GE Vernova GE Vernova Enervista UR Setup Uncontrolled Search Path Element, Path Traversal: ‘…/…//’ Background Critical Infrastructure […]
Honeywell CCTV Products
View CSAF Summary Successful exploitation of this vulnerability could lead to account takeovers and unauthorized access to camera feeds; an unauthenticated attacker may change the recovery email address, potentially leading to further network compromise. The following versions of Honeywell CCTV Products are affected: I-HIB2PI-UL 2MP IP 6.1.22.1216 (CVE-2026-1670) SMB NDAA MVO-3 WDR_2MP_32M_PTZ_v2.0 (CVE-2026-1670) PTZ WDR […]
Meeting Data Protection Working Group, Council
Meeting Data Protection Working Group, Council icolonnm Tue, 17/02/2026 – 12:19 27 February 2026 Deputy Chair, Jelena Virant Burnik Brussels
Fake Incident Report Used in Phishing Campaign, (Tue, Feb 17th)
This morning, I received an interesting phishing email. I’ve a “love & hate” relation with such emails because I always have the impression to lose time when reviewing them but sometimes it’s a win because you spot interesting “TTPs” (“tools, techniques & procedures”). Maybe one day, I’ll try to automate this process!
ISC Stormcast For Tuesday, February 17th, 2026 https://isc.sans.edu/podcastdetail/9812, (Tue, Feb 17th)
Post Content
Reply to the civil society open letter in response on recent spyware abuse cases in the EU
Reply to the civil society open letter in response on recent spyware abuse cases in the EU icolonnm Mon, 16/02/2026 – 10:15 16 February 2026 Reply to the civil society open letter 249KB English Download
2026 64-Bits Malware Trend, (Mon, Feb 16th)
In 2022 (time flies!), I wrote a diary about the 32-bits VS. 64-bits malware landscape[1]. It demonstrated that, despite the growing number of 64-bits computers, the “old-architecture” remained the standard. In the SANS malware reversing training (FOR610[2]), we quickly cover the main differences between the two architectures. One of the conclusions is that 32-bits code is […]
Making GDPR compliance easier through new initiatives: a key focus of the EDPB work programme 2026-2027
Making GDPR compliance easier through new initiatives: a key focus of the EDPB work programme 2026-2027 ipayotfr Thu, 12/02/2026 – 16:41 13 February 2026 EDPB Brussels, 13 February – The EDPB has recently adopted its work programme for 2026-2027, which is grounded in the four pillars of the EDPB strategy 2024-2027. The work programme is […]
EDPB Report on the public consultation on helpful templates for organisations to facilitate their GDPR compliance
EDPB Report on the public consultation on helpful templates for organisations to facilitate their GDPR compliance ipayotfr Thu, 12/02/2026 – 16:00 12 February 2026 EDPB Report on the public consultation on helpful templates for organisations to facilitate their GDPR compliance 118KB English Download Topics: GDPR EDPB Public consultation: Help make GDPR compliance easy for organisations: […]

EDPB work programme 2026-2027: easing compliance and strengthening cooperation across the evolving digital landscape
EDPB work programme 2026-2027: easing compliance and strengthening cooperation across the evolving digital landscape icolonnm Thu, 12/02/2026 – 10:53 12 February 2026 EDPB Brussels, 12 February – During its latest plenary, the EDPB adopted its work programme for 2026-2027. This is the second work programme to support the implementation of the EDPB strategy 2024-2027*. The […]
EDPB Work Programme 2026-2027
EDPB Work Programme 2026-2027 icolonnm Thu, 12/02/2026 – 10:33 12 February 2026 Work Programme 2026-2027 344.6KB English Download
Kimwolf Botnet Swamps Anonymity Network I2P
For the past week, the massive “Internet of Things” (IoT) botnet known as Kimwolf has been disrupting The Invisible Internet Project (I2P), a decentralized, encrypted communications network designed to anonymize and secure online communications. I2P users started reporting disruptions in the network around the same time the Kimwolf botmasters began relying on it to evade […]
Risky Business #824 -- Microsoft's Secure Future is looking a bit wobbly
On this week’s show Patrick Gray and Adam Boileau discuss the week’s cybersecurity news, including: Microsoft reshuffles security leadership. It doesn’t spark joy. Russia is hacking the Winter Olympics. Again. But y tho? China-linked groups are keeping busy, hacking telcos in Norway, Singapore and dozens of others Campaigns underway targeting Ivanti, BeyondTrust and SolarWinds products […]

Patch Tuesday, February 2026 Edition
Microsoft today released updates to fix more than 50 security holes in its Windows operating systems and other software, including patches for a whopping six “zero-day” vulnerabilities that attackers are already exploiting in the wild. Zero-day #1 this month is CVE-2026-21510, a security feature bypass vulnerability in Windows Shell wherein a single click on a […]
Risky Business #823 -- Humans impersonate clawdbots impersonating humans
Patrick Gray and Adam Boileau are joined by the newest guy on the Risky Business Media team, James WIlson. They discuss the week’s cybersecurity news, including: Notepad++ update supply chain attack has been attributed to China The AI agent future is even more stupid than expected; behold the OpenClaw/Clawdbot/Moltbook mess The Epstein files claim he […]

Please Don’t Feed the Scattered Lapsus ShinyHunters
A prolific data ransom gang that calls itself Scattered Lapsus ShinyHunters (SLSH) has a distinctive playbook when it seeks to extort payment from victim firms: Harassing, threatening and even swatting executives and their families, all while notifying journalists and regulators about the extent of the intrusion. Some victims reportedly are paying — perhaps as much […]