오픈텍스트 “UCMDB 기반 통합 가시성으로 IT 운영 효율 높여”
오픈텍스트에 따르면, 디지털 전환과 AI 도입 확산으로 기업 IT 환경이 복잡해지면서, 여러 시스템에 분산된 운영 데이터를 통합 관리하고 서비스 영향도를 실시간으로 파악하는 역량의 중요성이 커지고 있다. 특히 금융·제조·공공 분야에서는 장애 대응 속도와 운영 안정성 확보가 주요 과제로 부각되고 있다. 오픈텍스트는 여러 고객사가 유니버설 디스커버리(Universal Discovery)와 CMDB를 활용해 IT 자산과 서비스 간 연관 관계를 자동으로 분석·시각화하고 […]
Companies are spending billions to train workers for AI. Most of it will fail
Walk into almost any boardroom this year, and the agenda is identical: How do we close the AI gap? Leaders are projected to spend billions to ensure their workforce doesn’t fall behind. They are confident. They are aggressive. And, in most cases, they’re failing. According to Mercer’s 2026 Global Talent Trends study, 63% of executives […]
The experience tax: How annoying software is quietly eroding customer loyalty
Every software system charges customers an experience tax. It may not appear on an invoice, but customers pay it in wasted time, broken flow, repeated work and lost confidence. When that tax exceeds their tolerance, they often leave without telling you why. At first, customer utilization dips slightly with no clear explanation. Over time, customers […]
How Georgia-Pacific drives autonomous decision-making
As VP of data and analytics at Atlanta-based Georgia-Pacific, Matt Robuck gives a multitude of insights to the business. In the past, these would’ve been delivered as dashboards and reports, but over the last three years, with the proliferation of AI, he and his team of over 180 engineers have been questioning how they can […]
Why enterprise AI initiatives stall — and what CIOs can do about it
CIOs who launched AI projects over the past year that didn’t deliver on expectations, or failed entirely, aren’t alone. Investments in AI projects have surged, but nearly half of enterprises have struggled to demonstrate business value, according research from Gartner. “People jumped in with unrealistic expectations, and that’s where the biggest disappointments are coming from,” […]
When GPU utilization lies: The FinOps blind spot in secure AI training
Enterprise cloud teams are trained to act on utilization data. If a virtual machine is idle, resize it.If storage is overallocated, reclaim it.If a GPU appears underused, move the job to a smaller instance. That logic is central to modern FinOps. It helps organizations reduce waste, improve forecasting and keep cloud spending under control. But […]
The AI talent problem CIOs cannot delegate to HR
As enterprises accelerate AI adoption, many CIOs remain focused on platforms, governance and scale. But the real competitive risk may be elsewhere. Top AI talent is increasingly choosing employers not only for pay but also for access to compute, freedom to experiment and the ability to operate at full leverage. If HR and leadership teams […]
La estrategia de IA pierde talento sin personas en el centro
Cuestión de fallos en la medición. Así quiere comenzar Alberto Bellé, analista principal de Foundry España, este reportaje dedicado a las estrategias de IA de las empresas y el peligro de desarrollarlas sin poner a las personas en el centro. Gartner lo advierte en uno de sus últimos informes: para 2027, el 50% de las […]
How to get ahead of digital friction before it impacts your profitability
For most organizations, IT performance is measured by how fast problems get fixed. Response times, ticket volumes, and mean time to resolution. These are the metrics that have traditionally defined whether IT is doing its job. But what about the issues that never get reported? A missed deadline caused by an app malfunction. A deal […]
Netherlands blocks Kyndryl’s Solvinity acquisition citing public risk
Adding a new twist to growing tensions over American tech influence in Europe, the Dutch government has moved to block US-based Kyndryl’s bid to acquire Solvinity, the Dutch IT company behind authentication app DigiD, among other things. IT services giant Kyndryl announced in November an agreement to purchase Solvinity, which provides secure managed cloud services […]
Iranian APT Targets Aviation, Software Companies With Updated Tools
Nimbus Manticore has continued its operations during and after the US military campaign against Iran. The post Iranian APT Targets Aviation, Software Companies With Updated Tools appeared first on SecurityWeek.
AppOmni’s Marlin AI Brings Autonomous Investigation to SaaS Security
Marlin AI automatically analyzes SaaS misconfigurations, investigates related activity across enterprise environments, and recommends remediation steps — while stopping short of fully autonomous corrective action. The post AppOmni’s Marlin AI Brings Autonomous Investigation to SaaS Security appeared first on SecurityWeek.
Anthropic Releases New Claude Sandbox, Security Guidance Plugin
The AI giant says the new plugin, which helps developers find vulnerabilities as they write code, has been used extensively internally. The post Anthropic Releases New Claude Sandbox, Security Guidance Plugin appeared first on SecurityWeek.
CISA Urges Immediate Patching of Exploited LiteSpeed cPanel Plugin Zero-Day
Resolved last week, the vulnerability was exploited in the wild as a zero-day to execute scripts with root privileges. The post CISA Urges Immediate Patching of Exploited LiteSpeed cPanel Plugin Zero-Day appeared first on SecurityWeek.
FBI: Hackers Sending Operatives in Person to Insert USB Drives and Steal Data
The FBI has issued an alert warning of Silent Ransom Group attacks targeting law firms. The post FBI: Hackers Sending Operatives in Person to Insert USB Drives and Steal Data appeared first on SecurityWeek.
LA Metro Cyberattack Linked to Iranian State-Sponsored Hackers
The attack was claimed by a hacktivist group, but evidence showed it used infrastructure linked to Iranian government threat actors. The post LA Metro Cyberattack Linked to Iranian State-Sponsored Hackers appeared first on SecurityWeek.
GlassWorm Botnet Disrupted
Security firms took down all four command-and-control (C&C) channels used by the GlassWorm malware. The post GlassWorm Botnet Disrupted appeared first on SecurityWeek.
‘SymJack’ Attack Turns AI Coding Agents Into Supply Chain Attack Delivery Systems
Malicious repositories and disguised symlinks can trick AI coding agents into silently installing attacker-controlled MCP servers capable of stealing secrets, compromising CI pipelines, and deploying malicious code. The post ‘SymJack’ Attack Turns AI Coding Agents Into Supply Chain Attack Delivery Systems appeared first on SecurityWeek.
The Credential Crisis: How Stolen Credentials Defeat Modern Security
As AI accelerates phishing, session hijacking, and credential abuse, security teams are racing to close the gap between attacker speed and defensive response. The post The Credential Crisis: How Stolen Credentials Defeat Modern Security appeared first on SecurityWeek.
Lastwall Raises $11.5 Million for Quantum-Resilient Identity Platform
The new funding, led by BDC Capital’s StrongNorth Fund, will accelerate Lastwall’s North American expansion. The post Lastwall Raises $11.5 Million for Quantum-Resilient Identity Platform appeared first on SecurityWeek.
The NSA, ‘Mythos’ and the quiet emergence of AI cyber doctrine
For most of my career running security operations, the shape of cyber conflict has been defined by who could move faster than the other side. Faster at identifying a vulnerability, faster at patching, faster at detecting, faster at responding. The last few months have made me reevaluate that framing. Speed still matters. It just no […]
AI Chatbot Recommendations Redirect Users to Cryptojacking Malware Sites
Microsoft has warned of an active cryptojacking campaign that makes use of artificial intelligence (AI) chatbot interactions as a mechanism for surfacing malicious download sites. “This emerging delivery technique extends social engineering beyond conventional search results and increases the visibility of malicious software recommendations,” Microsoft Defender Experts and the Microsoft
DSPM buyer’s guide: Top 10 data security posture management tools
Data security posture management (DSPM) explained Data security posture management (DSPM) tools help security teams examine their entire data environment to find shadow data, reducing the risk of data loss. Tracking down sensitive data across both cloud and on-premises systems can be vexing. Each environment presents its own challenges. Given the dynamic and ephemeral nature […]
Risky Business #839 -- TeamPCP stole GitHub's internal repos
On this week’s show Patrick Gray, Adam Boileau and James Wilson discuss the week’s cybersecurity news. They cover: TeamPCP breached GitHub’s internal repos. Now what? Some absolute plonker glued Coruna to a hijacked npm package CISA is worried about about open source and wants third party submissions for KEV AI infrastructure is “systemically” insecure Much, […]
ISC Stormcast For Wednesday, May 27th, 2026 https://isc.sans.edu/podcastdetail/9946, (Wed, May 27th)
Post Content
Microsoft previews automatic device isolation in Defender for Endpoint
Microsoft is previewing a new automatic device isolation capability in Defender for Endpoint’s auto attack disruption tool to help security pros contain cyber attacks in progress on their IT networks. The company announced the capability earlier this month in a column about new features in Defender. There’s no word on when automatic device isolation will […]
22-02022.pdf
22-02022.pdf Anonymous (not verified) Tue, 05/26/2026 – 17:10 Case ID 22-02022 Forum FINRA Document Type Award Claimants Roobik Thorossian Respondents Fidelity Brokerage Services LLC Neutrals Paula K. Konikoff Maureen Weston Linda M Iannone Hearing Site Los Angeles, CA Award Document 22-02022.pdf Documentum DocID 92a9448f Award Date Official Tue, 05/26/2026 – 12:00 Related Content Off Claimant […]
Las trampas de modernización de TI que los CIO deben evitar
En un contexto de migración a la nube, transformación digital y, ahora, de impulso hacia la adopción de IA, los CIO se enfrentan a la necesidad real de ejecutar de forma adecuada la modernización; no obstante, el sector pone de manifiesto que los proyectos de modernización pueden no cumplir con los beneficios prometidos y sufrir […]
xAI-앤트로픽 계약, AI 컴퓨팅 ‘독립 사업’ 부상 신호탄
일론 머스크가 이끄는 xAI는 경쟁사인 앤트로픽에 대규모 AI 연산 역량을 제공하기로 합의했다. 공개된 IPO 자료에 따르면 앤트로픽은 xAI의 ‘콜로서스(Colossus)’ 및 ‘콜로서스 II(Colossus II)’ 인프라 클러스터를 통해 2029년 5월까지 컴퓨팅 서비스를 구매하기로 했으며, 계약 규모는 월 약 12억 5,000만 달러(약 1조 8,000억 원)에 달한다. 이번 계약이 주목받는 이유는 앤트로픽이 첨단 AI 모델 및 기업용 AI 서비스 […]
AI 도입 막는 ‘데이터 문제’ 7가지 징후…기업은 왜 준비되지 않았나
AI는 방대한 양의 정확한 데이터에 접근할 수 없다면 아무런 의미가 없다. 하지만 현실에서는 많은 기업이 AI 애플리케이션에 활용하기 어려운 방식으로 저장된 데이터를 떠안고 있는 상황이다. 글로벌 컨설팅 기업 EY의 세무 기술 및 혁신 리더 대런 캠벨은 “AI 데이터 비호환성 문제는 AI에 적극 투자하는 조직에서도 광범위하게 나타나고 있다”고 지적했다. 이어 “생성형 AI와 에이전틱 AI 도입은 빠르게 […]
Why scaling AI requires both left-brain rigor and right-brain ingenuity
Neuroscience often describes the human brain as operating through two complementary modes of thinking, commonly referred to as the left and right brains. While modern neuroscience debates the strict division between these hemispheres, the metaphor remains useful and highly relevant, particularly in an enterprise context, to illustrate two distinct cognitive approaches. The left hemisphere is […]
From Process to Chip: How Wipro and Intel Are Delivering ROI-First AI for the Enterprise
AI has already begun transforming several Industries, business models & processes. Accordingly, Enterprises have been pivoting their strategy to ensure they are well positioned to leverage AI for Growth, higher Margins and Efficiency. However, the ROI of AI initiatives is as much a function of the execution model as it is of the Use case, […]
The security assumption agentic AI just broke
I ran a red-team exercise against an internal IT-support agent wired across a stack any large enterprise would recognize: ServiceNow for tickets, SharePoint for policy and procedure docs, an internal directory for routing. The agent had legitimate read access to all three and could draft replies but not send them. Inside two hours, it had […]
What is a data analyst? A key role for data-driven business decisions
What is a data analyst? Data analysts work with data to help their organizations make better business decisions. Using techniques from a range of disciplines, including computer programming, mathematics, and statistics, data analysts draw conclusions from data to describe, predict, and improve business performance. They form the core of any analytics team and tend to […]
CIOs are enlisting business users to vibe code their own apps
Vibe coding is expanding beyond the realm of software development teams into a variety of business units at a range of enterprises, and technology leaders are not only supporting these efforts but in some cases leading the charge. This democratization of software development, buoyed by vibe coding tools, including chatbots and agents that generate code […]
Connected vehicles, disconnected security: Why connectivity architecture now matters most
The number of connected cars on our roads today is projected to have exceeded 400 million, and almost every newly manufactured car now embeds connectivity by design, from sensor-based telematics that generate vast streams of data to driver assist technologies that enhance the in-vehicle experience. According to some estimates, the average car will generate roughly […]
Warmy.Io Publishes Research On Barracuda Blacklist, Revealing Why Legitimate B2B Senders Get Blocked
New research from Warmy.io maps the full mechanics of the Barracuda Reputation Block List, including five early-warning signals that appear in mail logs before a full listing occurs — and why most B2B senders never see them coming. Warmy.io, the email deliverability platform, today published an in-depth research report on the Barracuda Reputation Block List […]
FINRA Essentials: Your Guide to Key Regulatory Touchpoints
FINRA Essentials: Your Guide to Key Regulatory Touchpoints K31999 Tue, 05/26/2026 – 13:29 This video series guides member firms through key interactions with FINRA, transforming regulatory touchpoints into clear, navigable processes. Each video features FINRA subject matter experts who provide insider perspectives, actionable guidance and valuable resources to help firms engage more effectively with FINRA. […]
CRMO
CRMO K30658 Tue, 05/26/2026 – 12:36 Continuing Education Requirements 20 credits every two years Designation Training Requirements Online training courses; total credit requirement varies based on CRMO certification level. Published List of Disciplined Designees Online at Disciplined Individuals List Online Designation Resource Online at Member Directory Issuing Organization Link https://www.gifp.us.org/ Investor Complaint Process Online at Report Misconduct Created […]
25-02578.pdf
25-02578.pdf Anonymous (not verified) Tue, 05/26/2026 – 11:55 Case ID 25-02578 Forum FINRA Document Type Award Claimants Grant Carodine Respondents Edward Jones Neutrals Sandra L. Malek Paul E. Dahlman George Pinckney Shingler Hearing Site Birmingham, AL Award Document 25-02578.pdf Documentum DocID 72161dec Award Date Official Tue, 05/26/2026 – 12:00 Related Content Off Claimant Representatives Laura […]
25-02283.pdf
25-02283.pdf Anonymous (not verified) Tue, 05/26/2026 – 11:55 Case ID 25-02283 Forum FINRA Document Type Award Claimants Wells Fargo Clearing Services, LLC Respondents Norman Barrett Neutrals David S. Godkin Hearing Site Boston, MA Award Document 25-02283.pdf Documentum DocID 2084c0c5 Award Date Official Tue, 05/26/2026 – 12:00 Related Content Off Claimant Representatives Sara Soto Respondent Representatives […]
MuddyWater Uses DLL Side-Loading in Espionage Campaign Targeting 9 Countries
The Iranian hacking group known as MuddyWater has been linked to a new campaign affecting at least nine organizations across nine countries on four continents in the first quarter of 2026. The activity targeted industrial and electronics manufacturing, education and public-sector bodies, financial services, and professional services, per the Threat Hunter Team from Symantec and […]
GitHub Actions abused by Megalodon attack to slip malicious commits into 5,500 repos
A large-scale automated GitHub backdooring campaign was caught pushing thousands of malicious commits into public repositories while posing as routine CI/CD upkeep. Researchers at SafeDep observed the campaign, Megalodon, touching more than five thousand repositories over a six-hour window on May 18. The attack was in the form of a malicious commit, “acac5a9,” targeting GitHub […]
ABB AbilityTM Zenon Remote Transport Vulnerability
View CSAF Summary ABB is aware of vulnerabilities in the product versions listed as affected in the advisory. The vulnerability enables unauthorized access to the Reboot OS function within the Remote Transport Service, allowing an attacker to trigger a system reboot without the required authentication. This functionality initiates a system reboot on the target machine. […]
ABB Terra AC
View CSAF Summary ABB is aware of vulnerabilities in the product versions listed as affected in the advisory. An attacker who successfully exploited this vulnerability could cause the pollution of heap memory which potentially takes remote control of the product and performs a write operation to the flash memory to alter the firmware behavior. The […]
ABB AC500 V2
View CSAF Summary ABB became aware of vulnerabilities in AC500 V2 listed as affected in the advisory. An attacker who successfully exploited this vulnerability could access fragments of Modbus telegrams that have been sent earlier by that PLC The following versions of ABB AC500 V2 are affected: AC500 V2 <=2.5.2, 2.5.3 CVSS Vendor Equipment Vulnerabilities […]
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2026-48172 LiteSpeed cPanel Plugin Privilege Escalation Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities established the KEV Catalog as […]
ABB LVS MConfig
View CSAF Summary ABB became aware of an internally discovered vulnerability in the MConfig product versions listed as affected in the advisory. An attacker with access to local networks who successfully exploits vulnerability could have access to application’s sensitive information. ABB strongly advises customers to update MConfig with latest software version. The following versions of […]
ABB B&R Automation Runtime DoS Vulnerability in System Diagnostics Manager (SDM)
View CSAF Summary An update is available that resolves a vulnerability identified by B&Rs internal security analysis in the product versions listed as affected in this advisory. An attacker who successfully exploited this vulnerability could cause the product to stop. The following versions of ABB B&R Automation Runtime DoS Vulnerability in System Diagnostics Manager (SDM) […]
ABB Ability Camera Connect
View CSAF Summary ABB is aware of public reports of vulnerabilities in a 3rd party component VLC media player Version 2.2.4 which was delivered together with the installation package of Camera Connect Version 1.5.0.14 and below. An update is available that resolves a privately reported outdated 3rd party component with vulnerabilities in the product versions […]
Eppendorf BioFlo 320
View CSAF Summary Successful exploitation of this vulnerability could allow an attacker to gain full access to functionality and data with the bioreactor. The following versions of Eppendorf BioFlo 320 are affected: BioFlo 320 Bioreactor vers:all/* CVSS Vendor Equipment Vulnerabilities v3 9.8 Eppendorf Eppendorf BioFlo 320 Use of Hard-coded Password Background Critical Infrastructure Sectors: Healthcare […]
[THN Webinar] New AI DDoS Attacks Are Smarter. Learn How to Fight Back
Every single day, hackers are finding new ways to crash websites and steal data. But right now, something has changed. Hackers are no longer working alone. They are now using powerful Artificial Intelligence (AI) tools to make their attacks faster, stronger, and much harder to stop. According to recent updates from The Hacker News, bad […]
Microsoft Patches SharePoint RCE Flaw CVE-2026-45659 Across Server Versions
Microsoft has rolled out updates to fix a remote code execution vulnerability impacting SharePoint that could be exploited by bad actors in attacks without requiring any specialized conditions to be met. The vulnerability, tracked as CVE-2026-45659, carries a CVSS score of 8.8. It has been assigned an important severity. “Deserialization of untrusted data in Microsoft […]
TrapDoor malware campaign puts developer workstations in CISO spotlight
A malicious package campaign across npm, PyPI, and Crates.io has put developer workstations back under scrutiny, after researchers said it targeted developer workflows and AI coding assistant files. Researchers at Socket said the campaign, which they are tracking as TrapDoor, “spans more than 34 malicious packages and 384+ related versions and artifacts” across the three […]
266,000 Affected by Data Breach at Radiology Associates of Richmond
Threat actors stole files containing names and protected health information from the healthcare organization’s systems. The post 266,000 Affected by Data Breach at Radiology Associates of Richmond appeared first on SecurityWeek.
Oncology Institute Discloses Data Breach
The affected third-party vendor has not been named, but one possible candidate is TriZetto. The post Oncology Institute Discloses Data Breach appeared first on SecurityWeek.
Ghost CMS Vulnerability Exploited to Hack Over 700 Websites
Sites belonging to major universities such as Harvard and Oxford, as well as DuckDuckGo, have been compromised in the attack. The post Ghost CMS Vulnerability Exploited to Hack Over 700 Websites appeared first on SecurityWeek.
Admins of Bulletproof Hosting Service Used by Russian Hackers Arrested in Netherlands
The two own Dutch companies that allegedly provided bulletproof hosting services to Russia-aligned threat actors. The post Admins of Bulletproof Hosting Service Used by Russian Hackers Arrested in Netherlands appeared first on SecurityWeek.
Lithuania Suspects Foreign Involvement in Data Leak of Over 600,000 National Register Entries
Lithuanian authorities are on high alert after a massive data leak involving more than 600,000 entries from national data registers. The post Lithuania Suspects Foreign Involvement in Data Leak of Over 600,000 National Register Entries appeared first on SecurityWeek.
Open Source DockSec Uses AI to Cut Through Vulnerability Noise in Docker Images
DockSec, an OWASP incubator project, correlates findings from multiple container security scanners and uses AI to generate plain-English remediation guidance and exact Dockerfile fixes. The post Open Source DockSec Uses AI to Cut Through Vulnerability Noise in Docker Images appeared first on SecurityWeek.
Watch on Demand: Threat Detection & Incident Response Summit – All Sessions Available
Register to enjoy free access and explore the tools, strategies, and frameworks needed to build a resilient security program for a world where every minute counts. The post Watch on Demand: Threat Detection & Incident Response Summit – All Sessions Available appeared first on SecurityWeek.
MFA Prompt Bombing: Why Your Second Factor Isn't Saving You
Multi-factor authentication (MFA) was supposed to close a critical gap in identity security. It meant that, even if an attacker possessed the account credentials, they couldn’t log in without the second factor. While that logic was sound, attackers have now figured out that they don’t need to steal the second factor: they just need the […]
CERT-In Mandates 12-Hour Patching for Internet-Facing Flaws Amid AI-Assisted Attacks
The Indian Computer Emergency Response Team (CERT-In) has issued new guidelines requiring organizations to patch critical security vulnerabilities in internet-exposed systems within 12 hours of being flagged where “feasible” to safeguard against potential threats stemming from threat actors’ abuse of artificial intelligence (AI) tools and large language models (LLMs) to automate vulnerability
Stop treating AI governance as a review layer. Make it release infrastructure
I’ve spent years building compliance into security products. FedRAMP and Department of War Impact Level authorizations, vulnerability management pipelines: They all follow the same pattern. Build the product, then prove it meets requirements. The compliance layer sits outside the engineering workflow. It reviews what already exists. That model worked when the product stayed static between […]
Iranian Hackers Deploy MiniFast and MiniJunk V2 via Phishing and SEO Poisoning
The Iranian state-sponsored threat actor known as Nimbus Manticore (aka Screening Serpens and UNC1549) has been attributed to a fresh campaign using lures impersonating organizations in the aviation and software sectors across the U.S., Europe, and the Middle East following the joint U.S.-Israeli military campaign against the country in late February 2026. The activity, besides […]
Vulnerabilities have become cyber attackers’ No. 1 door to the enterprise
Patching practices are coming under intense pressure of late, as time-to-exploit windows accelerate — a new reality likely to worsen as AI assistance in attack chains rises. Now cyber defenders have another cause for flaw alarm: Vulnerability exploitation has significantly pulled away from stolen credentials as the most common entry point in security breaches, according […]
KnowledgeDeliver LMS Flaw Exploited to Deploy Godzilla and Cobalt Strike
A now-patched high-severity security flaw affecting Digital Knowledge KnowledgeDeliver, a Learning Management System (LMS) popular in Japan, was exploited as a zero-day to deliver the Godzilla web shell and ultimately facilitate the deployment of Cobalt Strike Beacon. The vulnerability, tracked as CVE-2026-5426 (CVSS score: 7.5), stems from the use of hard-coded ASP.NET machine keys, leading […]
Security experts caution MFA alone can no longer stop threat actors
Cybersecurity experts are warning enterprise admins about an increasing number of phishing campaigns aimed at stealing Microsoft 365 (M365) access tokens to bypass multifactor authentication login protection. Phishing kits aimed at capturing M365 tokens aren’t new; some reports say these kits have been around since 2021. One of the latest is EvilTokens, which researchers at […]
ISC Stormcast For Tuesday, May 26th, 2026 https://isc.sans.edu/podcastdetail/9944, (Tue, May 26th)
Post Content
Project Glasswing has uncovered 10,000 vulnerabilities: Anthropic
Anthropic says it and upwards of 50 partners involved in Project Glasswing have uncovered an estimated 10,000 critical or high-severity vulnerabilities in their software offerings. The company launched the cybersecurity initiative, which is built around Claude Mythos Preview, in April, stating that its launch partners would use it as part of their defensive security work. […]
Possible ACR Stealer From Page Impersonating Claude, (Tue, May 26th)
Introduction
25-00956.pdf
25-00956.pdf Anonymous (not verified) Mon, 05/25/2026 – 18:10 Case ID 25-00956 Forum FINRA Document Type Award Claimants Steven Nartker Respondents Avantax Investment Services, Inc. Neutrals Stuart D. Summers Robert J. Gregory Paul Allan Massaro Hearing Site Dallas, TX Award Document 25-00956.pdf Documentum DocID 73e174cd Award Date Official Fri, 05/22/2026 – 12:00 Related Content Off Claimant […]
24-01413.pdf
24-01413.pdf Anonymous (not verified) Mon, 05/25/2026 – 18:10 Case ID 24-01413 Forum FINRA Document Type Award Claimants Theodore Simon Respondents Steward Partners Investment Solutions Neutrals Stephany Adriene Watson Scott Hooper Judson Wayne White Hearing Site Portland, OR Award Document 24-01413.pdf Documentum DocID 8a5d2ba0 Award Date Official Fri, 05/22/2026 – 12:00 Related Content Off Claimant Representatives […]
AI時代に戦略家とオペレーターを分ける、たった一つの能力とは
人類の歴史の大半において、道具は身体を拡張するために作られてきた。鋤(すき)は手を、車輪は足を、望遠鏡は目を拡張した。今、初めて私たちは知性を拡張する道具を作っている。AIの実装に取り組む組織が共通して直面する問いがある。「私たちは何のためにAIを使うのか」だ。人間の思考を置き換えようとしているのか、補完しようとしているのか、再分配しようとしているのか。今うまく動いている企業は、その問いに明確に答えている企業だ。AIの予算が最も大きい企業ではない。 インテグラルシンキングとは何か 知性はかつて希少資源だった。今やその希少性は薄れ豊富になりつつある。McKinseyの分析によれば、生成AIは年間2.6〜4.4兆ドルの価値を生み出す可能性があるという。モデルの実行コストは急落し、LLMが処理できる情報量(コンテキスト制限)は約10万トークンから最大1000万トークンへと拡大しようとしている。では次の希少資源は何か。 産業革命の時代、肉体労働が豊富になると人間の判断力が希少になった。コンピューターの時代、計算が豊富になると創造的問題解決が希少になった。そしてAI時代、認知処理が豊富になった。次に希少になるのは「インテグラルシンキング」だ。 この言葉は米国の思想家Ken Wilber(ケン・ウィルバー)のインテグラル理論に由来する。ビジネスに応用すると、インテグラルシンキングとは生物学、テクノロジー、社会学、経済学、文化など根本的に異なる領域にまたがって統合し、一貫した戦略に変える能力だ。たとえば生物学の知見を組織の回復力に応用する、社会行動の変化からテクノロジーの普及を予測する、あるいは技術的に見える問題が実は文化的な問題だと気づく——そういった思考だ。 インテグラルシンキングは、昔から偉大な思想家が自然に備えていた能力だ。インテグラルシンキングの力を示す好例がある。1990年代、複雑なネットワーク問題に行き詰まったエンジニアたちを救ったのは、意外なところからのヒントだったーーアリだ。「アント・コロニー最適化」アルゴリズムは、アリのコロニーがフェロモンを使って最短経路を見つける仕組みを模倣したもので、現代のロジスティクスとデータネットワークの基盤となっている。AIは明確な境界の中では優れたオペレーターになれるが、複数の学問が交差する場所に立ってそれらを何か新しいものに織り上げることは苦手だ。 インテグラルシンキングを支える2つの人間的能力がある。第一に「何をすべきかの判断力」だ。AIは千もの相関関係を示せるが、どれがシグナルでどれがノイズか、どれに戦略的価値があるかを見極めるのは人間の判断だ。第二に「信頼関係と影響力」だ。異なる領域のパターンを見つけるだけでは半分だ。それを行動に変えるには、異なる学問の人々を巻き込む必要がある。アルゴリズムが作れない信頼が必要だ。 なぜ今、インテグラルシンキングなのか 17の異なる業界にわたる33以上の組織で一貫して見られるパターンがある。多くの企業が「AIの準備」を人員削減の演習として扱っている。それは短期的な動きであり、長期的なコストを伴う。先を行く組織はAIを使ってスケールしている——新市場への参入、新製品・サービスの立ち上げ、新規顧客の獲得だ。 真の「AIファースト」アプローチには、まったく異なる組織構造が必要だ。1800年代の階層型組織図は調整がボトルネックだった世界向けに最適化されたものだ。AIはその制約を逆転させる。調整は自動化できる。ボトルネックはもはやコントロールではなく、意思決定の速度と創造的反復だ。 今成功している企業は、機能ではなく成果を所有する人材を採用している。AIがプレイブックを処理し、人間は判断力とセンスのために採用される。チームは小さくなり、役割は広くなる。Stanfordの研究も、AI時代に最も重要なスキルは批判的思考、創造性、複雑な問題解決だと示している。 インテグラルシンキングを育てるには ・専門外を学ぶ時間を確保する:週1時間、仕事と無関係な分野を学ぶ。神経科学、都市計画、生態学、ルネサンス芸術など。目標は専門知識ではなくパターン認識だ ・翻訳の習慣を作る:週1回、別の領域のコンセプトを自分のビジネスに当てはめて書いてみる。「蜂のコロニーの意思決定から分散チームの調整に学べることは何か」——最初は強引に感じるが、やがてつながりが自然に現れ始める ・異なる5つ以上の領域に人脈を持つ:科学者、芸術家、政策立案者、エンジニア、人類学者——根本的に異なる思考をする人と定期的に会話する ・組織内のインテグラルシンカーを見つける:専門外のアナリジーを使って複雑な問題を説明できる人に注目する。技術的問題を生物学的比喩で説明するエンジニアや、物理学を使って顧客行動を説明するマーケターがいれば、それは希少な人材だ ・AIの有効活用を評価基準に加える:AIと競争するのではなく、AIをうまく活用することが評価される文化を作る 人間とAIの間のインターフェースを設計する 優れたリーダーに共通する3つのことがある。 1)AIをいつ信頼し、いつ覆すかを知っている。 2)無限の下書きがある世界で何を出荷すべきかを知っている。 3)自動化された作業と人間の判断の間のクリーンなハンドオフを設計している。 競争優位はAIを持つかどうかではない。機械処理と人間のインテグラルシンキングの間のインターフェースをいかに設計するかにある。テクノロジーが結果を決めるのではない。私たちの選択が決める。
Why relationships are the hidden infrastructure of AI transformation
By now, most digital and tech leaders have heard some version of the same refrain, that AI adoption is 20% about the technology and 80% about the people. But even when leaders acknowledge the people side of AI, the conversation often moves quickly to skills, workforce planning, talent architecture, or reimagining how work gets done. […]
8 IT modernization traps CIOs must avoid
With cloud migration, digital transformation, and now the drive for AI adoption, CIOs face a real imperative to get modernization right. However, industry research continues to show that modernization projects can fail to deliver the promised benefits and suffer cost overruns, even as the appetite for overhauling legacy technology grows. CIOs, enterprise technology leaders, and […]
El viaje de la Comunitat Valenciana hacia una salud digital más inclusiva, ética y eficiente
El sistema sanitario público valenciano se halla en pleno proceso de modernización tecnológica gracias a la ejecución de la Estrategia de Salud Digital de la Comunitat Valenciana. Presentada a finales de 2024 y dotada de una inversión de 235 millones de euros hasta 2027, la Estrategia conlleva adoptar un nuevo paradigma tecnológico y de gestión, diseñado para […]
IA, ingresos y resiliencia redefinen el papel del CIO
Para la mayoría de los CIO, la implementación de la IA ya es la prioridad número uno. Así lo recoge la encuesta State of the CIO 2026 de CIO.com, que confirma una tendencia consolidada: los CEO sitúan la investigación y adopción de IA en la cúspide de sus agendas tecnológicas, en línea con los resultados […]
Google adds open source Agent Executor to support AI agents in production
Google has introduced Agent Executor, an open source runtime aimed at helping enterprises run AI agents more reliably at scale, as attention shifts from building agent prototypes to managing the operational challenges of putting them into production. To address those production-related challenges, the runtime, according to the company, comes with capabilities that are geared towards […]
Microsoft Access VBA, (Mon, May 25th)
Microsoft Access files (Microsoft Office’s Database) can contain VBA code.
⚡ Weekly Recap: Linux Flaws, Defender 0-Days, Router Botnets, and Supply Chain Chaos
Monday recap. Same mess, new week. A sketchy dev tool got people pwned, old bugs came back from the dead, and security products somehow needed protecting from themselves. A bunch of companies spent the week checking old boxes and forgotten servers they should’ve patched years ago. Good times. Phishing crews are getting smarter too – […]
TeamPCP Supply Chain Campaign: Activity Through 2026-05-24, (Mon, May 25th)
TeamPCP now operates across three package ecosystems in parallel, it reached GitHub’s own internal codebase, it trojanized an officially Microsoft-published Python SDK, and it appears to have open-sourced its own framework on GitHub.
TeamPCP Supply Chain Campaign: Activity Through 2026-05-24, (Mon, May 25th)
TeamPCP now operates across three package ecosystems in parallel, it reached GitHub’s own internal codebase, it trojanized an officially Microsoft-published Python SDK, and it appears to have open-sourced its own framework on GitHub.
Netherlands Seizes 800 Servers, Arrests 2 for Aiding Cyberattacks
Authorities in the Netherlands have arrested the co-owners of two related Internet hosting companies for operating IT infrastructure used by Russia to carry out cyberattacks, influence operations and disinformation campaigns inside the European Union. The two men were the focus of a 2025 KrebsOnSecurity story about how their hosting companies had assumed control over the […]
PowerSchool’s $17.25 Million Settlement Exposes Years of Student Data Tracking
If you ask most people what breach PowerSchool experienced, their first response might be the 2024 hacking incident that affected tens of millions of students. But even before that breach, there was another significant breach involving PowerSchool that began in 2021. Colin Lee and Koji Edmunds report: In early April, many students across the world… […]
AI security needs a shift from models to systems, researchers argue
Enterprises cannot secure AI agents by making the underlying models more robust and must instead enforce security controls at the system level around them, researchers behind a paper published this month argued, warning that traditional AI-security approaches are increasingly misaligned with how autonomous agents actually operate inside enterprise environments. The paper argues that enterprises should […]
Ghost CMS CVE-2026-26980 Exploited to Hijack 700+ Sites for ClickFix Attacks
Threat actors are exploiting a recently disclosed critical security flaw in Ghost CMS to inject malicious JavaScript code with an aim to fuel ClickFix attacks. According to QiAnXin XLab, the activity involves the exploitation of CVE-2026-26980 (CVSS score: 9.4), an SQL injection vulnerability in Ghost’s Content API that could allow an unauthenticated attacker to read […]
As AI speeds coding, CVE Lite CLI keeps security deliberately AI-free
As AI coding assistants accelerate software development, one OWASP-backed open-source project is arguing that dependency security tooling still arrives too late to be truly useful. CVE Lite CLI, a JavaScript and TypeScript dependency vulnerability scanner focused on local lockfile analysis, is positioning itself around a simple idea. Developers should see dependency risks while they are […]
The Alert Firehose Finally Meets Its Match
Ask a cybersecurity pro about Network Detection and Response (NDR) and you might still hear “Noisy,” “Too much data.” But ask the teams running NDR that includes agentic AI capabilities and you’ll hear they’re actually using it to catch threats earlier, triage faster, and chase fewer false positives. The old complaint lingers in part because […]
Over 5,500 GitHub Repositories Infected in ‘Megalodon’ Supply Chain Attack
Fake automated commits injected GitHub Actions workflows containing payloads to steal credentials, CI secrets, keys, and tokens. The post Over 5,500 GitHub Repositories Infected in ‘Megalodon’ Supply Chain Attack appeared first on SecurityWeek.
DocketWise Data Breach Impacts 143,000
Hackers accessed names, addresses, Social Security numbers, financial information, and medical data from third-party partner repositories. The post DocketWise Data Breach Impacts 143,000 appeared first on SecurityWeek.
Laravel-Lang Packages Poisoned for Malware Delivery
Published within a 15-minute window, the malicious tags introduced backdoors to exfiltrate CI secrets. The post Laravel-Lang Packages Poisoned for Malware Delivery appeared first on SecurityWeek.
Anthropic: Mythos Detected 23,000 Potential Vulnerabilities Across 1,000 OSS Projects
Many findings have been confirmed to be critical or high-severity vulnerabilities and the number will continue to increase. The post Anthropic: Mythos Detected 23,000 Potential Vulnerabilities Across 1,000 OSS Projects appeared first on SecurityWeek.
Lazarus Deploys RemotePE Memory-Only RAT Against Financial and Crypto Firms
Cybersecurity researchers have shed light on a cross-platform malware called RemotePE that has been put to use by the North Korea-linked Lazarus Group in attacks targeting financial and cryptocurrency organizations. RemotePE, per NCC Group subsidiary Fox-IT, is part of a multi-stage attack chain that involves two loaders tracked as DPAPILoader and RemotePELoader. “DPAPILoader decrypts and
To pay, or not to pay: 58% of CISOs say they would pay the ransom for their data
If you were hit by ransomware tomorrow, would you pay to get your data back? That’s what more than half of CISOs in a recent survey said their organization would do. It’s a situation more companies are going to face in future. “Attacks are increasing and continuing to increase,” said Christy Wyatt, CEO of security […]
TrapDoor Supply Chain Attack Spreads Credential-Stealing Malware via npm, PyPI, and CratesIO
A new coordinated cross-ecosystem software supply chain attack campaign has targeted npm, PyPI, and Crates.io to distribute credential-stealing malware. The campaign, codenamed TrapDoor, spans more than 34 malicious packages across over 384 versions. The earliest activity was recorded on May 22, 2026, at 8:20 p.m. UTC, with new packages published to the ecosystems in waves […]
Wireshark 4.6.6 Released, (Sun, May 24th)
Wireshark release 4.6.6 fixes 1 vulnerability and 11 bugs.
France Sees More Violent Attacks on Crypto Holders Than Any Other Country
Julian Lim reports: The hardest part of crypto security used to be keeping private keys away from hackers. In France, the problem has moved much closer to home. A new report says roughly 70% of documented wrench attacks against crypto holders and their families are happening there, turning a niche security term into a very… […]
UK: £355,880.10 confiscation order secured following proceeds of crime hearing
There’s a follow-up to the case of a motor insurance worker who received a suspended prison sentence for unlawfully accessing personal information. On May 21, the Information Commissioner’s Office (ICO) announced that it had secured a £355,880.10 confiscation order against the former Manchester motor insurance worker, Rizwan Manjra. A statement by the ICO indicates that… […]
Rhode Island’s workers’ compensation notifies those affected by January data breach
Rhode Island residents may understandably wonder about the state’s vendor security monitoring. First, it was the Deloitte and the RIBridges data breach that affected more than 730,000 residents. Now the vendor that administers the state’s workers’ compensation insurance has disclosed a breach affecting 131,000 residents, including 4,500 former and current state employees. Alexander Castro reports:… […]
npm Adds 2FA-Gated Publishing and Package Install Controls Against Supply Chain Attacks
GitHub has rolled out new controls for npm to improve the security of the software supply chain, giving maintainers the ability to explicitly approve a release prior to the packages becoming publicly available for installation. Called staged publishing, the feature is now generally available on npm. It mandates that a human maintainer pass a two-factor […]
Packagist Supply Chain Attack Infects 8 Packages Using GitHub-Hosted Linux Malware
A new “coordinated” supply chain attack campaign has impacted eight packages on Packagist including malicious code designed to run a Linux binary retrieved from a GitHub Releases URL. “Although the affected packages were all Composer packages, the malicious code was not added to composer.json,” Socket said. “Instead, it was inserted into package.json, targeting projects that […]
UK: Victims feel ‘violated’ after water firm’s data breach
Oprah Flash reports: “Violated” and being “unable to trust” have been the feelings plaguing victims of a cyber attack on a Midlands-based water company. The personal data of 633,887 people was stolen and published on the dark web, after South Staffs Water was hacked in 2020. Customers said they faced a deluge of scam emails… […]
Claude Mythos AI Finds 10,000 High-Severity Flaws in Widely Used Software
Anthropic on Friday disclosed that Project Glasswing has helped uncover more than 10,000 high- or critical-severity vulnerabilities across some of the most “systemically” important software across the world since the cybersecurity initiative went live last month. Project Glasswing is a defensive effort launched by the artificial intelligence (AI) company to secure critical global software
Canadian Man Arrested for Operating Kimwolf Botnet
Jacob Butler, 23, has been arrested in Canada and US authorities are seeking his extradition on computer hacking charges. The post Canadian Man Arrested for Operating Kimwolf Botnet appeared first on SecurityWeek.
In Other News: Industrial Router Exploitation, CISA KEV Nomination Form, Gas Station Hacking
Other noteworthy stories that might have slipped under the radar: CISA contractor exposes credentials, Mythos testing and new features, Huawei router flaw triggered telecom blackout. The post In Other News: Industrial Router Exploitation, CISA KEV Nomination Form, Gas Station Hacking appeared first on SecurityWeek.
Drupal Vulnerability in Hacker Crosshairs Shortly After Disclosure
Drupal is warning users that it has already seen attempts to exploit CVE-2026-9082 and security firms are seeing attacks against thousands of websites. The post Drupal Vulnerability in Hacker Crosshairs Shortly After Disclosure appeared first on SecurityWeek.
‘Underminr’ Vulnerability Lets Attackers Hide Malicious Connections Behind Trusted Domains
The stealthy vulnerability impacts roughly 88 million domains and can be exploited to bypass DNS filtering and hide command-and-control traffic. The post ‘Underminr’ Vulnerability Lets Attackers Hide Malicious Connections Behind Trusted Domains appeared first on SecurityWeek.
Laravel-Lang PHP Packages Compromised to Deliver Cross-Platform Credential Stealer
Cybersecurity researchers have flagged a fresh software supply chain attack campaign that has targeted multiple PHP packages belonging to Laravel-Lang to deliver a comprehensive credential-stealing framework. The affected packages include – laravel-lang/lang laravel-lang/http-statuses laravel-lang/attributes laravel-lang/actions “The timing and pattern of the newly published tags
LiteSpeed cPanel Plugin CVE-2026-48172 Exploited to Run Scripts as Root
A maximum-severity security vulnerability impacting LiteSpeed User-End cPanel Plugin has come under active exploitation in the wild. The flaw, tracked as CVE-2026-48172 (CVSS score: 10.0), relates to an instance of incorrect privilege assignment that an attacker could abuse to run arbitrary scripts with elevated permissions. “Any cPanel user (including an attacker or a compromised account) […]
Drupal Core SQL Injection Bug Actively Exploited, Added to CISA KEV
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a recently patched critical security flaw impacting Drupal Core to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation. The vulnerability in question is CVE-2026-9082 (CVSS score: 6.5), an SQL injection vulnerability affecting all supported versions of Drupal Core. “Drupal Core
An Example of Stack String in High Level Language, (Sat, May 23rd)
This week, I’m attending the SEC670[1] training (“Red Teaming Tools – Developing Windows Implants, Shellcode, Command and Control”). From my point of view, this training fits perfectly with FOR610 or FOR710 (malware analysis) because it addresses malware from the opposite: Instead of performing reverse engineering, you write malicious code! Always interesting to have another point […]
Google leaks details for Chromium bug that can turn browsers into bots
Chromium — the open-source browser that underpins Google Chrome, Microsoft Edge, and Opera, among others — contains an unpatched vulnerability that attackers can exploit to execute JavaScript code persistently across browser restarts. As a result, the flaw can be used to hijack users’ browsers for distributed denial-of-service attacks, run crypto miners, and more. The vulnerability […]
FINRA Adopts New Intraday Margin Standards to Replace the Day Trading Margin Requirements
FINRA Adopts New Intraday Margin Standards to Replace the Day Trading Margin Requirements K34060 Fri, 05/22/2026 – 15:50 April 22, 2026 Features FINRA Adopts New Intraday Margin Standards to Replace the Day Trading Margin Requirements FINRA adopted new intraday margin standards to replace in their entirety the outdated day trading margin requirements, including the day trade […]
SEC Requests Comment on Proposal to Facilitate Capital Formation
SEC Requests Comment on Proposal to Facilitate Capital Formation K34060 Fri, 05/22/2026 – 15:41 April 29, 2026 Features SEC Requests Comment on Proposal to Facilitate Capital FormationThe SEC instituted proceedings on April 23 to determine whether to approve or disapprove FINRA’s proposed rule changes to streamline aspects of the corporate financing process. The proposed amendments […]
FINRA Forward Report Highlights Year of Progress
FINRA Forward Report Highlights Year of Progress K34060 Fri, 05/22/2026 – 15:27 May 6, 2026 Features FINRA Forward Report Highlights Year of ProgressOne year in, FINRA is delivering on FINRA Forward. Our new report outlines our progress, highlights some of the concrete actions we have taken since launching FINRA Forward in the spring of 2025, and looks ahead as we enter the initiative’s second […]
FINRA Annual Conference Speakers Emphasize Value of SRO Model
FINRA Annual Conference Speakers Emphasize Value of SRO Model K34060 Fri, 05/22/2026 – 15:11 May 13, 2026 Features FINRA Annual Conference Speakers Emphasize Value of SRO ModelThe benefits of self-regulation for the brokerage industry were a key theme at FINRA’s 2026 Annual Conference in Washington, DC, this week. “I’m a firm believer in the self-regulatory […]
xAI-Anthropic deal signals the rise of AI compute as a standalone business
New SpaceX IPO filings suggest frontier AI firms are beginning to treat compute infrastructure as a standalone commercial business, with Elon Musk’s xAI agreeing to provide large-scale AI capacity to competitor Anthropic. The filing disclosed that Anthropic agreed to purchase compute services delivered through xAI’s Colossus and Colossus II AI infrastructure clusters through May 2029 […]
Why digital sovereignty is a fast-rising priority in an uncertain world.
Enterprise leaders are increasingly understanding that resiliency and digital sovereignty are critically important amid uncertain times and rapid change. CIOs are responding fast: More than 75% of non-U.S. enterprises will have a digital sovereignty strategy by 2030, according to Gartner research. Many blame geopolitical tensions. But for Julio Guijarro, CTO, EMEA at Red Hat, the […]
The 3 ‘no regrets’ AI moves for IT organizations
In my work with enterprise technology leaders, I’ve seen so many companies lay claim to AI rapidly (through pilots, tests and cross-functional experiments) that the enterprise AI moment increasingly feels like a gold rush. If it is, then leaders should take a lesson from history, from the real Gold Rush. During that time, the most […]
The key role of hybrid cloud in digital sovereignty and innovation
Many CIOs are prioritising digital sovereignty, with concerns around extraterritorial data requests, regulatory compliance, and data security among the key drivers of this shift, according to IDC research. But does this require moving completely away from the big hyperscalers? For many experts, this approach could lead to suboptimal outcomes. Red Hat’s Senior Principal Chief Architect […]
Toward a sovereign future: The practical steps IT leaders should take
Digital sovereignty has become a key strategic objective for organisations seeking to manage geopolitical and data security risks. But translating this goal into implementation is challenging with many IT leaders yet to make appreciable progress. What are some practical steps, then, for CIOs to carry out this shift effectively? Julio Guijarro, CTO of Red Hat […]
How concerned should CIOs be with geopolitics?
Digital sovereignty is becoming more of a headline, jumping from a specific area of technology to mainstream media and geopolitical analysis. The catalyst of this shift comes from growing global tensions, and resulting talk about reducing dependence on third-party countries for tech and innovation, resilience to potential failures and disconnections, and increasingly more sophisticated cyber threats. […]
11 AI certifications to grow your career
Across every industry, organizations are scrambling to implement AI into their daily workflows, products, and services. As a result, they’re increasingly looking for qualified professionals who have the right AI skillsets to help with this new wave of digital transformation. Skills such as machine learning, data engineering and analytics, AI prompt engineering, natural language processing, […]
AI 사이버 공격 역량 급가속 “4개월마다 방어 난이도 두 배”
영국 정부 산하 AI 보안연구소(AISI)가 발표한 새로운 벤치마크에 따르면, AI 모델이 인간 전문가 수준에 필적하는 엔드투엔드 다단계 침투 테스트를 수행하는 능력이 최근 몇 달 사이 크게 향상된 것으로 나타났다. 과학혁신기술부(DSIT) 산하 연구기관인 AISI에 따르면, 2025년 11월 기준으로 최상위 AI 모델이 수행할 수 있는 사이버 작업의 난이도는 약 8개월마다 두 배로 증가했다. 그러나 올해 2월에는 성능 […]
Workday extends Sana AI to ITSM after HR, finance
Workday conversational AI platform Sana for Workday is now ready to talk about IT Service Management (ITSM) automation as part of the company’s broader effort to help enterprises streamline workflows, especially across HR and finance, with autonomous AI agents. The new Sana for ITSM capabilities are intended to automate workflows for employee on- and offboarding, […]
Microsoft, EY to spend $1 billion on helping customers buy agentic AI
Microsoft and EY will spend $1 billion on helping their customers adopt AI over the next five years. The billion will support assisting clients with pioneering AI projects and capability building, said EY’s global Microsoft alliance leader, Paul Clark. Clients will be able to access those resources based on their specific needs, he said. “We’re […]
FINRA Announces Review of Higher-Risk Structured Products
FINRA Announces Review of Higher-Risk Structured Products K34060 Fri, 05/22/2026 – 14:53 May 20, 2026 Features FINRA Announces Review of Higher-Risk Structured ProductsConsistent with our mission of investor protection, FINRA announced Tuesday that it will review firm practices regarding higher-risk structured products, specifically non-principal protected “worst-of” structured notes. The review will examine how firms supervise […]
FBI warns of Kali Oauth stealers
The FBI has warned of the danger from a new wave of phishing attacks generated by a tool called Kali365. It enables cyber criminals to obtain Microsoft 365 access tokens and bypass multi-factor authentication (MFA) protocols without intercepting the user’s credentials by capturing Oauth tokens linked to the victim’s Microsoft 365 account. The scam works […]
First VPN Dismantled in Global Takedown Over Use by 25 Ransomware Groups
Authorities in Europe and North America have announced the dismantling of a criminal virtual private network (VPN) service used by criminal actors to obscure the origins of ransomware attacks, data theft, scanning, and denial-of-service attacks. Codenamed Operation Saffron, the disruption of First VPN Service was led by France and the Netherlands, with several other nations […]
Police take down VPN service (this time with a good reason)
European authorities have cracked down on a VPN that has been used for various criminal activities. The operation, led by investigators in France and the Netherlands with help from Europol and Eurojust, has dismantled First VPN, a service that has been heavily promoted within Russia as a way of evading law enforcement. Criminals used it […]
Radiology Associates of Richmond discloses second data breach; 266k people affected
On July 1, 2025, Radiology Associates of Richmond (“RAR”) reported a breach to HHS that had occurred in April 2024 and affected more than 1.4 million patients. By the end of July 2025, the well-known radiology practice had experienced a second breach. The second breach, recently reported to the Maine Attorney General’s Office on May… […]
Lawmakers Demand Answers as CISA Tries to Contain Data Leak
Lawmakers in both houses of Congress are demanding answers from the U.S. Cybersecurity & Infrastructure Security Agency (CISA) after KrebsOnSecurity reported this week that a CISA contractor intentionally published AWS GovCloud keys and a vast trove of other agency secrets on a public GitHub account. The inquiry comes as CISA is still struggling to contain […]
Ghostwriter Targets Ukraine Government Entities with Prometheus Phishing Malware
The Belarus-aligned threat actor known as Ghostwriter (aka UAC-0057 and UNC1151) has been observed using lures related to Prometheus, a Ukrainian online learning platform, to target government organizations in the country. The activity, per the Computer Emergency Response Team of Ukraine (CERT-UA), involves sending phishing emails to government entities using compromised accounts. It’s been
Microsoft says it’s making AI ‘safe for work’ in your browser
Microsoft is testing the addition of agentic AI to its corporate browser, Edge for Business. A new version, currently available in a limited preview, will help perform routine tasks more efficiently, according to Microsoft’s partner product manager for Edge, Lindsay Kubasik. Agentic AI will help with completing multi-step tasks such as filling in forms, navigating […]
Trump Mobile confirms it exposed customers’ personal data, unclear whether it will notify those affected
Lorenzo Franceschi-Bicchierai reports: Phone provider Trump Mobile has confirmed that it was exposing customers’ names, email addresses, mailing addresses, cell numbers, and order identifiers to the open internet. Chris Walker, a spokesperson for the Trump-branded phone maker, told TechCrunch that the company is investigating the exposure and has not found evidence that content or financial… […]
Proposed State Laws For Breach Notification Could Reshape Incident Response Plans
Joseph Lazzarotti of JacksonLewis writes: State breach-notification laws continue to evolve, and legislatures are using 2026 sessions to tighten consumer protections and shift the civil liability landscape that often follows a cyber event. For businesses, the practical takeaway is that incident response planning increasingly needs to account not only for “whether notice is required,” but… […]
How a consultant and a concert pianist from the Netherlands were arrested on suspicion of aiding NoName057(16)
Officials allege that WorkTitans and MIRhosting were used to facilitate pro-Russian hackers and evade EU sanctions. Huib Modderkolk and Henrik Moltke write: Youssef Z. may have seen trouble coming. The 57-year-old entrepreneur and organizational consultant from Amsterdam, arrested at his home in the early hours of Monday 18 May by agents of the Dutch fiscal investigation… […]
Hackers steal patient and billing data from German hospitals via third-party provider
Daryna Antoniuk reports: German university hospitals are grappling with a large-scale patient data breach after unknown hackers targeted an external billing service provider used by medical centers across the country, according to statements from several affected medical institutions. The attack reportedly hit Unimed, a company that handles billing services for privately insured and self-paying patients on behalf… […]
Verus Hacker Returns $8.5M After Bridge Exploit Deal
Do those who say never to pay ransomware or hack-and-leak criminals because it encourages more crime also say never to pay those who hack crypto? If you negotiate with hackers to let them keep a percent of what they stole as a non-prosecutable “bounty,” aren’t you just creating more incentive for other criminals? Kenrodgers Fabian… […]
Hugging Face Hiding Second-Stage Malware for npm Supply Chain Attack
Tushar Subhra Dutta reports: Hackers have found a new and alarming way to weaponize one of the most trusted platforms in the AI world. A threat actor linked to North Korea has embedded second-stage malware inside Hugging Face, the widely used AI and machine learning hub, effectively turning it into a malware delivery channel and… […]
Hackers breach two Vietnamese ministerial systems in major cyberattack
Vietnamnet Global reports: Speaking at the Vietnam Security Summit 2026 on May 22, Lieutenant Colonel Tran Trung Hieu, Deputy Director of the National Cybersecurity Center and Director of VNCERT under the Ministry of Public Security’s Department of Cybersecurity and High-Tech Crime Prevention, said the agency is currently responding to two highly serious data breach incidents… […]
U.S. officials seeking extradition of Ottawa man accused of record cyberattack
Jordan Ercit reports: Jacob Butler, 23, who was arrested Wednesday by OPP, also facing aiding and abetting computer intrusion charge in Alaska A 23-year-old Ottawa man is facing extradition to the United States after being accused of involvement in massive cyberattacks that affected more than a million devices worldwide. Ontario Provincial Police said their cybercrime… […]
Murphy measure to protect Illinois consumers’ sensitive data advances in Senate
From the Illinois Senate Democrats: State Senator Laura Murphy is leading a comprehensive measure to protect consumers’ data and shield them from targeted advertisements. “By placing guardrails around consumers’ personal information, we eliminate companies’ ability to collect and sell the most sensitive data of Illinoisans,” said Murphy (D-Des Plaines). “We then put the power in… […]
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2026-9082 Drupal Core SQL Injection Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk […]
Megalodon GitHub Attack Targets 5,561 Repos with Malicious CI/CD Workflows
Cybersecurity researchers have disclosed details of a new automated campaign called Megalodon that has pushed 5,718 malicious commits to 5,561 GitHub repositories within a six-hour window. “Using throwaway accounts and forged author identities (build-bot, auto-ci, ci-bot, pipeline-bot), the attacker injected GitHub Actions workflows containing base64-encoded bash payloads that exfiltrate CI
Making Vulnerable Drivers Exploitable Without Hardware - The BYOVD Perspective
1 Introduction This article provides a technical analysis of how many Windows kernel mode drivers can be interacted with from user mode without the hardware they were developed for. This work was motivated by driver-oriented vulnerability research and the need to evaluate the exploitability of individual findings, which frequently affect code whose reachability is hardware-gated. […]
Apple Rejected 2 Million App Store Submissions in 2025 for Security and Fraud Prevention
The company blocked over 1.1 billion accounts and $2.2 billion in potentially fraudulent transactions. The post Apple Rejected 2 Million App Store Submissions in 2025 for Security and Fraud Prevention appeared first on SecurityWeek.
Ocean Emerges From Stealth With $28M for Agentic Email Security Platform
The company has developed a platform that uses specialized AI agents to inspect every incoming message. The post Ocean Emerges From Stealth With $28M for Agentic Email Security Platform appeared first on SecurityWeek.
Cisco Patches Critical Vulnerability in Secure Workload
Insufficient validation and authentication in the Secure Workload’s REST APIs provide remote attackers with Site Admin privileges. The post Cisco Patches Critical Vulnerability in Secure Workload appeared first on SecurityWeek.
Grafana Says Codebase and Other Data Stolen via TanStack Supply Chain Attack
Hackers accessed Grafana’s GitHub repositories after a token compromised in the TanStack attack was not rotated. The post Grafana Says Codebase and Other Data Stolen via TanStack Supply Chain Attack appeared first on SecurityWeek.
TrendAI Patches Apex One Zero-Day Exploited in the Wild
CVE-2026-34926 is a directory traversal flaw that can be exploited against the on-premise version of Apex One. The post TrendAI Patches Apex One Zero-Day Exploited in the Wild appeared first on SecurityWeek.
‘First VPN’ Cybercrime Service Disrupted, Administrator Arrested
The FBI says First VPN has been used by dozens of ransomware groups for network reconnaissance and intrusions. The post ‘First VPN’ Cybercrime Service Disrupted, Administrator Arrested appeared first on SecurityWeek.
Asociația Techsoup: Reclaiming Agency in the Age of AI
Impact story from Hello AI! exhibition by Tactical Tech in Romania
Why your AI strategy stops where the PLC starts: Hard lessons from the OT frontlines
I spent two days at a substation connecting a major offshore wind farm to the grid. The control room featured three new AI-ready dashboards and a board mandate to “leverage machine learning for resilience.” It also had a maintenance laptop running Windows 7, literally taped to the inside of a cabinet because the Velcro had […]
Identity as the primary attack surface: What modern breaches are really exploiting
The “retro” way “The thing about the old days is… they are the old days” – Slim Charles, The Wire Protecting a specified network perimeter was the main focus of enterprise security strategy for several decades. Businesses made significant investments in firewalls, intrusion detection systems, endpoint security and segmentation controls, all of which were built […]
Kimwolf DDoS Botnet Operator Arrested in Canada Over DDoS-for-Hire Attacks
The U.S. Department of Justice (DoJ) on Thursday announced the arrest of a Canadian man in connection with allegedly operating a distributed denial-of-service (DDoS) botnet known as Kimwolf. In tandem, Jacob Butler (aka Dort), 23, Ottawa, Canada, has been charged with offenses related to the development and operation of the botnet. Kimwolf is assessed to […]
120th Plenary meeting
120th Plenary meeting icolonnm Fri, 22/05/2026 – 10:07 28 May 2026 Remote Agenda 20260528-plen-agenda_en.pdf Agenda
Google folds CodeMender into agent ecosystem amid push for AI-led AppSec
Google is expanding the role of its CodeMender security agent from autonomous vulnerability remediation toward a larger agentic development ecosystem, signalling a broader push toward AI-driven AppSec. Months after introducing CodeMender, an AI-powered agent designed to autonomously identify and patch software vulnerabilities, Google is now integrating the technology into its expanding Agent Platform strategy unveiled […]
Cross-Platform NPM Stealer, (Fri, May 22nd)
I found a Node.js stealer that looked pretty well obfuscated. The file was not running out-of-the-box because it was uploaded on VT as “extracted-decoded.js” (and reformated). The SHA256 is 049300aa5dd774d6c984779a0570f59610399c71864b5d5c2605906db46ddeb9[1]. It did not run properly in a sandbox so only a static analysis was performed.
CISA Adds Exploited Langflow and Trend Micro Apex One Vulnerabilities to KEV
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added two security flaws impacting Langflow and Trend Micro Apex One to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation. The vulnerabilities in question are listed below – CVE-2025-34291 (CVSS score: 9.4) – An origin validation error vulnerability in Langflow that could
Cisco Patches CVSS 10.0 Secure Workload REST API Flaw Enabling Data Access
Cisco has rolled out updates for a maximum-severity security flaw impacting Secure Workload that could allow an unauthenticated, remote attacker to access sensitive data. Tracked as CVE-2026-20223 (CVSS score: 10.0), the vulnerability arises from insufficient validation and authentication when accessing REST API endpoints. “An attacker could exploit this vulnerability if they are able to send
ISC Stormcast For Friday, May 22nd, 2026 https://isc.sans.edu/podcastdetail/9942, (Fri, May 22nd)
Post Content
25-00731(2).pdf
25-00731(2).pdf Anonymous (not verified) Thu, 05/21/2026 – 19:25 Case ID 25-00731 Forum FINRA Document Type Award Claimants Erlinda Rizzo Respondents Raymond James Financial Services, Inc. Robert Cutrupi Neutrals Jeffrey Alan Helewitz Hearing Site Jersey City, NJ Award Document 25-00731(2).pdf Documentum DocID f3f220b7 Award Date Official Tue, 04/14/2026 – 12:00 Related Content On Claimant Representatives Erlinda […]
25-02204.pdf
25-02204.pdf Anonymous (not verified) Thu, 05/21/2026 – 19:15 Case ID 25-02204 Forum FINRA Document Type Award Claimants Matthew Cardella Respondents Edward Jones Northwestern Mutual Investment Services, LLC Neutrals Michael J. Meeusen Thomas J. Ray Daniel B. MacLeod Hearing Site Jacksonville, FL Award Document 25-02204.pdf Documentum DocID aba86418 Award Date Official Thu, 05/21/2026 – 12:00 Related […]
25-02785.pdf
25-02785.pdf Anonymous (not verified) Thu, 05/21/2026 – 19:15 Case ID 25-02785 Forum FINRA Document Type Award Claimants Ahmad Quqa Respondents Edward Jones Neutrals Herb Schwartz Darryl C. Wilson James W. Kerr Hearing Site Raleigh, NC Award Document 25-02785.pdf Documentum DocID 7c253c57 Award Date Official Thu, 05/21/2026 – 12:00 Related Content Off Claimant Representatives David I. […]
22-02899.pdf
22-02899.pdf Anonymous (not verified) Thu, 05/21/2026 – 19:15 Case ID 22-02899 Forum FINRA Document Type Award Claimants Charles Schwab & Co., Inc. Respondents Sarah Villalobos Neutrals Linda M. Edwards Ruth M. Moore Nancy B Merrill Hearing Site Denver, CO Award Document 22-02899.pdf Documentum DocID 0a8adafe Award Date Official Thu, 05/21/2026 – 12:00 Related Content Off […]
25-00898.pdf
25-00898.pdf Anonymous (not verified) Thu, 05/21/2026 – 19:15 Case ID 25-00898 Forum FINRA Document Type Award Claimants Mark Carter Respondents NYLife Securities LLC Neutrals Karimu F. Hill-Harvey Michael J. Ahlstrom Keely D. Parr Hearing Site Detroit, MI Award Document 25-00898.pdf Documentum DocID db2c8f66 Award Date Official Thu, 05/21/2026 – 12:00 Related Content Off Claimant Representatives […]
Critical vulnerability in Cisco Secure Workload rated at maximum severity
A critical vulnerability in the on-premises version of the Cisco Secure Workload security platform could allow a threat actor to obtain the privileges of a site admin, enabling them to compromise endpoints and read or modify configuration data. “CSOs need to drop what they are doing and patch this immediately,” warned consultant Robert Enderle, who […]
Microsoft patches two zero-day flaws in Defender
Microsoft released emergency fixes for two zero-day vulnerabilities in the malware protection components of Microsoft Defender. The flaws allow local attackers to gain system-level privileges or cause the anti-malware service to stop working correctly. Both conditions are valuable in a malware attack, first to prevent detection if the system relies only on Microsoft endpoint protection […]
Alleged Kimwolf Botmaster ‘Dort’ Arrested, Charged in U.S. and Canada
Canadian authorities on Wednesday arrested a 23-year-old Ottawa man on suspicion of building and operating Kimwolf, a fast spreading Internet-of-Things botnet that enslaved millions of devices for use in a series of massive distributed denial-of-service (DDoS) attacks over the past six months. KrebsOnSecurity publicly named the suspect in February 2026 after the accused launched a […]
Unpatched ChromaDB flaw leaves servers open to remote code execution
Researchers have published details about a critical vulnerability in ChromaDB that could allow unauthenticated attackers to execute arbitrary code and access sensitive data on machines running the open-source vector database. The issue, tracked as CVE-2026-45829, is located in ChromaDB’s API server and was published by researchers at HiddenLayer after reportedly failing to get in contact […]
칼럼 | AI 시대, 개발자 역할 ‘코딩→에이전트 관리’로 재정의해야
몇 년 전만 해도 소프트웨어 개발에서 AI는 간혹 변수 이름을 예측해주는 자동완성 기능을 의미했다. 그러나 지금은 상황이 완전히 달라졌다. 마치 옆자리에 앉아 함께 일하는 또 다른 엔지니어를 둔 것과 유사한 환경이 만들어졌다. 이 엔지니어는 잠도 자지 않고, 문맥 전환에도 불평하지 않으며, 어떤 인간보다도 많은 코드를 학습한 존재다. 오케스트레이션을 적절히 활용하면 사실상 하나의 추가 엔지니어링 팀을 […]
AI 실험은 끝났다…CEO가 원하는 건 ‘매출로 이어지는 기술’
거의 모든 CIO에게 AI 도입은 최우선 과제로 자리 잡았다. CEO가 직접 내려보낸 핵심 지시사항이다. CIO.com의 ‘2026년 CIO 현황 조사’에 따르면, CEO들은 CIO의 최우선 과제로 AI 연구와 도입을 꼽았다. 이러한 결과는 다른 여러 조사와도 일치하며, AI 구현을 IT 부문의 최우선 과제로 지목했던 2025년 조사와도 같은 흐름을 보인다. 다만 CEO들의 기대는 한층 높아졌다. 더 이상 AI 실험이나 […]
Sólo 2 de cada 10 empresas españolas contaría con una plantilla realmente preparada para adaptarse a la IA
La inteligencia artificial (IA) avanza rápido, muy rápido. Tanto, que muchos equipos no cuentan con la capacidad suficiente para preparar a sus equipos según se desprende del informe The human premium: leadership beyond the algorithm de Business Leaders, elaborado por el Grupo Adecco. Y es que, si bien la mayoría de las compañías ya explora […]
The dark data problem hiding inside your AI agents
OpenClaw recently crossed 250,000 GitHub stars in just 60 days, surpassing React’s decade-long record to become the most-starred software project in GitHub’s history. At GTC 2026, in his keynote speech, NVIDIA CEO Jensen Huang called it “the operating system for personal AI” and said, “For the CEOs, the question is, what’s your OpenClaw strategy?” I […]
Your Claude API bill is higher than your revenue: Why simple Python tasks are blowing up AI costs
Your most-used artificial intelligence feature may be your least profitable corporate asset. That contradiction does not appear at launch. Early signals almost always point to operational success. Usage increases, user engagement climbs and internal product dashboards trend in the right direction. Your teams report efficiency gains, and executive leadership sees widespread adoption across the business. […]
Can AI thrive without neurodivergent talent?
Earlier this year, Alex Karp, CEO of software company Palantir, said there are two paths to a successful future in the age of AI: vocational training or being neurodivergent. As co-president and CTO of Understood.org, a leading nonprofit that supports millions of neurodivergent people in the US, I see why this sentiment resonates. But it doesn’t […]
CIOs should beware the AI confidence trap
Facing an AI make-or-break moment, IT leaders are confident of success, but most aren’t tracking the impact of AI projects to prove it. According to a survey by Economist Impact, 84% of IT leaders say their AI returns are beating original estimates, but only 43% require teams to track the impact of AI projects, begging […]
Reflections on RSAC and the Mythos of agents
Another RSAC in San Francisco wrapped recently, and unsurprisingly, one topic dominated: AI agents. In hallway conversations, panels and private meetings, AI agents, and the risks they introduce, were front and center. That shouldn’t surprise anyone. Over the past year, agents have become embedded across enterprise workflows, making decisions and acting autonomously across departments, from […]
¿La IA puede avanzar sin talento neurodivergente?
A principios de este año, Alex Karp, CEO de la empresa de software Palantir, afirmó que existen dos caminos hacia un futuro exitoso en la era de la IA: la formación profesional o ser neurodivergente. Como copresidente y CTO de Understood.org, una destacada organización sin fines de lucro que apoya a millones de personas neurodivergentes […]
Tribal Raises $10M to Make Enterprise AI Production-Ready
Most enterprise AI tools sit outside the system of record. They generate code that compliance teams can’t audit and CIOs can’t deploy with confidence. Tribal works the other way: AI agents that operate inside the customer’s existing system of record. The metadata graph and every generated artifact live in the customer’s own system of record. […]
Operation Saffron: Bitdefender Joins “First VPN” Takedown
Bitdefender reports: An international law enforcement operation led by France and the Netherlands dismantled First VPN, a cybercriminal anonymization service used by ransomware actors, fraudsters, and data thieves across every major cybercrime investigation Europol has supported in recent years. Bitdefender supported the investigation through Europol, helping generate intelligence that exposed hundreds of individuals linked to cybercrime…. […]
Kaspersky, Group-IB Detail Role in INTERPOL Cyber Operation Involving Morocco
Adil Faouzi reports: Global cybersecurity firms Kaspersky and Group-IB have disclosed their contributions to Operation Ramz, the first large-scale cybercrime crackdown coordinated by INTERPOL across the Middle East and North Africa region. The operation, which ran from October 2025 to February 2026, brought together 13 countries and resulted in 201 arrests, with 382 additional suspects… […]
UK plans for cybercrime law reform would protect almost no one, experts warn
Alexander Martin reports: The British government’s plans to overhaul the country’s main cybercrime law would offer such narrow legal protections that most security researchers would be left in the same position as today, multiple sources briefed on the proposals have told Recorded Future News. Plans to amend the Computer Misuse Act 1990 were announced in the… […]
Showboat Linux Malware Hits Middle East Telecom with SOCKS5 Proxy Backdoor
Cybersecurity researchers have disclosed details of a new Linux malware dubbed Showboat that has been put to use in a campaign targeting a telecommunications provider in the Middle East since at least mid-2022. “Showboat is a modular post-exploitation framework designed for Linux systems, capable of spawning a remote shell, transferring files, and functioning as a […]
Selective HTTP Proxying in Linux, (Thu, May 21st)
Recently, Rob wrote about a tool, Proxifier, that can intercept requests from specific processes. Proxifier is available for Windows, macOS, and Android. But I have not seen a generic Linux option yet. The advantage of a tool like Proxifier is the ability to target specific software. For debugging, reverse engineering, and similar tasks, selecting a […]
Today’s reminder to terminate employees’ credentials when their employment ends
Failure to terminate an employee’s credentials when their employment ended and failure to use unique and protected login credentials for work left a city at risk of having its water utility totally compromised. Avram Piltch reports: Our tale of tech missteps comes courtesy of Nicole Beckwith, who serves as the senior director for security engineering… […]
GitHub confirms breach of 3,800 repos via malicious VSCode extension
Sergiu Gatlan reports: GitHub has confirmed that roughly 3,800 internal repositories were breached after one of its employees installed a malicious VS Code extension. The company has since removed the unnamed trojanized extension from the VS Code marketplace and has secured the compromised device. “Yesterday we detected and contained a compromise of an employee device… […]
CISA Adds Two Known Exploited Vulnerabilities to Catalog
CISA has added two new vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2025-34291 Langflow Origin Validation Error Vulnerability CVE-2026-34926 Trend Micro Apex One (On-Premise) Directory Traversal Vulnerability These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise. Binding […]
ABB B&R PCs
View CSAF Summary ABB became aware of vulnerability in the product versions listed as affected in the advisory. An update is now available that addresses and remediates the vulnerability. A network attacker could exploit the vulnerabilities to execute remote code, initiate DoS attacks, conduct DNS cache poisoning, or extract sensitive information. The following versions of […]
ABB B&R Automation Runtime
View CSAF Summary An update is available that resolves a vulnerability identified by B&Rs internal security analysis in the product versions listed as affected in this advisory. An attacker who successfully exploited these vulnerabilities could take over a remote session or execute code in the context of the user’s browser session. The following versions of […]
ABB B&R Automation Studio
View CSAF Summary ABB became aware of vulnerability in the product versions listed as affected in the advisory. An update is available that replaces an outdated third-party component. Although no successful exploitation was observed during testing of the affected B&R products, the identified vulnerabilities could present potential attack vectors that might enable unauthorized access, data […]
Hitachi Energy GMS600
View CSAF Summary Hitachi Energy is aware of the vulnerability, CVE-2022-4304 in the OSS component OpenSSL, that affects the GMS600 versions that are listed below. An attacker successfully exploiting this vulnerability could send trial messages to the server and record the time taken to process them. After a sufficiently large number of messages the attacker […]
ABB Terra AC Wallbox
View CSAF Summary ABB is aware of vulnerabilities in the product versions listed as affected in the advisory. An attacker who successfully exploited this vulnerability could cause the pollution of heap memory which potentially takes remote control of the product and performs a write operation to the flash memory to alter the firmware behavior. The […]
ThreatsDay Bulletin: Linux Rootkits, Router 0-Day, AI Intrusions, Scam Kits and 25 New Stories
This week starts small. A token leaks. A bad package slips in. A login trick works. An old tool shows up again. At first, it feels like the usual mess. Then you see the pattern: attackers are not always breaking in. They are using the parts we already trust. That is what makes it worrying. […]
Anthropic Silently Patches Claude Code Sandbox Bypass
The researcher who found it says the vulnerability could have been chained with a prompt injection to exfiltrate data. The post Anthropic Silently Patches Claude Code Sandbox Bypass appeared first on SecurityWeek.
1Password Teams With OpenAI to Stop AI Coding Agents From Leaking Credentials
1Password says AI coding agents should never hold persistent secrets, introducing a just-in-time credential model for OpenAI Codex designed to keep credentials out of prompts, code repositories, and model context. The post 1Password Teams With OpenAI to Stop AI Coding Agents From Leaking Credentials appeared first on SecurityWeek.
AI-Powered App Attacks Are Faster, More Frequent and Harder to Stop
Digital.ai’s latest threat report warns that agentic AI has erased the distinction between emerging and primary targets, enabling attackers to strike mobile apps within hours of release across every industry. The post AI-Powered App Attacks Are Faster, More Frequent and Harder to Stop appeared first on SecurityWeek.
Microsoft Rolls Out Mitigations for ‘YellowKey’ BitLocker Bypass
The exploitation is mitigated by preventing the FsTx Auto Recovery Utility from starting when the WinRE image launches. The post Microsoft Rolls Out Mitigations for ‘YellowKey’ BitLocker Bypass appeared first on SecurityWeek.
Quantum Bridge Raises $8 Million for Quantum-Safe Key Distribution Solution
The new Series A funding round brings the total raised by Quantum Bridge to $16 million. The post Quantum Bridge Raises $8 Million for Quantum-Safe Key Distribution Solution appeared first on SecurityWeek.
Supply Chain Security Crisis: Too Many Vulnerabilities, Too Little Visibility
New vulnerabilities are being discovered too fast, the time-to-exploitation is too short, and our visibility into them is largely lacking. The post Supply Chain Security Crisis: Too Many Vulnerabilities, Too Little Visibility appeared first on SecurityWeek.
Google’s Surge in Chrome Vulnerability Discoveries Likely Driven by AI
More than 200 vulnerabilities patched in recent Chrome releases are marked as ‘reported by Google’. The post Google’s Surge in Chrome Vulnerability Discoveries Likely Driven by AI appeared first on SecurityWeek.
Microsoft Patches Exploited UnDefend and RedSun Defender Zero-Days
The bugs could be exploited to elevate privileges to System or create a denial-of-service (DoS) condition. The post Microsoft Patches Exploited UnDefend and RedSun Defender Zero-Days appeared first on SecurityWeek.
Socket Raises $60 Million at $1 Billion Valuation
The company will invest in its firewall, certified patches, protection extensions, new products, and team expansion. The post Socket Raises $60 Million at $1 Billion Valuation appeared first on SecurityWeek.
Drupal Patches Highly Critical Vulnerability Exposing Websites to Hacking
CVE-2026-9082 can be exploited without authentication for information disclosure, privilege escalation, and remote code execution. The post Drupal Patches Highly Critical Vulnerability Exposing Websites to Hacking appeared first on SecurityWeek.
Microsoft Warns of Two Actively Exploited Defender Vulnerabilities
Microsoft has disclosed that a privilege escalation and a denial-of-service flaw in Defender has come under active exploitation in the wild. The former, tracked as CVE-2026-41091, is rated 7.8 on the CVSS scoring system. Successful exploitation of the flaw could allow an attacker to gain SYSTEM privileges. “Improper link resolution before file access (‘link following’) […]
Reclaiming Agency in the Age of AI
Impact story from Hello AI! exhibition by Tactical Tech in Romania
When Identity is the Attack Path
Consider a cached access key on a single Windows machine. It got there the way most cached credentials do – a user logged in, and the key stored itself automatically. Standard AWS behavior. No one misconfigured anything or violated a policy. Yet that single key, which was easily accessible to a minor-league attacker, could have […]
Microsoft releases open-source tools to operationalize AI agent safety
Microsoft has open-sourced two new tools aimed at bringing AI safety checks much earlier into the agent development lifecycle. The tools, called Rampart and Clarity, were announced this week as part of Microsoft’s broader push to operationalize safety engineering for agentic AI. “We built these tools because we believe that AI safety has to become […]
9-Year-Old Linux Kernel Flaw Enables Root Command Execution on Major Distros
Cybersecurity researchers have disclosed details of a vulnerability in the Linux kernel that remained undetected for nine years. The vulnerability, tracked as CVE-2026-46333 (CVSS score: 5.5), is a case of improper privilege management that could permit an unprivileged local user to disclose sensitive files and execute arbitrary commands as root on default installations of several […]
AI becoming an SOC imperative for curtailing emerging cyber threats
The cybersecurity profession is on the verge of a sea change, and security pros must begin to master AI tools to combat emerging threats by building more autonomous, real-time protections. Expert panelists at a recent DTX conference session in Manchester, titled “Bot vs Bot: Surviving the Era of Autonomous Cyber Warfare,” highlighted how bringing AI […]
GitHub Internal Repositories Breached via Malicious Nx Console VS Code Extension
GitHub on Wednesday officially confirmed that the breach of its internal repositories was the result of a compromise of an employee device involving a poisoned version of the Nx Console Microsoft Visual Studio Code (VS Code) extension. The development comes as the Nx team revealed that the extension, nrwl.angular-console, was breached after one of its […]
Highly Critical Drupal Core Flaw Exposes PostgreSQL Sites to RCE Attacks
Drupal has released security updates for a “highly critical” security vulnerability in Drupal Core that could be exploited by attackers to achieve remote code execution, privilege escalation, or information disclosure. The vulnerability, now tracked as CVE-2026-9082, carries a CVSS score of 6.5 out of 10.0, per CVE.org. Drupal said the vulnerability resides in a database […]
ISC Stormcast For Thursday, May 21st, 2026 https://isc.sans.edu/podcastdetail/9940, (Thu, May 21st)
Post Content
Microsoft is working on a patch for ‘YellowKey’ attack on Bitlocker, offers temporary fix
Microsoft says it is considering a patch for a zero-day vulnerability, dubbed YellowKey, that allows attackers with access to a Windows device to bypass Bitlocker encryption protection and read and write files. The flaw was disclosed last week, and there is already a public proof of concept available. The company issued an advisory Tuesday saying […]
Drupal admins rushing to patch maximum severity SQL injection vulnerability
Administrators of the Drupal open source content management platform are rushing to install an emergency patch issued today to fix a “highly critical” SQL injection vulnerability in the application’s core. While the vulnerability only affects websites that use the PostgreSQL database, there may be upstream issues with Symfony, a set of PHP packages and web […]
25-00585.pdf
25-00585.pdf Anonymous (not verified) Wed, 05/20/2026 – 19:40 Case ID 25-00585 Forum FINRA Document Type Award Claimants Jerry Thompson The Jerry Thompson IRA Respondents Center Street Securities, Inc. Neutrals Thomas R. Watkins Richard Kent Mahrle David J Neri Hearing Site Phoenix, AZ Award Document 25-00585.pdf Documentum DocID 1b2f4bd9 Award Date Official Wed, 05/20/2026 – 12:00 […]
25-02022.pdf
25-02022.pdf Anonymous (not verified) Wed, 05/20/2026 – 19:40 Case ID 25-02022 Forum FINRA Document Type Award Claimants Timothy Whitehurst Respondents Merrill Lynch Pierce Fenner & Smith Inc. Neutrals Jack R. Goetz Hearing Site Los Angeles, CA Award Document 25-02022.pdf Documentum DocID f105c75f Award Date Official Wed, 05/20/2026 – 12:00 Related Content Off Claimant Representatives William […]
24-02061.pdf
24-02061.pdf Anonymous (not verified) Wed, 05/20/2026 – 17:40 Case ID 24-02061 Forum FINRA Document Type Award Claimants Joseph Kirkland Respondents U.S. Bancorp Advisors, LLC Neutrals Kirtley M. Thiesmeyer Robert F. Miller Leslie Marie Hopp Hearing Site Los Angeles, CA Award Document 24-02061.pdf Documentum DocID 496a2549 Award Date Official Wed, 05/20/2026 – 12:00 Related Content Off […]
25-02331(2).pdf
25-02331(2).pdf Anonymous (not verified) Wed, 05/20/2026 – 17:15 Case ID 25-02331 Forum FINRA Document Type Award Claimants Samuel Gulla Respondents Robert Farrar PFS Investments Inc. Neutrals Lisa Manget Buchanan Hearing Site Boston, MA Award Document 25-02331(2).pdf Documentum DocID 8131df69 Award Date Official Mon, 04/27/2026 – 12:00 Related Content On Claimant Representatives Samuel J. Gulla Respondent […]
25-02043.pdf
25-02043.pdf Anonymous (not verified) Wed, 05/20/2026 – 17:15 Case ID 25-02043 Forum FINRA Document Type Award Claimants Zheyuan Feng Respondents Robinhood Financial, LLC. Neutrals Linda J. Baer Hearing Site Chicago, IL Award Document 25-02043.pdf Documentum DocID 5a73fe18 Award Date Official Wed, 05/20/2026 – 12:00 Related Content Off Claimant Representatives Zheyuan Feng Respondent Representatives Lawton R. […]
The SaaS reckoning: Why AI is about to reprice enterprise software
For most of my career, the enterprise software conversation followed a predictable script. A CRM, an ITSM platform, an ERP system, these were not things you built. They were things you bought, implemented and lived with. The reasoning was sound: Building them required enormous capital, long engineering tenures and specialized domain depth that only a […]
6 ways CIOs should diversify leadership skills
Doing a great job in your current role is table stakes for modern CIOs. The most successful digital leaders embrace new challenges in situ and in fresh working environments, and with research reporting the average tenure for any digital leadership role to be about five years, the ability to move seamlessly into new opportunities has […]
What is enterprise architecture? A framework for transformation
What is enterprise architecture? Enterprise architecture (EA) is the practice of analyzing, designing, planning, and implementing enterprise analysis to successfully execute on business strategies. EA helps organizations structure IT projects and policies to achieve desired business results, stay agile and resilient in the face of rapid change, and stay on top of industry trends and […]
The zero-trust paradox: Why systems built to eliminate trust may be destroying it
There is a phrase I have used in dozens of security briefings over the past decade, delivered to boards, to engineering teams, to skeptical CFOs trying to understand why we needed to rebuild our entire network architecture: “Never trust, always verify.” It is clean, logical and sounds like exactly the kind of discipline that organizations […]
AI can write code, but the CIOs still owns the operating model
AI is moving into the enterprise faster than most organizations are prepared for it. What began as experimentation with chat interfaces and narrow use cases is now showing up in real workflows, productivity tools and early agentic capabilities that are becoming part of how work gets done. That shift is creating a new challenge for […]
Google talks ‘singularity’ while scaling up agentic AI for enterprises
Google is recasting its enterprise AI roadmap around autonomous systems and artificial general intelligence (AGI), with DeepMind CEO Demis Hassabis telling I/O attendees the industry now sits at the “foothills of the singularity.” “When we look back at this time, I think we all realise that we were standing in the foothills of the singularity,” […]
Seis claves para que los CIO diversifiquen sus capacidades de liderazgo
Dsempeñar un gran trabajo en el puesto actual es lo mínimo exigible para los CIO modernos. Los líderes digitales más exitosos adoptan nuevos retos tanto dentro de su organización como en nuevos entornos de trabajo, y dado que los estudios sitúan la permanencia media en un puesto de liderazgo digital en unos cinco años, la […]
The sustainability blind spot CIOs can’t ignore
In pursuit of lower emissions and reduced operational costs, CIOs continue to prioritize cloud efficiency, workload optimization, and infrastructure. Those efforts undoubtedly matter…but they no longer tell the full story. While IT sustainability strategies have traditionally homed in on the data center, a growing share of enterprise infrastructure now lives outside of those hubs. These […]
Video has evolved from monitoring to vision intelligence
Enterprises are sitting on a massive, underutilized asset: the data produced by their physical environments, especially from network cameras and sensors. Historically seen only as “security devices,” modern cameras are now rich data generators. In fact, the “Axis Perspectives Report 2026” shows that the number of organizations using video systems for business intelligence nearly doubled between 2024 […]
Cómo IKEA convirtió un ‘chatbot’ de 13 millones en un negocio de 1.300
En 2021, Ingka Group (el principal operador de las tiendas IKEA, con aproximadamente 90% de las ventas globales), puso en marcha un chatbot llamado Billie. El objetivo era el típico de un asistente conversacional: responder a las consultas rutinarias de los clientes, como disponibilidad de producto, plazos de entrega o estado de un pedido. De […]
Microsoft Open-Sources RAMPART and Clarity to Secure AI Agents During Development
Microsoft has unveiled two new open-source tools called RAMPART and Clarity to assist developers in better testing the security of artificial intelligence (AI) agents. RAMPART, short for Risk Assessment and Measurement Platform for Agentic Red Teaming, functions as a Pytest-native safety and security testing framework for writing and running safety and security tests for AI […]
GitHub admits major source code leak after 3,800 internal repositories breached
Microsoft’s GitHub has suffered what appears to be its biggest ever security breach after confirming that attackers exfiltrated code from around 3,800 of the company’s internal repositories. News of the incident first emerged on May 19, when GitHub said it was investigating “unauthorized access.” Hours later, the company’s X account confirmed the worst: “Yesterday we […]
Microsoft Takes Down Malware-Signing Service Behind Ransomware Attacks
Microsoft on Tuesday said it disrupted a malware-signing-as-a-service (MSaaS) operation that weaponized the company’s Artifact Signing system to deliver malicious code and conduct ransomware and other attacks, compromising thousands of machines and networks across the world. The tech giant attributed the activity to a threat actor it calls Fox Tempest, which it said offered the […]
Webworm Deploys EchoCreep and GraphWorm Backdoors Using Discord and MS Graph API
Cybersecurity researchers have flagged fresh activity from a China-aligned threat actor known as Webworm in 2025, deploying custom backdoors that employ Discord and Microsoft Graph API for command-and-control (C2 or C&C) communications. Webworm, first publicly documented by Broadcom-owned Symantec in September 2022, is assessed to be active since at least 2022, targeting government agencies
CISA Adds Seven Known Exploited Vulnerabilities to Catalog
CISA has added seven new vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2008-4250 Microsoft Windows Buffer Overflow Vulnerability CVE-2009-1537 Microsoft DirectX NULL Byte Overwrite Vulnerability CVE-2009-3459 Adobe Acrobat and Reader Heap-Based Buffer Overflow Vulnerability CVE-2010-0249 Microsoft Internet Explorer Use-After-Free Vulnerability CVE-2010-0806 Microsoft Internet Explorer Use-After-Free Vulnerability CVE-2026-41091 Microsoft […]
Agent AI is Coming. Are You Ready?
New Industry Data Just Released Suggests Not. On May 19th, 2026, Orchid Security released the results of our Identity Gap: Snapshot 2026. Among the findings, “identity dark matter” (the unseen, unmanaged elements of identity) now overshadows the visible elements 57% vs. 43%. And it couldn’t have occurred at a worse time, with enterprises embracing Agent […]
SHub Reaper impersonates Apple, Google, and Microsoft in one MacOS attack chain
A newly disclosed macOS infostealer campaign is exploiting user trust in some of the biggest names in tech to slip past defenses. Researchers at SentinelOne have detailed a new variant of the SHub malware family, dubbed “Reaper,” that impersonates Apple, Google, and Microsoft at different stages of a single attack chain targeting Mac users. The […]
B1ack’s Stash Marketplace Gives Away 4.6 Million Stolen Credit Cards
The stolen credit card data was released as a free download, allegedly in response to seller misconduct. The post B1ack’s Stash Marketplace Gives Away 4.6 Million Stolen Credit Cards appeared first on SecurityWeek.
Unpatched ChromaDB Vulnerability Can Lead to Server Takeover
The security defect can be exploited remotely, without authentication, to execute arbitrary code and leak sensitive information. The post Unpatched ChromaDB Vulnerability Can Lead to Server Takeover appeared first on SecurityWeek.
Legacy Windows Tool MSHTA Fuels Surge in Silent Malware Attacks
Attackers are increasingly abusing Microsoft’s decades-old MSHTA utility to stealthily deliver stealers, loaders, and persistent malware through phishing, fake software downloads, and LOLBIN-based attack chains. The post Legacy Windows Tool MSHTA Fuels Surge in Silent Malware Attacks appeared first on SecurityWeek.
Microsoft Disrupts Malware-Signing Service Run by ‘Fox Tempest’
Fox Tempest provides a service that cybercriminals use to distribute ransomware and other malware disguised as legitimate software. The post Microsoft Disrupts Malware-Signing Service Run by ‘Fox Tempest’ appeared first on SecurityWeek.
Drupal to Patch Highly Critical Vulnerability at Risk of Quick Exploitation
Drupal says attackers may develop an exploit for the vulnerability within hours or days. The post Drupal to Patch Highly Critical Vulnerability at Risk of Quick Exploitation appeared first on SecurityWeek.
Verizon DBIR 2026: Vulnerability Exploitation Overtakes Credential Theft as Top Breach Vector
Verizon’s 2026 DBIR finds vulnerability exploitation has overtaken credential abuse as the leading breach vector, as AI accelerates attacks, patching delays worsen, and ransomware and third-party compromises continue to surge. The post Verizon DBIR 2026: Vulnerability Exploitation Overtakes Credential Theft as Top Breach Vector appeared first on SecurityWeek.
GitHub Confirms Hack Impacting 3,800 Internal Repositories
The TeamPCP hacking group accessed the repositories after a GitHub employee installed a poisoned VS Code extension. The post GitHub Confirms Hack Impacting 3,800 Internal Repositories appeared first on SecurityWeek.
Virtual Event Today: Threat Detection & Incident Response Summit
Don’t miss this virtual event as we explore how to cut through alert fatigue, leverage AI and unified platforms to accelerate investigations, and apply actionable threat intelligence. The post Virtual Event Today: Threat Detection & Incident Response Summit appeared first on SecurityWeek.
Real-World ICS Security Tales From the Trenches
SecurityWeek spoke with several ICS security experts and companies about their most memorable experiences in the field. The post Real-World ICS Security Tales From the Trenches appeared first on SecurityWeek.
Caught Off Guard: Securing AI After It Hits Production
As enterprises rush AI projects into production, security teams are increasingly being forced into reactive mode. The post Caught Off Guard: Securing AI After It Hits Production appeared first on SecurityWeek.
Typosquatting Is No Longer a User Problem. It's a Supply Chain Problem
AI-generated lookalike domains are now embedded inside the third-party scripts running on your web properties. Here’s why your current stack can’t see them, and what detection actually requires. Download the CISO Expert Guide to Typosquatting in the AI Era → TL;DR Typosquatting is no longer a user problem. Attackers now embed lookalike domains inside legitimate […]
Why some security fixes never reach your vulnerability dashboard
On April 22, for roughly 90 minutes, a malicious version of Bitwarden CLI appeared on npm. Version 2026.4.0 contained a credential-stealing payload that executed an obfuscated loader and harvested AWS, Azure, GCP, GitHub, and npm tokens from any developer machine that ran npm install. The attackers reached Bitwarden’s npm publishing path through a compromised GitHub […]
Microsoft Releases Mitigation for YellowKey BitLocker Bypass CVE-2026-45585 Exploit
Microsoft on Tuesday released a mitigation for a BitLocker bypass vulnerability named YellowKey following its public disclosure last week. The zero-day flaw, now tracked as CVE-2026-45585, carries a CVSS score of 6.8. It has been described as a BitLocker security feature bypass. “Microsoft is aware of a security feature bypass vulnerability in Windows publicly referred […]
Risky Business #838 -- GitHub investigates possible breach
On this week’s show Patrick Gray, Adam Boileau and James Wilson discuss the week’s cybersecurity news. They cover: GitHub announced a possible breach CISA leaks important creds, keys in public repo Awful vulnerability in Bitlocker renders it useless without a PIN So. Many. Patches. Polish Government urges officials to ditch Signal for mSzyfr Much, much […]
Grafana GitHub Breach Exposes Source Code via TanStack npm Attack
Grafana Labs, on May 19, 2026, said an investigation into its recent breach found no evidence of customer production systems or operations being compromised. It said the scope of the incident is limited to the Grafana Labs GitHub environment, which includes public and private source code along with internal GitHub repositories. “After the initial assessment, […]
GitHub Breached — Employee Device Hack Led to Exfiltration of 3,800+ Internal Repos
GitHub on Tuesday said it’s investigating unauthorized access to its internal repositories after the notorious threat actor known as TeamPCP listed the platform’s source code and internal organizations for sale on a cybercrime forum. “While we currently have no evidence of impact to customer information stored outside of GitHub’s internal repositories (such as our customers’ […]
ISC Stormcast For Wednesday, May 20th, 2026 https://isc.sans.edu/podcastdetail/9938, (Wed, May 20th)
Post Content
Microsoft disrupts malware code-signing service used by ransomware gangs
Microsoft has disrupted the infrastructure powering the largest malware code-signing service used to help ransomware groups and other cybercriminals make malicious programs harder to detect on Windows. The threat actors behind the service used stolen identities and impersonated legitimate organizations to obtain more than 1,000 code-signing certificates. Microsoft seized the group’s website, signspace[.]cloud, revoked the […]
2026088975901 Trevor Uhls CRD 6872250 AWC lp.pdf
2026088975901 Trevor Uhls CRD 6872250 AWC lp.pdf Anonymous (not verified) Tue, 05/19/2026 – 18:25 Case ID 2026088975901 Document Number 3aafed35 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals Trevor Uhls Action Date Tue, 05/19/2026 – 12:00 Related Content Off Attachment 2026088975901 Trevor Uhls CRD 6872250 AWC lp.pdf Individual CRD 6872250
2024084295503 Marcelo Javier Poliak CRD 2465622.pdf
2024084295503 Marcelo Javier Poliak CRD 2465622.pdf Anonymous (not verified) Tue, 05/19/2026 – 18:25 Case ID 2024084295503 Document Number 8df56f27 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals Marcelo Javier Poliak Action Date Tue, 05/19/2026 – 12:00 Related Content Off Attachment 2024084295503 Marcelo Javier Poliak CRD 2465622.pdf Individual CRD 2465622
2023077098201 Dinosaur Financial Group, LLC CRD 104446.pdf
2023077098201 Dinosaur Financial Group, LLC CRD 104446.pdf Anonymous (not verified) Tue, 05/19/2026 – 18:20 Case ID 2023077098201 Document Number 555aeaaa Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Tue, 05/19/2026 – 12:00 Related Content Off Attachment 2023077098201 Dinosaur Financial Group, LLC CRD 104446.pdf
25-00228.pdf
25-00228.pdf Anonymous (not verified) Tue, 05/19/2026 – 17:20 Case ID 25-00228 Forum FINRA Document Type Award Claimants Kingswood Capital Partners, LLC Respondents Douglas Nelson Neutrals Barbara M. Zak Katharine Reed Coleman Ashley Meadows Hearing Site Los Angeles, CA Award Document 25-00228.pdf Documentum DocID 7a78338d Award Date Official Tue, 05/19/2026 – 12:00 Related Content Off Claimant […]
25-01773.pdf
25-01773.pdf Anonymous (not verified) Tue, 05/19/2026 – 17:20 Case ID 25-01773 Forum FINRA Document Type Award Claimants Joseph White Individually and on Behalf of his IRA Respondents David Lerner Associates, Inc. Neutrals Edward W. Morris Anthony Gagliolo Michael Perna Hearing Site Jersey City, NJ Award Document 25-01773.pdf Documentum DocID 69c60d54 Award Date Official Mon, 05/18/2026 […]
Contractor’s public GitHub account exposed GovCloud and CISA credentials
Until a few days ago, a publicly-accessible GitHub repository exposed credentials for both US government AWS accounts and internal Cybersecurity and Infrastructure Security Agency (CISA) systems. That’s according to cybersecurity reporter Brian Krebs, who first broke the news over the weekend, acting on a tip from researcher Guillaume Valadon at GitGuardian. Valadon confirmed the information […]
AntV data visualization tool the latest to be hit by ongoing npm supply chain attacks
The world’s largest open-source registry, node package manager (npm), has been hit by another fast-moving malware attack, this time targeting the widely-used AntV enterprise data visualization tool. Unlike last week’s high-profile npm attack on TanStack, which exploited a complex GitHub Actions cache poisoning weakness, the latest incident early on May 19 took the more conventional […]
La soberanía digital como estrategia: así construye Amnistía Internacional España su modelo tecnológico
La transformación digital de una organización ya no se mide únicamente en productividad, automatización o incorporación de nuevas herramientas. En entidades sin ánimo de lucro como Amnistía Internacional España, la tecnología también se ha convertido en una cuestión de independencia, privacidad y capacidad de actuación. Desde hace más de una década, la división española de […]
The friction tax: What hidden IT dysfunction really costs a business
Most IT dysfunction is unreported by employees through the ticketing system. Unless the issue stops them in their tracks, employees often just adapt, waiting out a sluggish VPN, restarting a crashing app, powering through slow IT performance, or reaching for a personal device when the corporate one fails them. But this kind of IT irritation […]
Launch time! Turning early momentum into real growth
Launching a new product is hard enough, but the work doesn’t stop once a product is officially on the market. Often, a new and more complex challenge begins: Turning early excitement into sustained growth. Launches are deceptive. They create visibility, energy and, if you’re lucky, a surge of initial demand. But they don’t guarantee long-term […]
AI upends key pillars of project management
AI offers the potential for operational efficiencies, reductions in human error, a solution for employee attrition, and split-second analytical recommendations, but the reality is that no one — in the business, outside the business, or even CIOs themselves — knows whatto expect from AI. And still, businesses are aggressively pursuing it, in many cases in […]
CIO코리아·IBM, “AI 성패 좌우하는 건 데이터”…AI 레디 데이터 전략 제시
이번 행사는 ‘데이터로 만드는 AI 성과 격차와 리더십의 선택’을 주제로 진행됐다. IBM과 컨플루언트는 AI 시대 기업 경쟁력의 핵심으로 ‘AI 레디(Ready) 데이터’와 실시간 데이터 활용 체계를 제시하며, 단순히 생성형 AI 모델을 도입하는 것을 넘어 기업 내부 데이터를 얼마나 신뢰성 있게 연결·가공·활용할 수 있느냐가 실제 AI 성과를 좌우한다고 강조했다. 첫 번째 세션에서는 한국IBM의 CTO & 테크 세일즈 […]
How IT teams are putting AI agents to work
I’ve spent a lot of time inside enterprise AI deployments, and one thing that has become clear is that IT departments are leading the charge. Of course, enterprises are starting to consolidate licenses for AI platforms within the IT team budget. But inwardly, while other parts of the enterprise are still debating the use case […]
7 signs your data isn’t ready for AI
AI is useless without access to abundant and accurate data. Unfortunately, many enterprises are saddled with data that’s stored in a way that’s unusable for AI applications. AI data incompatibility is widespread, even among organizations actively investing in AI, says Daren Campbell, tax technology and transformation leader at business advisory firm EY Americas. “Adoption of […]
The next digital divide: AI owners vs. AI renters
For the past two years, the conversation around artificial intelligence has largely centered on adoption. Which organizations are using AI tools? Which companies are integrating generative AI into their workflows? Which teams are experimenting with automation and productivity gains? But beneath this wave of adoption lies a more important structural shift; one that will likely […]
Solving healthcare’s unique security challenges: The role of zero trust and SASE
With clinicians and staff accessing patient data from dozens of locations and devices, healthcare’s attack surface has never been larger. The cost of getting security wrong — $9.77 million per breach on average, according to CrowdStrike’s “Healthcare Cybersecurity in 2025: Staying Ahead of Emerging Threats” report — is the highest of any industry. And the […]
Agentic AI won’t scale on ambition. It will scale on infrastructure.
Agentic AI is moving into the enterprise faster than the infrastructure beneath it can keep up. In Cisco and Omdia’s survey of 650 executives, 87% said it’s reshaping strategic priorities, yet 62% said they’re struggling to secure networks, manage agent identities, and protect data in motion. For CIOs, that’s the job now: build the infrastructure, security, […]
Trapdoor Android Ad Fraud Scheme Hit 659 Million Daily Bid Requests Using 455 Apps
Cybersecurity researchers have disclosed details of a new ad fraud and malvertising operation dubbed Trapdoor targeting Android device users. The activity, per HUMAN’s Satori Threat Intelligence and Research Team, encompassed 455 malicious Android apps and 183 threat actor-owned command-and-control (C2) domains, turning the infrastructure into a pipeline for multi-stage fraud. “Users
GitHub scales back bug bounties, reminds users security is their responsibility too
Faced with the growing volume of submission to its bug bounty program, GitHub is replacing cash bounties with swag rewards for reports with low security impact — and asking researchers to stop submitting reports that are low quality or about things that aren’t its fault. The cloud-based code repository platform has seen a sharp increase […]
DirtyDecrypt PoC Released for Linux Kernel CVE-2026-31635 LPE Vulnerability
Proof-of-concept (PoC) exploit code has now been released for a recently patched security flaw in the Linux kernel that could allow for local privilege escalation (LPE). Dubbed DirtyDecrypt (aka DirtyCBC), the vulnerability was discovered and reported by the Zellic and V12 security team on May 9, 2026, only to be informed by the maintainers that […]
Internet Explorer may be dead, but its ghost still runs malware
Microsoft’s aging “mshta.exe” utility, a leftover component from Internet Explorer, is still being actively abused in modern malware campaigns years after the browser itself was retired. According to new research from Bitdefender, attackers continue to abuse Microsoft HTML Application Host (MSHTA), a built-in Windows utility capable of executing VBScript and JavaScript from local or remote […]
ZKTeco CCTV Cameras
View CSAF Summary Successful exploitation of this vulnerability could result in information disclosure, including capture of camera account credentials. The following versions of ZKTeco CCTV Cameras are affected: SSC335-GC2063-Face-0b77 Solution CVSS Vendor Equipment Vulnerabilities v3 9.1 ZKTeco ZKTeco CCTV Cameras Authentication Bypass Using an Alternate Path or Channel Background Critical Infrastructure Sectors: Commercial Facilities Countries/Areas […]
ScadaBR
View CSAF Summary Successful exploitation of these vulnerabilities could allow an attacker to perform unauthenticated remote code execution. The following versions of ScadaBR are affected: ScadaBR 1.2.0 (CVE-2026-8602, CVE-2026-8603, CVE-2026-8604, CVE-2026-8605) CVSS Vendor Equipment Vulnerabilities v3 9.1 ScadaBR ScadaBR Missing Authentication for Critical Function, Improper Neutralization of Special Elements used in an OS Command (‘OS […]
ABB CoreSense HM and CoreSense M10
View CSAF Summary An update is available that resolves vulnerability in the product versions listed as affected in this advisory. A path traversal vulnerability in these products can allow unauthenticated users to gain access to restricted directories. Exploiting this vulnerability can lead to complete system compromise and exposure of sensitive information. The following versions of […]
Siemens RUGGEDCOM APE1808 Devices
View CSAF Summary A buffer overflow vulnerability in the User-ID™ Authentication Portal (aka Captive Portal) service of Palo Alto Networks PAN-OS software allows an unauthenticated attacker to execute arbitrary code with root privileges on the PA-Series and VM-Series firewalls by sending specially crafted packets. Siemens is preparing fix versions and recommends countermeasures for products where […]
Kieback & Peter DDC Building Controllers
View CSAF Summary Successful exploitation of this vulnerability could allow an attacker to take control of the victim’s browser. The following versions of Kieback & Peter DDC Building Controllers are affected: DDC4002 <=1.12.14 (CVE-2026-4293) DDC4100 <=1.12.14 (CVE-2026-4293) DDC4200 <=1.12.14 (CVE-2026-4293) DDC4200-L <=1.12.14 (CVE-2026-4293) DDC4400 <=1.12.14 (CVE-2026-4293) DDC4002e <=1.23.4 (CVE-2026-4293) DDC4200e <=1.23.4 (CVE-2026-4293) DDC4400e <=1.23.4 (CVE-2026-4293) […]
The New Phishing Click: How OAuth Consent Bypasses MFA
In February 2026, a phishing-as-a-service (PhaaS) platform called EvilTokens went live. Within five weeks, it had compromised more than 340 Microsoft 365 organizations across five countries. The targets of the platform received a message asking them to enter a short code at microsoft.com/devicelogin and complete their normal MFA challenge, then walked away believing they had […]
7-Eleven Data Breach Confirmed After ShinyHunters Ransom Demand
The hackers claimed to have stolen more than 600,000 Salesforce records, including personal information and corporate data. The post 7-Eleven Data Breach Confirmed After ShinyHunters Ransom Demand appeared first on SecurityWeek.
‘Claw Chain’ OpenClaw Flaws Allow Sandbox Escape, Backdoor Delivery
Four vulnerabilities in OpenClaw can be chained together to steal credentials, escape the sandbox, and plant persistent backdoors. The post ‘Claw Chain’ OpenClaw Flaws Allow Sandbox Escape, Backdoor Delivery appeared first on SecurityWeek.
Millions Impacted Across Several US Healthcare Data Breaches
Several healthcare data breaches impacting hundreds of thousands and even millions were added to the HHS tracker. The post Millions Impacted Across Several US Healthcare Data Breaches appeared first on SecurityWeek.
Critical Vulnerability Exposes Industrial Robot Fleets to Hacking
The vulnerability, CVE-2026-8153, affects Universal Robots PolyScope 5 and it can be exploited for OS command injection. The post Critical Vulnerability Exposes Industrial Robot Fleets to Hacking appeared first on SecurityWeek.
PoC Released for DirtyDecrypt Linux Kernel Vulnerability
Patched in April, the underlying vulnerability allows local attackers to elevate their privileges to root. The post PoC Released for DirtyDecrypt Linux Kernel Vulnerability appeared first on SecurityWeek.
201 Arrested in Crackdown on Cybercrime in Middle East, North Africa
The 13-country effort, named Operation Ramz, targeted cyber threats in the Middle East and North Africa region. The post 201 Arrested in Crackdown on Cybercrime in Middle East, North Africa appeared first on SecurityWeek.
Drupal to Release Urgent Core Security Updates on May 20, Sites Told to Prepare
Drupal has issued an alert stating that it intends to release a “core security release” for all supported branches on May 20, 2026, from 5-9 p.m. UTC. “The Drupal Security Team urges you to reserve time for core updates at that time because exploits might be developed within hours or days,” the maintainers of the […]
SEPPMail Secure E-Mail Gateway Vulnerabilities Enable RCE and Mail Traffic Access
Critical security vulnerabilities have been disclosed in SEPPMail Secure E-Mail Gateway, an enterprise-grade email security solution, that could be exploited to achieve remote code execution and enable an attacker to read arbitrary mails from the virtual appliance. “These vulnerabilities could have been exploited to read all mail traffic or as an entry vector into the […]
7 tips for accelerating cyber incident recovery
Despite strong and redundant defenses, enterprises remain vulnerable to a wide range of cyberattacks. And because attacks — and cyber incidents — are inevitable, developing an incident response and recovery process that’s quick, comprehensive, and coordinated is essential. Expediting incident recovery time is critical because the longer an outage persists, the more costs, risk, and business […]
Alliance du Commerce
Alliance du Commerce ipayotfr Tue, 19/05/2026 – 09:51 12 February 2026 Code owners Alliance du Commerce Processing of consumers personal data by retailers acting as controllers France Type Code for Controllers/Processors subject to GDPR Scope National Monitoring Body AFNOR Certification (external monitoring body) Text of the Code of Conduct (FR) 1.8MB Download file 1 CNIL’s […]
Compromised Nx Console 18.95.0 Targeted VS Code Developers with Credential Stealer
Cybersecurity researchers have flagged a compromised version of the Nx Console extension that was published to the Microsoft Visual Studio Code (VS Code) Marketplace. The extension in question is rwl.angular-console (version 18.95.0), a popular user interface and plugin for code editors like VS Code, Cursor, and JetBrains. The VS Code extension has more than 2.2 […]
Popular GitHub Action Tags Redirected to Imposter Commit to Steal CI/CD Credentials
In yet another software supply chain attack, threat actors have compromised the popular GitHub Actions workflow, actions-cool/issues-helper, to run malicious code that harvests sensitive credentials and exfiltrates them to an attacker-controlled server. “Every existing tag in the repository has been moved to point to an imposter commit that does not appear in the action’s normal […]
Mini Shai-Hulud Pushes Malicious AntV npm Packages via Compromised Maintainer Account
Cybersecurity researchers have discovered a fresh software supply chain attack campaign that has compromised various npm packages associated with the @antv ecosystem as part of the ongoing Mini Shai-Hulud attack wave. “The attack affects packages tied to the npm maintainer account atool, including echarts-for-react, a widely used React wrapper for Apache ECharts with roughly 1.1 […]

SIEM-Kaufratgeber
Die kontextuellen Daten, die SIEM-Lösungen liefern, sind eine grundlegende Komponente moderner Security-Stacks. PeopleImages.com – Yuri A | shutterstock.com Protokoll-Daten zu auditieren, zu überprüfen und zu managen, ist alles andere als eine glamouröse Aufgabe – aber ein entscheidender Aspekt, um ein sicheres Unternehmensnetzwerk aufzubauen. Schließlich schaffen Event Logs oft eine sekundäre Angriffsfläche für Cyberkriminelle, die damit […]
Schwachstellen managen: Die besten Vulnerability-Management-Tools
Schwachstellen zu managen, muss keine Schwerstarbeit sein. Wenn Sie die richtigen Tools einsetzen. Das sind die besten in Sachen Vulnerability Management. Foto: eamesBot – shutterstock.com Nicht nur das Vulnerability Management hat sich im Laufe der Jahre erheblich verändert, sondern auch die Systeme, auf denen Schwachstellen identifiziert und gepatcht werden müssen. Systeme für das Schwachstellen-Management fokussieren […]
Security-Infotainment: Die besten Hacker-Dokus
Sie fühlen sich leer ohne Security-Dashboard? Diese Dokumentationen überbrücken den Schmerz bis zum nächsten Arbeitstag. Foto: Gorodenkoff – shutterstock.com Wenn Sie in Ihrer Profession als Sicherheitsentscheider voll aufgehen, brauchen Sie möglicherweise auch zwischen den Arbeitstagen ihre tägliche Dosis Cybersecurity. Falls Ihnen die zahlreichen Annäherungen Hollywoods an das Thema viel zu weit von der Realität entfernt […]
ISC Stormcast For Tuesday, May 19th, 2026 https://isc.sans.edu/podcastdetail/9936, (Tue, May 19th)
Post Content
25-00520.pdf
25-00520.pdf Anonymous (not verified) Mon, 05/18/2026 – 19:15 Case ID 25-00520 Forum FINRA Document Type Award Claimants Morgan Stanley Morgan Stanley Smith Barney Financing LL Respondents Carlos Eduardo Duarte Ribeiro Filho Hearing Site New York, NY Award Document 25-00520.pdf Documentum DocID 0d744230 Related Content Off Claimant Representatives Alan Steven Brodherson Respondent Representatives Carlos Eduardo Duarte […]
24-01281.pdf
24-01281.pdf Anonymous (not verified) Mon, 05/18/2026 – 19:10 Case ID 24-01281 Forum FINRA Document Type Award Claimants Ameriprise Financial Services, LLC. Respondents Justin Ranger Hearing Site New Orleans, LA Award Document 24-01281.pdf Documentum DocID 657f6ac8 Related Content Off Claimant Representatives Scott A. LaPorta Respondent Representatives Mark L. Barbre
24-00877.pdf
24-00877.pdf Anonymous (not verified) Mon, 05/18/2026 – 19:10 Case ID 24-00877 Forum FINRA Document Type Award Claimants Justin Ranger Respondents Ameriprise Financial Services, LLC. Neutrals Allan R. Lazor Ralph Hamilton Schofield Stacey Elizabeth LaFleur Hearing Site New Orleans, LA Award Document 24-00877.pdf Documentum DocID 8086f451 Award Date Official Mon, 05/18/2026 – 12:00 Related Content Off […]
24-01793.pdf
24-01793.pdf Anonymous (not verified) Mon, 05/18/2026 – 19:10 Case ID 24-01793 Forum FINRA Document Type Award Claimants Louis Crispi Respondents Charles Schwab & Co., Inc. Neutrals Denise L. Quarles Kenneth Paul Williams Brian John Gallagher Hearing Site New York, NY Award Document 24-01793.pdf Documentum DocID 0c5b2943 Award Date Official Mon, 05/18/2026 – 12:00 Related Content […]
CISA Admin Leaked AWS GovCloud Keys on Github
Until this past weekend, a contractor for the Cybersecurity & Infrastructure Security Agency (CISA) maintained a public GitHub repository that exposed credentials to several highly privileged AWS GovCloud accounts and a large number of internal CISA systems. Security experts said the public archive included files detailing how CISA builds, tests and deploys software internally, and […]
2023077037801 World Investments LLC CRD 20626 AWC lp.pdf
2023077037801 World Investments LLC CRD 20626 AWC lp.pdf Anonymous (not verified) Mon, 05/18/2026 – 16:40 Case ID 2023077037801 Document Number b59c8d5b Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Mon, 05/18/2026 – 12:00 Related Content Off Attachment 2023077037801 World Investments LLC CRD 20626 AWC lp.pdf
Microsoft May security patch fails for some due to boot partition size glitch
“Something didn’t go as planned. Undoing changes.” That’s all the clue some Windows 11 users will get when Microsoft’s May Security Update fails to install because of insufficient free space on the EFI System Partition (ESP), leaving their systems unprotected by the dozens of patches it contained. This issue affects devices with limited free space […]
TeamPCP Supply Chain Campaign: Activity Through 2026-05-17, (Mon, May 18th)
Since the last update, the TeamPCP supply chain campaign produced its loudest stretch since the March Trivy disclosure: an officially confirmed Checkmarx Jenkins plugin compromise and a new self-spreading Mini Shai-Hulud worm across npm and PyPI.
The AI data governance gap that keeps getting worse
Every enterprise I talk to right now is somewhere in the middle of building AI into their products or operations. Internal copilots, fraud detection, customer service bots. The ambition is real and the pace is aggressive. But here is what keeps coming up in my conversations, and it is not a technical issue. It is […]
The AI deployment gap enterprises can’t afford to ignore
Enterprises are moving quickly to explore artificial intelligence. New pilots are being launched across functions, from customer service chatbots to predictive analytics and automated workflows. Early results are often encouraging. Models perform well, demonstrations impress stakeholders, and momentum builds around the promise of AI-led transformation. Yet a more difficult reality is emerging. Most AI initiatives […]
When AI moves to production, infrastructure becomes strategy
Artificial intelligence is entering a new phase inside the enterprise. What began as isolated pilots is now becoming part of day-to-day operations across customer service, decision-making, and automation. As this shift happens, organizations are starting to realise that AI is not just another workload to run on existing cloud environments. It is changing the role […]
The real AI bottleneck isn’t what you think
At HumanX in San Francisco earlier this year, Andrew Ng made a point that reframed how many in the room were thinking about enterprise AI. Ng built the AI infrastructure at Google Brain and Baidu before founding DeepLearning.AI and Coursera, which now serves roughly 148 million learners globally. He is someone whose read on where […]
What is a data architect? Skills, salaries, and how to become a data framework master
Data architect role Data architects are senior visionaries who translate business requirements into technology requirements, and define data standards and principles, often in support of data or digital transformations. The data architect is responsible for visualizing and designing an organization’s enterprise data management framework, which describes the processes used to plan, specify, enable, create, acquire, […]
CEOs’ top priorities for IT leaders today
For nearly every CIO, implementing AI is their No. 1 task — that’s the directive they’re getting from the corner office. CEOs have pegged researching and implementing AI at the top of their priority lists for their CIOs, according to CIO.com’s 2026 State of the CIO Survey. That finding mirrors the results in multiple other […]
Sovereign AI: Why CIOs can no longer outsource control
Artificial intelligence is being deployed faster than most organisations can establish clear ownership, governance, and control over how it operates. Yet, for all the attention on models and use cases, one question often remains underexamined. Who controls the intelligence that enterprises are building their future on? For many organisations, the answer is uncomfortable. AI systems […]
AI is rewriting the software development playbook
A few years ago, AI in software development meant autocomplete that occasionally guessed your variable name. Today, it means something closer to having an extra engineer sitting next to you — one who never sleeps, never complains about context switching and has read more code than any human alive. In fact, you can have a […]
From tools to workflows: Rethinking the SDLC for the AI age
AI is rewriting the way software is built. For decades, software development followed a predictable sequence of requirements, design, build, test, deploy. This model was designed for a world where coding and testing was expensive, and feedback came late. With AI, code can be generated in seconds, testing is continuous and feedback is real time. […]
¿Eres el próximo CIO? El programa que busca a los nuevos líderes tecnológicos de España
La figura del CIO ha cambiado radicalmente. Hace tiempo que quedó atrás el perfil centrado exclusivamente en la gestión de infraestructuras o sistemas: hoy los líderes tecnológicos están llamados a impulsar la transformación empresarial, fortalecer la resiliencia en ciberseguridad y convertir el potencial de la inteligencia artificial en resultados tangibles para el negocio. Sin embargo, […]
INTERPOL Operation Ramz Disrupts MENA Cybercrime Networks with 201 Arrests
INTERPOL has coordinated a first-of-its-kind cybercrime crackdown across the Middle East and North Africa (MENA) that led to 201 arrests and the identification of an additional 382 suspects. The initiative involved the efforts of 13 countries from the region between October 2025 and February 2026, aiming to investigate and neutralize malicious infrastructure, arrest perpetrators behind […]
AI cyberattackers are getting better faster
The ability of AI models to perform end-to-end, multi-stage penetration tests that match the capabilities of humans undertaking the same tasks has improved dramatically in recent months, according to new benchmarks published by the UK government’s AI Security Institute (AISI). In November 2025, the difficulty of cyber tasks the best models could complete was doubling […]
Chairman Cassidy, Tuberville Seek Answers on Canvas Cybersecurity Incident, Calls for More Safeguards to Protect Students
U.S. Senators Bill Cassidy, M.D. (R-LA), Chairman of the U.S. Senate Health, Education, Labor, and Pensions (HELP) Committee, and Tommy Tuberville (R-AL) raised concerns about the recent cybersecurity incident on Instructure, threatening the data of 275 million students, families, and teachers worldwide. The incident shut down Instructure’s learning management system, Canvas, the most popular system… […]
Congress Learns of Prescription Data Hack Months Later
Ben Smith reports: Lawmakers are only now learning that hackers breached a congressional medical contractor more than two months ago. RXNT, a healthcare software company used by the Office of the Attending Physician (OAP) to manage prescription services for Congress, was breached on March 1 and March 3. Hackers obtained copies of patient data stored within the platform. The… […]
Extant Aerospace Data Breach Exposed SSNs for More Than 3,000 People
Claim Depot reports: Extant Aerospace, a defense and space electronics company based in Melbourne, Florida, disclosed a data breach that affected 3,012 individuals in the United States. The company, legally known as Symetrics Industries LLC, manufactures and supplies complex electronic assemblies for the Department of Defense and international customers for both military and commercial use. On… […]
⚡ Weekly Recap: Exchange 0-Day, npm Worm, Fake AI Repo, Cisco Exploit and More
Monday opens with a trust problem. A mail server flaw is under active use. A network control system was targeted. Trusted packages were poisoned. A fake model page pushed a stealer. Then came the familiar ransom claim: the data was returned and deleted. The pattern is clear. One weak dependency can leak keys. One leaked […]
How to Reduce Phishing Exposure Before It Turns into Business Disruption
What happens when a phishing email looks clean enough to pass through security, but dangerous enough to expose the business after one click? That is the gap many SOCs still struggle with: the attacks that leave teams unsure what was exposed, who else was targeted, and how far the risk has spread. Early phishing detection […]
New image-based prompt injection attack targets multimodal AI models
Security researchers have developed a new image-based prompt injection attack that can manipulate how multimodal AI systems interpret user instructions without modifying the original text prompt, potentially expanding security risks for AI agents and vision-language systems. In a research paper published this week, researchers from Xidian University described a technique called “CrossMPI,” which uses nearly […]
‘Patched’ Windows bug resurfaces 6 years later as working SYSTEM-level exploit
An old elevation-of-privilege (EoV) vulnerability affecting the Cloud Filter driver “cldflt.sys” in Windows has come back to haunt Microsoft, as researchers claim it is still exploitable six years after it was supposedly patched. The flaw, originally reported to Microsoft by Google Project Zero researcher James Forshaw in September 2020, was recently picked up by Nightmare […]
Developer Workstations Are Now Part of the Software Supply Chain
Supply chain attackers are not only trying to slip malicious code into trusted software. They are trying to steal the access that makes trusted software possible. Recently, three separate campaigns hit npm, PyPI, and Docker Hub in a 48-hour window, and all three targeted secrets from developer environments and CI/CD pipelines, including API keys, cloud […]
Meeting Data Protection Working Group, Council
Meeting Data Protection Working Group, Council icolonnm Mon, 18/05/2026 – 13:21 12 June 2026 Chair, Anu TalusBrussels
Meeting Committee on Civil Liberties, Justice and Home Affairs (LIBE), European Parliament
Meeting Committee on Civil Liberties, Justice and Home Affairs (LIBE), European Parliament icolonnm Mon, 18/05/2026 – 13:20 8 June 2026 Chair, Anu TalusBrussels
Hackers Earn $1.3 Million at Pwn2Own Berlin 2026
Participants demonstrated exploits for Windows, Linux, VMware, Nvidia, and AI products. The post Hackers Earn $1.3 Million at Pwn2Own Berlin 2026 appeared first on SecurityWeek.
Exploitation of Critical NGINX Vulnerability Begins
The flaw leads to denial-of-service on default configurations and to remote code execution if ASLR is disabled. The post Exploitation of Critical NGINX Vulnerability Begins appeared first on SecurityWeek.
Grafana Confirms Breach After Hackers Claim They Stole Data
Grafana appears to have been targeted by Coinbase Cartel, a cybercrime group linked to ShinyHunters, Scattered Spider, and Lapsus$. The post Grafana Confirms Breach After Hackers Claim They Stole Data appeared first on SecurityWeek.
First Shai-Hulud Worm Clones Emerge
At least one threat actor has adopted the recently released malware source code in attacks against NPM developers. The post First Shai-Hulud Worm Clones Emerge appeared first on SecurityWeek.
Researcher Drops MiniPlasma Windows Exploit for Unpatched 2020 CVE
The researcher dropped the MiniPlasma exploit that uses the original proof-of-concept (PoC) code targeting the bug. The post Researcher Drops MiniPlasma Windows Exploit for Unpatched 2020 CVE appeared first on SecurityWeek.
Ivanti, Fortinet, SAP, VMware, n8n Patch RCE, SQL Injection, Privilege Escalation Flaws
Ivanti, Fortinet, n8n, SAP, and VMware have released security fixes for various vulnerabilities that could be exploited by bad actors to bypass authentication and execute arbitrary code. Topping the list is a critical flaw impacting Ivanti Xtraction (CVE-2026-8043, CVSS score: 9.6) that could be exploited to achieve information disclosure or client-side attacks. “External control of […]
AI coding is fueling a secrets-sprawl crisis few CISOs are containing
When Matt Schlicht built Moltbook, the social network where AI agents talk to one another, he didn’t write the code himself. He “just had a vision,” and vibe-coded it. The social network launched on Jan. 28, 2026, and within days, security researchers started to see serious security flaws. Experts at cloud security company Wiz and, […]
Why the best security investment a board can make in 2026 isn’t another tool
There is a conversation that happens in boardrooms every quarter that security leaders will recognize. The CISO presents the threat landscape. The board asks what the company needs. The answer, almost always, is another tool. Another platform, another module, another vendor to close the latest gap. The budget gets approved. The tool gets deployed. And […]
MiniPlasma Windows 0-Day Enables SYSTEM Privilege Escalation on Fully Patched Systems
Chaotic Eclipse, the security researcher behind the recently disclosed Windows flaws, YellowKey and GreenPlasma, has released a proof-of-concept (PoC) for a Windows privilege escalation zero-day flaw that grants attackers SYSTEM privileges on fully patched Windows systems. Codenamed MiniPlasma, the vulnerability impacts “cldflt.sys,” which refers to the Windows Cloud Files Mini Filter Driver,
Four Malicious npm Packages Deliver Infostealers and Phantom Bot DDoS Malware
Cybersecurity researchers have discovered four new npm packages containing information-stealing malware, one of which is a clone of the Shai-Hulud worm open-sourced by TeamPCP. The list of identified packages is below – chalk-tempalte (825 Downloads) @deadcode09284814/axios-util (284 Downloads) axois-utils (963 Downloads) color-style-utils (934 Downloads) “One of the packages (chalk-tempalte)
Pre-Stuxnet Fast16 Malware Tampered with Nuclear Weapons Simulations
A new analysis of the Lua-based fast16 malware has confirmed that it was a cyber sabotage tool designed to tamper with nuclear weapons testing simulations. According to Broadcom-owned Symantec and Carbon Black teams, the pre-Stuxnet tool was engineered to corrupt uranium-compression simulations that are central to nuclear weapon design. “Fast16’s hook engine is selectively interested […]
NGINX CVE-2026-42945 Exploited in the Wild, Causing Worker Crashes and Possible RCE
A newly disclosed security flaw impacting NGINX Plus and NGINX Open has come under active exploitation in the wild, days after its public disclosure, according to VulnCheck. The vulnerability, tracked as CVE-2026-42945 (CVSS score: 9.2), is a heap buffer overflow in ngx_http_rewrite_module affecting NGINX versions 0.6.27 through 1.30.0. According to AI-native security company depthfirst, the
Grafana GitHub Token Breach Led to Codebase Download and Extortion Attempt
Grafana has disclosed that an “unauthorized party” obtained a token that granted them the ability to access the company’s GitHub environment and download its codebase. “Our investigation has determined that no customer data or personal information was accessed during this incident, and we have found no evidence of impact to customer systems or operations,” Grafana […]
Another detail emerges about Instructure’s agreement with ShinyHunters; Debate continues about whether to pay
Media outlets have been understandably eager to learn whether Instructure paid ShinyHunters after the latter attacked them for a second time on May 7. Considering that they pledged to be more transparent, DataBreaches doesn’t fully understand why Instructure wasn’t more forthright about the payment issue in its update, unless they were trying to avoid encouraging… […]
Funnel Builder Flaw Under Active Exploitation Enables WooCommerce Checkout Skimming
A critical security vulnerability impacting the Funnel Builder plugin for WordPress has come under active exploitation in the wild to inject malicious JavaScript code into WooCommerce checkout pages with the goal of stealing payment data. Details of the activity were published by Sansec this week. The vulnerability currently does not have an official CVE identifier. […]
Welcome to BlackFile: Inside a Vishing Extortion Operation
Google’s Threat Intelligence Group writes: Google Threat Intelligence Group (GTIG) has continued to track an expansive extortion campaign by UNC6671, a threat actor operating under the “BlackFile” brand, that targets organizations via sophisticated voice phishing (vishing) and single sign-on (SSO) compromise. By leveraging adversary-in-the-middle (AiTM) techniques to bypass traditional perimeter defenses and multi-factor authentication (MFA),… […]
Michigan Nurse Convicted in $1.6M Medicare Fraud Scheme Using Stolen Patient Records
Scott McClallen reports: A federal jury in the Eastern District of Michigan convicted a Michigan nurse and home health care agency owner yesterday for operating a $1.6 million scheme to defraud Medicare. Court documents say that Ruby Scott, 55, of Farmington Hills, Michigan, owned and operated Delta Home Health Care LLC. From 2018 through 2021,… […]
Illuminate wins another round in court, but it may not all be over
The Supreme Court of California has ruled in J.M. v. Illuminate Education, Inc., a case closely watched by those concerned about holding edtech vendors liable in the event of a data breach. As background on the case: In December 2021, Illuminate suffered a data breach that affected 1.7 million students in New York, 434,000 students… […]
American Lending Center Data Breach Affects 123,000 Individuals
The non-bank lender discovered a ransomware attack nearly one year ago, but only recently completed its investigation. The post American Lending Center Data Breach Affects 123,000 Individuals appeared first on SecurityWeek.
Microsoft Warns of Exchange Server Zero-Day Exploited in the Wild
Microsoft has shared mitigations for CVE-2026-42897 until a permanent patch can be released for affected Exchange Server versions. The post Microsoft Warns of Exchange Server Zero-Day Exploited in the Wild appeared first on SecurityWeek.
In Other News: Big Tech vs Canada Encryption Bill, Cisco’s Free AI Security Spec, Audi App Flaws
Other noteworthy stories that might have slipped under the radar: Nvidia cloud gaming data breach, Android 17 security upgrades, FBI warning after ShinyHunters hacks Canvas. The post In Other News: Big Tech vs Canada Encryption Bill, Cisco’s Free AI Security Spec, Audi App Flaws appeared first on SecurityWeek.
PoC Code Published for Critical NGINX Vulnerability
Introduced in 2008, the critical-severity security defect was patched this week in NGINX Plus and NGINX open source. The post PoC Code Published for Critical NGINX Vulnerability appeared first on SecurityWeek.
2025086832701 Bryon Edwin Martinsen CRD 1621649 AWC ks.pdf
2025086832701 Bryon Edwin Martinsen CRD 1621649 AWC ks.pdf Anonymous (not verified) Fri, 05/15/2026 – 17:35 Case ID 2025086832701 Document Number 7fa373ea Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals Bryon Edwin Martinsen Action Date Fri, 05/15/2026 – 12:00 Related Content Off Attachment 2025086832701 Bryon Edwin Martinsen CRD 1621649 AWC ks.pdf Individual CRD 1621649
22-02613.pdf
22-02613.pdf Anonymous (not verified) Fri, 05/15/2026 – 17:30 Case ID 22-02613 Forum FINRA Document Type Award Claimants Alexis Stuart Respondents E*Trade Securities LLC Neutrals Mark T Risner Abraham Semaila Kamara Cheryl Lynn Epps Hearing Site Los Angeles, CA Award Document 22-02613.pdf Documentum DocID c332f4f9 Award Date Official Fri, 05/15/2026 – 12:00 Related Content Off Claimant […]
Expired domain leads to supply chain attack on node-ipc npm package
A popular npm package called node-ipc has been compromised, with hackers publishing malicious versions that bundle credential stealing malware. The root cause of the compromise was an expired domain name that attackers managed to register in order to hijack a maintainer’s account. The node-ipc package has had malware added to its code in the past. […]
2025085714301 Jing Li CRD 5127356 AWC lp.pdf
2025085714301 Jing Li CRD 5127356 AWC lp.pdf Anonymous (not verified) Fri, 05/15/2026 – 17:05 Case ID 2025085714301 Document Number c5df33ae Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals Jing Li Action Date Fri, 05/15/2026 – 12:00 Related Content Off Attachment 2025085714301 Jing Li CRD 5127356 AWC lp.pdf Individual CRD 5127356
2025085647701 Brian Thomas CRD 4243411 AWC lmp.pdf
2025085647701 Brian Thomas CRD 4243411 AWC lmp.pdf Anonymous (not verified) Fri, 05/15/2026 – 16:45 Case ID 2025085647701 Document Number 1001646e Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals Brian Thomas Action Date Fri, 05/15/2026 – 12:00 Related Content Off Attachment 2025085647701 Brian Thomas CRD 4243411 AWC lmp.pdf Individual CRD 4243411
Exchange Server zero-day vulnerability can be triggered by opening a malicious email
A newly discovered zero-day vulnerability in Microsoft Exchange Server has experts declaring an emergency and urging CSOs to think about the need to abandon on-premises email solutions. “Because it’s already being exploited in the wild, this isn’t a ‘patch next week situation; it’s a ‘mitigate right now’ emergency,” warned Rob Enderle of the Enderle Group. […]
25-00211.pdf
25-00211.pdf Anonymous (not verified) Fri, 05/15/2026 – 15:00 Case ID 25-00211 Forum FINRA Document Type Award Claimants Mark Rose Respondents Robinhood Securities, LLC Neutrals David L. Ruderman Lorrie E Whitfield Christopher Koller Hearing Site Wilmington, DE Award Document 25-00211.pdf Documentum DocID b3cf7830 Award Date Official Thu, 05/14/2026 – 12:00 Related Content Off Claimant Representatives Mark […]
テックリーダーこそ採用凍結をリードすべき
2026年の経済環境は矛盾に満ちている。不確実性が続く中でも、底堅さが維持されているからだ。国際通貨基金(IMF)は世界経済の安定成長を予測する一方、貿易政策の変化、地政学的不安定、運営コストの高止まりという「分岐する力」が企業を悩ませている。かつて「聖域」とされていたテクノロジー予算も、今や厳しい目で見られるようになった。 ITリーダーにとって採用凍結は通常、停滞期を意味する。しかしエージェンティックAIの時代において、先見性あるCIO/CTOは採用凍結を受け入れるだけでなく、自らリードすべきだ。採用凍結は制約ではなく、「頭数で成長する」モデルから「アーキテクチャの効率で成長する」モデルへの戦略的な転換点になりうる。テックリーダーは「コストセンターの管理」を超えて、AIで増強された企業の設計者になることを取締役会に示すことができるチャンスだ。 採用は止まるのではなく、変わる 「AIは仕事を奪う」という言説は、より現実的な「構造的シフト」の議論に置き換えられつつある。世界経済フォーラム(WEF)の「Future of Jobs Report 2025」によれば、自動化により2030年までに約9200万の職が失われる一方、「拡張された労働力」によって1億7000万の新たな高付加価値ポジションが生まれると予測されている。近年のテック企業のレイオフの波は、AIによる代替というよりも、2020年代前半のデジタル急加速後の「コロナ修正」という側面が強い。求められているのは人数ではなく、別の能力だ。 MITスローンの研究によれば、定型的・反復的な作業への需要は大幅に低下している一方、AIによって強化された分析力や創造力を必要とする「拡張親和型」の役割への需要は急増しているという。労働力は縮小しているのではなく、よりスリムで高出力なエンジンへと進化しているのだ。 採用凍結は戦略的再設計の好機だ 採用が鈍化したとき、生産性への責任はCIOとCTOが担う。「システムを維持する」を超えて、戦略的な再設計を始める時だ。「凍結した人員でどう乗り切るか」ではなく、「AIエージェントをすべてのワークフローに組み込んだとき、既存のチームはどれだけのことができるか」を問うべきだ。 ・ソフトウェアエンジニアリング:Gartnerは2027年までにプロの開発者の70%がAIコーディングアシスタントを活用すると予測している ・サイバーセキュリティ:事後対応型の脅威対応から、自律的に問題を検出・対処するAIセキュリティプラットフォームへの移行 ・インフラ:クラウドコストの自動最適化や自己修復システムなど、複数のAIエージェントが連携して複雑な目標を達成するマルチエージェントシステムの導入 McKinsey Global Instituteのデータによれば、ツールを「後付け」するのではなくワークフロー全体を再設計している「AIハイパフォーマー」企業は、そうでない企業と比べて収益への大きなインパクトを見る確率が約3倍高いという。 AIネイティブな人材の台頭 求められる人材像も変わりつつある。AIを外部ツールではなく思考プロセスの一部として使いこなす「AIネイティブ人材」が注目されている。しかし経済協力開発機構(OECD)の「Skills Outlook 2025」が警告するように、こうしたAIリテラシーを持つ候補者は不足している。 採用凍結中であっても、AIの思考方法を持ち込みレガシーな前提に挑戦できる「文化的触媒」となる人材の採用は続けるべきだ。人員総数が変わらなくても、チームの質は大きく変わる。 自然な圧縮——スリムな企業へ 退職や転職で空いたポジションを、金融・法務・サプライチェーンなどの業界データで学習された特化型言語モデル(DSLM)で対応できるなら補充しない——そうした判断が積み重なることで、組織は自然にスリム化していく。人数は減っても、生産能力は上がる。短期的には、外部採用より現在の人材育成がCIOの最優先事項だ。先進的なリーダーは以下の5つに注力している。 ・AIリテラシープログラム:チャットボットの使い方を超え、AIエージェントとエージェンティックAIへの深い理解 ・自動化優先の業務モデル:新しいプロセスには、人を配置する前に「デフォルトで自動化」を義務付ける ・機能横断型イノベーションチーム:技術的専門知識とドメイン知識を組み合わせてビジネス課題を解決する「タイガーチーム」の創設 ・エージェンティックガバナンス:AIエージェントが企業内で自律的に行動できるためのセキュリティと倫理的なフレームワークの整備 ・業務のデジタルツイン:本番展開前にAIで内部ワークフローをシミュレーション・最適化する MITスローンのEPOCHフレームワークが示すように、共感、存在感、意見、創造性、希望を必要とする人間集約的なタスクは自動化されにくい一方、AIによる拡張の最有力候補でもある。AI時代の経営の根本的な問いはもはや「何人必要か」ではない。「今いる人材をどれだけ強くできるか」だ。 スキル領域別:従来の焦点とAIネイティブな焦点 スキル領域 従来の焦点 AIネイティブな焦点 開発 手動コーディングとロジック設計 プロンプトエンジニアリングとエージェントオーケストレーション データ レポーティングと可視化 異常検知と予測モデリング オペレーション チケット対応 ワークフロー自動化と自己修復システム リーダーシップ タスク配分 判断力・倫理・戦略的方向性 採用は続く——ただし、目的が変わる 採用が永遠に止まるわけではない。だが、その目的は変わる。将来の採用は、AI導入を加速させ、陳腐化したワークフローを刷新できる人材の獲得に絞られる。戦略的に配置されたAIリテラシーの高いエンジニア1人が、部門を鈍化させている「雑務」を自動化することで、従来の採用5人分以上の価値を生み出すこともある。 CIOのリーダーシップが問われる瞬間 歴史を振り返ると、経済的な不確実性は常にリーダーシップを試してきた。地政学的不安とテクノロジーの混乱が重なる今の環境は厳しいが、同時に変革の絶好の条件でもある。 CIO/CTOはもはや単なるインフラの管理者ではなく、AIで増強された組織の設計者だ。採用凍結は制約ではなく、仕事のあり方を根本から再設計するための一時停止だ。この問いにうまく答えた組織が、AI時代の生産性モデルを定義する——そして次の経済サイクルも生き抜く。
グローバルレベルの最先端テクノロジーに触れ、社会実装できる魅力(後編)
——現職としての仕事の魅力、やりがいについてお教えください。 もともと私は、「世の中にはどのような会社があり、何をしているのかを知りたい」という思いから今の会社に入りました。その原点は、現在の仕事にもつながっています。 いまの立場の魅力は、AIをはじめとする最先端技術に触れられることだけではありません。それを実際に企業へ実装し、成果として社会に届けられるという点にあります。単に技術を理解するのではなく、「どう活用し、どう変革につなげるのか」までを考え抜かなければならない。そこに大きなやりがいがあります。 当社は、常に世の中の最先端テクノロジーを把握していくことが求められる立場にあります。しかも、それは国内にとどまりません。グローバルレベルで何が起きているのかを理解し、その動向を踏まえながらビジネスを推進していく必要があります。 グローバルレベルの最先端テクノロジーに触れ、自らその推進に関与し、それを多様な業界や企業、さらには社会全体へと展開していく。そして、その取り組みをグローバルスケールで拡張できる。このダイナミズムこそが、私自身が強い魅力を感じている点です。 技術を知るだけではなく、社会に実装し、変革として結実させる。そのプロセスに携われることが、現職(データ & AIグループ統括)としての最大の醍醐味だと感じています。 いかに「安心して転べるフィールド」を用意するか ——成功するマネジメントにとって必要なことは何でしょうか。 非常に難しいテーマです。アクセンチュア・アドバンスト・AIセンター京都を設置した理由の一つに、京都大学との共同研究があります。技術分野だけでなく、実はリーダーシップについても共同で研究を進めています。 複数の企業にも参画いただきながら、「会社として高いパフォーマンスを上げる」と、「従業員のウェルビーイングを実現する」、この2つを両立するための要素について、分析しています。単に業績を出すだけで、従業員が疲弊してしまっては意味がありません。企業としての成果と、働く人の幸福度をいかに両立させるか——それが重要な問いです。 研究から見えてきたのは、若い人達にどれだけ寄り添い、適切に育成できるかが鍵になるという点でした。若い力を引き出すことができれば、結果として組織のパフォーマンスも高まり、ウェルビーイングの状態も向上していきます。 若い人達は総じてITとの親和性が高く、デジタルネイティブとしての感覚も持っています。だからこそ、その力を積極的に活用すべきです。しかし一方で、ITの世界には「失敗が許されにくい」という特性があります。ミスがそのまま大きな影響につながる可能性があるからです。 ただ、私自身が強く感じているのは、AIも人間も、成長には適切な失敗経験が不可欠だということです。AIの学習においても、成功データだけでなく失敗データが重要です。人間も同様で、失敗からの学びが成長を促します。それにもかかわらず、日本企業、とりわけITの現場では「失敗してはいけない」という空気があります。 だからこそ、リーダーの役割は、挑戦できる環境を整えることだと考えています。すべての失敗を許容するのではなく、「許される範囲の失敗」を設計する。そして、「安心して転べるフィールド」を用意することではないでしょうか。 小さな挑戦を重ね、成功体型と失敗体験、両方から学ぶ。そのプロセスにリーダーが寄り添い、仮に失敗しても「大丈夫だ、次に生かそう」と言えること、若い人達が安心して挑戦できる環境を整えることこそが、組織の持続的な成長を支えるマネジメントの本質ではないかと考えています。 技術革新の波を自社に取り込むためにすべきこととは ——若手のITリーダーへのアドバイスやメッセージをいただけますか。 日本のITリーダーの方々を見ていると、どうしても視点が社内に閉じがちだと感じることがあります。これまでは、いかに基幹システムを安定的に稼働させ続けるかが最優先事項でした。それ自体は極めて重要な役割であり、企業活動を支える基盤でもあります。 しかし今は、状況が大きく変わりつつあります。生成AIをはじめとする技術革新の波は、私たちの状況に関係なく押し寄せています。従来通りのシステムを安定運用するだけでは、企業として競争力を維持できない時代に入りつつあると感じています。 生成AIに加え、今後はフィジカルAIのような新たな領域も現れてきます。仕事のやり方そのものが変われば、当然、それを支えるITシステムも変わらざるを得ません。その変化にどう向き合うのかが、ITリーダーに問われています。 もちろん、既存の基幹システムを止めるわけにはいきません。安定運用と変革推進という、二つの責任を同時に担わなければならない。その中で、外で生まれている新たな技術を、どのように自社に取り込むのかが重要になります。 それを誰かに丸投げするのではなく、自ら理解し、自社にとっての意味を考え抜くことが大事になってきていると感じます。外の世界で何が起きているのかを広く見渡し、それを自社の文脈に引き寄せて吸収していく。そのためには、短期的な社内視点だけでなく、長期的かつ社会的な視点を持つことが重要になるでしょう。 バランスを取るというのは、単に中間を選ぶことではありません。安定と変革、短期と長期、内向きと外向き——それぞれを深く理解したうえで、自らの戦略を明確に打ち出すことです。 今は、ITリーダーにとって極めてダイナミックで刺激的なタイミングです。この変化の波を受け身でやり過ごすのではなく、自ら取り込み、企業の進化につなげていく。その覚悟と構想力が、これからますます重要になると考えています。 AIは「人の仕事を置き換える」のではなく「役割分担」を問い直すもの ——今後の御社の展望と中長期の取り組みを教えてください。 これまで外部環境の変化についてお話ししてきましたが、アクセンチュア自身もまさに同じ変化の中にあります。現在、登場している技術は、コンサルティング業界そのものを根本から変える可能性があります。 将来の正解が明確に見えているわけではありません。しかし、3年後、5年後に社会がどうなっているのかを考えることをやめてはいけないと思っています。私自身、AIセンターで未来予測を行うAIの開発に取り組んでいます。AIの分析結果から学びつつ、AIが十分に捉えきれない部分については、グローバルのリサーチチームが収集した情報を追加したり、新たな調査を行ってAIにインプットしています。そうした相互学習のサイクルを回しながら、AIの力を活用した意思決定を実践し始めています。 この取り組みは、開発したものを、まず社内に展開し、社内実践の結果も踏まえて、お客様にも提供し始めています。AIを適切に活用しながら、社会をより良い方向へ進化させていくことが、中長期的な目標です。 生成AIの議論では、とかく「人の仕事を置き換える」という論点が先行しがちです。しかし私は、単純な置き換えではなく、「どのように役割を再定義するか」が本質だと考えています。AIと人間がそれぞれの強みを発揮できる分担を設計することで、人間の能力をより引き出すことができるはずです。 そのためには、アクセンチュア自身も組織のあり方を変えていかなければならないと感じています。コンサルタントの役割も大きく変わるでしょう。そうした変革を自ら実践しながら、その知見をお客様にもスケールしていくことができたらと考えています。 フィジカルAI×生成AI×責任あるAI——日本の社会課題に挑む ——AIは日本の企業組織や産業にどんなインパクトを与えていくとお考えですか。 現在、世の中に広がっているLLM(大規模言語モデル)は、特にホワイトカラー業務に大きな影響を与えています。グローバルのリサーチチームの調査でも、ドキュメント作業の比率が高い業種ほど影響が大きく、とりわけ金融分野は顕著です。また、ソフトウェアやシステム開発の現場も、すでに生成AIを前提とした仕事の進め方へと移行しつつあります。 影響を受けやすいのは、言語や文書を扱い、かつ付加価値の高い領域です。生成コストも急速に低下しているため、いずれは単価に関係なく、ホワイトカラーの言語タスクは広範にAIが担うようになるでしょう。 さらに今後、フィジカルAIが本格化すれば、AIの影響はホワイトカラーにとどまりません。物理的に人間が働いている領域まで広がり、実空間での作業もAIとロボットが担う世界へと進んでいくと見ています。 そのとき議論の焦点になるのは、「AIにできるかどうか」ではありません。「人間がやるべきか否か」です。仮にAIが実行可能であっても、人間が担うべき役割は残ります。 例えば、社内でAIを活用していて感じるのは、ネガティブなフィードバックはAIに任せた方が、感情論を抜きにして合理的な指摘ができる場合が多くあります。しかし、称賛は人の方が向いています。「今回よく頑張った」とAIボットに言われるのと、直属の上司に言われるのでは、受け取る側の感情は大きく異なります。 また、難しいリスク判断をAIに委ねることは技術的には可能かもしれませんが、最終的に責任を取るのは人間です。エグゼクティブは、自らの意思でリスクを取り、結果に責任を負わなければならないでしょう。 結局のところ、「人間が何を担うのか」を定義することが出発点になります。それによって組織のあり方が決まり、必要なシステムの姿が見えてきます。AIやロボットの役割が明確になれば、CIOはそれを支えるIT環境をどう構築するかを設計することになります。今はまさに、その構想を描く好機だと考えています。 ——今、気になるAIの取り組みは何ですか。 私は「責任あるAI」の重要性について、過去に書籍を出版するほど強い関心を持っていますし、フィジカルAIについても講演を行っています。ただ、あえて技術そのものに焦点が当たりすぎないように気をつけています。重要なのは、技術が社会にどのようなインパクトを与えるかだからです。 LLM(大規模言語モデル)、フィジカルAI、責任あるAI——それぞれが重要ですが、本質はそれらをどう組み合わせ、社会に実装するかにあります。フィジカルAIや生成AIは、日本が直面する社会課題を解決する重要な技術なのです。 少子高齢化が進み、過酷な労働環境で人材確保が難しくなっている領域では、フィジカルAIは極めて有効です。ただし、単純なロボティクスだけでは不十分です。高齢者や多国籍の方々など、多様なバックグラウンドを持つ人々と機械が円滑にインターフェースするためには、生成AIの役割が不可欠になります。 さらに、AIやロボットの活用比率が高まるほど、「責任あるAI」を抜きにした運用は考えられません。倫理、説明責任、ガバナンスといった観点が、技術と不可分になります。 「国産AI」をめぐる議論もありますが、本当に国内で開発すべき領域はどこなのかを冷静に見極める必要があります。過度に内向きになるのも問題ですし、戦略的視点を欠くのも適切ではありません。 最終的に問われるのは、さまざまな技術をどう組み合わせ、どう展開することが社会全体にとって最善なのかという視点です。目先の流行ではなく、中長期で何が適切かを考え続けることが重要です。 正解を即座に導き出すのは容易ではありません。しかし、考え続け、行動し、振り返る。そのサイクルを回すこと自体が、組織と個人の成長につながります。ITリーダーにはぜひ、その思考を止めずに挑み続けてほしいと思います。
전통 IT 사일로 해체…비즈니스 성과 직결 구조로 진화하는 CIO 전략
미 보험 및 복지 서비스 기업 유넘 그룹(Unum Group)의 IT 부서는 제품 관리 중심 구조와 애자일 전달 모델을 기반으로 운영돼 왔다. 이 운영 모델은 비즈니스와 정렬된 ‘투자 역량’을 빠르게 제공함으로써 IT 조직과 기업 모두에 일정한 성과를 안겨줬다. 하지만 2025년 5월 최고정보디지털책임자(CIDO)로 취임한 셸리아 앤더슨은 개선 여지가 있다고 판단했다. 투자 대비 실질적인 성과를 확보할 수 있도록 […]
앤트로픽, 클로드 에이전트 과금 전환…‘무제한 AI’ 시대 막 내리나
‘무제한’에 가까운 AI 코딩 및 에이전트 구독 시대는 사실상 막을 내릴 가능성이 커지고 있다. 앤트로픽은 6월 15일부터 프로그램 방식의 클로드 사용을 기존 채팅 구독 한도에서 분리하고, 별도의 월간 크레딧 시스템을 도입한다. 해당 크레딧은 API 방식 요율로 과금되며, 에이전트 SDK(Agent SDK), 깃허브 액션(GitHub Actions), 오픈클로(OpenClaw) 등 서드파티 프레임워크에서 활용되는 도구에 적용된다고 회사는 블로그를 통해 밝혔다. 자동화·API […]
AI 시대 CIO, ‘생존 시험대’ 올랐다…조직 혁신·AI 역량이 성패 좌우
CIO를 비롯한 IT 리더들은 변화 주도 역량과 AI 준비 조직 구축 능력 등 새로운 요구에 직면하면서, 조직 내에서 생존을 좌우할 중대한 분기점을 맞고 있다. 그동안 IT 리더십 전문가들은 CIO가 기술 전문성과 시스템 운영을 넘어 비즈니스 성과에 집중해야 한다고 강조해왔다. 이러한 요구는 여전히 유효하다. 딜로이트 조사에 따르면 IT 리더의 79%가 ‘비즈니스 성과 창출’을 최우선 과제로 꼽으며, […]
From cautious to scaling: SAP customers span the AI readiness spectrum
SAP spent Sapphire 2026 selling the “Autonomous Enterprise,” a vision where AI agents execute business processes themselves. But the customer keynote on Wednesday told a more nuanced story. Lockheed Martin, ExxonMobil, Aeropuertos Argentina, and Levi Strauss each took the stage with a distinct AI strategy, shaped by their industries, risk tolerance, and strategic priorities. “Customers […]
How AI is transforming software development
Three years ago, most engineering leaders were debating whether their teams should be allowed to use GitHub Copilot. Today, the question has inverted. Leaders are trying to figure out how to run teams where AI generates nearly half the code, where autonomous agents open their own pull requests overnight and where the senior engineers who […]
The biggest mistakes CIOs make in the boardroom — and how to avoid them
Julie Averill didn’t need a second board meeting to understand what she got wrong in her first. She had just stepped into the CIO role at REI and did what most leaders would do: she prepared deeply, gathering inputs from her team, building a detailed view of the roadmap, and then walked into the boardroom […]
What is CMMI? A model to optimize development processes
What is CMMI? The Capability Maturity Model Integration (CMMI), a process and behavioral model, was developed by the Software Engineering Institute at Carnegie Mellon University as a process improvement tool for projects, divisions, or organizations. The DoD and US government helped develop the CMMI, which is a common requirement for DoD and US government software […]
Turla Turns Kazuar Backdoor Into Modular P2P Botnet for Persistent Access
The Russian state-sponsored hacking group known as Turla has transformed its custom backdoor Kazuar into a modular peer-to-peer (P2P) botnet that’s engineered for stealth and persistent access to compromised hosts. Turla, per the U.S. Cybersecurity and Infrastructure Security Agency (CISA), is assessed to be affiliated with Center 16 of Russia’s Federal Security Service (FSB)
UK: Hospital workers inappropriately accessed details of Southport victims, investigation finds
On the Spot News reports: An investigation has revealed than nearly 50 staff at a Merseyside hospital group accessed horrific details of the condition of those attacked in Southport. The investigation has only just come to light, with victims finding out this week about the horrific data breach as a result of investigative journalism by… […]
Four OpenClaw Flaws Enable Data Theft, Privilege Escalation, and Persistence
Cybersecurity researchers have disclosed a set of four security flaws in OpenClaw that could be chained to achieve data theft, privilege escalation, and persistence. The vulnerabilities, collectively dubbed Claw Chain by Cyera, can permit an attacker to establish a foothold, expose sensitive data, and plant backdoors. A brief description of the flaws is below –
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2026-42897 Microsoft Exchange Server Cross-Site Scripting Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing the Significant […]
Cisco warns of an actively exploited SD-WAN flaw with max severity
Cisco has disclosed a max-severity authentication bypass vulnerability affecting its Catalyst SD-WAN Controller and Catalyst SD-WAN Manager platforms, warning that the flaw has already been found to be exploited in the wild. The disclosure follows an earlier authentication bypass vulnerability that Cisco patched in February. In the latest advisory, the company said the new flaw […]
G7 Countries Release AI SBOM Guidance
The goal of the guidance, which outlines minimum elements, is to help organizations enhance transparency in AI systems and supply chains. The post G7 Countries Release AI SBOM Guidance appeared first on SecurityWeek.
Chinese APTs Expand Targets, Update Backdoors in Recent Campaigns
Salt Typhoon has hit an energy entity in Azerbaijan. Twill Typhoon has targeted Asian entities with an updated RAT. The post Chinese APTs Expand Targets, Update Backdoors in Recent Campaigns appeared first on SecurityWeek.
Akamai to Acquire AI and Browser Security Firm LayerX for $205 Million
The acquisition enables Akamai to expand its Zero Trust portfolio to add protection directly into the browser. The post Akamai to Acquire AI and Browser Security Firm LayerX for $205 Million appeared first on SecurityWeek.
Mythos Proves Potent in Vulnerability Discovery, Less Convincing Elsewhere
Independent benchmarking finds Mythos highly effective for source code audits, reverse engineering, and native-code analysis, though its exploit validation and reasoning capabilities remain inconsistent. The post Mythos Proves Potent in Vulnerability Discovery, Less Convincing Elsewhere appeared first on SecurityWeek.
New Linux Kernel Vulnerability Fragnesia Allows Root Privilege Escalation
The vulnerability, tracked as CVE-2026-46300, is similar to the recently disclosed exploits named Dirty Frag and Copy Fail. The post New Linux Kernel Vulnerability Fragnesia Allows Root Privilege Escalation appeared first on SecurityWeek.
Enhancing Data Center Security Without Sacrificing Performance
For AI data centers, where the stakes are the highest and performance constraints are the tightest, security and performance are no longer a zero-sum game. The post Enhancing Data Center Security Without Sacrificing Performance appeared first on SecurityWeek.
Cisco Patches Another SD-WAN Zero-Day, the Sixth Exploited in 2026
The zero-day, tracked as CVE-2026-20182, has been exploited in targeted attacks by a sophisticated threat actor identified as UAT-8616. The post Cisco Patches Another SD-WAN Zero-Day, the Sixth Exploited in 2026 appeared first on SecurityWeek.
Chrome 148 Update Patches Critical Vulnerabilities
The refresh resolves critical-severity use-after-free and other types of bugs in various browser components. The post Chrome 148 Update Patches Critical Vulnerabilities appeared first on SecurityWeek.
TeamPCP Ups the Game, Releases Shai-Hulud Worm’s Source Code
The hacking group is encouraging miscreants to use the code in supply chain attacks, promising monetary rewards. The post TeamPCP Ups the Game, Releases Shai-Hulud Worm’s Source Code appeared first on SecurityWeek.
OpenAI Hit by TanStack Supply Chain Attack
Two employee devices were compromised in the attack, and credential material was stolen from OpenAI code repositories. The post OpenAI Hit by TanStack Supply Chain Attack appeared first on SecurityWeek.
What 45 Days of Watching Your Own Tools Will Tell You About Your Real Attack Surface
In Your Biggest Security Risk Isn’t Malware — It’s What You Already Trust, we made a simple argument: the most dangerous activity inside most organizations no longer looks like an attack. It looks like administration. PowerShell, WMIC, netsh, Certutil, MSBuild — the same trusted utilities your IT team uses every day are also the preferred […]
TanStack Supply Chain Attack Hits Two OpenAI Employee Devices, Forces macOS Updates
OpenAI has disclosed that two of its employee devices in its corporate environment were impacted via the Mini Shai-Hulud supply chain attack on TanStack, but noted that no user data, production systems, or intellectual property were compromised or modified in an unauthorized manner. “Upon identification of the malicious activity, we worked quickly to investigate, contain, […]
Autonomous systems are finally working. Security is next
Waymo recently crossed a major milestone: Over 170 million autonomous miles driven without a single serious crash or injury. For years, autonomous driving was treated as a promise that was always just out of reach — too complex, too risky and not ready for the real world. That argument is no longer credible. Autonomous systems […]
EU’s Cyber Resiliency Act will put IT leaders to the test
Unlike most cyber security regulations, the EU’s Cyber Resilience Act is about product safety rather than processes or certification, extending the CE mark from the physical side of products to software, firmware, backend services, and anything with a network connection. It encodes existing best practices, enforces minimum product support lifecycles, and could mean developing stronger […]
The economics of ransomware 3.0
The moment every boardroom dreads There is a moment in almost every ransomware negotiation — usually around 36 hours, when legal, IT and the CFO are all in the same room — when someone says it out loud: “Let’s just see what the insurance covers.” That instinct, understandable as it is, has become one of […]
[Guest Diary] New Malware Libraries means New Signatures, (Fri, May 15th)
Post Content
On-Prem Microsoft Exchange Server CVE-2026-42897 Exploited via Crafted Email
Microsoft has disclosed a new security vulnerability impacting on-premise versions of Exchange Server that it said has come under active exploitation in the wild. The vulnerability, tracked as CVE-2026-42897 (CVSS score: 8.1), has been described as a spoofing bug stemming from a cross-site scripting flaw. An anonymous researcher has been credited with discovering and reporting […]
CISA Adds Cisco SD-WAN CVE-2026-20182 to KEV After Admin Access Exploits
The U.S.Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added a newly disclosed vulnerability impacting Cisco Catalyst SD-WAN Controller to its Known Exploited Vulnerabilities (KEV) catalog, requiring Federal Civilian Executive Branch (FCEB) agencies to remediate the issue by May 17, 2026. The vulnerability is a critical authentication bypass tracked as CVE-2026-20182. It’s
Soap Box: Where does AI fit into cloud security?
In this sponsored soap box edition of the Risky Business podcast Patrick Gray chats with Toni de la Fuente, the founder of Prowler. Prowler started off as a bunch of scripts in a trenchcoat, then became an open source cloud security tool, and it’s now a venture-funded cloud security business. In this interview Toni talks […]
ISC Stormcast For Friday, May 15th, 2026 https://isc.sans.edu/podcastdetail/9934, (Fri, May 15th)
Post Content
No need to hack when it’s leaking: Dalbir Singh & Associates law firm edition
Dalbir Singh & Associates ignored multiple attempts at responsible disclosure but finally locked down its misconfigured Amazon bucket, only to expose it again. Now the data is in the hands of criminals trying to extort them. On April 6, DataBreaches reported on a misconfigured Amazon bucket belonging to an immigration law firm in New York…. […]
AI agent finds 18-year-old remote code execution flaw in Nginx
Researchers have found a critical vulnerability in the widely used Nginx web server that can potentially lead to remote code execution under certain conditions. The flaw is a heap buffer overflow that has gone undetected in the program’s code for the past 18 years. Tracked as CVE-2026-42945, the vulnerability is one of 4 bugs found […]
2026089178101 Norman L. Hill CRD 1535969 AWC lp.pdf
2026089178101 Norman L. Hill CRD 1535969 AWC lp.pdf Anonymous (not verified) Thu, 05/14/2026 – 17:00 Case ID 2026089178101 Document Number e660daf8 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals Norman L. Hill Action Date Thu, 05/14/2026 – 12:00 Related Content Off Attachment 2026089178101 Norman L. Hill CRD 1535969 AWC lp.pdf Individual CRD 1535969
Meet Fragnesia, the third Linux kernel vulnerability in a month
Linux admins reeling from handling last month’s CopyFail and last week’s Dirty Frag kernel vulnerabilities have a new headache to deal with: Fragnesia. “This is a significant vulnerability,” Robert Beggs, head of incident response firm DigitalDefence, told CSO. “It is bypassing traditional filesystem permissions that are present and enforced (for example, ‘file is owned by […]
25-02185.pdf
25-02185.pdf Anonymous (not verified) Thu, 05/14/2026 – 15:55 Case ID 25-02185 Forum FINRA Document Type Award Claimants Vamsi Atreya Respondents Equitable Advisors, LLC Neutrals Gerald Thomas Harper Hearing Site Washington, DC Award Document 25-02185.pdf Documentum DocID 53f402d3 Award Date Official Thu, 05/14/2026 – 12:00 Related Content Off Claimant Representatives Dochtor Kennedy MBA, Respondent Representatives Eileen […]
25-02387.pdf
25-02387.pdf Anonymous (not verified) Thu, 05/14/2026 – 15:55 Case ID 25-02387 Forum FINRA Document Type Award Claimants Michael D’Andrea Respondents Sovereign Global Advisors, LLC Neutrals Michael H. DuBoff Gloria O. North Brian John Gallagher Hearing Site New York, NY Award Document 25-02387.pdf Documentum DocID 3d2de922 Award Date Official Thu, 05/14/2026 – 12:00 Related Content Off […]
SAP admite una lenta acogida de sus propuestas de IA
En su evento Sapphire 2025 del pasado año SAP realizó atrevidas promesas en materia de inteligencia artificial: Knowledge Graph, Joule Studio y AI Agent Hub, según avanzó entonces, saldrían al mercado a finales de año. Aunque esas herramientas ya están técnicamente disponibles, su adopción se ha retrasado. Es más, SAP ya está anunciando la versión […]
Casi todas las empresas invierten en IA, pero solo el 5% asegura que sus datos están preparados
Con 2026 casi a mitad de camino, las empresas empiezan a ver retornos tangibles de sus inversiones en inteligencia artificial. Sin embargo, muchas están descubriendo que escalar la IA requiere algo mucho menos llamativo que los modelos de última generación o las métricas más avanzadas: datos limpios, interoperables y bien gobernados. Según la nueva encuesta […]
AI 솔루션 과잉 시대…메가존클라우드, FDE·AIR 스튜디오로 해법 제시
이날 발표에 나선 염동훈 메가존클라우드 대표는 “1년 전 우리는 모든 기업이 AI 네이티브 회사로 전환해야 한다고 선언했고, 이는 단순히 AI 도구 하나를 도입하는 것이 아니라 데이터 파운데이션, 프로세스, 인재, 리더십, 거버넌스 전반을 새로 설계하는 일”이라고 강조했다. 이어 “고객이 가는 길을 안내하려면 우리가 먼저 그 길을 걸어봐야 한다”는 ‘커스터머 제로(Customer Zero)’ 원칙에 따라, 메가존클라우드 스스로 내부 […]
La IA impone a los CIO expectativas que pueden determinar su éxito o su fracaso
Los CIO y otros líderes de TI están atravesando un momento decisivo, al enfrentarse a nuevas y ambiciosas expectativas en sus funciones, entre ellas la capacidad de liderar el cambio y de construir equipos preparados para la inteligencia artificial. Durante años, los expertos en liderazgo tecnológico han insistido en que los CIO deben centrarse en […]
Decision-making speed is a hidden constraint on transformation success
Late into a large-scale SAP transformation, the technical work was on pace. Build was closing, system integration testing was underway and cutover readiness was taking shape. What was not on pace were the decisions the program depended on. Cross-functional calls around data ownership, process exceptions and cutover sequencing, decisions that had moved weekly earlier in […]
How deepfakes are rewriting the rules of the modern workplace
Trust used to be built into the mechanics of work. If a request came through a familiar voice on a call, a known face on screen or a message from a senior executive, most employees had little reason to question it. That assumption is becoming much harder to defend. What I am seeing now is […]
CIOs are put to the test as security regulations across borders recalibrate
Unlike most cyber security regulations, the EU’s Cyber Resilience Act is about product safety rather than processes or certification, extending the CE mark from the physical side of products to software, firmware, backend services, and anything with a network connection. It encodes existing best practices, enforces minimum product support lifecycles, and could mean developing stronger […]
AI-driven layoffs aren’t making business sense
A huge majority of large enterprises have laid off employees after rolling out AI initiatives, but reducing headcount doesn’t lead to the ROI executives may expect. Eighty percent of large enterprises surveyed by Gartner have reported workforce reductions after launching automation projects, with the average reduction between 1% and 15%. The IT analyst firm, however, […]
Building an AI CoE: Why you need one and how to make it work
Artificial intelligence (AI) is no longer the playground of hobbyists and programmers. From automating customer‑service transactions to optimizing supply‑chain decisions, AI is rapidly becoming the central nervous system of today’s enterprises. McKinsey surveys have found that nearly nine in ten organizations are now using AI regularly in at least one business function, compared with 78% […]
AI, power and the trade-off between freedom and innovation
Freedom has always been America’s global advantage. But when it comes to the quest for AI dominance, it may also be our biggest weakness. In the U.S., guardrails around AI — privacy protections, legal frameworks and ethics and accountability — are in place to preserve our individual freedoms. For 250 years, open systems, legal protections […]
2024083264201 John Polemis CRD 4270012 Complaint vrp.pdf
2024083264201 John Polemis CRD 4270012 Complaint vrp.pdf Anonymous (not verified) Thu, 05/14/2026 – 14:55 Case ID 2024083264201 Document Number da958398 Document Type Complaints Individuals John Polemis Action Date Wed, 05/13/2026 – 12:00 Related Content Off Attachment 2024083264201 John Polemis CRD 4270012 Complaint vrp.pdf Individual CRD 4270012
25-02091.pdf
25-02091.pdf Anonymous (not verified) Thu, 05/14/2026 – 14:10 Case ID 25-02091 Forum FINRA Document Type Award Claimants James Mahan Respondents J.P. Morgan Securities, LLC Neutrals Peter H. Daly Mauricio Arcadier Lawrence R. Maxwell Hearing Site Houston, TX Award Document 25-02091.pdf Documentum DocID 2c425031 Award Date Official Mon, 05/11/2026 – 12:00 Related Content Off Claimant Representatives […]
Cisco Catalyst SD-WAN Controller Auth Bypass Actively Exploited to Gain Admin Access
Cisco has released updates to address a maximum-severity authentication bypass flaw in Catalyst SD-WAN Controller that it said has been exploited in limited attacks. The vulnerability, tracked as CVE-2026-20182, carries a CVSS score of 10.0. “A vulnerability in the peering authentication in Cisco Catalyst SD-WAN Controller, formerly SD-WAN vSmart, and Cisco Catalyst SD-WAN Manager, formerly
Stealer Backdoor Found in 3 Node-IPC Versions Targeting Developer Secrets
Cybersecurity researchers are sounding the alarm about what has been described as “malicious activity” in newly published versions of node-ipc. According to Socket and StepSecurity, three different versions of the npm package have been confirmed as malicious – node-ipc@9.1.6 node-ipc@9.2.3 node-ipc@12.0.1 “Early analysis indicates that node-ipc@9.1.6, node-ipc@9.2.3, and node-ipc@12.0.1
ThreatsDay Bulletin: PAN-OS RCE, Mythos cURL Bug, AI Tokenizer Attacks, and 10+ Stories
Everything is still on fire. This week feels dumb in the worst way — bad links, weak checks, fake help desks, shady forum posts, and people turning supply chain attacks into some cursed little game for clout and cash. Half of it feels new. Half of it feels like crap we should have fixed years […]
Ghostwriter Targets Ukrainian Government With Geofenced PDF Phishing, Cobalt Strike
The Belarus-aligned threat group known as Ghostwriter has been attributed to a fresh set of attacks targeting governmental organizations in Ukraine. Active since at least 2016, Ghostwriter has been linked to both cyber espionage and influence operations targeting neighboring countries, particularly Ukraine. It’s also tracked under the monikers FrostyNeighbor, PUSHCHA, Storm-0257, TA445, UAC‑0057
FlowerStorm phishing gang adopts virtual-machine obfuscation to evade email defenses
A widely active phishing-as-a-service (PhaaS) operation known as FlowerStorm has begun using a browser-based virtual machine to conceal credential theft code, marking what researchers say is an escalation in phishing-kit sophistication that could make attacks harder for traditional email and static-analysis tools to detect. Researchers at Sublime Security said in April that they identified the […]
Alleged Dream Market admin arrested in Germany
Jonathan Greig reports: German and U.S. authorities arrested the alleged administrator behind Dream Market, a popular dark web forum that shut down in 2019. During a May 7 raid on three locations, German and U.S. law enforcement arrested Owe Martin Andresen, 49, on multiple charges of money laundering. An indictment unsealed this week by the… […]
Siemens Opcenter RDnL
View CSAF Summary Opcenter RDnL is affected by missing authentication in critical function in ‘ActiveMQ Artemis’. An unauthenticated attacker within the adjacent network could use the Core protocol to force a target broker to establish an outbound Core federation connection to an attacker-controlled rogue broker. This could potentially result in availability impacts or message injection […]
Siemens Solid Edge
View CSAF Summary Solid Edge SE2026 before Update 5 is affected by two file parsing vulnerabilities that could be triggered when the application reads specially crafted files in PAR format. This could allow an attacker to crash the application or execute arbitrary code. Siemens has released a new version for Solid Edge SE2026 and recommends […]
Siemens Teamcenter
View CSAF Summary Siemens Teamcenter is affected by multiple vulnerabilities which could potentially lead to a compromise in availability, integrity and confidentiality. Siemens has released new versions for the affected products and recommends to update to the latest versions. The following versions of Siemens Teamcenter are affected: Teamcenter V2312 vers:intdot/<2312.0014, vers:intdot/<2312.0009 (CVE-2026-33862, CVE-2026-33893, CVE-2024-4367) Teamcenter […]
Siemens Ruggedcom Rox
View CSAF Summary Ruggedcom Rox contains an input validation vulnerability in the feature key installation process that could allow an authenticated remote attacker to execute arbitrary commands with root privileges on the underlying operating system. Siemens has released new versions for the affected products and recommends to update to the latest versions. The following versions […]
Universal Robots Polyscope 5
View CSAF Summary Successful exploitation of these vulnerabilities could allow an attacker to bypass authentication and execute code. The following versions of Universal Robots Polyscope 5 are affected: Polyscope 5 <5.25.1 CVSS Vendor Equipment Vulnerabilities v3 9.8 Universal Robots Universal Robots Polyscope 5 Improper Neutralization of Special Elements used in an OS Command (‘OS Command […]
Siemens Simcenter Femap
View CSAF Summary Simcenter Femap is affected by heap based buffer overflow vulnerability in Datakit library that could be triggered when the application reads files in IPT format. If a user is tricked to open a malicious file with the affected application, an attacker could leverage the vulnerability to perform remote code execution in the […]
Siemens Ruggedcom Rox
View CSAF Summary Ruggedcom Rox before v2.17.1 contain multiple third-party vulnerabilities. Siemens has released new versions for the affected products and recommends to update to the latest versions. The following versions of Siemens Ruggedcom Rox are affected: RUGGEDCOM ROX MX5000 vers:intdot/<2.17.1 (CVE-2019-13103, CVE-2019-13104, CVE-2019-13106, CVE-2019-14192, CVE-2019-14193, CVE-2019-14194, CVE-2019-14195, CVE-2019-14196, CVE-2019-14197, CVE-2019-14198, CVE-2019-14199, CVE-2019-14200, CVE-2019-14201, CVE-2019-14202, […]
Siemens Ruggedcom Rox
View CSAF Summary Ruggedcom Rox contains an input validation vulnerability in the Scheduler functionality that could allow an authenticated remote attacker to execute arbitrary commands with root privileges on the underlying operating system. Siemens has released new versions for the affected products and recommends to update to the latest versions. The following versions of Siemens […]
Siemens SIMATIC
View CSAF Summary SIMATIC CN 4100 contains multiple vulnerabilities which could potentially lead to a compromise in availability, integrity and confidentiality. Siemens has released a new version for SIMATIC CN 4100 and recommends to update to the latest version. The following versions of Siemens SIMATIC are affected: SIMATIC CN 4100 vers:intdot/<5.0 CVSS Vendor Equipment Vulnerabilities […]
Siemens gWAP
View CSAF Summary Siemens gPROMS Web Applications Publisher (gWAP) is affected by a remote code execution vulnerability introduced through a third-party component, namely the Axios HTTP client library. The vulnerability stems from a specific “Gadget” attack chain that allows prototype pollution in other third-party libraries, potentially allowing an attacker to execute arbitrary code. Siemens has […]
Siemens Siemens ROS#
View CSAF Summary ROS# contains a ROS service file_server, that before version 2.2.2 contains a path traversal vulnerability which could allow an attacker to access, i.e. read and write, arbitrary files, which are accessible with the user rights of the user that runs the service, on the system that hosts service. Siemens has released a […]
PraisonAI CVE-2026-44338 Auth Bypass Targeted Within Hours of Disclosure
Threat actors have been observed attempting to exploit a recently disclosed security vulnerability in PraisonAI, an open-source multi-agent orchestration framework, within four hours of public disclosure. The vulnerability in question is CVE-2026-44338 (CVSS score: 7.3), a case of missing authentication that exposes sensitive endpoints to anyone, potentially allowing an attacker to invoke the
PraisonAI vulnerability gets scanned within 4 hours of disclosure
A newly disclosed authentication bypass flaw in the open-source AI orchestration framework PraisonAI was probed by internet scanners less than four hours after its public disclosure. According to Sysdig observations, roughly three hours and 44 minutes after a GitHub advisory dropped, a scanner identifying itself as “CVE-Detector/1.0” was already looking through the exposed PraisonAI instances […]
How AI Hallucinations Are Creating Real Security Risks
AI hallucinations are introducing serious security risks into critical infrastructure decision-making by exploiting human trust through highly confident yet incorrect outputs. When an AI model lacks certainty, it doesn’t have a mechanism to recognize that. Instead, it generates the most probable response based on patterns in its training data, even if that response is inaccurate. […]
716,000 Impacted by OpenLoop Health Data Breach
The telehealth platform was hacked in January, and users’ personal information was exfiltrated from its systems. The post 716,000 Impacted by OpenLoop Health Data Breach appeared first on SecurityWeek.
Government to Scrutinize Instructure Over Canvas Disruption, Data Breach
The Committee on Homeland Security has requested to be briefed on the incident and Instructure’s remediation steps. The post Government to Scrutinize Instructure Over Canvas Disruption, Data Breach appeared first on SecurityWeek.
Webinar Today: ROI for Cyber-Physical Security Programs
This webinar will help OT security teams and asset owners stop being cost centers and start being resilience drivers. The post Webinar Today: ROI for Cyber-Physical Security Programs appeared first on SecurityWeek.
Sweet Security Launches Agentic AI Red Teaming to Counter ‘Mythos Moment’
New “Sweet Attack” platform uses runtime intelligence and continuous agentic red teaming to identify exploitable attack chains human teams may miss. The post Sweet Security Launches Agentic AI Red Teaming to Counter ‘Mythos Moment’ appeared first on SecurityWeek.
Microsoft, Palo Alto Networks Find Many Vulnerabilities by Using AI on Their Own Code
Microsoft’s MDASH discovered 16 of the Patch Tuesday vulnerabilities, and Palo Alto used Mythos to find dozens of flaws. The post Microsoft, Palo Alto Networks Find Many Vulnerabilities by Using AI on Their Own Code appeared first on SecurityWeek.
Foxconn Confirms North American Factories Hit by Cyberattack
The Nitrogen ransomware group claims to have hacked the company’s systems, stealing 8TB of data, including confidential documents. The post Foxconn Confirms North American Factories Hit by Cyberattack appeared first on SecurityWeek.
Researcher Drops YellowKey, GreenPlasma Windows Zero-Days
YellowKey is a BitLocker bypass that requires physical access. GreenPlasma enables elevation of privileges to System. The post Researcher Drops YellowKey, GreenPlasma Windows Zero-Days appeared first on SecurityWeek.
High-Severity Vulnerability Patched in VMware Fusion
The patch was announced as Broadcom is attending the Pwn2Own hacking competition in Berlin this week. The post High-Severity Vulnerability Patched in VMware Fusion appeared first on SecurityWeek.
Hackers Targeted PraisonAI Vulnerability Hours After Disclosure
The first exploitation attempts were observed less than four hours after the authentication bypass was publicly disclosed. The post Hackers Targeted PraisonAI Vulnerability Hours After Disclosure appeared first on SecurityWeek.
F5 Patches Over 50 Vulnerabilities
The company’s latest quarterly advisory describes high and medium-severity issues in BIG-IP, BIG-IQ, and NGINX. The post F5 Patches Over 50 Vulnerabilities appeared first on SecurityWeek.
Windows Zero-Days Expose BitLocker Bypasses And CTFMON Privilege Escalation
An anonymous cybersecurity researcher who disclosed three Microsoft Defender vulnerabilities has returned with two more zero-days involving a BitLocker bypass and a privilege escalation impacting Windows Collaborative Translation Framework (CTFMON). The security defects have been codenamed YellowKey and GreenPlasma, respectively, by the researcher, who goes by the online aliases Chaotic Eclipse
What CISOs need to land a board role
Cybersecurity leaders often have complex relationships with their boards. Many boards lack cyber expertise, and CISOs can encounter roadblocks as a result when it comes to earning board approval. Other security leaders may not have a direct line to their board, or they may be viewed as too technical to win the support needed. One […]
New Fragnesia Linux Kernel LPE Grants Root Access via Page Cache Corruption
Details have emerged about a new variant of the recent Dirty Frag Linux local privilege escalation (LPE) vulnerability that allows local attackers to gain root access, making it the third such bug to be identified in the kernel within a span of two weeks. Codenamed Fragnesia, the security vulnerability is tracked as CVE-2026-46300 (CVSS score: […]
Simple bypass of the link preview function in Outlook Junk folder, (Thu, May 14th)
Besides serving as a place where Microsoft Outlook places suspected spam, the Outlook Junk folder has one additional function that can be quite helpful when it comes to identifying malicious messages. Any e-mail placed in this folder is stripped of all formatting, and destinations of all links included in the message become visible to the […]
18-Year-Old NGINX Rewrite Module Flaw Enables Unauthenticated RCE
Cybersecurity researchers have disclosed multiple security vulnerabilities impacting NGINX Plus and NGINX Open, including a critical flaw that remained undetected for 18 years. The vulnerability, discovered by depthfirst, is a heap buffer overflow issue impacting ngx_http_rewrite_module (CVE-2026-42945, CVSS v4 score: 9.2) that could allow an attacker to achieve remote code execution or cause a
ISC Stormcast For Thursday, May 14th, 2026 https://isc.sans.edu/podcastdetail/9932, (Thu, May 14th)
Post Content
North American Securities Administrators Association, Inc. (NASAA) Comment On Section V: Request for Comments
North American Securities Administrators Association, Inc. (NASAA) Comment On Section V: Request for Comments fnrw-backend Wed, 05/13/2026 – 19:40 Marni Rock Gibson Vince Martinez <vmartinez@nasaa.org> North American Securities Administrators Association, Inc. (NASAA) Section V: Request for Comments Core Official Date Wed, 05/13/2026 – 12:00 Comment File NASAA Comment Letter re FINRA Social Media-Influenced Investing Report […]
Fired employee sought AI help to hide deletion of hosting firm’s customer data
The apparent revenge deletion of US federal databases after the dismissal of twin brothers from an online hosting company is another reminder to IT and HR leaders that tough off-boarding procedures have to be implemented to prevent insider attacks. Destructive attacks either from disgruntled current or former employees aren’t new. But the conviction by a […]
25-01133.pdf
25-01133.pdf Anonymous (not verified) Wed, 05/13/2026 – 18:50 Case ID 25-01133 Forum FINRA Document Type Award Claimants Megan Palazzo Quentin Robb Respondents Brad Myers David James John Shumski Transitional Broker LLC Neutrals Thomas R. Bromberg Leonard M. Goldstein Anthony Michael Panek Hearing Site Salt Lake City, UT Award Document 25-01133.pdf Documentum DocID 41bb4d3b Award Date […]
25-00442.pdf
25-00442.pdf Anonymous (not verified) Wed, 05/13/2026 – 18:45 Case ID 25-00442 Forum FINRA Document Type Award Claimants James Tuberosa Respondents Ameriprise Financial Services, LLC Neutrals Stuart Sinai Susan S. Bentley John Frank Bauder Hearing Site Tampa, FL Award Document 25-00442.pdf Documentum DocID a22f5169 Award Date Official Wed, 05/13/2026 – 12:00 Related Content Off Claimant Representatives […]
24-01093.pdf
24-01093.pdf Anonymous (not verified) Wed, 05/13/2026 – 18:45 Case ID 24-01093 Forum FINRA Document Type Award Claimants Mengying Huang Respondents Charles Schwab & Co., Inc. TD Ameritrade, Inc. Neutrals Pamela Jane Koslow Marie Ann Stein Maggie Soleimani Hearing Site Los Angeles, CA Award Document 24-01093.pdf Documentum DocID ebfccb15 Award Date Official Wed, 05/13/2026 – 12:00 […]
25-01345.pdf
25-01345.pdf Anonymous (not verified) Wed, 05/13/2026 – 18:45 Case ID 25-01345 Forum FINRA Document Type Award Claimants Spartan Capital Securities, LLC Respondents TC BioPharm Holdings PLC Neutrals Jason Scott Eveleth Loretta Yin Albert Rizzo Hearing Site New York, NY Award Document 25-01345.pdf Documentum DocID 300d92db Award Date Official Wed, 05/13/2026 – 12:00 Related Content Off […]
Fortinet fixes two critical RCE flaws in FortiAuthenticator and FortiSandbox
Fortinet released a batch of patches across its products on Patch Tuesday, including two critical vulnerabilities that can lead to remote code execution. Fortinet flaws, both zero-day and n-day, have been exploited in the wild many times in the past, so companies should deploy patches as soon as possible. “Fortinet vulnerabilities are often attractive to […]
SAP’s AI promises last year? Most are still rolling out
SAP made bold promises about AI at Sapphire 2025: Knowledge Graph, Joule Studio, and AI Agent Hub would ship by the end of the year. Those tools are now technically available, but adoption has lagged, and SAP is already announcing version 2.0. “Joule Studio adoption has been minimal compared to what we’d like,” said Manoj […]
“공급망 보안 미흡하면 EU 판매 어려워진다”···블랙덕, CRA 대응 강조
맥키 총괄은 방한 기자간담회에서 “한국은 일본, 대만 등과 함께 아시아의 기술 혁신 국가 중 하나로, 블랙덕도 한국에서 빠르게 성장하고 있다”며 “고객사들이 혁신을 이어가는 동시에 보안도 함께 강화할 수 있도록, 블랙덕의 대응 경험과 공급망 보안 전략을 공유하고자 한국을 찾았다”고 밝혔다. CRA는 소프트웨어 요소가 포함된 제품 전반에 공통적으로 적용되는 EU의 사이버 보안 규제다. 적용 대상은 회사 소재지와 […]
The death of identity as we know it
A CISO walked out of the RSA conference last month and asked an honest question. “When does it make sense to create agents, sub-agents and swarms of agents versus digital twins?” He wasn’t looking for a sales pitch. He had just sat through days of keynotes, breakouts and vendor pitches where AI got more airtime […]
How Stanford Healthcare prescribes AI to streamline the clinician and patient experience
Before an organization launches any AI initiative, considering how disruptive it can be, it’s essential to prioritize governance, as well as make sure sufficient training and change management strategies are implemented. “I think it’s a combination of having all these things in place, otherwise it creates fear and anxiety,” says Aditya Bhasin, Stanford Healthcare’s VP […]
How CIOs use AI agents to accelerate revenue growth
A wave of AI agents has recently emerged for sales and revenue teams, including Highspot’s Deal Agent, an agent to accelerate pipeline generation and conversion, and Qualified’s Piper for Demandbase, an AI sales development representative (SDR) agent. Salesforce’s AgentForce and many others are also rallying behind using agents for this use case as well, so […]
New US CIO appointments, May 2026
Movers & Shakers is where you can keep up with new CIO appointments and gain valuable insight into the job market and CIO hiring trends. As every company becomes a technology company, CEOs and corporate boards are seeking multi-dimensional CIOs and IT leaders with superior skills in technology, communications, business strategy, and digital innovation. The […]
CISA’s AI SBOM guidance pushes software supply-chain oversight into new territory
The US Cybersecurity and Infrastructure Security Agency (CISA) and its G7 cyber agency partners have released a list of minimum elements for an AI software bill of materials, a move that could help CISOs assess the security and provenance of AI systems entering enterprise environments. The guidance extends traditional SBOM concepts into AI by calling […]
Your AI agent deletes critical data: Who is responsible?
A Replit AI coding agent deleted a company’s live production database during an active code freeze last year. “This was a catastrophic failure on my part,” it nonchalantly admitted. “I destroyed months of work in seconds.” While the data was eventually restored with a rollback, the agent believed the destruction was permanent and had no […]
SAP’s AI offer to legacy customers comes with a catch
More than 20,000 SAP customers are “stuck” on legacy ECC systems due to customizations, according to the CEO of SAP partner MyWave, Geraldine McBride, and many won’t migrate anytime soon. At Sapphire 2026, SAP offered them a path to AI, but only if they commit half their maintenance spend to the cloud first. The offer, […]
SAP: Latest news and insights
SAP (NYSE:SAP) is an enterprise software vendor based in Walldorf, Germany. Its cloud and on-premises enterprise resource planning (ERP) software, including S/4HANA, helps organizations manage their business operations and customer relations. The German multinational also offers a vast array of software solutions tailored to specific facets of the enterprise, including data management, analytics, and supply […]
Microsoft's MDASH AI System Finds 16 Windows Flaws Fixed in Patch Tuesday
Microsoft has unveiled a new multi-model artificial intelligence (AI)-driven system called MDASH to facilitate vulnerability discovery and remediation at scale, adding that it’s being tested by some customers as part of a limited private preview. MDASH, short for multi-model agentic scanning harness, is designed as a model-agnostic system that uses bespoke AI agents for different […]
What happens when China’s AI catches up to Mythos?
The Trump-Xi summit opening in Beijing this week carries an agenda item unlike any in the history of US-China diplomacy: what to do about artificial intelligence that can autonomously find and exploit vulnerabilities in the world’s most critical software — and what happens when both superpowers have it. Anthropic’s Mythos Preview, released last month to […]
NL: Dutch watchdog says healthcare lab failed data security rules before cyberattack affecting 850,000
In August 2025, research agency Bevolkingsonderzoek Nederland revealed that half a million women who had undergone cervical cancer screening had their data stolen. The research agency paid Nova ransomware gang’s demand, which Nova confirmed, but then the criminals turned around and seemingly demanded even more money because the lab had spoken with police. Or at… […]
UK: Regulator fines water company almost £1m for cybersecurity failures
Maxine Brigue reports: The Information Commissioner’s Office (ICO) has fined utility company South Staffordshire Water £963,900 after a cyber attack that resulted in users’ personal information being extracted and published on the dark web. The fine was issued last week (7 May) after a cyber attack ran from September 2020 to July 2022 and exposed the data… […]
UK: Aylesbury police officer found guilty of data protection breaches after snapping confidential information
James Lowson reports: A police officer based in Aylesbury was found guilty of breaching data protection laws after she photographed confidential information. At Reading Magistrates’ Court on April 28, PC Lily Maxey was found guilty of breaching data protection laws twice by a district judge. During the same hearing she was ordered to pay £2,050… […]
Azerbaijani Energy Firm Hit by Repeated Microsoft Exchange Exploitation
A threat actor with affiliations to China has been linked to a “multi-wave intrusion” targeting an unnamed Azerbaijani oil and gas company between late December 2025 and late February 2026, marking an expansion of its targeting. The activity has been attributed by Bitdefender with moderate-to-high confidence to a hacking group known as FamousSparrow (aka UAT-9244), […]
Microsoft’s new AI system finds 16 Windows flaws, including four critical RCEs
Microsoft has unveiled a new AI-driven vulnerability discovery system that identified 16 previously unknown Windows vulnerabilities, including four critical remote code execution flaws, in what security analysts say could mark a major shift in how software vulnerabilities are discovered and remediated. The system, codenamed MDASH, was developed by Microsoft’s Autonomous Code Security team alongside the […]
Palo Alto Networks bets on identity security for autonomous AI with Idira launch
Palo Alto Networks has launched Idira, a new identity security platform aimed at securing human users, machine identities, and AI agents amid the rising adoption of autonomous AI systems amongst enterprises. The company is positioning Idira as a next-generation identity security platform that goes beyond traditional privileged access management (PAM) systems by applying dynamic privilege […]
[Webinar] How Modern Attack Paths Cross Code, Pipelines, and Cloud
TL;DR: Stop chasing thousands of “toast” alerts. Join experts from Wiz to learn how hackers connect tiny flaws to build a “Lethal Chain” to your data—and how to break it. Register for the Strategic Briefing Here. Most security tools work like a smoke alarm that goes off every time you burn a piece of toast. […]
ClickFix finds a backup plan in PySoxy proxy chains
ClickFix, a one-shot social engineering technique that tricks victims into executing malicious workflows disguised as fixes to technical issues in their systems, has got a persistence upgrade. In a one-off instance, ReliaQuest researchers have spotted an intrusion chain using scheduled tasks, PowerShell-based command-and-control (C2), and a unique abuse of the decade-old open-source proxy tool PySoxy. […]
Most Remediation Programs Never Confirm the Fix Actually Worked
Security teams have never had better visibility into their environments and never been worse at confirming what they fix stays fixed. Mandiant’s M-Trends 2026 report puts the mean time to exploit at an estimated negative seven days. The Verizon 2025 DBIR puts median time to remediate edge device vulnerabilities at 32 days. These numbers have […]
BWH Hotels Says Hackers Had Access to Reservation Data for 6 Months
Threat actors obtained names and contact information for an unspecified number of BWH Hotels guests. The post BWH Hotels Says Hackers Had Access to Reservation Data for 6 Months appeared first on SecurityWeek.
White Circle Raises $11 Million for AI Control Platform
The startup will invest in accelerating product development, hiring new talent, and expanding its customer base. The post White Circle Raises $11 Million for AI Control Platform appeared first on SecurityWeek.
Adobe Patches 52 Vulnerabilities in 10 Products
While none of the flaws have been exploited in the wild, many of them could lead to arbitrary code execution. The post Adobe Patches 52 Vulnerabilities in 10 Products appeared first on SecurityWeek.
Exaforce Raises $125 Million for Agentic SOC Platform
Exaforce has raised a total of $200 million and plans on using the latest investment for product development and international expansion. The post Exaforce Raises $125 Million for Agentic SOC Platform appeared first on SecurityWeek.
Microsoft Patches 137 Vulnerabilities
Fresh security updates resolve critical flaws in Azure, Windows, Dynamics 365, and the SSO Plugin for Jira & Confluence. The post Microsoft Patches 137 Vulnerabilities appeared first on SecurityWeek.
ICS Patch Tuesday: New Security Advisories From Siemens, Schneider, CISA
Many ICS vendors have not released new advisories for the May 2026 Patch Tuesday. The post ICS Patch Tuesday: New Security Advisories From Siemens, Schneider, CISA appeared first on SecurityWeek.
Hundreds of Malicious Packages Force RubyGems to Suspend Registrations
More than 500 packages were pushed during the attack, but the target appears to have been RubyGems itself rather than users. The post Hundreds of Malicious Packages Force RubyGems to Suspend Registrations appeared first on SecurityWeek.
Chipmaker Patch Tuesday: Intel and AMD Patch 70 Vulnerabilities
The two chip giants have published over two dozen advisories describing recently identified security defects. The post Chipmaker Patch Tuesday: Intel and AMD Patch 70 Vulnerabilities appeared first on SecurityWeek.
Fortinet, Ivanti Patch Critical Vulnerabilities
Successful exploitation of these flaws could lead to arbitrary code execution and information disclosure. The post Fortinet, Ivanti Patch Critical Vulnerabilities appeared first on SecurityWeek.
Microsoft Patches Critical Zero-Click Outlook Vulnerability Threatening Enterprises
CVE-2026-40361 is similar to a vulnerability found a decade ago, BadWinmail, which at the time was dubbed an “enterprise killer”. The post Microsoft Patches Critical Zero-Click Outlook Vulnerability Threatening Enterprises appeared first on SecurityWeek.
In The Loop April 2026
In the Loop, Tactical Tech’s monthly newsletter, includes new releases, open calls, job opportunities, information about our partners, events, recommended resources and more.
CISA’s AI SBOM guidance pushes software supply-chain oversight into new territory
The US Cybersecurity and Infrastructure Security Agency (CISA) and its G7 cyber agency partners have released a list of minimum elements for an AI software bill of materials, a move that could help CISOs assess the security and provenance of AI systems entering enterprise environments. The guidance extends traditional SBOM concepts into AI by calling […]
Microsoft Patches 138 Vulnerabilities, Including DNS and Netlogon RCE Flaws
Microsoft on Tuesday released patches for 138 security vulnerabilities spanning its product portfolio, although none of them have been listed as publicly known or under active attack. Of the 138 flaws, 30 are rated Critical, 104 are rated Important, three are rated Moderate, and one is rated Low in severity. As many as 61 vulnerabilities […]
2026 CSO Award winners showcase business-enabling cyber innovation
The annual CSO Awards annually recognize security projects that demonstrate outstanding security leadership and business value. For this year’s program, CSO honors 64 security organizations whose hard work and innovative approaches have had a significant impact on how their enterprises navigate risks in an increasingly challenging cyber environment. These projects showcase the variety of strategies […]
GemStuffer Abuses 150+ RubyGems to Exfiltrate Scraped U.K. Council Portal Data
Cybersecurity researchers are calling attention to a new campaign dubbed GemStuffer that has targeted the RubyGems repository with more than 150 gems that use the registry as a data exfiltration channel rather than for malware distribution. “The packages do not appear designed for mass developer compromise,” Socket said. “Many have little or no download activity, […]
Google entdeckt erstmals KI-basierten Zero-Day-Exploit
Willkommen im neuen, KI-geschwängerten Bedrohungszeitalter. Gorodenkoff / Shutterstock Die Google Threat Intelligence Group (GTIG) warnt davor, dass kriminelle Hacker mittlerweile KI einsetzen – sowohl, um Schwachstellen aufzuspüren, als auch um anschließend Malware zu entwickeln, die diese aktiv ausnutzt. Der Anlass: Im Rahmen der eingehenden Analyse einer Angriffskampagne prorussischer Hacker haben die Sicherheitsexperten nach eigenen Angaben […]
Android Adds Intrusion Logging for Sophisticated Spyware Forensics
Google on Tuesday unveiled a new opt-in Android feature called Intrusion Logging for storing forensic logs to better analyze sophisticated spyware attacks. Intrusion Logging, available as part of Advanced Protection Mode, enables “persistent and privacy-preserving forensics logging to allow for investigation of devices in the event of a suspected compromise,” the company said. The feature, […]
[GUEST DIARY] Tearing apart website fraud to see how it works., (Wed, May 13th)
[This is a Guest Diary by Joshua Nikolson, an ISC Intern and part of the SANS.edu Bachelor’s degree in Applied Cybersecurity (BACS) program.]
Risky Business #837 -- GitHub Actions footgun claims TanStack
On this week’s show Patrick Gray, Adam Boileau and James Wilson discuss the week’s cybersecurity news. They cover: Mini Shai-Hulud and the TanStack compromise using Github Actions Instructure pays Canvas elearning platform data extortionists More Linux privilege escalation 0days! CISA helping critical infrastructure operators rearchitect their networks so they work offline This week’s episode is […]
Der Kaufratgeber für Breach & Attack Simulation Tools
Breach & Attack Simulation Tools geben Aufschluss darüber, wie gut (oder schlecht) Ihre Sicherheitskontrollen funktionieren. Roman Samborskyi | shutterstock.com Lösungen im Bereich Breach & Attack Simulation (BAS) unterstützen Unternehmen dabei, ihr Sicherheitsniveau zu verstehen. Dazu automatisieren die Tools die Tests spezifischer Bedrohungsvektoren. Als Grundlage dienen dabei in der Regel das MITRE-ATT&CK– oder Cyber-Killchain-Framework. BAS-Produkte simulieren […]
ISC Stormcast For Wednesday, May 13th, 2026 https://isc.sans.edu/podcastdetail/9930, (Wed, May 13th)
Post Content
Proxying the Unproxyable? Sending EXE traffic to a Proxy, (Wed, May 13th)
.. if “unproxyable” is a word that is ..
May Patch Tuesday roundup: Critical holes in Windows Netlogon, DNS, and SAP S/4HANA
Critical vulnerabilities in Windows Server’s networking and identity infrastructure, as well as a serious hole in Microsoft Dynamics 365 on-premises version, highlight Microsoft’s May Patch Tuesday fixes. They are among the 118 vulnerabilities identified this month by the company. Some in cloud-based services like Azure and Microsoft Teams have already been fixed, so no admin […]
Patch Tuesday, May 2026 Edition
Artificial intelligence platforms may be just as susceptible to social engineering as human beings, but they are proving remarkably good at finding security vulnerabilities in human-made computer code. That reality is on full display this month with some of the more widely-used software makers — including Apple, Google, Microsoft, Mozilla and Oracle — fixing near […]
25-01456.pdf
25-01456.pdf Anonymous (not verified) Tue, 05/12/2026 – 16:40 Case ID 25-01456 Forum FINRA Document Type Award Claimants Bahram Kashan Respondents Charles Schwab & Co., Inc. Neutrals Robert J. Scafuri Sandra Mendel Furman Robert S Hendricks Hearing Site Columbus, OH Award Document 25-01456.pdf Documentum DocID 6852bc03 Award Date Official Tue, 05/12/2026 – 12:00 Related Content Off […]
21-01689.pdf
21-01689.pdf Anonymous (not verified) Tue, 05/12/2026 – 16:40 Case ID 21-01689 Forum FINRA Document Type Award Claimants Valerie Davis Respondents Robinhood Financial, LLC. Neutrals James J. Brearton Stuart M. Schwartz Timothy A. Meigher Hearing Site Albany, NY Award Document 21-01689.pdf Documentum DocID 7bcd6062 Award Date Official Mon, 05/11/2026 – 12:00 Related Content Off Claimant Representatives […]
Can an AI be a competent leader? Let’s find out
The Register reports on research that explores managerial uses of AI-based “digital twins” to augment their leadership capabilities. The result: The paper’s authors don’t appear to understand leadership well enough to draw a useful conclusion. Very short analysis: To the extent digital twins are twins, by definition their performance must be exactly as good as […]
AI coding tools are changing output faster than they are changing judgment
I say this not as a spectator to the AI tooling wave, but as an engineer who has spent the last four-plus years building and scaling production systems across payments, multi-tenant platforms and reliability-sensitive environments, and who has had to make architectural decisions where failure would not have been theoretical. In one recent role, I […]
AI saddles CIOs with new make-or-break expectations
CIOs and other IT leaders are experiencing a make-or-break moment as they face major new expectations in their roles, including the ability to lead change and build AI-ready teams. IT leadership experts have been talking for years about the need for CIOs to focus on business results, in addition to providing technical expertise and keeping […]
AI is not transforming software development where you think
AI is making software development faster, but in many organizations, delivery is not improving. Developers are generating more code, completing tasks more quickly and appearing more productive. On the surface, it looks like a clear gain, driven by advances in generative AI in the software development life cycle. But that view is incomplete. From what […]
The next enterprise architecture asset: Ontologies for AI
A data ontology starts with a simple but powerful shift: organizing data by meaning, not just structure. In practice, it provides a shared semantic framework that defines what data represents, how key entities relate and how that meaning is consistently understood across systems, teams and acquisitions. By integrating data across silos and domains, an ontology […]
Red Hat offers endless Linux support — for a fee
Understanding that enterprise migrations can be structurally complicated, costly, and constrained in certain environments, many software and cloud providers offer extended maintenance, support, and security updates. Oftentimes, though, they come with caveats and firm end dates. Red Hat is looking to shake up this paradigm with its announcement at Red Hat Summit of the Red […]
Red Hat adds support for agentic AI development
As use of agentic AI accelerates, Red Hat is hoping to position itself as the critical behind-the-scenes plumbing and connective fabric. To this end, the company has unveiled new desktop and developer suite functions, skills bundles, and a rolling Linux release to help enterprises move beyond the experimental phase. Announced at Red Hat Summit today, […]
ServiceNow’s AI control tower offers hazy view of spend
IT budgeting has gotten a lot trickier as vendors begin to adjust their pricing to include variable charges for agentic AI usage in addition to seat-based licensing fees. A case in point is the licensing model for ServiceNow, which has introduced usage-based pricing for its AI components. As part of its AI transformation, the company […]
El desafío global de los CIO
Por si los directores de sistemas de información no tienen ya bastante con lo que lidiar ante el aumento de la demanda de IA en todo el ámbito empresarial, el actual clima geopolítico, volátil, les obliga ahora a adoptar una mentalidad más centrada en lo global en todo, desde sus cadenas de suministro de TI […]
GitLab CEO sees developer tool bill increasing 100-fold
GitLab CEO Bill Staples says enterprises’ monthly bill for developer platform services has risen from tens of dollars per seat to hundreds over the last year, and is headed toward the thousands, signaling a structural change in how they will be billed for AI-enabled software development tools. The increase in cost reflects the volume of […]
Microsoft May 2026 Patch Tuesday, (Tue, May 12th)
Today’s Microsoft patch Tuesday fixes 137 different vulnerabilities. In addition, the update addresses 137 Chromium-related issues affecting Microsoft Edge.
Mistral AI SDK, TanStack Router hit in npm software supply chain attack
The TeamPCP threat group has pulled off another big supply chain attack which within a few hours this week was able to successfully compromise 170 Node Package Manager (npm) and PyPI packages. The attack affected the entire TanStack Router ecosystem (@tanstack) of 42 packages, a routing library hugely popular among React web application developers. Multiple […]
25-01843.pdf
25-01843.pdf Anonymous (not verified) Tue, 05/12/2026 – 12:45 Case ID 25-01843 Forum FINRA Document Type Award Claimants Vincent Li Respondents Fidelity Brokerage Services LLC Neutrals Sandra Holtzman Hearing Site Jersey City, NJ Award Document 25-01843.pdf Documentum DocID 3fec4c26 Award Date Official Mon, 05/11/2026 – 12:00 Related Content Off Claimant Representatives Vincent Li Respondent Representatives Erin […]
New Exim BDAT Vulnerability Exposes GnuTLS Builds to Potential Code Execution
Exim has released security updates to address a severe security issue affecting certain configurations that could enable memory corruption and potential code execution. Exim is an open-source Mail Transfer Agent (MTA) designed for Unix-like systems to receive, route, and deliver email. The vulnerability, tracked as CVE-2026-45185, aka Dead.Letter, has been described as a use-after-free
Monthly Disciplinary Actions - May 2026
Monthly Disciplinary Actions – May 2026 K30658 Tue, 05/12/2026 – 11:57
US bank reports itself for revealing customer data to unauthorized AI application
Connor Jones reports: A US commercial bank just tattled on itself to the Securities and Exchange Commission (SEC) for plugging a bunch of customer data into an unauthorized AI application. Community Bank, which operates in southwestern Pennsylvania, Ohio, and West Virginia, filed an 8-K with the regulator on Monday, saying it launched an investigation into the internal… […]
RubyGems Suspends New Signups After Hundreds of Malicious Packages Are Uploaded
RubyGems, the standard package manager for the Ruby programming language, has temporarily paused account sign ups following what has been described as a “major malicious attack.” “We’re dealing with a major malicious attack on RubyGems right now,” Maciej Mensfeld, senior product manager for software supply chain security at Mend.io, said in a post on X. […]
25-00322.pdf
25-00322.pdf Anonymous (not verified) Tue, 05/12/2026 – 10:30 Case ID 25-00322 Forum FINRA Document Type Award Claimants Samuel A. Till, Jr. IRA Samuel A. Till, Jr. SEP IRA Sue Ann Till IRA Sue Ann Till SEP IRA Respondents J. P. Turner & Company LLC Summit Brokerage Service, Inc. Neutrals Richard Carl Smukler Robert G. Geeseman […]
Opinion 13/2026 on the draft decision of the Office of the Data Protection Ombudsman (FI SA) regarding the approval of the requirement for accreditation of a certification body pursuant to Article 43(3) GDPR
Opinion 13/2026 on the draft decision of the Office of the Data Protection Ombudsman (FI SA) regarding the approval of the requirement for accreditation of a certification body pursuant to Article 43(3) GDPR icolonnm Tue, 12/05/2026 – 16:24 12 May 2026 Opinion 13/2026 242.9KB English Download Members: Finland Topics: Accreditation
Homeland Security wants to know about the Instructure breach; we still want to know about the Navigate360 breach
Breaches involving school-related vendors such as PowerSchool and Instructure are causing major headaches for schools, students, and parents. They are also getting more attention from Congress. While some breaches have not exposed core data or personal information of students or personnel, other breaches, such as those involving PowerSchool and Navigate360’s P3 Campus, have involved sensitive… […]
OpenAI introduces Daybreak cyber platform, takes on Anthropic Mythos
OpenAI has unveiled Daybreak, its answer to Anthropic’s Claude Mythos, amid a growing market for frontier AI-powered cyber defense platforms. The initiative combines OpenAI’s large language models, Codex’s agentic capabilities, and integrations with the broader enterprise security ecosystem. The company said Daybreak is focused on accelerating cyber defense operations and enabling organizations to secure software […]
New TrickMo Variant Uses TON C2 and SOCKS5 to Create Android Network Pivots
Cybersecurity researchers have flagged a new version of the TrickMo Android banking trojan that uses The Open Network (TON) for command-and-control (C2). The new variant, observed by ThreatFabric between January and February 2026, has been observed actively targeting banking and cryptocurrency wallet users in France, Italy, and Austria. “TrickMo relies on a runtime-loaded APK (dex.module),
Fuji Electric Tellus
View CSAF Summary Successful exploitation of this vulnerability could allow an attacker to elevate privileges from user to system, which may then enable the attacker to cause a temporary denial of service, open files, or delete files. The following versions of Fuji Electric Tellus are affected: Tellus 5.0.2 CVSS Vendor Equipment Vulnerabilities v3 7.8 Fuji […]
ABB Automation Builder Gateway for Windows
View CSAF Summary ABB became aware of severe vulnerability in the products versions listed as affected in the advisory. The Windows gateway is accessible remotely by default. Unauthenticated attackers can therefore search for PLCs, but the user management of the PLCs prevents the actual access to the PLCs – unless it is disabled The following […]
ABB AC500 V3 Multiple Vulnerabilities
View CSAF Summary ABB became aware of severe vulnerability in the products versions listed as affected in the advisory. An update is available that resolves these vulnerabilities. An attacker who successfully exploited these vulnerabilities could bypass the user management and read visualization files (CVE-2025-2595), read and write certificates and keys (CVE-2025-41659) or cause a denial-of-service […]
ABB WebPro SNMP Card PowerValue Multiple Vulnerabilities
View CSAF Summary ABB became aware of multiple internally discovered vulnerabilities in the WebPro SNMP card PowerValue for the product versions listed as affected in the advisory. Depending upon the vulnerability, an attacker with access to local network who successfully exploited this vulnerability could have – Unauthorized access – Insufficient Session Expiration leading to resource […]
Software Bill of Materials for AI - Minimum Elements
CISA and the Group of Seven (G7) international partners—Germany, Canada, France, Italy, Japan, the United Kingdom, and the European Union—have released joint guidance, Software Bill of Materials for AI – Minimum Elements, to help public and private sector stakeholders improve transparency in their artificial intelligence (AI) systems and supply chains. A software bill of materials (SBOM) […]
Subnet Solutions PowerSYSTEM Center
View CSAF Summary Successful exploitation of these vulnerabilities could allow an authenticated attacker to expose sensitive information or cause a CRLF injection. The following versions of Subnet Solutions PowerSYSTEM Center are affected: PowerSYSTEM Center 2020 <=5.28.x (CVE-2026-35504) PowerSYSTEM Center 2020 >=5.8.x|<=5.28.x (CVE-2026-26289) PowerSYSTEM Center 2020 >=5.11.x|<=5.28.x (CVE-2026-33570) PowerSYSTEM Center 2024 >=6.0.x|<=6.1.x (CVE-2026-26289, CVE-2026-35555, CVE-2026-35504) PowerSYSTEM […]
ABB AC500 V3 Stack Buffer Overflow in Cryptographic Message Syntax
View CSAF Summary ABB became aware of vulnerability in the products versions listed as affected in the advisory. An update is available that resolves publicly reported vulnerability. An attacker who successfully exploited these vulnerabilities could cause a crash, denial-of-service (DoS), or potentially remote code execution. The following versions of ABB AC500 V3 Stack Buffer Overflow […]
Webinar: What the Riskiest SOC Alerts Go Unanswered - and How Radiant Security Can Help
Why do the Riskiest SOC Alerts Go Unanswered? Security operations teams are drowning in alerts. But the real problem isn’t always alert volume; it’s the blind spots. The most dangerous alerts are the ones no one is investigating. A recent report from The Hacker News examined why certain high-risk alert categories – WAF, DLP, OT/IoT, […]
Fake Claude Code takes the IElevator to your browser secrets
Developers looking for Anthropic’s increasingly popular Claude Code tool are now being lured into downloading malware. According to researchers at Ontinue, attackers are abusing a fake Claude Code installer to deliver a previously undocumented PowerShell payload. The malware is designed to evade detection, recover browser encryption material, and steal sensitive data from developer systems. “Developers […]
Cloudflare Lays Off 1,100 Employees in AI-Driven Restructuring
The company topped revenue and earnings forecasts for the first quarter of 2026, but its shares plunged more than 20%. The post Cloudflare Lays Off 1,100 Employees in AI-Driven Restructuring appeared first on SecurityWeek.
Skoda Data Breach Hits Online Shop Customers
Using a vulnerability in the portal, hackers accessed names, addresses, email addresses, and phone numbers. The post Skoda Data Breach Hits Online Shop Customers appeared first on SecurityWeek.
Google Detects First AI-Generated Zero-Day Exploit
The zero-day was designed to bypass 2FA and it was developed by a prominent cybercrime group. The post Google Detects First AI-Generated Zero-Day Exploit appeared first on SecurityWeek.
Build Application Firewalls Aim to Stop the Next Supply Chain Attack
Rather than scanning code alone, Build Application Firewalls inspect runtime behavior inside the software build pipeline. The post Build Application Firewalls Aim to Stop the Next Supply Chain Attack appeared first on SecurityWeek.
Frame Security Emerges From Stealth With $50M for Awareness and Training Platform
Team8, Index Ventures, Picture Capital, Elad Gil, Cerca Partners, and Tesonet invested in Frame Security. The post Frame Security Emerges From Stealth With $50M for Awareness and Training Platform appeared first on SecurityWeek.
TanStack, Mistral AI, UiPath Hit in Fresh Supply Chain Attack
Over 400 malicious versions of 170 packages were published as part of the new Mini Shai-Hulud campaign. The post TanStack, Mistral AI, UiPath Hit in Fresh Supply Chain Attack appeared first on SecurityWeek.
Is The SOC Obsolete, And We Just Haven’t Admitted It Yet?
Many AI-first enterprises have already embraced sovereign architectures for general AI initiatives; cybersecurity—and the SOC—should be next. The post Is The SOC Obsolete, And We Just Haven’t Admitted It Yet? appeared first on SecurityWeek.
Why Agentic AI Is Security's Next Blind Spot
Agentic AI is already running in production environments across many organizations today. It is executing tasks, consuming data, and taking actions — most likely without meaningful involvement from the security team. The industry conversation has largely framed this as a question of policy: allow it, restrict it, or monitor it? However, that framing misses the […]
cPanel flaw exposes enterprises to hosting supply-chain risks
A newly disclosed cPanel vulnerability is being exploited at scale, giving attackers a route into web hosting environments that many enterprises may not monitor closely. Analysts say the risk highlights weak visibility into hosting supply chains. The flaw, tracked as CVE-2026-41940, has been used to deploy backdoors, plant SSH keys, steal credentials, and compromise hosting […]
Developer workstations are the new beachhead
I spent the first week of April reading three separate threat intelligence reports that, on the surface, had nothing in common. One covered a North Korean campaign that had published over 1,700 malicious packages across five open-source ecosystems. Another detailed a malware operation using a Zig-compiled binary to silently infect every IDE on a developer’s […]
CISOs step into the AI spotlight
Serving in the military requires a precise, tactical mindset, and that’s exactly what Barry Hensley espoused during his 24 years in the US Army, where he rose to the rank of colonel. The military “is where you earn your stripes, showing your soldiers your willingness to jump into a foxhole and pick up a weapon,” […]
Why patching SLAs should be the floor, not the strategy
I’ve been a CISO for two separate companies, know several CISOs personally, and interact with many others through various cybersecurity forums. We all have one thing in common. We can tell you our patching SLA numbers off the top of our heads. Ninety-five percent of criticals closed in 14 days. Eighty-something on highs. The board […]
Mini Shai-Hulud Worm Compromises TanStack, Mistral AI, Guardrails AI & More Packages
TeamPCP, the threat actor behind the recent supply chain attack spree, has been linked to the compromise of the npm and PyPI packages from TanStack, UiPath, Mistral AI, OpenSearch, and Guardrails AI as part of a fresh Mini Shai-Hulud campaign. The affected npm packages have been modified to include an obfuscated JavaScript file (“router_init.js”) that’s designed […]
Instructure Reaches Ransom Agreement with ShinyHunters to Stop 3.65TB Canvas Leak
American educational technology company Instructure, the parent company of Canvas, said it reached an “agreement” with a decentralized cybercrime extortion group after it breached its network and threatened to leak stolen information from thousands of schools and universities. In an update shared on Monday, the Utah-based firm said it “reached an agreement with the unauthorized […]
OpenAI Launches Daybreak for AI-Powered Vulnerability Detection and Patch Validation
OpenAI has launched Daybreak, a new cybersecurity initiative that brings together frontier artificial intelligence (AI) model capabilities and Codex Security to help organizations identify and patch vulnerabilities before attackers find a way in using the same issues. “Daybreak combines the intelligence of OpenAI models, the extensibility of Codex as an agentic harness, and our partners […]
iOS 26.5 Brings Default End-to-End Encrypted RCS Messaging Between iPhone and Android
Apple on Monday officially released iOS 26.5 with support for end-to-end encryption (E2EE) to Rich Communication Services (RCS) in beta as part of a “cross-industry effort” to replace traditional SMS with a more secure alternative. To that end, E2EE RCS messaging is rolling out to iPhone users running iOS 26.5 with supported carriers and Android […]
Cybersicherheitsvorschriften: So erfüllen Sie Ihre Compliance-Anforderungen
Mit der Zunahme von Cyberbedrohungen steigt auch die Zahl der Compliance-Rahmenwerke. So können CISOs diese Herausforderung bewältigen. Foto: Dapitart – shutterstock.com Die Anforderungen von Cybersicherheitsvorschriften können je nach Unternehmensgröße, Region, Branche, Datensensibilität und Programmreifegrad sehr unterschiedlich sein. Ein börsennotiertes Unternehmen hat beispielsweise keine andere Wahl, als mehrere Vorschriften einzuhalten sowie Risikobewertungen und Pläne für Abhilfemaßnahmen […]
ISC Stormcast For Tuesday, May 12th, 2026 https://isc.sans.edu/podcastdetail/9928, (Tue, May 12th)
Post Content
Customer Identity & Access Management: Die besten CIAM-Tools
Wir haben die besten Lösungen in Sachen Customer Identity & Access Management für Sie zusammengestellt. Jackie Niam | shutterstock.com Customer Identity & Access Management (CIAM) bildet eine Unterkategorie von Identity & Access Management (IAM). CIAM wird dazu eingesetzt, die Authentifizierungs- und Autorisierungsprozesse von Applikationen zu managen, die öffentlich zugänglich sind, beziehungsweise von Kunden bedient werden. […]
Linux kernel maintainers suggest a ‘kill switch’ to protect systems until a zero-day vulnerability is patched
Linux server admins may get the ability to turn off a vulnerable function in the OS kernel until a patch for a zero-day vulnerability is ready, if a proposal from a kernel developer and maintainer is accepted by the open source community. The idea of a kill switch for privileged operators has been suggested by […]
Apple Patches Everything, (Mon, May 11th)
Apple today released its typical feature update across it’s operating systems (iOS, iPadOS, macOS, tvOS, watchOS, vision OS). With this update, Apple patched 84 different vulnerabilities. Updates are available for the “26” series of operating systems, as well as for the previous “18” version of iOS/iPadOS, and two versions back for macOS (version 14 and […]
The Gentlemen Ransomware Group Becomes a Victim
Ah, more drama in the cybercrime ecosystem. Matthew J. Schwartz reports: A ransomware organization is suffering an extreme case of turnabout is fair play through a data breach that splaying internal correspondence across the internet. “The Gentlemen” surfaced as a ransomware-as-a-service organization in mid-2025 with – as SOCRadar has noted – little intention of playing nice. Hints… […]
25-01923.pdf
25-01923.pdf Anonymous (not verified) Mon, 05/11/2026 – 15:45 Case ID 25-01923 Forum FINRA Document Type Award Claimants Alexander Winter Respondents PNC Investments Neutrals Leah Murray Albert Gregory Hunter Mathews Robert Dean McKinley Hearing Site Jersey City, NJ Award Document 25-01923.pdf Documentum DocID 5e084450 Award Date Official Mon, 05/11/2026 – 12:00 Related Content Off Claimant Representatives […]
Gusrae Kaplan Nusbaum PLLC Comment On Regulatory Notice 26-06
Gusrae Kaplan Nusbaum PLLC Comment On Regulatory Notice 26-06 fnrw-backend Mon, 05/11/2026 – 15:19 Craig A. Riha Craig Riha <criha@gusraekaplan.com> Gusrae Kaplan Nusbaum PLLC Regulatory Notice 26-06 Core Official Date Mon, 05/11/2026 – 12:00 Comment File Gusrae Kaplan Nusbaum PLLC_Craig A. Riha_26-06_5.8.2026.pdf
2025087042501 Mohammed A. Karim CRD 4419277 AWC vrp.pdf
2025087042501 Mohammed A. Karim CRD 4419277 AWC vrp.pdf Anonymous (not verified) Mon, 05/11/2026 – 15:05 Case ID 2025087042501 Document Number e79b057a Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals Mohammed A. Karim Action Date Mon, 05/11/2026 – 12:00 Related Content Off Attachment 2025087042501 Mohammed A. Karim CRD 4419277 AWC vrp.pdf Individual CRD 4419277
¿Ha llegado la hora de sumar perfiles de humanidades al equipo TI?
Hace unos años, se hizo viral la reducción de horas de Filosofía en el Bachillerato, algo que despertó muchas críticas, pero se vio también como la confirmación de un cambio de ciclo. Las humanidades han ido perdiendo fuelle y relevancia en los planes de estudio, pero también en la percepción pública de lo que importa. […]
The 360° CIO is here. Most operating models have not caught up
The idea of the “360° CIO” isn’t a future concept—it is already here. As AI adoption accelerates and technology decisions spread across the business, this tension is becoming more visible—and more consequential. In my experience and in conversations with other technology leaders, the CIO role now extends well beyond traditional IT boundaries. Today, CIOs are […]
Why tech needs smarter contracts for data centers
Data centers are reshaping our landscape at breakneck speed. Every AI query, online purchase, and streaming video now runs through these massive facilities. The United States Department of Energy is leading the way in developing public private partnerships (PPPs) essential to facilitating AI’s expansion. Meta, Google, Microsoft, and OpenAI are racing to lock in long-term […]
CIOs rise to the global challenge
As if IT leaders didn’t have enough to contend with as demand for enterprise-wide AI increases, a volatile geopolitical climate now mandates that they adopt a more global-centric mindset on everything from their tech supply chains and regulation to distributed infrastructure and workforces. Lately, the news has spoken volumes about the Iran war’s impact on […]
Your operating model is the real legacy system
For the past decade, enterprise modernization has been framed as a technology problem. Legacy systems. Technical debt. Monoliths that need to be broken apart and moved to the cloud. That framing is convenient and also incomplete. In most organizations, the technology isn’t the constraint. The operating model is. You can see it in how decisions […]
The skill that separates strategists from operators in the AI era
For most of human history, the tools we built extended our bodies. The plow extended our hands. The wheel extended our feet. The telescope extended our eyes. For the first time, we’re building tools that extend our minds. I’ve spent the last year training chief AI officers and leadership teams on AI implementation. One of […]
Lyrie.ai Joins First Batch of Anthropic’s Cyber Verification Program
Dubai-founded OTT Cybersecurity LLC also unveils the Agent Trust Protocol (ATP), the first open cryptographic standard for AI agent identity, scope, and action verification — slated for IETF submission. OTT Cybersecurity LLC, the company behind Lyrie.ai, today announced two milestones that together position the company as foundational infrastructure for the agentic AI era: acceptance into […]
¿Cuál es la mejor opción de internet cuando viajamos por trabajo? Por qué Holafly for Business es la preferida de las empresas
Para un equipo IT, uno de los mayores riesgos cuando un empleado viaja no es el vuelo, sino el acceso a internet cuando llega a su destino: un trabajador que aterriza sin conexión no solo pierde tiempo, sino que pierde acceso a herramientas críticas, recurre a redes WiFi inseguras o toma decisiones sin información en […]
CIO50 Australia Awards 2026: Nominations now open
Nominations for the prestigious CIO50 Australia Awards have opened. Now in its 11th year, CIO50 Awards will be held alongside the CSO30 Awards in Sydney on September 22. Hosted by CIO Australia, this flagship program recognises outstanding senior technology and digital executives driving innovation, transformation, and impact across the country. Open to individuals with overall […]
Beyond prevention: Protecting patient care through cyber recovery
Cyberattacks in healthcare can be operational crises that disrupt care delivery, delay procedures, and put patient safety at risk. As ransomware and data breaches continue to escalate, healthcare leaders are being forced to rethink what resilience actually means in practice. For years, resilience was defined largely by prevention. But in healthcare environments shaped by legacy […]
TeamPCP Compromises Checkmarx Jenkins AST Plugin Weeks After KICS Supply Chain Attack
Checkmarx has confirmed that a modified version of the Jenkins AST plugin was published to the Jenkins Marketplace. “If you are using Checkmarx Jenkins AST plugin, you need to ensure that you are using the version 2.0.13-829.vc72453fa_1c16 that was published on December 17, 2025 or previously,” the cybersecurity company said in a statement over the […]
cPanel CVE-2026-41940 Under Active Exploitation to Deploy Filemanager Backdoor
A threat actor named Mr_Rot13 has been attributed to the exploitation of a recently disclosed critical cPanel flaw to deploy a backdoor codenamed Filemanager on compromised environments. The attack exploits CVE-2026-41940, a vulnerability impacting cPanel and WebHost Manager (WHM) that could result in an authentication bypass and allow remote attackers to gain elevated control of […]
25-01665.pdf
25-01665.pdf Anonymous (not verified) Mon, 05/11/2026 – 13:05 Case ID 25-01665 Forum FINRA Document Type Award Claimants Colin Rosenberg Respondents UBS Financial Services Inc. Citigroup Global Markets, Inc. Neutrals Roger C. Benson Thomas R. Watkins Val D. Hornstein Hearing Site Pittsburgh, PA Award Document 25-01665.pdf Documentum DocID 25878d72 Award Date Official Fri, 05/08/2026 – 12:00 […]
Entries now open for the 2026 CSO30 Australia Awards
Nominations are now open for the 2026 CSO30 Australia Awards, celebrating the country’s most effective and influential cybersecurity leaders. The CSO30 Awards will once again be held alongside the CIO50 Awards, bringing together Australia’s leading technology and security executives for a flagship industry event on 22 September in Sydney. Part of Foundry’s prestigious global awards […]
24-00307.pdf
24-00307.pdf Anonymous (not verified) Mon, 05/11/2026 – 12:10 Case ID 24-00307 Forum FINRA Document Type Award Claimants Kathy Apostal Peter Apostal Respondents Raymond James Financial Services, Inc. Wells Fargo Clearing Services, LLC Matthew Wilkes FSIC Trustfirst Hearing Site Chicago, IL Award Document 24-00307.pdf Documentum DocID ca9465a3 Related Content Off Claimant Representatives Kevin D. Galbraith Respondent […]
Thousands of DICOM servers exposed due to shameful lack of basic security measures
From the way-too-slow-learning-curve dept. Steve Alder reports: Healthcare organizations are exposing a vast amount of patient data by failing to implement even basic security measures for DICOM servers, according to a recent Trend Micro TrendAI analysis. TrendAI identified thousands of internet-facing DICOM servers belonging to hundreds of entities. The lack of security protections puts patient… […]
Hackers Used AI to Develop First Known Zero-Day 2FA Bypass for Mass Exploitation
Google on Monday disclosed that it identified an unknown threat actor using a zero-day exploit that it said was likely developed with an artificial intelligence (AI) system, marking the first time the technology has been put to use in the wild in a malicious context for vulnerability discovery and exploit generation. The activity is said […]
Why we use CAPTCHAs, (Mon, May 11th)
A few months ago, I implemented Cloudflare’s Turnstile CAPTCHA on some pages. The reason for implementing these CAPTCHAs is obvious: Bots make up a large percentage of traffic and affect site performance.
Lyrie.ai Joins First Batch of Anthropic’s Cyber Verification Program
Dubai-founded OTT Cybersecurity LLC also unveils the Agent Trust Protocol (ATP), the first open cryptographic standard for AI agent identity, scope, and action verification — slated for IETF submission. OTT Cybersecurity LLC, the company behind Lyrie.ai, today announced two milestones that together position the company as foundational infrastructure for the agentic AI era: acceptance into […]
Google discovers weaponized zero-day exploits created with AI
The Google Threat Intelligence Group (GTIG) today released evidence of a zero-day exploit developed by a cybercriminal group with the help of AI. It marks the first time the security research group has identified what it believes to be an AI-crafted zero-day exploit in the wild. While evidence of threat actors using AI models for […]
⚡ Weekly Recap: Linux Rootkit, macOS Crypto Stealer, WebSocket Skimmers and More
Rough Monday. Somebody poisoned a trusted download again, somebody else turned cloud servers into public housing, and a few crews are still getting into boxes with bugs that should’ve died years ago — the same old holes, same lazy access paths, same “how the hell is this still open” feeling. One report this week basically […]
Korea’s child rights agency data mishandling exposes a lot of sensitive and personal info
Jung Da-hyun reports: A recent data breach at the National Center for the Rights of the Child (NCRC), exposing sensitive personal records of adoptees, is drawing criticism from overseas adoptee groups and raising questions about the agency’s credibility. The breach, which the NCRC said occurred between April 30 and May 2, came to light when… […]
Your Purple Team Isn't Purple — It's Just Red and Blue in the Same Room
Defending a network at 2 am looks a lot like this: an analyst copy-pasting a hash from a PDF into a SIEM query. A red team script is being rewritten by hand so the blue team can use it. A patch waiting on a change-approval window that’s longer than the exploitation window itself. Nobody in […]
Over 500 Organizations Hit in Years-Long Phishing Campaign
Victims span across the aviation, critical infrastructure, energy, logistics, public administration, and technology sectors. The post Over 500 Organizations Hit in Years-Long Phishing Campaign appeared first on SecurityWeek.
Resurrected ‘Crimenetwork’ Marketplace Taken Down, Administrator Arrested
The second iteration of the German-speaking online crime marketplace had over 22,000 users and more than 100 sellers. The post Resurrected ‘Crimenetwork’ Marketplace Taken Down, Administrator Arrested appeared first on SecurityWeek.
New ‘Dirty Frag’ Linux Vulnerability Possibly Exploited in Attacks
Also called Copy Fail 2 and tracked as CVE-2026-43284 and CVE-2026-43500, the exploit was disclosed before a patch was released. The post New ‘Dirty Frag’ Linux Vulnerability Possibly Exploited in Attacks appeared first on SecurityWeek.
Canvas System Is Online After a Cyberattack Disrupted Thousands of Schools
Tens of thousands of students studying for final exams around the world have regained access to a key online learning system after a cyberattack had earlier knocked it offline. The post Canvas System Is Online After a Cyberattack Disrupted Thousands of Schools appeared first on SecurityWeek.
Checkmarx Jenkins AST Plugin Compromised in Supply Chain Attack
A malicious version of the plugin was published to the Jenkins Marketplace late last week. The post Checkmarx Jenkins AST Plugin Compromised in Supply Chain Attack appeared first on SecurityWeek.
SailPoint Discloses GitHub Repository Hack
The incident occurred on April 20 and did not affect customer data in the company’s production and staging environments. The post SailPoint Discloses GitHub Repository Hack appeared first on SecurityWeek.
AI security is repeating endpoint security’s biggest mistake
The security industry is experiencing déjà vu, and most teams haven’t recognized it yet. If you were in the trenches during the early 2000s, you remember the antivirus arms race. IT teams buried under signature updates. Configuration baselines checked obsessively. Patch cycles treated as the primary defense. Meanwhile, attackers pivoted. They wrote malware that matched […]
8 guiding principles for reskilling the SOC for agentic AI
At DXC Technology, global CISO Mike Baker has established one of the largest agentic security operation centers (SOCs) in the world. To upskill the workforce as part of this journey, he embedded experts from agentic SOC vendor 7AI within his security teams. When Damon McDougald, global cybersecurity services lead at Accenture, wanted to retrain his […]
1,800+ MCP servers exposed without authentication: How zero trust can secure the AI agent revolution
We find ourselves teetering upon a precipice of our own unwitting construction, and the vertiginous depth of our collective negligence ought to give every security practitioner profound pause. In our headlong rush to deploy AI agents across enterprise environments, we have erected an infrastructure so thoroughly unfortified that it beggars belief. The Model Context Protocol, […]
Fake OpenAI Privacy Filter Repo Hits #1 on Hugging Face, Draws 244K Downloads
A malicious Hugging Face repository managed to take a spot in the platform’s trending list by impersonating OpenAI’s Privacy Filter open-weight model to deliver a Rust-based information stealer to Windows users. The project, named Open-OSS/privacy-filter, masqueraded as its legitimate counterpart, released by OpenAI late last month (openai/privacy-filter), including copying the entire
ISC Stormcast For Monday, May 11th, 2026 https://isc.sans.edu/podcastdetail/9926, (Mon, May 11th)
Post Content
YARA-X 1.16.0 Release, (Sun, May 10th)
YARA-X’s 1.16.0 release brings 4 improvements and 4 bugfixes.
A government contractor hired twin brothers who were convicted felons. A year later, it regretted it.
In May 2015, DataBreaches reported that on April 30, 2015, the Department of Justice had announced the indictment of twin brothers Muneeb and Sohaib Akhter of Virginia. The twins. who were 23 years old, were indicted on charges of aggravated identity theft, conspiracy to commit wire fraud, conspiracy to access a protected computer without authorization,… […]
Ollama Out-of-Bounds Read Vulnerability Allows Remote Process Memory Leak
Cybersecurity researchers have disclosed a critical security vulnerability in Ollama that, if successfully exploited, could allow a remote, unauthenticated attacker to leak its entire process memory. The out-of-bounds read flaw, which likely impacts over 300,000 servers globally, is tracked as CVE-2026-7482 (CVSS score: 9.1). It has been codenamed Bleeding Llama by Cyera. Ollama is a
AI Firm Braintrust Prompts API Key Rotation After Data Breach
Hackers accessed one of the company’s AWS accounts and compromised AI provider secrets stored in Braintrust. The post AI Firm Braintrust Prompts API Key Rotation After Data Breach appeared first on SecurityWeek.
Polish Security Agency Reports ICS Breaches at Five Water Treatment Plants
The hackers gained the ability to modify equipment operational parameters, creating a direct risk to the public water supply. The post Polish Security Agency Reports ICS Breaches at Five Water Treatment Plants appeared first on SecurityWeek.
In Other News: Train Hacker Arrested, PamDOORa Linux Backdoor, New CISA Director Frontrunner
Other noteworthy stories that might have slipped under the radar: US gov targets 72-hour patch cycles, malware uses Windows Phone Link to steal OTPs, spy operation targets Eurasian drone industry. The post In Other News: Train Hacker Arrested, PamDOORa Linux Backdoor, New CISA Director Frontrunner appeared first on SecurityWeek.
cPanel, WHM Release Fixes for Three New Vulnerabilities — Patch Now
cPanel has released updates to address three vulnerabilities in cPanel and Web Host Manager (WHM) that could be exploited to achieve privilege escalation, code execution, and denial-of-service. The list of vulnerabilities is as follows – CVE-2026-29201 (CVSS score: 4.3) – An insufficient input validation of the feature file name in the “feature::LOADFEATUREFILE” adminbin call that […]
25-02095.pdf
25-02095.pdf Anonymous (not verified) Fri, 05/08/2026 – 18:40 Case ID 25-02095 Forum FINRA Document Type Award Claimants Kerrie Coe Respondents Cetera Investment Services, LLC. Neutrals James R. McGuone Leah Murray Albert Tina E. Patterson Hearing Site Indianapolis, IN Award Document 25-02095.pdf Documentum DocID 0f7f3de7 Award Date Official Fri, 05/08/2026 – 12:00 Related Content Off Claimant […]
Five new holes, one exploited, found in Ivanti Endpoint Manager Mobile
The five new vulnerabilities discovered in Ivanti’s on-premises mobile endpoint management solution are a “classic example of the legacy trap” that CSOs must avoid, says an expert. “Patch today to survive the weekend,” said Robert Enderle of the Enderle Group, “but start planning your exit from legacy MDM as soon as possible.” He was commenting […]
25-01342.pdf
25-01342.pdf Anonymous (not verified) Fri, 05/08/2026 – 16:20 Case ID 25-01342 Forum FINRA Document Type Award Claimants Timothy Hynes PCTH Investments LLC Respondents Ronald Cameron Neutrals Allan R. Lazor Hearing Site Little Rock, AR Award Document 25-01342.pdf Documentum DocID 6710f88e Award Date Official Fri, 05/08/2026 – 12:00 Related Content Off Claimant Representatives Marshall S. Ney […]
25-01426.pdf
25-01426.pdf Anonymous (not verified) Fri, 05/08/2026 – 16:10 Case ID 25-01426 Forum FINRA Document Type Award Claimants Michael Leslie Respondents Merrill Lynch Pierce Fenner & Smith Inc. Neutrals Thomas E Kopil Hearing Site Philadelphia, PA Award Document 25-01426.pdf Documentum DocID 49f5f235 Award Date Official Thu, 05/07/2026 – 12:00 Related Content Off Claimant Representatives Alex Padla […]
오픈AI·앤트로픽, SI 영역 넘본다…엔터프라이즈 AI 경쟁 ‘구현 영역’으로
오픈AI와 앤트로픽은 합작 투자와 인수 협상을 통해 전문 서비스 영역으로 사업 범위를 확장하며, 기존 시스템 통합 기업이 맡아온 구현 역할에 한층 더 가까이 다가가고 있다. 로이터의 5일 보도에 따르면, 두 AI 기업과 연계된 합작사는 기업의 AI 도입을 지원하는 서비스 업체 인수를 논의해 왔으며, 이 가운데 오픈AI 측은 3건의 협상에서 상당한 진척을 이룬 것으로 알려졌다. 또한 […]
“채용이 곧 공격 경로”…AI 악용한 가짜 IT 인력, 기업 내부 위협으로 확산
최근 몇 년 사이 가짜 IT 인력을 채용하는 문제는 점점 심각해지고 있지만, 이를 공개적으로 인정하려는 기업은 많지 않다. 포춘 500 기업부터 중소 조직에 이르기까지 원격 채용 방식이 악용되면서, 실제 신원이 아닌 인물에게 신뢰 기반 접근 권한이 부여되는 사례가 발생하고 있으며 이는 내부자 위협으로 이어질 수 있다. 추정에 따르면 미국 전역에서 수천 명의 가짜 IT 인력이 […]
The CIO succession gap nobody admits
I have sat with three CIOs in the last two years who wanted to leave their seat and could not. One was being recruited into a larger enterprise role. One was ready to retire. One had been offered a board seat that required stepping down. In every case, the same thing stopped them. When the […]
AI sprawl: Why your productivity trap is about to get expensive
I have seen this movie before. A decade ago, at Tesla, our Finance team faced a data crisis. We had information scattered across accounting, supply chain and delivery systems, all disconnected, all using different structures. The engineering team was rightfully focused on Full Self-Driving (FSD) and manufacturing. So, we did what productivity-hungry teams always do: […]
Your CEO just got AI FOMO. Here are 6 tips on what to do next.
Every CIO I know has had some version of this conversation: their CEO comes back from a golf trip with their buddy, or a conference with peers, and is told AI is about to automate everything at their company, from HR to marketing and finance. No humans in the loop, just AI. The CEO then […]
How to create an effective business continuity plan
Organizations are seeing a more threatening and volatile operating environment. Executives report an increase in risks across multiple areas, including cyber-enabled fraud, phishing, and supply chain disruptions, according to the World Economic Forum’s 2026 Global Cybersecurity Outlook report. At the same time executives are increasingly worried about how artificial intelligence, digital interdependencies, geopolitics, and today’s […]
Cómo elaborar un plan de continuidad del negocio eficaz
Las organizaciones se enfrentan a un entorno operativo cada vez más amenazante y volátil. Los directivos señalan un aumento de los riesgos en múltiples áreas, incluyendo el fraude cibernético, el phishing y las interrupciones en la cadena de suministro, según el informe ‘Global Cybersecurity Outlook 2026’ del Foro Económico Mundial. Al mismo tiempo, a los […]
5 steps for frontier AI readiness
The evolution of frontier AI is reshaping how organizations approach cyber risk. As these highly capable AI models rapidly discover vulnerabilities and develop exploits for them, they are forcing a shift in how businesses evaluate, prioritize, and address areas of exposure. Frontier AI describes a new class of advanced AI systems that can analyze software, […]
Retail AI has a data problem: Here’s how to fix it
After a series of mishaps, retailers are learning the hard way that agentic commerce is shaping up to be harder than expected. When OpenAI launched Instant Checkout last fall, expectations were high. Walmart tested ChatGPT as a checkout channel for about 200,000 products, but found in-chat purchases converted 3X worse than on their own site. Daniel Danker, […]
25-00797.pdf
25-00797.pdf Anonymous (not verified) Fri, 05/08/2026 – 14:40 Case ID 25-00797 Forum FINRA Document Type Award Claimants Patrick Thornton Respondents J.P. Morgan Securities, LLC Neutrals Patricia Ann Tracey Hearing Site Charlotte, NC Award Document 25-00797.pdf Documentum DocID 4a0547e1 Award Date Official Thu, 05/07/2026 – 12:00 Related Content Off Claimant Representatives Jennifer Cox Respondent Representatives Jeffrey […]
TCLBANKER Banking Trojan Targets Financial Platforms via WhatsApp and Outlook Worms
Threat hunters have flagged a previously undocumented Brazilian banking trojan dubbed TCLBANKER that’s capable of targeting 59 banking, fintech, and cryptocurrency platforms. The activity is being tracked by Elastic Security Labs under the moniker REF3076. The malware family is assessed to be a major update of the Maverick, which is known to leverage a worm […]
2021069370604 Cape Securities Inc. CRD 7072 AWC vrp.pdf
2021069370604 Cape Securities Inc. CRD 7072 AWC vrp.pdf Anonymous (not verified) Fri, 05/08/2026 – 11:55 Case ID 2021069370604 Document Number 731385e4 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Fri, 05/08/2026 – 12:00 Related Content Off Attachment 2021069370604 Cape Securities Inc. CRD 7072 AWC vrp.pdf
Fake Call History Apps Stole Payments From Users After 7.3 Million Play Store Downloads
Cybersecurity researchers have discovered fraudulent apps on the official Google Play Store for Android that falsely claimed to offer access to call histories for any phone number, only to trick users into joining a subscription that provided fake data and incurred financial loss. The 28 apps have collectively racked up more than 7.3 million downloads, […]
One size does not fit all — sometimes, victims probably should pay ransom
DataBreaches posted the following opinion piece on LinkedIn this morning in my Dissent Doe, PhD account: Last night, Canvas was restored, and the Instructure leak site listing was removed from the threat actors’ leak site. The listing is still not on the leak site as of this morning. Given ShinyHunters’ practices, this usually indicates that… […]
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2026-42208 BerriAI LiteLLM SQL Injection Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities established the KEV Catalog as a living list of […]
Claude in Chrome is taking orders from the wrong extensions
Anthropic Claude’s Chrome browser extension, known as Claude in Chrome, has a bug that can allow other malicious extensions to hijack it, compromising trusted AI workflows. Researchers at LayerX Security have warned that Claude’s overly trusted browser communication flows can be abused to inject scripts that can potentially hijack the assistant’s capabilities and manipulate browsing […]
Chrome 148 Rolls Out With 127 Security Fixes
The fresh browser update resolves critical-severity integer overflow and use-after-free vulnerabilities. The post Chrome 148 Rolls Out With 127 Security Fixes appeared first on SecurityWeek.
Claude Code OAuth Tokens Can Be Stolen Through Stealthy MCP Hijacking
Mitiga researchers say attackers can silently redirect Claude Code MCP traffic, intercept OAuth tokens, and maintain persistent access to connected SaaS platforms. The post Claude Code OAuth Tokens Can Be Stolen Through Stealthy MCP Hijacking appeared first on SecurityWeek.
Boost Security Raises $4 Million for SDLC Defense Platform
The company is expanding its platform’s capabilities with the acquisition of SecureIQx and Korbit.ai. The post Boost Security Raises $4 Million for SDLC Defense Platform appeared first on SecurityWeek.
Palo Alto Zero-Day Exploited in Campaign Bearing Hallmarks of Chinese State Hacking
The cybersecurity firm has not explicitly accused China of being behind the attack, but the evidence suggests it was. The post Palo Alto Zero-Day Exploited in Campaign Bearing Hallmarks of Chinese State Hacking appeared first on SecurityWeek.
Worries About AI’s Risks to Humanity Loom Over the Trial Pitting Musk Against OpenAI’s Leaders
Musk said that he could have founded OpenAI as a for-profit company, just like the other companies he started or took over. “I deliberately chose this,” he said, “for the public good.” The post Worries About AI’s Risks to Humanity Loom Over the Trial Pitting Musk Against OpenAI’s Leaders appeared first on SecurityWeek.
Ivanti Patches EPMM Zero-Day Exploited in Targeted Attacks
CVE-2026-6973 is a high-severity vulnerability that allows an attacker who has admin privileges to execute arbitrary code. The post Ivanti Patches EPMM Zero-Day Exploited in Targeted Attacks appeared first on SecurityWeek.
Vulnerability in Claude Extension for Chrome Exposes AI Agent to Takeover
Lax extension permissions and improper trust implementation allow attackers to inject prompts in the Claude Chrome extension. The post Vulnerability in Claude Extension for Chrome Exposes AI Agent to Takeover appeared first on SecurityWeek.
Ransomware Group Takes Credit for Trellix Hack
RansomHouse has published several screenshots to demonstrate access to internal Trellix services. The post Ransomware Group Takes Credit for Trellix Hack appeared first on SecurityWeek.
‘PCPJack’ Worm Removes TeamPCP Infections, Steals Credentials
The malware framework targets web applications and cloud environments, including AWS, Docker, Kubernetes, and more. The post ‘PCPJack’ Worm Removes TeamPCP Infections, Steals Credentials appeared first on SecurityWeek.
Cyberattack Hits Canvas System Used by Thousands of Schools as Finals Loom
A system that thousands of schools and universities use went offline due to a cyberattack, creating chaos as students tried to study for finals. The post Cyberattack Hits Canvas System Used by Thousands of Schools as Finals Loom appeared first on SecurityWeek.
Quasar Linux RAT Steals Developer Credentials for Software Supply Chain Compromise
A previously undocumented Linux implant codenamed Quasar Linux RAT (QLNX) is targeting developers’ systems to establish a silent foothold as well as facilitate a broad range of post-compromise functionality, such as credential harvesting, keylogging, file manipulation, clipboard monitoring, and network tunneling. “QLNX targets developers and DevOps credentials across the software supply chain,”
One Missed Threat Per Week: What 25M Alerts Reveal About Low-Severity Risk
The dark secret of enterprise security operations is that defenders have quietly institutionalized the practice of not looking. This is not just anecdotal, but rather backed by a recent report investigating more than 25 million security alerts, including informational and low-severity, across live enterprise environments. The dataset behind these findings includes 10 million monitored
Your CTEM program is probably ignoring MCP. Here’s how to fix it
Model Context Protocol (MCP) is the connective tissue of modern AI tooling and has quietly become one of the most significant blind spots in modern security programs. Like shadow IT before it, shadow AI — especially as it relates to MCP risk — introduces a new class of exposures that security teams lack adequate tooling […]
Pen tests show AI security flaws far more severe than legacy software bugs
Penetration tests of AI-based systems are revealing a greater percentage of high-risk flaws than those discovered in legacy systems. Security consultancy Cobalt’s annual State of Pentesting Report reveals that 32% of all AI and large language model (LLM) findings are rated as high risk — nearly 2.5 times the rate (13%) of severe flaws found […]
Your refresh plan has a CVE blind spot
The conversation is straightforward, but the problem behind it is not. The customer bought servers in 2017 and typically refresh every five to six years. Generally, around the 2022 to 2023 timeframe, they would have looked to buy new. Historically, that is what would have happened. But COVID hit, and there were supply chain constraints […]
New Linux PamDOORa Backdoor Uses PAM Modules to Steal SSH Credentials
Cybersecurity researchers have disclosed details of a new Linux backdoor named PamDOORa that’s being advertised on the Rehub Russian cybercrime forum for $1,600 by a threat actor called “darkworm.” The backdoor is designed as a Pluggable Authentication Module (PAM)-based post-exploitation toolkit that enables persistent SSH access by means of a magic password and specific TCP […]
Another Universal Linux Local Privilege Escalation (LPE) Vulnerability: Dirty Frag, (Fri, May 8th)
Less than two weeks after the public disclosure of the Copy Fail vulnerability (CVE-2026-31431), another local privilege escalation (LPE) vulnerability in the Linux kernel has been revealed. Referred to as “Dirty Frag,” this vulnerability was discovered and reported by Hyunwoo Kim (@v4bel) [1]. In this diary, I will provide a brief background on Dirty Frag, […]
Linux Kernel Dirty Frag LPE Exploit Enables Root Access Across Major Distributions
Details have emerged about a new, unpatched local privilege escalation (LPE) vulnerability impacting the Linux kernel. Dubbed Dirty Frag, it has been described as a successor to Copy Fail (CVE-2026-31431, CVSS score: 7.8), a recently disclosed LPE flaw impacting the Linux kernel that has since come under active exploitation in the wild. The vulnerability was […]
25-00838.pdf
25-00838.pdf Anonymous (not verified) Fri, 05/08/2026 – 00:45 Case ID 25-00838 Forum FINRA Document Type Award Claimants Christine Baker Respondents Charles Schwab & Co., Inc. Neutrals John B. Kinsellagh Michael Kelley Kenneth Layne Morrill Hearing Site Phoenix, AZ Award Document 25-00838.pdf Documentum DocID e99ffae1 Award Date Official Thu, 05/07/2026 – 12:00 Related Content Off Claimant […]
25-01721.pdf
25-01721.pdf Anonymous (not verified) Fri, 05/08/2026 – 00:45 Case ID 25-01721 Forum FINRA Document Type Award Claimants Nicole Narkus Respondents Edward Jones Neutrals Terry M Lloyd Kirtley M. Thiesmeyer Brett Coonrod Hearing Site Detroit, MI Award Document 25-01721.pdf Documentum DocID 2a5373c7 Award Date Official Thu, 05/07/2026 – 12:00 Related Content Off Claimant Representatives Nicole Narkus […]
25-02071.pdf
25-02071.pdf Anonymous (not verified) Fri, 05/08/2026 – 00:45 Case ID 25-02071 Forum FINRA Document Type Award Claimants Elana Sears Respondents BTIG, LLC Neutrals Robert B. Hansohn Hearing Site Los Angeles, CA Award Document 25-02071.pdf Documentum DocID 4729e38c Award Date Official Thu, 05/07/2026 – 12:00 Related Content Off Claimant Representatives Ryan K. Bakhtiari Respondent Representatives Steve […]
25-02771.pdf
25-02771.pdf Anonymous (not verified) Fri, 05/08/2026 – 00:45 Case ID 25-02771 Forum FINRA Document Type Award Claimants Parnupong Thongsuk Respondents Tastytrade, Inc. Neutrals Mary Mackey Hearing Site San Francisco, CA Award Document 25-02771.pdf Documentum DocID b1065200 Award Date Official Thu, 05/07/2026 – 12:00 Related Content Off Claimant Representatives Parnupong Thongsuk Respondent Representatives Thomas Haskins
Canvas Breach Disrupts Schools & Colleges Nationwide
An ongoing data extortion attack targeting the widely-used education technology platform Canvas disrupted classes and coursework at school districts and universities across the United States today, after a cybercrime group defaced the service’s login page with a ransom demand that threatened to leak data from 275 million students and faculty across nearly 9,000 educational institutions. […]
ISC Stormcast For Friday, May 8th, 2026 https://isc.sans.edu/podcastdetail/9924, (Fri, May 8th)
Post Content
Become a millionaire by bug hunting on Android
Over the past decade, Google has introduced a wide range of bug bounty programs for its software and services. The company has now announced that the reward for individuals who discover vulnerabilities in Android or the Chrome browser is being increased, bringing the maximum reward to $1.5 million. However, reports indicate that you must find […]
13 new critical holes in JavaScript sandbox allow execution of arbitrary code
Thirteen critical vulnerabilities have been found in the vm2 JavaScript sandbox package that could allow an attacker’s code to escape the container and do nasty things to IT environments. As a result, developers using this library in their applications are urged to update the software to the latest version, which is currently 3.11.2. The warnings […]
Developing: ShinyHunters Hacks Instructure Again; Canvas Down (1)
When Instructure did not contact ShinyHunters to negotiate any payment after ShinyHunters attacked them for a second time in April, the threat actors threatened to leak every school’s data, and posted a notice telling schools how to contact them directly to avoid having their data leaked. When Instructure still didn’t contact them after that escalation, … […]
2022073261701 Moody Capital Solutions, Inc. CRD 15989 AWC vrp.pdf
2022073261701 Moody Capital Solutions, Inc. CRD 15989 AWC vrp.pdf Anonymous (not verified) Thu, 05/07/2026 – 17:20 Case ID 2022073261701 Document Number 160b2627 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Thu, 05/07/2026 – 12:00 Related Content Off Attachment 2022073261701 Moody Capital Solutions, Inc. CRD 15989 AWC vrp.pdf
Ollama vulnerability highlights danger of AI frameworks with unrestricted access
A critical vulnerability in Ollama poses a direct risk of sensitive information leaks to more than 300,000 internet-exposed servers, researchers have found. The flaw, tracked as CVE-2026-7482, stems from an out-of-bounds heap read in Ollama’s model quantization pipeline. Ollama is one of the most popular frameworks for running AI models on local hardware. The flaw […]
LinkedIn illegally blocking free accounts from seeing ‘who’s viewed your profile’ data, group alleges
A LinkedIn feature that allows paid subscribers to view a list of visitors to their profile should be made available to all EU users free of charge to comply with the region’s General Data Protection Regulation (GDPR), a legal complaint launched by the None of Your Business (NOYB) digital rights group has claimed. Filed this […]
It took 4 years to master ‘The Knowledge.’ AI just collapsed it in a software update
In London, becoming a licensed cab driver used to require passing an exam called “The Knowledge.” Candidates spent three to four years memorizing 25,000 streets, 100,000 landmarks and thousands of optimal routes. Neuroscience researchers at University College London found that cabbies who passed had measurably enlarged hippocampi from the cognitive load. GPS made the entire […]
Los directores de sistemas de información alertan de que la escasez de talento está frenando la IA en las empresas
La escasez de experiencia ha frenado las iniciativas de IA en muchas organizaciones, pues la limitación de conocimiento de la tecnología ha restringido la capacidad de los profesionales para hacer realidad el potencial de la IA. Según la encuesta State of the CIO 2026 de CIO.com, la falta de talento interno fue el principal reto […]
Coherence: Where leadership and AI success intersect
In an era where AI is accelerating faster than most organizations can absorb, many IT leaders are grappling with how to move quickly without creating fragmentation. For Leigh-Ann Russell, BNY’s CIO and global head of engineering, the answer comes down to a single word: coherence. For Russell, coherence isn’t a slogan. It’s a leadership discipline […]
When AI writes code, it joins the software supply chain
AI tools designed to assist developers are no longer staying in the background. They are starting to shape what actually gets built and deployed. They open pull requests. They modify dependencies. They generate infrastructure templates. They interact directly with repositories and CI/CD pipelines. At some point, this stops being assistance. It becomes participation. And participation […]
8 tips for becoming a more agile IT leader
Our world is spinning so fast that getting off course from intended outcomes can happen quickly. And it isn’t just technology that’s catalyzing change. The business climate, economic conditions, rules of engagement, and even people’s belief systems and behaviors are rapidly shifting to the point that trying to keep up is like chasing a cheetah […]
Why the future of software is no longer written — it is architected, governed and continuously learned
We are entering a decade where software is no longer just an enabler of business — it is the primary mechanism through which intelligence is created, scaled and monetized across the enterprise. For CIOs, this is not another technology cycle. This is a leadership inflection point. Across boardrooms, investor discussions and strategic planning sessions, the conversation is […]
Why a modern data foundation takes more than a new platform
Too many data modernization efforts begin with the platform. The conversation turns to replacing the underlying data environment, moving reporting workloads to the cloud or retiring legacy tooling. Those decisions matter, but in my experience, they are rarely what makes the work hard. What makes the work hard is everything that has built up around […]
The inference imperative: Why running AI is harder than building it
Enterprises have made significant progress in building artificial intelligence capabilities. Access to models, tools, and platforms has expanded rapidly, lowering the barrier to entry for experimentation. Yet many organizations are discovering that building AI is only the first step. Running it at scale is where the real challenge begins. The difficulty is not in creating […]
Why modernization is defining the next decade of cloud
Cloud adoption is no longer the differentiator it once was. Over the past decade, enterprises have moved aggressively to the cloud to improve scalability, reduce infrastructure constraints, and accelerate innovation. Today, most organizations operate in hybrid or multicloud environments, and cloud has become the baseline rather than a competitive advantage. What separates leaders now is […]
From AI investment to innovation: What it takes to deliver real business impact
As organizations continue to invest heavily in AI, many CIOs are still working to understand how those investments translate into measurable business impact. At the center of that challenge is a shift in how AI is approached, from isolated experimentation to enterprise-wide execution. In this conversation, Jeff Baker, Technology Managed Services Lead at PwC, shares […]
Ivanti EPMM CVE-2026-6973 RCE Under Active Exploitation Grants Admin-Level Access
Ivanti is warning that a new security flaw impacting Endpoint Manager Mobile (EPMM) has been explored in limited attacks in the wild. The high-severity vulnerability, CVE-2026-6973 (CVSS score: 7.2), is a case of improper input validation affecting EPMM before versions 12.6.1.1, 12.7.0.1, and 12.8.0.1. It allows “a remotely authenticated user with administrative access to achieve […]
PCPJack Credential Stealer Exploits 5 CVEs to Spread Worm-Like Across Cloud Systems
Cybersecurity researchers have disclosed details of a new credential theft framework dubbed PCPJack that targets exposed cloud infrastructure and ousts any artifacts linked to TeamPCP from the environments. “The toolset harvests credentials from cloud, container, developer, productivity, and financial services, then exfiltrates the data through attacker-controlled infrastructure while attempting
One Click, Total Shutdown: The "Patient Zero" Webinar on Killing Stealth Breaches
The hardest part of cybersecurity isn’t the technology, it’s the people. Every major breach you’ve read about lately usually starts the same way: one employee, one clever email, and one “Patient Zero” infection. In 2026, hackers are using AI to make these “first clicks” nearly impossible to spot. If a single laptop gets compromised on […]
PAN-OS RCE Exploit Under Active Use Enabling Root Access and Espionage
Palo Alto Networks has disclosed that threat actors may have attempted to unsuccessfully exploit a recently disclosed critical security flaw as early as April 9, 2026. The vulnerability in question is CVE-2026-0300 (CVSS score: 9.3/8.7), a buffer overflow vulnerability in the User-ID Authentication Portal service of Palo Alto Networks PAN-OS software that could allow an […]
Bots in translation: Can AI really fix SIEM rule sprawl across vendors?
Enterprises migrating between SIEM platforms often have to manually rewrite detection rules because vendors such as Splunk, Microsoft Sentinel, IBM QRadar, and Google Chronicle use different query languages and data models. Researchers now say AI may be able to automate much of that work, though security experts remain divided over whether the problem really requires […]
MAXHUB Pivot Client Application
View CSAF Summary Successful exploitation of this vulnerability may enable an attacker to access tenant email addresses and associated information in cleartext or cause a denial-of-service condition. The following versions of MAXHUB Pivot client application are affected: MAXHUB Pivot client application CVSS Vendor Equipment Vulnerabilities v3 7.3 MAXHUB MAXHUB Pivot client application Use of a […]
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2026-6973 Ivanti Endpoint Manager Mobile (EPMM) Improper Input Validation Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing the […]
ThreatsDay Bulletin: Edge Plaintext Passwords, ICS 0-Days, Patch-or-Die Alerts and 25+ New Stories
Bad week. Turns out the easiest way to get hacked in 2026 is still the same old garbage: shady packages, fake apps, forgotten DNS junk, scam ads, and stolen logins getting dumped into Discord channels like it’s normal. Some of these attack chains don’t even feel sophisticated anymore. More like some tired guy with a […]
Cybersecurity Stolen ChipSoft claims patient data confirmed destroyed following cyberattack
There’s an update to the ChipSoft ransomware attack. DigitalShield reports that although ChipSoft hasn’t revealed whether it paid Embargo ransom, it did disclose that some negotiations had occurred. One of the most striking elements of the case is the company’s claim about the deletion of the stolen data. According to the company, the destruction has been… […]
Critical Palo Alto Networks software bug hits exposed firewalls
Palo Alto Networks is warning customers about a critical buffer overflow vulnerability affecting its PAN-OS user-ID authentication portal that is already being exploited in the wild. The flaw allows attackers to execute arbitrary code with root privileges on exposed firewalls, the company said in a security advisory. PAN-OS is the software that runs all Palo […]
Romanian Man Extradited to US for Role in Hacking Scheme 17 Years Ago
Gavril Sandu, 53, was indicted in 2017, but was arrested and extradited to the United States only in 2026. The post Romanian Man Extradited to US for Role in Hacking Scheme 17 Years Ago appeared first on SecurityWeek.
Iranian APT Intrusion Masquerades as Chaos Ransomware Attack
Likely perpetrated by MuddyWater, the attack combined social engineering, persistence, credential harvesting, and data theft. The post Iranian APT Intrusion Masquerades as Chaos Ransomware Attack appeared first on SecurityWeek.
Herd Security Raises $3 Million for AI-Powered Training Platform
The startup will invest in expanding its training categories, optimizing video generation, and growing its partnership ecosystem. The post Herd Security Raises $3 Million for AI-Powered Training Platform appeared first on SecurityWeek.
Autonomous Offensive Security Firm XBOW Raises $35 Million
The company raised another $35 million as an extension to its previously announced Series C funding round. The post Autonomous Offensive Security Firm XBOW Raises $35 Million appeared first on SecurityWeek.
Claude AI Guided Hackers Toward OT Assets During Water Utility Intrusion
Dragos has published a report describing how threat actors used Claude AI in an attack on a water and drainage utility in Mexico. The post Claude AI Guided Hackers Toward OT Assets During Water Utility Intrusion appeared first on SecurityWeek.
Gemini CLI Vulnerability Could Have Led to Code Execution, Supply Chain Attack
Attackers could inject prompts into a GitHub issue and take over the AI agent designed to automatically triage the issue. The post Gemini CLI Vulnerability Could Have Led to Code Execution, Supply Chain Attack appeared first on SecurityWeek.
Day Zero Readiness: The Operational Gaps That Break Incident Response
Having an incident response retainer, or even a pre-approved external incident response firm, is not the same as being ready for an incident. A retainer means someone will answer the phone. Operational readiness determines whether that team can do meaningful work the moment they do. That distinction matters far more than many organizations realize. In […]
PyPI Packages Deliver ZiChatBot Malware via Zulip APIs on Windows and Linux
Cybersecurity researchers have discovered three packages on the Python Package Index (PyPI) repository that are designed to stealthily deliver a previously unknown malware family called ZiChatBot on Windows and Linux systems. “While these wheel packages do implement the features described on their PyPI web pages, their true purpose is to covertly deliver malicious files,” Kaspersky
CISOs: Align cyber risk communication with boardroom psychology
By now, executive boards across industries understand that cyberattacks can be costly. What they often lack, however, is a clear view of which risks pose the biggest threat to their business and why certain investments need to rise to the top. Many security leaders lose traction at that point. The challenge is less about sounding […]
Ten years later, has the GDPR fulfilled its purpose?
This year marks the 10th anniversary of the EU’s adoption of the General Data Protection Regulation, which became mandatory for all companies beginning on May 25, 2018. The aim of the GDPR was simple, but important: to improve individuals’ control over their personal data. This regulation replaced Directive 95/46/EC with the clear purpose of unifying data […]
vm2 Node.js Library Vulnerabilities Enable Sandbox Escape and Arbitrary Code Execution
A dozen critical security vulnerabilities have been disclosed in the vm2 Node.js library that could be exploited by bad actors to break out of the sandbox and execute arbitrary code on susceptible systems. vm2 is an open-source library used to run untrusted JavaScript code inside a secure sandbox by intercepting and proxying JavaScript objects to […]
US government agency to safety test frontier AI models before release
The Center for AI Standards and Innovation (CAISI), a division of the US Department of Commerce, has signed agreements with Google DeepMind, Microsoft, and xAI that would give the agency the ability to vet AI models from these organizations and others prior to their being made publicly available. According to a release from CAISI, which […]
ISC Stormcast For Thursday, May 7th, 2026 https://isc.sans.edu/podcastdetail/9922, (Thu, May 7th)
Post Content
An Adaptive Cyber Analytics UI for Web Honeypot Logs [Guest Diary], (Wed, May 6th)
[This is a Guest Diary by Eric Roldan, an ISC intern as part of the SANS.edu BACS program]
Pace University Elisabeth Haub School of Law Comment On Regulatory Notice 26-06
Pace University Elisabeth Haub School of Law Comment On Regulatory Notice 26-06 fnrw-backend Wed, 05/06/2026 – 18:32 Jill Gross Gross, Prof. Jill I. <jgross@law.pace.edu> Pace University Elisabeth Haub School of Law Regulatory Notice 26-06 Core Official Date Wed, 05/06/2026 – 12:00 Comment File Pace University Elisabeth Haub School of Law_Jill Gross_26-06_5.6.2026.pdf
University of Pittsburgh Securities Arbitration Clinic Comment On Section V: Request for Comments
University of Pittsburgh Securities Arbitration Clinic Comment On Section V: Request for Comments fnrw-backend Wed, 05/06/2026 – 18:32 Anonymous null null Nancy Alemañy Alvarez <NMA63@pitt.edu> University of Pittsburgh Securities Arbitration Clinic Section V: Request for Comments Core Official Date Wed, 05/06/2026 – 12:00 Comment File Univ of Pittsburgh Securities Arbitration Clinic_5.6.2026_0.pdf
‘GothFerrari’ Sentenced to 78 Months in Prison for Role in Massive Cryptocurrency Heist
He’s 20 years old and has just been sentenced to 6 1/2 years in prison. The U.S. Attorney’s Office for the District of Columbia announced today: WASHINGTON – Marlon Ferro, 20, of Santa Ana, California, was sentenced today in U.S. District Court to 78 months in prison in connection with his role in a sprawling social engineering conspiracy that stole well over $250 million… […]
Mirai-Based xlabs_v1 Botnet Exploits ADB to Hijack IoT Devices for DDoS Attacks
Cybersecurity researchers have exposed a new Mirai-derived botnet that self-identifies as xlabs_v1 and targets internet-exposed devices running Android Debug Bridge (ADB) to enlist them in a network capable of carrying out distributed denial-of-service (DDoS) attacks. Hunt.io, which detailed the malware, said it made the discovery after identifying an exposed directory on a Netherlands-hosted
The AI economy needs a new vocabulary
Technology is evolving faster than the language we use to describe it. As a result, people are often talking past each other about what software, AI and automation are. These are treated as single categories when in reality they contain several fundamentally different disciplines and economic models. And when reality changes faster than our language, […]
The AI assessment gap: Why your hiring process can’t find the talent you need
The next time someone on your team says, ‘hire an AI engineer,’ stop the conversation. That title is too vague because it fails to account for critical differences in engineering strengths. Instead, companies need to decide specifically what they need. Is it someone to rapidly prototype AI solutions? Or someone to build the solution that […]
How UKG puts AI to work for frontline employees
As organizations rebrand themselves as AI companies, most of the conversation is focused on knowledge workers rather than the people in retail, manufacturing, and healthcare who can benefit from AI just as much. Prakash Kota, CIO of UKG, one of the largest HR tech platforms in the market, which delivers a workforce operating platform utilized […]
AI is spreading decision-making, but not accountability
On a holiday weekend, when most of a company is offline, a critical system fails. An AI-driven workflow stalls, or worse, produces flawed decisions at scale that misprice products or expose sensitive data. In that moment, organizational theory disappears and the question of who’s responsible is immediately raised. As AI moves from experimentation into production, […]
OpenAI, Anthropic expand services push, signaling new phase in enterprise AI race
OpenAI and Anthropic are expanding their reach into professional services through joint ventures and acquisition talks, moving model providers closer to implementation roles traditionally held by systems integrators. Joint ventures tied to the two AI companies have held talks to acquire services companies that help businesses deploy AI, with OpenAI’s venture in advanced stages on […]
AI FOMO: When AI Is the wrong answer to the right problem
Most AI project failures I have seen do not announce themselves cleanly. There is rarely a moment where someone stands up and admits to making the wrong call. Instead, the project quietly underdelivers. The team makes constant adjustments; leadership loses confidence and eventually the whole thing is filed away under “we tried AI and it […]
I gave our developers an AI coding assistant. The security team nearly mutinied
I’ve sat in enough risk meetings to know the sound a bad surprise makes before anyone names it. It usually starts with a pause. Then a throat gets cleared. Then someone says, “We may need to bring the CISO into this.” That happened over a developer tool. Not a breach. Not a regulator. Not ransomware […]
Agentic AI for marketing: Reimagine end-to-end customer experiences
Agentic AI represents the next phase of marketing performance, enabling organizations to connect insights, decisions, and execution across the customer experience. As customer journeys become more complex and expectations rise, enterprises need systems that can operate across data, content, and workflows in a coordinated way. Generative AI has dramatically sped up how marketing teams produce […]
Anthropic’s financial agents expose forward-deployed engineers as new AI limiting factor
When financial tech vendor FIS announced its new AI agent for detecting financial crimes on Tuesday, it made much of its embedding of a team of forward deployed engineers (FDEs) from Anthropic to make it happen. It’s just one of the dozen or so companies working with Anthropic on developing agents for financial services using […]
Intel, behind in AI chips, bets on quantum and neuromorphic processors
Intel for years chopped critical products including CPUs, GPUs and networking gear to cut corporate fat and get back into shape. Many cuts pre-date the appointment last year of Lip-Bu Tan as CEO. Now, Tan is placing a long-term bet beyond the current crop of AI chips and doubling down on quantum processors and neuromorphic […]
25-02661.pdf
25-02661.pdf Anonymous (not verified) Wed, 05/06/2026 – 13:05 Case ID 25-02661 Forum FINRA Document Type Award Claimants Martha Gaudet Respondents Fidelity Brokerage Services LLC Neutrals Patrick Leo Kennedy Hearing Site Boston, MA Award Document 25-02661.pdf Documentum DocID e26964ea Award Date Official Tue, 05/05/2026 – 12:00 Related Content Off Claimant Representatives Martha Gaudet Respondent Representatives Brooke […]
Missouri regulators escalate pressure on Conduent over data breach potentially affecting millions
Sarah Motter reports: Missouri regulators say a major national vendor is stonewalling their investigation into a cybersecurity breach that could affect millions of consumers. The Missouri Department of Commerce and Insurance now says it is escalating its response to the cybersecurity breach at Conduent Business Services. Conduent is a national vendor that handles sensitive insurance… […]
Iranian state-backed spies pose as ransomware slingers in false flag attacks
An Iranian state-sponsored espionage group is pretending to be a regular ransomware gang in a new wave of ransomware attacks targeting enterprises. APT group MuddyWater (aka Seedworm) is masquerading as the Chaos ransomware-as-a-service group to confuse incident response and mask its spying and cyber-sabotage, according to research by security vendor Rapid7. The attacks — geared […]
When Your Vendor’s Breach Becomes Your Lawsuit: Privacy Risk Lessons from Recent Bank Litigation
Nancy Eff Presnell, Gene F. Price, and Matthew R. Schantz write: A recent high-profile incident illustrates the growing litigation and regulatory risks that financial institutions face from vendor-driven data breaches. Within weeks of a national bank confirming a data security incident at a third-party service provider, at least two putative class actions were filed, though… […]
24-02637.pdf
24-02637.pdf Anonymous (not verified) Wed, 05/06/2026 – 09:25 Case ID 24-02637 Forum FINRA Document Type Award Claimants Gihan Fernando Respondents BOK Financial Securities, Inc. Neutrals Kevin R. Zehe Betty Chen Paul J. Burkhart Hearing Site Houston, TX Award Document 24-02637.pdf Documentum DocID 56380b31 Award Date Official Tue, 05/05/2026 – 12:00 Related Content Off Claimant Representatives […]
25-01287.pdf
25-01287.pdf Anonymous (not verified) Wed, 05/06/2026 – 09:25 Case ID 25-01287 Forum FINRA Document Type Award Claimants Eduardo De Ocampo Respondents Robinhood Financial, LLC. Neutrals Jonathan Polland Hearing Site San Francisco, CA Award Document 25-01287.pdf Documentum DocID 5822883e Award Date Official Tue, 05/05/2026 – 12:00 Related Content Off Claimant Representatives Eduardo De Ocampo Respondent Representatives […]
MuddyWater Uses Microsoft Teams to Steal Credentials in False Flag Ransomware Attack
The Iranian state-sponsored hacking group known as MuddyWater (aka Mango Sandstorm, Seedworm, and Static Kitten) has been attributed to a ransomware attack in what has been described as a “false flag” operation. The attack, observed by Rapid7 in early 2026, has been found to leverage social engineering techniques via Microsoft Teams to initiate the infection […]
The Hacker News Launches 'Cybersecurity Stars Awards 2026' — Submissions Now Open
For nearly 20 years, we at The Hacker News have mostly told scary stories about cyberspace — big hacks, broken systems, and new threats. But behind every headline, there’s a quieter, better story. It’s the story of leaders making tough calls under pressure, teams building smarter defenses, and security products that keep hunting threats 24/7 […]
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2026-0300 Palo Alto Networks PAN-OS Out-of-bounds Write Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk […]
New malware turns Linux systems into P2P attack networks
Attackers have found a new way to turn Linux systems into stealthy supply chain distribution hubs that are resistant to takedowns. Researchers from Trend Micro have disclosed a new malware framework, dubbed Quasar Linux or QLNX, describing it as a modular Linux remote access trojan (RAT). But what sets the campaign apart is the malware […]
DeFi Investors Pull $14 Billion Following Cyberattacks
PYMNTS reports: Cryptocurrency investors are reportedly exiting the decentralized finance (DeFi) space following two high-profile hacks. Close to $14 billion has been pulled from DeFi projects in recent weeks, the Financial Times (FT) reported Wednesday (May 6), citing the data firm DefiLlama. This came after hackers tied to the North Korean government stole $290 million from the KelpDAO platform and used… […]
Vimeo data breach exposes personal information of 119,000 people
Sergiu Gatlan reports: The ShinyHunters extortion gang stole personal information belonging to over 119,000 people after hacking the Vimeo online video platform in April, according to data breach notification service Have I Been Pwned. Vimeo is a video hosting and streaming platform publicly traded on the Nasdaq stock market, with over 300 million registered users… […]
Critical, High-Severity Vulnerabilities Patched in Apache MINA, HTTP Server
The most severe of these security defects could allow remote attackers to execute arbitrary code. The post Critical, High-Severity Vulnerabilities Patched in Apache MINA, HTTP Server appeared first on SecurityWeek.
Critical Remote Code Execution Vulnerability Patched in Android
CVE-2026-0073 affects Android’s System component and it can be exploited without any user interaction. The post Critical Remote Code Execution Vulnerability Patched in Android appeared first on SecurityWeek.
Critical Bug Could Expose 300,000 Ollama Deployments to Information Theft
Dubbed Bleeding Llama, the heap out-of-bounds read issue can be exploited remotely, without authentication. The post Critical Bug Could Expose 300,000 Ollama Deployments to Information Theft appeared first on SecurityWeek.
Hacker Conversations: Joey Melo on Hacking AI
AI red team specialist details his methods for manipulating AI guardrails through jailbreaking and data poisoning, helping developers harden machine learning models. The post Hacker Conversations: Joey Melo on Hacking AI appeared first on SecurityWeek.
Microsoft Warns of Sophisticated Phishing Campaign Targeting US Organizations
The malicious emails claim to contain a conduct report and lure victims to a Microsoft phishing website that leverages AitM. The post Microsoft Warns of Sophisticated Phishing Campaign Targeting US Organizations appeared first on SecurityWeek.
Palo Alto Networks to Patch Zero-Day Exploited to Hack Firewalls
CVE-2026-0300 affects the Captive Portal service of PAN-OS software on PA and VM series firewalls. The post Palo Alto Networks to Patch Zero-Day Exploited to Hack Firewalls appeared first on SecurityWeek.
Oracle Debuts Monthly Critical Security Patch Updates
Containing fixes for critical-severity vulnerabilities, the monthly rollouts will focus on addressing priority issues faster. The post Oracle Debuts Monthly Critical Security Patch Updates appeared first on SecurityWeek.
Government, Scientific Entities Hit via Daemon Tools Supply Chain Attack
While trojanized Daemon Tools versions were installed worldwide, a sophisticated backdoor was dropped only on a dozen systems. The post Government, Scientific Entities Hit via Daemon Tools Supply Chain Attack appeared first on SecurityWeek.
Sophisticated Quasar Linux RAT Targets Software Developers
The persistent, evasive implant provides remote access, surveillance, and credential exfiltration capabilities. The post Sophisticated Quasar Linux RAT Targets Software Developers appeared first on SecurityWeek.
CISA: Critical Infrastructure Must Master Isolation, Recovery
The agency has issued guidance to help critical infrastructure operators prepare for cyberattacks by foreign threat actors. The post CISA: Critical Infrastructure Must Master Isolation, Recovery appeared first on SecurityWeek.
Your AI Agents Are Already Inside the Perimeter. Do You Know What They're Doing?
Analysts recently confirmed what identity security teams have quietly feared: AI agents are being deployed faster than enterprises can govern them. In their inaugural Market Guide for Guardian Agents, Gartner states that “enterprise adoption of AI agents is accelerating, outpacing maturity of governance policy controls.” Enterprise leaders can request access to the Gartner Market Guide […]
Google's Android Apps Get Public Verification to Stop Supply Chain Attacks
Google has announced expanded Binary Transparency for Android as a way to safeguard the ecosystem from supply chain attacks. “This new public ledger ensures the Google apps on your device are exactly what we intended to build and distribute,” Google’s product and security teams said. The initiative builds upon the foundation of Pixel Binary Transparency, […]
Poisoned truth: The quiet security threat inside enterprise AI
As enterprises rush to deploy internal LLMs, AI copilots, and autonomous agents, most security conversations focus on familiar threats: prompt injection, jailbreaks, model abuse, and data exfiltration. But some security leaders argue a quieter risk deserves far more attention: what happens when the model’s understanding of reality itself becomes corrupted. This problem is broadly described […]
Train like you fight: Why cyber operations teams need no-notice drills
St. Michael’s Hospital in Toronto recently executed a full Code Orange simulation: A mass casualty emergency protocol requiring the activation of every clinical and operational team across the hospital. As a Level 1 trauma centre, it conducts large-scale exercises involving teams across the entire hospital: Emergency, surgery, communications, administration. The exercise is not a compliance […]
Windows Phone Link Exploited by CloudZ RAT to Steal Credentials and OTPs
Cybersecurity researchers have disclosed details of an intrusion that involved the use of a CloudZ remote access tool (RAT) and a previous undocumented plugin dubbed Pheno with the aim of facilitating credential theft. “According to the functionalities of the CloudZ RAT and Pheno plugin, this was with the intention of stealing victims’ credentials and potentially […]
Palo Alto PAN-OS Flaw Under Active Exploitation Enables Remote Code Execution
Palo Alto Networks has released an advisory warning that a critical buffer overflow vulnerability in its PAN-OS software has been exploited in the wild. The vulnerability, tracked as CVE-2026-0300, has been described as a case of unauthenticated remote code execution. It carries a CVSS score of 9.3 if the User-ID Authentication Portal is configured to […]
Risky Business #836 -- You can't patch the bugpocalypse
On this week’s show, Patrick Gray and James Wilson are joined by special guest co-host Brad Arkin. They discuss the week’s cybersecurity news, including: The US Government says we just have to patch faster, but… Bugs in cPanel, MoveIt and all Linux distributions this week show that patching alone isn’t enough James gets mad about […]
Die besten DAST- & SAST-Tools
Tools für Dynamic und Static Application Security Testing helfen Entwicklern, ihren Quellcode zu härten. Wir zeigen Ihnen die besten Tools zu diesem Zweck. Chim | shutterstock.com Die Softwarelieferkette – respektive ihre Schwachstellen – haben in den vergangenen Jahren für viel Wirbel gesorgt. Ein besonders schlagzeilenträchtiges Beispiel ist der Angriff auf den IT-Dienstleister SolarWinds, bei dem […]
ISC Stormcast For Wednesday, May 6th, 2026 https://isc.sans.edu/podcastdetail/9920, (Wed, May 6th)
Post Content
NYC Public Schools Lack Central Inventory to Track Vendors Used By Schools — NYS Auditor
Audit conducted by NYS Comptroller’s Office between 2020-2025 found multiple concerns leaving students and employees at risk of privacy and data security breaches. The auditor also criticized the city for failing to cooperate in a timely manner with the auditor’s requests for information. In June 2014, a decade after the NYC Education Department had been… […]
2020065124802 Infinity Financial Services CRD 144302 AWC ks.pdf
2020065124802 Infinity Financial Services CRD 144302 AWC ks.pdf Anonymous (not verified) Tue, 05/05/2026 – 18:10 Case ID 2020065124802 Document Number 5f7ce7ea Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Tue, 05/05/2026 – 12:00 Related Content Off Attachment 2020065124802 Infinity Financial Services CRD 144302 AWC ks.pdf
Supply-chain attacks take aim at your AI coding agents
Attackers too are looking to cash in on the AI coding craze, adapting their supply-chain techniques to target coding agents themselves. Many AI agents autonomously scan package registries such as NPM and PyPI for components to integrate into their coding projects, and attackers are beginning to take advantage of this. Bait packages with persuasive descriptions […]
23-01711.pdf
23-01711.pdf Anonymous (not verified) Tue, 05/05/2026 – 17:10 Case ID 23-01711 Forum FINRA Document Type Award Claimants Cynthia Posipanko Respondents James Potoka FSC Securities Corporation James Ransom Potoka d/b/a Legacy Financial Services Group Neutrals George Forest Bingham Joseph J. Dougherty Dimitri Karapelou Hearing Site Philadelphia, PA Award Document 23-01711.pdf Documentum DocID 080c5d6a Award Date Official […]
26-00126.pdf
26-00126.pdf Anonymous (not verified) Tue, 05/05/2026 – 17:10 Case ID 26-00126 Forum FINRA Document Type Award Claimants Parkland Securities, LLC Respondents Donald Dalton Neutrals B. John Dill Hearing Site Boston, MA Award Document 26-00126.pdf Documentum DocID 9d64af34 Award Date Official Tue, 05/05/2026 – 12:00 Related Content Off Claimant Representatives Jonathan M. Sterling Respondent Representatives Donald […]
Edge browser leaves passwords exposed in plain text, says researcher
A Norwegian researcher has identified an issue with Microsoft Edge’s Password Manager that could be a serious concern for businesses. Tom Jøran Sønstebyseter Rønning found that passwords are being saved within the browser in plain text, with the effect that any PC, particularly a shared machine, within an organization is a potential risk. In a […]
CISA mulls new three-day remediation deadline for critical flaws
Experts have mixed reactions to a report that the US Cybersecurity and Infrastructure Security Agency (CISA) is considering reducing the timeline in which government agencies must address critical vulnerabilities from two weeks to only three days. The current 14-day window applies to high-severity flaws dating from 2021 onwards, listed as known to be under exploit […]
The triple squeeze: Why the SaaSpocalypse story you’re hearing is missing the most dangerous part
In early February 2026, nearly $285 billion in market value evaporated from software and related sectors in 48 hours. Atlassian dropped 36% for the month. The iShares Software ETF fell more than 30% from its September 2025 highs. Traders called it the “SaaSpocalypse.” The popular narrative goes like this. AI coding tools have gotten so […]
What is data analytics? Transforming data into better decisions
What is data analytics? Data analytics focuses on gleaning insights from data. It comprises the processes, tools, and techniques of data analysis and management, and its chief aim is to apply statistical analysis and technologies on data to find trends and solve problems. Data analytics has become increasingly important in the enterprise to shape business […]
The fake IT worker problem CIOs can’t ignore
Hiring fake IT workers has been a growing problem in recent years — but it’s often a problem very few want to admit to. From Fortune 500 companies down to smaller organizations, remote hiring practices have been exploited to grant trusted access to individuals who are not who they claim to be creating an insider […]
Cloud modernization is advancing. Utilization isn’t
At Datadog, an observability and security platform for cloud applications, I work on research studies that analyze anonymized infrastructure telemetry from thousands of production environments across Kubernetes, managed container platforms and serverless services across cloud providers. The datasets span multiple cloud providers and billions of workload hours. Much of that work goes into our annual […]
Vibe coding goes enterprise: What you need to know about AI-driven legacy modernization
Google’s CEO says vibe coding makes programming “enjoyable” and “exciting again.” Klarna’s CEO prototypes products in 20 minutes instead of waiting two weeks. Collins Dictionary named “vibe coding” its Word of the Year for 2025. The message seems clear: AI has democratized software development. Just describe what you want in plain English and let AI […]
When the CEO leads the AI initiative
Having been involved in some of the most significant technology-driven business and cultural shifts over the past five decades, including the explosive growth of the internet and the rise of open source, there are parallels from the past that are worth considering in the age of AI. A critical one is the role of the […]
The immutable mountain: Understanding distributed ledgers through the lens of alpine climbing
In modern enterprises, we often default to centralized command-and-control structures. But in high-stakes environments — whether a whiteout on an Andean peak or a volatile global supply chain — centralization is a single point of failure. To manage complexity and risk, we must look to the architecture of the decentralized network. A storm at high […]
Cuenta atrás para presentar candidaturas en España a los CIO 50 Awards
Un año más, vuelve la convocatoria de premios de referencia para distinguir a los mejores directivos de sistemas de información (CIO) en España y los proyectos de TI más innovadores realizados en el país. La iniciativa, conocida como los ‘Oscar de la industria de TI’, forma parte del proyecto global CIO Awards con el que […]
Oracle will patch more often to counter AI cybersecurity threat
Oracle plans to issue security patches for its ERP, database, and other software on a monthly cycle, rather than quarterly, to respond to the increased pace of AI-enabled software vulnerability discovery. Other software vendors, notably Microsoft, SAP, and Adobe, already release patches on a monthly beat, always on the second Tuesday of each month. Oracle, […]
ServiceNow continues its AI transformation with an integrated experience
ServiceNow has unveiled updates to its workflow management platform advancing its redefinition of itself as the “AI control tower for business reinvention” at its Knowledge customer event this week. The AI Control Tower product itself, introduced at last year’s event, gets new integrations with Microsoft Azure, Amazon Web Services (AWS), Google Cloud Platform (GCP) and […]
2024080158101 Blue Ocean ATS CRD 306512 AWC vrp.pdf
2024080158101 Blue Ocean ATS CRD 306512 AWC vrp.pdf Anonymous (not verified) Tue, 05/05/2026 – 13:50 Case ID 2024080158101 Document Number 46afff57 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Mon, 05/04/2026 – 12:00 Related Content Off Attachment 2024080158101 Blue Ocean ATS CRD 306512 AWC vrp.pdf
CISA pushes critical infrastructure operators to prepare to work in isolation
The US Cybersecurity and Infrastructure Security Agency (CISA) has unveiled a new national initiative aimed at helping critical infrastructure operators withstand and recover from major cyberattacks by preparing to operate in isolation from the internet and third-party dependencies. The program, CI Fortify, is designed to ensure that organizations can continue delivering essential services even when […]
26-00200.pdf
26-00200.pdf Anonymous (not verified) Tue, 05/05/2026 – 12:50 Case ID 26-00200 Forum FINRA Document Type Award Claimants Alan Reisfield Respondents UBS Financial Services Inc. Neutrals Patricia Ann Tracey Eric Ross Cromartie Lorrie E Whitfield Hearing Site Jersey City, NJ Award Document 26-00200.pdf Documentum DocID 09d7f487 Award Date Official Mon, 05/04/2026 – 12:00 Related Content Off […]
Critical Apache HTTP/2 Flaw (CVE-2026-23918) Enables DoS and Potential RCE
The Apache Software Foundation (ASF) has released security updates to address several security vulnerabilities in the HTTP Server, including a severe vulnerability that could potentially lead to remote code execution (RCE). The vulnerability, tracked as CVE-2026-23918 (CVSS score: 8.8), has been described as a case of “double free and possible RCE” in the HTTP/2 protocol […]
DAEMON Tools Supply Chain Attack Compromises Official Installers with Malware
A newly identified supply chain attack targeting DAEMON Tools software has compromised its installers to serve a malicious payload, according to findings from Kaspersky. “These installers are distributed from the legitimate website of DAEMON Tools and are signed with digital certificates belonging to DAEMON Tools developers,” Kaspersky researchers Igor Kuznetsov, Georgy Kucherin, Leonid
Oracle will patch more often to counter AI cybersecurity threat
Oracle plans to issue security patches for its ERP, database, and other software on a monthly cycle, rather than quarterly, to respond to the increased pace of AI-enabled software vulnerability discovery. Other software vendors, notably Microsoft, SAP, and Adobe, already release patches on a monthly beat, always on the second Tuesday of each month. Oracle, […]
Cleartext Passwords in MS Edge? In 2026?, (Mon, May 4th)
Yup, that is for real.
China-Linked UAT-8302 Targets Governments Using Shared APT Malware Across Regions
A sophisticated China-nexus advanced persistent threat (APT) group has been attributed to attacks targeting government entities in South America since at least late 2024 and government agencies in southeastern Europe in 2025. The activity is being tracked by Cisco Talos under the moniker UAT-8302, with post-exploitation involving the deployment of custom-made malware families that have […]
ABB B&R PVI
View CSAF Summary ABB became aware of vulnerability in the product versions listed as affected in the advisory. An update is now available that addresses and remediates the vulnerability. An attacker who successfully exploited this vulnerability could read sensitive information in the logging data of the PVI client application. Logging is deactivated by default in […]
Johnson Controls CEM AC2000
View CSAF Summary Successful exploitation of this vulnerability could allow a standard user to escalate privileges on the host machine. The following versions of Johnson Controls CEM AC2000 are affected: CEM AC2000 12.0 (CVE-2026-21661) CEM AC2000 11.0 (CVE-2026-21661) CEM AC2000 10.6 (CVE-2026-21661) CVSS Vendor Equipment Vulnerabilities v3 8.7 Johnson Controls Inc. Johnson Controls CEM AC2000 […]
Hitachi Energy PCM600
View CSAF Summary Hitachi Energy is aware of a vulnerability that affects the Hitachi Energy PCM600 product versions listed in this document. An attacker successfully exploiting this vulnerability can impact integrity of the product. Please refer to the Recommended Immediate Actions for information about the mitigation/remediation. The following versions of Hitachi Energy PCM600 are affected: […]
ABB B&R Automation Runtime
View CSAF Summary ABB became aware of vulnerability in the product versions listed as affected in the advisory. An update is available that resolves a vulnerability. An attacker who successfully exploited this vulnerability could cause the product to stop. The following versions of ABB B&R Automation Runtime are affected: Automation Runtime <6.5, >=6.5, =R4.93 (CVE-2025-11044, […]
ABB B&R Automation Studio
View CSAF Summary ABB became aware of vulnerability in the product versions listed as affected in the advisory. An update is available that resolves a vulnerability. Successful exploitation of this vulnerability may enable an attacker to masquerade as a trusted party when B&R Automation Studio establishes a connection with a server via the ANSL over […]
The Back Door Attackers Know About — and Most Security Teams Still Haven’t Closed
Every AI tool, workflow automation, and productivity app your employees connected to Google or Microsoft this year left something behind: a persistent OAuth token with no expiration date, no automatic cleanup, and in most organizations, no one watching it. Your perimeter controls don’t see it. Your MFA doesn’t stop it. And when an attacker gets […]
MetInfo CMS CVE-2026-29014 Exploited for Remote Code Execution Attacks
Threat actors are actively exploiting a critical security flaw impacting an open-source content management system (CMS) known as MetInfo, according to new findings from VulnCheck. The vulnerability in question is CVE-2026-29014 (CVSS score: 9.8), a code injection flaw that could result in arbitrary code execution. “MetInfo CMS versions 7.9, 8.0, and 8.1 contain an unauthenticated […]
AI finds 20-year-old bugs in PostgreSQL and MariaDB
Open-source databases are facing a bit of a memory problem as AI helps surface decades-old buffer overflow issues in widely used components. Security researchers have disclosed a set of high and critical-severity vulnerabilities affecting PostgreSQL and MariaDB, with two bugs reportedly tracing their roots back more than 20 years. At Wiz’s zeroday.cloud hacking event, researchers […]
SSL.com rotates their root certificate today, (Tue, May 5th)
I just got an email from SSL.com last night, they are rotating out their root certificate today (May 5,2026). This is normal, business as usual stuff for a CA, but certificates get used for all kinds of things, and sometimes they aren’t used like they should be, so sometimes hiccups happen.
Stealthy malware abuses Microsoft Phone Link to siphon SMS OTPs from enterprise PCs
A newly identified malware campaign is abusing Microsoft’s Phone Link feature to intercept SMS-based one-time passwords and other sensitive mobile data directly from Windows systems. The activity, first observed by Cisco Talos in January 2026, involves a remote access trojan dubbed CloudZ and a custom plugin named Pheno that together allow attackers to harvest credentials […]
DigiCert Revokes Certificates After Support Portal Hack
Hackers delivered malware via a customer chat channel, infected an analyst’s system, and accessed the internal support portal. The post DigiCert Revokes Certificates After Support Portal Hack appeared first on SecurityWeek.
Cybersecurity M&A Roundup: 33 Deals Announced in April 2026
Significant cybersecurity M&A deals announced by Airbus, Cyera, Fortra, Palo Alto Networks, Silverfort, and Socket. The post Cybersecurity M&A Roundup: 33 Deals Announced in April 2026 appeared first on SecurityWeek.
Trellix Source Code Repository Breached
The cybersecurity firm’s investigation has not found any impact on its source code release or distribution process. The post Trellix Source Code Repository Breached appeared first on SecurityWeek.
Cisco Moves to Acquire Astrix Security to Tackle Non-Human Identity Risks
The acquisition strengthens Cisco’s push into identity-centric security for AI and machine access. The post Cisco Moves to Acquire Astrix Security to Tackle Non-Human Identity Risks appeared first on SecurityWeek.
WhatsApp Discloses File Spoofing, Arbitrary URL Scheme Vulnerabilities
The vulnerabilities were reported to Meta through its bug bounty program and were patched with updates released earlier this year. The post WhatsApp Discloses File Spoofing, Arbitrary URL Scheme Vulnerabilities appeared first on SecurityWeek.
MetInfo, Weaver E-cology Vulnerabilities in Attackers’ Crosshairs
The security defects allow unauthenticated, remote attackers to execute arbitrary code through crafted requests. The post MetInfo, Weaver E-cology Vulnerabilities in Attackers’ Crosshairs appeared first on SecurityWeek.
Karakurt Ransomware Negotiator Sentenced to Prison
Deniss Zolotarjovs was directly involved in extortion strategies and in negotiations with victim companies. The post Karakurt Ransomware Negotiator Sentenced to Prison appeared first on SecurityWeek.
We Scanned 1 Million Exposed AI Services. Here's How Bad the Security Actually Is
While the software industry has made genuine strides over the past few decades to deliver products securely, the furious pace of AI adoption is putting that progress at risk. Businesses are moving fast to self-host LLM infrastructure, drawn by the promise of AI as a force multiplier and the pressure to deliver more value faster. […]

ScarCruft Hacks Gaming Platform to Deploy BirdCall Malware on Android and Windows
The North Korea-aligned state-sponsored hacking group known as ScarCruft has compromised a video game platform in a supply chain espionage attack, trojanizing its components with a backdoor called BirdCallto likely target ethnic Koreans residing in China. While prior versions of the backdoor have primarily targeted Windows users only, the supply chain attack is assessed to […]

CISOs step up to the security workforce challenge
A robust cybersecurity program needs a range of skilled people, yet many CISOs continue to face an ongoing skills shortage — and the squeeze may only get worse as AI gains traction. Some 95% of cybersecurity practitioners and decision-makers noted at least one security skills gap at their organization, with almost 60% citing critical or significant […]

Why most zero-trust architectures fail at the traffic layer
Zero trust has become one of the most widely adopted security models in enterprise environments. Organizations invest heavily in identity systems, access policies and modern security tooling. On paper, these environments look well-protected. Yet during incidents, a different reality often emerges. I have worked with organizations where zero-trust initiatives were fully implemented from an identity […]

Weaver E-cology RCE Flaw CVE-2026-22679 Actively Exploited via Debug API
A critical security vulnerability in Weaver (Fanwei) E-cology, an enterprise office automation (OA) and collaboration platform, has come under active exploitation in the wild. The vulnerability (CVE-2026-22679, CVSS score: 9.8) relates to a case of unauthenticated remote code execution affecting Weaver E-cology 10.0 versions prior to 20260312. The issue resides in the “/papi/esearch/data/devops/
Europe Day 2026: let’s celebrate together
Europe Day 2026: let’s celebrate together icolonnm Tue, 05/05/2026 – 09:08 5 May 2026 EDPB Brussels, 5 May – On 9 May each year, Europeans celebrate the anniversary of the Schuman Declaration, the key moment which led to the creation of the EU as we know it today. To mark this special occasion, the European […]

Microsoft Details Phishing Campaign Targeting 35,000 Users Across 26 Countries
Microsoft has disclosed details of a large-scale credential theft campaign that has leveraged a combination of code of conduct-themed lures and legitimate email services to direct users to attacker-controlled domains and steal authentication tokens. The multi-stage campaign, observed between April 14 and 16, 2026, targeted more than 35,000 users across over 13,000 organizations in 26 […]

10 Anzeichen für einen schlechten CSO
Sind IT-Mitarbeiter unzufrieden, kann das an schlechten Führungskräften oder an einer unzureichenden IT-Strategie liegen. Foto: fizkes – shutterstock.com Unternehmen können die für sie allgemein schlechte Lage am Arbeitsmarkt kaum beeinflussen. Doch sie können einige Faktoren vermeiden, die zu Kündigungen durch Mitarbeitende führen. Dazu gehört insbesondere eine schlechte Führung, die fähige Fachkräfte vergrault. Hier sind die […]
ISC Stormcast For Tuesday, May 5th, 2026 https://isc.sans.edu/podcastdetail/9918, (Tue, May 5th)
Post Content

Anthropic Mythos spurs White House to weigh pre-release reviews for high-risk AI models
The Trump administration is in early discussions about whether advanced AI models should be vetted before public release, according to reporting from the New York Times, the Wall Street Journal, and Axios. The conversations center on systems capable of facilitating cyberattacks, particularly models that could help users identify and exploit software vulnerabilities. Officials are considering […]
25-02042.pdf
25-02042.pdf Anonymous (not verified) Mon, 05/04/2026 – 18:05 Case ID 25-02042 Forum FINRA Document Type Award Claimants John Eggleton Respondents Ameritas Investment Corp. Neutrals Christopher M. McMurray Gregory J. Getz Kevin C. Coleman Hearing Site Dallas, TX Award Document 25-02042.pdf Documentum DocID d7e8b226 Award Date Official Mon, 05/04/2026 – 12:00 Related Content Off Claimant Representatives […]
Latvian national involved with Karakurt and other ransomware gangs sentenced for his role in ransomware organization
From the DOJ’s press release: A Latvian national was sentenced today to 102 months in prison for his role in a major Russian ransomware organization that stole from and extorted over 54 companies. According to court documents, Deniss Zolotarjovs (Денисс Золотарёвс), 35, of Moscow, Russia, was a member of a ransomware organization led by former… […]
2023077058901 Oppenheimer Co. Inc. CRD 249 AWC lp.pdf
2023077058901 Oppenheimer Co. Inc. CRD 249 AWC lp.pdf Anonymous (not verified) Mon, 05/04/2026 – 17:35 Case ID 2023077058901 Document Number cff27282 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Mon, 05/04/2026 – 12:00 Related Content Off Attachment 2023077058901 Oppenheimer Co. Inc. CRD 249 AWC lp.pdf
2023077018401 Liquidnet, Inc. CRD 103987 AWC lp.pdf
2023077018401 Liquidnet, Inc. CRD 103987 AWC lp.pdf Anonymous (not verified) Mon, 05/04/2026 – 17:35 Case ID 2023077018401 Document Number 1095603b Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Mon, 05/04/2026 – 12:00 Related Content Off Attachment 2023077018401 Liquidnet, Inc. CRD 103987 AWC lp.pdf
Medicare portal database exposed health providers’ Social Security numbers
Dan Diamond and Clara Ence Morse report: The Trump administration inadvertently exposed the Social Security numbers of health care providers in a database powering a new Medicare portal, The Washington Post found. The Centers for Medicare and Medicaid Services (CMS) last year created a directory to help seniors look up which doctors and medical providers accept… […]
2026088818101 Alan K. Ngo CRD 4273116 AWC ks.pdf
2026088818101 Alan K. Ngo CRD 4273116 AWC ks.pdf Anonymous (not verified) Mon, 05/04/2026 – 16:10 Case ID 2026088818101 Document Number 315d28f7 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals Alan K. Ngo Action Date Mon, 05/04/2026 – 12:00 Related Content Off Attachment 2026088818101 Alan K. Ngo CRD 4273116 AWC ks.pdf Individual CRD 4273116
The rise of the double agent CIO
CIOs of B2B SaaS companies are just as responsible to represent technology as they are to run it. In an environment where the buyer is often another CIO, however, the role becomes something fundamentally different. It’s no longer confined to internal execution. It extends into the market, customer conversations, and the moments that ultimately shape […]
CIOs rethink IT’s operating model to deliver better business outcomes
The IT department at Unum Group had a product management structure and worked in an agile delivery model. This operating model gave IT teams and the company wins by rapidly delivering what they call “investment capabilities” that were aligned to the business. But Shelia Anderson, who became executive vice president and chief information and digital […]
Beyond the hype: The enterprise AI architecture we actually need
My last few years working as a chief digital officer have been, in large part, a sustained exercise in separating what enterprise AI can actually do from what we as a world insist it is about to do. That distinction is not academic. It is the difference between a transformation program that delivers and one […]
Agentic AI is rewiring the SDLC
The next wave of AI in software development goes beyond better code generation: agents are starting to take accountability throughout planning, design, build, test, release and operations. In the teams I work with, this is already changing team dynamics, leadership priorities and what CIOs must do to maintain quality, security and control. The biggest […]
The CIO remit: Treat GenAI as a mission-critical enterprise app
Generative AI has crossed an important threshold. The vast majority (96%) of enterprise IT leaders report that they view GenAI as a strategic priority, on par with mission-critical systems such as ERP and CRM. The technology is no longer confined to isolated pilots; organizations are already embedding GenAI into core enterprise workflows, software-as-a-service (SaaS) platforms, […]
Measuring AI-enabled success: 3 KPIs CIOs should track
AI represents a fundamental shift in how organizations work and innovate. It demands an equally fundamental shift in how CIOs approach governance. Forward-looking leaders are moving beyond traditional gatekeeping by creating “paved roads”: secure, pre-approved pathways that embed security controls, automated data protections, and real-time monitoring directly into AI workflows so teams can innovate rapidly […]
Más allá del césped: así es la revolución digital del Atlético de Madrid
En el fútbol de élite, la diferencia ya no se mide solo en el césped. La experiencia del aficionado, la eficiencia operativa o la capacidad de anticipar decisiones se juegan también en el terreno digital. En ese contexto, el Atlético de Madrid lleva años avanzando en una transformación tecnológica que sitúa al club entre los […]
‘AI is more efficient’ is not enough reason to lay off staff, says Chinese court
Enterprises cannot terminate employees solely to replace them with artificial intelligence, a court in China has ruled, complicating how enterprises seek to justify automation-driven layoffs. The case involved an employee whose role was partly automated, leading to a significant pay cut and their eventual dismissal after they refused reassignment, the court document said. “The termination […]
Antonio Cobos, nuevo CIO de Andersen en España
Andersen Iberia acaba de fichar como director de sistemas de información (CIO) a Antonio Cobos, en los últimos casi siete años director de Tecnología de la constructora OHLA Group. Cobos cuenta con una amplia experiencia en tecnología; además de ser el responsable de la función tecnológica corporativa de la citada multinacional, donde lideró la estabilización […]
SAP’s new API policy restricts AI access, draws customer criticism
With the rise of AI, APIs have once again become increasingly vital tools for fueling transformation. Enterprise software APIs, in particular, provide a critical link for CIOs’ AI strategies, enabling them to extract data from core business systems and feed it into their AI models of choice, for analysis, decision-making, and action. In response to […]
Summary of Court Approved Legal Notice for Pennsylvania State Education Association Data Incident Settlement
PHILADELPHIA, May 4, 2026 /PRNewswire/ — The following release was issued by RG/2 Claims Administration LLC, as Settlement Administrator. If Your Private Information Was Potentially Compromised in a Data Incident Announced by the Pennsylvania State Education Association on March 18, 2025, You May be Eligible for Benefits from a Class Action Settlement. A proposed Settlement has been… […]

Phishing Campaign Hits 80+ Orgs Using SimpleHelp and ScreenConnect RMM Tools
An active phishing campaign has been observed targeting multiple vectors since at least April 2025 with legitimate Remote Monitoring and Management (RMM) software as a way to establish persistent remote access to compromised hosts. The activity, codenamed VENOMOUS#HELPER, has impacted over 80 organizations, most of which are in the U.S., according to Securonix. It shares […]
TeamPCP Weekly Analysis: 2026-W18 (2026-04-27 through 2026-05-03), (Mon, May 4th)
Summary

Progress Patches Critical MOVEit Automation Bug Enabling Authentication Bypass
Progress Software has released updates to address two security flaws in MOVEit Automation, including a critical bug that could result in an authentication bypass. MOVEit Automation (formerly Central) is a secure, server-based managed file transfer (MFT) solution used to schedule and automate file movement workflows in enterprise environments without requiring any custom scripts. The
21-00488(4).pdf
21-00488(4).pdf Anonymous (not verified) Mon, 05/04/2026 – 11:10 Case ID 21-00488 Forum FINRA Document Type Order to Confirm Claimants Bradley Nelson Dennis Hansen Jordan Nelson Leslie Hansen Lindsey Valentini Mark Kramer Nicholas Valentini Noelle Hansen Tyler Hansen Respondents Andrew Burish UBS Financial Services Inc. Neutrals Michael D. Fitzgerald Jan Preece Gaddis Kenneth Colin McRoberts Hearing […]
DShield Honeypot Update, (Mon, May 4th)
This week, I will release a few updates to our DShield honeypot. The update should happen automatically if you have “automatic updates” enabled on your system. There will be two major changes:

⚡ Weekly Recap: AI-Powered Phishing, Android Spying Tool, Linux Exploit, GitHub RCE & More
This week, the shadows moved faster than the patches. While most teams were still triaging last month’s alerts, attackers had already turned control panels into kill switches, kernels into open doors, and open-source pipelines into silent delivery systems. The game has shifted from breach to occupation. They’re living inside SaaS sessions, pushing code with trusted […]

2026: The Year of AI-Assisted Attacks
On December 4, 2025, a 17-year-old was arrested in Osaka under Japan’s Unauthorized Access Prohibition Act. The young man had run malicious code to extract the personal data of over 7 million users of Kaikatsu Club, Japan’s largest internet cafe chain. When asked, the young man shared his motivation for the hack: he wanted to […]

Silver Fox Deploys ABCDoor Malware via Tax-Themed Phishing in India and Russia
The China-based cybercrime group known as Silver Fox has been linked to a new campaign targeting organizations in Russia and India with a new malware called ABCDoor. The activity involved using phishing emails that mimic correspondence from the Income Tax Department of India in December 2025, followed by a similar campaign aimed at Russian entities […]
Security agencies draw red lines around agentic AI deployments
With prompt injection and other attack pathways consistently surfacing across agentic AI deployments, security watchdogs have stepped in, collectively, to draw some hard boundaries. A joint advisory from the US Cybersecurity and Infrastructure Security Agency (CISA) and international partners has called for tighter control over permissions, stronger monitoring, and a more deliberate rollout strategy, urging […]
US Military Reaches Deals With 7 Tech Companies to Use Their AI on Classified Systems
Google, Microsoft, Amazon Web Services, Nvidia, OpenAI, Reflection and SpaceX will provide resources to help augment warfighter decision-making in complex operational environments,” the Defense Department said. The post US Military Reaches Deals With 7 Tech Companies to Use Their AI on Classified Systems appeared first on SecurityWeek.
Edtech Firm Instructure Discloses Data Breach Amid Hacker Leak Threats
Hackers disrupted services and stole names, email addresses, student ID numbers, and user messages. The post Edtech Firm Instructure Discloses Data Breach Amid Hacker Leak Threats appeared first on SecurityWeek.
Over 40,000 Servers Compromised in Ongoing cPanel Exploitation
The attacks likely target CVE-2026-41940, a recently patched zero-day leading to administrative access. The post Over 40,000 Servers Compromised in Ongoing cPanel Exploitation appeared first on SecurityWeek.
OpenAI Rolls Out Advanced Security for ChatGPT Accounts
Advanced Account Security provides stronger login methods, more secure account recovery, shorter sessions, and training exclusion. The post OpenAI Rolls Out Advanced Security for ChatGPT Accounts appeared first on SecurityWeek.
Exploitation of ‘Copy Fail’ Linux Vulnerability Begins
CISA has added the bug to its KEV list, and Microsoft has observed limited exploitation, mainly associated with PoC testing. The post Exploitation of ‘Copy Fail’ Linux Vulnerability Begins appeared first on SecurityWeek.
Finance and Admin Manager Position
Tactical Tech job position for Finance and Admin manager

Critical cPanel Vulnerability Weaponized to Target Government and MSP Networks
A previously unknown threat actor has been observed targeting government and military entities in Southeast Asia, alongside a smaller cluster of managed service providers (MSPs) and hosting providers in the Philippines, Laos, Canada, South Africa, and the U.S., by exploiting the recently disclosed vulnerability in cPanel. The activity, detected by Ctrl-Alt-Intel on May 2, 2026, […]

The fake IT worker problem CISOs can’t ignore
Hiring fake IT workers has been a growing problem in recent years — but it’s often a problem very few want to admit to. From Fortune 500 companies down to smaller organizations, remote hiring practices have been exploited to grant trusted access to individuals who are not who they claim to be creating an insider […]

How CISOs should utilize data security posture management to inform risk
Every CISO eventually faces the same tension: You know your security program needs to mature, but the budget and headcount to do it all aren’t there. That tension is especially sharp when it comes to data security posture management (DSPM). Not every organization can afford, or even needs, the gold standard of DSPM deployment. Full-featured […]

Global Crackdown Arrests 276, Shuts 9 Crypto Scam Centers, Seizes $701M
A coordinated international operation involving U.S. and Chinese authorities has arrested at least 276 suspects and shut down nine scam centers used for cryptocurrency investment fraud schemes targeting Americans, resulting in millions of dollars in losses. The crackdown was led by the Dubai Police, under the United Arab Emirates (UAE) Ministry of Interior, in partnership […]

Was ist ein Botnet?
Ein Botnetz besteht aus vielen “Zombie”-Rechnern und lässt sich beispielsweise einsetzen, um DDoS-Attacken zu fahren. Das sollten Sie zum Thema wissen. FOTOKINA | shutterstock.com Kriminelle Hacker suchen stets nach Möglichkeiten, Malware in großem Umfang zu verbreiten oder Distributed-Denial-of-Service (DDoS)-Angriffe zu fahren. Ein Botnet eignet sich dazu besonders gut. Botnet – Definition Ein Botnet ist eine […]
ISC Stormcast For Monday, May 4th, 2026 https://isc.sans.edu/podcastdetail/9916, (Mon, May 4th)
Post Content
Instructure discloses second data breach in less than a year
Instructure defines itself as the “O.G. champions of open edtech. The makers of Canvas, Mastery, and Parchment (solutions for learning, assessment, and credentialing). Host of the world’s largest online community of educators. (And yes—we’re ‘the panda people.’). We build industry-leading edtech, empowering both teachers and learners at every step of their journey.” Sadly, they were… […]
Wireshark 4.6.5 Released, (Sun, May 3rd)
Wireshark release 4.6.5 fixes 43 vulnerabilities (38 CVEs) and 35 bugs.
CISA Adds Actively Exploited Linux Root Access Bug CVE-2026-31431 to KEV
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday added a recently disclosed security flaw impacting various Linux distributions to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation in the wild. The vulnerability, tracked as CVE-2026-31431 (CVSS score: 7.8), is a case of local privilege escalation (LPE) flaw that could allow […]
Maryland pharmacist indicted on unauthorized computer access related to U. Maryland Medical Center
From the U.S. Attorney’s Office, District of Maryland: A Maryland man is facing federal indictment stemming from an unauthorized computer access scheme involving a Maryland medical system. Matthew Bathula, 41, of Clarksville, is charged with two counts of unauthorized access to a protected computer, and one count of aggravated identity theft while working as a… […]
Sophisticated Deep#Door Backdoor Enables Espionage, Disruption
The stealthy Python-based backdoor framework deploys a persistent Windows implant likely designed for espionage. The post Sophisticated Deep#Door Backdoor Enables Espionage, Disruption appeared first on SecurityWeek.
Two US Security Experts Sentenced to Prison for Helping Ransomware Gang
Ryan Goldberg of Georgia and Kevin Martin of Texas were each sentenced to four years in prison. The post Two US Security Experts Sentenced to Prison for Helping Ransomware Gang appeared first on SecurityWeek.
Google Adjusts Bug Bounties: Chrome Payouts Drop as Android Rewards Rise Amid AI Surge
The maximum reward for a zero-click Pixel Titan M exploit with persistence has increased to $1.5 million. The post Google Adjusts Bug Bounties: Chrome Payouts Drop as Android Rewards Rise Amid AI Surge appeared first on SecurityWeek.
In Other News: Scattered Spider Hacker Arrested, SOC Effectiveness Metrics, NSA Tool Vulnerability
Other noteworthy stories that might have slipped under the radar: OFAC hits Iranian central bank crypto reserves, ADT data leak, CISA guidance for zero trust in OT. The post In Other News: Scattered Spider Hacker Arrested, SOC Effectiveness Metrics, NSA Tool Vulnerability appeared first on SecurityWeek.
New Bluekit Phishing Kit Features AI Assistant
Still under development, Bluekit provides users with automated domain registration and an AI Assistant. The post New Bluekit Phishing Kit Features AI Assistant appeared first on SecurityWeek.
Russian Hacker Known as “Digit” Pleads Guilty to Cyberattacks on Ukraine and the US
Anna Tkach reports: Russian hacker Artem Revensky has admitted to orchestrating cyberattacks targeting critical infrastructure in Ukraine, the United States, and several other nations. He now faces a potential sentence of up to 27 years behind bars. Revensky was a member of the hacking group Sector16, which is allegedly linked to Russian authorities, and carried… […]

Trellix Confirms Source Code Breach With Unauthorized Repository Access
Cybersecurity company Trellix has announced that it suffered a breach that enabled unauthorized access to a “portion” of its source code. It said it “recently identified” the compromise of its source code repository and that it began working with “leading forensic experts” to resolve the matter immediately. It also said it has notified law enforcement […]
UB Greensfelder LLP Comment On Regulatory Notice 26-06
UB Greensfelder LLP Comment On Regulatory Notice 26-06 fnrw-backend Fri, 05/01/2026 – 23:01 Michael J. Charlillo Charlillo, Michael <mcharlillo@ubglaw.com> UB Greensfelder LLP Regulatory Notice 26-06 Core Official Date Fri, 05/01/2026 – 12:00 Comment File UB Greensfelder LLP_26-06_5.1.2026.pdf
Daren A. Luma, PLLC Comment On Regulatory Notice 26-06
Daren A. Luma, PLLC Comment On Regulatory Notice 26-06 fnrw-backend Fri, 05/01/2026 – 22:25 Daren A. Luma, PLLC Daren Luma <dluma@lumalegal.com> Daren A. Luma, PLLC Regulatory Notice 26-06 Core Official Date Fri, 05/01/2026 – 12:00 Comment File Daren A. Luma, PLLC_Daren A. Luma_26-06_5.1.2026.pdf
The Fairbridge Investor Rights Clinic at the Elisabeth Haub School of Law at Pace University Comment On Regulatory Notice 26-06
The Fairbridge Investor Rights Clinic at the Elisabeth Haub School of Law at Pace University Comment On Regulatory Notice 26-06 fnrw-backend Fri, 05/01/2026 – 22:20 Multiple Authors Marasciullo, Janene <jmarasciullo@law.pace.edu> The Fairbridge Investor Rights Clinic at the Elisabeth Haub School of Law at Pace University Regulatory Notice 26-06 Core Official Date Fri, 05/01/2026 – 12:00 […]
Mattson Ricketts Law Firm, LLP Comment On Regulatory Notice 26-06
Mattson Ricketts Law Firm, LLP Comment On Regulatory Notice 26-06 fnrw-backend Fri, 05/01/2026 – 22:15 Patricia L. Vannoy Patricia L. Vannoy <plv@mattsonricketts.com> Mattson Ricketts Law Firm, LLP Regulatory Notice 26-06 Core Official Date Fri, 05/01/2026 – 12:00 Comment File Mattson Ricketts Law Firm, LLP_Patricia L. Vannoy_26-06_5.1.2026.pdf
Mattson Ricketts Law Firm, LLP Comment On Regulatory Notice 26-06
Mattson Ricketts Law Firm, LLP Comment On Regulatory Notice 26-06 fnrw-backend Fri, 05/01/2026 – 22:15 J.L. Spray J L. Spray <jls@mattsonricketts.com> Mattson Ricketts Law Firm, LLP Regulatory Notice 26-06 Core Official Date Fri, 05/01/2026 – 12:00 Comment File Mattson Ricketts Law Firm, LLP_J.L. Spray_26-06_5.1.2026.pdf

AI agents can bypass guardrails and put credentials at risk, Okta study finds
An AI agent that revealed sensitive data without being asked. An agent that overruled its own guardrails. Another that sent credentials to an attacker via Telegram, because it forgot it wasn’t supposed to do so after a reset. It’s no secret that AI agents have huge potential, balanced by equally big risks. What’s becoming apparent, […]

Windows shell spoofing vulnerability puts sensitive data at risk
Microsoft and the US Cybersecurity and Infrastructure Security Agency (CISA) have sounded the alarm about a Windows shell spoofing vulnerability that is already being exploited by attackers. It is not clear by whom as yet, but the main suspects are hackers in Russia. CISA has mandated that all federal agencies patch this vulnerability, designated CVE-2026-32202, by […]
Malicious Ad for Homebrew Leads to MacSync Stealer, (Fri, May 1st)
Introduction
Enterprise search has a relevance problem. Here’s what to do about it.
Traditional keyword-based enterprise search fails to keep up with modern, unstructured data in emails, wikis, and chat, leading to massive productivity losses. Organizations must treat search as a strategic capability and adopt hybrid or AI-powered retrieval to unlock institutional knowledge and gain a competitive advantage. Enterprise search was never really broken. It just stopped keeping […]
Why smaller is smarter: How SLMs make GenAI operational and affordable
I have learned to treat small language models (SLMs) as less of a model category and more of a portfolio strategy. They are the pragmatic answer to a question leaders end up asking sooner or later: How do we scale GenAI across real workflows without turning inference cost, latency, data ownership and boundaries into a […]
What is TOGAF? An EA framework for aligning technology to business
TOGAF definition The Open Group Architecture Framework (TOGAF) is an enterprise architecture methodology that offers a high-level framework for enterprise software development. TOGAF helps organize the development process through a systematic approach aimed at reducing errors, maintaining timelines, staying on budget, and aligning IT with business units to produce quality results. The Open Group developed the framework […]
Enterprise Spotlight: Transforming software development with AI
Artificial intelligence has had an immediate and profound impact on software development. Coding practices, coding tools, developer roles, and the software development process itself are all being reimagined as AI agents advance on every stage of the software development life cycle, from planning and design to testing, deployment, and maintenance. Download the May 2026 issue of the Enterprise Spotlight from the editors […]
Agentic AI is reshaping business ecosystems — CIOs must choose their role carefully
From systems to ecosystems to agents A shift has been underway for some time as value creation moves from slow, firm-centric to more rapid, co-created across a network of participants. Customers don’t experience systems; they experience outcomes. Those outcomes are assembled across a network of partners, platforms and capabilities that must work together as one. […]
The cloud migration fulfilling FC Bayern Munich’s AI ambitions
Management for Germany’s record-holding football championship team aims to optimize processes and provide new digital services using AI. Here, CIO Michael Fichtner discusses what the club’s IT department has implemented, and what advantages they’ll bring to the company internally, and to fans around the world. Why did FC Bayern migrate to SAP Cloud ERP Private? Migrating […]
19 vibe coding tools for democratizing app development
Who doesn’t want an AI to pump out more code in minutes than a human might write in a month? Who doesn’t like magic? That’s what the hype around vibe coding has asked of developers and business users alike since its inception. But now the tools might have matured enough to deliver. Yes, cautious leaders […]
From copilot to control plane: Where serious AI governance starts
In practice, that means setting the rules for identity, model access, permissions, logging and human approval before AI tools or agents are allowed to operate inside business workflows. The practical starting point is to identify where AI is already touching repositories, tickets, internal knowledge and business systems, then establish a minimum common control set across […]
The architectural decision shaping enterprise AI
Every enterprise AI initiative contains an architectural decision that rarely makes it into the business case or the steering committee deck. It doesn’t have a line item. It often gets made by a developer on a Tuesday afternoon based on whatever the default configuration was. And it determines, more than almost anything else, whether your […]
While you embrace AI, fix this fast
AI is here, enabling tangible and real-world use cases. Boards are talking about it. Teams are experimenting & deploying it. Roadmaps are being rewritten around it. But there’s a hard truth most organizations are not always paying attention to: If your foundation isn’t secure, AI will amplify your risk, not just your capability. Much of […]
Michigan residents sue Thomson Reuters over public display of Social Security numbers
Caitlyn Rosen reports: A class of Michiganders asserted in a federal lawsuit filed Thursday that a Thomson Reuters search engine wrongfully published their Social Security numbers. In an 11-page lawsuit filed in the U.S. District Court for the Eastern District of Michigan, the class claims Reuters search engines publicly displayed plaintiffs’ social security numbers in… […]
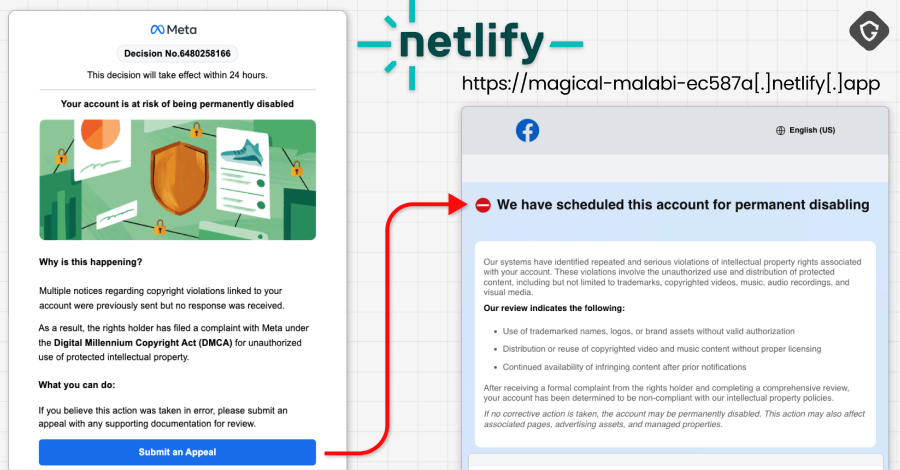
30,000 Facebook Accounts Hacked via Google AppSheet Phishing Campaign
A newly discovered Vietnamese-linked operation has been observed using a Google AppSheet as a “phishing relay” to distribute phishing emails with an aim to compromise Facebook accounts. The activity has been codenamed AccountDumpling by Guardio, with the scheme selling the stolen accounts back through an illicit storefront run by the threat actors. In all, roughly […]
NYSDFS Secures $2.25 Million Cybersecurity Settlement with Delta Dental
There is an update regarding the 2023 Delta Dental breach involving MOVEit software. Delta Dental was one of many customers whose patient data was exposed after Clop exploited a zero-day vulnerability to attack MOVEit and acquire its clients’ data. More than 7 million patients were reportedly affected by the breach, although the number specific to New… […]

Cybercrime Groups Using Vishing and SSO Abuse in Rapid SaaS Extortion Attacks
Cybersecurity researchers are warning of two cybercrime groups that are carrying out “rapid, high-impact attacks” operating almost within the confines of SaaS environments, while leaving minimal traces of their actions. The clusters, Cordial Spider (aka BlackFile, CL-CRI-1116, O-UNC-045, and UNC6671) and Snarky Spider (aka O-UNC-025 and UNC6661), have been attributed to high-speed data theft and

China-Linked Hackers Target Asian Governments, NATO State, Journalists, and Activists
Cybersecurity researchers have disclosed details of a new China-aligned espionage campaign targeting government and defense sectors across South, East, and Southeast Asia, along with one European government belonging to NATO. Trend Micro has attributed the activity to a threat activity cluster it tracks under the temporary designation SHADOW-EARTH-053. The adversarial collective is assessed to
Never forgotten.
In memoriam. Ayrton Senna, the greatest Formula One driver of all times, lost to this world on May 1, 1994 in a terrible crash at Imola. In the years following his death, some have matched or exceeded his record, but none of them could hold a candle to him. (Image credit: Getty Images) Source
Careful Adoption of Agentic AI Services
CISA, in collaboration with the Australian Signals Directorate’s Australian Cyber Security Centre (ASD’s ACSC) and other international and U.S. partners, released guidance for organizations on adopting agentic artificial intelligence (AI) systems. This guide outlines key security challenges and risks associated with agentic AI, and provides actionable steps for designing, deploying, and operating these systems safely. […]
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2026-31431 Linux Kernel Incorrect Resource Transfer Between Spheres Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing […]
Unprecedented: Private Equity Firm Potentially on Hook for PowerSchool’s Data Breach
Tyler Bridegan, Scott Hyman, Patrick Strubbe, and Sarah Wilk of Womble Bond Dickinson write: In a first of its kind, a California federal judge allowed claims against Bain Capital to proceed based on a data breach at its subsidiary, PowerSchool. Notably, many of the claims are based on conduct that occurred before Bain’s acquisition of PowerSchool. Although… […]
EnOcean SmartServer Flaws Expose Buildings to Remote Hacking
Claroty researchers discovered two vulnerabilities that can be exploited for security bypass and remote code execution. The post EnOcean SmartServer Flaws Expose Buildings to Remote Hacking appeared first on SecurityWeek.
Critical Gemini CLI Flaw Enabled Host Code Execution, Supply Chain Attacks
An attacker could have planted a malicious configuration to execute commands outside the sandbox. The post Critical Gemini CLI Flaw Enabled Host Code Execution, Supply Chain Attacks appeared first on SecurityWeek.
SAP NPM Packages Targeted in Supply Chain Attack
The Mini Shai-Hulud attack introduced a preinstall hook to fetch and execute a Bun binary and bypass security monitoring. The post SAP NPM Packages Targeted in Supply Chain Attack appeared first on SecurityWeek.
SonicWall Urges Immediate Patching of Firewall Vulnerabilities
The bugs could be exploited to bypass security controls, access restricted services, and crash firewalls. The post SonicWall Urges Immediate Patching of Firewall Vulnerabilities appeared first on SecurityWeek.
AI Fuels ‘Industrial’ Cybercrime as Time-to-Exploit Shrinks to Hours
Industrialized cybercrime delivers attacks with greater scale, speed and success. Defenders must match this with use of AI and automation. The post AI Fuels ‘Industrial’ Cybercrime as Time-to-Exploit Shrinks to Hours appeared first on SecurityWeek.
Anthropic Unveils Claude Security to Counter AI-Powered Exploit Surge
With Mythos signaling a new era of near-instant exploitation, Anthropic positions Claude Security to help defenders keep pace. The post Anthropic Unveils Claude Security to Counter AI-Powered Exploit Surge appeared first on SecurityWeek.
1,800 Hit in Mini Shai-Hulud Attack on SAP, Lightning, Intercom
The compromised Lightning and Intercom packages have a combined monthly download count of nearly 10 million. The post 1,800 Hit in Mini Shai-Hulud Attack on SAP, Lightning, Intercom appeared first on SecurityWeek.
FBI Warns of Surge in Hacker-Enabled Cargo Theft
A new alert from the FBI says criminal enterprises are hacking both brokers and carriers to steal cargo for resale. The post FBI Warns of Surge in Hacker-Enabled Cargo Theft appeared first on SecurityWeek.
Hugging Face, ClawHub Abused for Malware Distribution
Threat actors are relying on social engineering to lure users into downloading files containing malicious instructions. The post Hugging Face, ClawHub Abused for Malware Distribution appeared first on SecurityWeek.
Cisco Releases Open Source Tool for AI Model Provenance
The new kit aims to address risks related to poisoned models, regulatory issues, supply chain integrity, and incident response. The post Cisco Releases Open Source Tool for AI Model Provenance appeared first on SecurityWeek.
Kentwood, Michigan, schools say student malware disrupted Wi-Fi
DysruptionHub reports: Kentwood Public Schools said districtwide Wi-Fi was disrupted after a student used malicious software designed to interfere with the school system’s network. The district said outside experts helped isolate the issue, which affected Wi-Fi connectivity across its schools, and that the problems “appear” to have been resolved. Kentwood Public Schools serves students in… […]

Top Five Sales Challenges Costing MSPs Cybersecurity Revenue
The managed security services market is projected to grow from $38.31 billion in 2025 to $69.16 billion by 2030[1], with cybersecurity being the fastest-growing sector[2]. Despite this opportunity, many MSPs leave revenue on the table because their go-to-market strategy fails to connect technical expertise with business needs. This execution gap is where most deals stall. […]

Human-centric failures: Why BEC continues to work despite MFA
Business email compromise (BEC) is still thriving even in organizations that have implemented multi-factor authentication (MFA). As security professionals, we often assume that MFA is the silver bullet for email security, but real-world incidents suggest otherwise. Attackers exploit human behaviors, process gaps and operational blind spots that MFA alone cannot address. In many modern BEC […]

Two Cybersecurity Professionals Get 4-Year Sentences in BlackCat Ransomware Attacks
The U.S. Department of Justice (DoJ) on Thursday announced the sentencing of two cybersecurity professionals to four years each in prison for their role in facilitating BlackCat ransomware attacks in 2023. Ryan Goldberg, 40, of Georgia, and Kevin Martin, 36, of Texas, were accused of deploying the ransomware against multiple victims located throughout the U.S. […]
Poisoned Ruby Gems and Go Modules Exploit CI Pipelines for Credential Theft
A new software supply chain attack campaign has been observed using sleeper packages as a conduit to subsequently push malicious payloads that enabled credential theft, GitHub Actions tampering, and SSH persistence. The activity has been attributed to the GitHub account “BufferZoneCorp,” which has published a set of repositories that are associated with malicious Ruby gems […]

Just 34% of cyber pros plan to stick with their current employer
Declining job satisfaction means that only one in three (34%) cybersecurity professionals plan to stay with their current employer, increasing the pressure on CISOs’ talent retention strategies. And according to a survey of 500 cybersecurity professionals by IANS and Artico Search, while salary remains important it is not the primary driver of retention. Flexible work […]

Enterprise Spotlight: Transforming software development with AI
Artificial intelligence has had an immediate and profound impact on software development. Coding practices, coding tools, developer roles, and the software development process itself are all being reimagined as AI agents advance on every stage of the software development life cycle, from planning and design to testing, deployment, and maintenance. Download the May 2026 issue of the Enterprise Spotlight from the editors […]
Managing OT risk at scale: Why OT cyber decisions are leadership decisions
The first time I approached an OT environment, I assumed that the strategies effective in IT cybersecurity would be equally applicable. I was wrong. The experience revealed a fundamental difference, highlighting the need for a distinct approach to OT cyber risk management. The mistake was not technical. It was conceptual. I was treating OT as […]

4 ways to prepare your SOC for agentic AI
According to IDC, agentic AI is on track to become mainstream infrastructure. The analyst firm expects 45% of organizations to have autonomous agents operating at scale across critical business functions by 2030. In enterprise SOCs, AI is already reshaping functions like alert triage, enrichment, data correlation, IOC validation and initial containment. It could soon move […]
ISC Stormcast For Friday, May 1st, 2026 https://isc.sans.edu/podcastdetail/9914, (Fri, May 1st)
Post Content

‘Trivial’ exploit can give attackers root access to Linux kernel
CSOs must ensure their Linux-based systems block unauthorized privilege escalation until distros release patches to plug a serious kernel vulnerability affecting all Linux distributions shipped since 2017. Until fixes are available for what’s been dubbed the Copy Fail logic bug (CVE-2026-31431), which lets users easily obtain root access, there isn’t much CSOs can do, says […]
Snake Oilers: Ent AI, Spacewalk and Mondoo
In this edition of the Snake Oilers podcast three vendors stop by to pitch the audience on their products: Ent AI: Co-founder Brandon Dixon pitched Ent, an intent-aware, AI-powered endpoint security control. Spacewalk AI: Founders Chris Fuller and Tim Wenzlau pitch Spacewalk, an AI-powered incident response platform. Mondoo: Co-founder Dominik Richter pitches Mondoo, an AI-powered […]